| File name: | AnyDesk.exe |
| Full analysis: | https://app.any.run/tasks/b4e0c0de-24ac-461c-a9eb-29c4af41608f |
| Verdict: | Malicious activity |
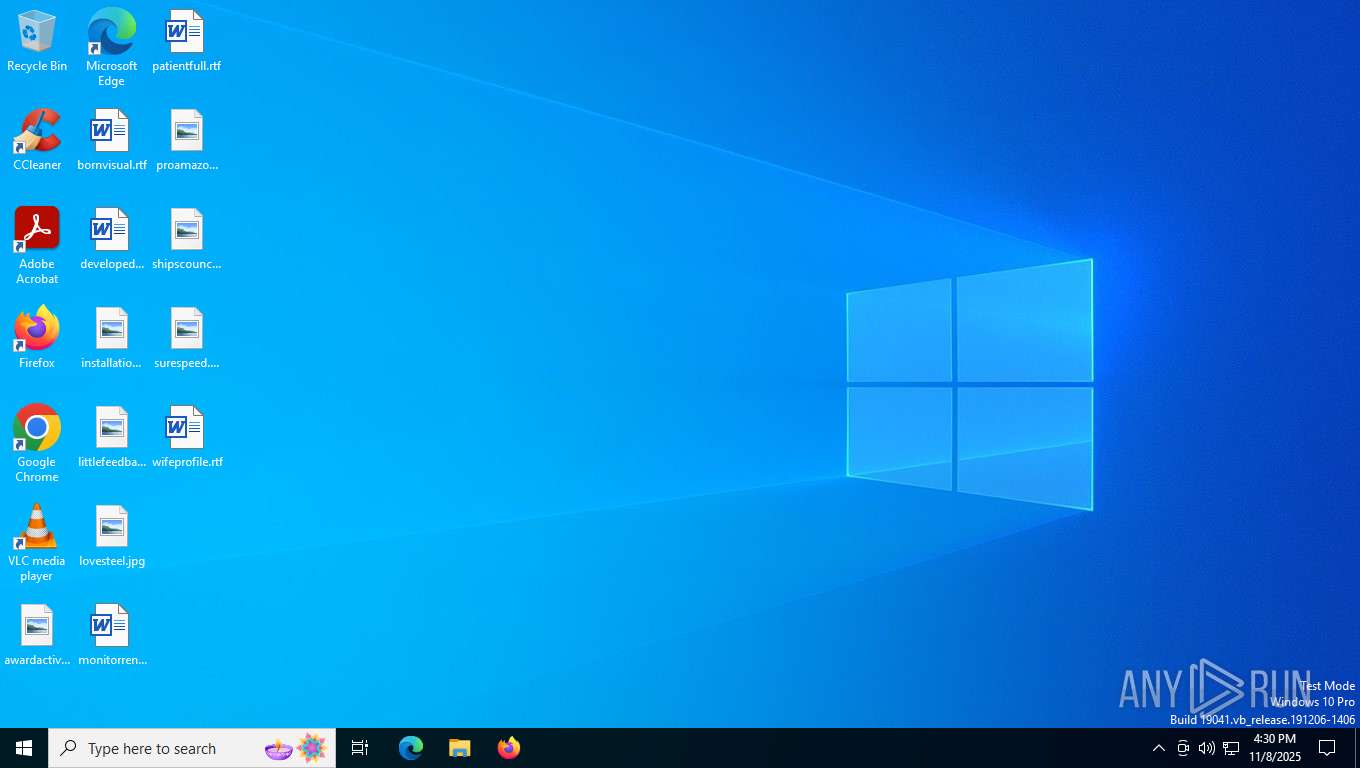
| Analysis date: | November 08, 2025, 16:30:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 325E49B504CC47E1F16956FFE1772795 |
| SHA1: | 2829933453C404C3FDDCC1E349146AD32D1F0AE9 |
| SHA256: | CC1DAE253B72906CFE2E89C278AB45A9CCC63567919373DE7600783A05DD6D0A |
| SSDEEP: | 12288:Fx93eROQ0wCh+P/6cjbE1c69t/IFE5TbXe1R3WaMn7isF8LUUI:Fxw0dLcHE1c6EFqgc7LUI |
MALICIOUS
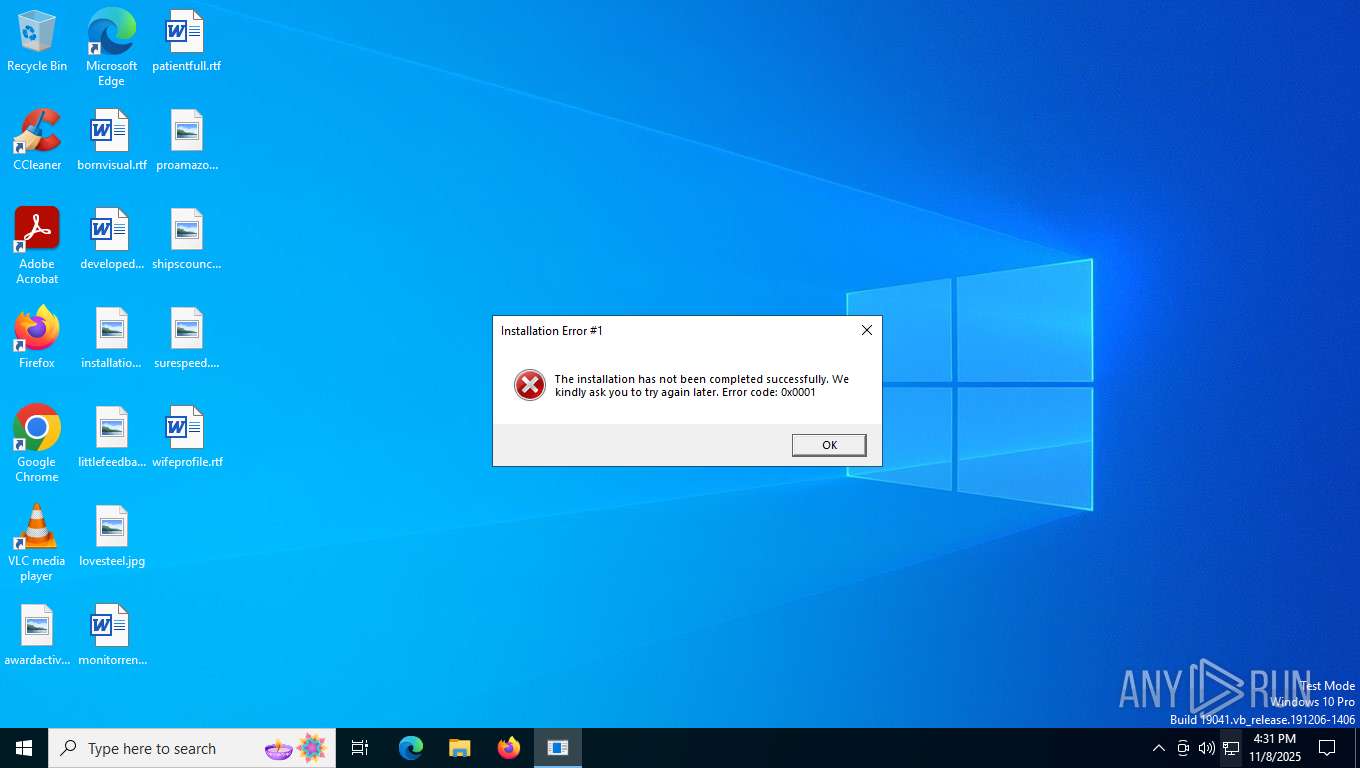
Executing a file with an untrusted certificate
- AnyDesk.exe (PID: 7596)
Uses Task Scheduler to run other applications
- AnyDesk.exe (PID: 7596)
SUSPICIOUS
Executable content was dropped or overwritten
- AnyDesk.exe (PID: 7596)
Reads security settings of Internet Explorer
- AnyDesk.exe (PID: 7596)
Uses RUNDLL32.EXE to load library
- AnyDesk.exe (PID: 7596)
Searches for installed software
- rundll32.exe (PID: 7860)
There is functionality for taking screenshot (YARA)
- AnyDesk.exe (PID: 7596)
- rundll32.exe (PID: 7860)
The process executes via Task Scheduler
- rundll32.exe (PID: 5580)
INFO
Reads the software policy settings
- AnyDesk.exe (PID: 7596)
- slui.exe (PID: 7976)
- rundll32.exe (PID: 7860)
Creates files or folders in the user directory
- AnyDesk.exe (PID: 7596)
- rundll32.exe (PID: 7860)
Reads the computer name
- AnyDesk.exe (PID: 7596)
Checks proxy server information
- AnyDesk.exe (PID: 7596)
- slui.exe (PID: 7976)
- rundll32.exe (PID: 7860)
Checks supported languages
- AnyDesk.exe (PID: 7596)
Reads the machine GUID from the registry
- AnyDesk.exe (PID: 7596)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 7860)
Launching a file from Task Scheduler
- AnyDesk.exe (PID: 7596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Clipper DOS Executable (33.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (33) |
| .exe | | | DOS Executable Generic (33) |
| .vxd | | | VXD Driver (0.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:11:07 13:06:45+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 471040 |
| InitializedDataSize: | 21504 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x71910 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
159
Monitored processes
7
Malicious processes
1
Suspicious processes
0
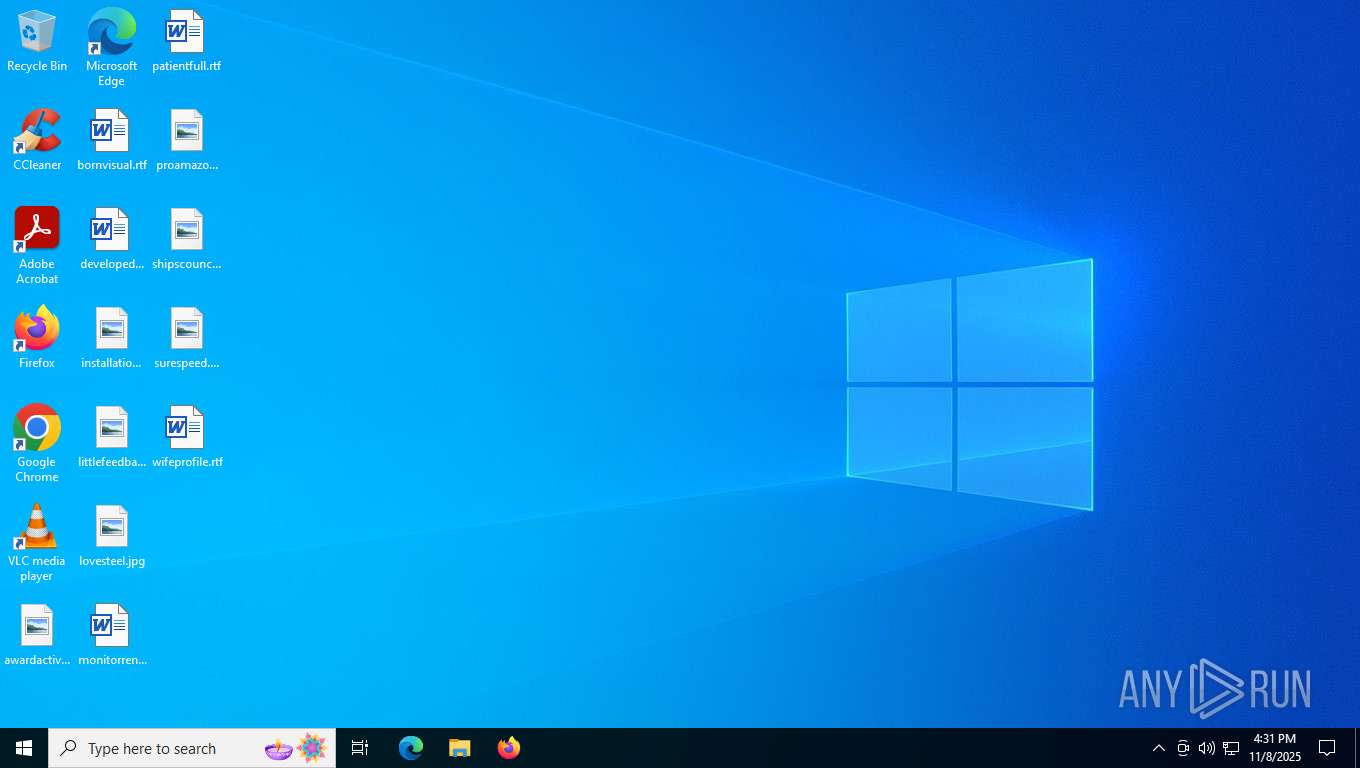
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4156 | C:\WINDOWS\System32\schtasks.exe /run /tn "ProgramFilesManager" | C:\Windows\System32\schtasks.exe | — | AnyDesk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5580 | "C:\WINDOWS\System32\rundll32.exe" C:\Users\admin\AppData\Roaming\n61VDZHbOQ210zS\ProgramFilesManager.dll RTKBootStrv | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7596 | "C:\Users\admin\AppData\Local\Temp\AnyDesk.exe" | C:\Users\admin\AppData\Local\Temp\AnyDesk.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7604 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AnyDesk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7860 | C:\WINDOWS\System32\rundll32.exe C:\Users\admin\AppData\Roaming\n61VDZHbOQ210zS\ProgramFilesManager.dll RTKBootStrv | C:\Windows\System32\rundll32.exe | AnyDesk.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7976 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8092 | C:\WINDOWS\System32\schtasks.exe /Create /SC MINUTE /MO 18 /TN "ProgramFilesManager" /TR "C:\WINDOWS\System32\rundll32.exe C:\Users\admin\AppData\Roaming\n61VDZHbOQ210zS\ProgramFilesManager.dll RTKBootStrv" | C:\Windows\System32\schtasks.exe | — | AnyDesk.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 204
Read events
5 190
Write events
14
Delete events
0
Modification events
| (PID) Process: | (7596) AnyDesk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7596) AnyDesk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7596) AnyDesk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7596) AnyDesk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7596) AnyDesk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7596) AnyDesk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7596) AnyDesk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7860) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7860) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7860) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
6
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7596 | AnyDesk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:7F924EAEA21BB91214FF7B4525F3BD29 | SHA256:E718475014C8F51A8F2746FBE90A7BFF516B65BEF36EE6340A5FC746BC5DFC32 | |||
| 7860 | rundll32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A4A76C0B890145BCEBEB63644B729C97 | binary | |
MD5:0E285DC80725D5044FEE4F3ED8E49658 | SHA256:D301C20B6E75C6C66E8B2C15BE60FCAC40215602A44B557BB2247EB0A3FA5769 | |||
| 7596 | AnyDesk.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\reg[1].txt | text | |
MD5:260CA9DD8A4577FC00B7BD5810298076 | SHA256:AEE408847D35E44E99430F0979C3357B85FE8DBB4535A494301198ADBEE85F27 | |||
| 7596 | AnyDesk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EFB34FC434BEEEE2DD58694954479FC | binary | |
MD5:AEB41DC5A29ABEC6571A9B0EA39BE1D7 | SHA256:71C5A3193663238BA8119429948B61BDEC497010DD2E8982827F58A458F12D73 | |||
| 7596 | AnyDesk.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\login[1].ico | image | |
MD5:08C42ECBF0BBB428E630AF86167106F9 | SHA256:DDFE59CD8A78F35C56A468A3EC58029CA92223ED8711E9E47EF566968D805152 | |||
| 7596 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\n61VDZHbOQ210zS\ProgramFilesManager.dll | executable | |
MD5:C6CFEAD8B347A3FA480566D4827E409B | SHA256:849398D91FABC66C708731B598877F688591F8A90A7535E13AE502C85A029A31 | |||
| 7860 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\list[1].json | binary | |
MD5:99914B932BD37A50B983C5E7C90AE93B | SHA256:44136FA355B3678A1146AD16F7E8649E94FB4FC21FE77E8310C060F61CAAFF8A | |||
| 7596 | AnyDesk.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EFB34FC434BEEEE2DD58694954479FC | binary | |
MD5:79CB824B1B9AEE2F6FE7F822FC1CE779 | SHA256:0C1E1756C73B2FEF68DCCB1910AB7C8571706C72DCC42E282FB80B1D475015EA | |||
| 7860 | rundll32.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A4A76C0B890145BCEBEB63644B729C97 | binary | |
MD5:EBE2102652FE7DA2608B99EE3CF1ECE9 | SHA256:56430C3E9D815D22405E0979D36C2B0472F6DD6033869A0E8D477566BBCFAD53 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
46
DNS requests
25
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7596 | AnyDesk.exe | GET | 200 | 104.18.21.213:80 | http://r13.c.lencr.org/83.crl | unknown | — | — | whitelisted |
4712 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7860 | rundll32.exe | GET | 200 | 104.18.20.213:80 | http://r12.c.lencr.org/70.crl | unknown | — | — | whitelisted |
2564 | svchost.exe | GET | 200 | 95.101.78.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2736 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
2736 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
2736 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
3228 | svchost.exe | GET | 304 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7088 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4316 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 2.16.204.161:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7596 | AnyDesk.exe | 62.204.35.223:443 | tedbutz.com | COGENT-174 | US | unknown |
7596 | AnyDesk.exe | 104.18.21.213:80 | r13.c.lencr.org | CLOUDFLARENET | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7860 | rundll32.exe | 149.56.95.175:443 | gloitch.com | OVH SAS | CA | unknown |
7860 | rundll32.exe | 104.18.20.213:80 | r13.c.lencr.org | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
tedbutz.com |
| unknown |
r13.c.lencr.org |
| whitelisted |
gloitch.com |
| unknown |
r12.c.lencr.org |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Malware Command and Control Activity Detected | ET MALWARE Oyster Backdoor CnC Checkin M5 |
— | — | Malware Command and Control Activity Detected | ET MALWARE Oyster Backdoor CnC Checkin M6 |
— | — | Malware Command and Control Activity Detected | ET MALWARE Oyster Backdoor CnC Checkin M6 |