| File name: | CrackerHack.exe |
| Full analysis: | https://app.any.run/tasks/ca7c95cc-f714-49b6-ac07-c43d10fafe83 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | May 30, 2020, 14:07:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D6290A2A4F0B7BB8AD44E95882F66E84 |
| SHA1: | E6BBFD454185A95850B59E412F30A9C62F8F9C0E |
| SHA256: | CC51FA808F70664E1F1C8439D782FC681A10FC2B906DF8EDFA6318D661948757 |
| SSDEEP: | 49152:azXv/mzEhO82b2LnydW2YAZx8UClcqPkcwlqZUjdUkZYRfUCRq:az3mQhb2b2LydW2Kdl7Pk3lqgKkafU/ |
MALICIOUS
Application was dropped or rewritten from another process
- build.exe (PID: 332)
Poullight was detected
- build.exe (PID: 332)
Actions looks like stealing of personal data
- build.exe (PID: 332)
SUSPICIOUS
Executable content was dropped or overwritten
- CrackerHack.exe (PID: 2644)
Reads Environment values
- build.exe (PID: 332)
Reads the cookies of Google Chrome
- build.exe (PID: 332)
Creates files in the user directory
- build.exe (PID: 332)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (75) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (15.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.6) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:15 18:44:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 3584 |
| InitializedDataSize: | 2201600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ae1 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Unicode |
| CompanyName: | RF-Cheats.ru |
| FileDescription: | TotalInjector |
| FileVersion: | 1.8 |
| InternalName: | TotalInjector.exe |
| LegalCopyright: | (c) RF-Cheats.ru. Все права защищены. |
| OriginalFileName: | TotalInjector.exe |
| ProductName: | Total DLL injector |
| ProductVersion: | 1.8 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jun-2013 16:44:28 |
| Detected languages: |
|
| CompanyName: | RF-Cheats.ru |
| FileDescription: | TotalInjector |
| FileVersion: | 1.8 |
| InternalName: | TotalInjector.exe |
| LegalCopyright: | (c) RF-Cheats.ru. Все права защищены. |
| OriginalFilename: | TotalInjector.exe |
| ProductName: | Total DLL injector |
| ProductVersion: | 1.8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-Jun-2013 16:44:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000C26 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.14633 |
.rdata | 0x00002000 | 0x000004C0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.21236 |
.data | 0x00003000 | 0x0000D6F0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.72555 |
.rsrc | 0x00011000 | 0x00218B20 | 0x00218C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99743 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.50948 | 760 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
2 | 7.99786 | 2132077 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
128 | 1.81924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
4097 | 5.53242 | 149 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
shlwapi.dll |
user32.dll |
Total processes
40
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Users\admin\AppData\Local\Temp\build.exe" | C:\Users\admin\AppData\Local\Temp\build.exe | CrackerHack.exe | ||||||||||||
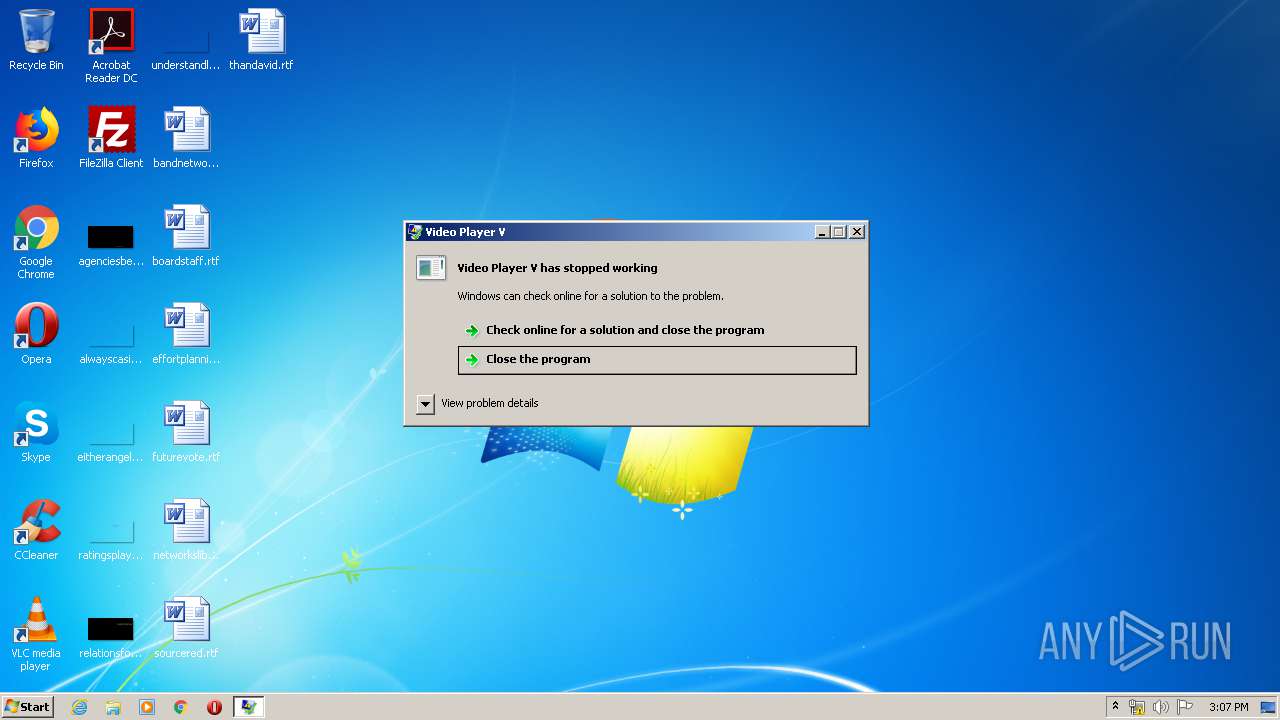
User: admin Integrity Level: MEDIUM Description: Video Player V Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2644 | "C:\Users\admin\AppData\Local\Temp\CrackerHack.exe" | C:\Users\admin\AppData\Local\Temp\CrackerHack.exe | explorer.exe | ||||||||||||
User: admin Company: RF-Cheats.ru Integrity Level: MEDIUM Description: TotalInjector Exit code: 0 Version: 1.8 Modules
| |||||||||||||||
Total events
415
Read events
394
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2644) CrackerHack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2644) CrackerHack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (332) build.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | vga.drv 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
| (PID) Process: | (332) build.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\build_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (332) build.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\build_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (332) build.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\build_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (332) build.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\build_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (332) build.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\build_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (332) build.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\build_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (332) build.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\build_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
2
Suspicious files
5
Text files
33
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2644 | CrackerHack.exe | C:\Users\admin\AppData\Local\Temp\Bot_Hack.exe | executable | |
MD5:— | SHA256:— | |||
| 332 | build.exe | C:\Users\admin\AppData\Local\Temp\pl2d4vfegvbqddddkms0zhqii0i | text | |
MD5:— | SHA256:— | |||
| 332 | build.exe | C:\Users\admin\AppData\Local\vhrpt1a2\Stealer Files\Desktop Files\futurevote.rtf | text | |
MD5:— | SHA256:— | |||
| 332 | build.exe | C:\Users\admin\AppData\Local\vhrpt1a2\Stealer Files\Desktop Files\bandnetworks.rtf | text | |
MD5:— | SHA256:— | |||
| 332 | build.exe | C:\Users\admin\AppData\Local\vhrpt1a2\Stealer Files\Desktop Files\effortplanning.rtf | text | |
MD5:— | SHA256:— | |||
| 332 | build.exe | C:\Users\admin\AppData\Local\vhrpt1a2\Stealer Files\Desktop Files\boardstaff.rtf | text | |
MD5:— | SHA256:— | |||
| 332 | build.exe | C:\Users\admin\AppData\Local\vhrpt1a2\Stealer Files\Desktop Files\thandavid.rtf | text | |
MD5:— | SHA256:— | |||
| 332 | build.exe | C:\Users\admin\AppData\Local\vhrpt1a2\Stealer Files\Desktop Files\sourcered.rtf | text | |
MD5:— | SHA256:— | |||
| 332 | build.exe | C:\Users\admin\AppData\Local\vhrpt1a2\Stealer Files\Desktop Files\networkslibrary.rtf | text | |
MD5:— | SHA256:— | |||
| 332 | build.exe | C:\Users\admin\AppData\Local\vhrpt1a2\Stealer Files\Documents Files\conditionmeet.rtf | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
332 | build.exe | GET | 404 | 91.210.201.108:80 | http://ru-uid-507352920.pp.ru/example.exe | RU | html | 196 b | suspicious |
332 | build.exe | POST | 200 | 141.8.194.203:80 | http://a0441467.xsph.ru/gate.php | RU | text | 4 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
332 | build.exe | 91.210.201.108:80 | ru-uid-507352920.pp.ru | ICC Makhachkala-Telecom Ltd. | RU | suspicious |
332 | build.exe | 141.8.194.203:80 | a0441467.xsph.ru | Sprinthost.ru LLC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
a0441467.xsph.ru |
| malicious |
ru-uid-507352920.pp.ru |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
332 | build.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
332 | build.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no accept headers |
332 | build.exe | A Network Trojan was detected | STEALER [PTsecurity] Poulight |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
build.exe | CLR: Managed code called FailFast, saying " |
build.exe | "
|
build.exe | "
|