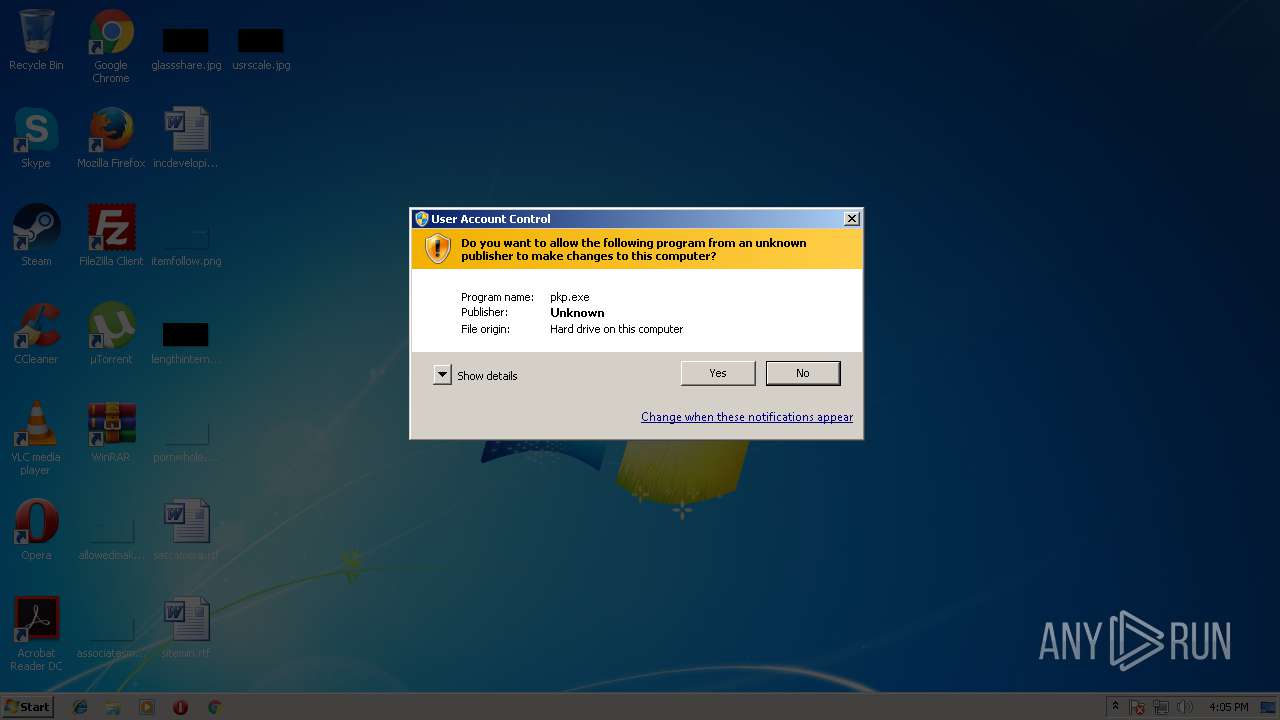
| File name: | pkp.exe |
| Full analysis: | https://app.any.run/tasks/1f09eae1-6613-421d-8ce3-a87aea834d19 |
| Verdict: | Malicious activity |
| Analysis date: | September 05, 2018, 15:05:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EC424423C5B5718722C0D2B3278D02CC |
| SHA1: | 107D2EF7357DD31DE5944BA0A18EDB98EEB89324 |
| SHA256: | CC67F37950BDA3FC755E693B05355696CA785E945BE86A5D0B11F120AB3CB3B6 |
| SSDEEP: | 6144:FeBtz44JNmIn+ebrcZ3dIG9d/9dwW4mNSGIFrrOCV83khh9DQzrpeQLf0k:FB4i2IdIGUD/nrKB0hDQvkQLh |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3708)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 2792)
SUSPICIOUS
Executable content was dropped or overwritten
- pkp.exe (PID: 584)
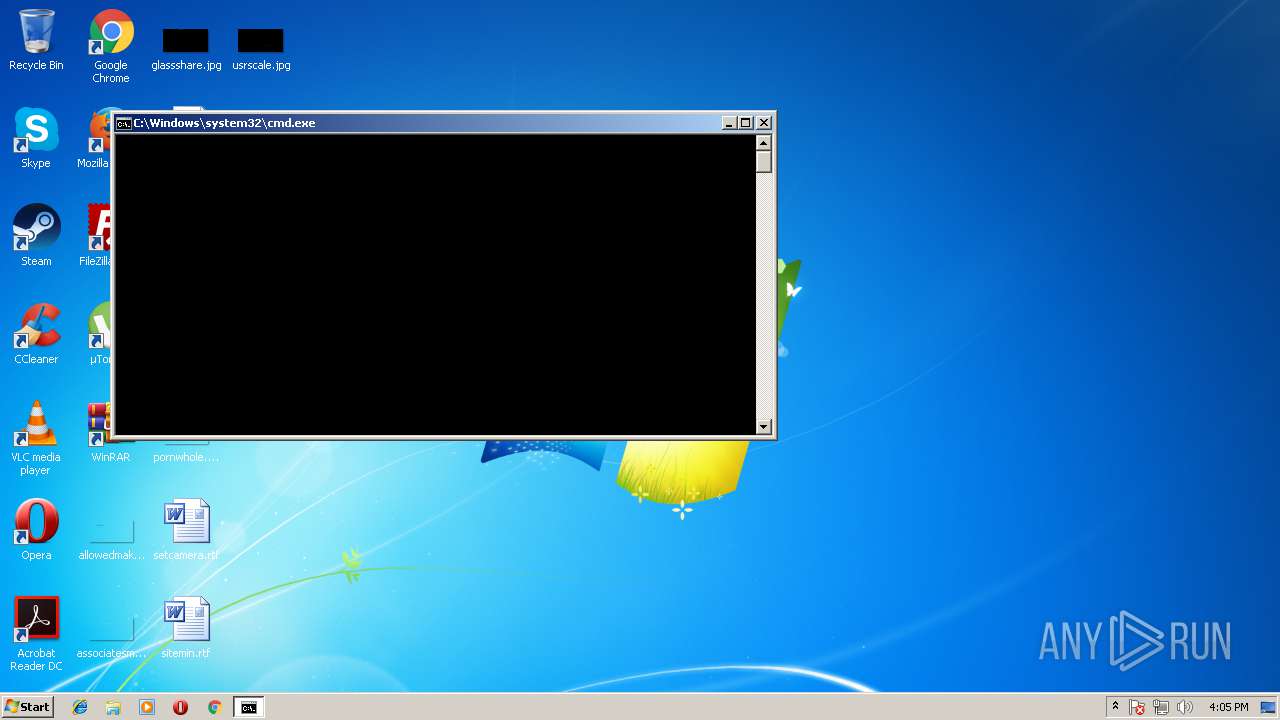
Starts CMD.EXE for commands execution
- pkp.exe (PID: 584)
Creates files in the Windows directory
- pkp.exe (PID: 584)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:12:26 16:34:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 45056 |
| InitializedDataSize: | 32256 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Dec-2004 15:34:28 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 26-Dec-2004 15:34:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000B000 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39933 |
.data | 0x0000C000 | 0x00010000 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.87523 |
.idata | 0x0001C000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.24057 |
.rsrc | 0x0001D000 | 0x00005F24 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.79653 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.5 | 4 | Latin 1 / Western European | Chinese - PRC | UNKNOWN |
2 | 3.88998 | 1384 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 4.12176 | 744 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 4.68705 | 2216 | Latin 1 / Western European | Russian - Russia | RT_ICON |
7 | 5.31352 | 226 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.80297 | 336 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.51373 | 216 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 4.80037 | 420 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
100 | 2.64576 | 62 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
101 | 4.19099 | 2998 | Latin 1 / Western European | Chinese - PRC | RT_BITMAP |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Users\admin\AppData\Local\Temp\pkp.exe" | C:\Users\admin\AppData\Local\Temp\pkp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1192 | "C:\Users\admin\AppData\Local\Temp\pkp.exe" | C:\Users\admin\AppData\Local\Temp\pkp.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2792 | cmd /c ""C:\Windows\H264MediaPlayPlugins\register.bat" " | C:\Windows\system32\cmd.exe | — | pkp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3708 | regsvr32 "C:\Windows\H264MediaPlayPlugins\MediaDecFilter.ax" /s | C:\Windows\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
58
Read events
40
Write events
18
Delete events
0
Modification events
| (PID) Process: | (584) pkp.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%Windows |
Value: C:\Windows | |||
| (PID) Process: | (584) pkp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (584) pkp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3708) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Media Type\Extensions\.h264 |
| Operation: | write | Name: | Source Filter |
Value: {D4DA6077-2239-4C9E-AE16-C78DD9F35631} | |||
| (PID) Process: | (3708) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Media Type\Extensions\.mp4 |
| Operation: | write | Name: | Source Filter |
Value: {D4DA6077-2239-4C9E-AE16-C78DD9F35631} | |||
| (PID) Process: | (3708) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D4DA6077-2239-4C9E-AE16-C78DD9F35631} |
| Operation: | write | Name: | |
Value: H264 File Source | |||
| (PID) Process: | (3708) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D4DA6077-2239-4C9E-AE16-C78DD9F35631}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Windows\H264MediaPlayPlugins\MediaDecFilter.ax | |||
| (PID) Process: | (3708) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D4DA6077-2239-4C9E-AE16-C78DD9F35631}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (3708) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{76C90120-D6E9-4CDD-8163-466B950BB133} |
| Operation: | write | Name: | |
Value: H264 File Source Property Page | |||
| (PID) Process: | (3708) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{76C90120-D6E9-4CDD-8163-466B950BB133}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Windows\H264MediaPlayPlugins\MediaDecFilter.ax | |||
Executable files
5
Suspicious files
0
Text files
1
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 584 | pkp.exe | C:\Windows\H264MediaPlayPlugins\MediaDecFilter.ax | executable | |
MD5:— | SHA256:— | |||
| 584 | pkp.exe | C:\Windows\H264MediaPlayPlugins\H264Play.dll | executable | |
MD5:— | SHA256:— | |||
| 584 | pkp.exe | C:\Windows\H264MediaPlayPlugins\StreamReader.dll | executable | |
MD5:EDD4713C052CC483886CAC892E3958F0 | SHA256:5DAAC4738A487181368A7A2F0822C089A7A05FE132F2C21BC128D6216A355987 | |||
| 584 | pkp.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat | hiv | |
MD5:— | SHA256:— | |||
| 584 | pkp.exe | C:\Windows\H264MediaPlayPlugins\register.bat | text | |
MD5:— | SHA256:— | |||
| 584 | pkp.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1 | log | |
MD5:— | SHA256:— | |||
| 584 | pkp.exe | C:\Users\Administrator\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 584 | pkp.exe | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
| 584 | pkp.exe | C:\Windows\H264MediaPlayPlugins\hi_h264dec.dll | executable | |
MD5:3B3FE802F6CE692568DCFF60758CB81A | SHA256:3E6BD5374379288783069FDB2E59D77849F0237F57B4EA4712434EDCD2B17964 | |||
| 584 | pkp.exe | C:\Windows\H264MediaPlayPlugins\DllDeinterlace.dll | executable | |
MD5:734654F3C6B732FAD89FCC17F3816DF1 | SHA256:1616778BABE6DA0C0CEEF10CBC7814A584299AAA01106B18C26F4E1F4DA1DD74 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report