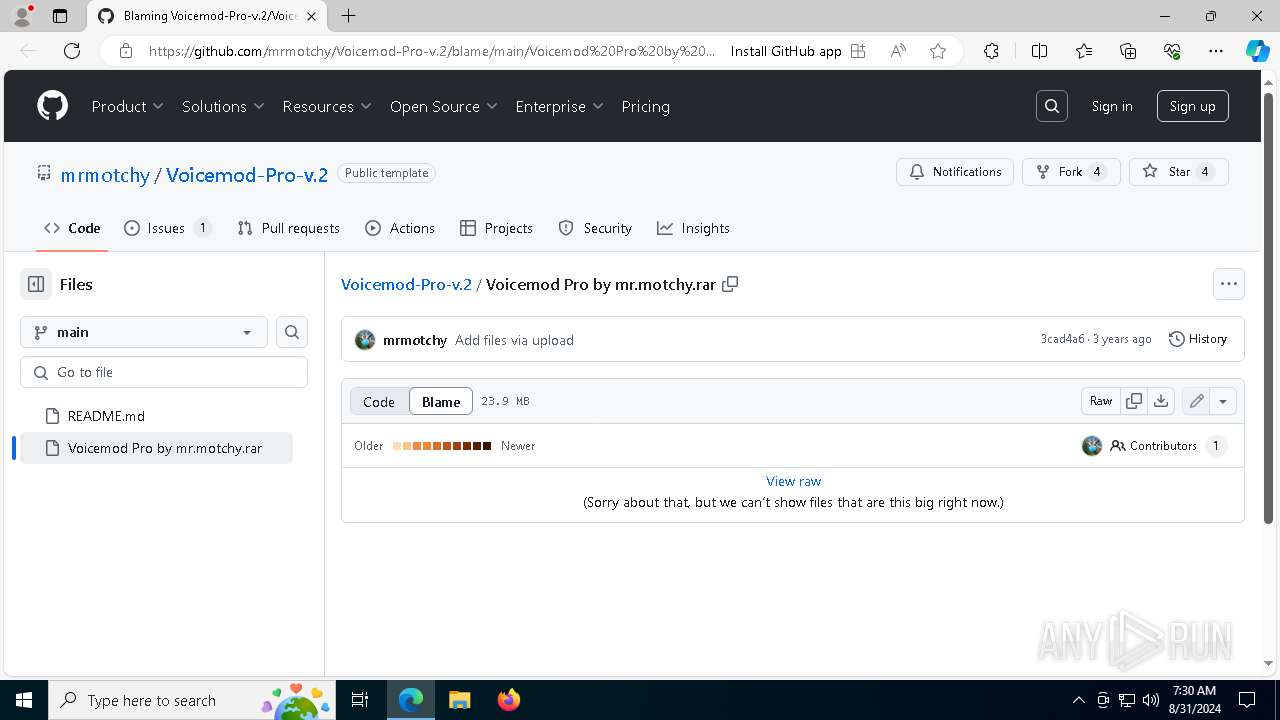
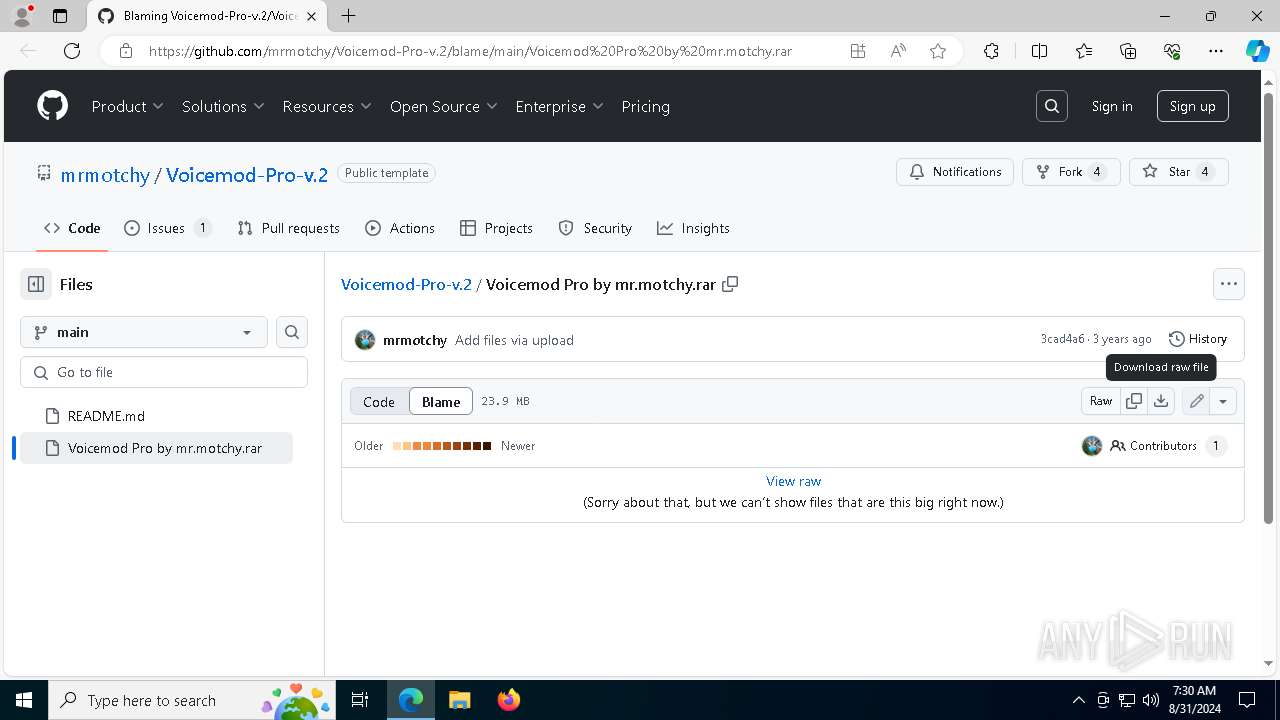
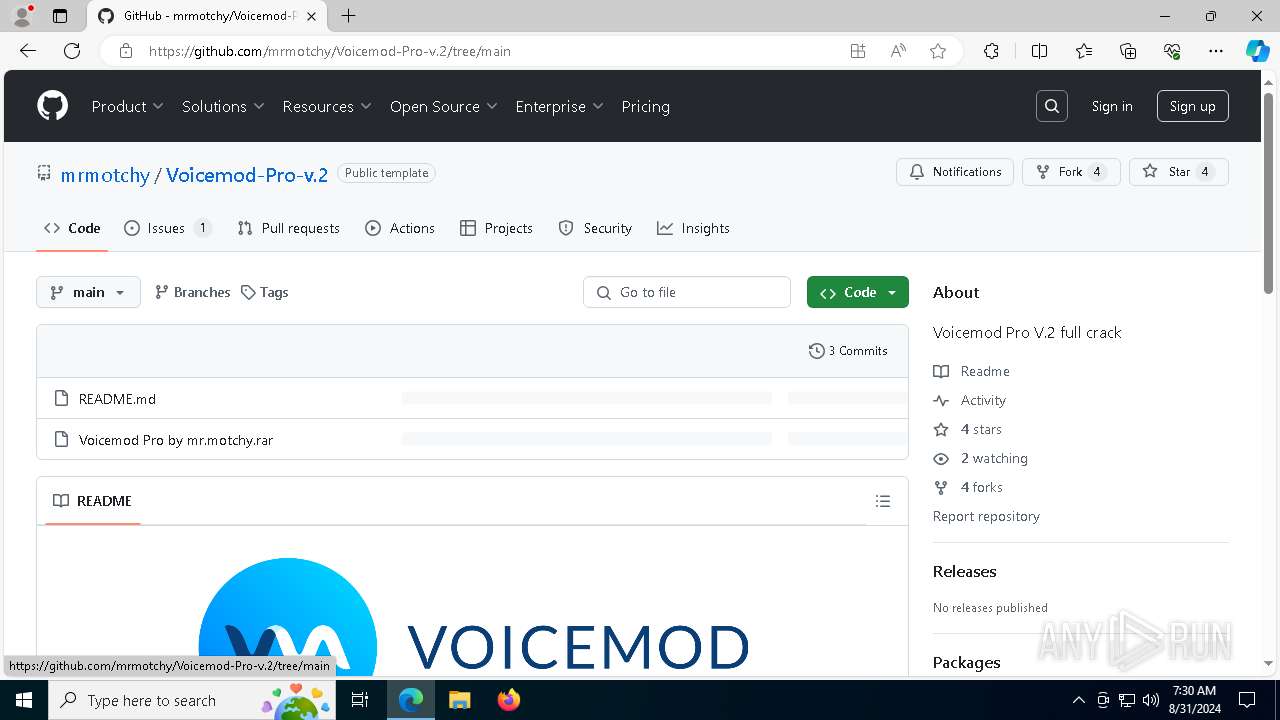
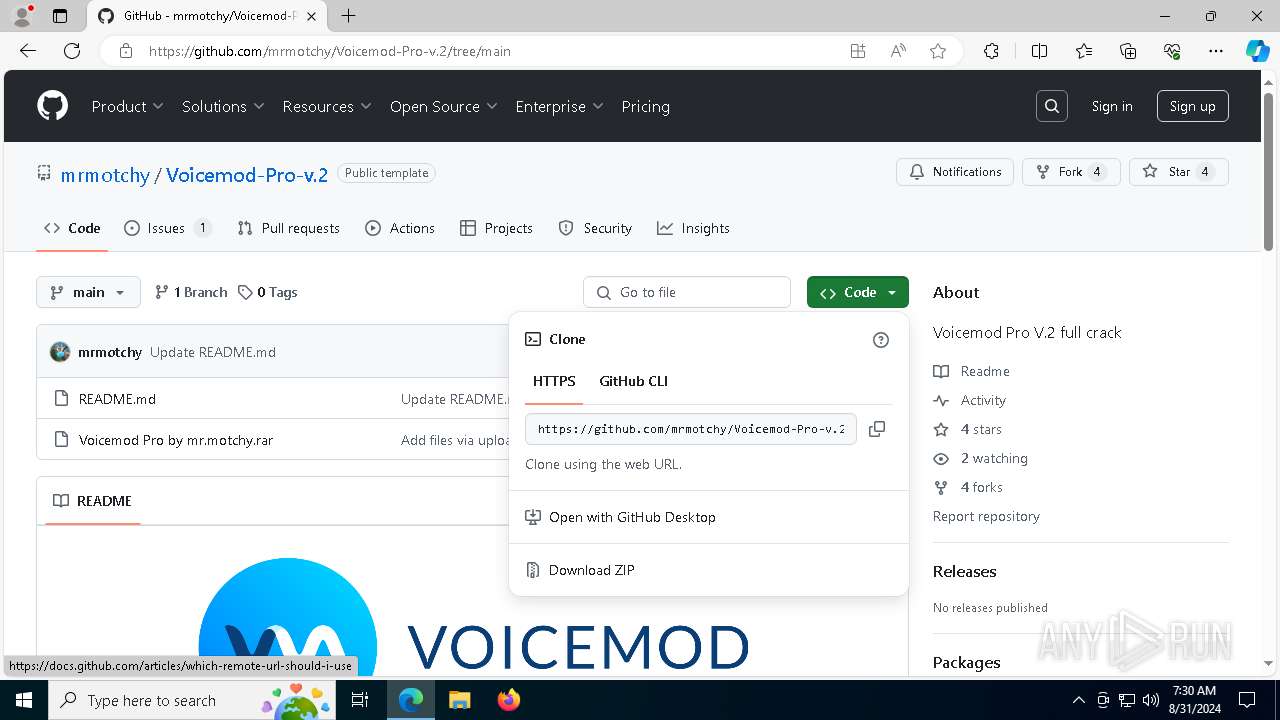
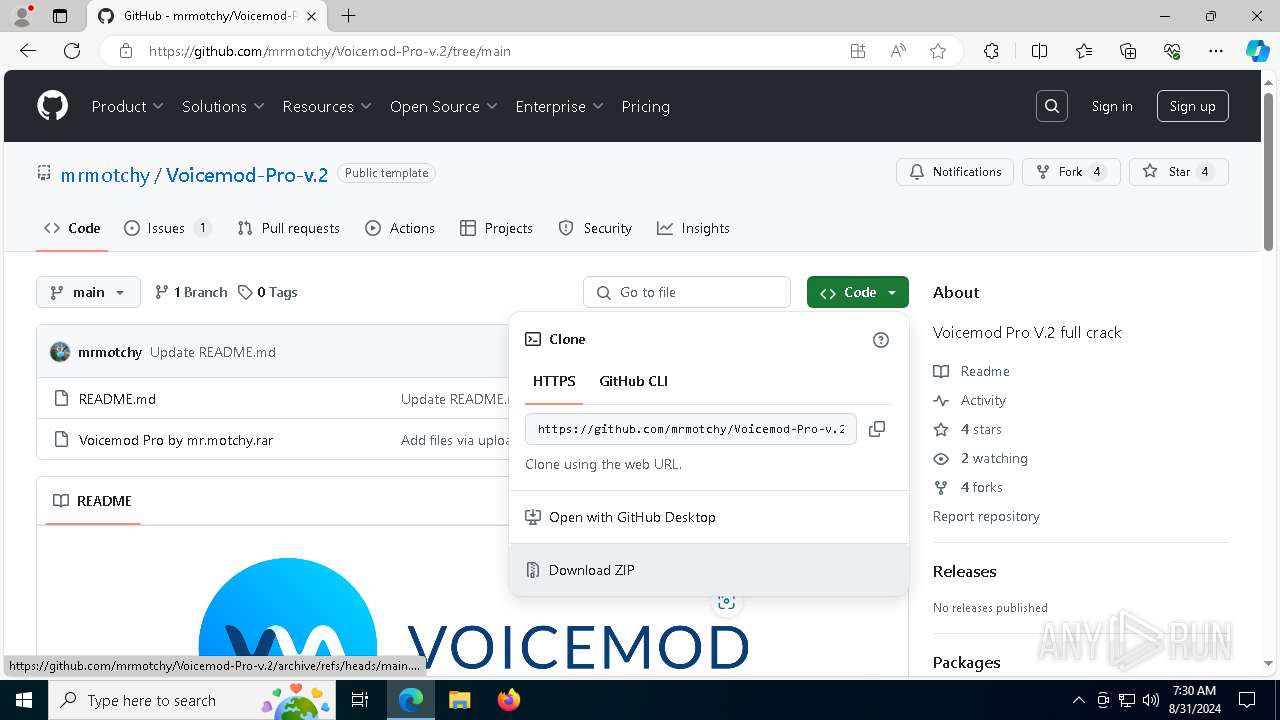
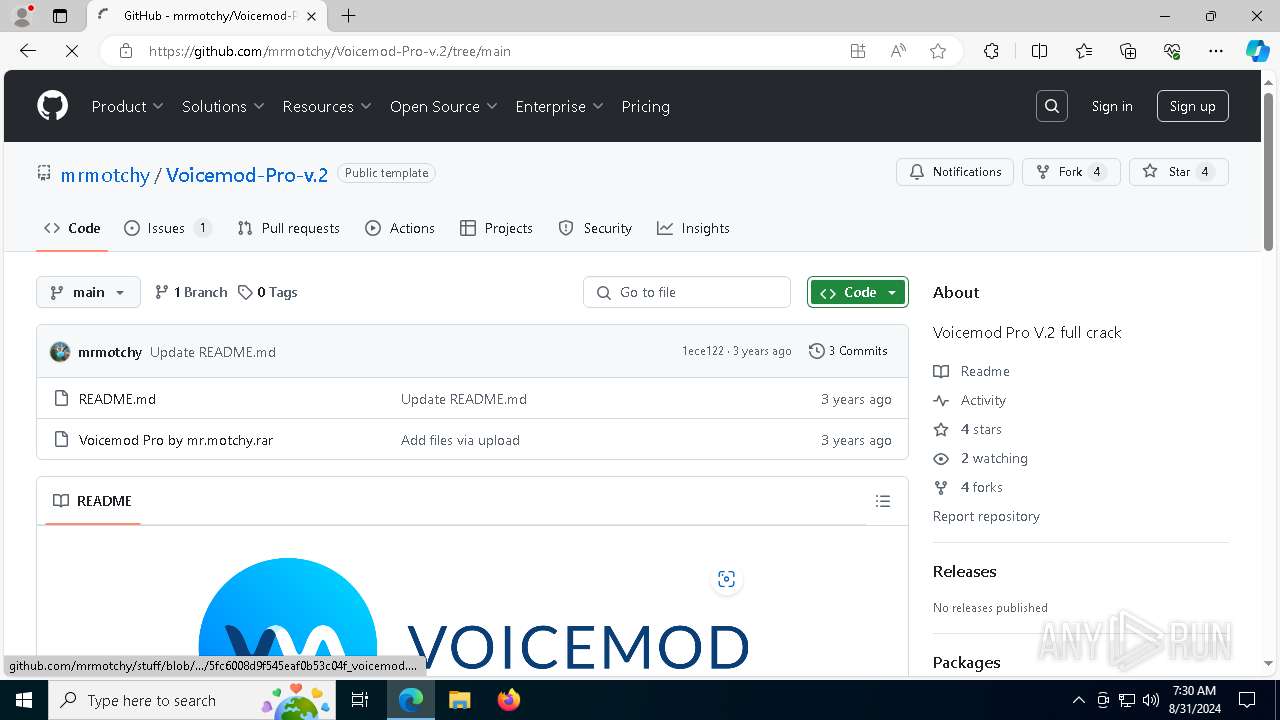
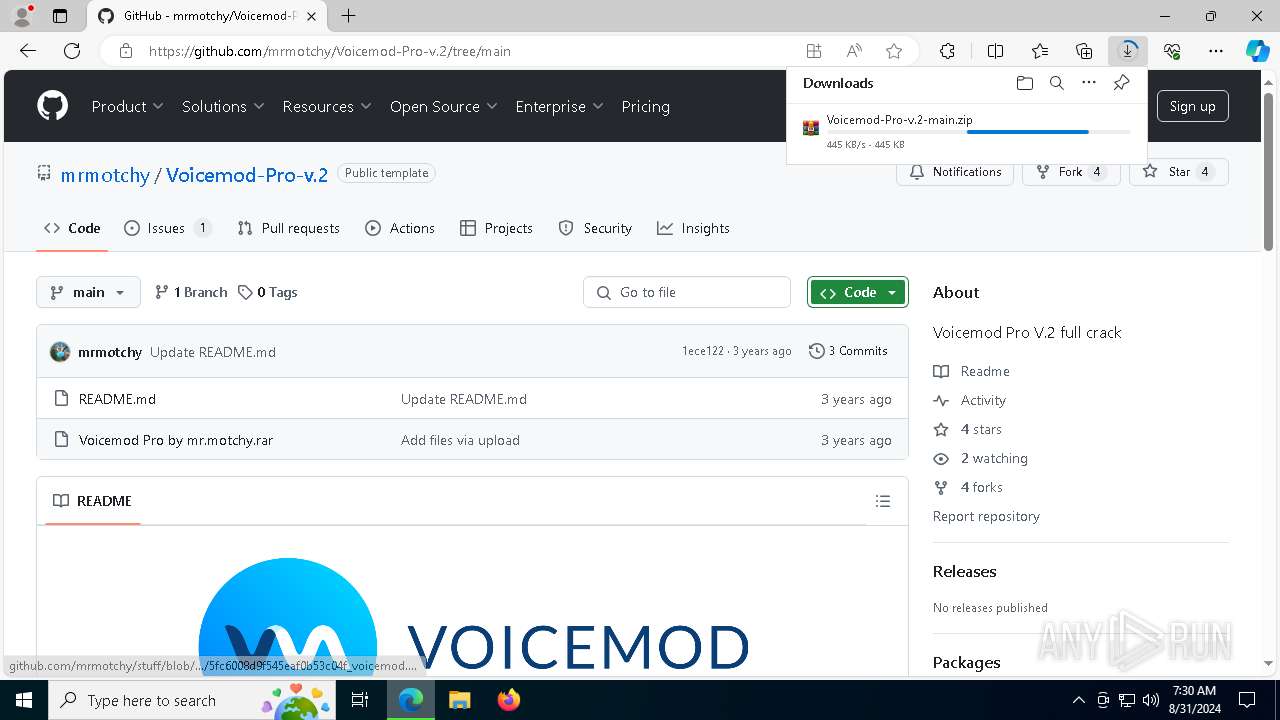
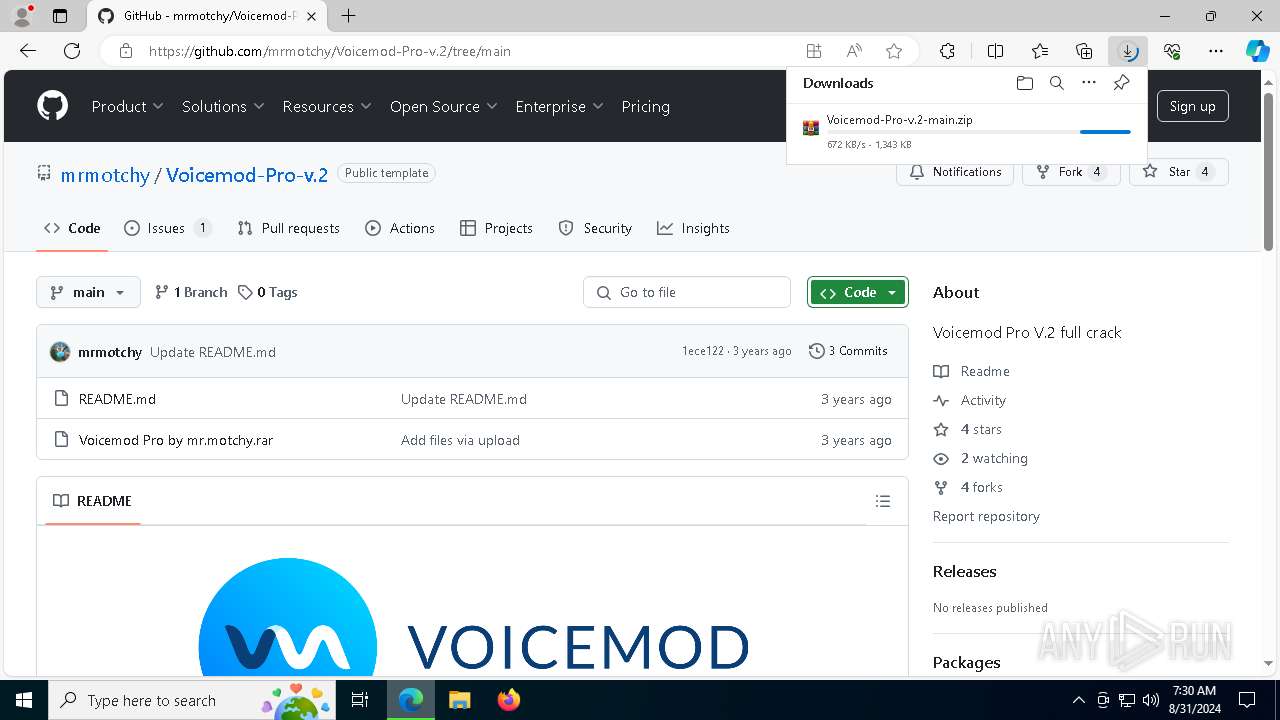
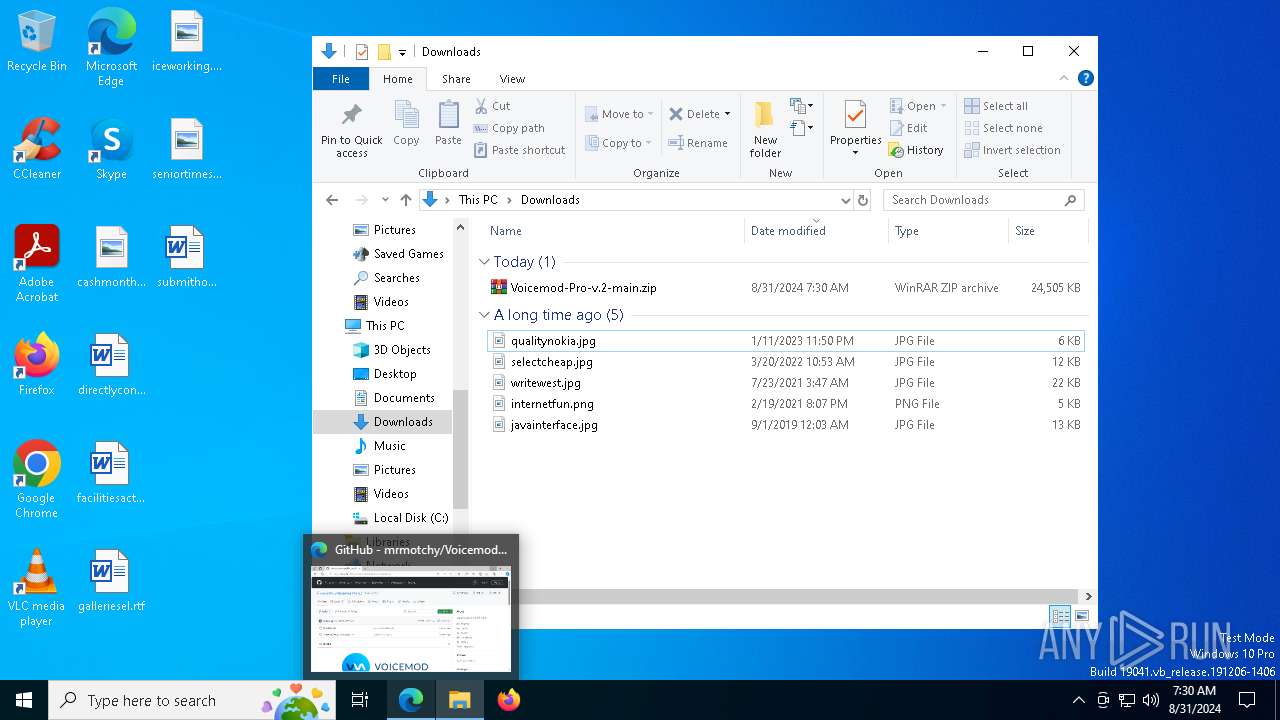
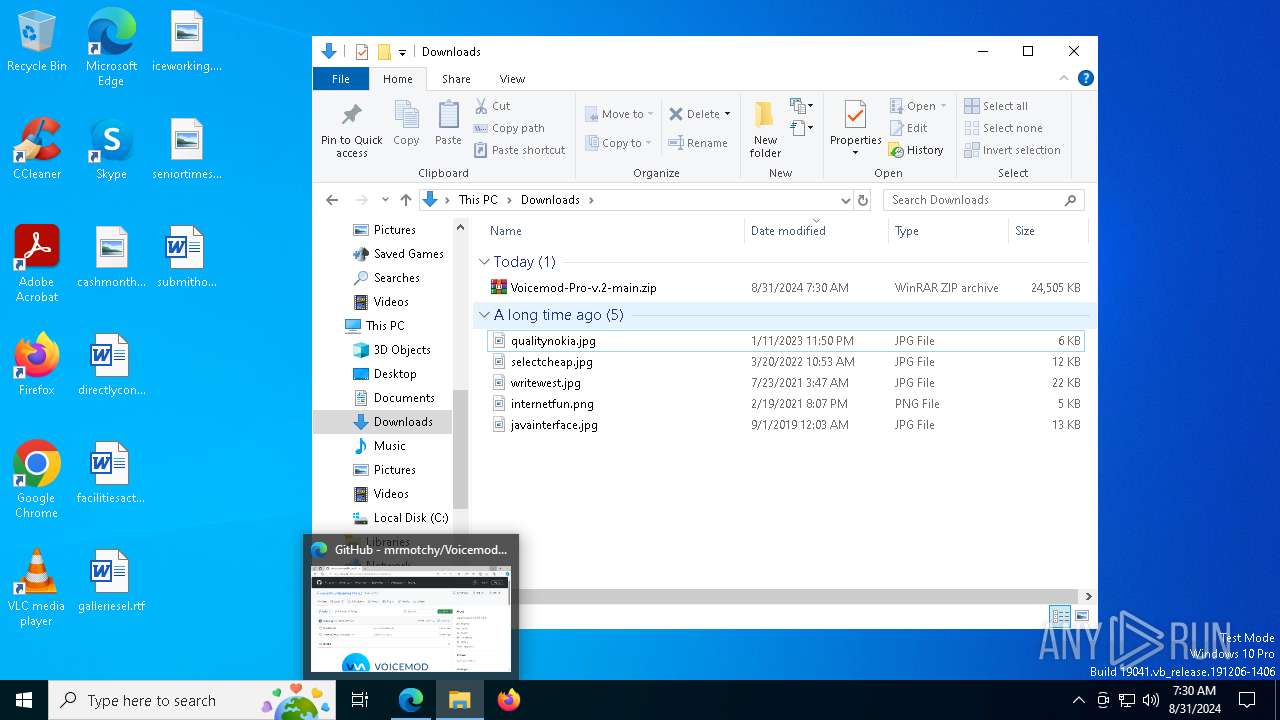
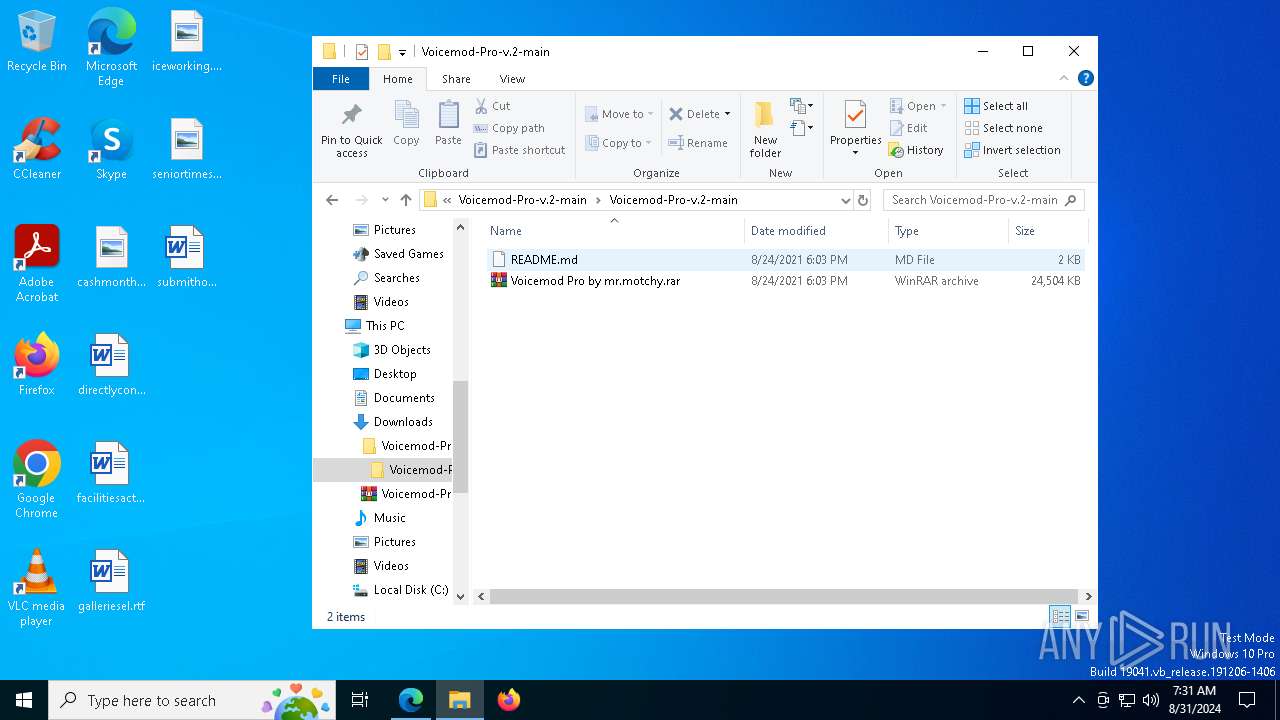
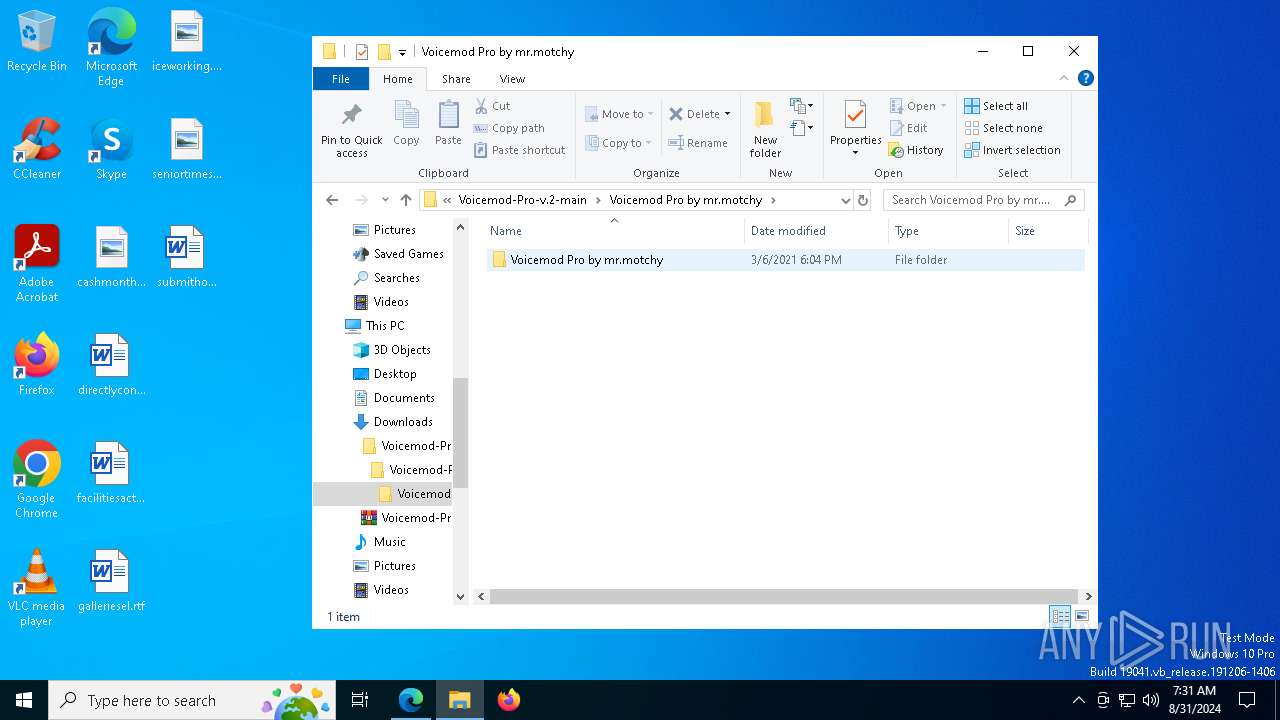
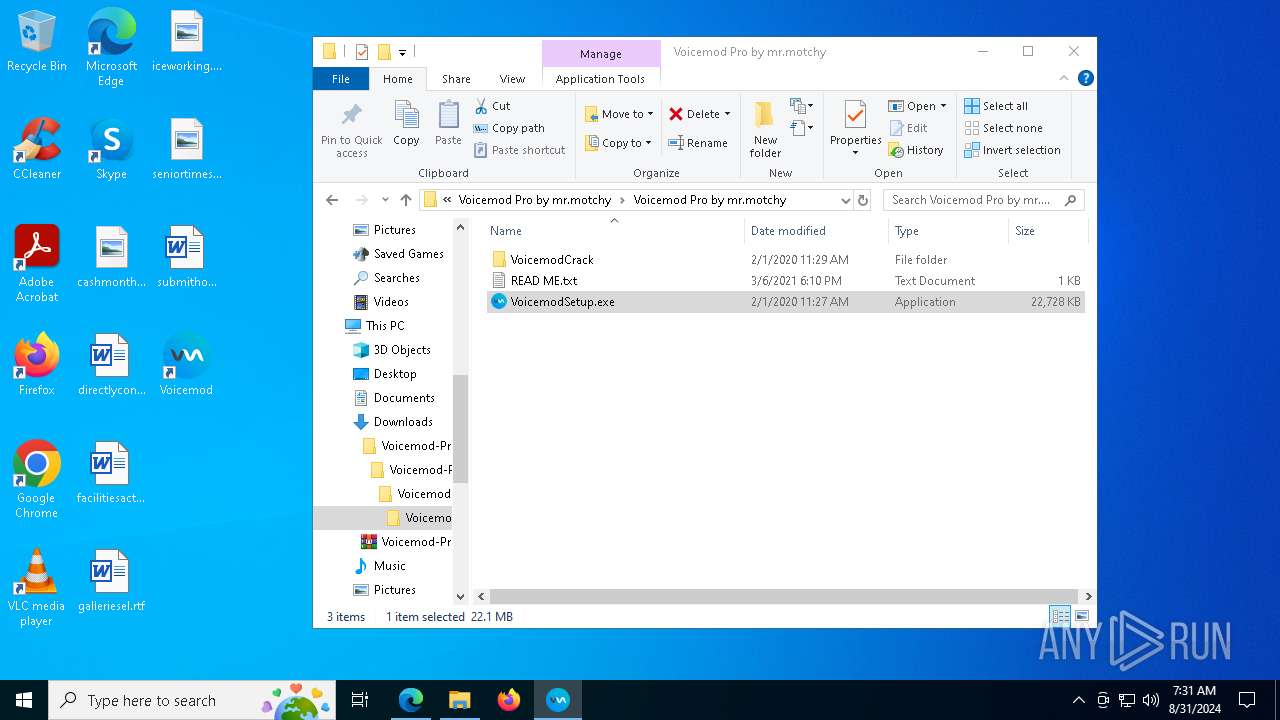
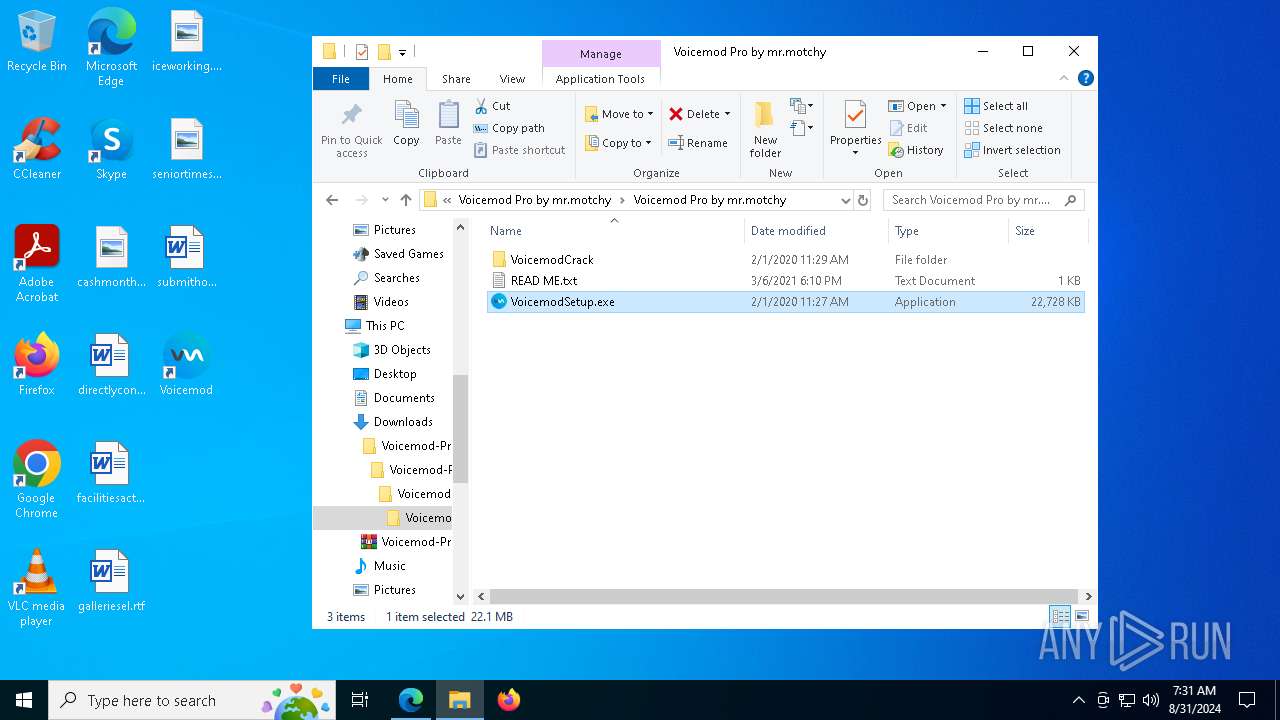
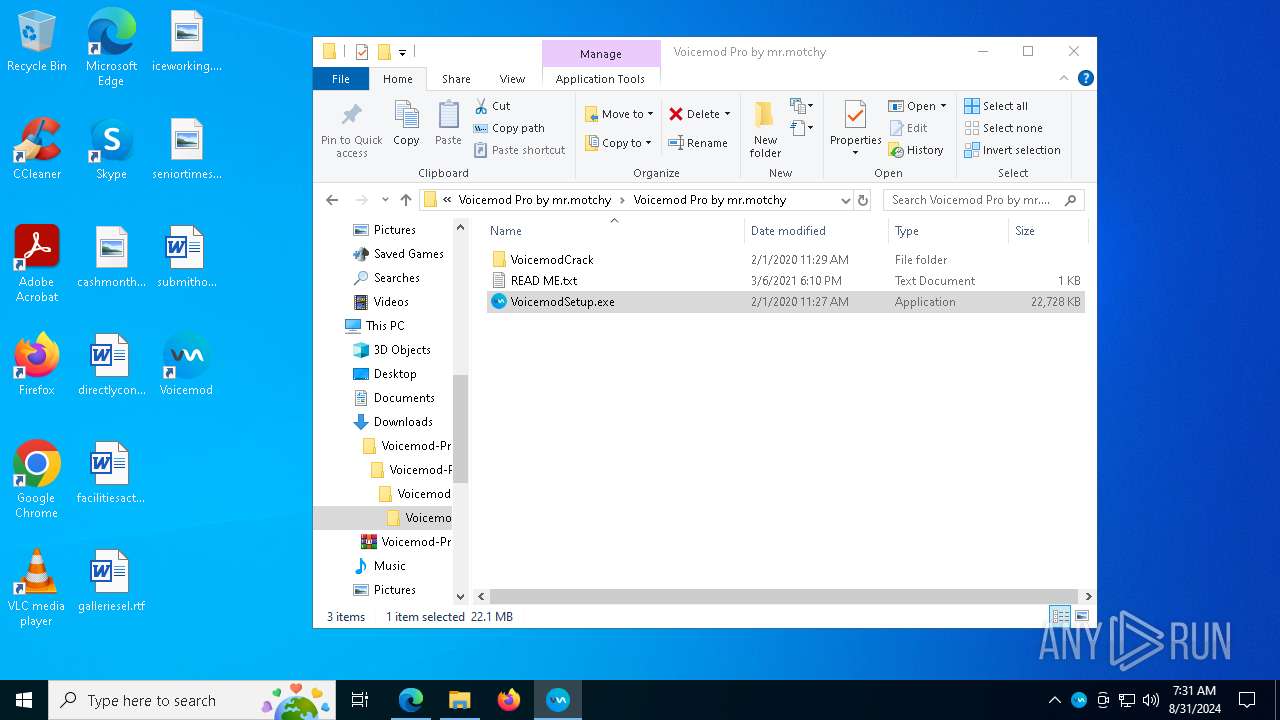
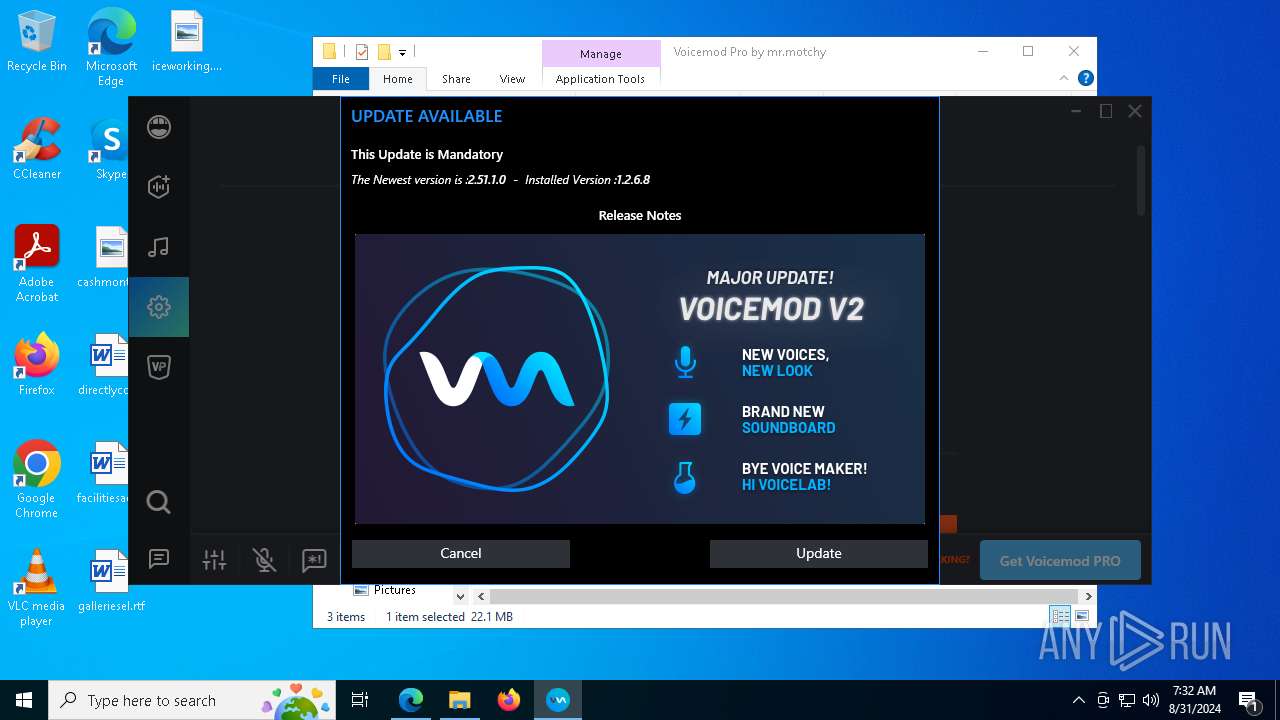
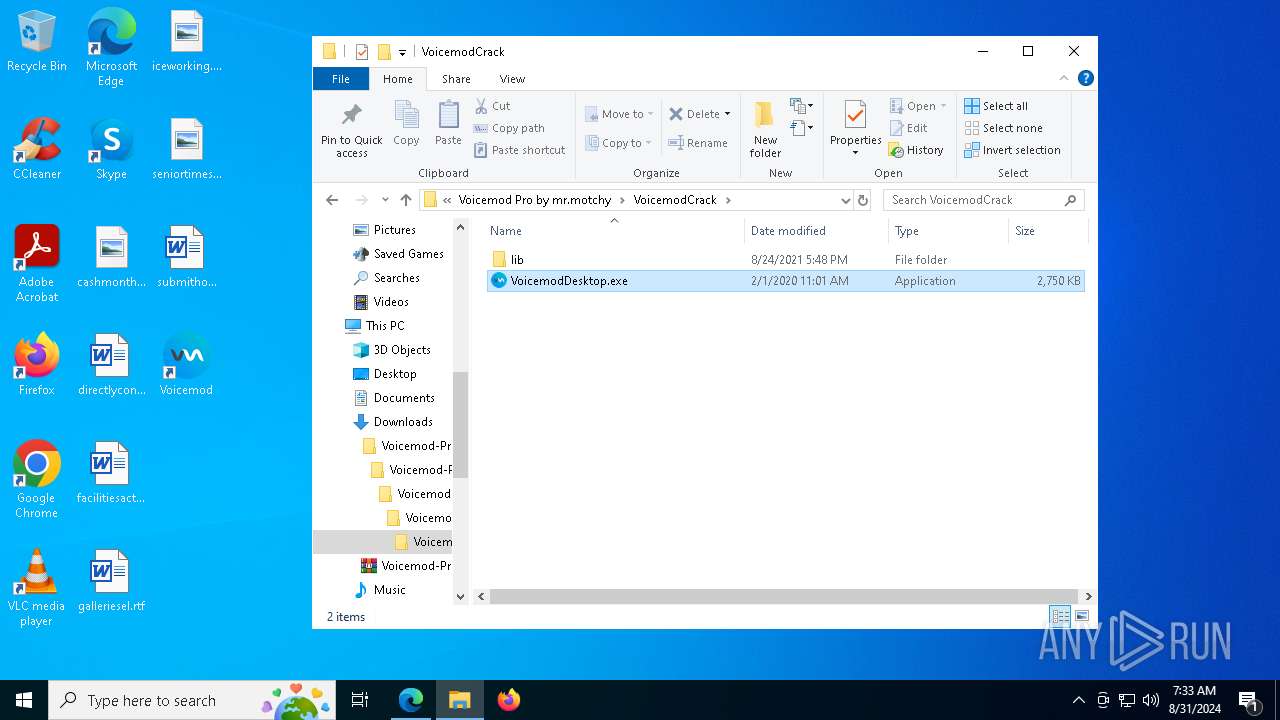
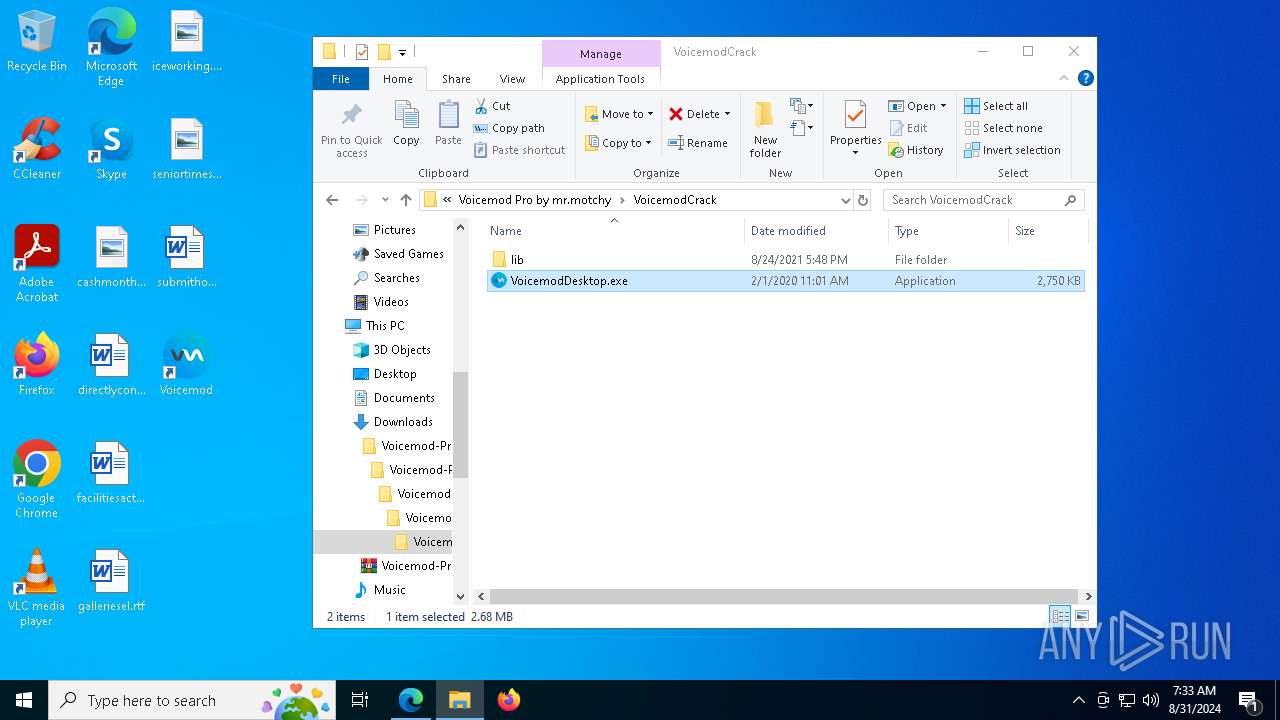
| URL: | https://github.com/mrmotchy/Voicemod-Pro-v.2/blame/main/Voicemod%20Pro%20by%20mr.motchy.rar |
| Full analysis: | https://app.any.run/tasks/952abc98-7be5-49f5-ae35-b9eaec2f224d |
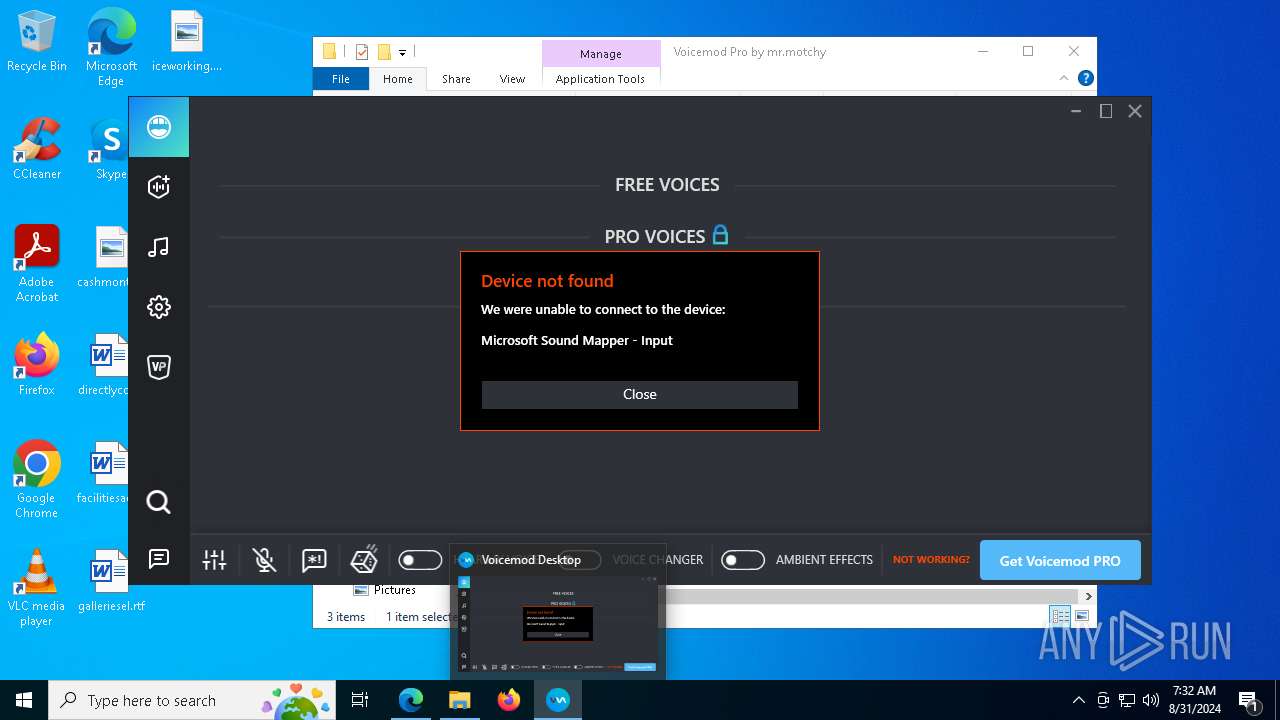
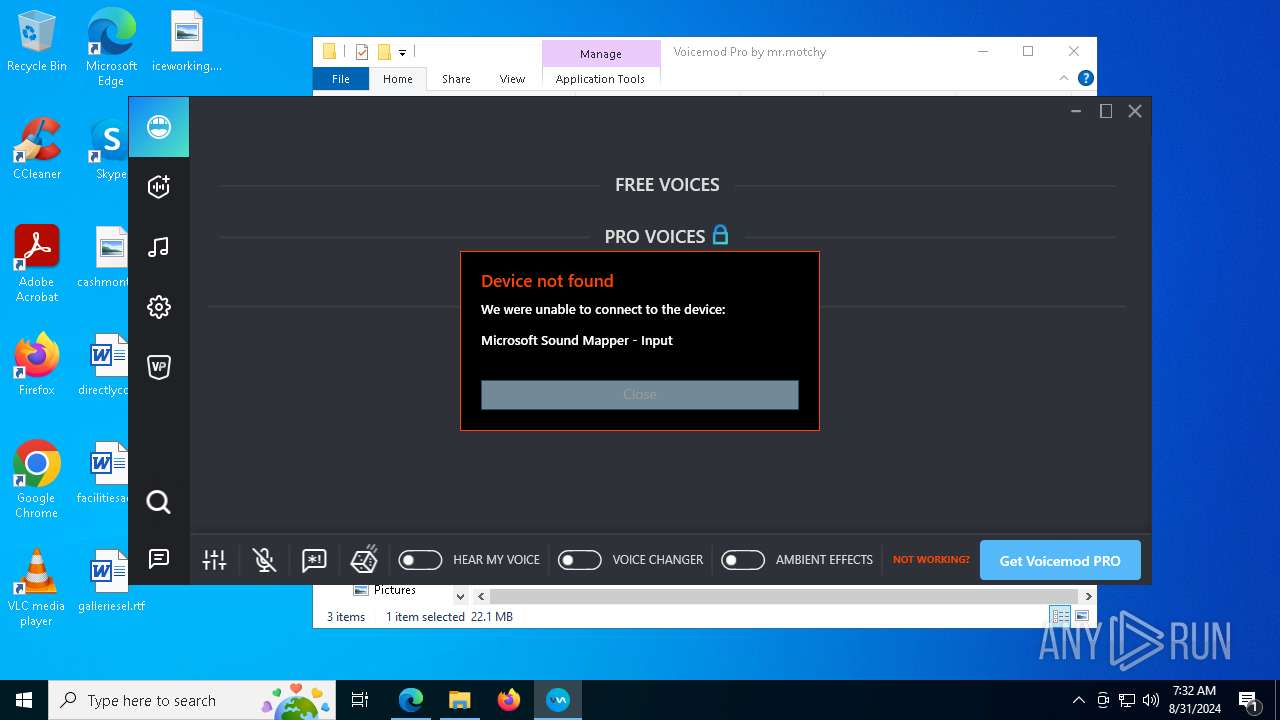
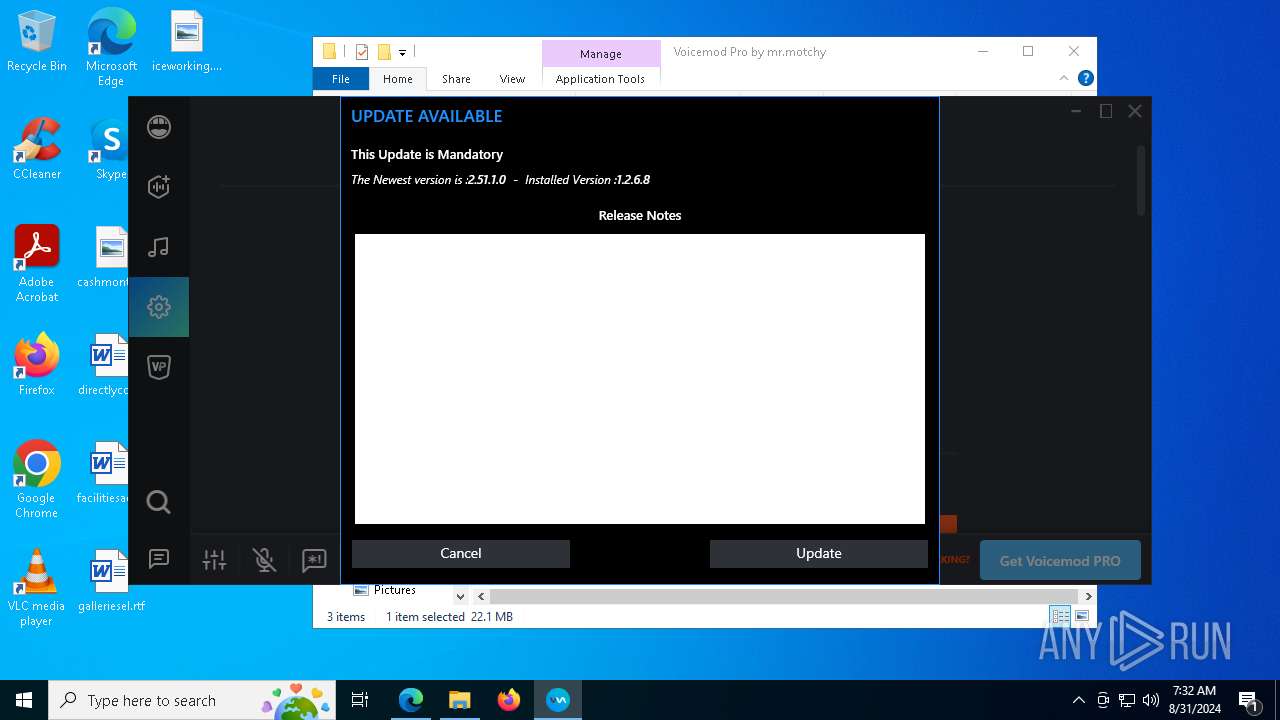
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2024, 07:30:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 16B1298E8F4A3ECB2730FEDC4555488F |
| SHA1: | 86E9621C2E435B036496A03C8888BBC4B0081A92 |
| SHA256: | CC0123E13E58BF166A88CB73A6EB0E880FD6BC3A48511E17A64E77F7A7D26869 |
| SSDEEP: | 3:N8tEd4YKsnBqTsJhATs7G4BiLXtzw3RGz:2uuY/BqLTsN2tzwo |
MALICIOUS
Changes the autorun value in the registry
- VoicemodSetup.tmp (PID: 1172)
Scans artifacts that could help determine the target
- VoicemodDesktop.exe (PID: 4760)
SUSPICIOUS
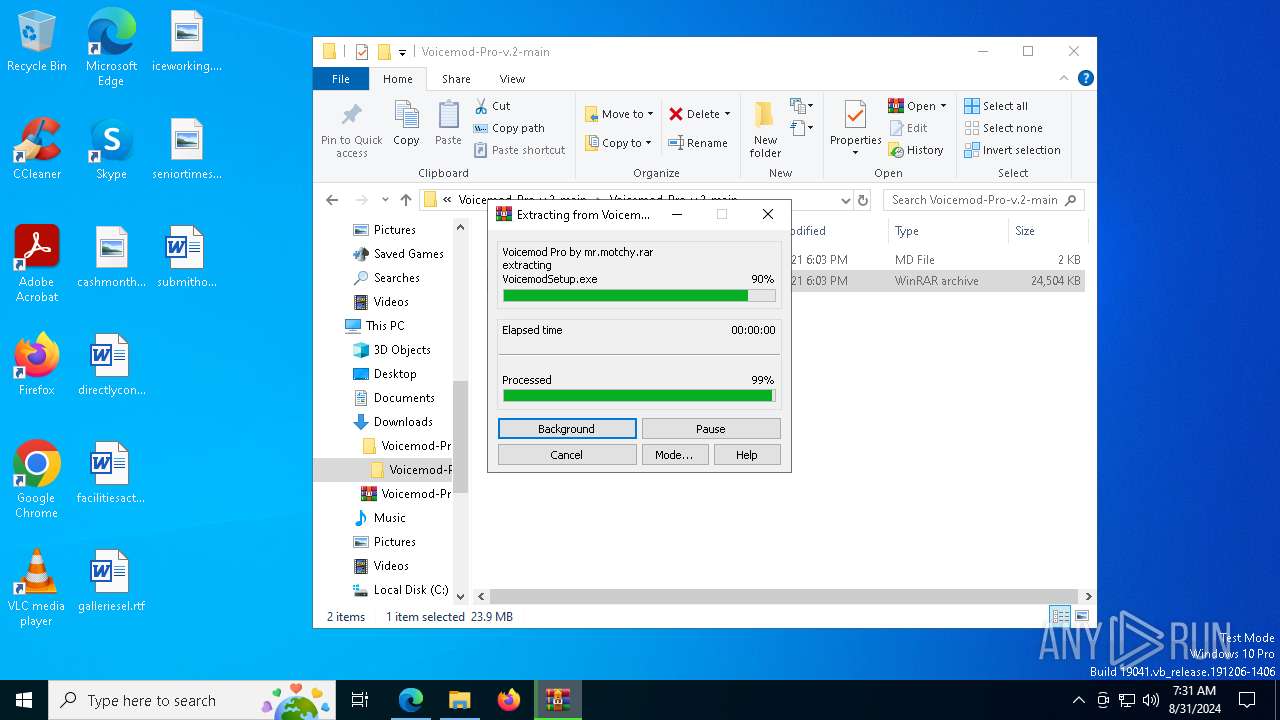
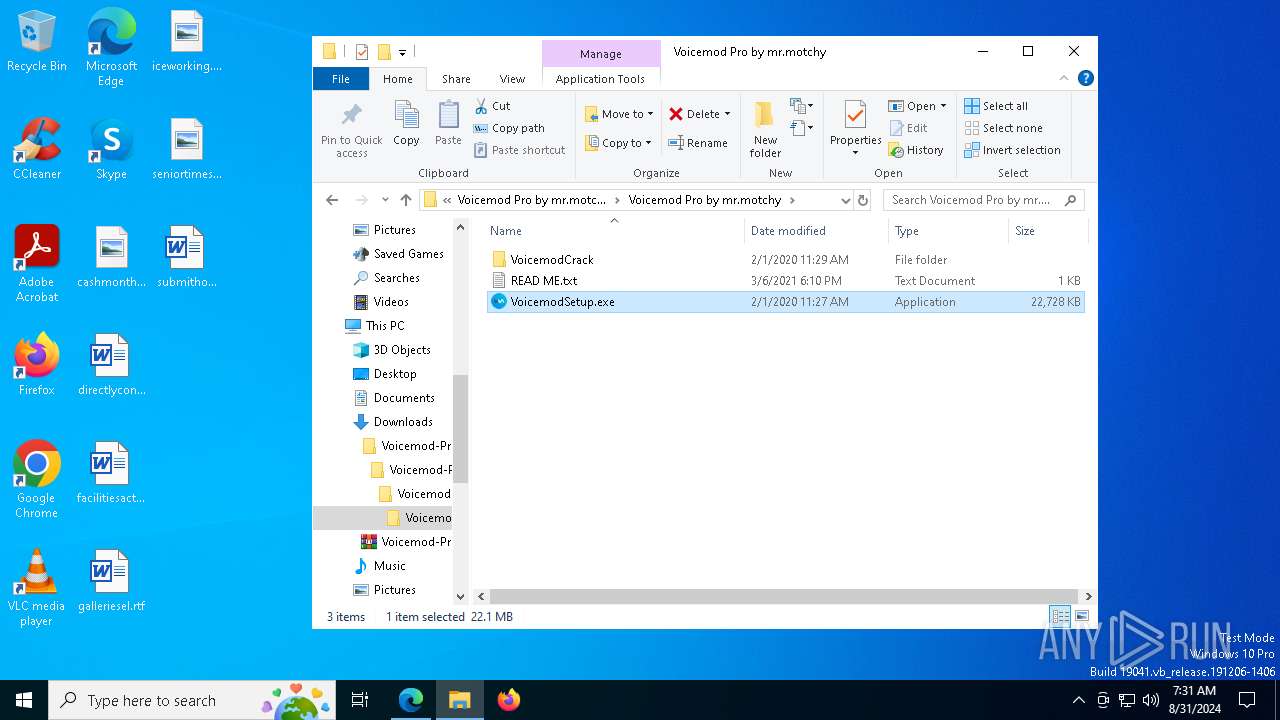
Executable content was dropped or overwritten
- VoicemodSetup.exe (PID: 7296)
- VoicemodSetup.exe (PID: 1148)
- VoicemodSetup.tmp (PID: 1172)
- vc_redist.x64.exe (PID: 7636)
- vc_redist.x86.exe (PID: 5140)
- vc_redist.x64.exe (PID: 7660)
- vc_redist.x86.exe (PID: 7740)
- devcon.exe (PID: 7904)
- drvinst.exe (PID: 3328)
- drvinst.exe (PID: 6212)
- drvinst.exe (PID: 7184)
- VoicemodDesktop.exe (PID: 4760)
Drops the executable file immediately after the start
- VoicemodSetup.exe (PID: 7296)
- VoicemodSetup.exe (PID: 1148)
- VoicemodSetup.tmp (PID: 1172)
- vc_redist.x64.exe (PID: 7636)
- vc_redist.x64.exe (PID: 7660)
- vc_redist.x86.exe (PID: 5140)
- vc_redist.x86.exe (PID: 7740)
- devcon.exe (PID: 7904)
- drvinst.exe (PID: 3328)
- drvinst.exe (PID: 7184)
- drvinst.exe (PID: 6212)
- VoicemodDesktop.exe (PID: 4760)
Reads security settings of Internet Explorer
- VoicemodSetup.tmp (PID: 6244)
- VoicemodSetup.tmp (PID: 1172)
- devcon.exe (PID: 7904)
- VoicemodDesktop.exe (PID: 4760)
- ShellExperienceHost.exe (PID: 6272)
Reads the date of Windows installation
- VoicemodSetup.tmp (PID: 6244)
Reads the Windows owner or organization settings
- VoicemodSetup.tmp (PID: 1172)
Checks Windows Trust Settings
- VoicemodSetup.tmp (PID: 1172)
- devcon.exe (PID: 7904)
- drvinst.exe (PID: 3328)
- VoicemodDesktop.exe (PID: 4760)
Process drops legitimate windows executable
- VoicemodSetup.tmp (PID: 1172)
- vc_redist.x64.exe (PID: 7660)
- vc_redist.x86.exe (PID: 5140)
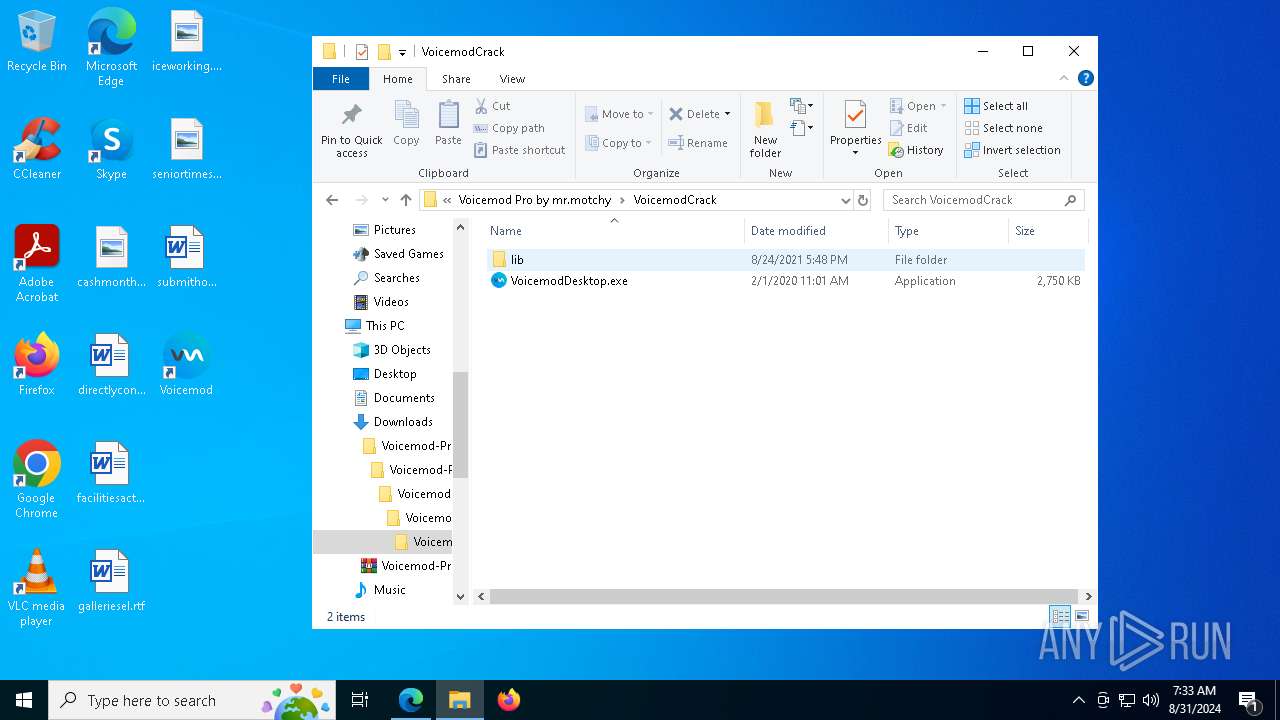
Drops a system driver (possible attempt to evade defenses)
- VoicemodSetup.tmp (PID: 1172)
- devcon.exe (PID: 7904)
- drvinst.exe (PID: 3328)
- drvinst.exe (PID: 6212)
Starts a Microsoft application from unusual location
- vc_redist.x64.exe (PID: 7636)
- vc_redist.x64.exe (PID: 7660)
- vc_redist.x86.exe (PID: 5140)
- vc_redist.x86.exe (PID: 7740)
Searches for installed software
- vc_redist.x64.exe (PID: 7636)
- vc_redist.x86.exe (PID: 7740)
Executing commands from a ".bat" file
- VoicemodSetup.tmp (PID: 1172)
Starts CMD.EXE for commands execution
- VoicemodSetup.tmp (PID: 1172)
- cmd.exe (PID: 3672)
- VoicemodDesktop.exe (PID: 4760)
Application launched itself
- cmd.exe (PID: 3672)
Creates files in the driver directory
- drvinst.exe (PID: 3328)
- drvinst.exe (PID: 6212)
- drvinst.exe (PID: 7184)
The process checks if it is being run in the virtual environment
- drvinst.exe (PID: 6212)
Creates or modifies Windows services
- drvinst.exe (PID: 6212)
- drvinst.exe (PID: 7184)
Reads Internet Explorer settings
- VoicemodDesktop.exe (PID: 4760)
Executes application which crashes
- VoicemodDesktop.exe (PID: 8144)
Reads Microsoft Outlook installation path
- VoicemodDesktop.exe (PID: 4760)
INFO
Checks supported languages
- identity_helper.exe (PID: 2612)
- VoicemodSetup.exe (PID: 7296)
- VoicemodSetup.tmp (PID: 6244)
- VoicemodSetup.exe (PID: 1148)
- VoicemodSetup.tmp (PID: 1172)
- vc_redist.x64.exe (PID: 7660)
- vc_redist.x64.exe (PID: 7636)
- vc_redist.x86.exe (PID: 5140)
- SaveDefaultDevices.exe (PID: 7764)
- devcon.exe (PID: 7864)
- devcon.exe (PID: 7904)
- vc_redist.x86.exe (PID: 7740)
- drvinst.exe (PID: 3328)
- drvinst.exe (PID: 6212)
- drvinst.exe (PID: 7184)
- devcon.exe (PID: 6712)
- VoicemodDesktop.exe (PID: 4760)
- VoicemodDesktop.exe (PID: 8144)
- ShellExperienceHost.exe (PID: 6272)
Application launched itself
- msedge.exe (PID: 1288)
Reads Microsoft Office registry keys
- msedge.exe (PID: 1288)
Reads the computer name
- identity_helper.exe (PID: 2612)
- VoicemodSetup.tmp (PID: 6244)
- VoicemodSetup.tmp (PID: 1172)
- vc_redist.x64.exe (PID: 7636)
- vc_redist.x86.exe (PID: 7740)
- SaveDefaultDevices.exe (PID: 7764)
- devcon.exe (PID: 7904)
- drvinst.exe (PID: 3328)
- drvinst.exe (PID: 6212)
- drvinst.exe (PID: 7184)
- devcon.exe (PID: 6712)
- VoicemodDesktop.exe (PID: 4760)
- VoicemodDesktop.exe (PID: 8144)
- ShellExperienceHost.exe (PID: 6272)
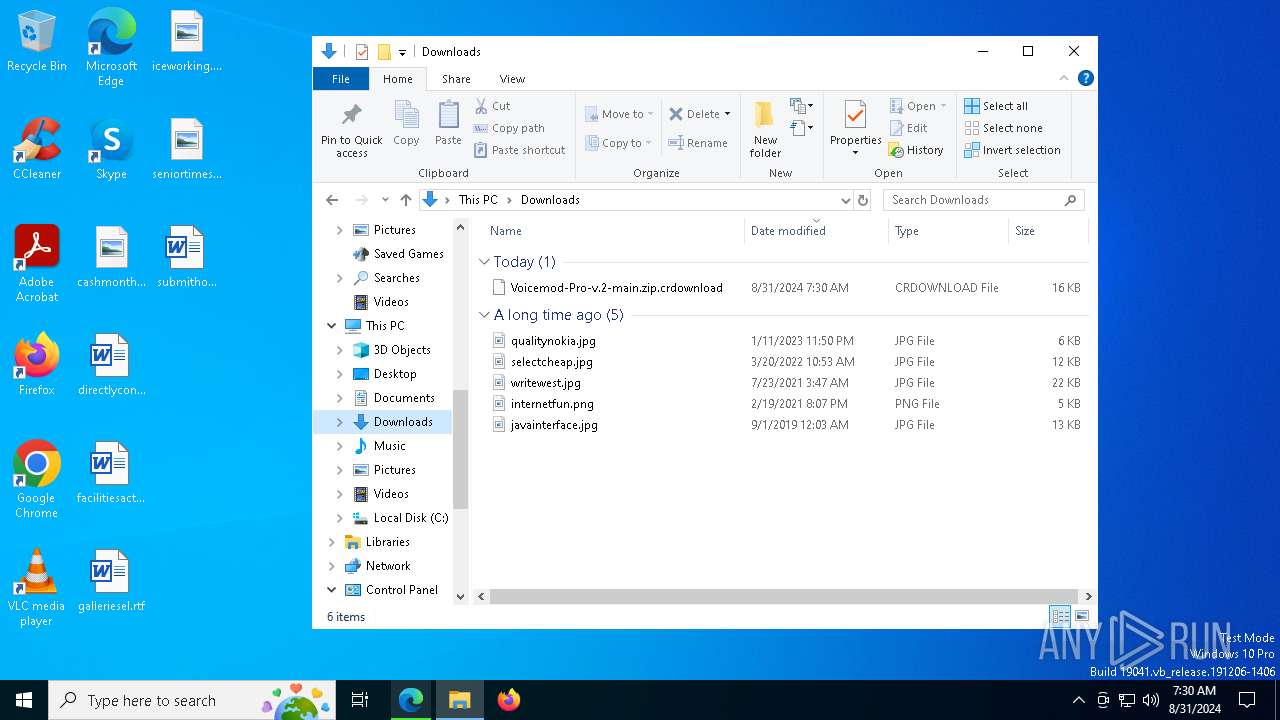
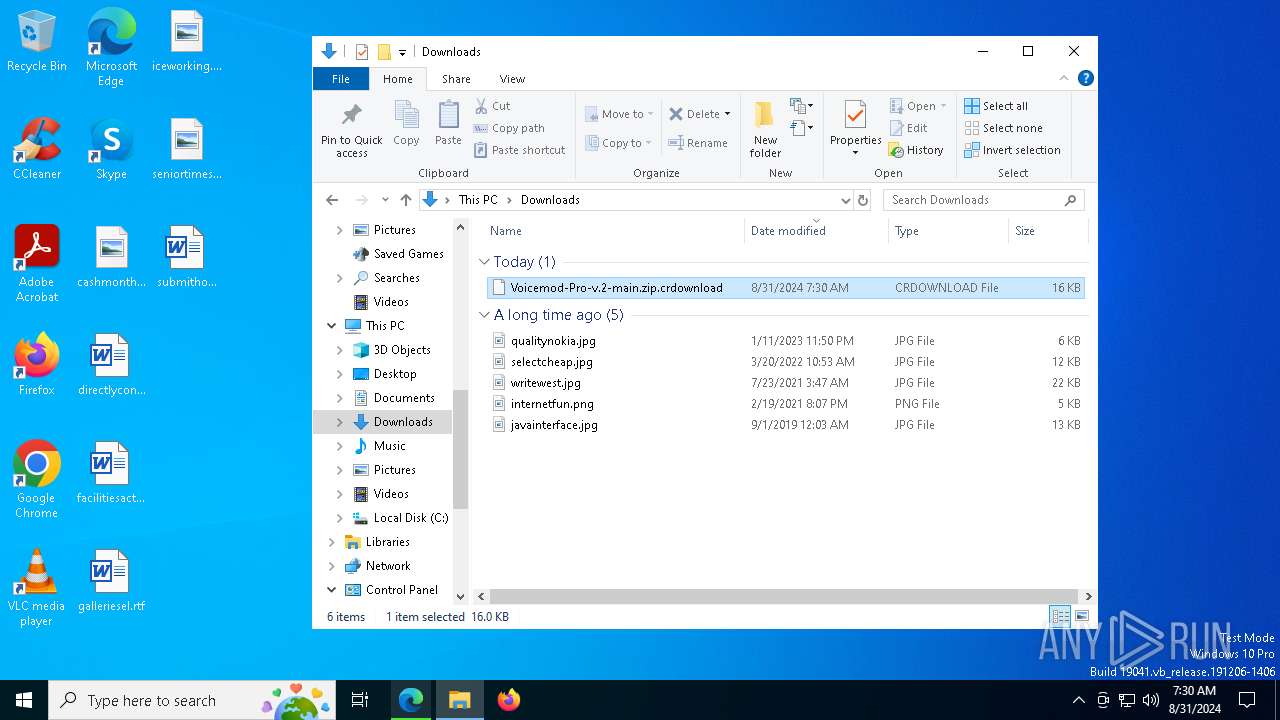
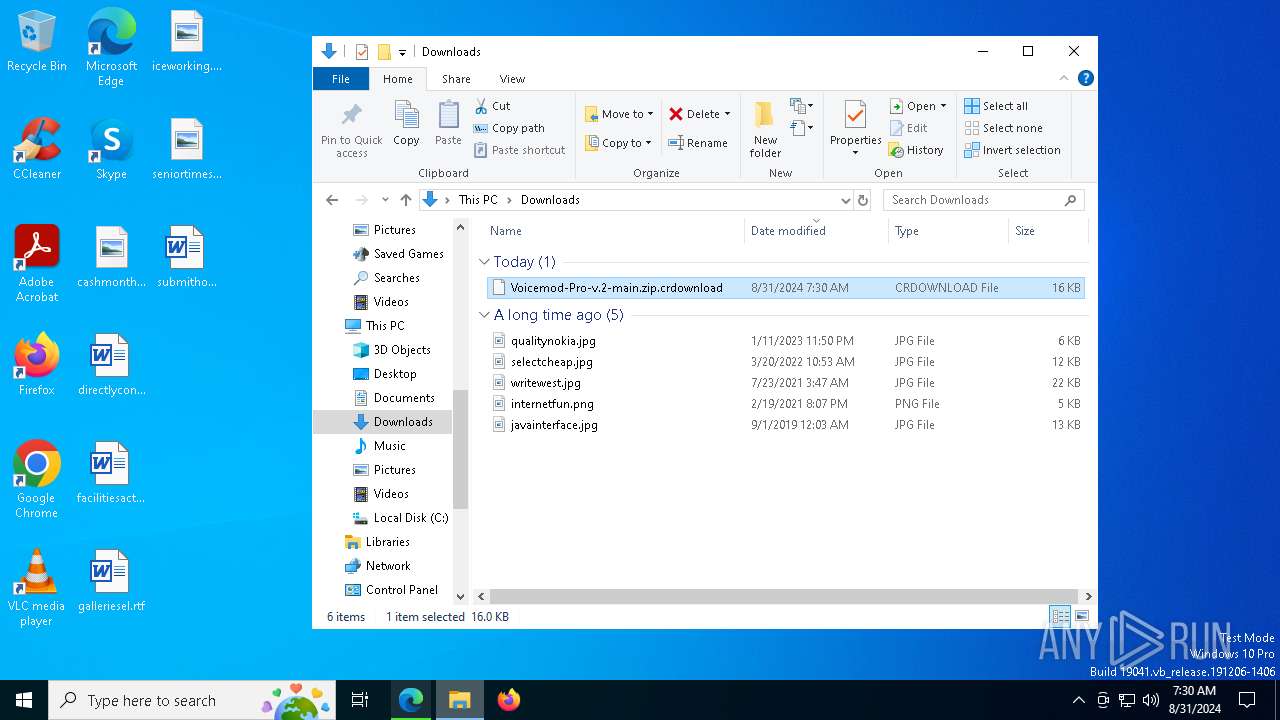
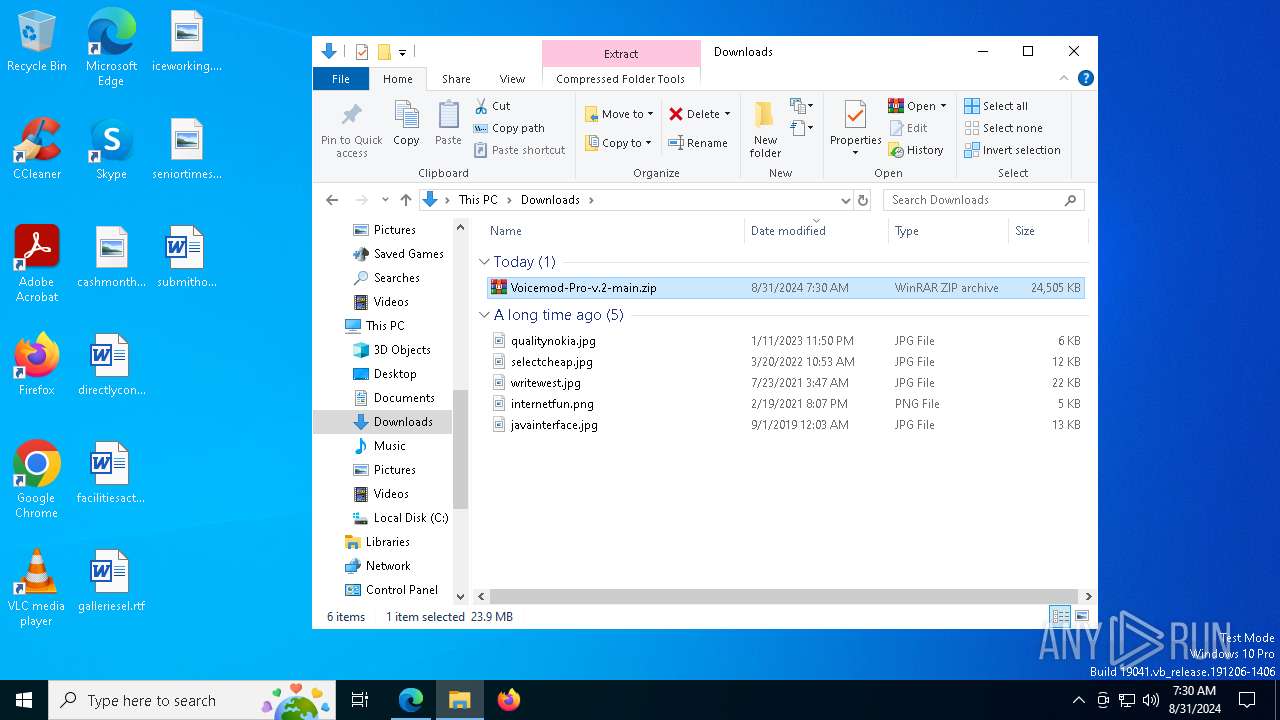
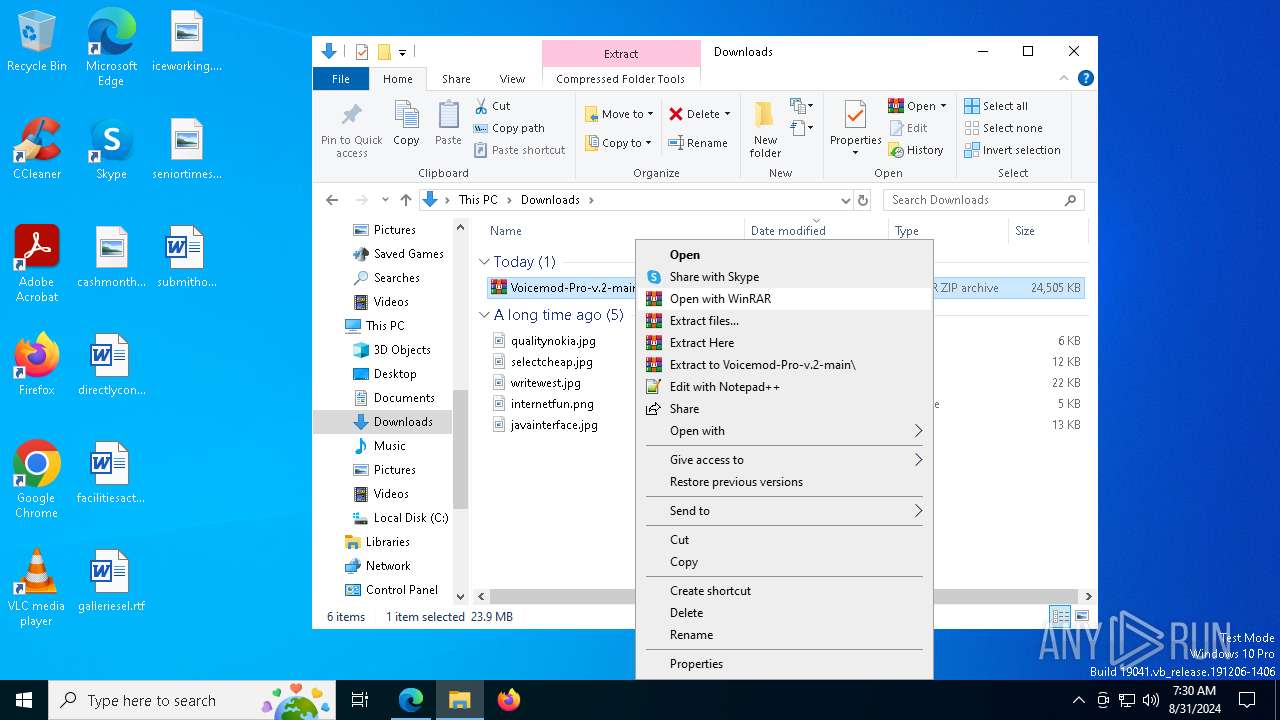
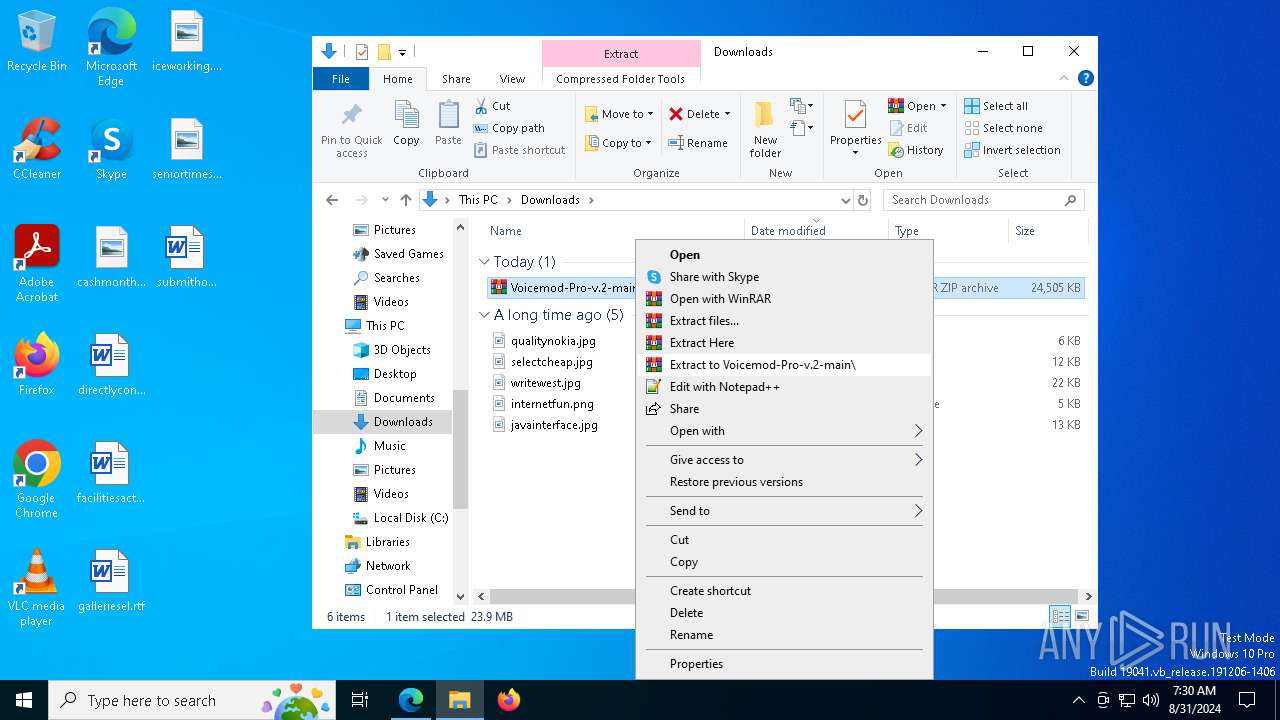
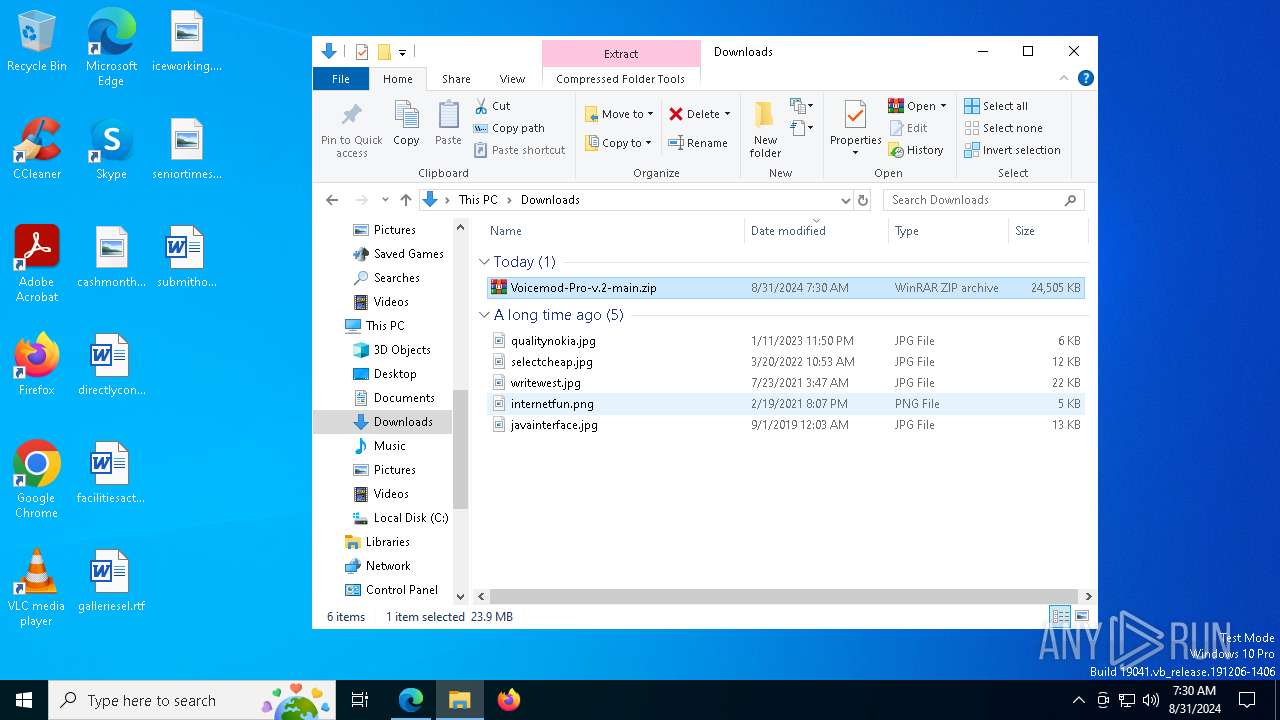
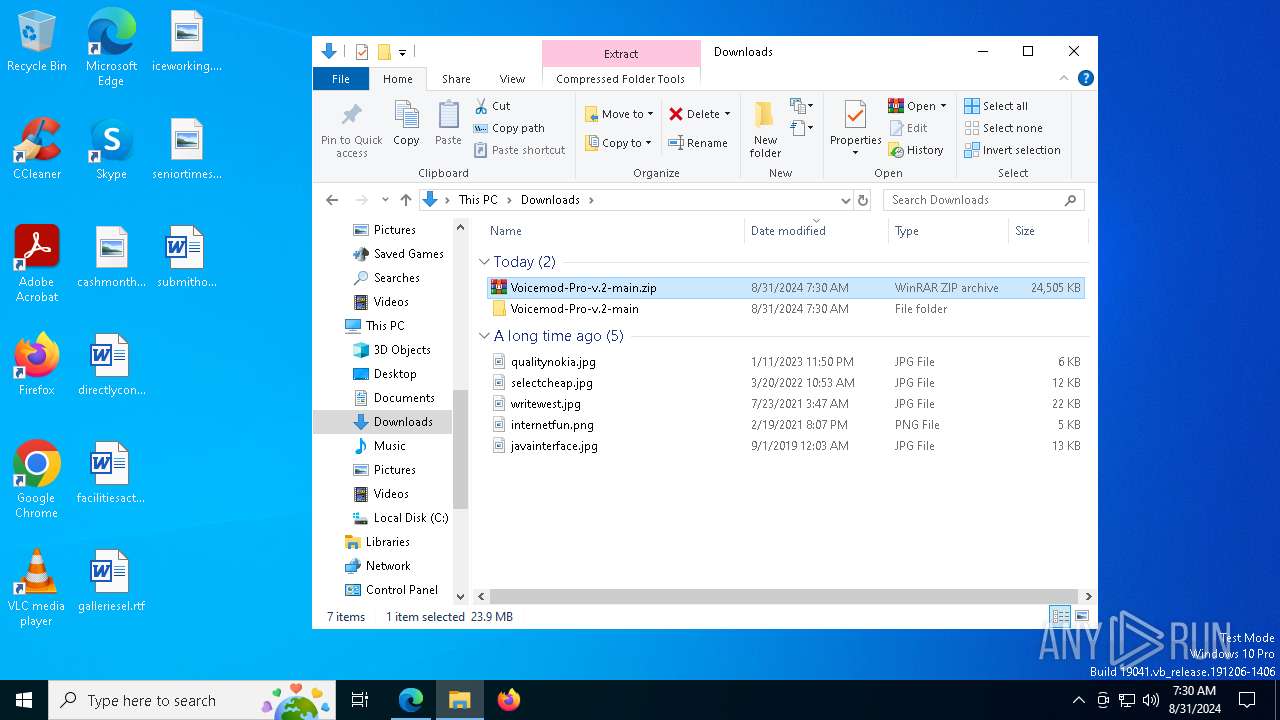
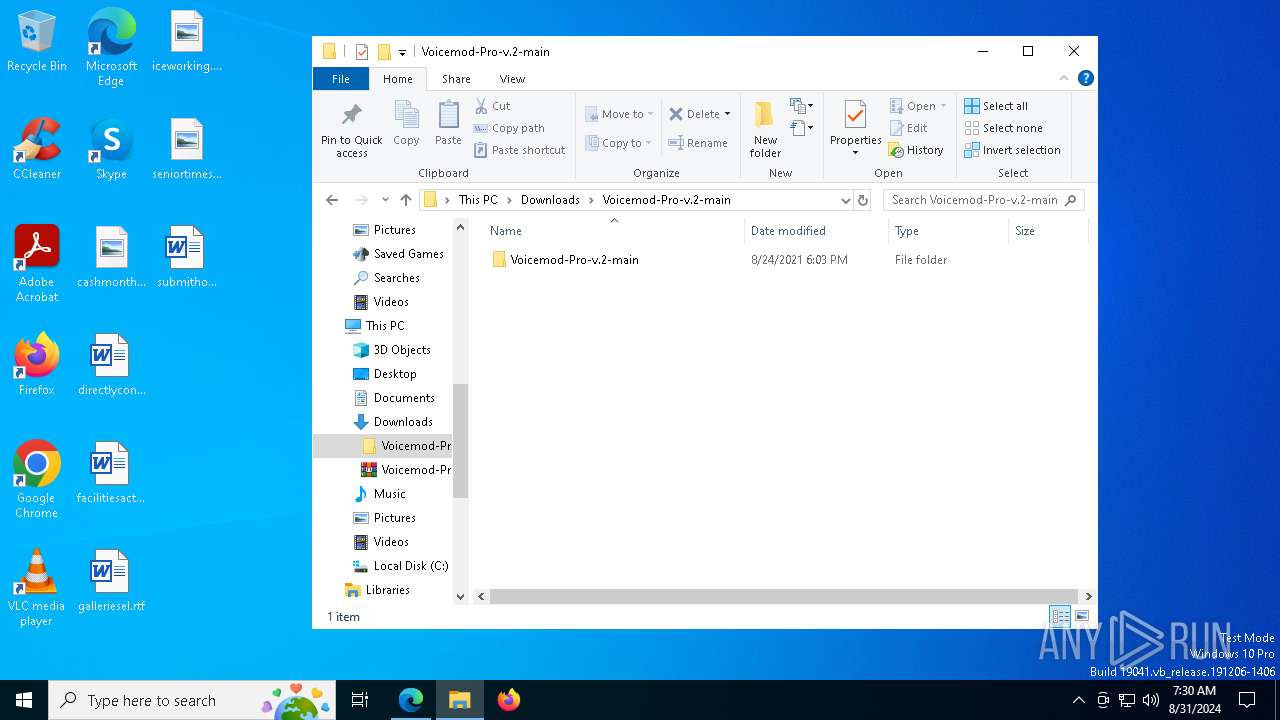
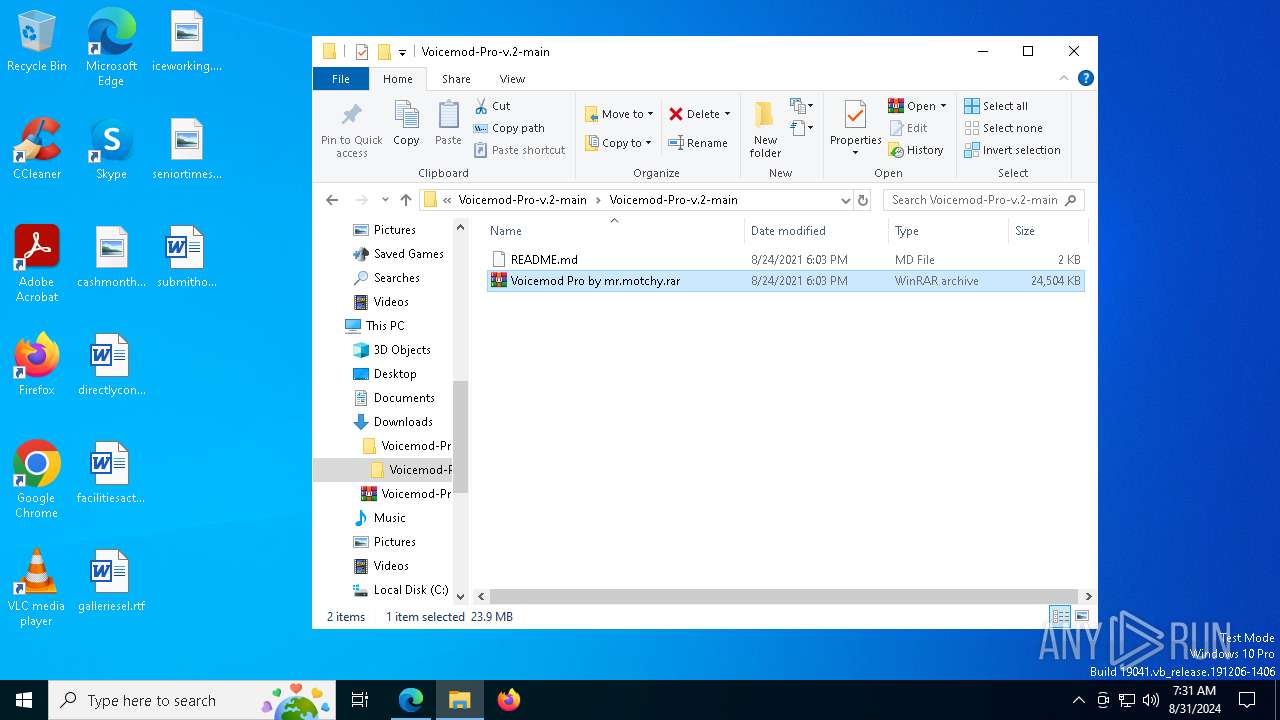
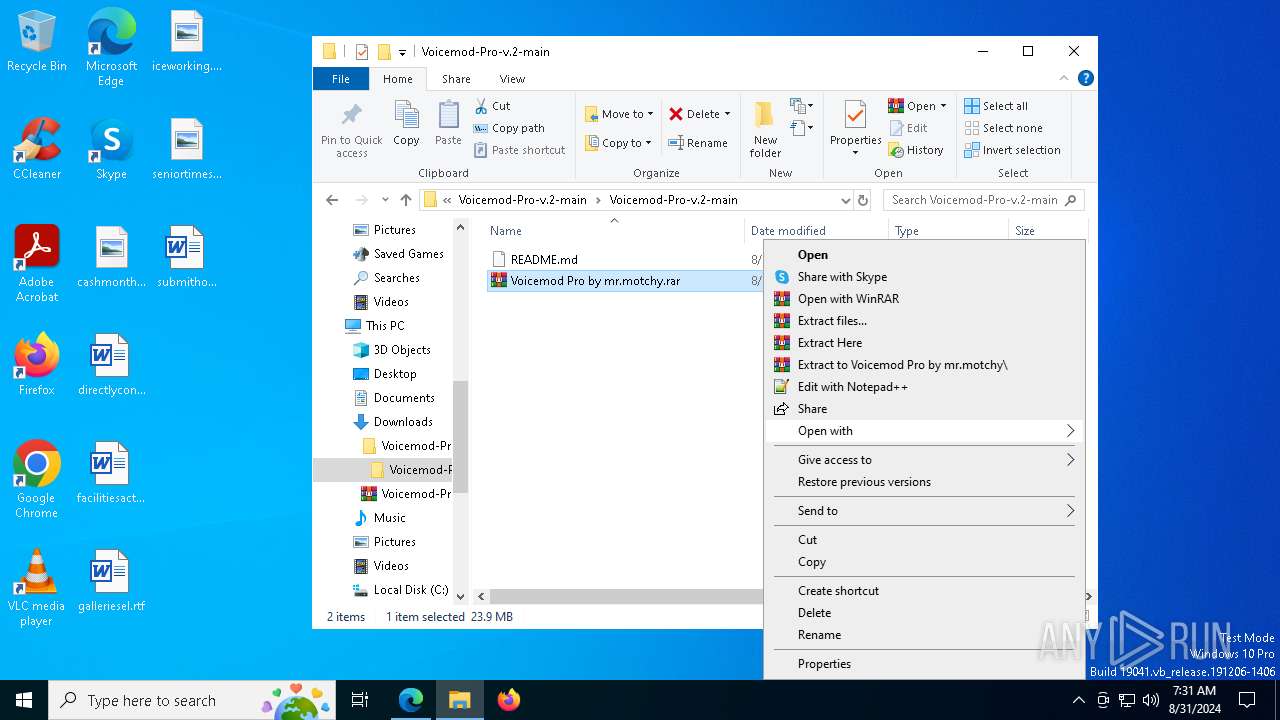
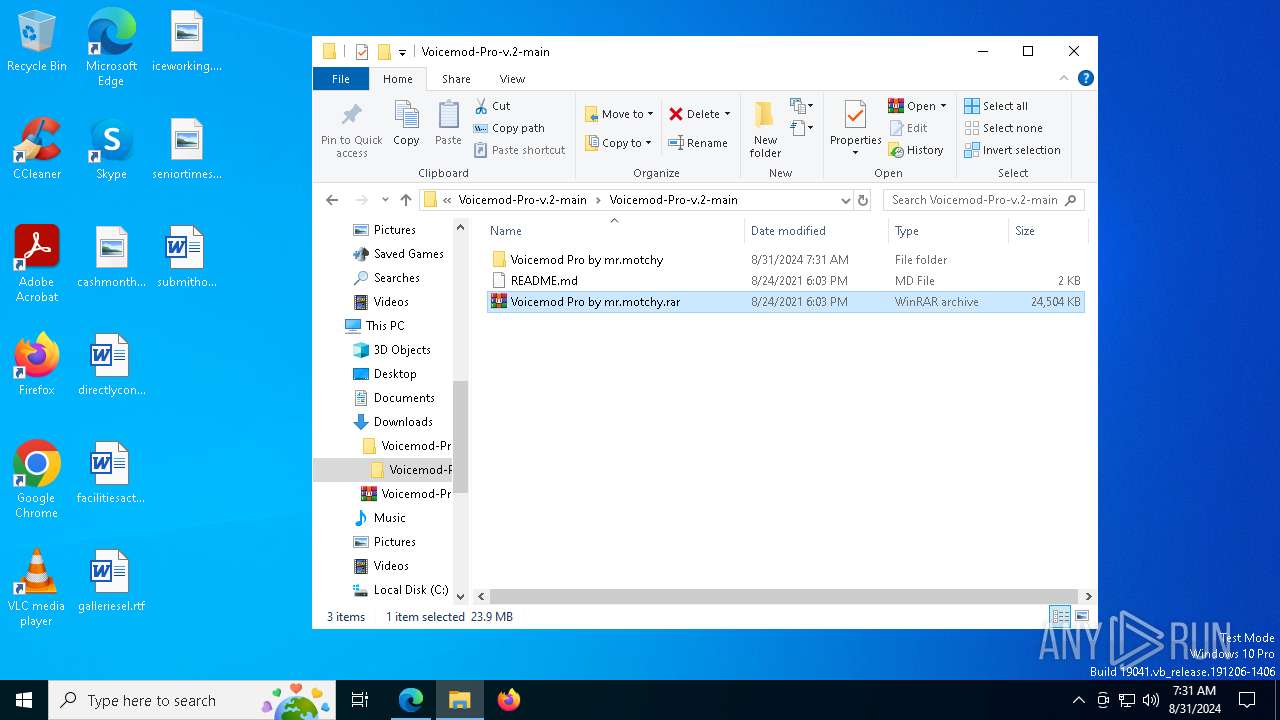
The process uses the downloaded file
- msedge.exe (PID: 7856)
- WinRAR.exe (PID: 2400)
- WinRAR.exe (PID: 7960)
- VoicemodDesktop.exe (PID: 4760)
Reads Environment values
- identity_helper.exe (PID: 2612)
- VoicemodDesktop.exe (PID: 4760)
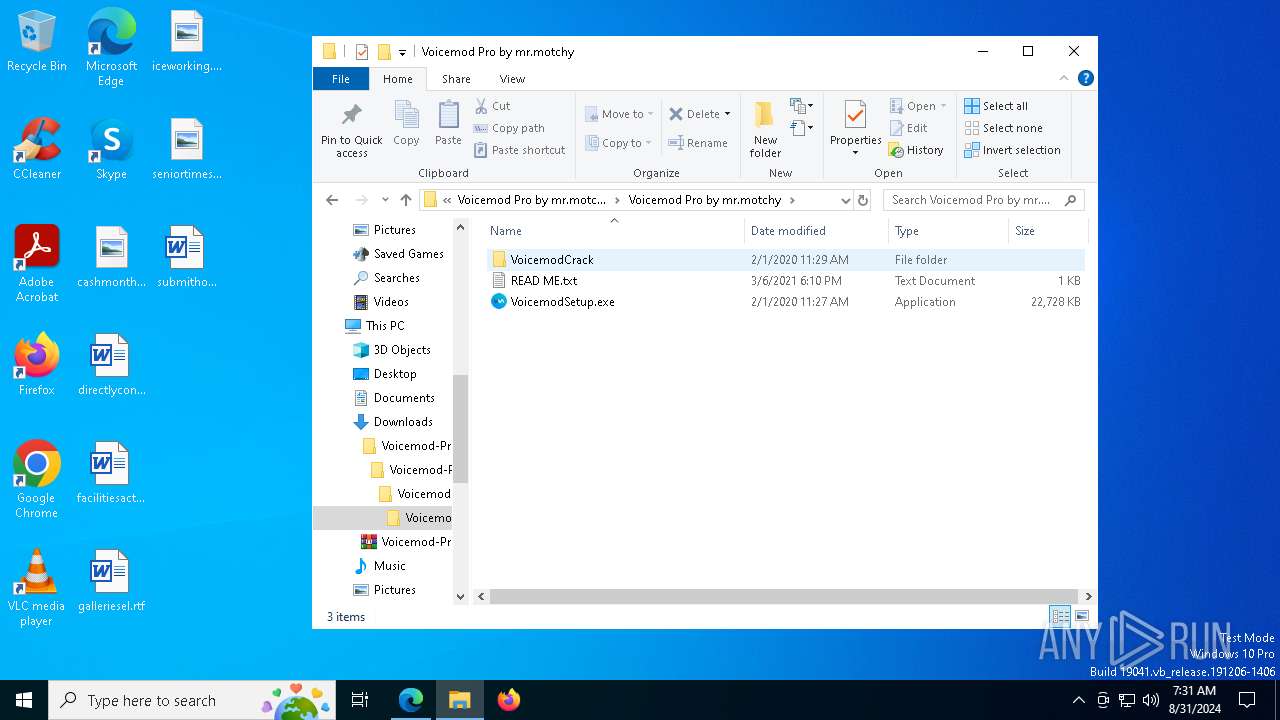
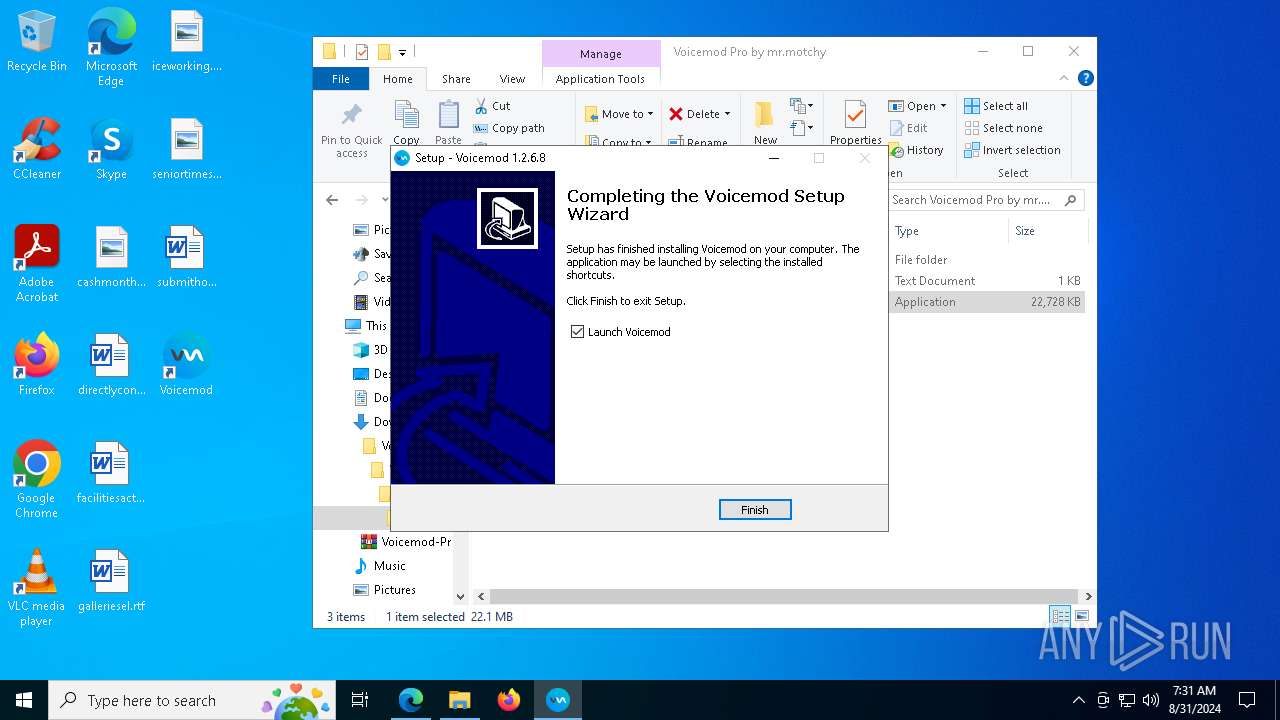
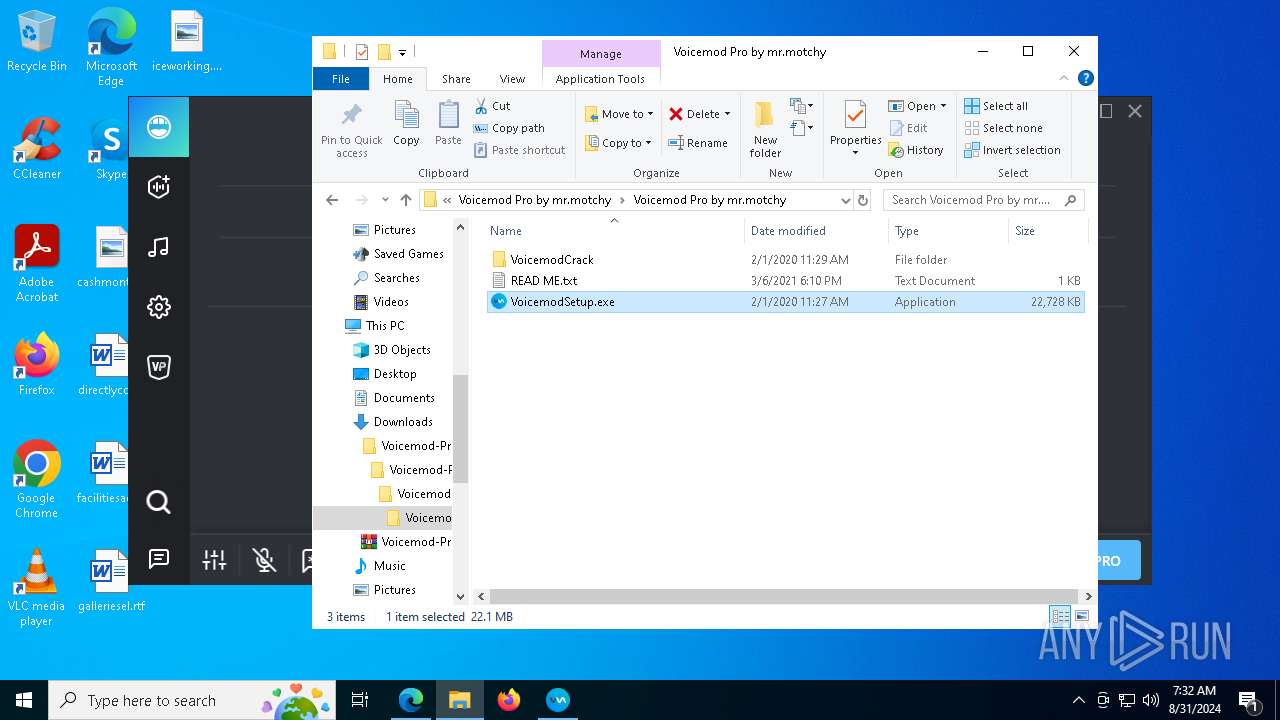
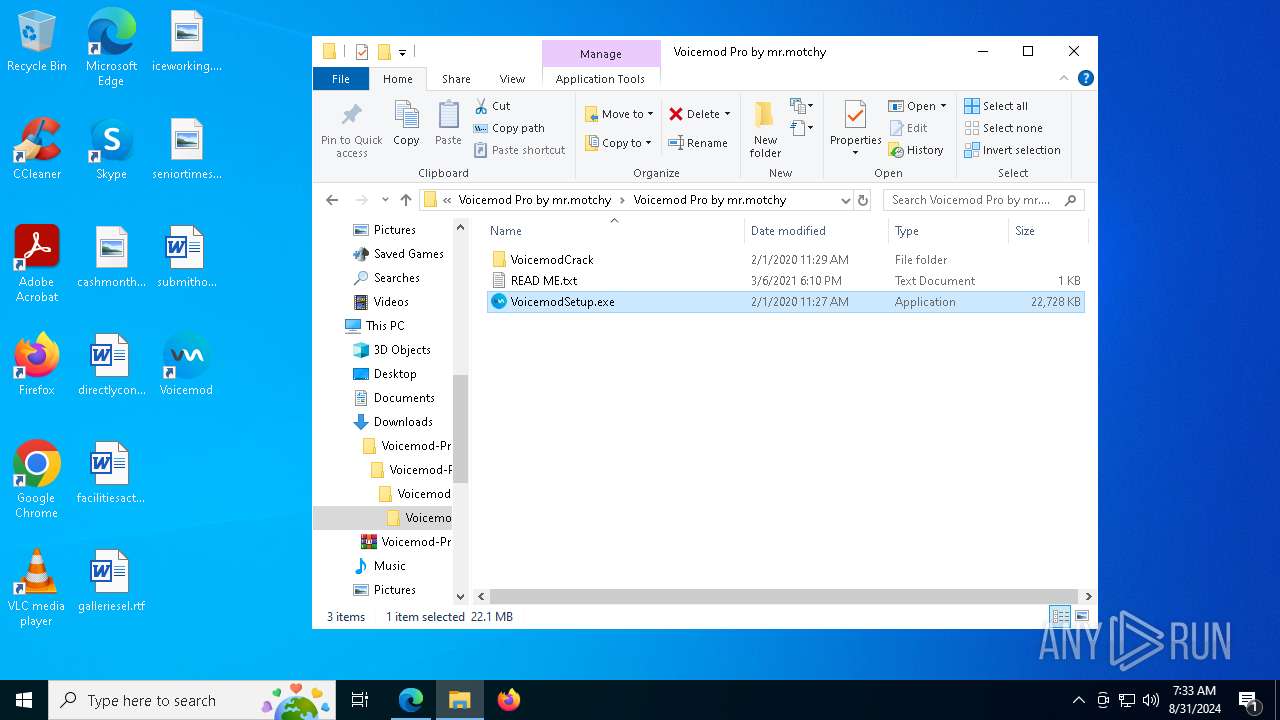
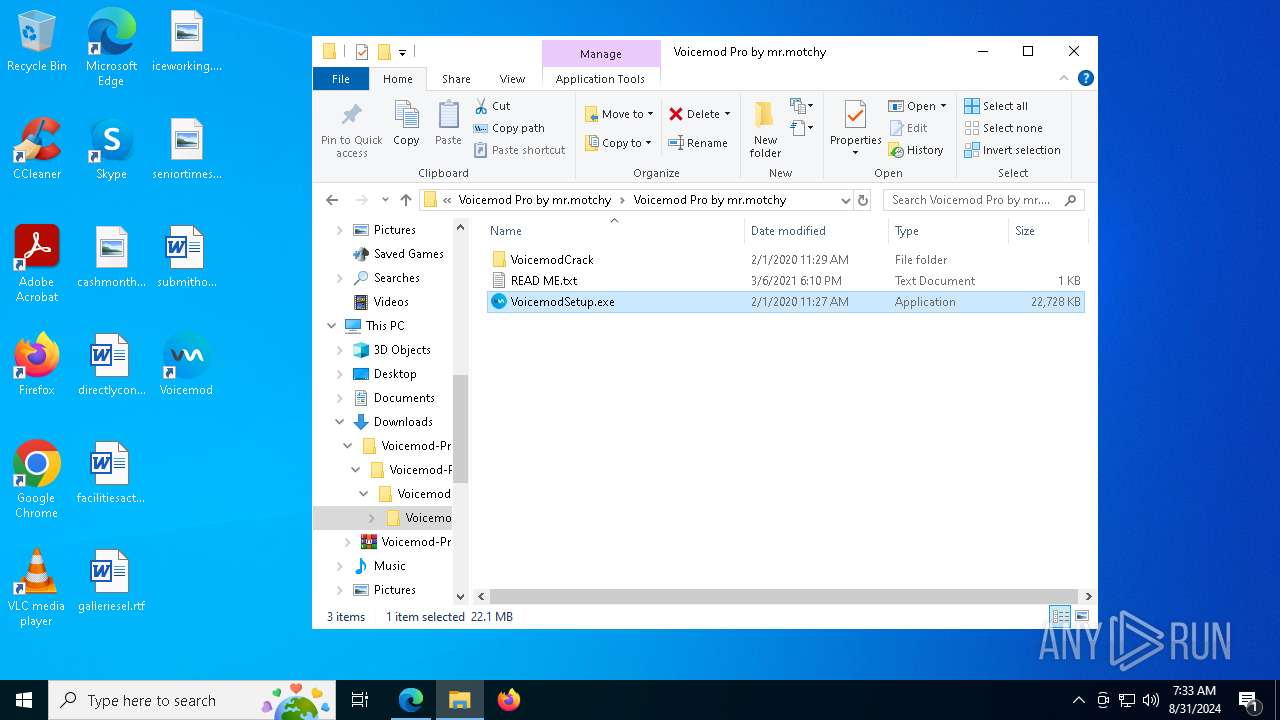
Manual execution by a user
- WinRAR.exe (PID: 2400)
- WinRAR.exe (PID: 7960)
- VoicemodSetup.exe (PID: 7296)
- VoicemodDesktop.exe (PID: 8144)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2400)
Create files in a temporary directory
- VoicemodSetup.exe (PID: 7296)
- VoicemodSetup.exe (PID: 1148)
- VoicemodSetup.tmp (PID: 1172)
- vc_redist.x64.exe (PID: 7636)
- vc_redist.x86.exe (PID: 7740)
- devcon.exe (PID: 7904)
- VoicemodDesktop.exe (PID: 4760)
Process checks computer location settings
- VoicemodSetup.tmp (PID: 6244)
Checks proxy server information
- VoicemodSetup.tmp (PID: 1172)
- VoicemodDesktop.exe (PID: 4760)
- WerFault.exe (PID: 7916)
- slui.exe (PID: 4040)
Reads the machine GUID from the registry
- VoicemodSetup.tmp (PID: 1172)
- drvinst.exe (PID: 3328)
- devcon.exe (PID: 7904)
- VoicemodDesktop.exe (PID: 4760)
- VoicemodDesktop.exe (PID: 8144)
Reads the software policy settings
- slui.exe (PID: 2128)
- VoicemodSetup.tmp (PID: 1172)
- devcon.exe (PID: 7904)
- drvinst.exe (PID: 3328)
- VoicemodDesktop.exe (PID: 4760)
- slui.exe (PID: 4040)
- WerFault.exe (PID: 7916)
Creates files or folders in the user directory
- VoicemodSetup.tmp (PID: 1172)
- VoicemodDesktop.exe (PID: 4760)
- WerFault.exe (PID: 7916)
Creates a software uninstall entry
- VoicemodSetup.tmp (PID: 1172)
Creates files in the program directory
- VoicemodSetup.tmp (PID: 1172)
- SaveDefaultDevices.exe (PID: 7764)
- cmd.exe (PID: 3672)
- VoicemodDesktop.exe (PID: 4760)
Process checks Internet Explorer phishing filters
- VoicemodDesktop.exe (PID: 4760)
Disables trace logs
- VoicemodDesktop.exe (PID: 4760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
425
Monitored processes
284
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | cmd /C del /Q C:\ProgramData\Voicemod\Temp\sdk-poison-roar5*.wav | C:\Windows\System32\cmd.exe | — | VoicemodDesktop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2412 --field-trial-handle=2416,i,10304114706210571197,7780527696043758911,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | cmd /C del /Q C:\ProgramData\Voicemod\Temp\sdk-romantic-ulala*.wav | C:\Windows\System32\cmd.exe | — | VoicemodDesktop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 940 | cmd /C del /Q C:\ProgramData\Voicemod\Temp\sdk-franky-background*.wav | C:\Windows\System32\cmd.exe | — | VoicemodDesktop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5680 --field-trial-handle=2416,i,10304114706210571197,7780527696043758911,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6220 --field-trial-handle=2416,i,10304114706210571197,7780527696043758911,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
81 619
Read events
80 137
Write events
1 405
Delete events
77
Modification events
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1288) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
111
Suspicious files
517
Text files
248
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12992b.TMP | — | |
MD5:— | SHA256:— | |||
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12992b.TMP | — | |
MD5:— | SHA256:— | |||
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12993b.TMP | — | |
MD5:— | SHA256:— | |||
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12994a.TMP | — | |
MD5:— | SHA256:— | |||
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF129979.TMP | — | |
MD5:— | SHA256:— | |||
| 1288 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
111
DNS requests
94
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8020 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec3f42ff-db07-4960-b560-3fa136bcb5d5?P1=1725610034&P2=404&P3=2&P4=gvp%2bLpX7%2bx36%2ftWGV55vRjpJhlokv5XDQzYG6xj3OoVzmWMZj0cJUVEvpHAN0AfkSQ5XnZws5B3urc6DP4aC5w%3d%3d | unknown | — | — | whitelisted |
6580 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8020 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec3f42ff-db07-4960-b560-3fa136bcb5d5?P1=1725610034&P2=404&P3=2&P4=gvp%2bLpX7%2bx36%2ftWGV55vRjpJhlokv5XDQzYG6xj3OoVzmWMZj0cJUVEvpHAN0AfkSQ5XnZws5B3urc6DP4aC5w%3d%3d | unknown | — | — | whitelisted |
8020 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec3f42ff-db07-4960-b560-3fa136bcb5d5?P1=1725610034&P2=404&P3=2&P4=gvp%2bLpX7%2bx36%2ftWGV55vRjpJhlokv5XDQzYG6xj3OoVzmWMZj0cJUVEvpHAN0AfkSQ5XnZws5B3urc6DP4aC5w%3d%3d | unknown | — | — | whitelisted |
8020 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec3f42ff-db07-4960-b560-3fa136bcb5d5?P1=1725610034&P2=404&P3=2&P4=gvp%2bLpX7%2bx36%2ftWGV55vRjpJhlokv5XDQzYG6xj3OoVzmWMZj0cJUVEvpHAN0AfkSQ5XnZws5B3urc6DP4aC5w%3d%3d | unknown | — | — | whitelisted |
8020 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec3f42ff-db07-4960-b560-3fa136bcb5d5?P1=1725610034&P2=404&P3=2&P4=gvp%2bLpX7%2bx36%2ftWGV55vRjpJhlokv5XDQzYG6xj3OoVzmWMZj0cJUVEvpHAN0AfkSQ5XnZws5B3urc6DP4aC5w%3d%3d | unknown | — | — | whitelisted |
7524 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7524 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8020 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec3f42ff-db07-4960-b560-3fa136bcb5d5?P1=1725610034&P2=404&P3=2&P4=gvp%2bLpX7%2bx36%2ftWGV55vRjpJhlokv5XDQzYG6xj3OoVzmWMZj0cJUVEvpHAN0AfkSQ5XnZws5B3urc6DP4aC5w%3d%3d | unknown | — | — | whitelisted |
1172 | VoicemodSetup.tmp | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7080 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
568 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1480 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
1288 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1480 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1480 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1480 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1480 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1480 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1480 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1480 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |