| URL: | http://link.benchmarkone.com/api/LinkHandler/getaction?redirectParam2=K09weU5vMDBKWXA5TmxLTkhHN3BEWmUyeDF6TUVIbXZ6cVZNSVdOTys0YzRZMkVveEhFWlVZU1h1UGNtcGVRR2ZJWXBKV0hEcUNMM0FlcVhVaTc2ZEd2VVFYeHh4WGo0S1gxdk9xVjJ0R1duYytXV3pNbTg1RWllTC9xc0dNMWpFSDZ6VDBRN0s3UHBXNlJuSGIrakkvMnpLU3d4Z2dYdXFmQ1diNzZzanE1Mi9HRE14M2NRYlE9PQ%3d%3d |
| Full analysis: | https://app.any.run/tasks/903559c2-1ea8-42d8-a20b-52e6d3dac5ae |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2024, 05:09:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3115E0A8A78162C304B299517C3F9846 |
| SHA1: | FFD65859A76437BA977444F17AAFEA5F9ECBB4B6 |
| SHA256: | CC4C4076BE6E4B3F7F7BB5BD12D6A20B2D14A7246F7DE50680962A93B3C18082 |
| SSDEEP: | 6:CShO6DiC0JgvS6kvOrBgKgKkaHSbpifn/GEhEBBl7dhW5CZXyMGGRhT8XB8XJRNy:BO6DiNJ+f1mi/9hwXAYiCRhTGibqAW |
MALICIOUS
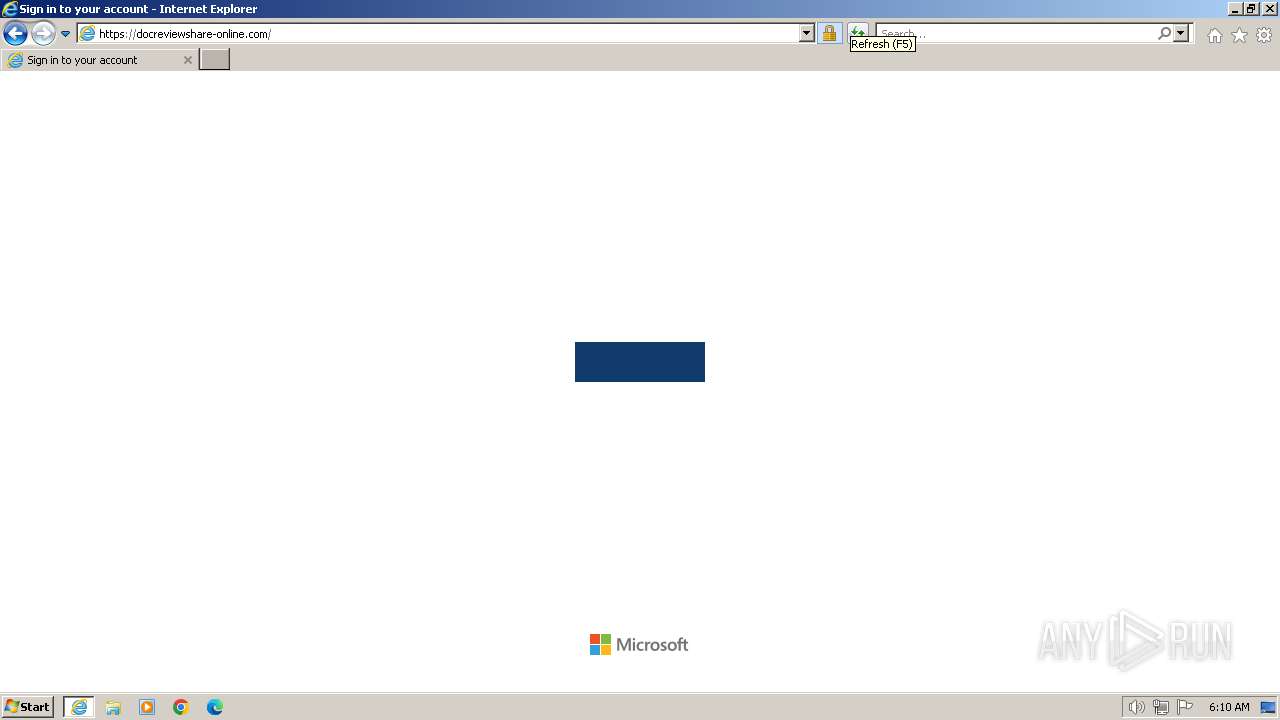
PHISHING has been detected (SURICATA)
- iexplore.exe (PID: 3964)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3956 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://link.benchmarkone.com/api/LinkHandler/getaction?redirectParam2=K09weU5vMDBKWXA5TmxLTkhHN3BEWmUyeDF6TUVIbXZ6cVZNSVdOTys0YzRZMkVveEhFWlVZU1h1UGNtcGVRR2ZJWXBKV0hEcUNMM0FlcVhVaTc2ZEd2VVFYeHh4WGo0S1gxdk9xVjJ0R1duYytXV3pNbTg1RWllTC9xc0dNMWpFSDZ6VDBRN0s3UHBXNlJuSGIrakkvMnpLU3d4Z2dYdXFmQ1diNzZzanE1Mi9HRE14M2NRYlE9PQ%3d%3d" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3956 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 695
Read events
21 557
Write events
95
Delete events
43
Modification events
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31099653 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31099653 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
16
Text files
15
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab29E9.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar29EA.tmp | cat | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab29EB.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar29FC.tmp | cat | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
32
DNS requests
19
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | iexplore.exe | GET | 304 | 92.122.192.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?36ca310eb28aaa33 | unknown | — | — | unknown |
3964 | iexplore.exe | GET | 301 | 52.203.176.26:80 | http://link.benchmarkone.com/api/LinkHandler/getaction?redirectParam2=K09weU5vMDBKWXA5TmxLTkhHN3BEWmUyeDF6TUVIbXZ6cVZNSVdOTys0YzRZMkVveEhFWlVZU1h1UGNtcGVRR2ZJWXBKV0hEcUNMM0FlcVhVaTc2ZEd2VVFYeHh4WGo0S1gxdk9xVjJ0R1duYytXV3pNbTg1RWllTC9xc0dNMWpFSDZ6VDBRN0s3UHBXNlJuSGIrakkvMnpLU3d4Z2dYdXFmQ1diNzZzanE1Mi9HRE14M2NRYlE9PQ%3d%3d | unknown | — | — | unknown |
3964 | iexplore.exe | GET | 304 | 92.122.192.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b150b552b216e1f4 | unknown | — | — | unknown |
3964 | iexplore.exe | GET | 200 | 92.122.192.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0d63d644c62b7637 | unknown | — | — | unknown |
3964 | iexplore.exe | GET | 200 | 2.19.217.103:80 | http://x2.c.lencr.org/ | unknown | — | — | unknown |
3956 | iexplore.exe | GET | 304 | 92.122.192.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?76ad697231f9b13b | unknown | — | — | unknown |
3964 | iexplore.exe | GET | 200 | 2.19.217.103:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
3956 | iexplore.exe | GET | 304 | 92.122.192.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e55f0cb727843010 | unknown | — | — | unknown |
3964 | iexplore.exe | GET | 200 | 92.122.192.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9df0723acf4b4299 | unknown | — | — | unknown |
3964 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3964 | iexplore.exe | 52.203.176.26:80 | link.benchmarkone.com | AMAZON-AES | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3964 | iexplore.exe | 104.17.96.13:443 | cloudflare-ipfs.com | CLOUDFLARENET | — | unknown |
3964 | iexplore.exe | 92.122.192.65:80 | ctldl.windowsupdate.com | Akamai International B.V. | GB | whitelisted |
3964 | iexplore.exe | 2.19.217.103:80 | x1.c.lencr.org | Akamai International B.V. | NL | unknown |
3956 | iexplore.exe | 104.17.96.13:443 | cloudflare-ipfs.com | CLOUDFLARENET | — | unknown |
3956 | iexplore.exe | 92.122.192.65:80 | ctldl.windowsupdate.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
link.benchmarkone.com |
| unknown |
cloudflare-ipfs.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
docreviewshare-online.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
code.jquery.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO Peer to Peer File Sharing Service in DNS Lookup (cloudflare-ipfs .com) |
3964 | iexplore.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cloudflare-ipfs .com) |
3964 | iexplore.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cloudflare-ipfs .com) |
3964 | iexplore.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cloudflare-ipfs .com) |
3956 | iexplore.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cloudflare-ipfs .com) |
3956 | iexplore.exe | Misc activity | ET INFO Peer to Peer File Sharing Service Domain in TLS SNI (cloudflare-ipfs .com) |
3964 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |
3964 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Phishing domain chain detected (ipfsquery) |
3964 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
3964 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |