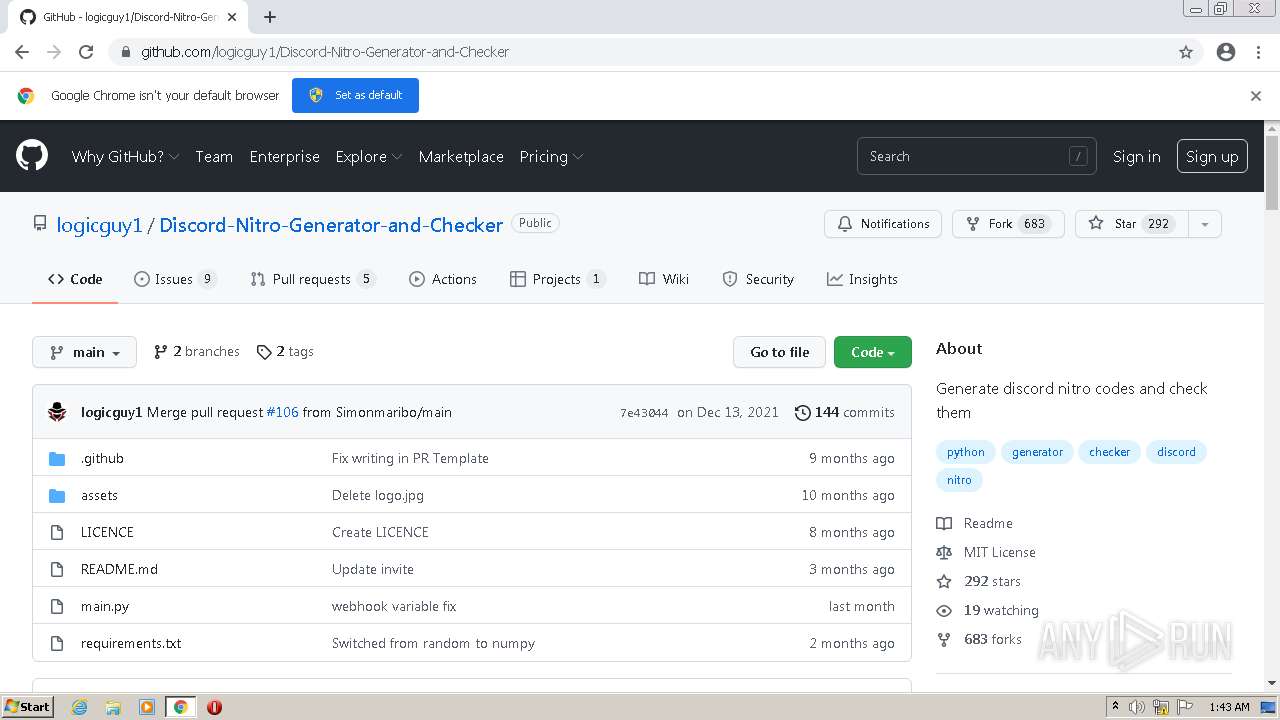
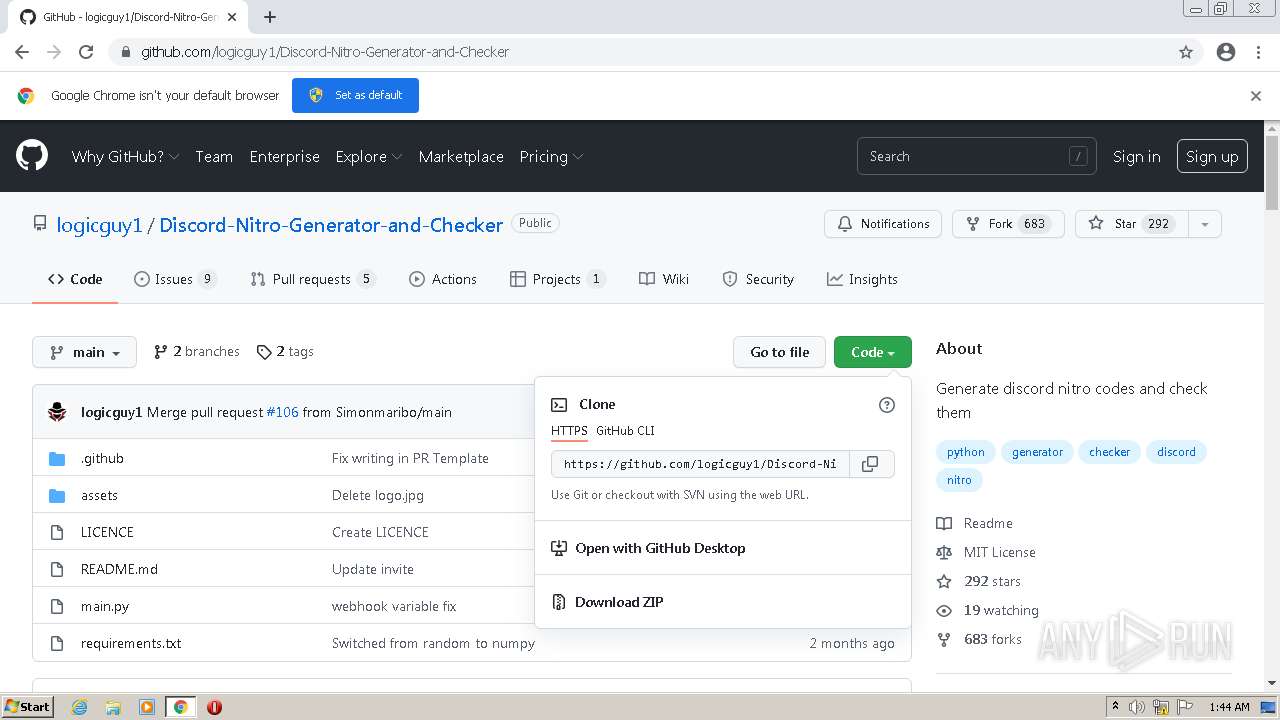
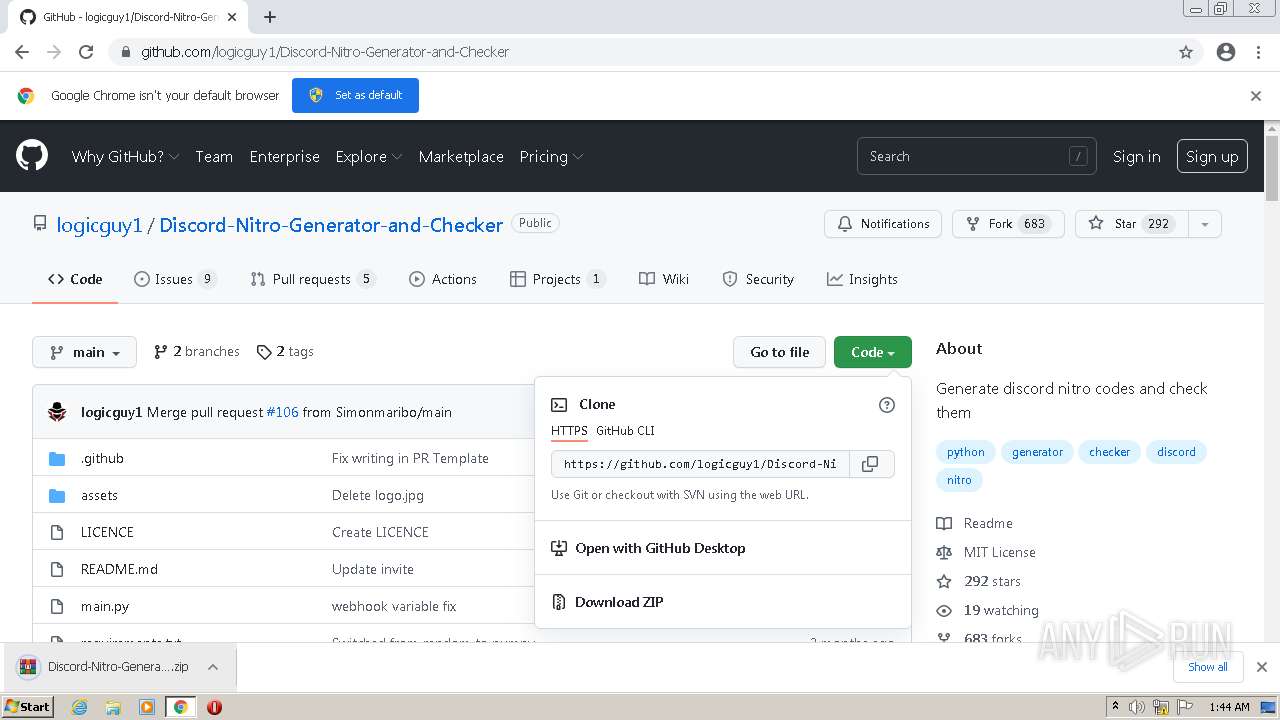
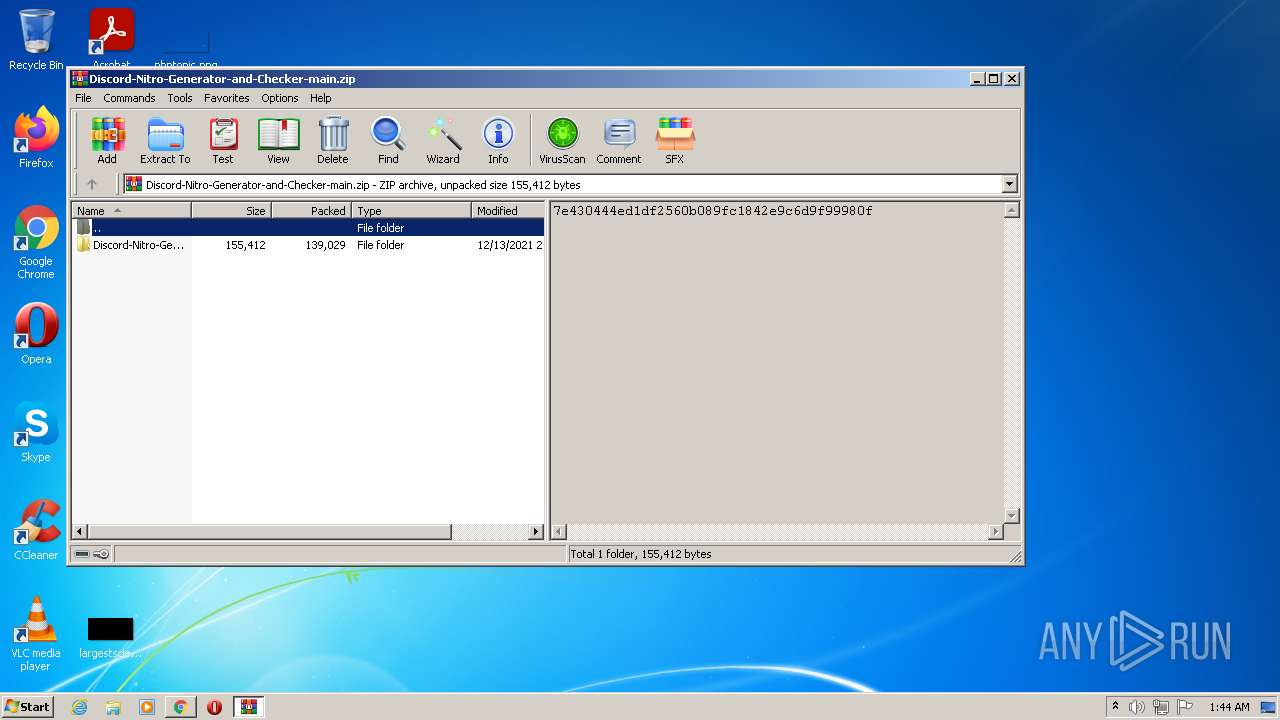
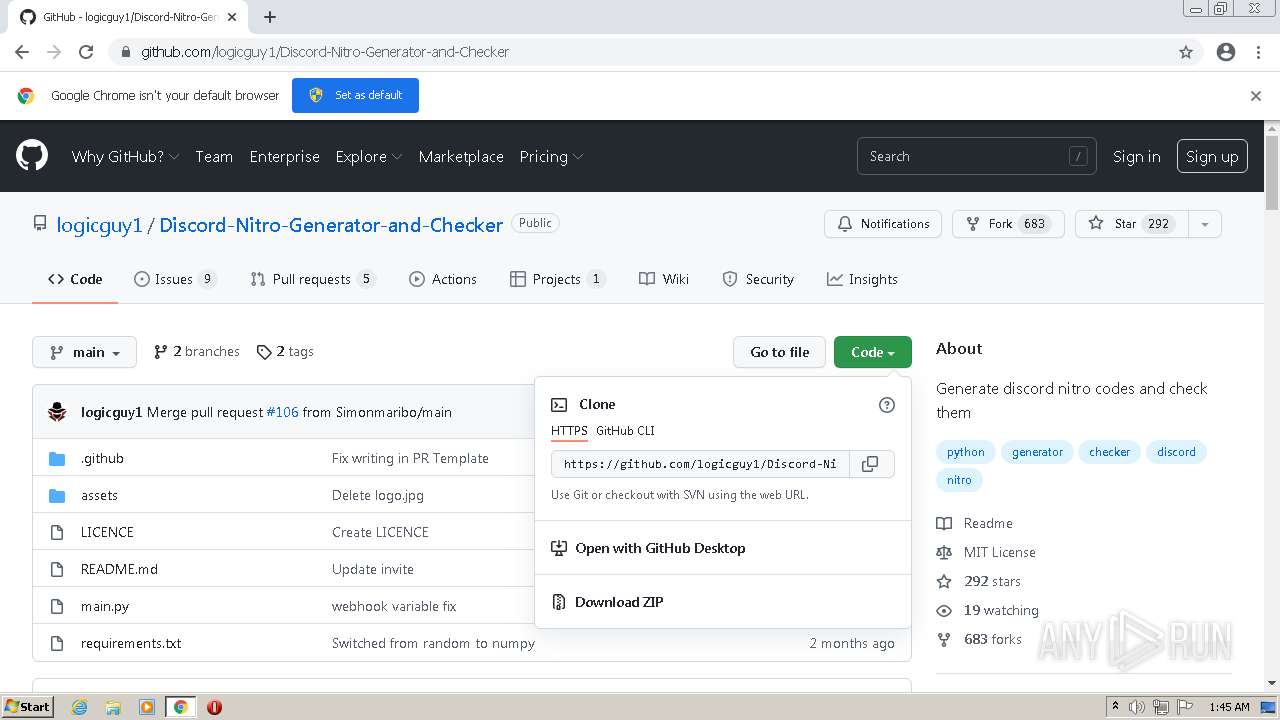
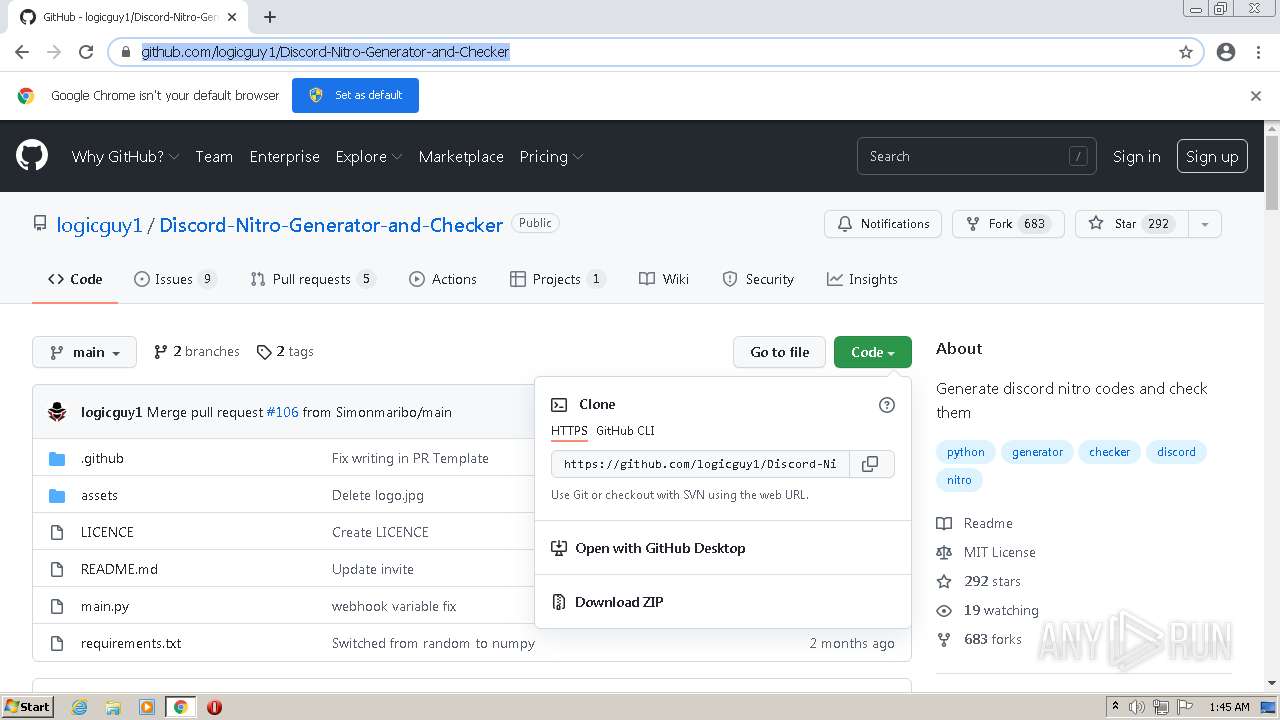
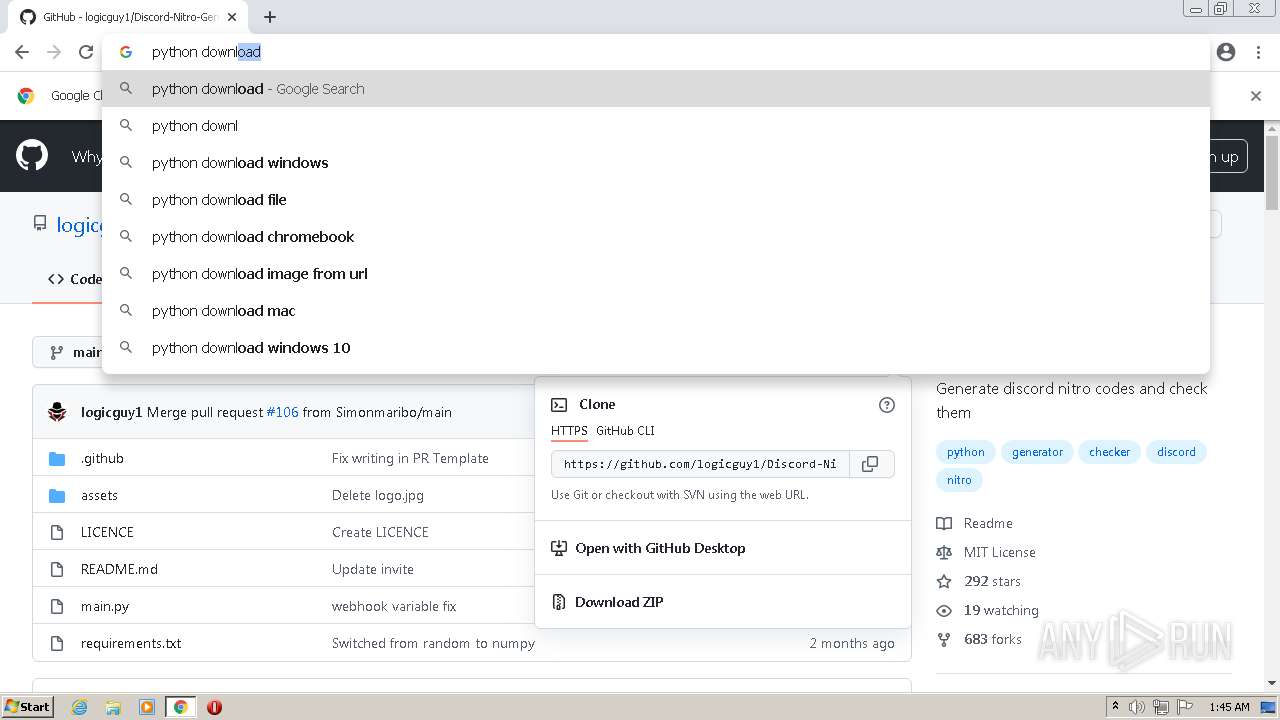
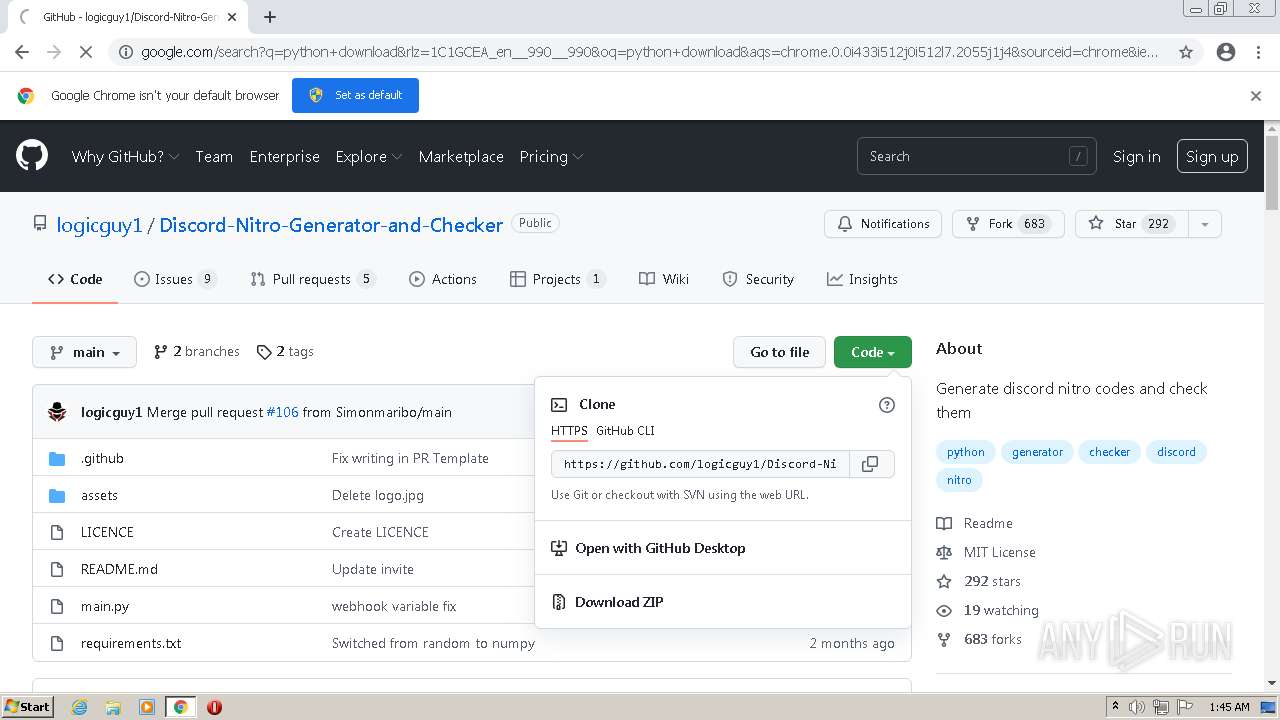
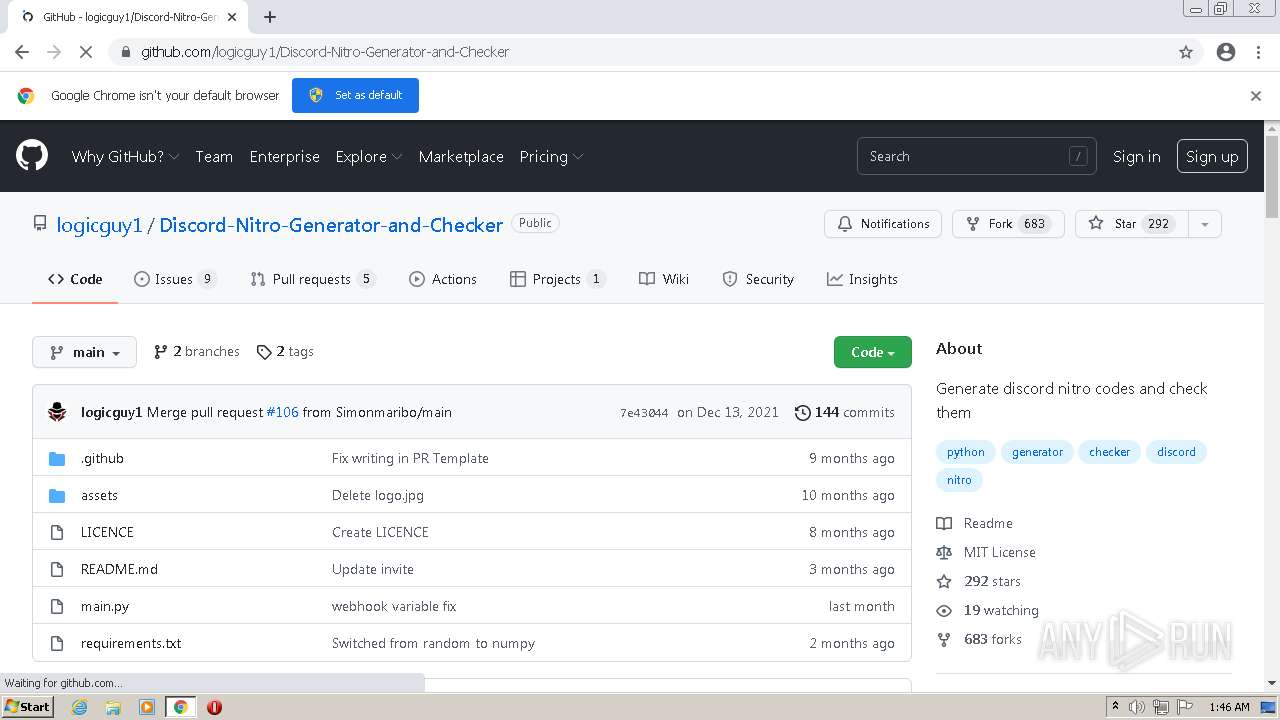
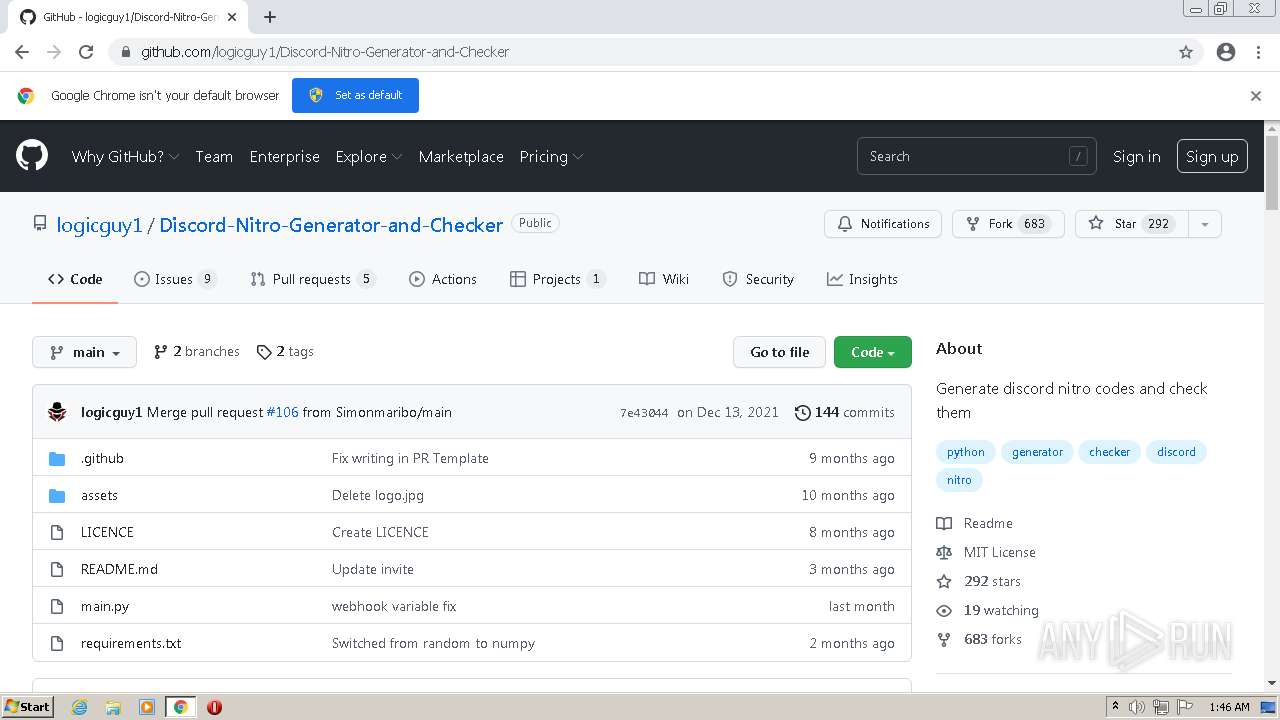
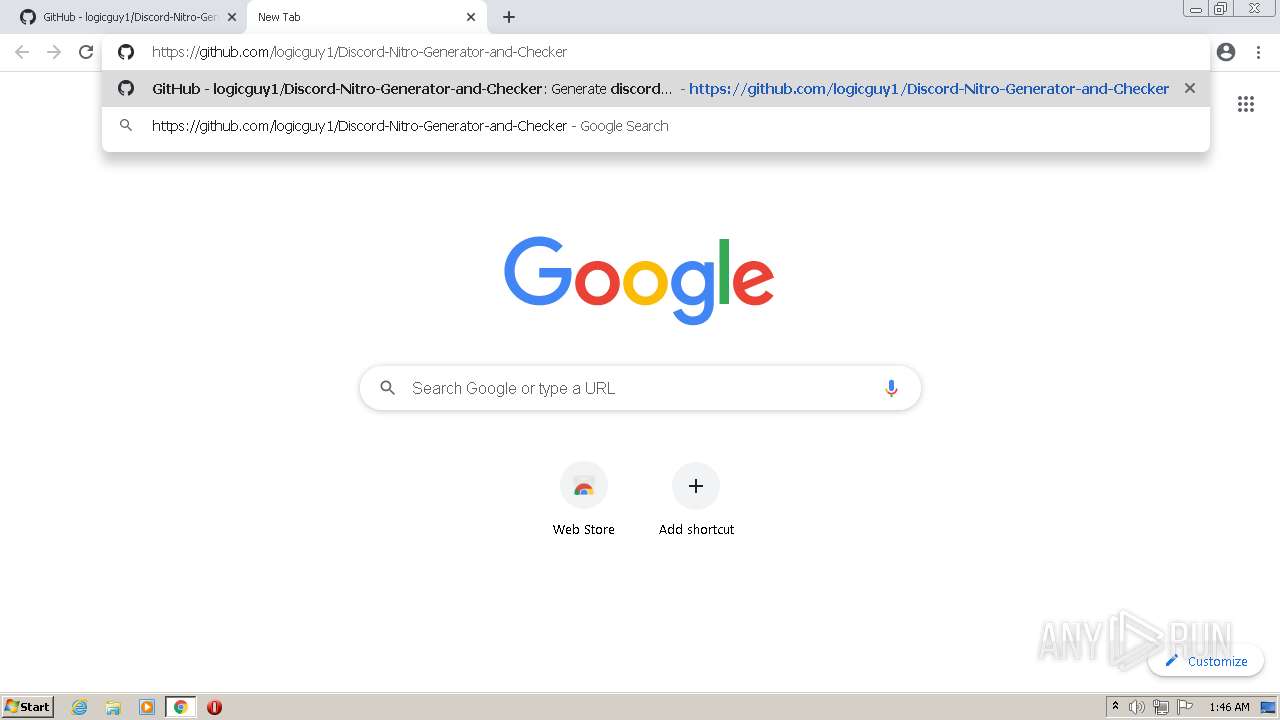
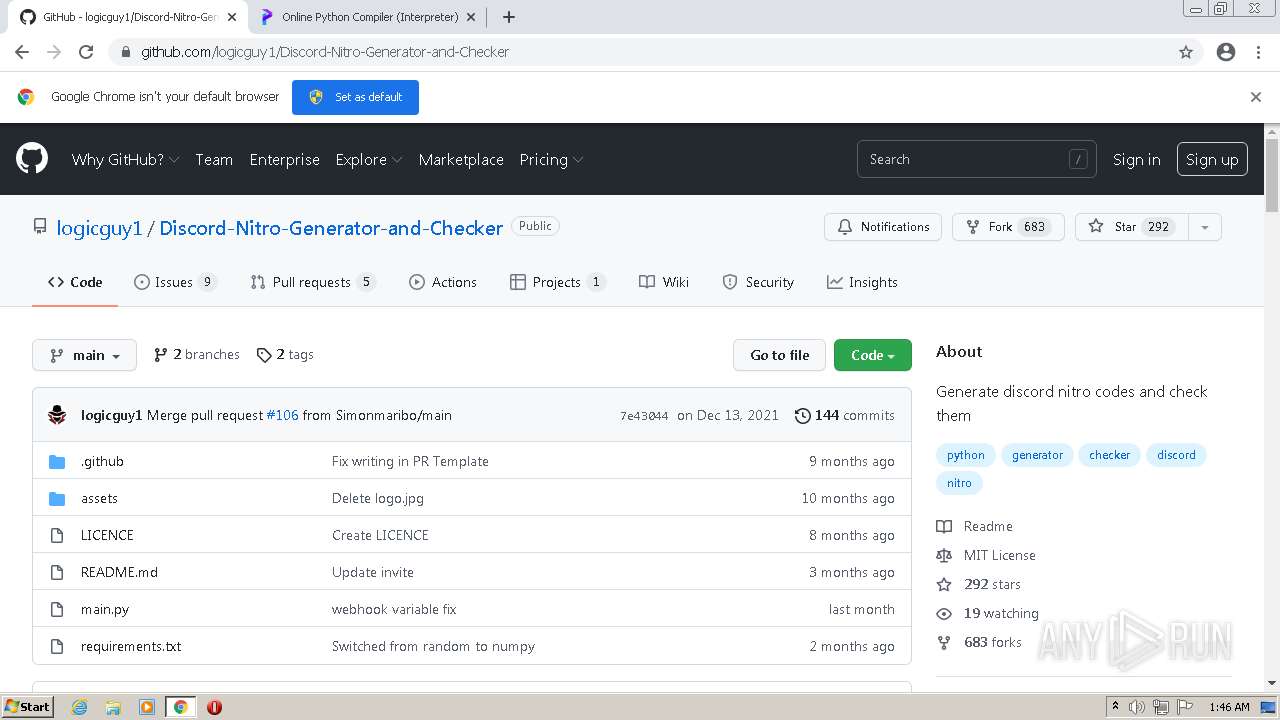
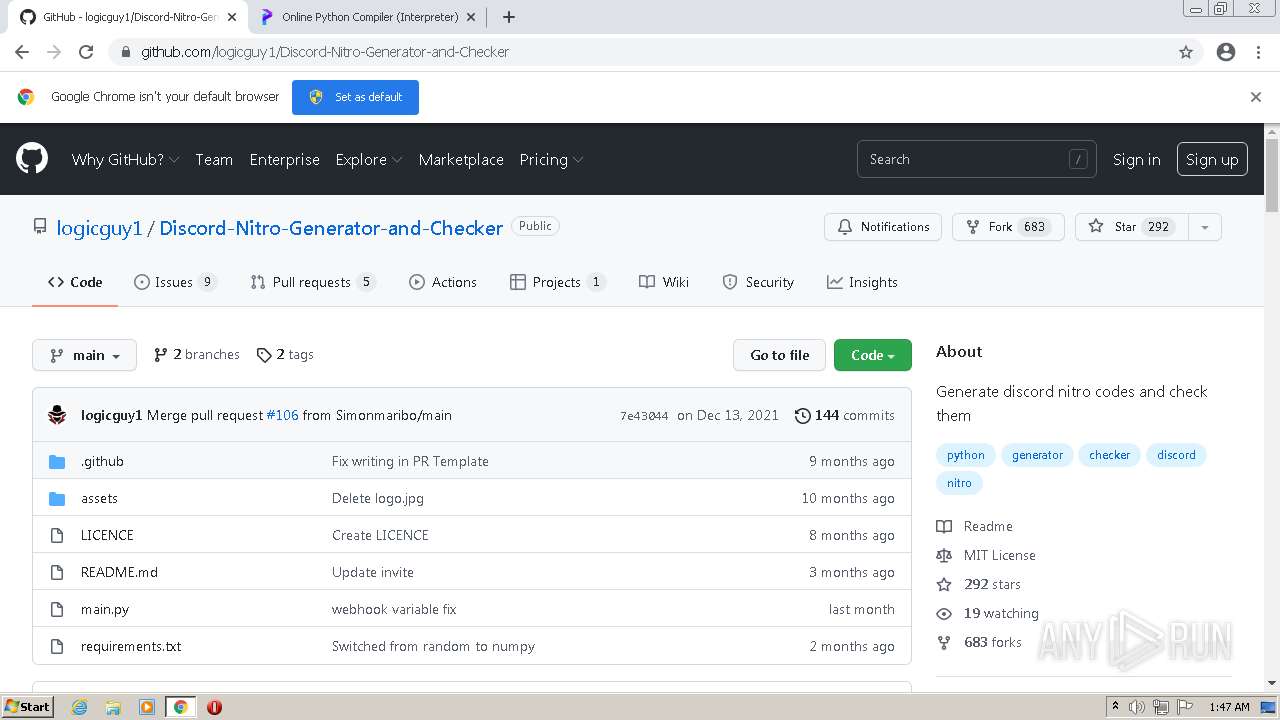
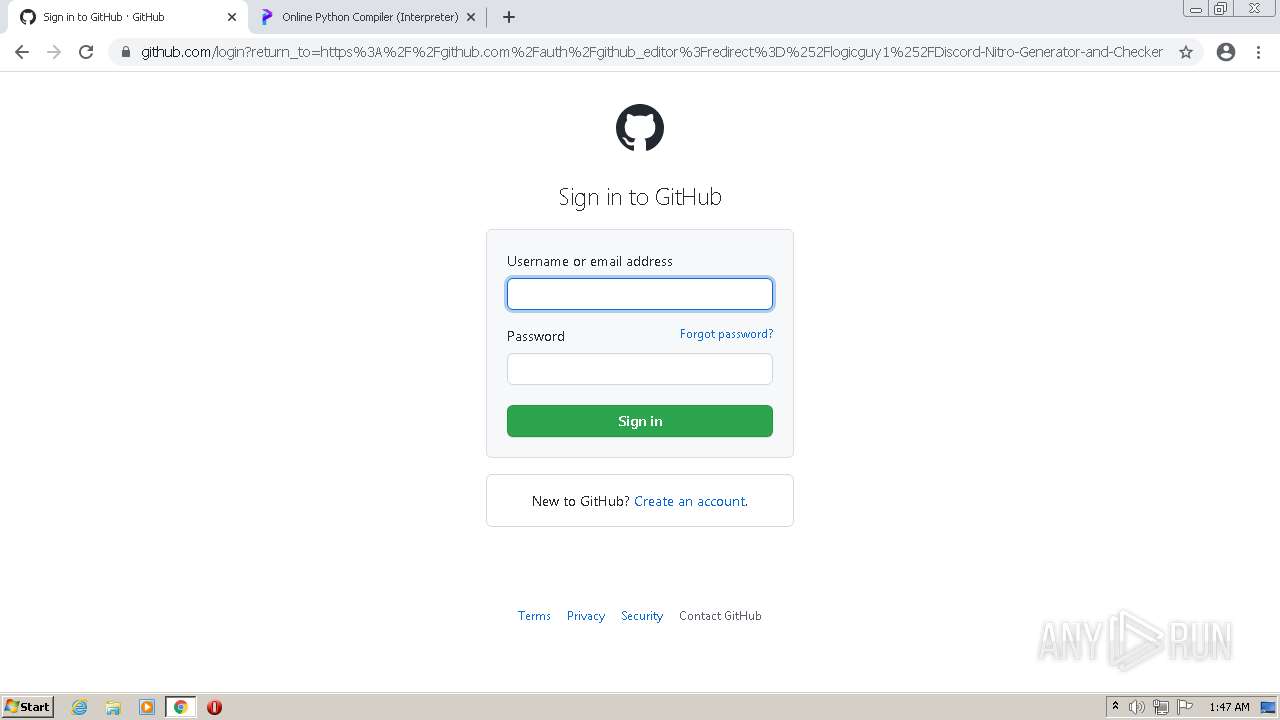
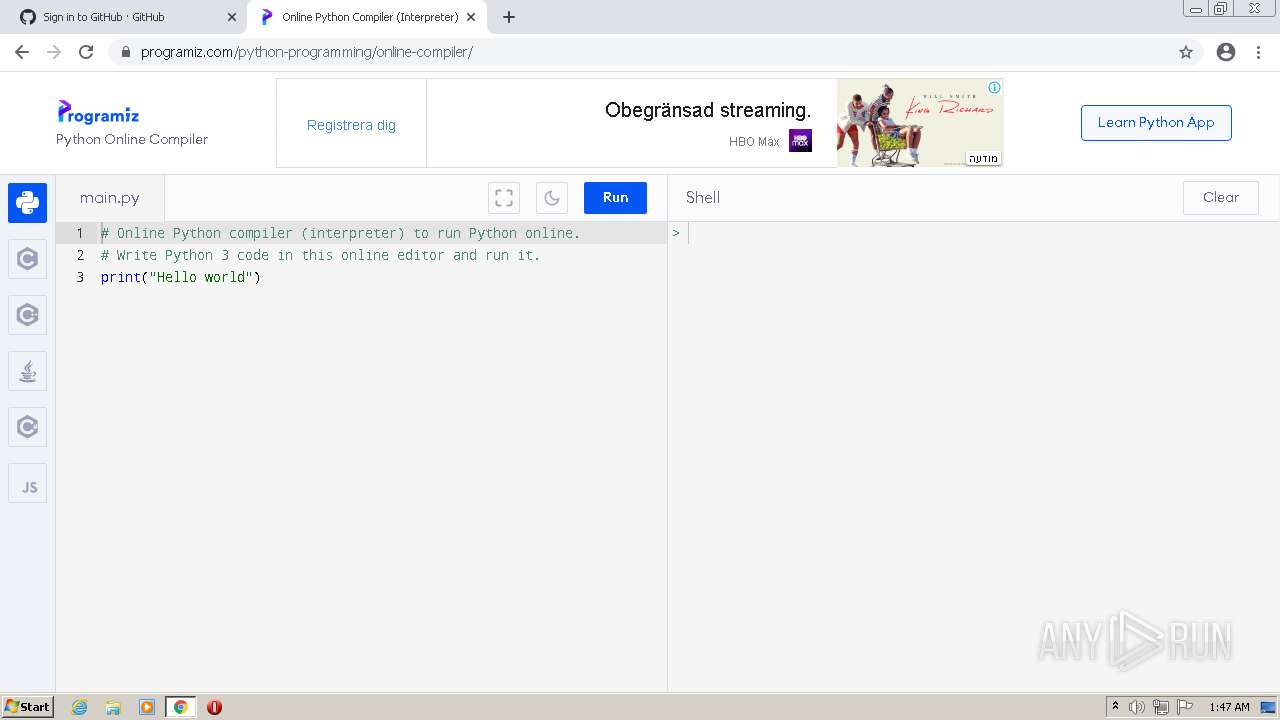
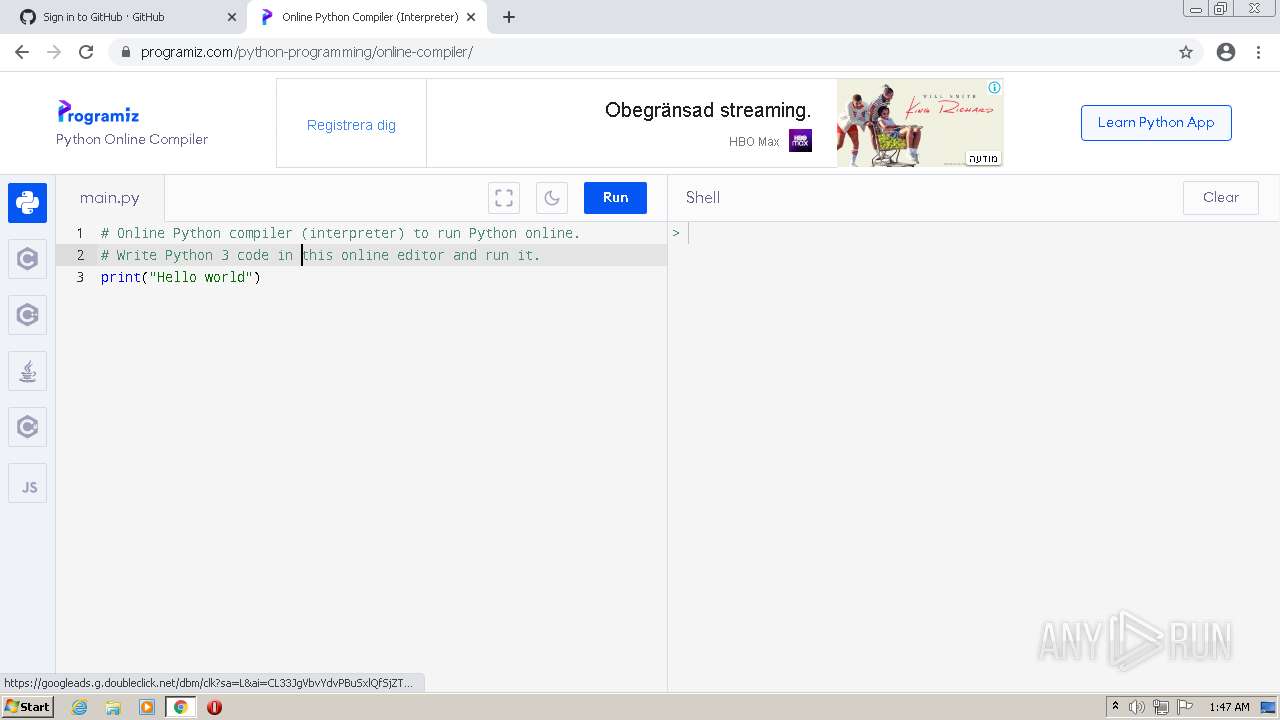
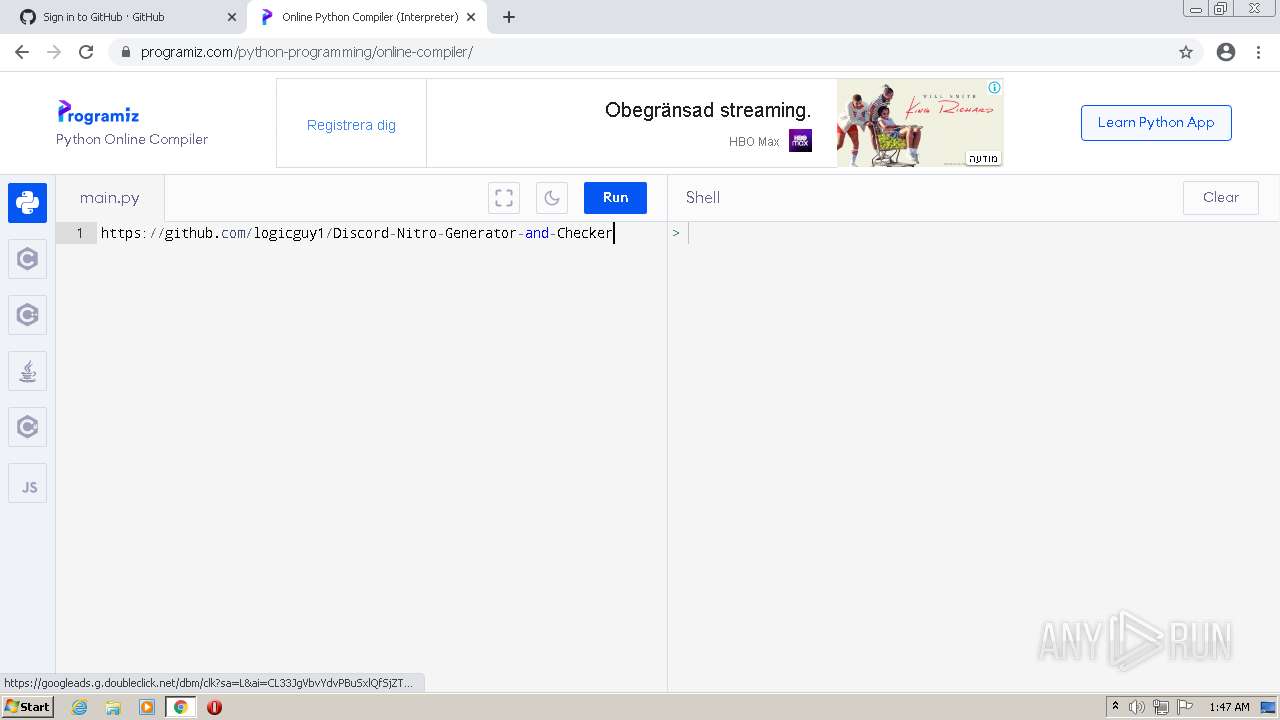
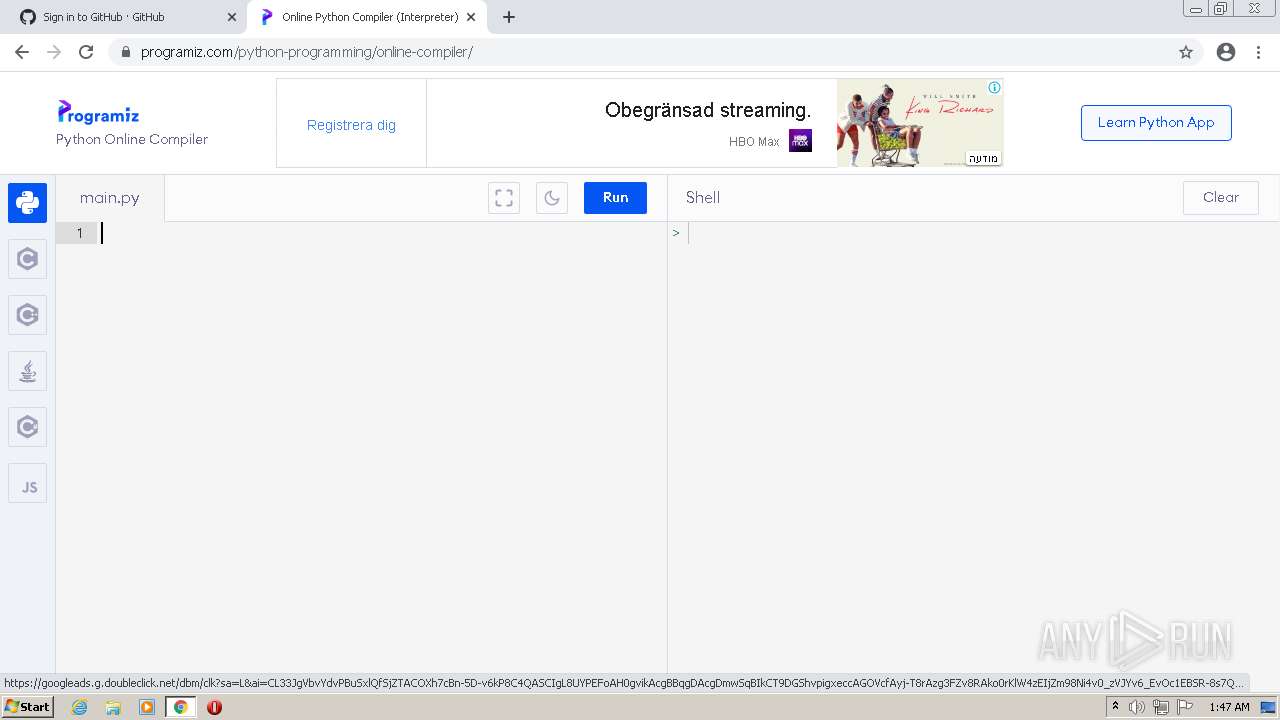
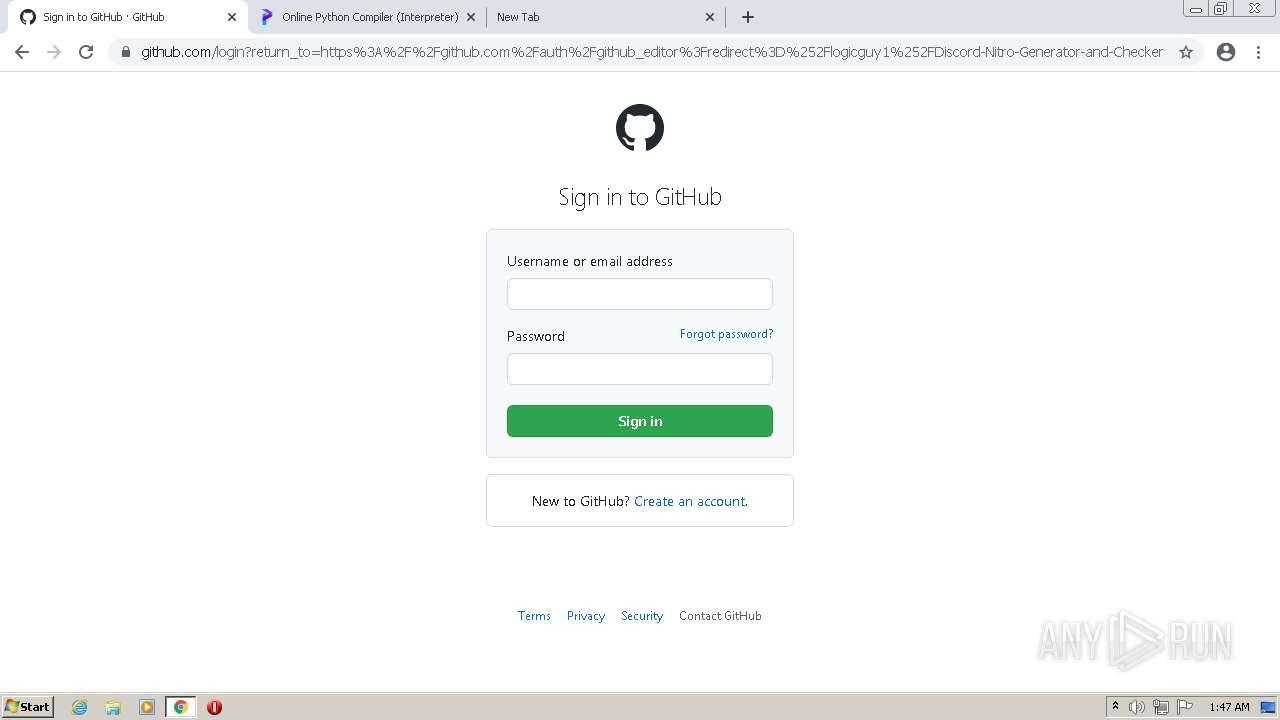
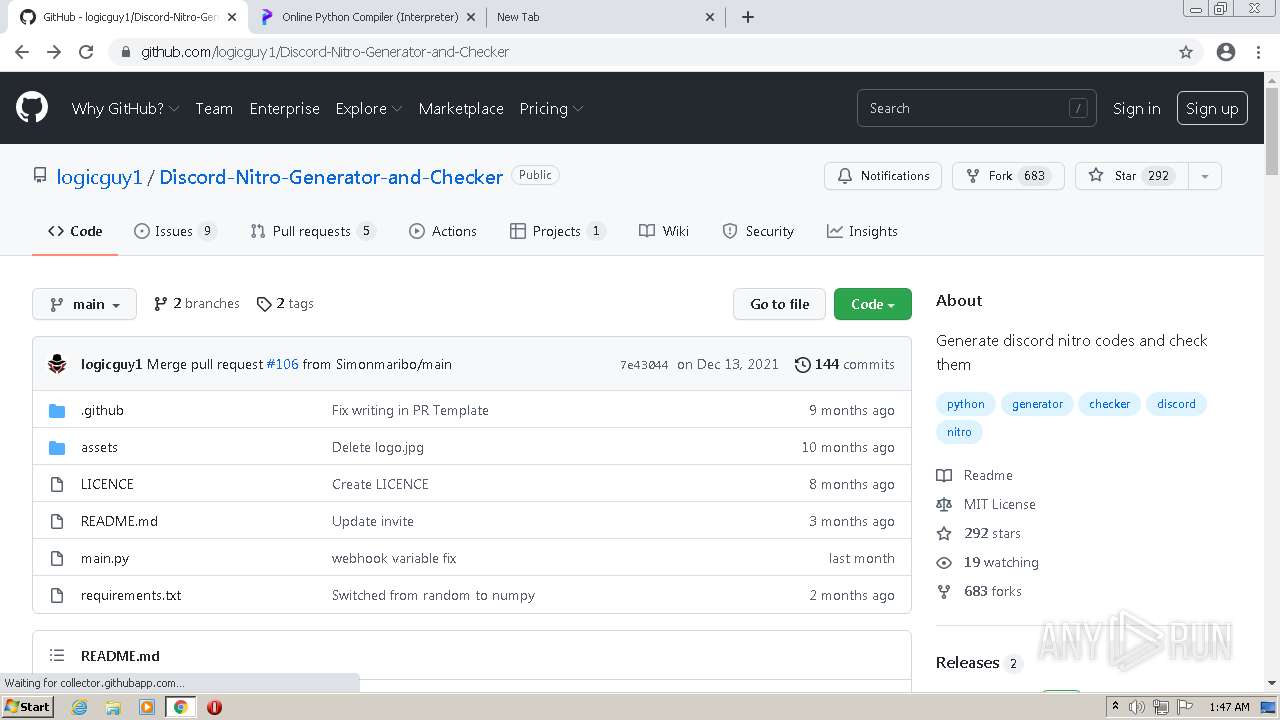
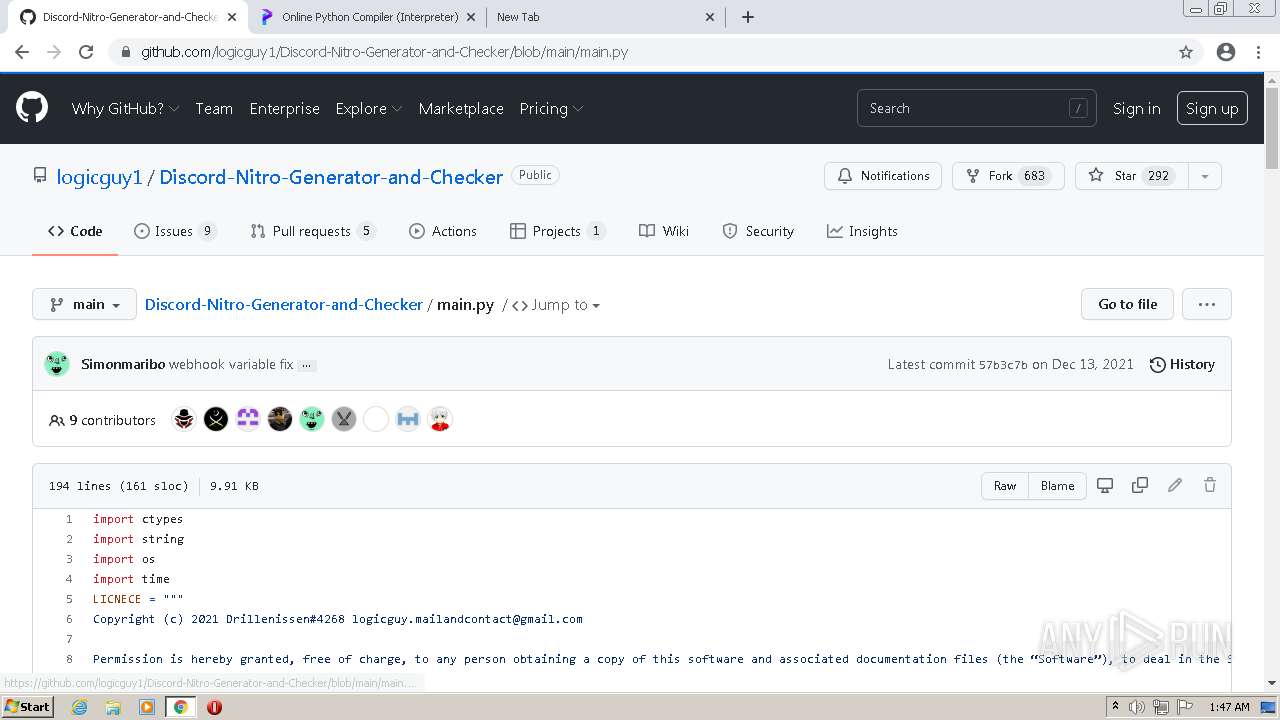
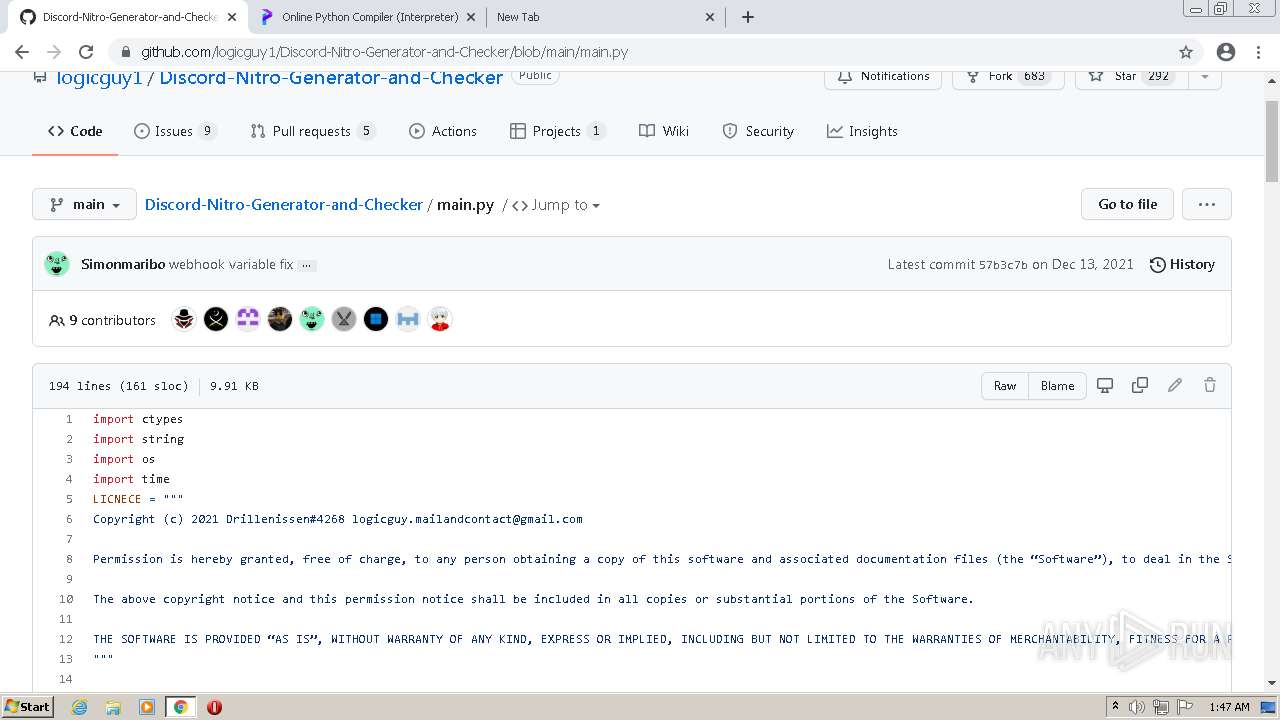
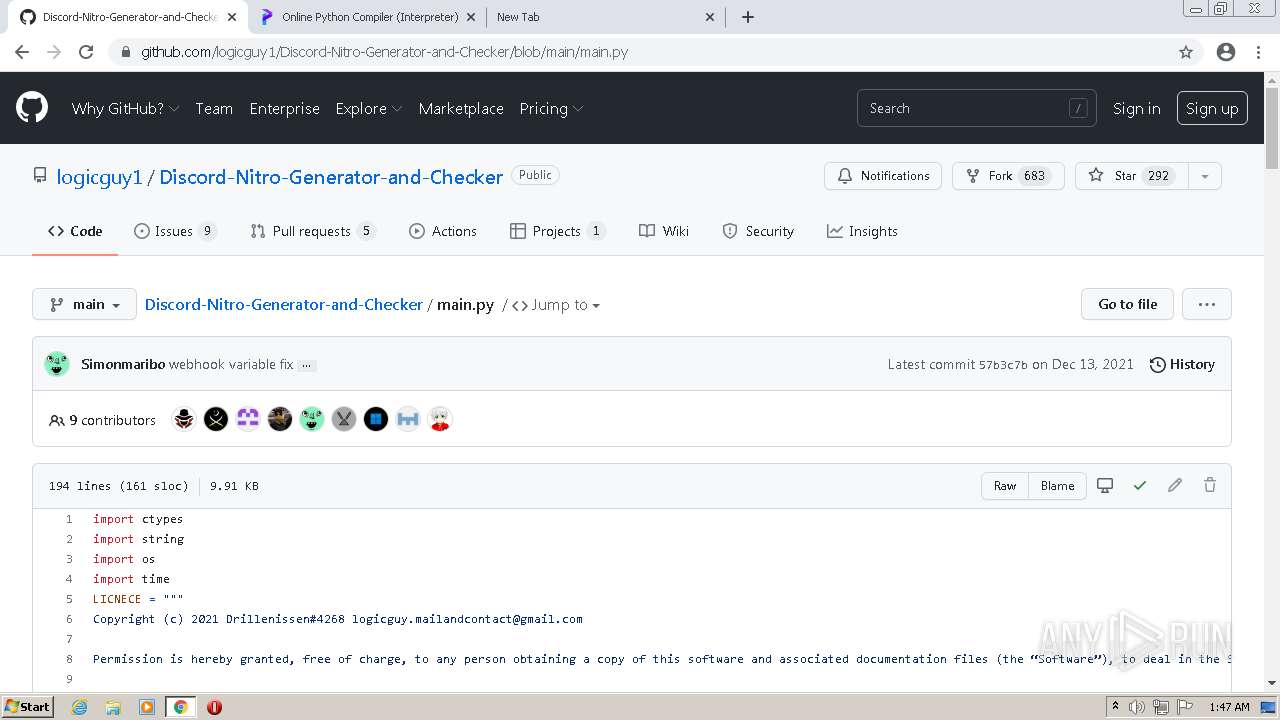
| URL: | https://github.com/logicguy1/Discord-Nitro-Generator-and-Checker |
| Full analysis: | https://app.any.run/tasks/876d076a-ba1e-46bc-a7ff-1d3dc04dea3f |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 01:43:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
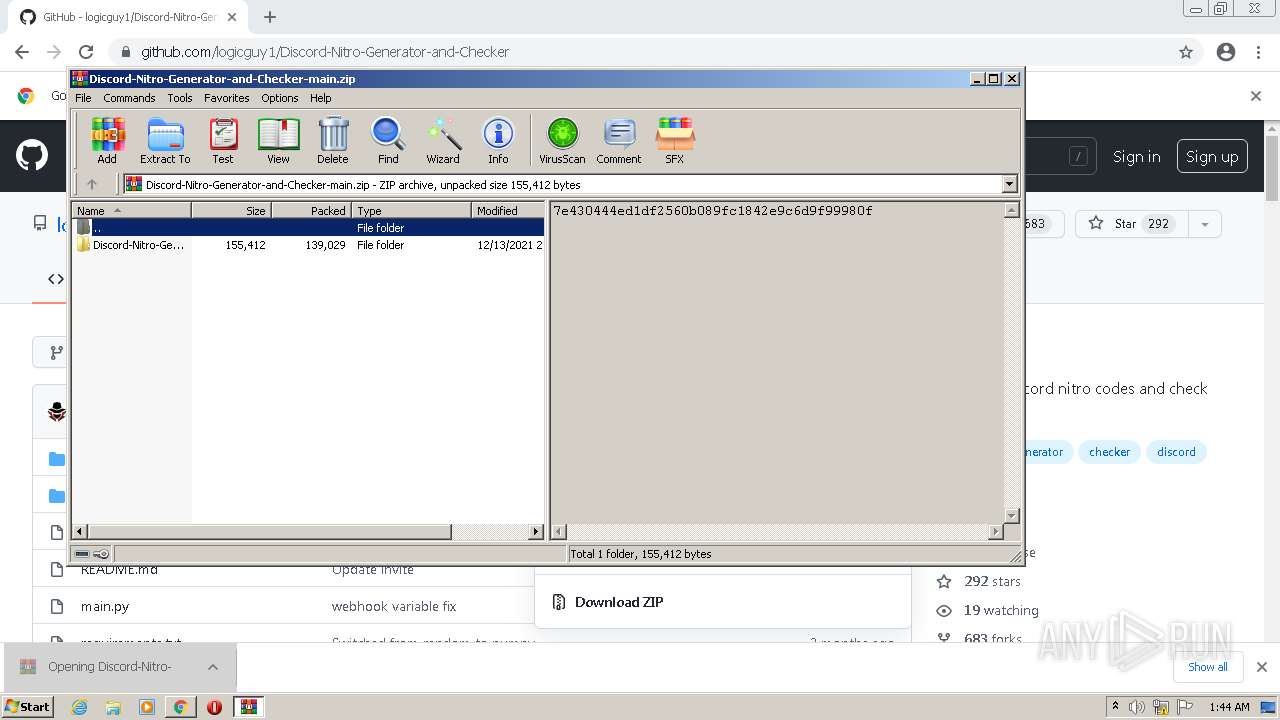
| MD5: | 70DB553A01A37463784717CFB41EF2E1 |
| SHA1: | 8487794FACC4D28395B6AF009A2CB1D022B488D1 |
| SHA256: | CC2F57E96727583468FD1AC95BE98A1F4AE9AD59E06F19137BED999DABC84C5F |
| SSDEEP: | 3:N8tEd5KCMGBnBUjcL+mpX:2uSPuBRZ5 |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 3092)
Drops executable file immediately after starts
- chrome.exe (PID: 1424)
- chrome.exe (PID: 3196)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3608)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3468)
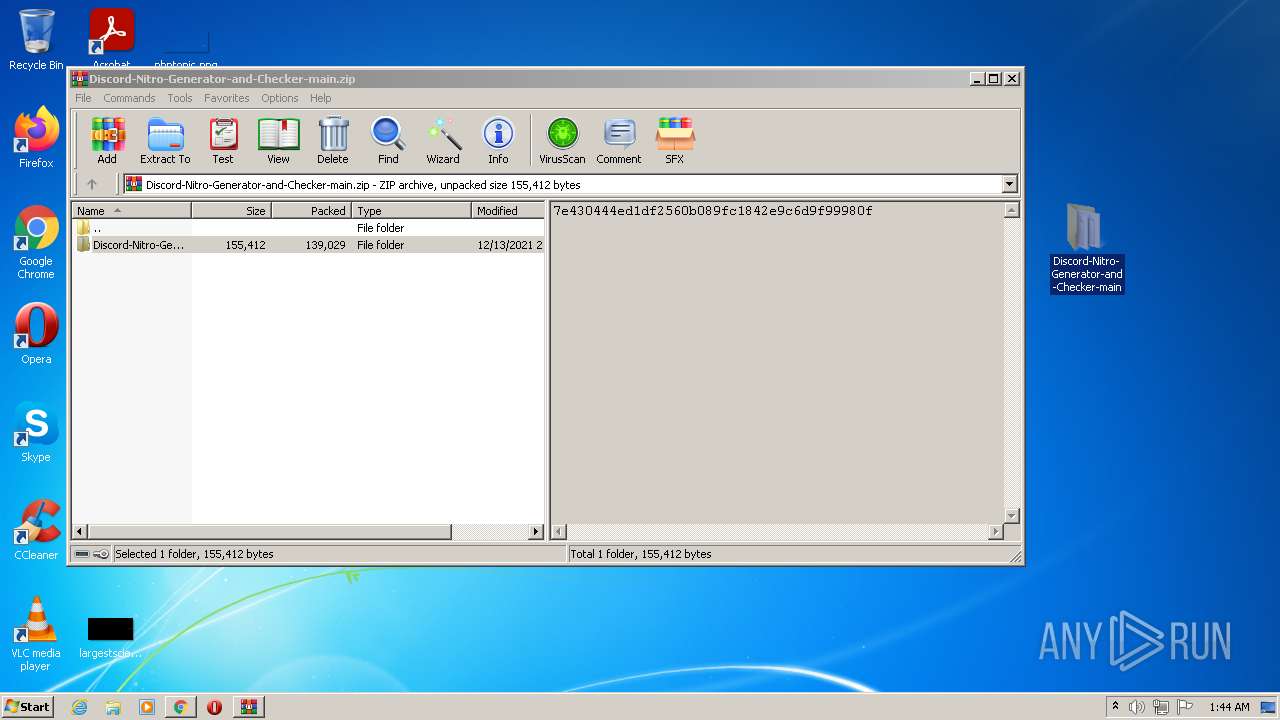
Reads the computer name
- WinRAR.exe (PID: 3324)
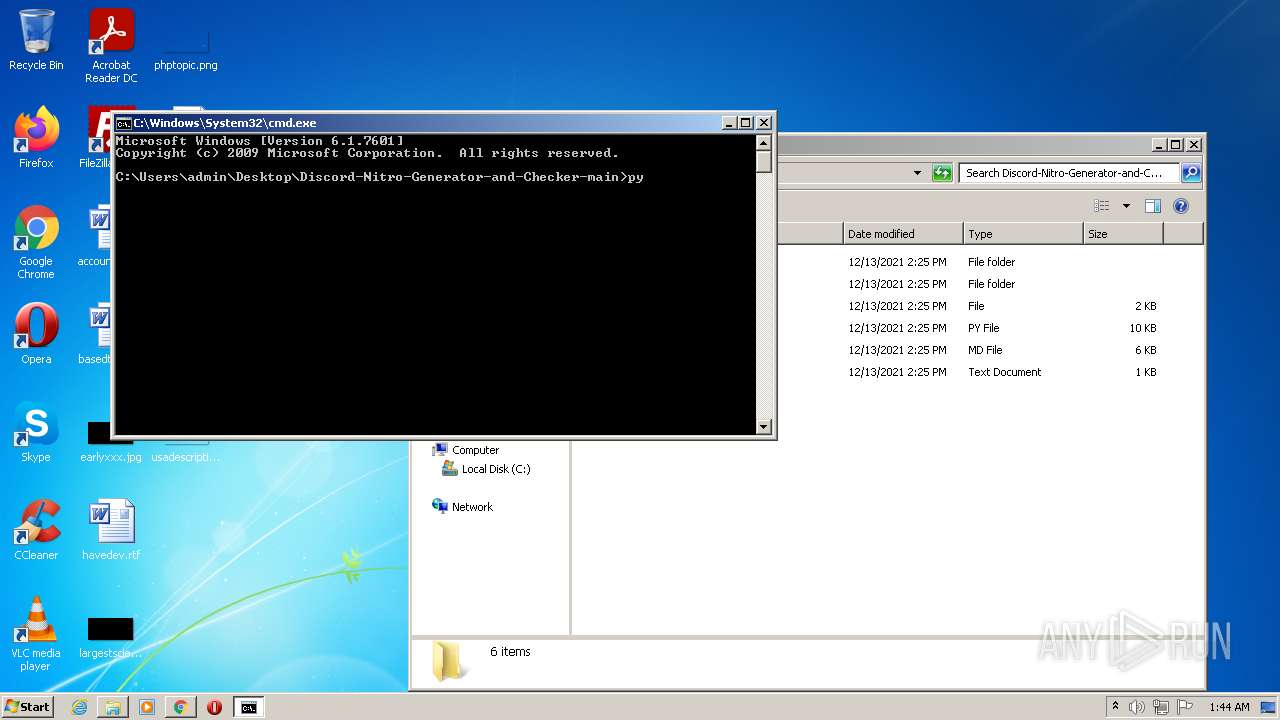
Checks supported languages
- WinRAR.exe (PID: 3324)
- cmd.exe (PID: 3568)
Executable content was dropped or overwritten
- chrome.exe (PID: 1424)
- chrome.exe (PID: 3196)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1424)
- chrome.exe (PID: 3196)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3576)
Application launched itself
- iexplore.exe (PID: 3576)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 2844)
Checks supported languages
- iexplore.exe (PID: 3608)
- iexplore.exe (PID: 3576)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 560)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2236)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 1368)
- chrome.exe (PID: 3956)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 492)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 3768)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 1372)
- chrome.exe (PID: 1888)
- chrome.exe (PID: 1704)
- chrome.exe (PID: 1488)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 1252)
- chrome.exe (PID: 1512)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 480)
- chrome.exe (PID: 3620)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 2272)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 1412)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 4084)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2672)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 868)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 676)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 1436)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 3372)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 744)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 3100)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 1404)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 1424)
- chrome.exe (PID: 1608)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 2780)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 572)
- chrome.exe (PID: 3076)
Reads the computer name
- iexplore.exe (PID: 3576)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 3892)
- iexplore.exe (PID: 3608)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 492)
- chrome.exe (PID: 3768)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 1488)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 3132)
Checks Windows Trust Settings
- iexplore.exe (PID: 3608)
- iexplore.exe (PID: 3576)
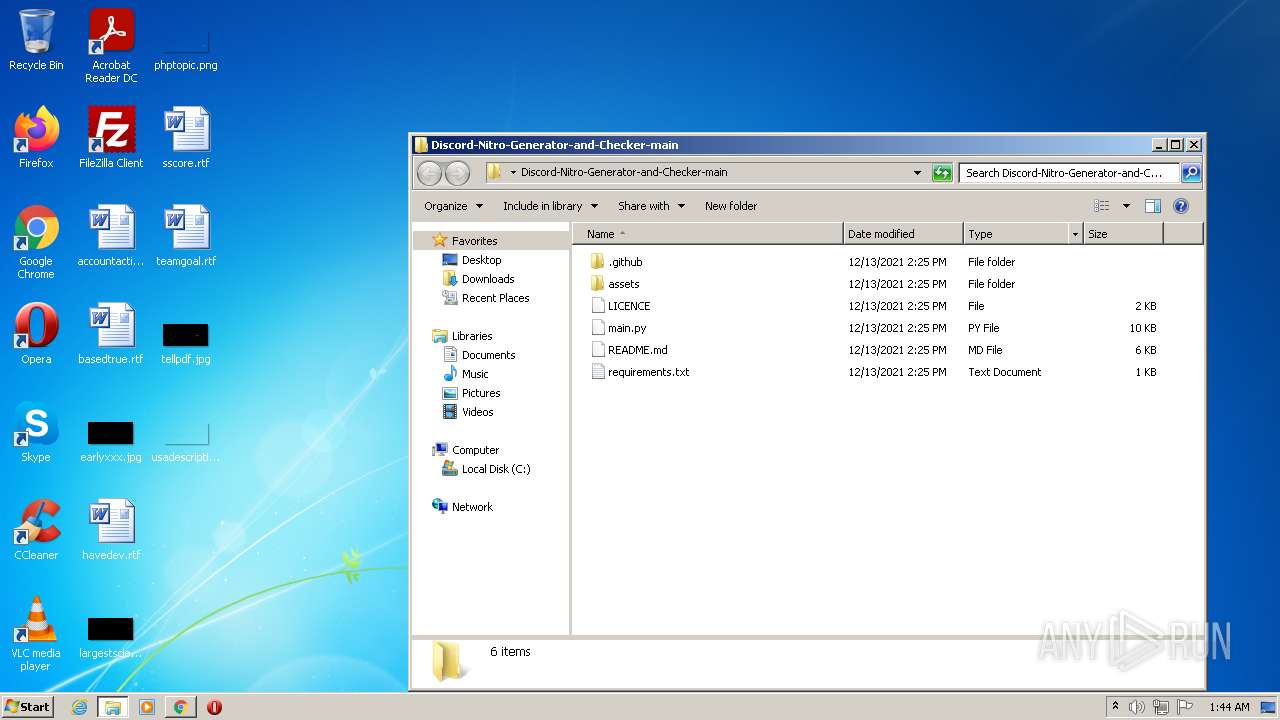
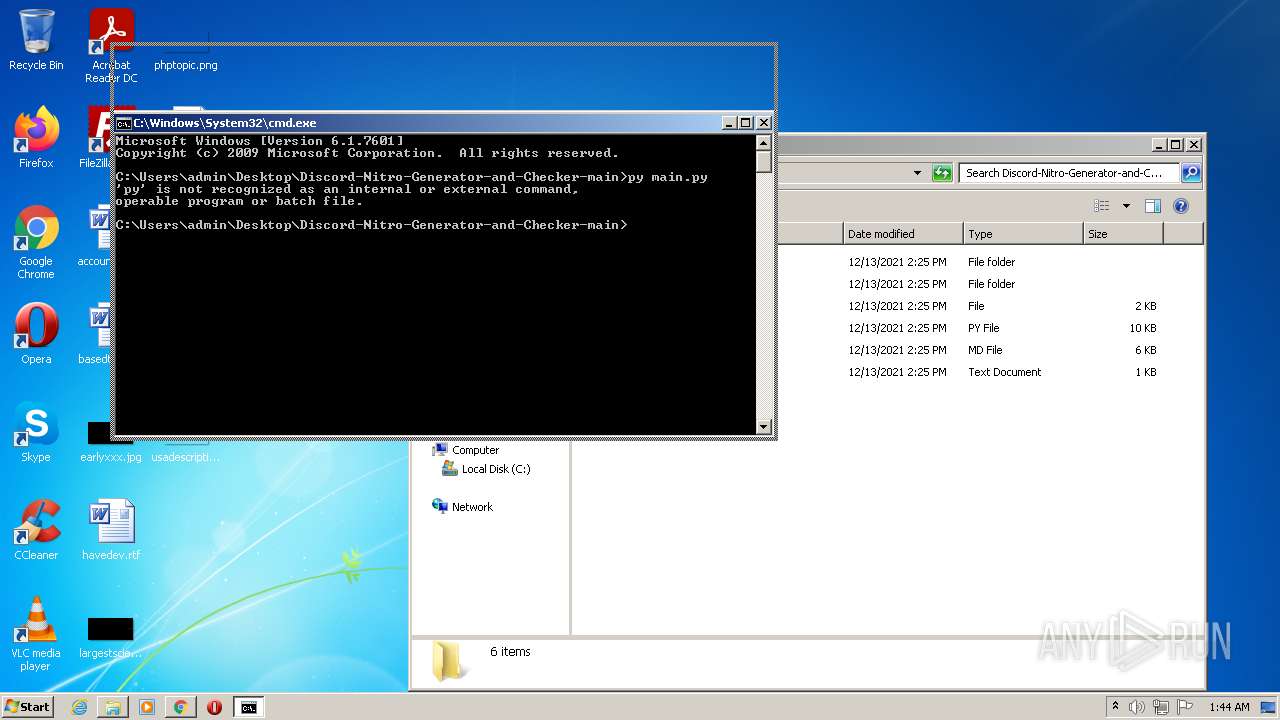
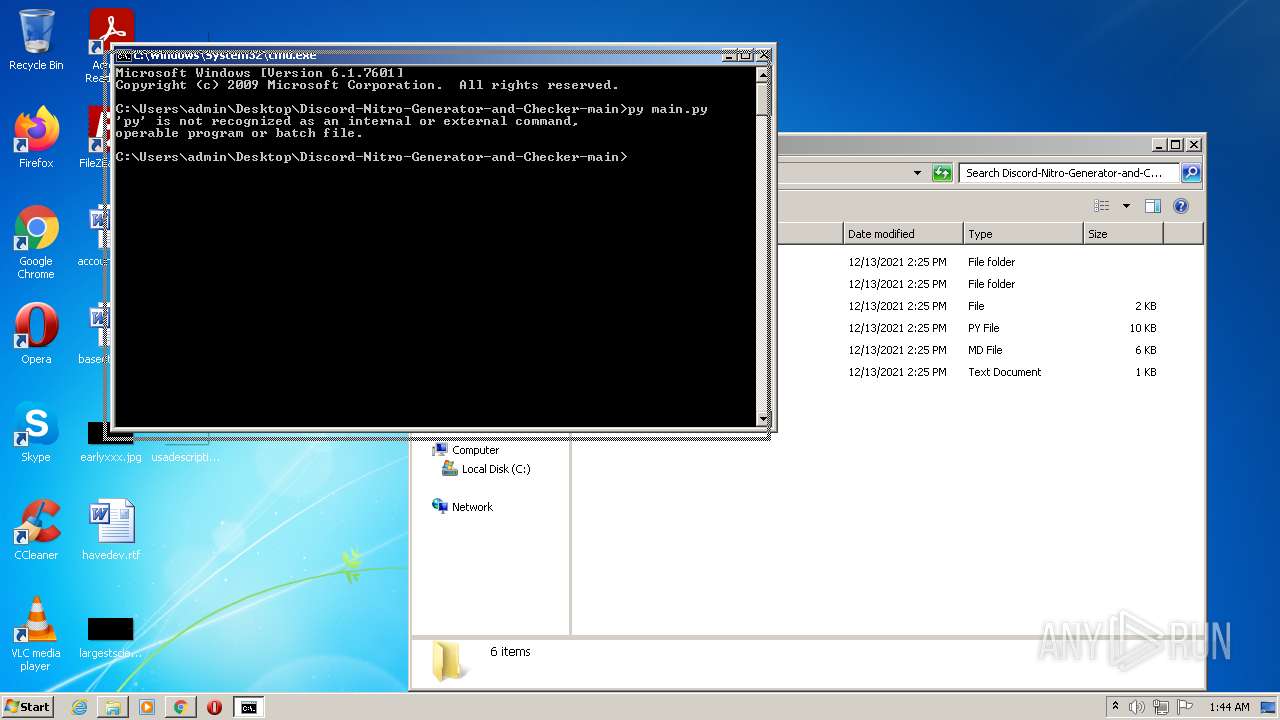
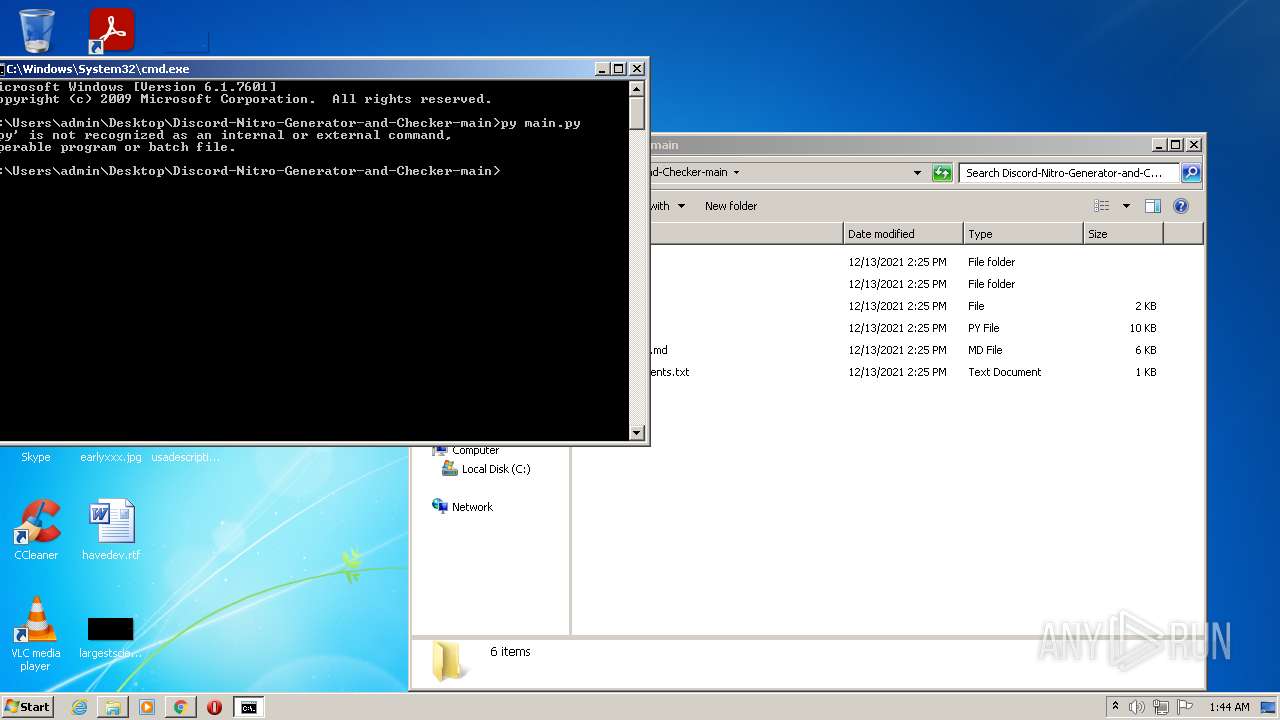
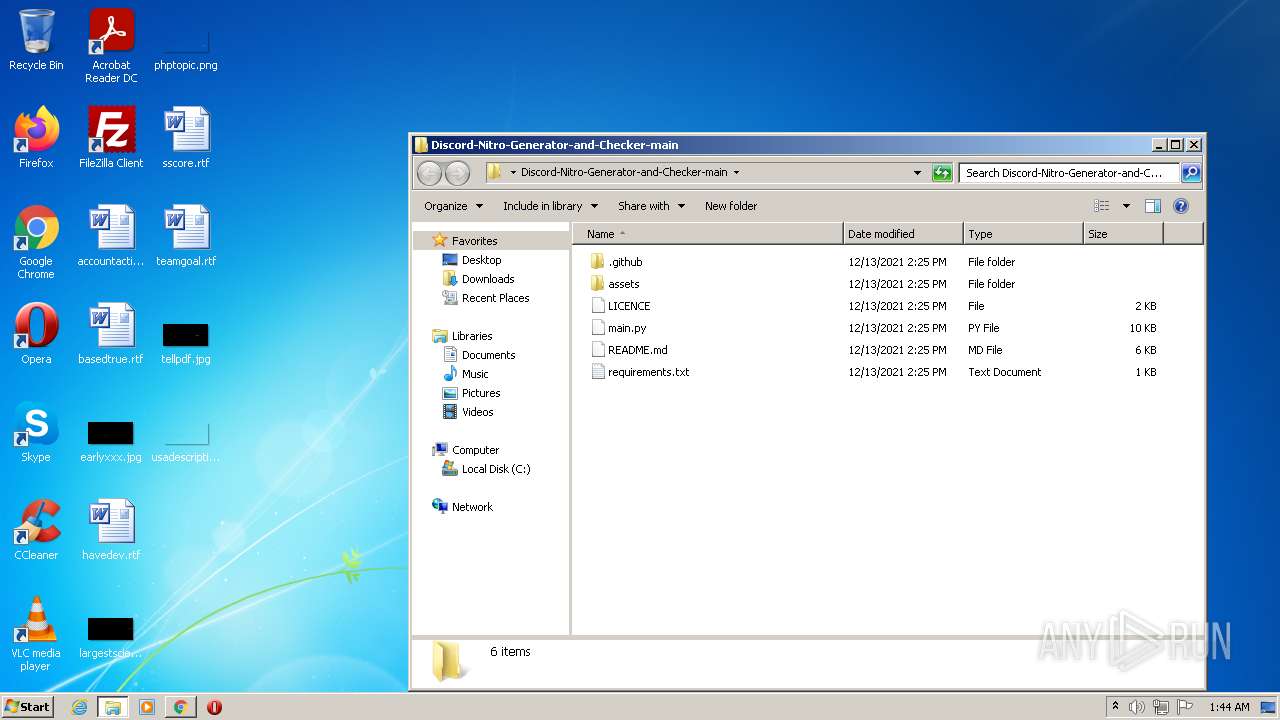
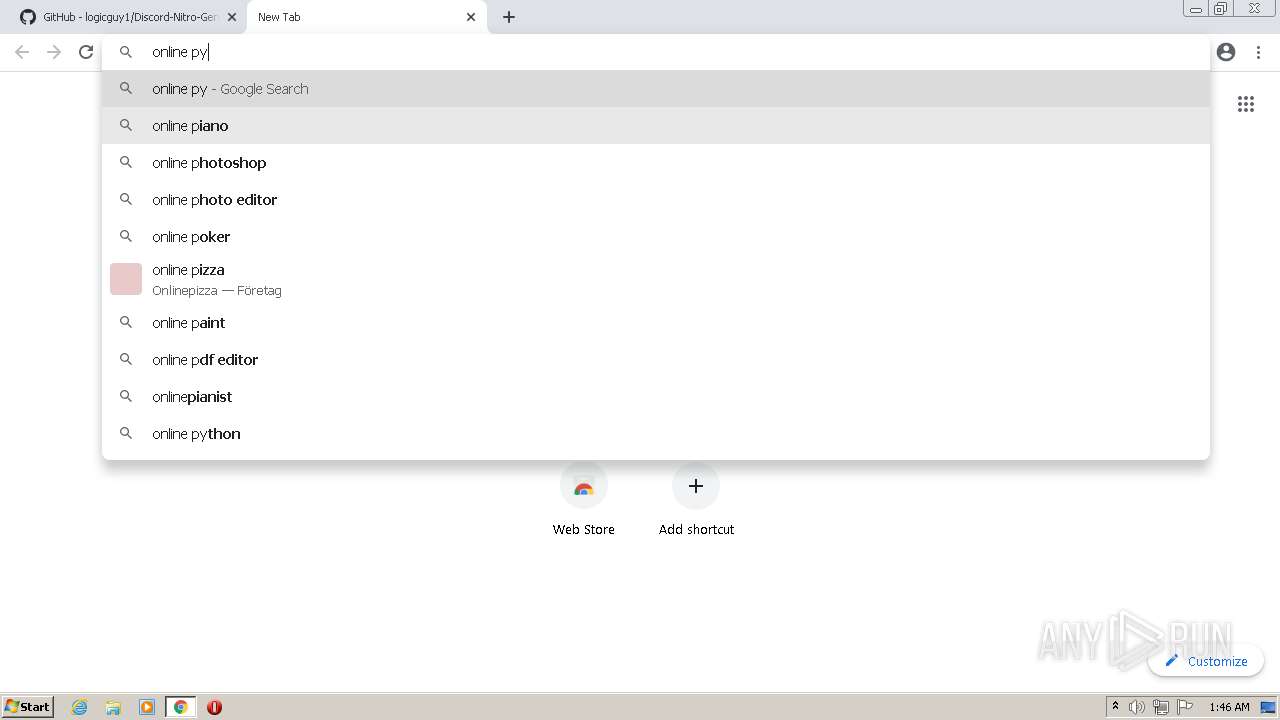
Manual execution by user
- chrome.exe (PID: 3468)
- cmd.exe (PID: 3568)
- chrome.exe (PID: 2844)
Reads settings of System Certificates
- iexplore.exe (PID: 3608)
- chrome.exe (PID: 3892)
- iexplore.exe (PID: 3576)
- chrome.exe (PID: 2844)
Reads the hosts file
- chrome.exe (PID: 3468)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 3092)
Reads the date of Windows installation
- iexplore.exe (PID: 3576)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 3132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
151
Monitored processes
111
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,12748419176144164029,2831570067583395956,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,7166919400934522312,12330157875798278777,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2180 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7166919400934522312,12330157875798278777,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,12748419176144164029,2831570067583395956,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=6484 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,12748419176144164029,2831570067583395956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,12748419176144164029,2831570067583395956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,12748419176144164029,2831570067583395956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,12748419176144164029,2831570067583395956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=61 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,12748419176144164029,2831570067583395956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=47 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,12748419176144164029,2831570067583395956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3688 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
51 161
Read events
50 767
Write events
384
Delete events
10
Modification events
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937484 | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 281645690 | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937485 | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3576) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
340
Text files
297
Unknown types
26
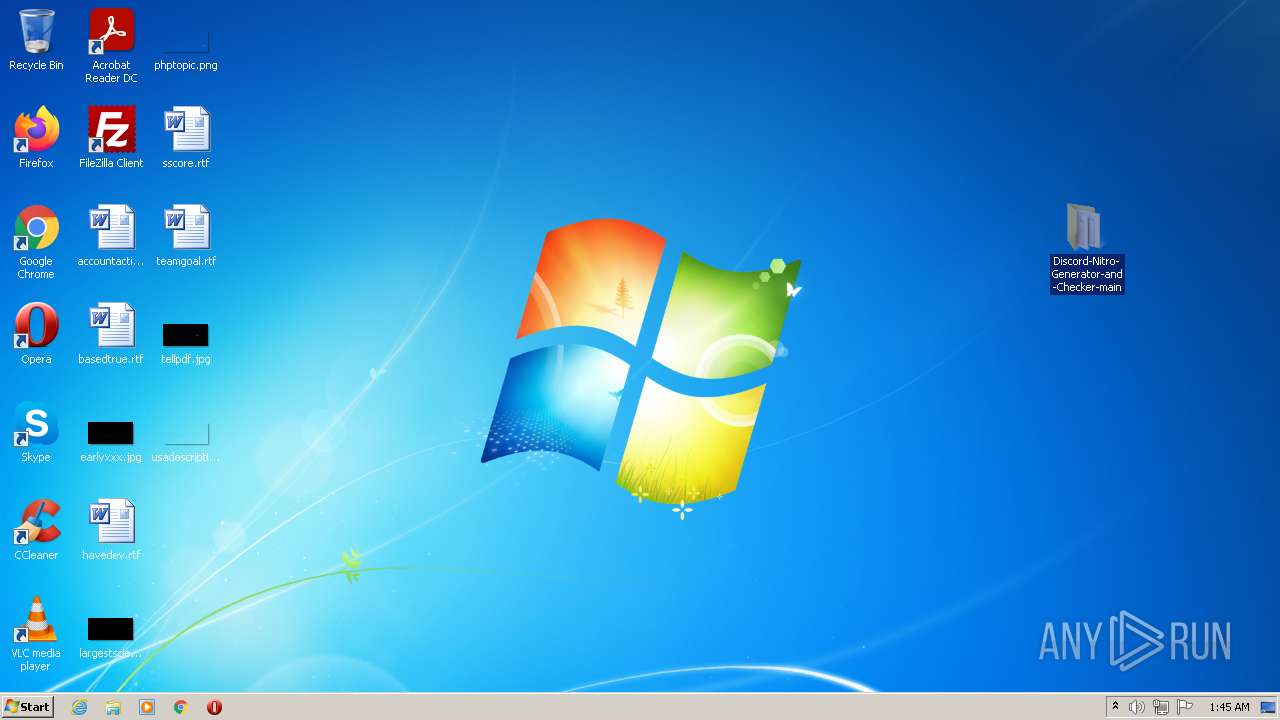
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EF55D8-D8C.pma | — | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13f64a.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF13f65a.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF13f6f6.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF13f773.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
314
DNS requests
201
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 200 | 74.125.104.231:80 | http://r2---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1643074821&mv=m&mvi=2&pl=27&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
924 | svchost.exe | HEAD | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
3892 | chrome.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 556 b | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 577 b | whitelisted |
3576 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 577 b | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 577 b | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.104.231:80 | http://r2---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1643074821&mv=m&mvi=2&pl=27&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 20.7 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 74.125.104.231:80 | http://r2---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1643074821&mv=m&mvi=2&pl=27&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 5.63 Kb | whitelisted |
924 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 577 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3608 | iexplore.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
3608 | iexplore.exe | 2.16.106.171:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3608 | iexplore.exe | 2.16.106.233:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3892 | chrome.exe | 142.250.185.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 142.250.185.228:443 | www.google.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
3892 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3576 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3892 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3892 | chrome.exe | 142.250.184.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3092 | chrome.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 1 |
3092 | chrome.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |