| URL: | http://penisland.com |
| Full analysis: | https://app.any.run/tasks/01d60293-2170-4b37-8a60-ba8c64f04623 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2020, 05:59:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3EC44920B7A7FEF24CB6B6C84C0AD383 |
| SHA1: | 15BCAB1BA4A05D3638C56AD1D328E4509745BCE1 |
| SHA256: | CC27F8DDA7FEDDDA090193D8AF11F6505DBC489CDF5AA32A3DD93EDB6EE81CA9 |
| SSDEEP: | 3:N1KOAL6BdI:CO3/I |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 2664)
Changes internet zones settings
- iexplore.exe (PID: 2956)
Creates files in the user directory
- iexplore.exe (PID: 2664)
Reads settings of System Certificates
- iexplore.exe (PID: 2664)
- iexplore.exe (PID: 2956)
Reads internet explorer settings
- iexplore.exe (PID: 2664)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2956)
Changes settings of System certificates
- iexplore.exe (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2664 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://penisland.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
5 805
Read events
618
Write events
3 470
Delete events
1 717
Modification events
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2991599002 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30802538 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
29
Text files
36
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0N7XOESD.txt | — | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\df774159-6e5d-11ea-8d30-125932cb82a3[1].htm | — | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JX2N06Z7.txt | — | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab811F.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8120.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8QU1CQCK.txt | text | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\click[1].htm | html | |
MD5:— | SHA256:— | |||
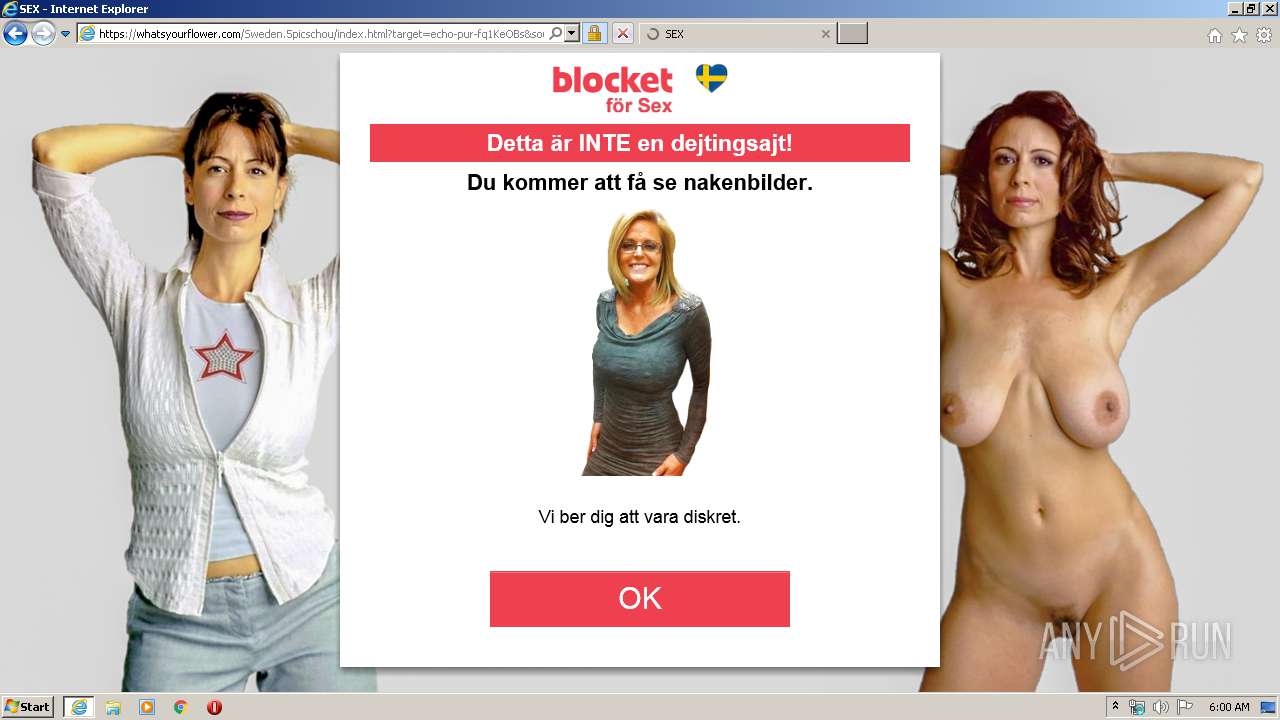
| 2664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\zcredirect[1].htm | html | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\index[1].htm | html | |
MD5:— | SHA256:— | |||
| 2664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\landing[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
41
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2664 | iexplore.exe | GET | 302 | 178.79.147.193:80 | http://whatsyourflower.com/dailytrack/base.php?c=532&key=55d8674a88bed490b45fa72989e3170d&target=echo-pur-fq1KeOBs&source=gamboge-moose&keyword=pen+island%2Cpenisland%2Cpenisland.com&os=Windows&browser=IE&cid=zrdf7741596e5d11ea8d30125932cb82a33c6c3c175d1e4ae7b0341f666baf2dfe045846c1e969e145ac | GB | — | — | whitelisted |
2664 | iexplore.exe | GET | 200 | 209.15.13.136:80 | http://dprtb.com/click?data=TEJMZ00wclN5Sm1iUF9hLVprLVRqYVJ1TmF0VHZIdzllZmY4LWk5Y0luYmw5YnVsejlqa3lQT0VFNEVrSFlBRlZLXzhrWWtzMFIwWjFSN2xoTzVtX1pNbExUbzlSNDJNQ0xySDJDeDk2NWpvN1ZvWmJtX2NjWEtsUlk4WUxKS1JiUzlyd19SeHhJUE5SS0QwMEl6cXVBMg2&id=a06a546f-c1b5-4161-a395-e8040415a394 | CA | html | 2.14 Kb | malicious |
2664 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2664 | iexplore.exe | GET | 200 | 195.138.255.24:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | DE | der | 1.37 Kb | whitelisted |
2664 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2664 | iexplore.exe | POST | 302 | 209.15.13.136:80 | http://dprtb.com/Redirect/ | CA | html | 236 b | malicious |
2664 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2664 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFeh1L3VO0beCAAAAAAyCgc%3D | US | der | 471 b | whitelisted |
2664 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2956 | iexplore.exe | GET | 404 | 54.91.125.197:80 | http://usd.jared-don.com/favicon.ico | US | html | 940 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2664 | iexplore.exe | 85.159.233.55:80 | penisland.com | NForce Entertainment B.V. | NL | suspicious |
2664 | iexplore.exe | 209.15.13.136:80 | dprtb.com | Peer 1 Network (USA) Inc. | CA | malicious |
2956 | iexplore.exe | 209.15.13.136:80 | dprtb.com | Peer 1 Network (USA) Inc. | CA | malicious |
2664 | iexplore.exe | 178.79.147.193:443 | whatsyourflower.com | Linode, LLC | GB | suspicious |
2664 | iexplore.exe | 178.79.147.193:80 | whatsyourflower.com | Linode, LLC | GB | suspicious |
2664 | iexplore.exe | 195.138.255.24:80 | isrg.trustid.ocsp.identrust.com | AS33891 Netzbetrieb GmbH | DE | whitelisted |
2664 | iexplore.exe | 172.217.21.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2664 | iexplore.exe | 216.58.210.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
— | — | 205.185.216.42:443 | ads.exoclick.com | Highwinds Network Group, Inc. | US | whitelisted |
2956 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
penisland.com |
| unknown |
dprtb.com |
| unknown |
usd.jared-don.com |
| shared |
whatsyourflower.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |