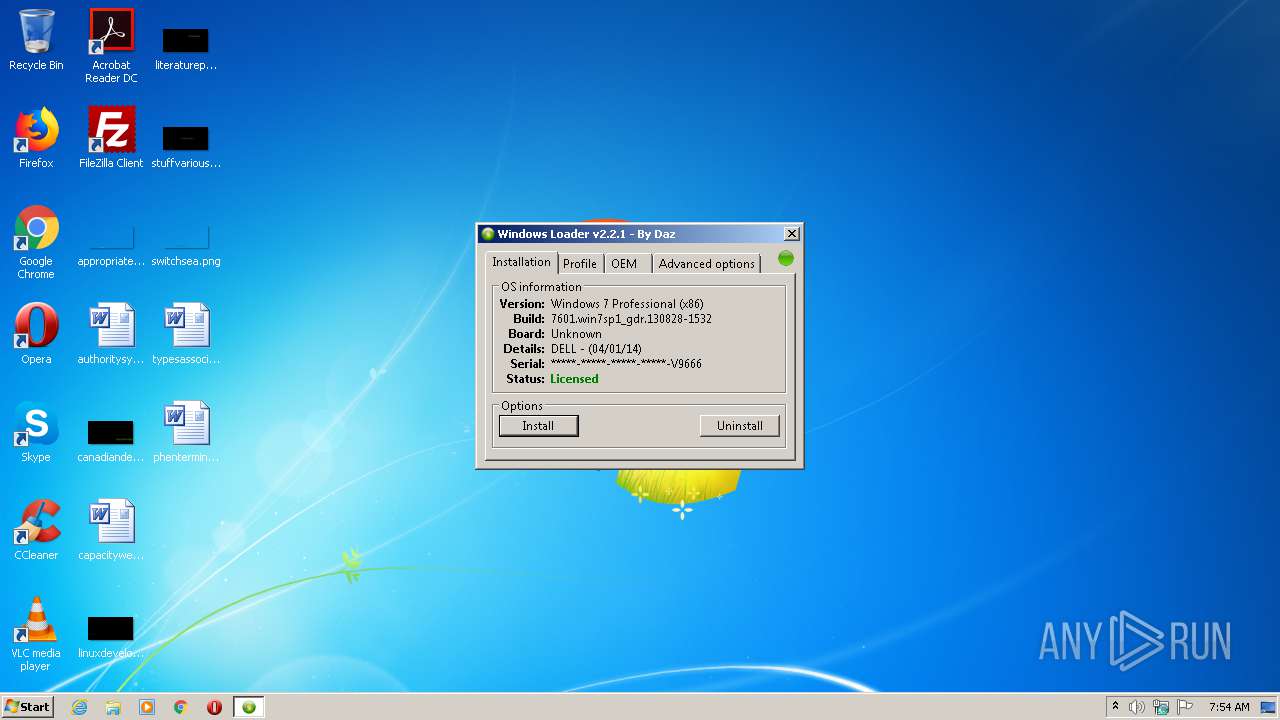
| File name: | Windows 7 Loader.exe |
| Full analysis: | https://app.any.run/tasks/6af7dbe6-27c6-44ba-a116-56fdd61f86bf |
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2020, 06:53:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | C219FDB4E5C327D16913D78D844AA1AB |
| SHA1: | D163E1F1628DDF223E8CE69756B110192FC7FF3A |
| SHA256: | CC30186F3768FB29155BFE7DE70A3B296AFC863511DF36EFBFB0B1DB3D64D962 |
| SSDEEP: | 49152:8E1duz5d0vRoLV3fVVF3SDkd8L2yydVX1WljTt5Xm:Itd+RodtuDkWyd11Wlq |
MALICIOUS
Application was dropped or rewritten from another process
- Windows 7 Loader.exe (PID: 3552)
- Windows 7 Loader.exe (PID: 2588)
- taskmg.exe (PID: 3192)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 3352)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3932)
SUSPICIOUS
Executable content was dropped or overwritten
- Windows 7 Loader.exe (PID: 3884)
Executed via COM
- explorer.exe (PID: 2344)
Creates files in the user directory
- Windows 7 Loader.exe (PID: 3884)
Starts CMD.EXE for commands execution
- taskmg.exe (PID: 3192)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:15 23:23:42+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 2940928 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | 4481024 |
| EntryPoint: | 0x714780 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.1.1.1 |
| ProductVersionNumber: | 0.1.1.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
| FileVersion: | - |
| FileDescription: | Windows 7 Loader Installation |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Windows 7 Loader Installation |
| ProductVersion: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Aug-2017 21:23:42 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | - |
| FileVersion: | - |
| FileDescription: | Windows 7 Loader Installation |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | Windows 7 Loader Installation |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Aug-2017 21:23:42 |
| Pointer to Symbol Table: | 0x0070B400 |
| Number of symbols: | 5368 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00446000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00447000 | 0x002CE000 | 0x002CDA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.79462 |
.rsrc | 0x00715000 | 0x00005000 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.60159 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.12852 | 688 | UNKNOWN | English - United States | RT_VERSION |
2 | 5.93962 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.503 | 9640 | UNKNOWN | English - United States | RT_ICON |
A | 2.45849 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.DLL |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
50
Monitored processes
10
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2344 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | "C:\Users\admin\AppData\Roaming\WindowsLoader\Windows 7 Loader.exe" | C:\Users\admin\AppData\Roaming\WindowsLoader\Windows 7 Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3192 | "C:\Users\admin\AppData\Roaming\taskmg.exe" | C:\Users\admin\AppData\Roaming\taskmg.exe | — | Windows 7 Loader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3216 | "C:\Users\admin\AppData\Local\Temp\Windows 7 Loader.exe" | C:\Users\admin\AppData\Local\Temp\Windows 7 Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 7 Loader Installation Exit code: 3221226540 Modules
| |||||||||||||||
| 3352 | "C:\Windows\System32\cmd.exe" /c schtasks /create /sc onlogon /f /tn "UpdateChecker" /tr "C:\Users\admin\AppData\Roaming\taskmg.exe" | C:\Windows\System32\cmd.exe | taskmg.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3468 | "C:\Windows\explorer.exe" C:\Users\admin\AppData\Roaming\WindowsLoader\Windows 7 Loader.exe | C:\Windows\explorer.exe | — | Windows 7 Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3552 | "C:\Users\admin\AppData\Roaming\WindowsLoader\Windows 7 Loader.exe" | C:\Users\admin\AppData\Roaming\WindowsLoader\Windows 7 Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3668 | "C:\Windows\System32\cmd.exe" /c del /S /Q "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent" | C:\Windows\System32\cmd.exe | — | taskmg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3884 | "C:\Users\admin\AppData\Local\Temp\Windows 7 Loader.exe" | C:\Users\admin\AppData\Local\Temp\Windows 7 Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Windows 7 Loader Installation Exit code: 0 Modules
| |||||||||||||||
| 3932 | schtasks /create /sc onlogon /f /tn "UpdateChecker" /tr "C:\Users\admin\AppData\Roaming\taskmg.exe" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
556
Read events
542
Write events
14
Delete events
0
Modification events
| (PID) Process: | (3884) Windows 7 Loader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3884) Windows 7 Loader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2344) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2344) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3192) taskmg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3192) taskmg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3884 | Windows 7 Loader.exe | C:\Users\admin\AppData\Roaming\taskmg.exe | executable | |
MD5:6A64C60E4F98E35B74676D0844D23AC3 | SHA256:CE08048FA45E9CB8C3A799712EC5A235C05AB70251AE9996C53734B39370BDE3 | |||
| 3192 | taskmg.exe | C:\Users\admin\AppData\Local\Temp\build.conf | text | |
MD5:— | SHA256:— | |||
| 3884 | Windows 7 Loader.exe | C:\Users\admin\AppData\Roaming\WindowsLoader\Windows 7 Loader.exe | executable | |
MD5:3976BD5FCBB7CD13F0C12BB69AFC2ADC | SHA256:BF5070EF8CF03A11D25460B3E09A479183CC0FA03D0EA32E4499998F509B1A40 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
frontescent.pw |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |