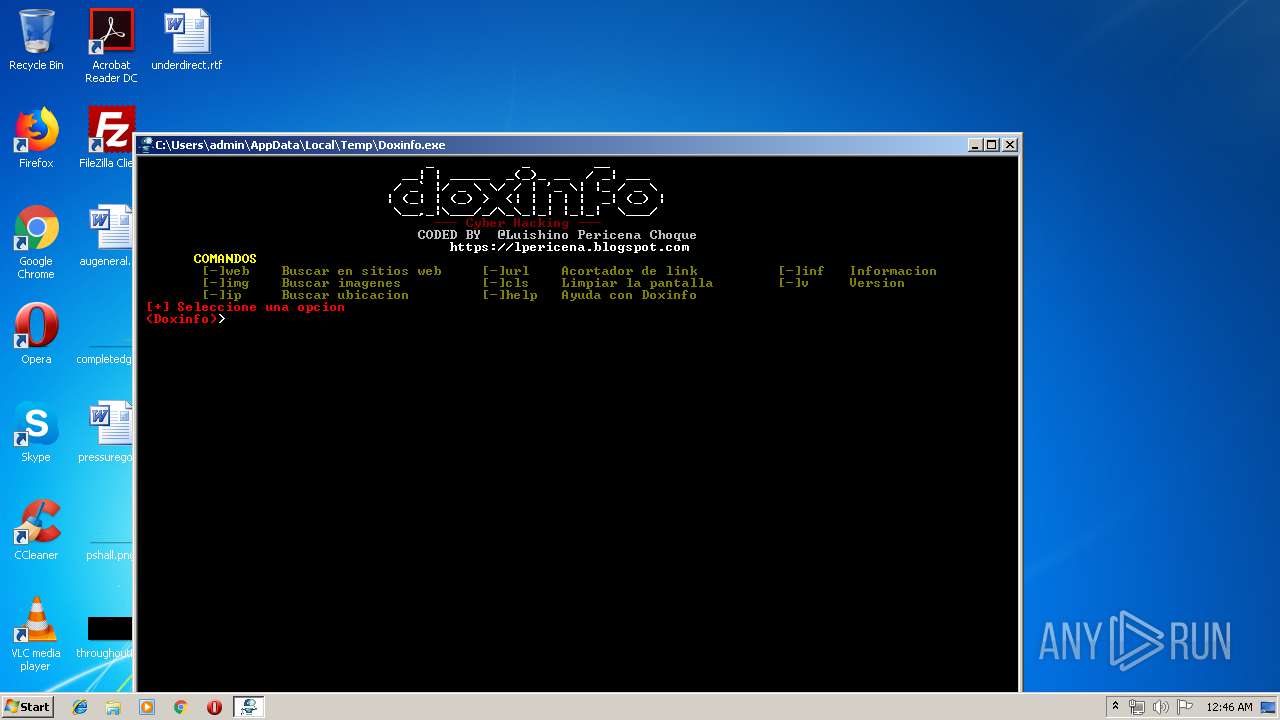
| File name: | Doxinfo.exe |
| Full analysis: | https://app.any.run/tasks/8aa95fd7-d9e5-4c8f-9ac3-1e50926bb4f4 |
| Verdict: | No threats detected |
| Analysis date: | April 10, 2019, 23:46:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 078639FA0EDA91454C03374BB90D938F |
| SHA1: | A10C694F38759187098C57D63C0AE925322CDFA9 |
| SHA256: | CC2028DB9DAECFC962308F695BCA0D46EA2E451984E4762C14DD8C3F3F055BAE |
| SSDEEP: | 1536:mLdD+0MON593j/NL0R21zt2kxi9dBkLpwWoNVzqkjaOT:mLdSro1xL221ztidmWr1n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- Doxinfo.exe (PID: 2516)
- cmd.exe (PID: 1668)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable PureBasic (generic) (54.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (16) |
| .exe | | | Win64 Executable (generic) (14.2) |
| .scr | | | Windows screen saver (6.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:07:30 18:15:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 29696 |
| InitializedDataSize: | 61952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Luishiño Pericena Choque |
| FileDescription: | Doxinfo busca los datos de una persona |
| FileVersion: | 1,0,0,0 |
| ProductName: | Doxinfo |
| InternalName: | Doxinfo |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | https://lpericena.blogspot.com/ |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 30-Jul-2014 16:15:11 |
| Detected languages: |
|
| CompanyName: | Luishiño Pericena Choque |
| FileDescription: | Doxinfo busca los datos de una persona |
| FileVersion: | 1,0,0,0 |
| ProductName: | Doxinfo |
| InternalName: | Doxinfo |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | https://lpericena.blogspot.com/ |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jul-2014 16:15:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x0000187C | 0x00001A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.3379 |
.text | 0x00003000 | 0x000058B7 | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55244 |
.rdata | 0x00009000 | 0x0000050A | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.87307 |
.data | 0x0000A000 | 0x000013F8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.78029 |
.rsrc | 0x0000C000 | 0x0000D920 | 0x0000DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.37726 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
B | 5.13463 | 21716 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D | 3.46772 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
N | 3.03658 | 24 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
O | 0.918296 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLE32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
43
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1288 | C:\Windows\system32\cmd.exe /c "prompt #$H#$E# & echo on & for %b in (1) do rem" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1472 | findstr /v /a:06 /R "+" " [-]web Buscar en sitios web [-]url Acortador de link [-]inf Informacion" nul | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | findstr /v /a:0C /R "+" " (Doxinfo)" nul | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1636 | findstr /v /a:06 /R "+" " [-]img Buscar imagenes [-]cls Limpiar la pantalla [-]v Version" nul | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1668 | cmd /c ""C:\Users\admin\AppData\Local\Temp\2D85.tmp\Doxinfo.bat"" | C:\Windows\system32\cmd.exe | — | Doxinfo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1680 | findstr /v /a:0E /R "+" " COMANDOS" nul | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | findstr /v /a:0C /R "+" " [+] Seleccione una opcion" nul | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\Temp\Doxinfo.exe" | C:\Users\admin\AppData\Local\Temp\Doxinfo.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 255 Modules
| |||||||||||||||
| 2692 | findstr /v /a:07 /R "+" " CODED BY @Luishino Pericena Choque " nul | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3532 | findstr /v /a:04 /R "+" " --- Cyber Hacking ---" nul | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
12
Read events
12
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ --- Cyber Hacking --- | — | |
MD5:— | SHA256:— | |||
| 1668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ CODED BY @Luishino Pericena Choque | — | |
MD5:— | SHA256:— | |||
| 1668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ COMANDOS | — | |
MD5:— | SHA256:— | |||
| 1668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ [-]web Buscar en sitios web [-]url Acortador de link [-]inf Informacion | — | |
MD5:— | SHA256:— | |||
| 1668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ [-]img Buscar imagenes [-]cls Limpiar la pantalla [-]v Version | — | |
MD5:— | SHA256:— | |||
| 1668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ [-]ip Buscar ubicacion [-]help Ayuda con Doxinfo | — | |
MD5:— | SHA256:— | |||
| 1668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ (Doxinfo) | — | |
MD5:— | SHA256:— | |||
| 2516 | Doxinfo.exe | C:\Users\admin\AppData\Local\Temp\2D85.tmp\Doxinfo.bat | text | |
MD5:F90F7F81BED1F7F200DF22DE5EAE78FD | SHA256:E8F44227A9090D0E118843F5706C52409655CE5F5363BBA08DCC3682AD727930 | |||
| 1668 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ [+] Seleccione una opcion | text | |
MD5:DF66FA563A2FAFDB93CC559DEB0A38C4 | SHA256:3E39ED22DC63246937C4DBBF34CE4FB1CFE6B00DE7596B020CAD49AE50031351 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report