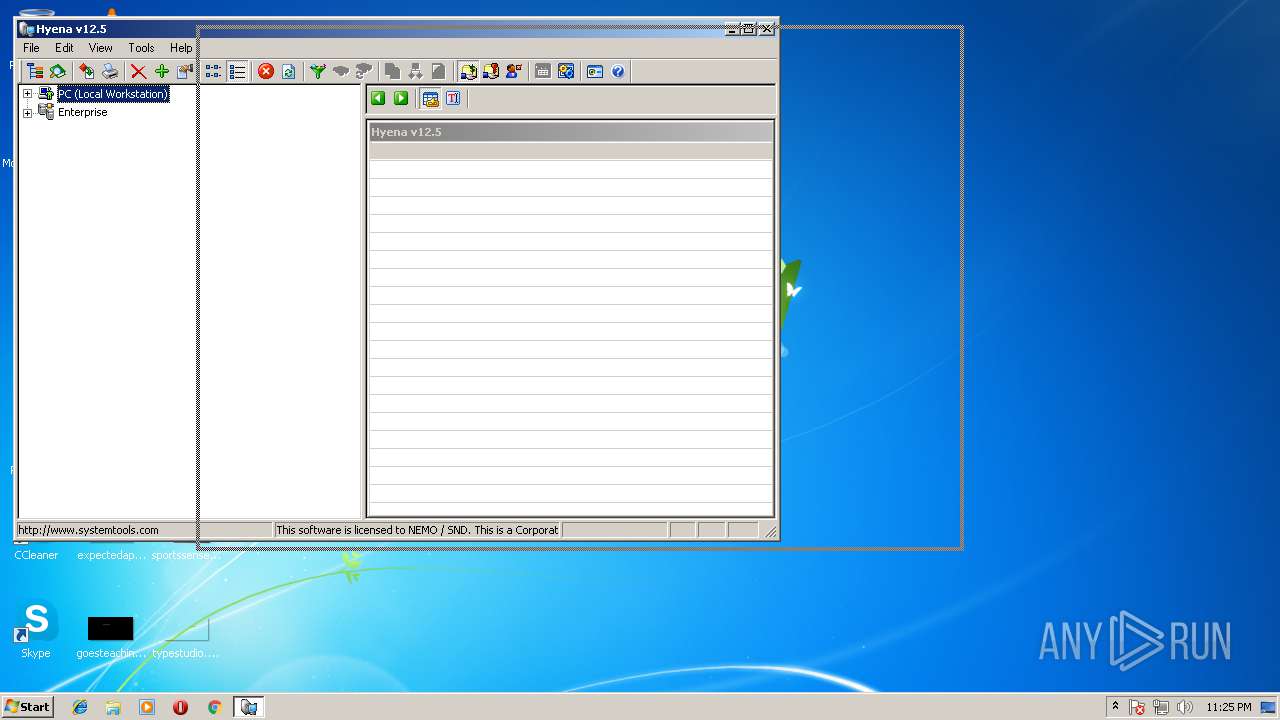
| File name: | Hyena.exe |
| Full analysis: | https://app.any.run/tasks/10b40dc8-f37c-4de3-bc73-d07ede58eb43 |
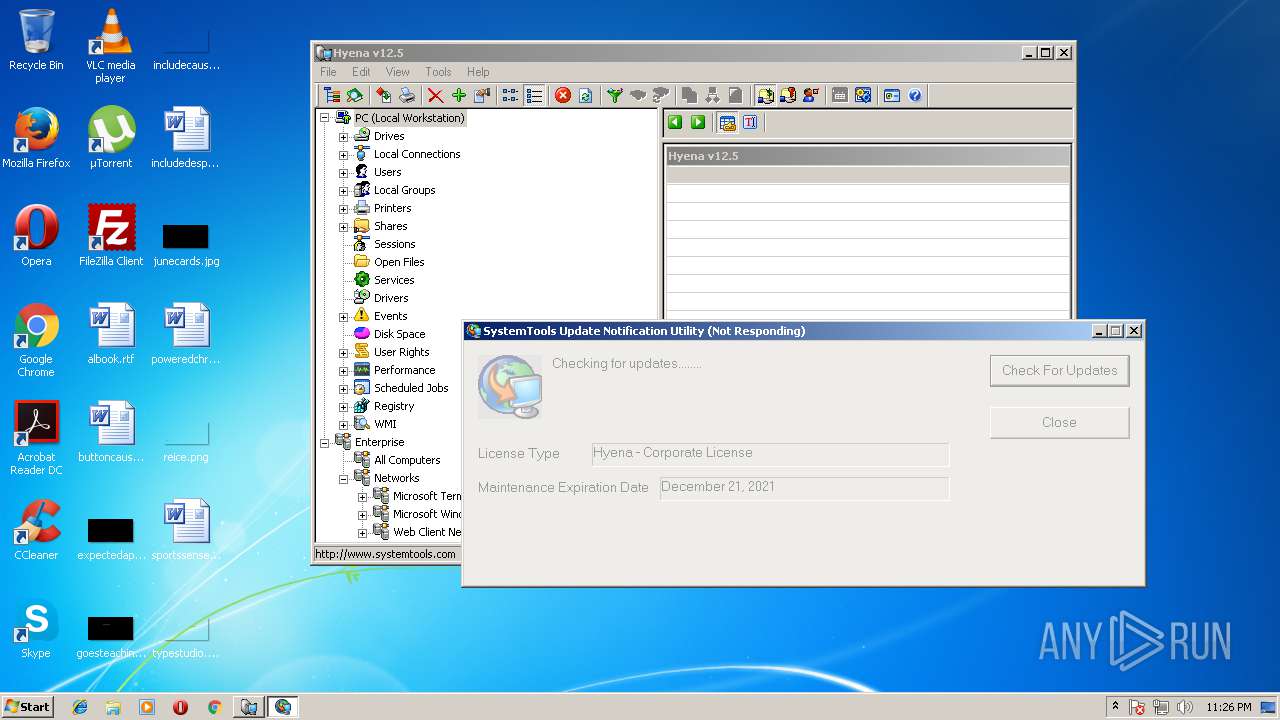
| Verdict: | Suspicious activity |
| Analysis date: | July 07, 2018, 22:24:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9B75B0640D2743C2E7998A725BAD2AAA |
| SHA1: | 6C5FD645215620632DE42B6028B2280589408EC0 |
| SHA256: | CC3795AC17A66D9496C2247F8C7925CEBCCE0EF16C55B7E62CED0C877D015D9D |
| SSDEEP: | 98304:S7b/DZ6/AobMre5KpGOymHSluOwq0APBgRdoMz9AJbGpeDJ22szVR/:S96/GrppG+SEOr0APBgj90DC3/ |
MALICIOUS
Application was dropped or rewritten from another process
- HYENA.exe (PID: 1620)
- stuc.exe (PID: 3388)
- stuc.exe (PID: 1768)
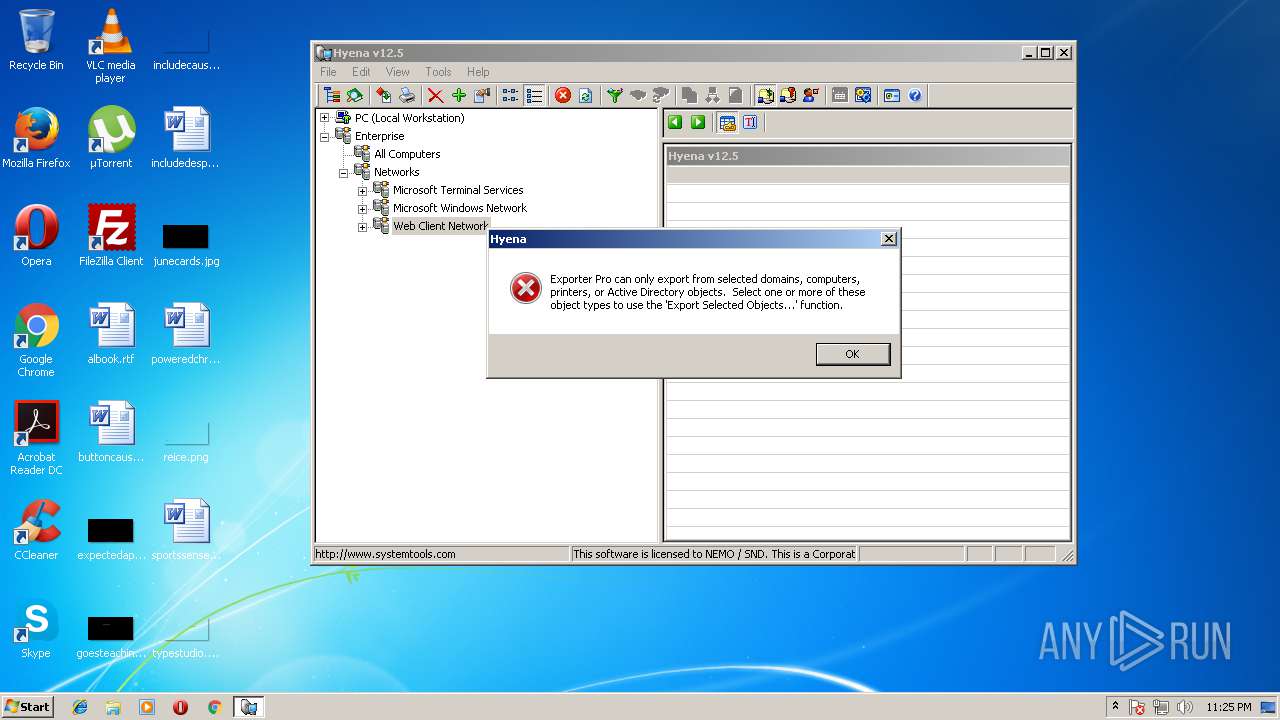
SUSPICIOUS
Executable content was dropped or overwritten
- HYENA.exe (PID: 1620)
- Hyena.exe (PID: 2200)
Starts itself from another location
- HYENA.exe (PID: 1620)
INFO
Dropped object may contain URL's
- stuc.exe (PID: 1768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.7) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.4) |
| .exe | | | DOS Executable Generic (23.4) |
| .vxd | | | VXD Driver (0.3) |
EXIF
EXE
| ThinAppVersion: | 5.2.2-4435715 |
|---|---|
| ThinAppLicense: | goodcow |
| ThinAppBuildDateTime: | 20180120 005539 |
| ProductVersion: | 12, 5, 4, 0 |
| ProductName: | HYENA |
| OriginalFileName: | HYENA.EXE |
| LegalTrademarks: | Hyena is a trademark of SystemTools Software Inc. |
| LegalCopyright: | Copyright © 1997-2017 |
| InternalName: | Hyena |
| FileVersion: | 12, 5, 4, 0 |
| FileDescription: | Hyena v12.5.4 |
| CompanyName: | SystemTools Software Inc. |
| Comments: | Windows System and Active Directory Management Software |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 12.5.4.0 |
| FileVersionNumber: | 12.5.4.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x13a6 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 184320 |
| CodeSize: | 100352 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2017:08:23 18:11:29+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Aug-2017 16:11:29 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | Windows System and Active Directory Management Software |
| CompanyName: | SystemTools Software Inc. |
| FileDescription: | Hyena v12.5.4 |
| FileVersion: | 12, 5, 4, 0 |
| InternalName: | Hyena |
| LegalCopyright: | Copyright © 1997-2017 |
| LegalTrademarks: | Hyena is a trademark of SystemTools Software Inc. |
| OriginalFilename: | HYENA.EXE |
| ProductName: | HYENA |
| ProductVersion: | 12, 5, 4, 0 |
| ThinAppBuildDateTime: | 20180120 005539 |
| ThinAppLicense: | goodcow |
| ThinAppVersion: | 5.2.2-4435715 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000050 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Aug-2017 16:11:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000186A9 | 0x00018800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56315 |
.rdata | 0x0001A000 | 0x000051F8 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17254 |
.data | 0x00020000 | 0x00027D78 | 0x00026000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.2101 |
.rsrc | 0x00048000 | 0x00001D84 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18763 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.55669 | 1188 | UNKNOWN | English - United States | RT_VERSION |
2 | 1.9815 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
3 | 6.06978 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 2.42369 | 34 | UNKNOWN | English - United Kingdom | RT_GROUP_ICON |
5 | 4.50245 | 1384 | UNKNOWN | English - United Kingdom | RT_ICON |
6 | 4.67377 | 2216 | UNKNOWN | English - United Kingdom | RT_ICON |
Imports
KERNEL32.dll |
USER32.dll |
ntdll.dll |
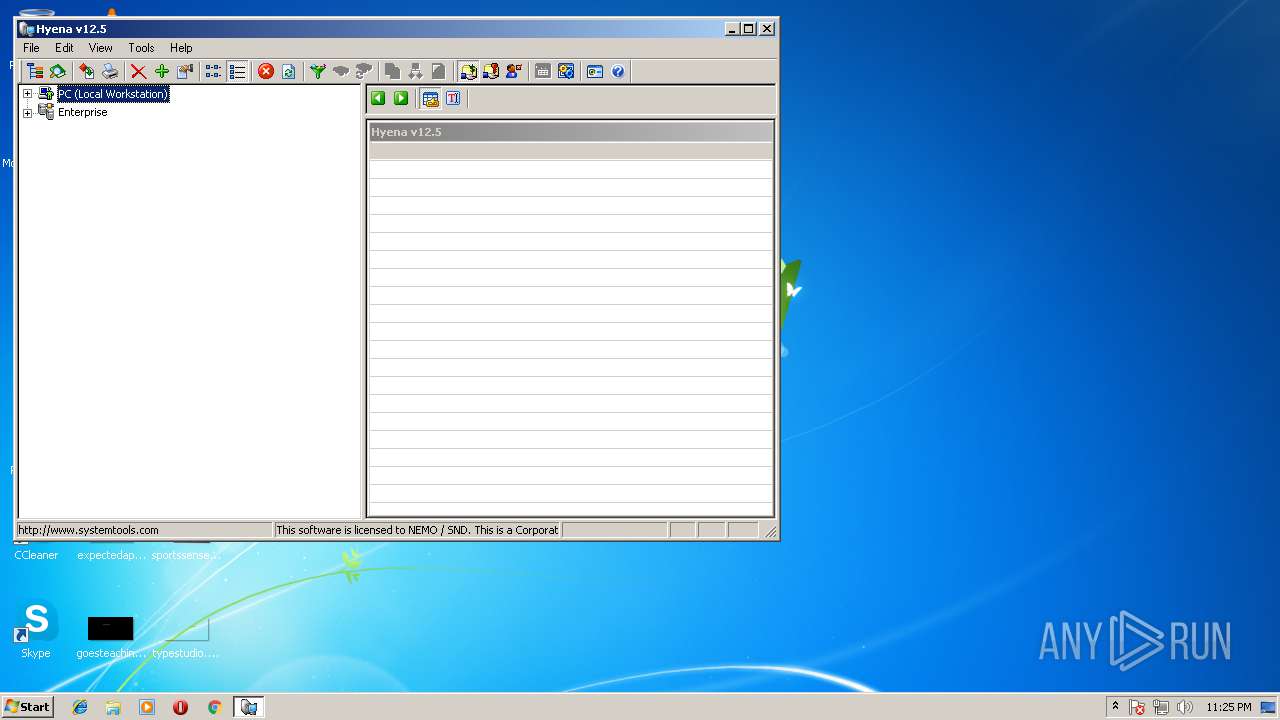
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
3
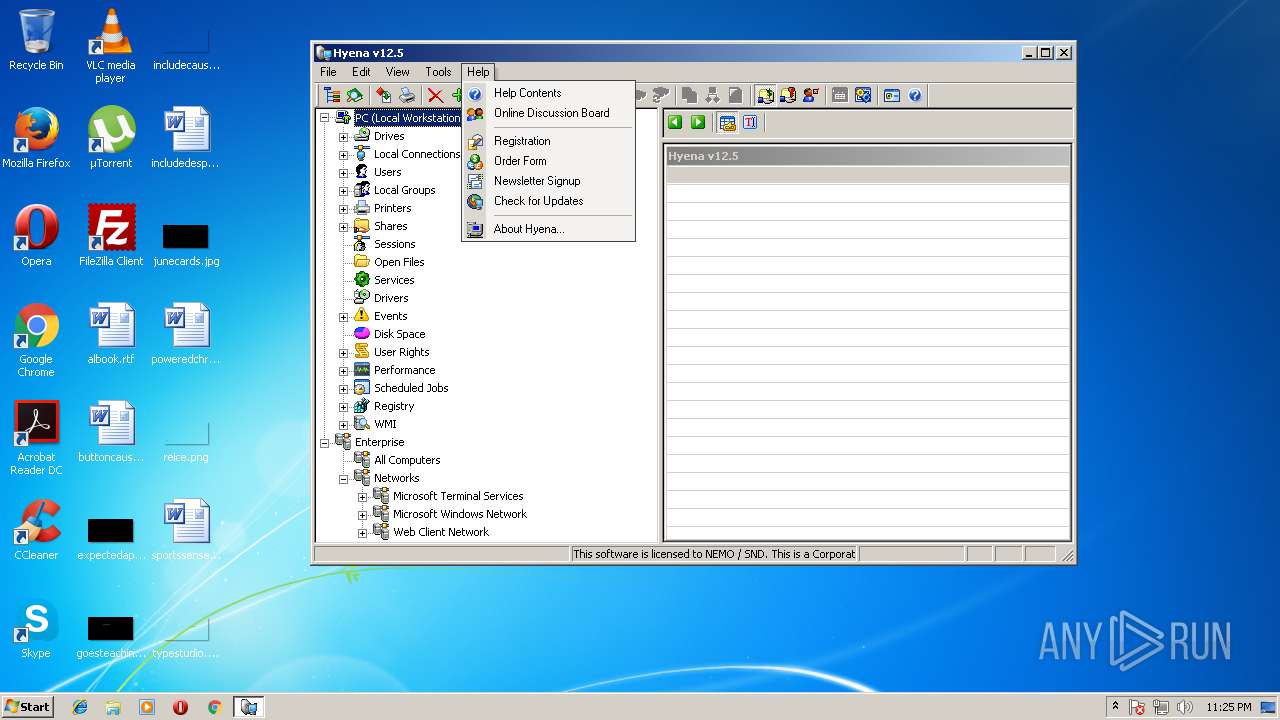
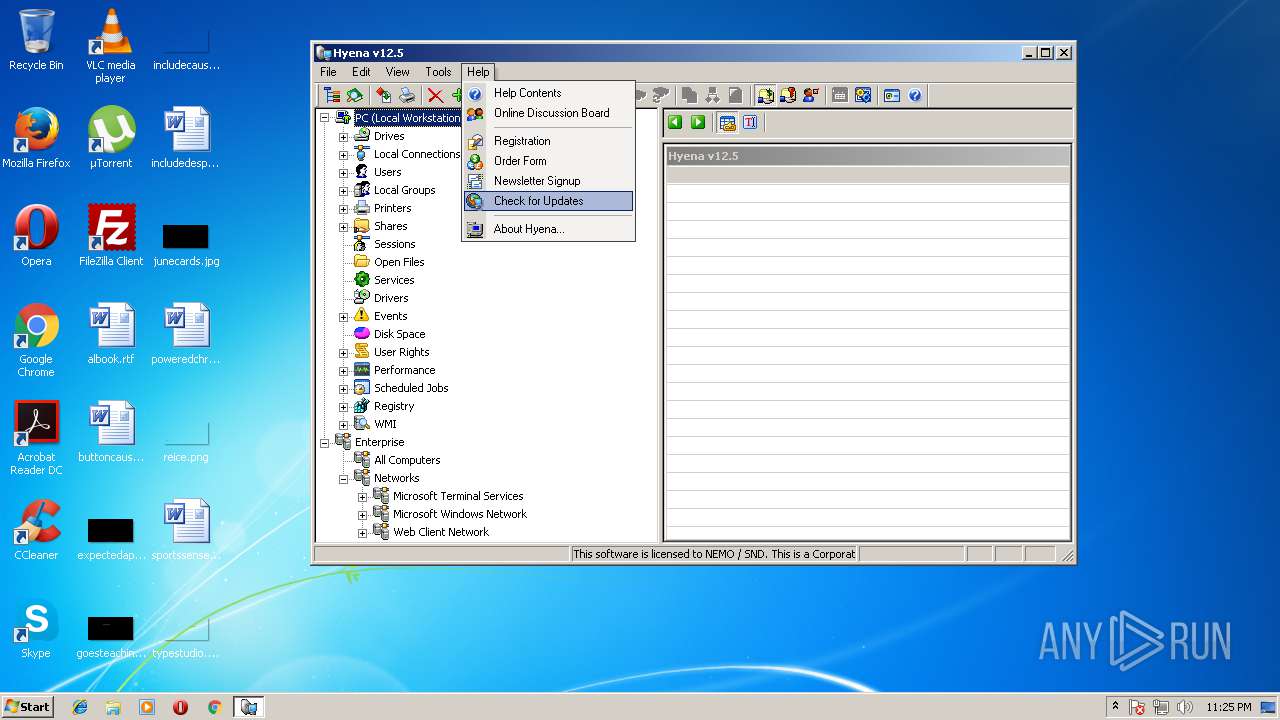
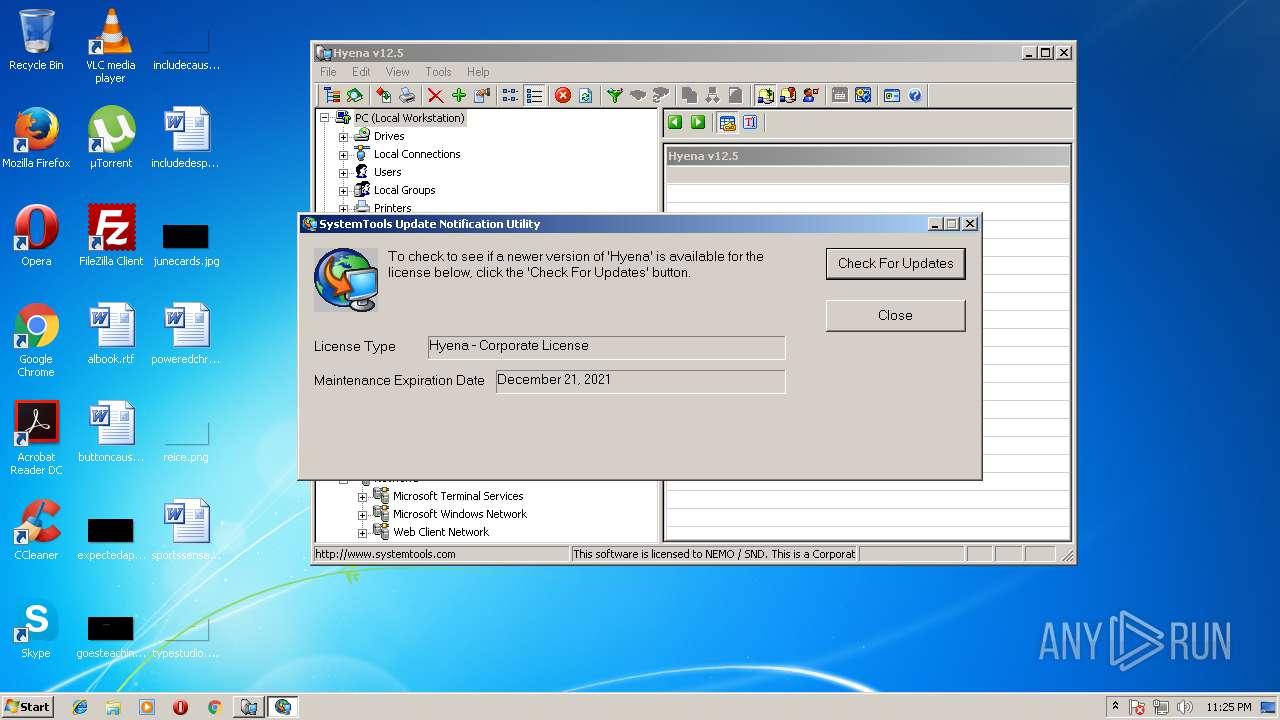
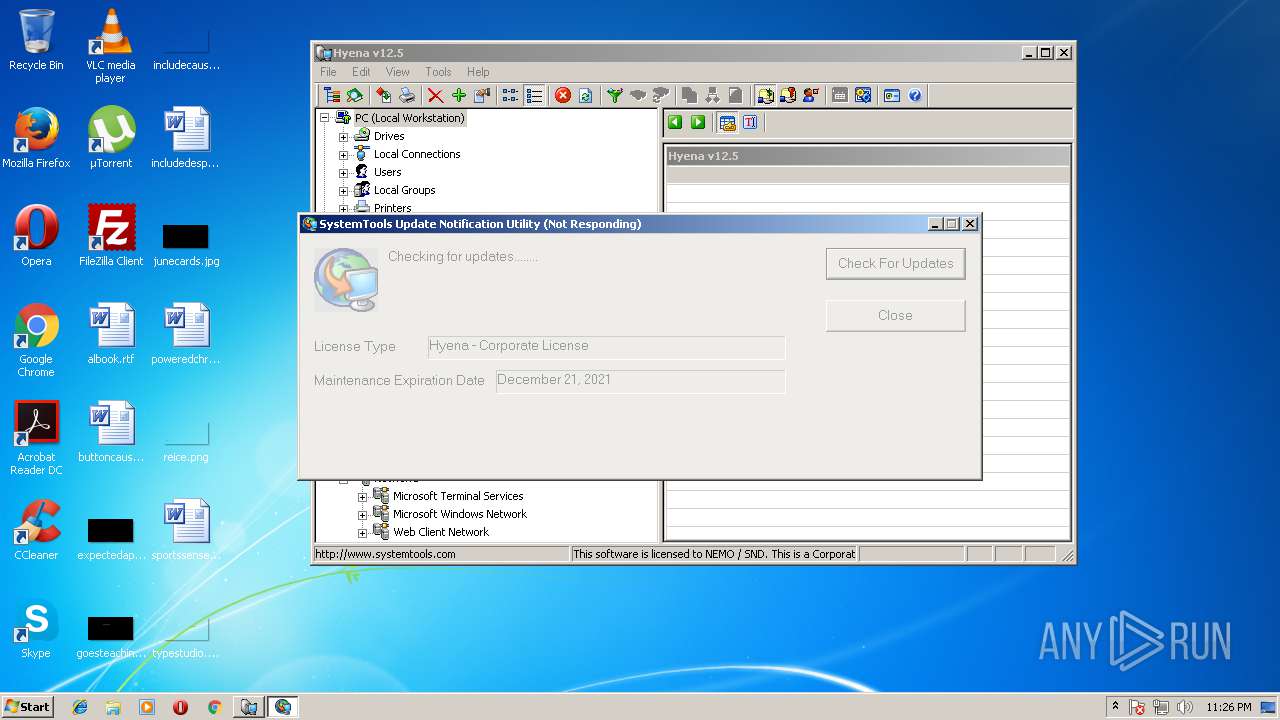
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
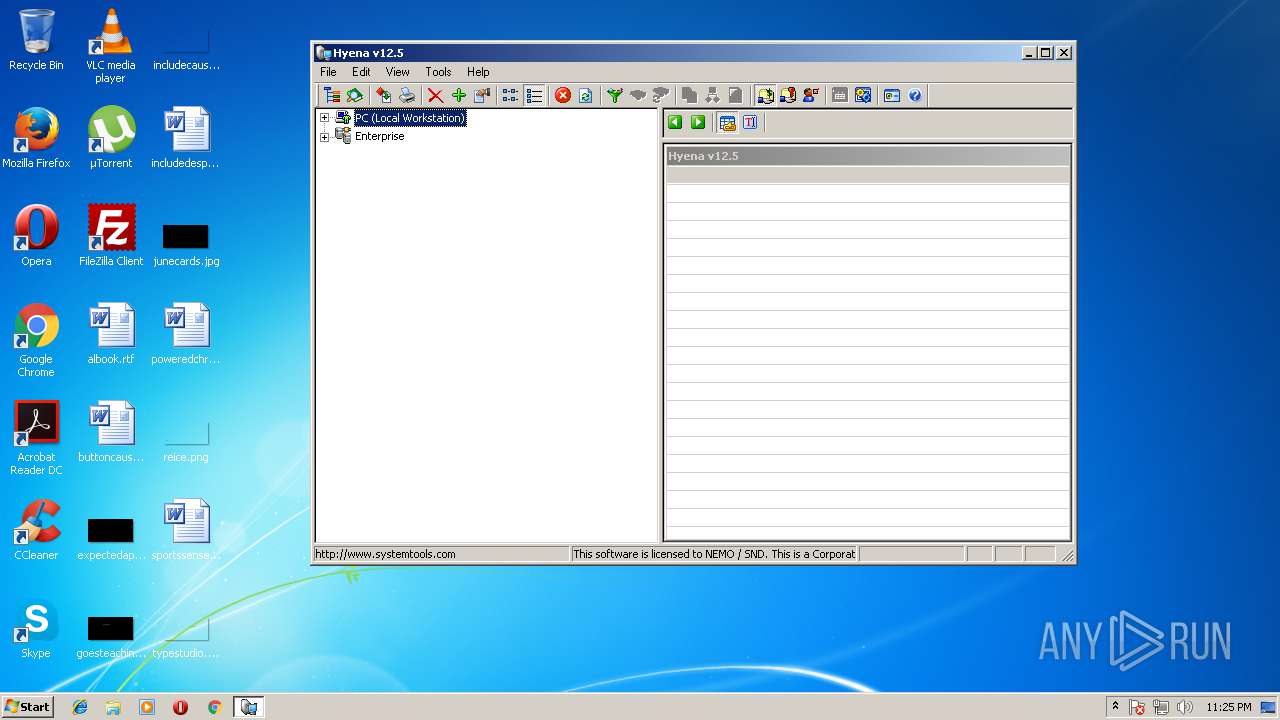
| 1620 | "C:\Program Files\Hyena\HYENA.exe" | C:\Users\admin\AppData\Local\Temp\Hyena\SKEL\4a2f59ed4995686fbf5c849bef65fbad5c31af66\HYENA.exe | Hyena.exe | ||||||||||||
User: admin Company: SystemTools Software Inc. Integrity Level: MEDIUM Description: Hyena v12.5.4 Exit code: 0 Version: 12, 5, 4, 0 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Hyena\stuc.exe" Hyena | C:\Users\admin\AppData\Local\Temp\Hyena\SKEL\4a2f59ed4995686fbf5c849bef65fbad5c31af66\stuc.exe | HYENA.exe | ||||||||||||
User: admin Company: SystemTools Software Inc. Integrity Level: MEDIUM Description: Hyena v12.5.4 Exit code: 0 Version: 12, 5, 4, 0 Modules
| |||||||||||||||
| 2200 | "C:\Users\admin\AppData\Local\Temp\Hyena.exe" | C:\Users\admin\AppData\Local\Temp\Hyena.exe | explorer.exe | ||||||||||||
User: admin Company: SystemTools Software Inc. Integrity Level: MEDIUM Description: Hyena v12.5.4 Exit code: 0 Version: 12, 5, 4, 0 Modules
| |||||||||||||||
| 3388 | "C:\Program Files\Hyena\stuc.exe" Hyena | C:\Users\admin\AppData\Local\Temp\Hyena\SKEL\4a2f59ed4995686fbf5c849bef65fbad5c31af66\stuc.exe | HYENA.exe | ||||||||||||
User: admin Company: SystemTools Software Inc. Integrity Level: MEDIUM Description: Hyena v12.5.4 Exit code: 0 Version: 12, 5, 4, 0 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
4
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2200 | Hyena.exe | C:\Users\admin\AppData\Local\Temp\Hyena\Registry.rw.tvr.lck.PC.ffffffff.a80 | — | |
MD5:— | SHA256:— | |||
| 2200 | Hyena.exe | C:\Users\admin\AppData\Local\Temp\Hyena\SKEL\4a2f59ed4995686fbf5c849bef65fbad5c31af66\HYENA.exe.a80.898 | — | |
MD5:— | SHA256:— | |||
| 1620 | HYENA.exe | C:\Users\admin\AppData\Local\Temp\Hyena\SKEL\4a2f59ed4995686fbf5c849bef65fbad5c31af66\stuc.exe.400.654 | — | |
MD5:— | SHA256:— | |||
| 1768 | stuc.exe | C:\Users\admin\AppData\Local\Temp\Cabc2b5.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | stuc.exe | C:\Users\admin\AppData\Local\Temp\Tarc2b6.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | stuc.exe | C:\Users\admin\AppData\Local\Temp\Cabc305.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | stuc.exe | C:\Users\admin\AppData\Local\Temp\Tarc306.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | stuc.exe | C:\Users\admin\AppData\Local\Temp\Cabc3d2.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | stuc.exe | C:\Users\admin\AppData\Local\Temp\Tarc3d3.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | stuc.exe | C:\Users\admin\AppData\Local\Temp\Cabc441.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
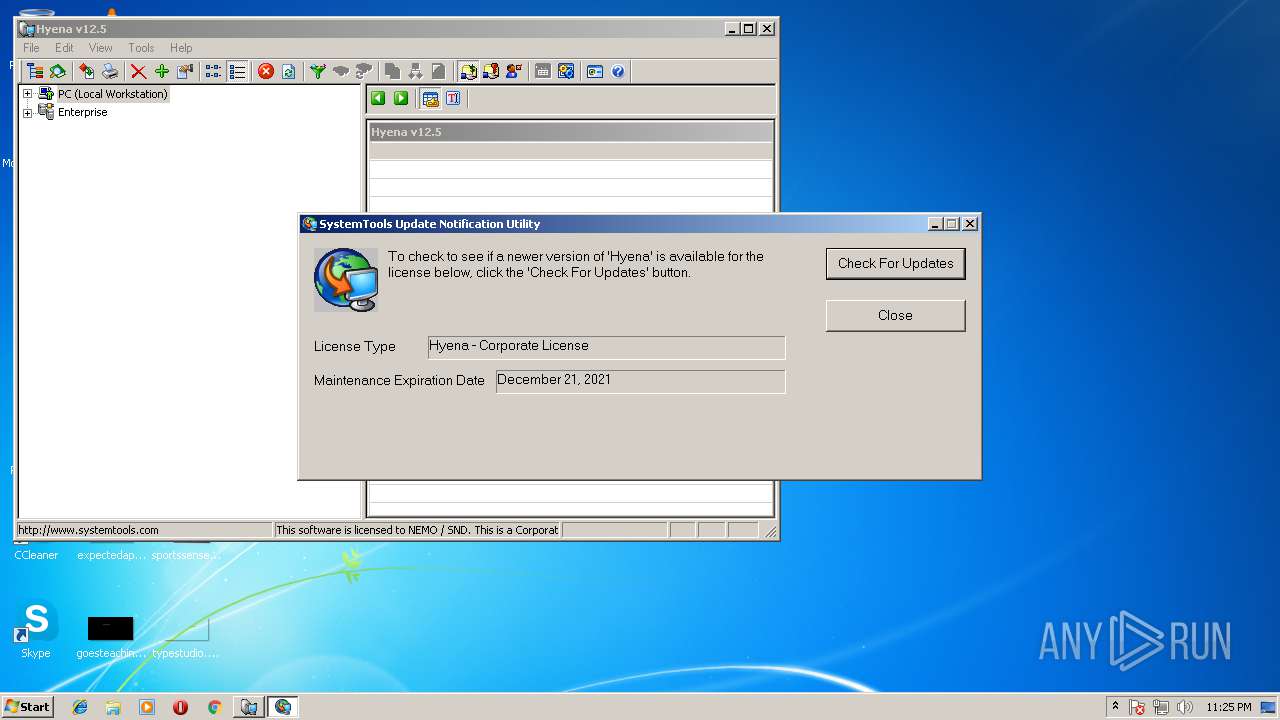
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1768 | stuc.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
1768 | stuc.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
1768 | stuc.exe | GET | 301 | 166.78.147.244:80 | http://www.systemtools.com/hyena.dat | US | html | 245 b | unknown |
3388 | stuc.exe | GET | 301 | 166.78.147.244:80 | http://www.systemtools.com/hyena.dat | US | html | 245 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1768 | stuc.exe | 166.78.147.244:80 | www.systemtools.com | Rackspace Ltd. | US | unknown |
1768 | stuc.exe | 166.78.147.244:443 | www.systemtools.com | Rackspace Ltd. | US | unknown |
1768 | stuc.exe | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1768 | stuc.exe | 166.78.147.244:21 | www.systemtools.com | Rackspace Ltd. | US | unknown |
3388 | stuc.exe | 166.78.147.244:80 | www.systemtools.com | Rackspace Ltd. | US | unknown |
3388 | stuc.exe | 166.78.147.244:443 | www.systemtools.com | Rackspace Ltd. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.systemtools.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Hyena.exe | <?dml?>#1 p=2200/898h t=2688/A80h: <link cmd=".reload /f boot_loader.exe=0x66200000">Reload</link> <b>boot_loader.exe</b> 0x66200000
|
Hyena.exe | <?dml?>#2 p=2200/898h t=2688/A80h: Loading packaged nt0_dll.dll...
|
Hyena.exe | <?dml?>#3 p=2200/898h t=2688/A80h: <link cmd=".reload /f nt0_dll.dll=0x7FDD0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDD0000 packaged
|
Hyena.exe | <?dml?>#1 p=2200/898h t=2688/A80h: <link cmd=".reload /f nt0_dll.dll=0x7FDC0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDC0000 <b>mapped to pid=1620/654h</b>
|
HYENA.exe | <?dml?>#1 p=1620/654h t=1024/400h: <link cmd=".reload /f nt0_dll.dll=0x7FDC0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDC0000 <b>mapped to pid=1768/6E8h</b>
|
HYENA.exe | <?dml?>#2 p=1620/654h t=1024/400h: <link cmd=".reload /f nt0_dll.dll=0x7FDC0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDC0000 <b>mapped to pid=3388/D3Ch</b>
|