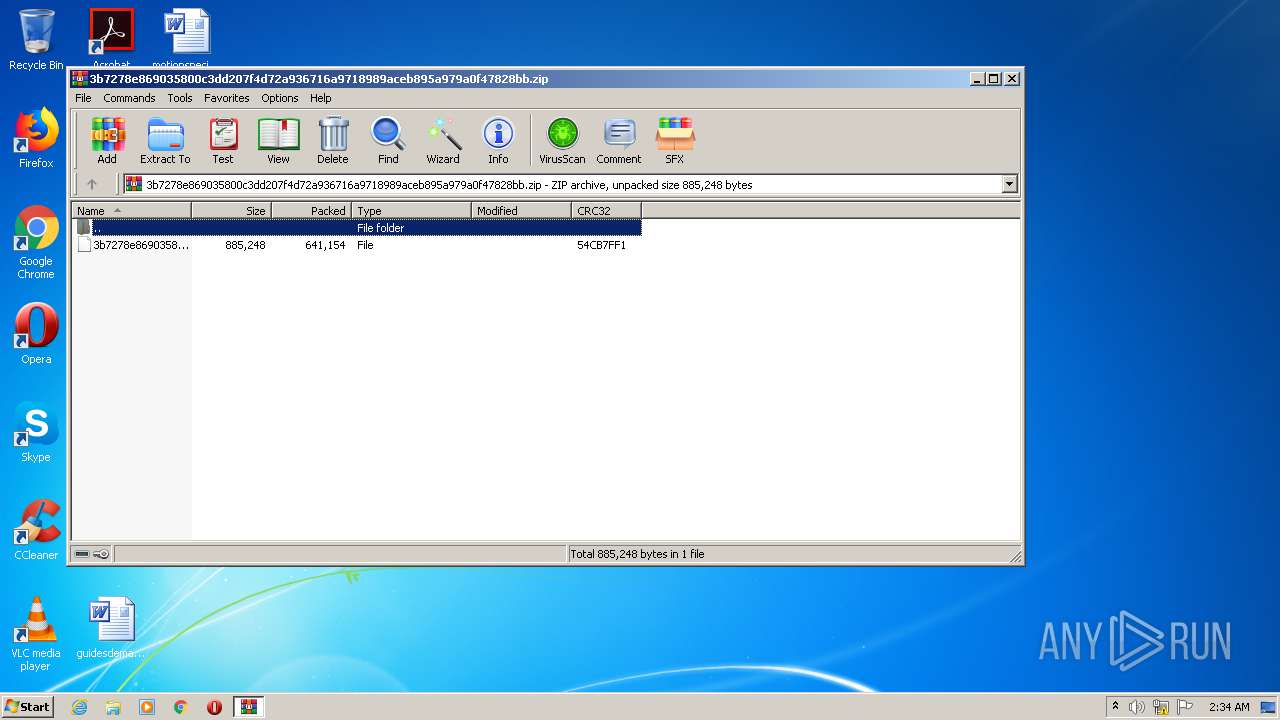
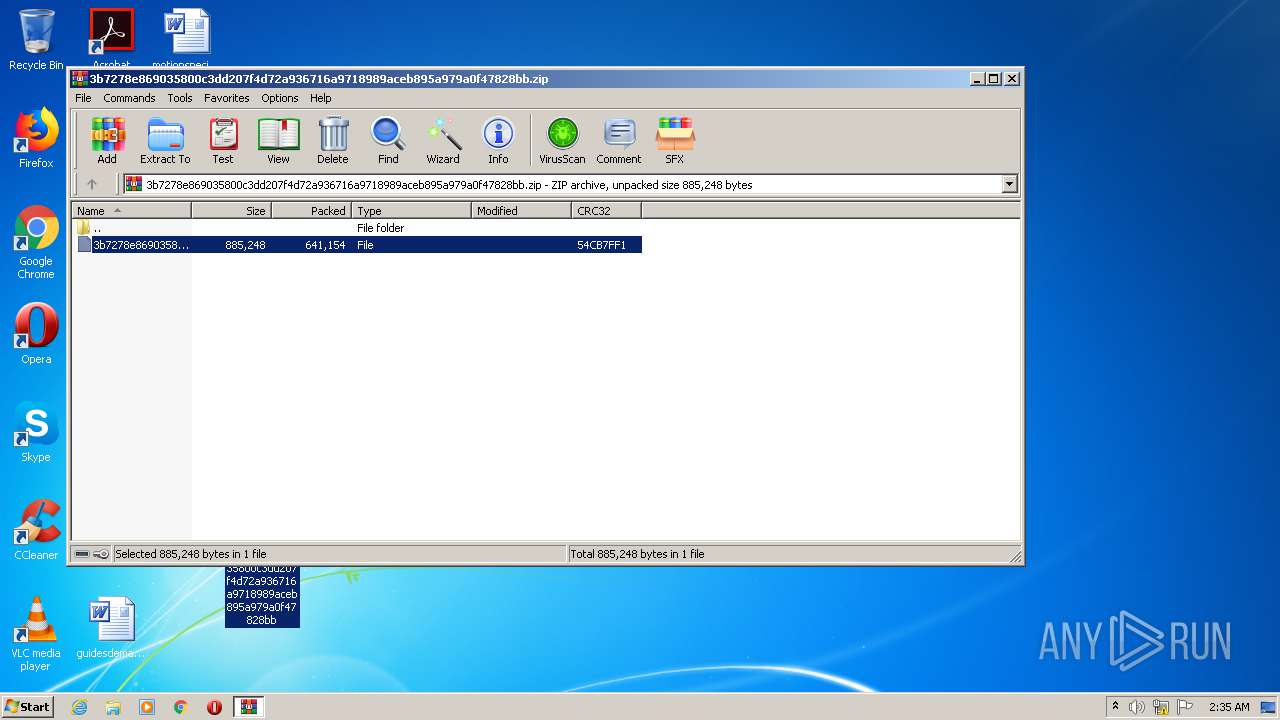
| File name: | 3b7278e869035800c3dd207f4d72a936716a9718989aceb895a979a0f47828bb.zip |
| Full analysis: | https://app.any.run/tasks/0c55442e-e065-4681-83f5-6f05b7768658 |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2020, 01:34:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F11F4D16FE18B6AF493DB6B11EEEB9A4 |
| SHA1: | 0C45ECD9CD6E48F4BF74110CB6789097C99D98DD |
| SHA256: | CC2F3AC03C7A175A2FD1201F28705CD1DE677799AC34FD1E7F60D3EE15D4FA75 |
| SSDEEP: | 12288:j5eM2ttlOvXFAOBsgyp3BauR/LAEERaf74TL5nbYyAf8iHD9hMcRVlZ/6B4jSy74:9utlOvl+gsBauNsh7L5MFfbD/b/6B4ps |
MALICIOUS
Application was dropped or rewritten from another process
- 1.exe (PID: 1668)
- 1.exe (PID: 3020)
- UAC.exe (PID: 1764)
- UAC.exe (PID: 372)
Loads dropped or rewritten executable
- UAC.exe (PID: 1764)
- UAC.exe (PID: 372)
Loads the Task Scheduler COM API
- 1.exe (PID: 3020)
Changes settings of System certificates
- UAC.exe (PID: 1764)
SUSPICIOUS
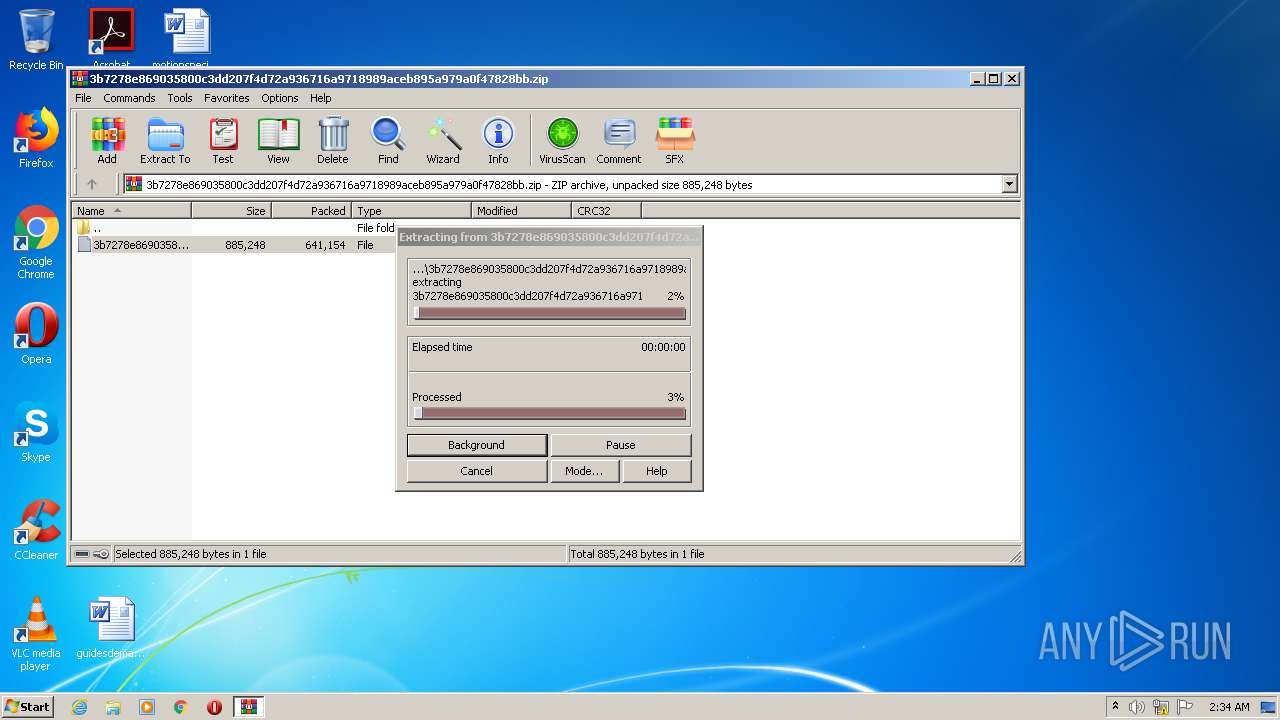
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4032)
- 1.exe (PID: 3020)
Executed as Windows Service
- UAC.exe (PID: 1764)
Creates files in the Windows directory
- 1.exe (PID: 3020)
- UAC.exe (PID: 1764)
Starts CMD.EXE for commands execution
- 1.exe (PID: 3020)
Removes files from Windows directory
- UAC.exe (PID: 1764)
Adds / modifies Windows certificates
- UAC.exe (PID: 1764)
INFO
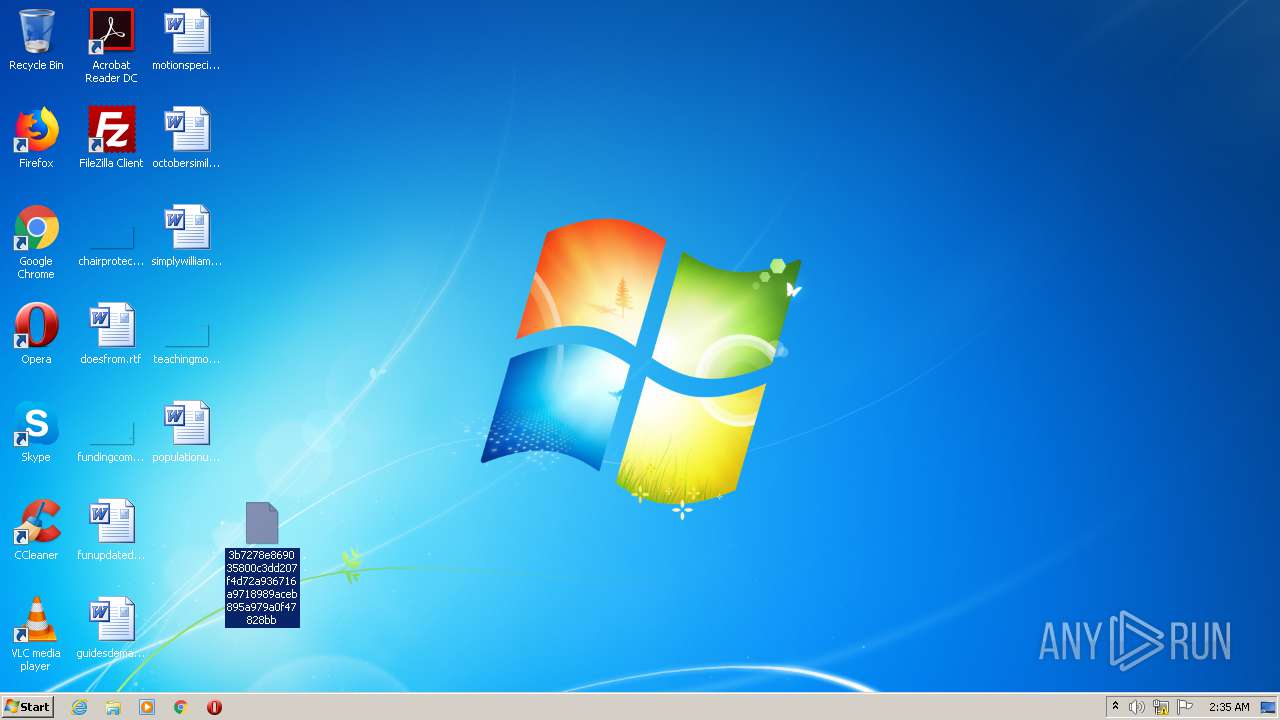
Manual execution by user
- 1.exe (PID: 1668)
- 1.exe (PID: 3020)
Reads settings of System Certificates
- UAC.exe (PID: 1764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
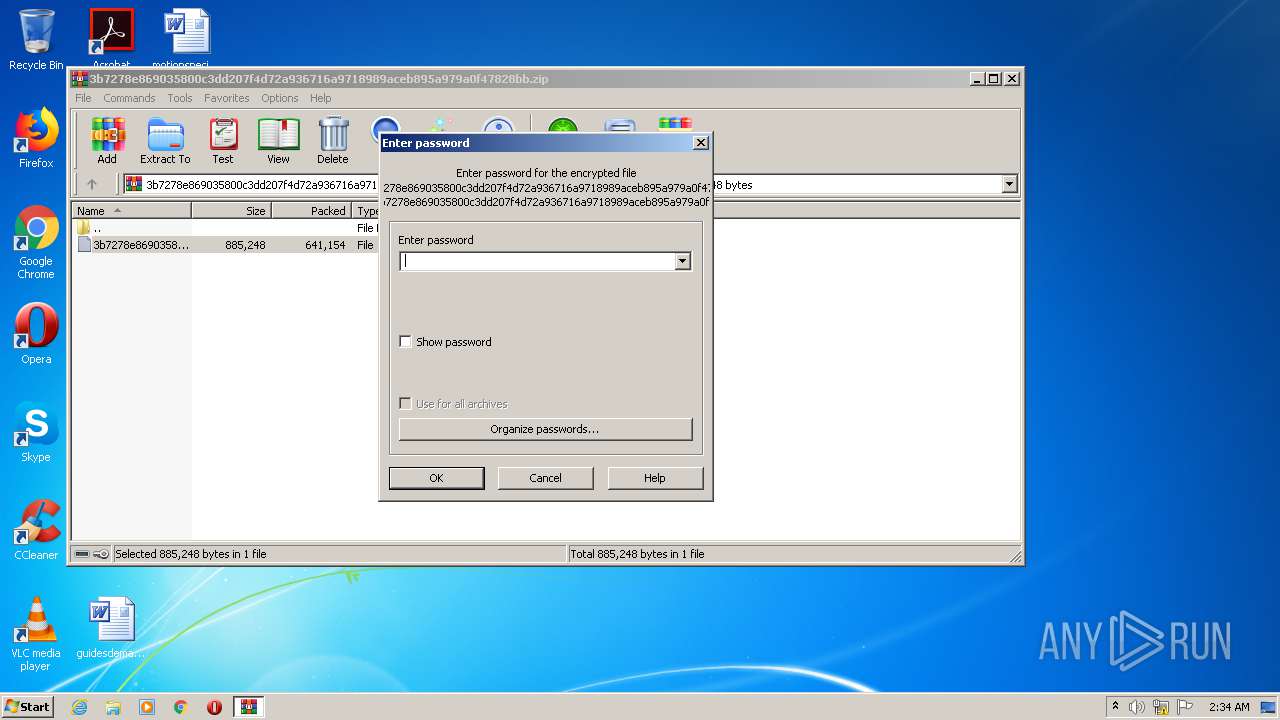
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x54cb7ff1 |
| ZipCompressedSize: | 641154 |
| ZipUncompressedSize: | 885248 |
| ZipFileName: | 3b7278e869035800c3dd207f4d72a936716a9718989aceb895a979a0f47828bb |
Total processes
49
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\UAC.exe application | C:\Windows\UAC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows User Access Control Exit code: 0 Version: 6.0.0.1 Modules
| |||||||||||||||
| 1668 | "C:\Users\admin\Desktop\1.exe" | C:\Users\admin\Desktop\1.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Windows Integrity Level: MEDIUM Description: USB Disk Security Exit code: 3221226540 Version: 0.2.0.0 Modules
| |||||||||||||||
| 1764 | C:\Windows\UAC.exe | C:\Windows\UAC.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows User Access Control Exit code: 0 Version: 6.0.0.1 Modules
| |||||||||||||||
| 3020 | "C:\Users\admin\Desktop\1.exe" | C:\Users\admin\Desktop\1.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Windows Integrity Level: HIGH Description: USB Disk Security Exit code: 0 Version: 0.2.0.0 Modules
| |||||||||||||||
| 3300 | C:\Windows\system32\cmd.exe /c "C:\Windows\UAC.exe" application | C:\Windows\system32\cmd.exe | — | 1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4032 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\3b7278e869035800c3dd207f4d72a936716a9718989aceb895a979a0f47828bb.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
547
Read events
487
Write events
60
Delete events
0
Modification events
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\3b7278e869035800c3dd207f4d72a936716a9718989aceb895a979a0f47828bb.zip | |||
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
4
Suspicious files
4
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1764 | UAC.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\default[1].htm | — | |
MD5:— | SHA256:— | |||
| 1764 | UAC.exe | C:\Windows\TEMP\CabA6E5.tmp | — | |
MD5:— | SHA256:— | |||
| 1764 | UAC.exe | C:\Windows\TEMP\TarA6E6.tmp | — | |
MD5:— | SHA256:— | |||
| 1764 | UAC.exe | C:\Windows\system32\config\systemprofile\AppData\Roaming\Microsoft\Windows\Cookies\BUDG8CTA.txt | — | |
MD5:— | SHA256:— | |||
| 4032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4032.2432\3b7278e869035800c3dd207f4d72a936716a9718989aceb895a979a0f47828bb | executable | |
MD5:— | SHA256:— | |||
| 3020 | 1.exe | C:\Windows\UACiPack.exe | executable | |
MD5:— | SHA256:— | |||
| 1764 | UAC.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | binary | |
MD5:— | SHA256:— | |||
| 1764 | UAC.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5080DC7A65DB6A5960ECD874088F3328_6CBA2C06D5985DD95AE59AF8FC7C6220 | binary | |
MD5:— | SHA256:— | |||
| 1764 | UAC.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5080DC7A65DB6A5960ECD874088F3328_6CBA2C06D5985DD95AE59AF8FC7C6220 | der | |
MD5:— | SHA256:— | |||
| 3020 | 1.exe | C:\windows\UAC.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1764 | UAC.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
1764 | UAC.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
1764 | UAC.exe | GET | 301 | 153.92.0.100:80 | http://elmaspice.net76.net/default.php?v=0.5&id=SH6N0-GZTA2-JPR6X-2OLP5-YZO09&app=0&msg=USER-PC | US | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1764 | UAC.exe | 153.92.0.100:80 | elmaspice.net76.net | Hostinger International Limited | US | shared |
1764 | UAC.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1764 | UAC.exe | 104.18.107.8:443 | www.000webhost.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
elmaspice.net76.net |
| malicious |
www.000webhost.com |
| shared |
ocsp.comodoca.com |
| whitelisted |