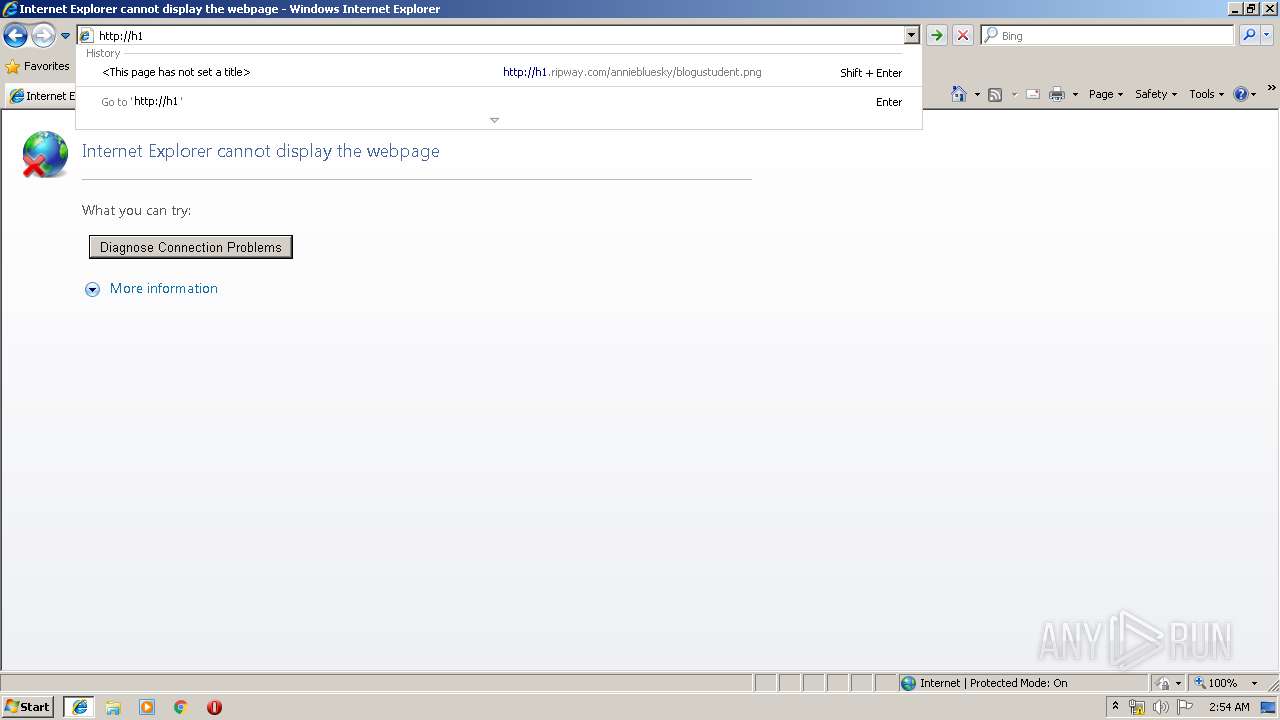
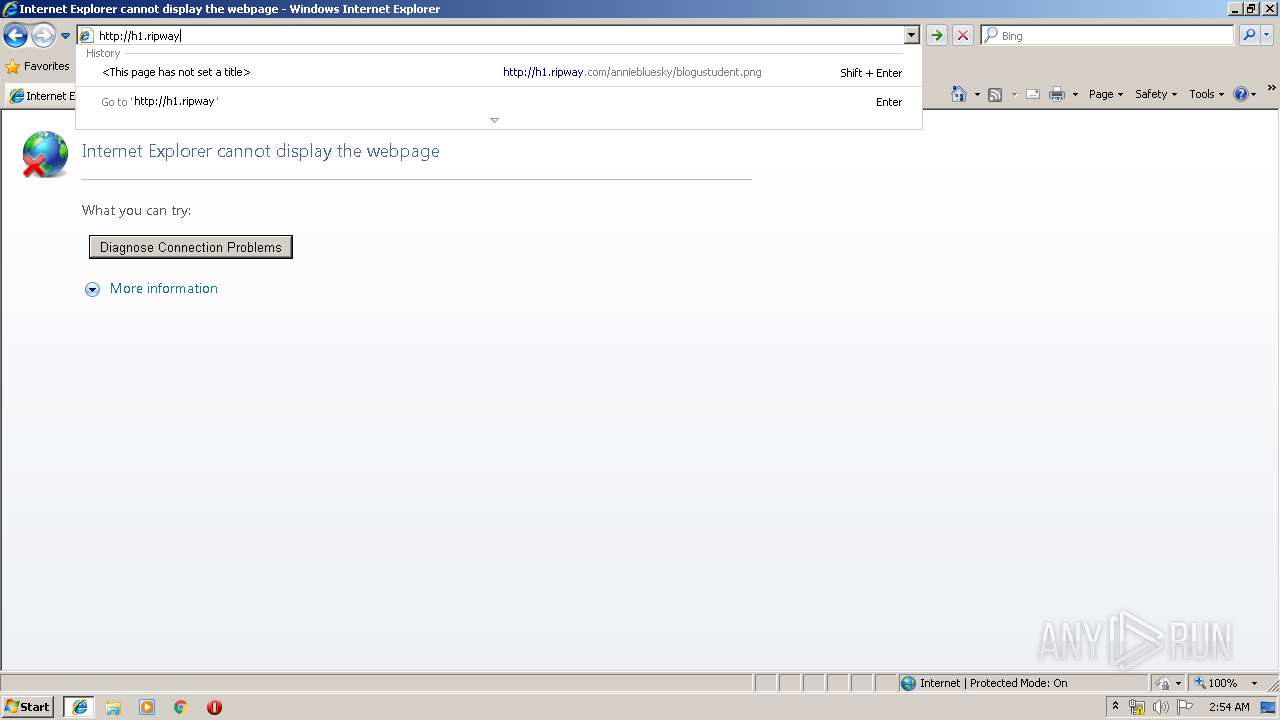
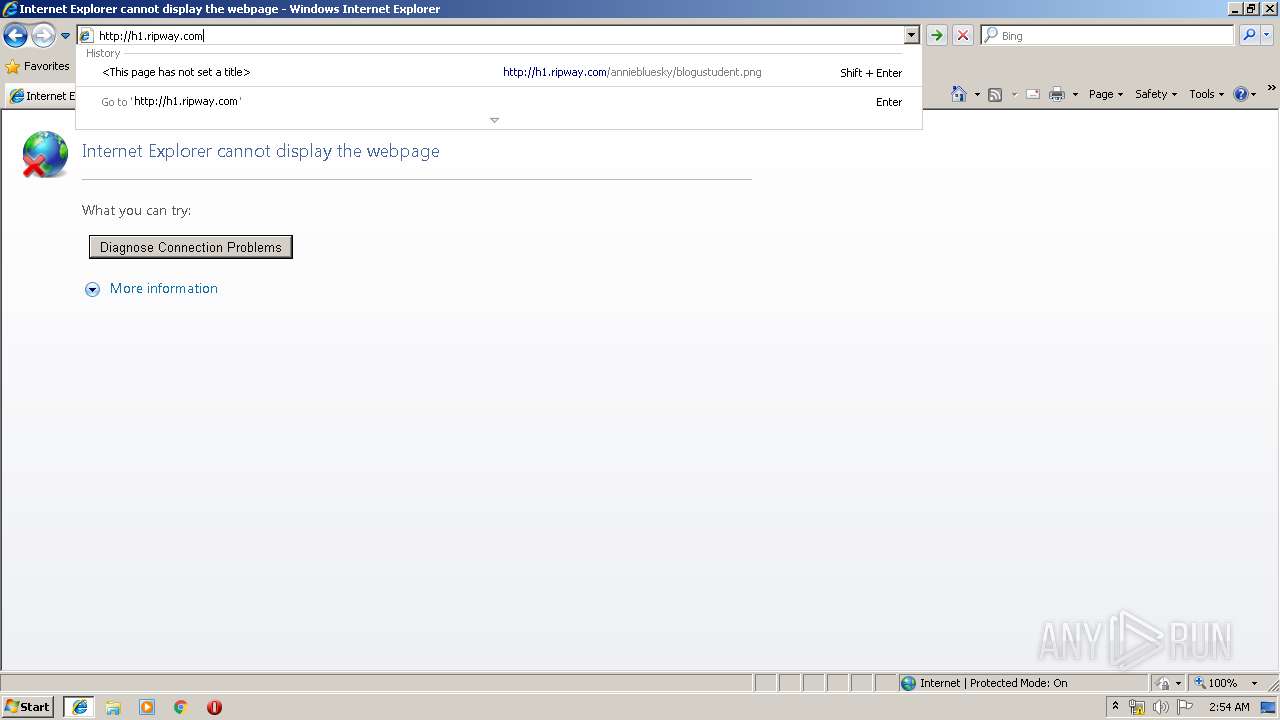
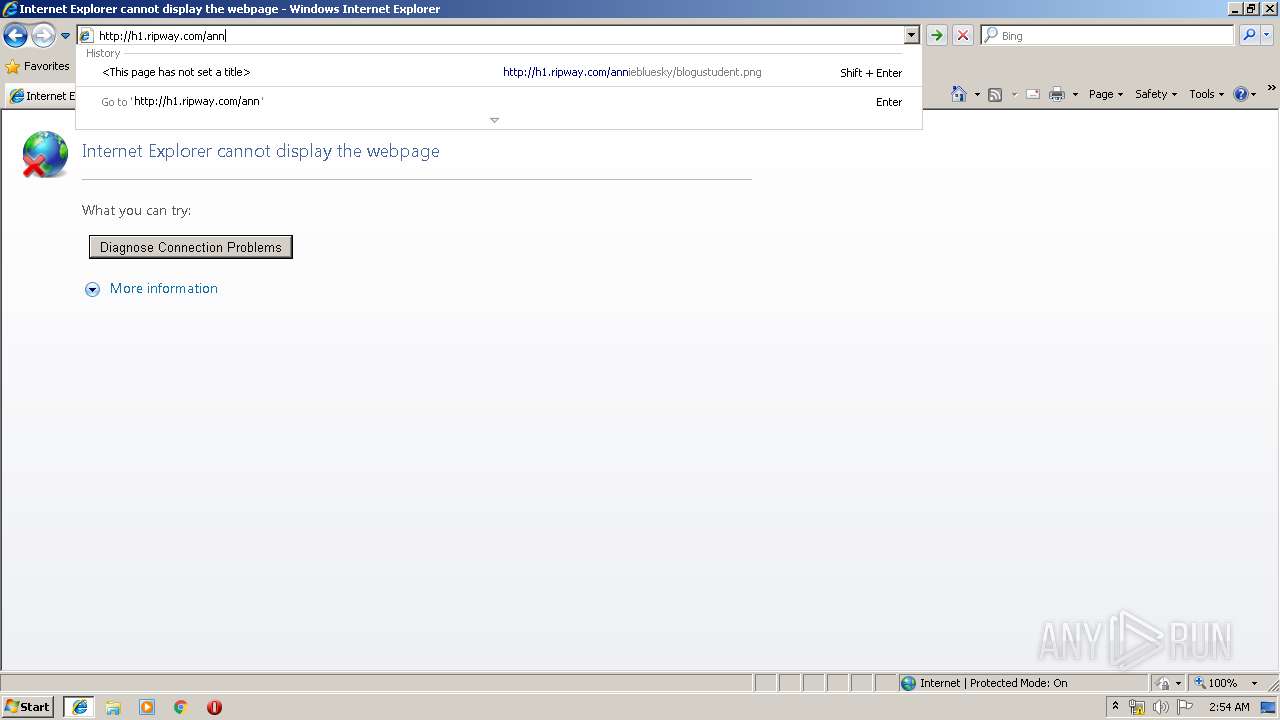
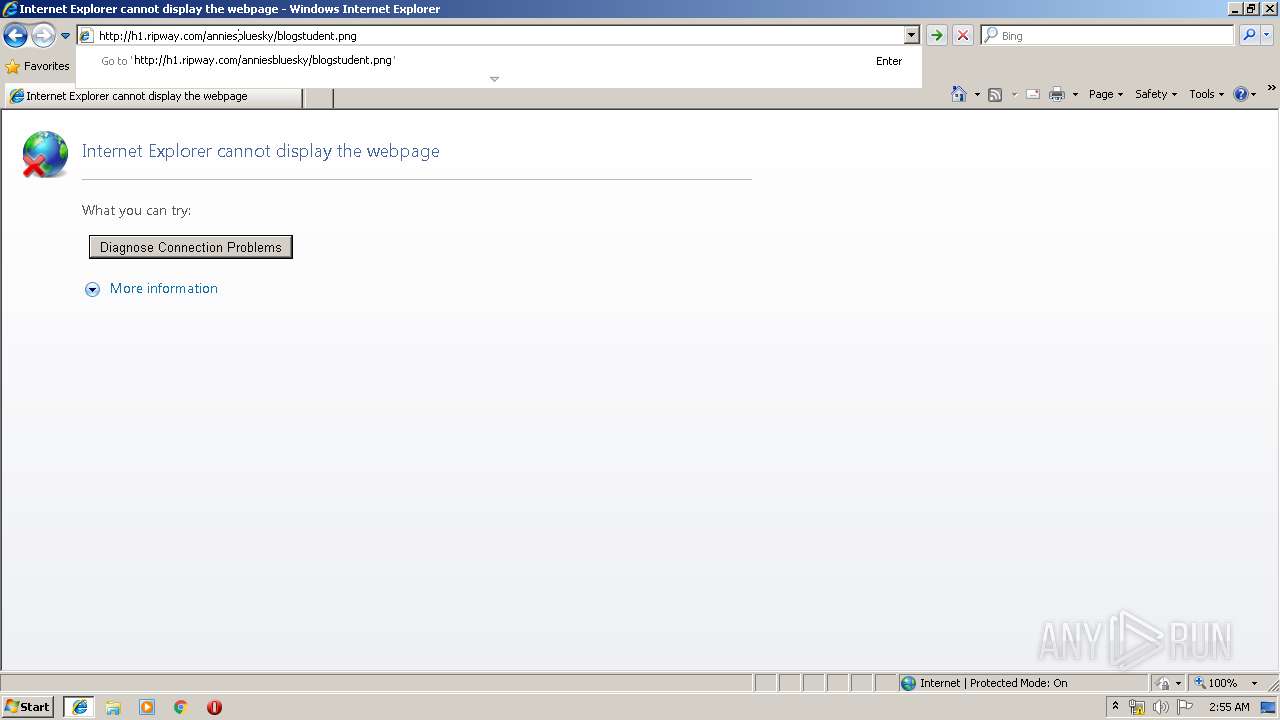
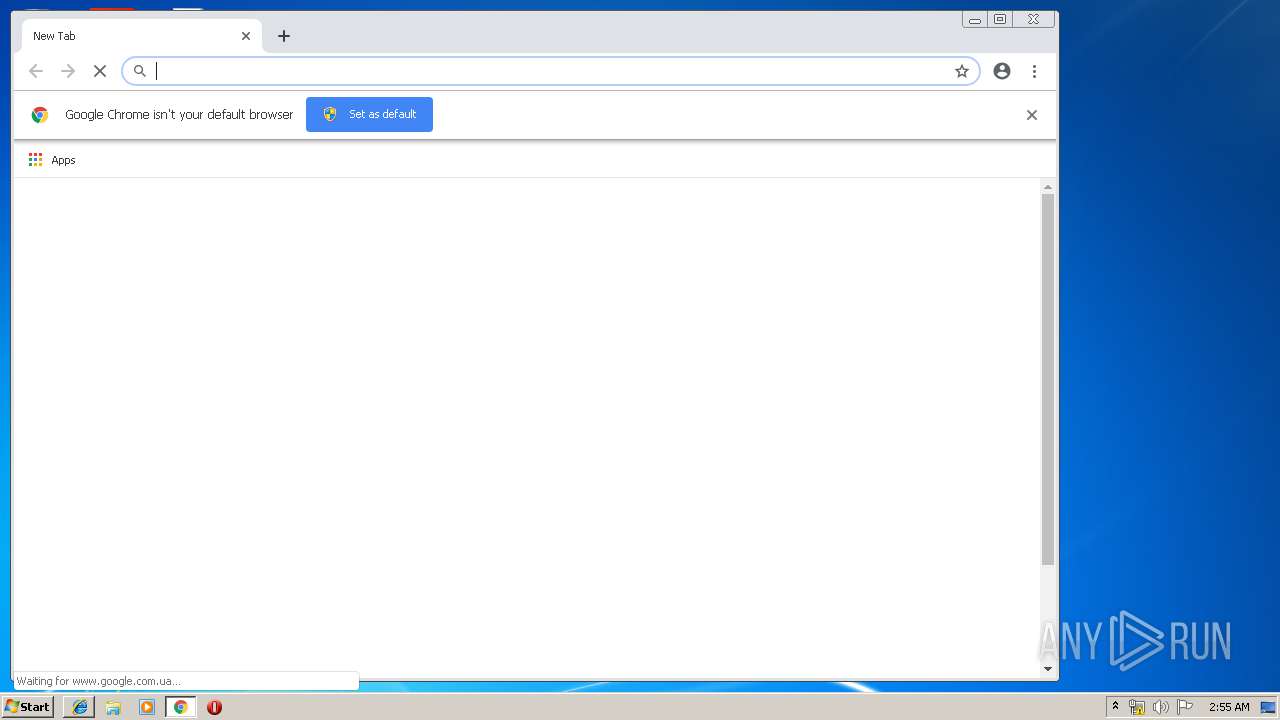
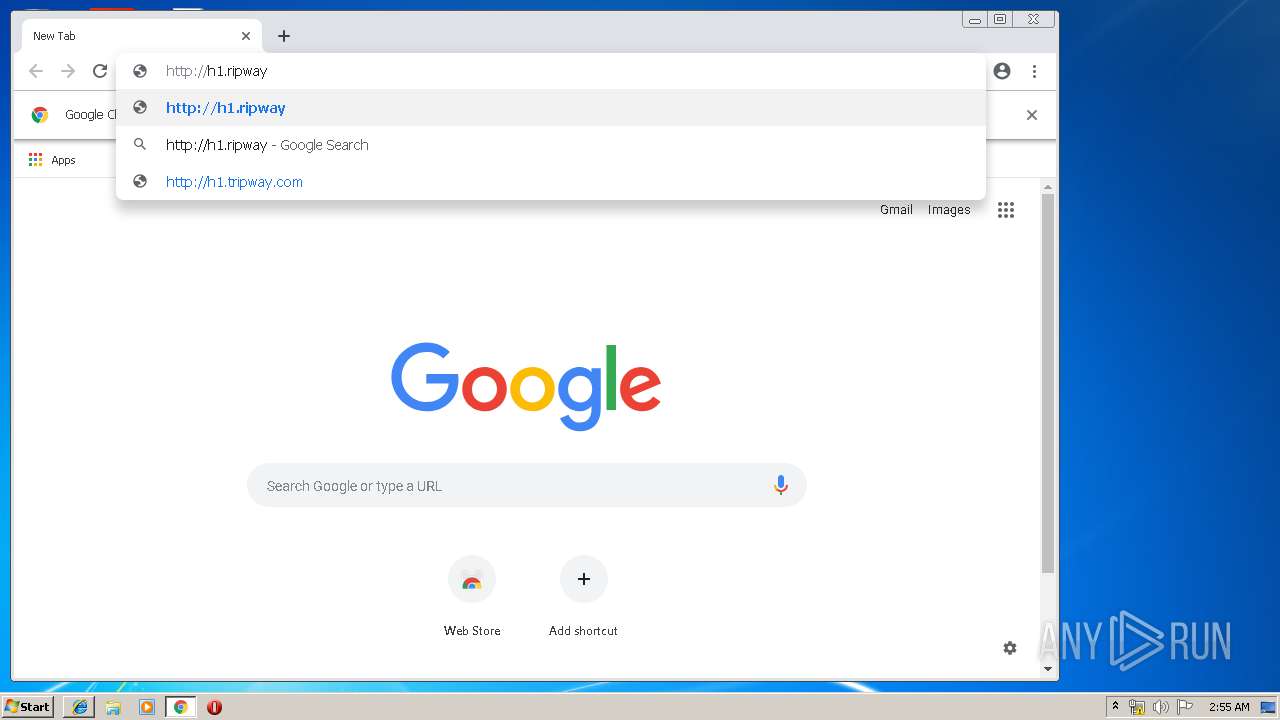
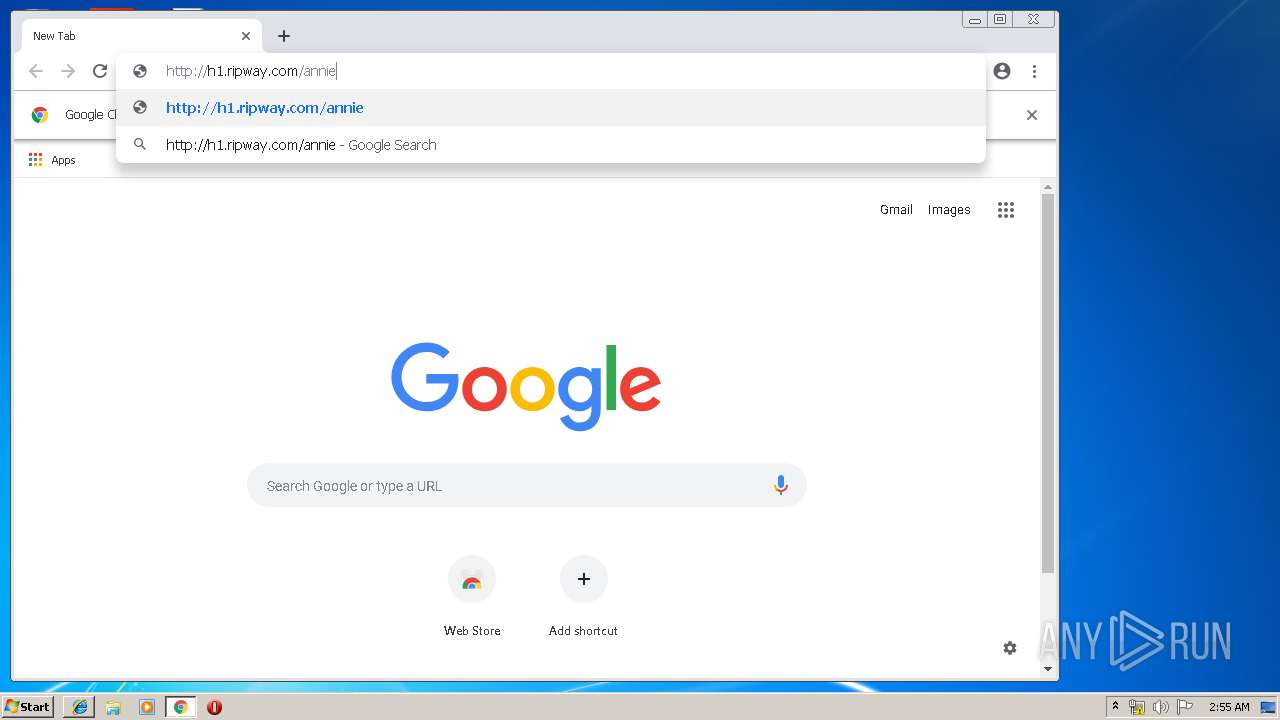
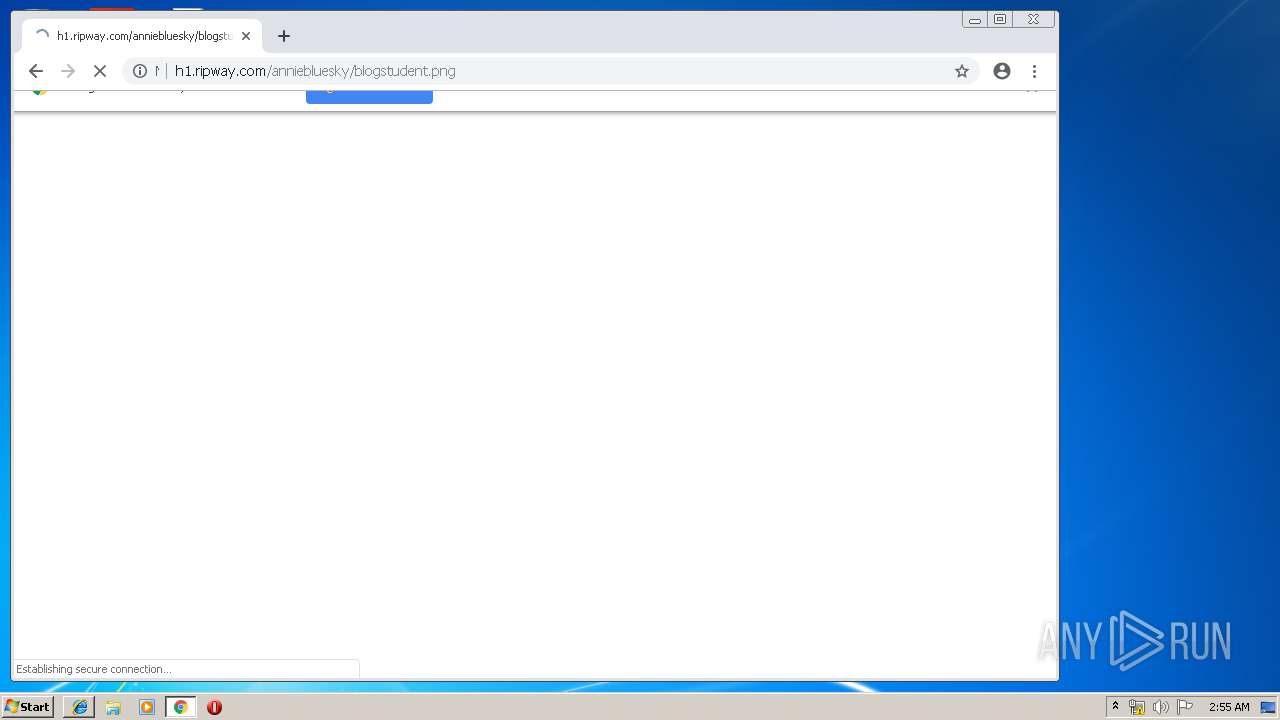
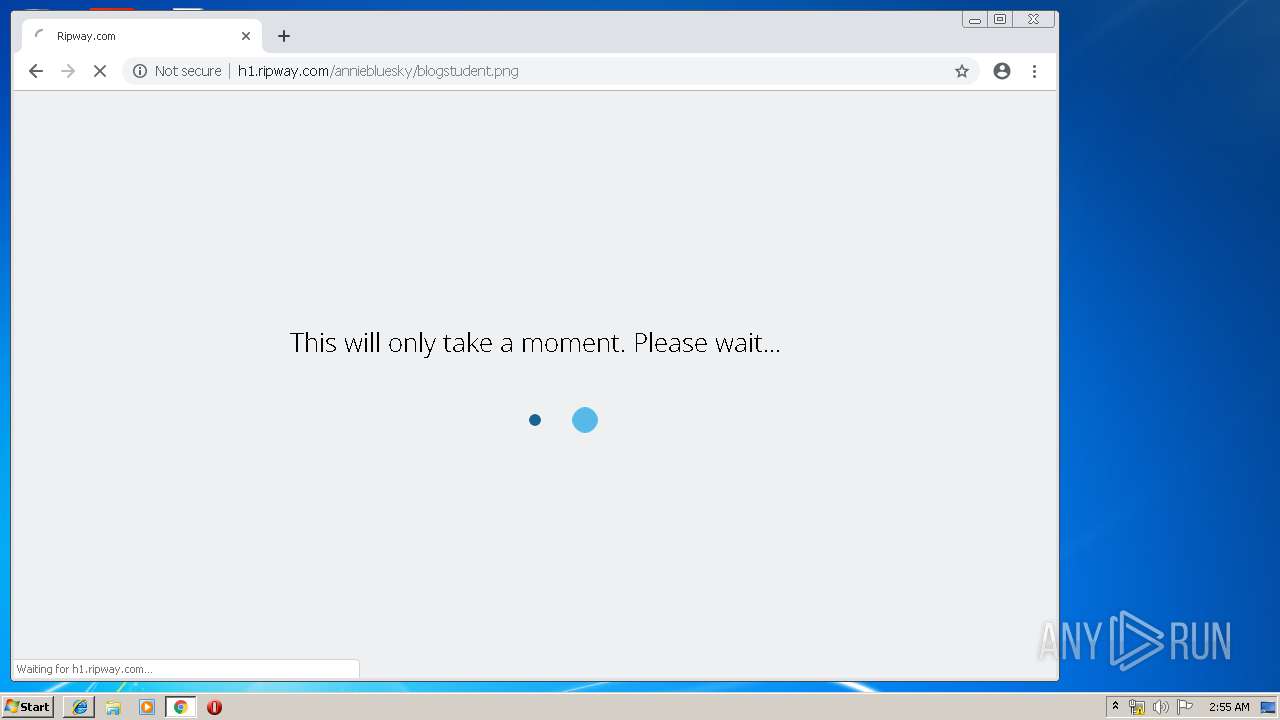
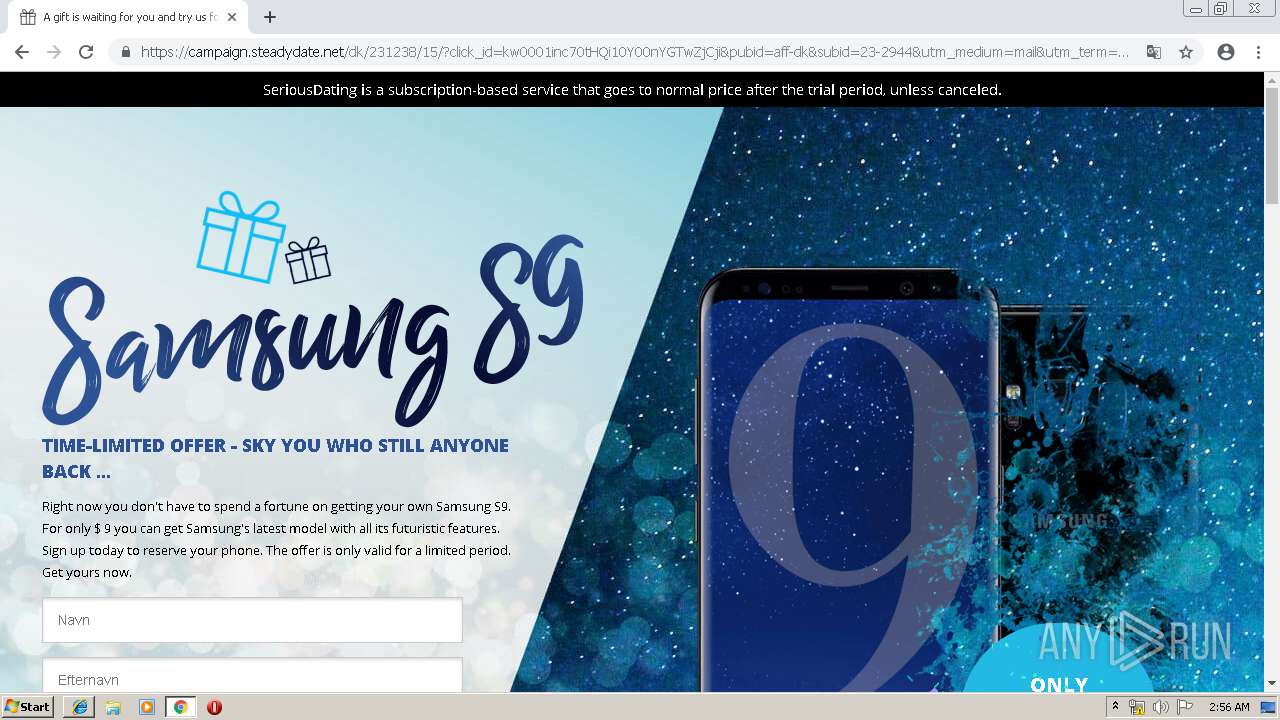
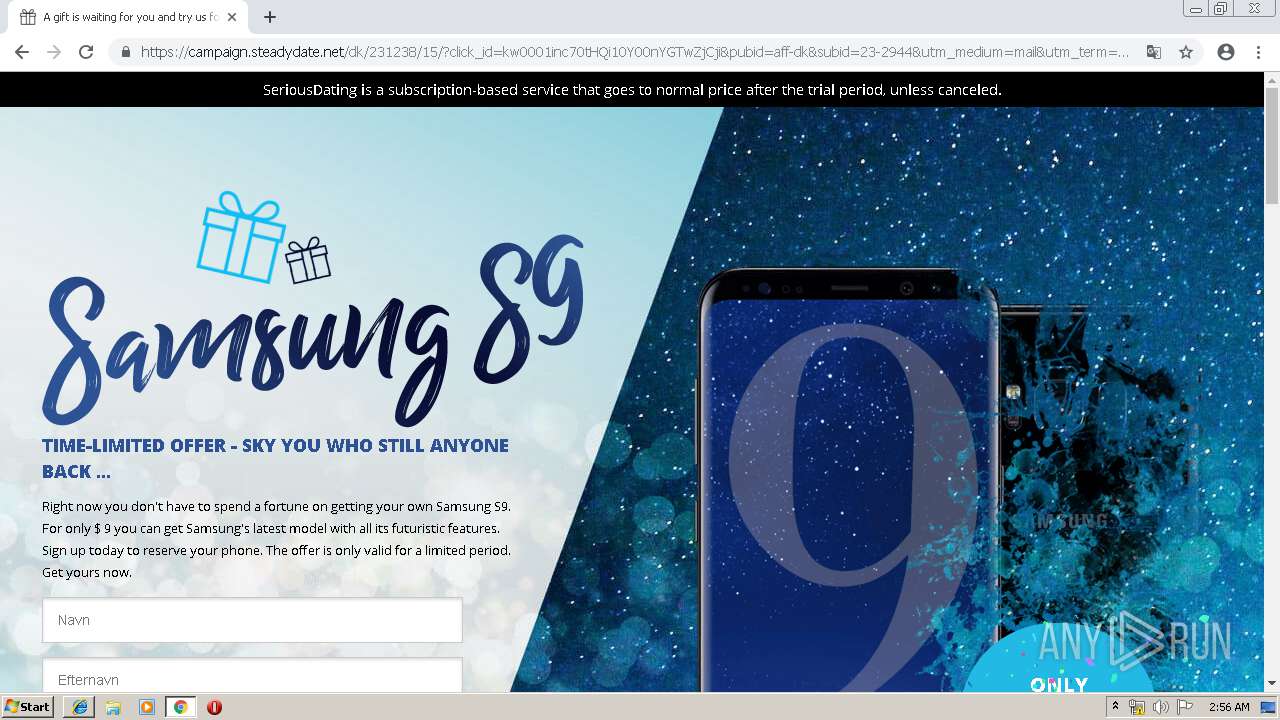
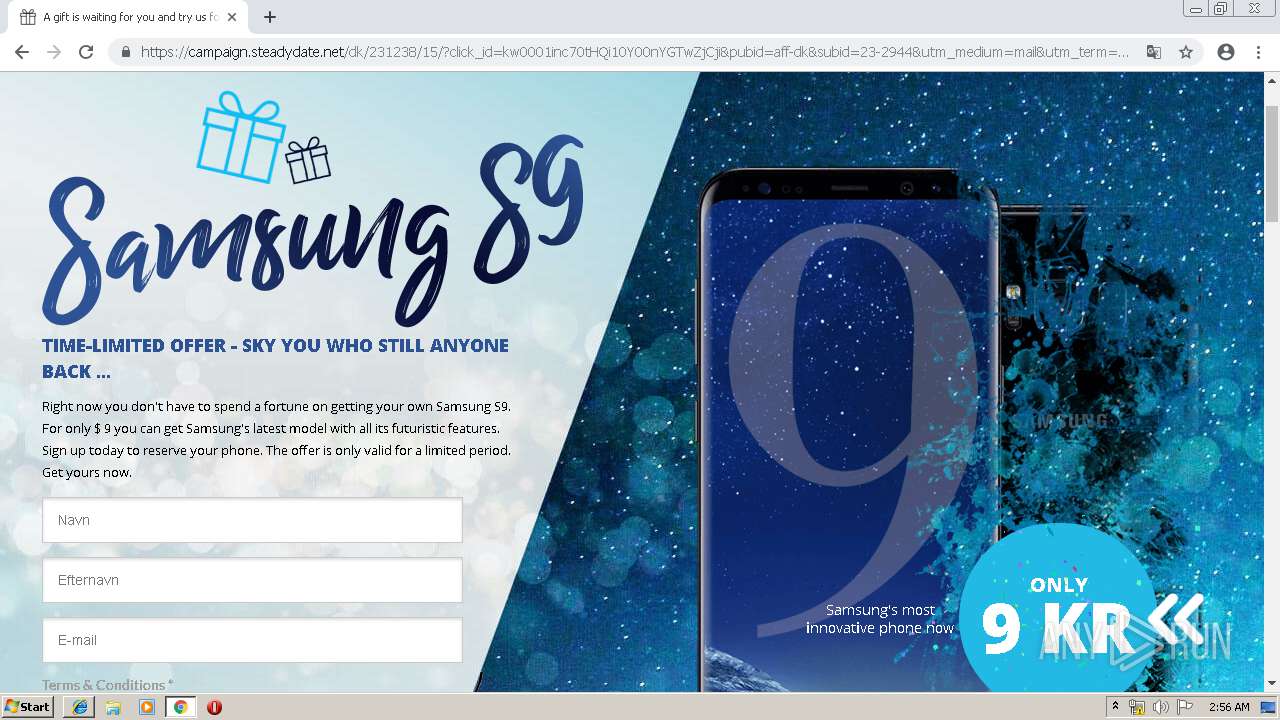
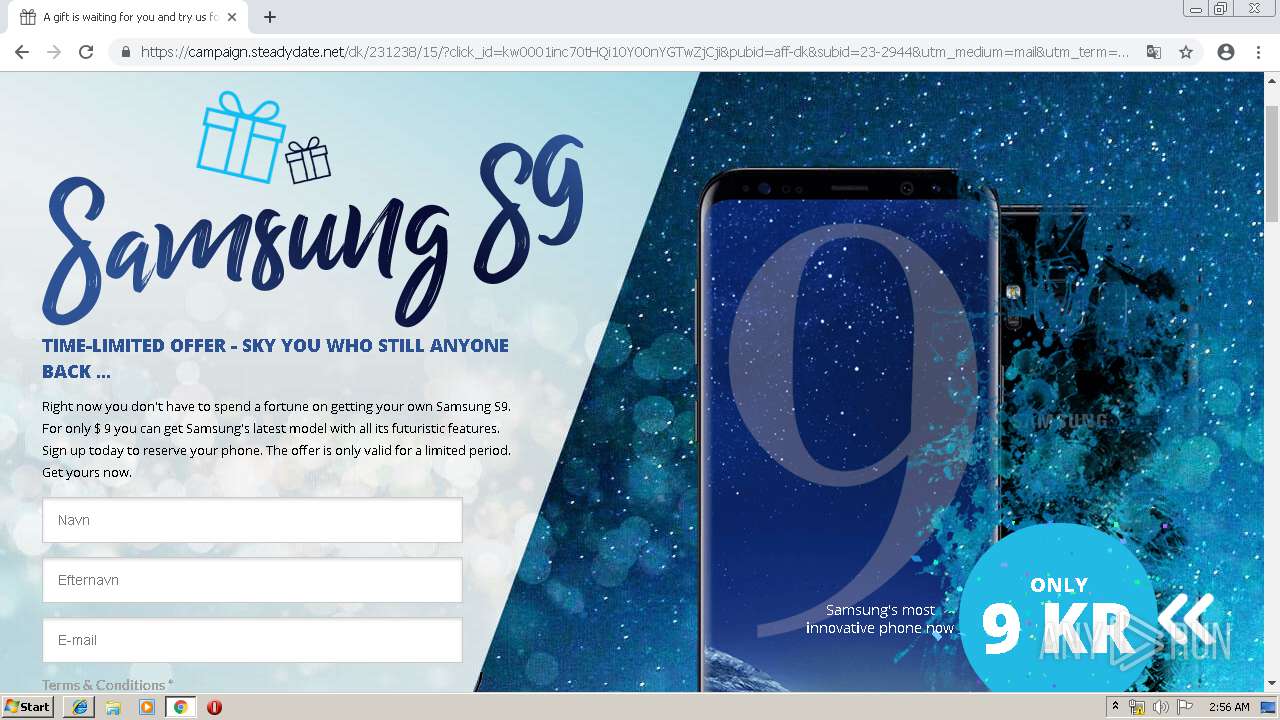
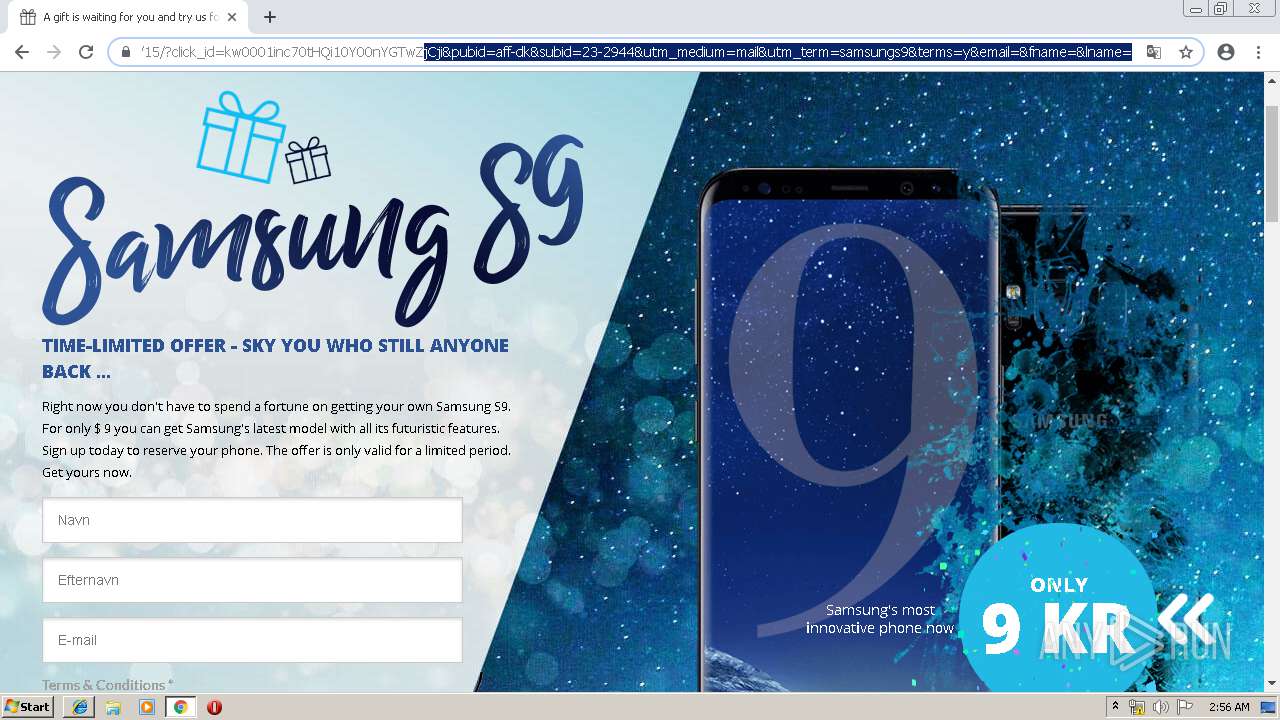
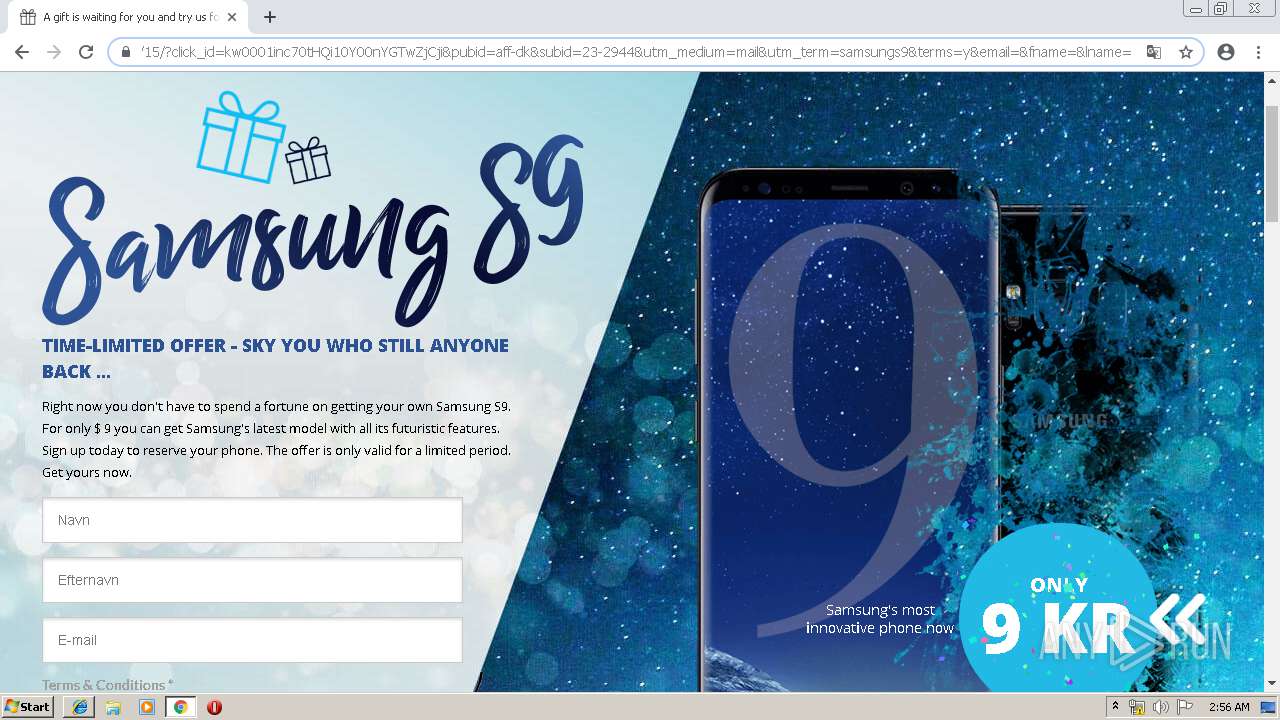
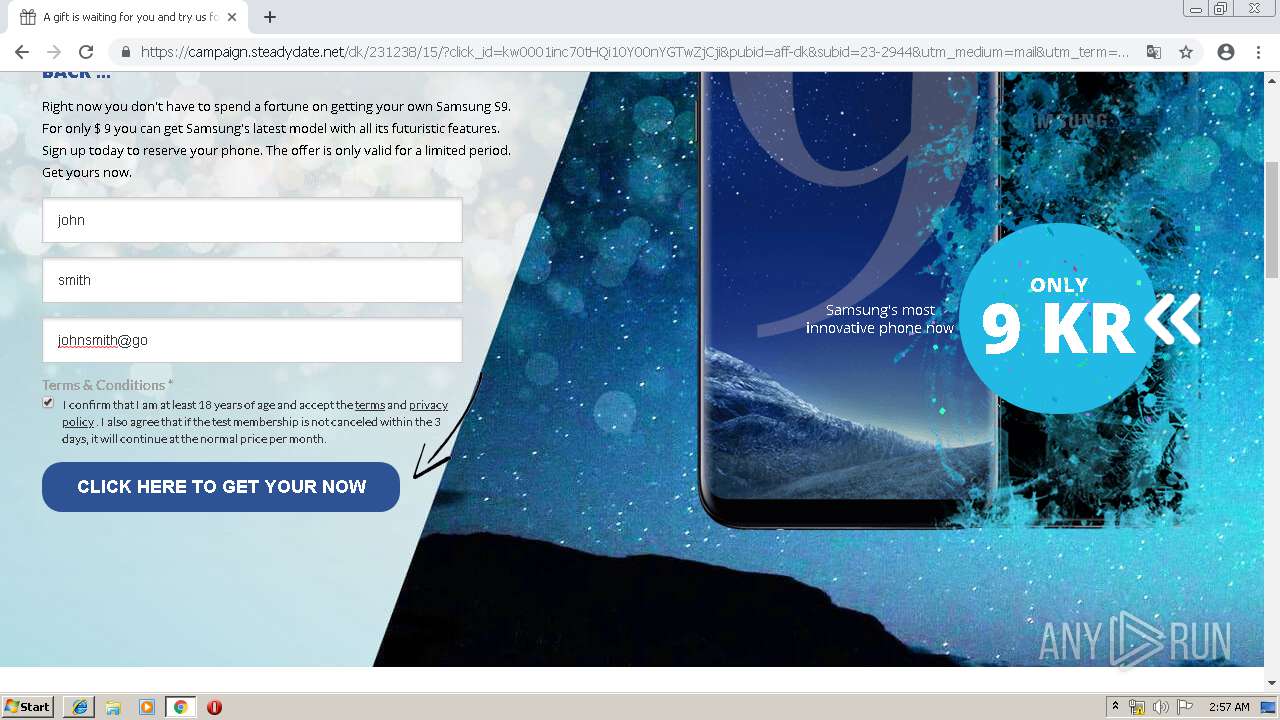
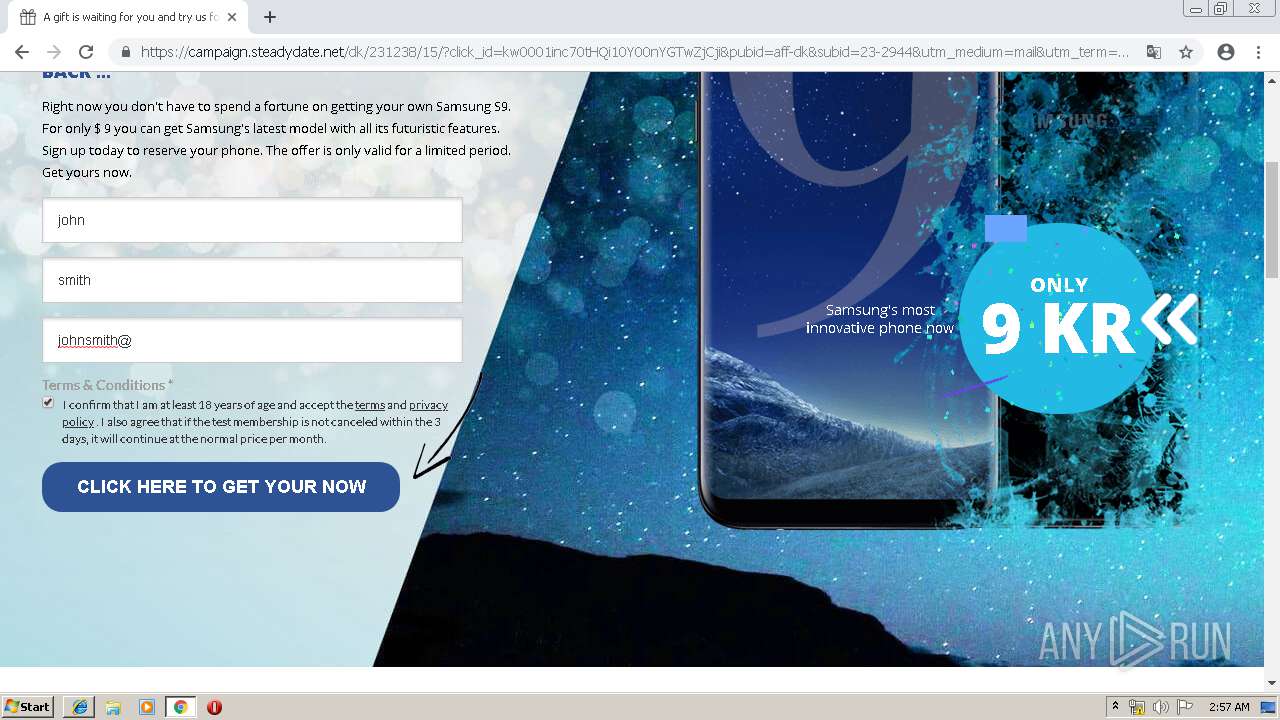
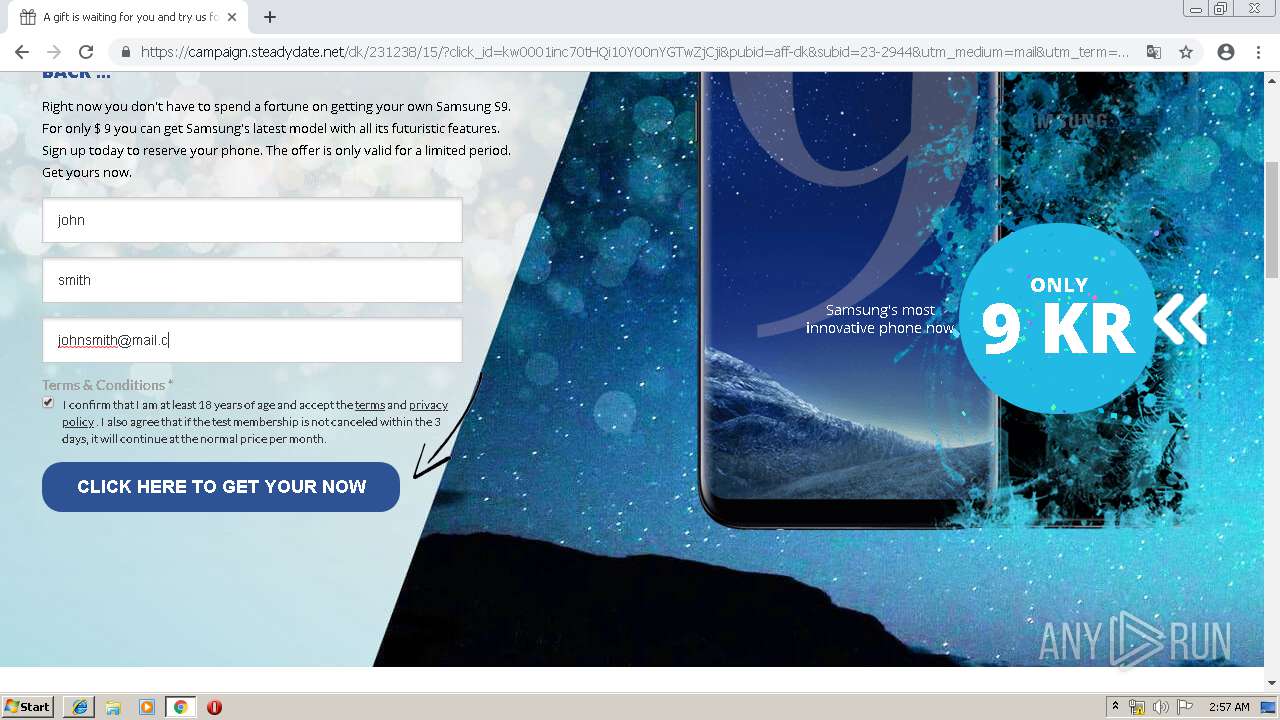
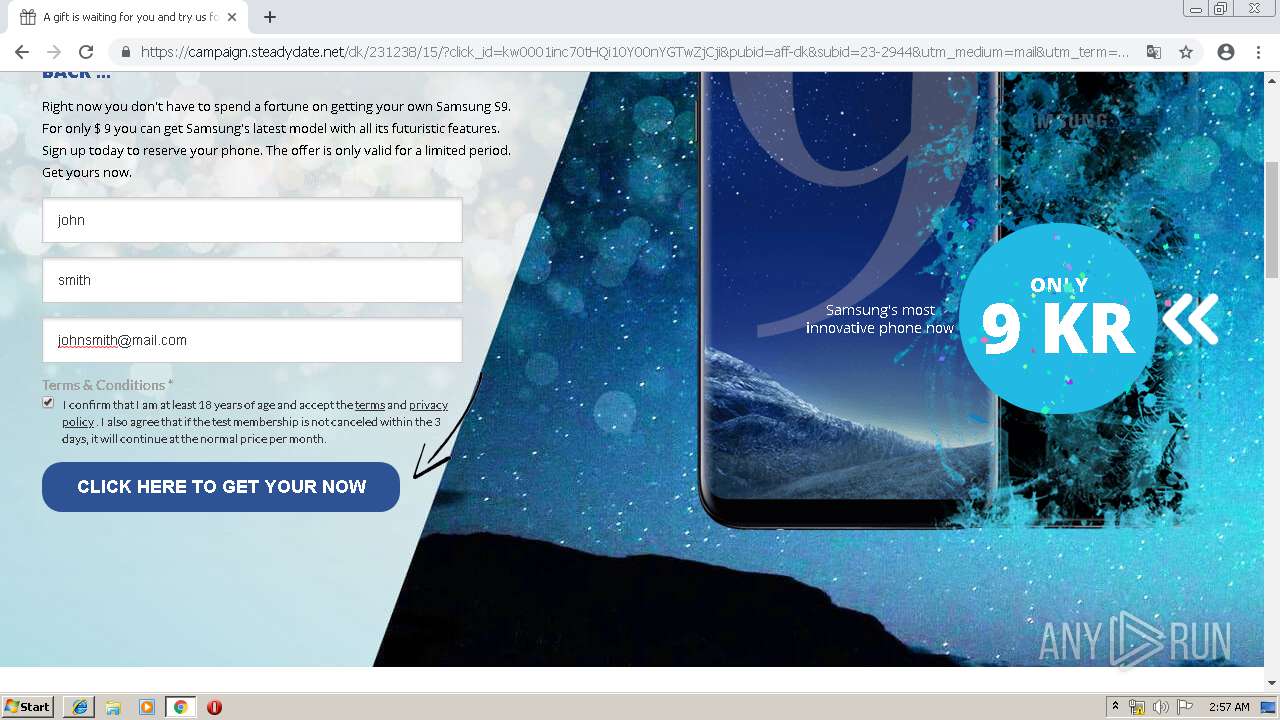
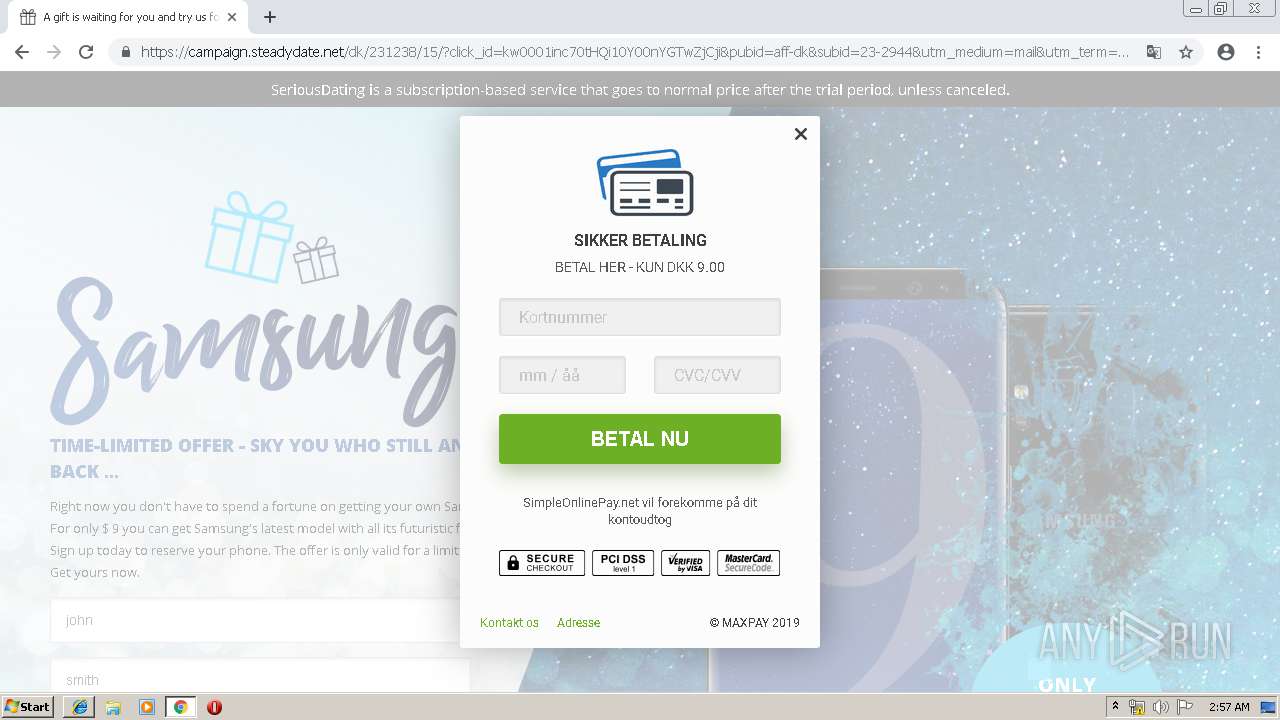
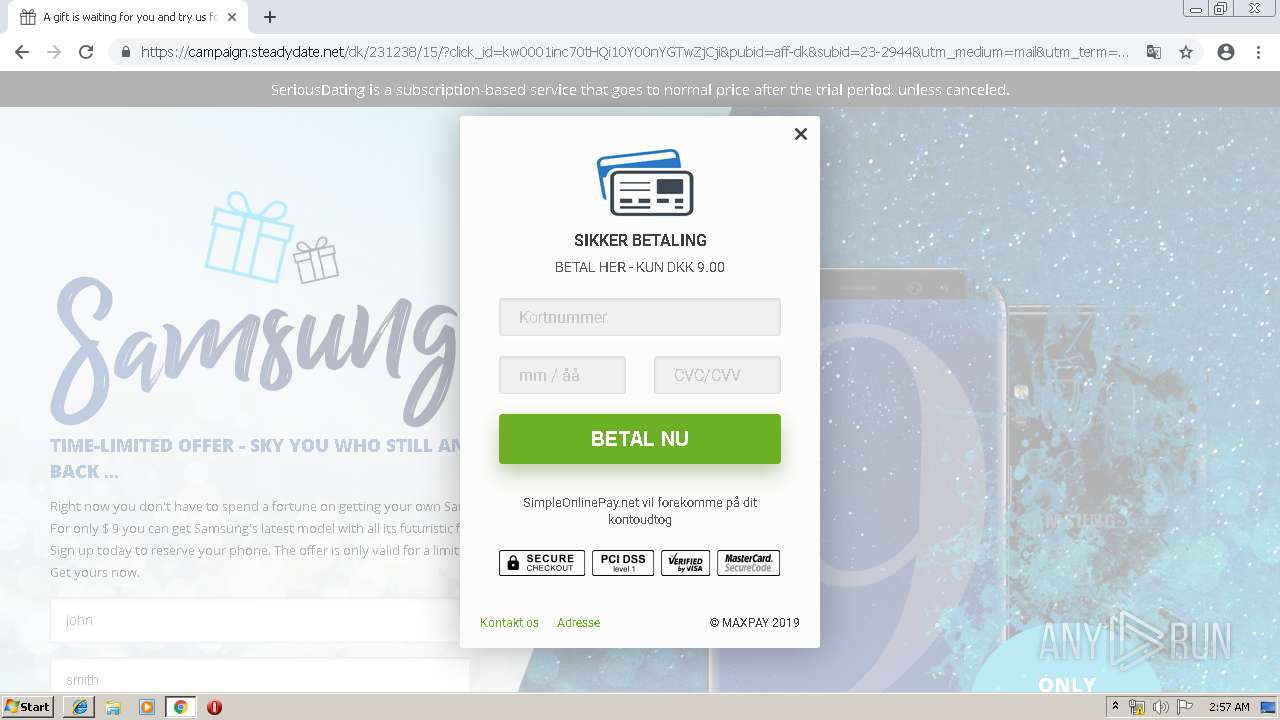
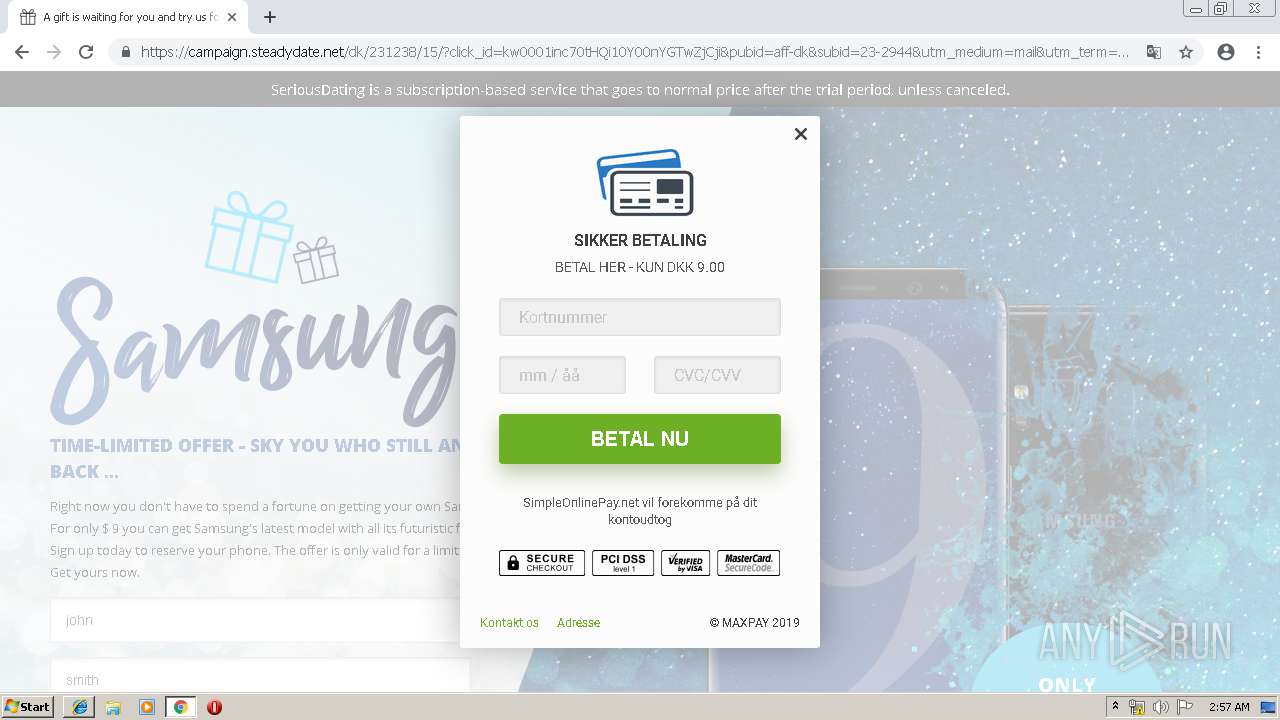
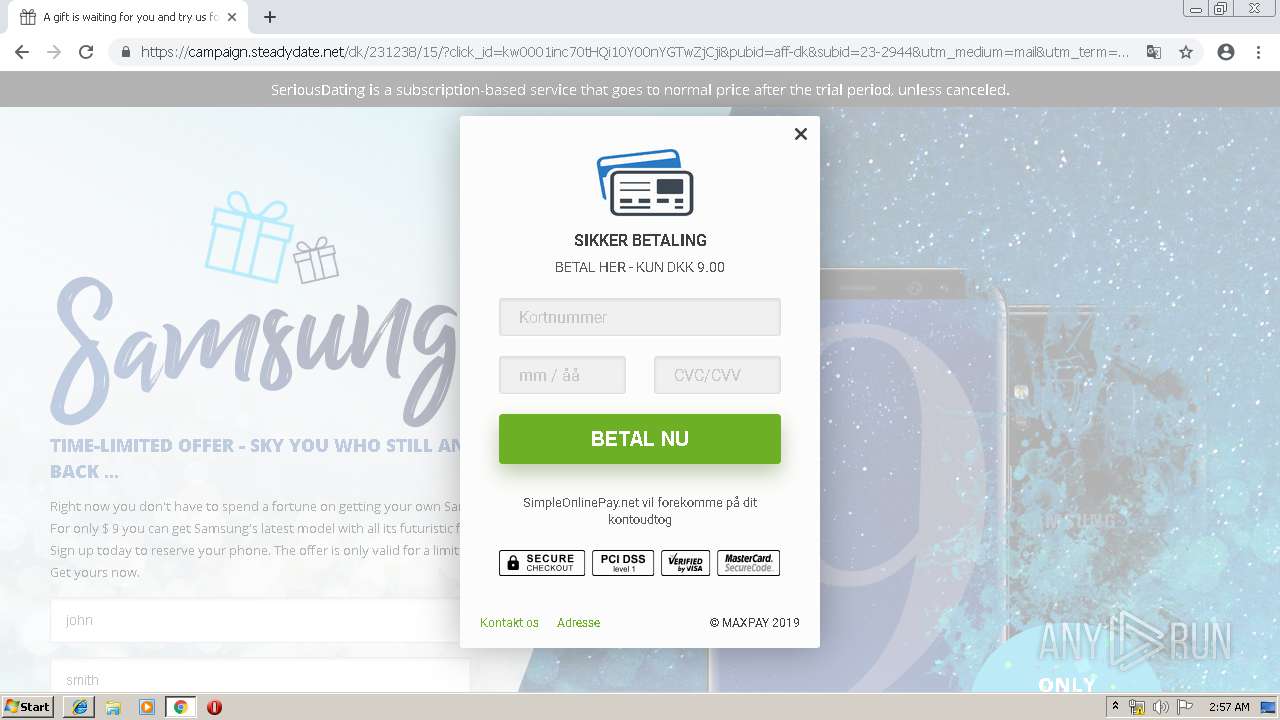
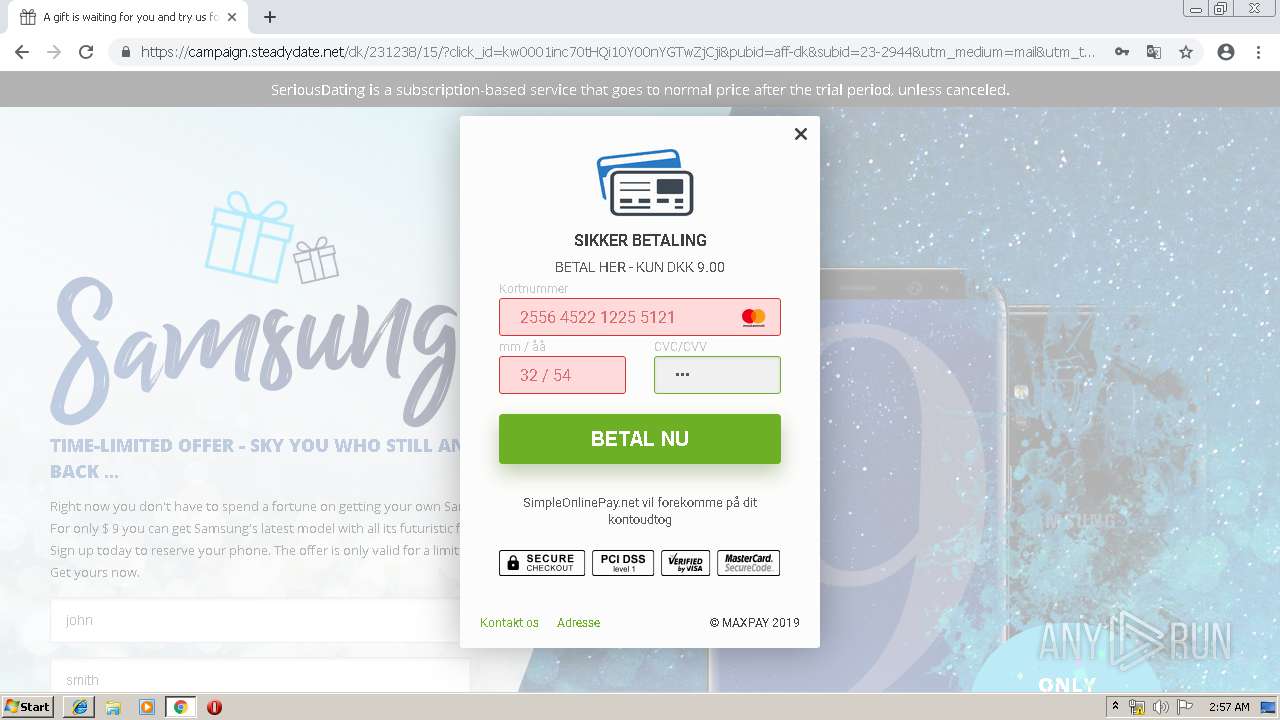
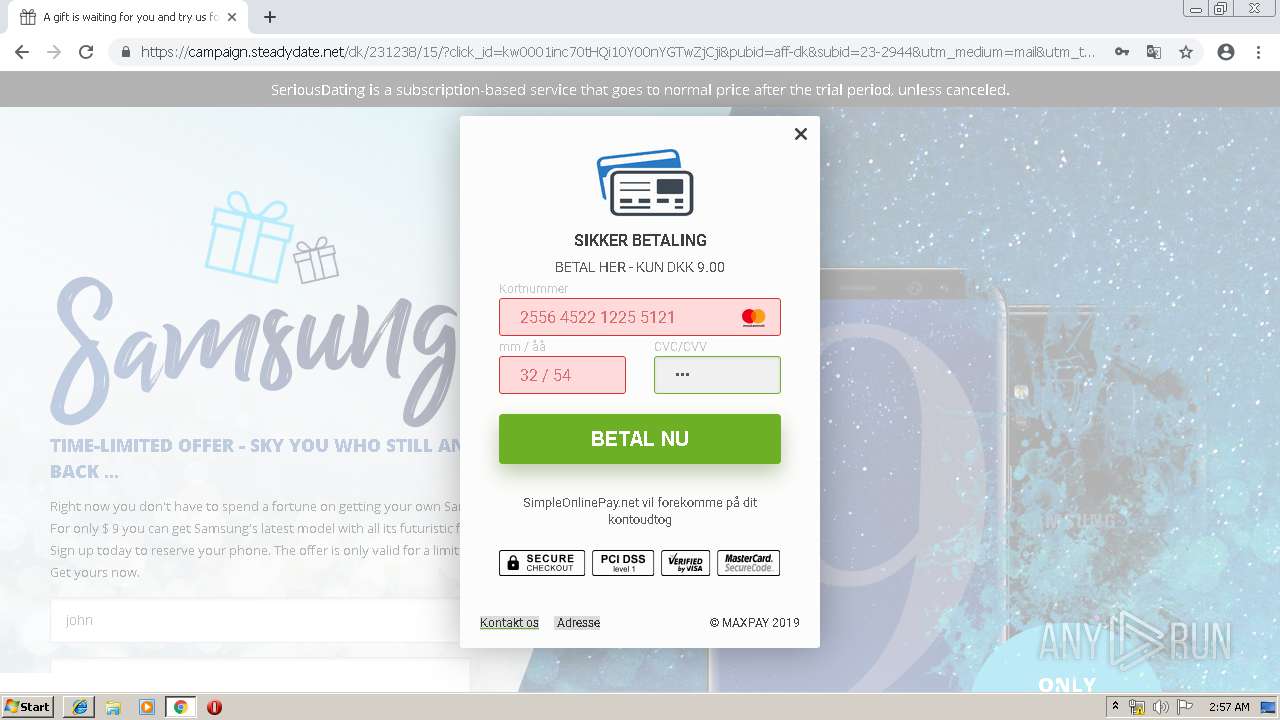
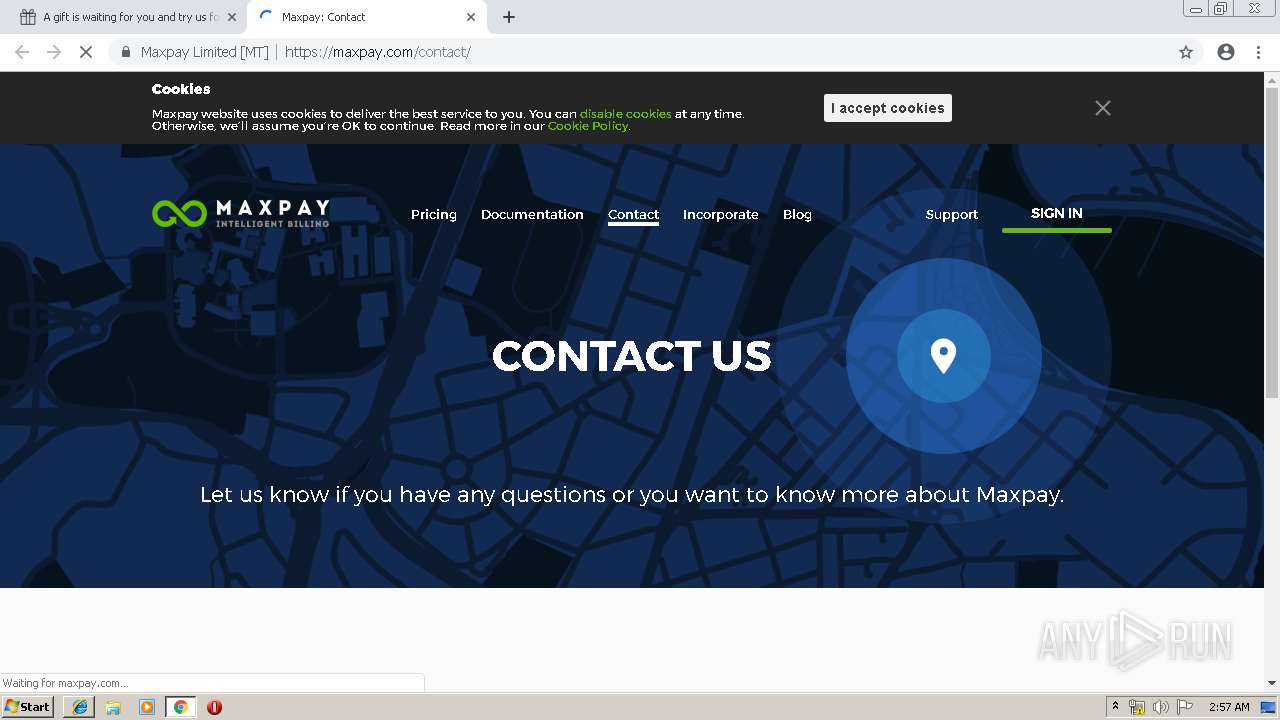
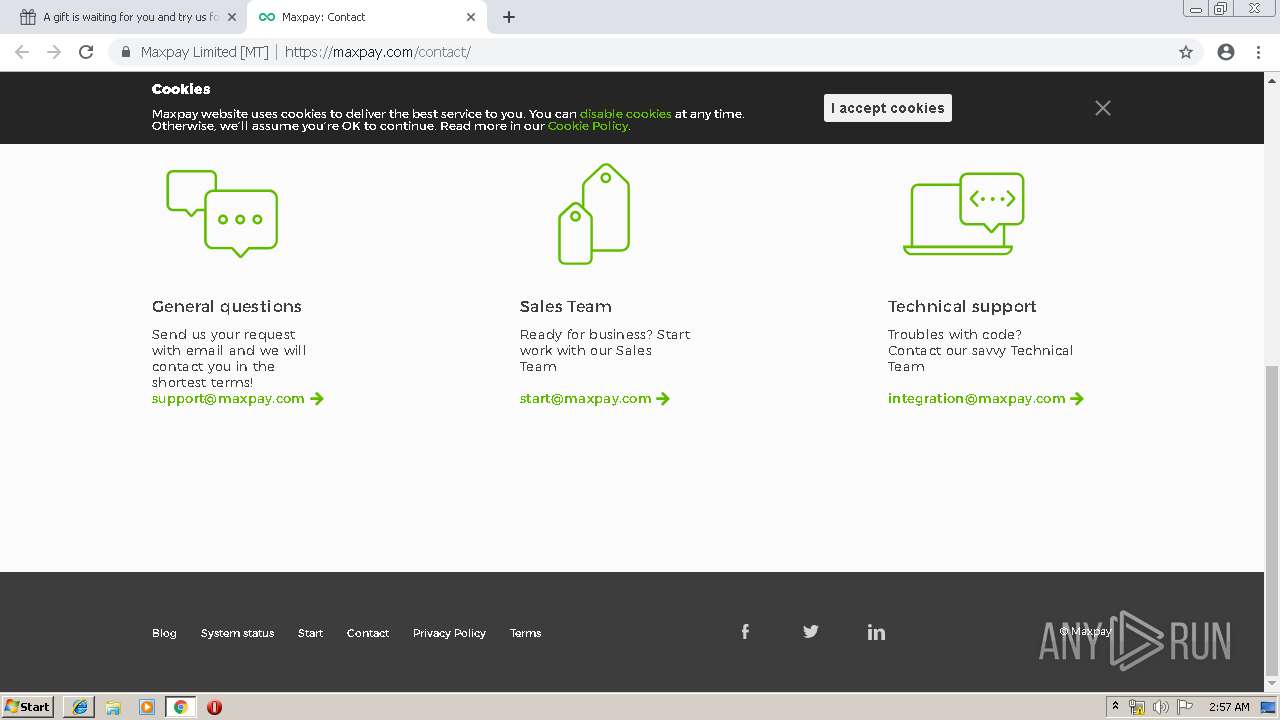
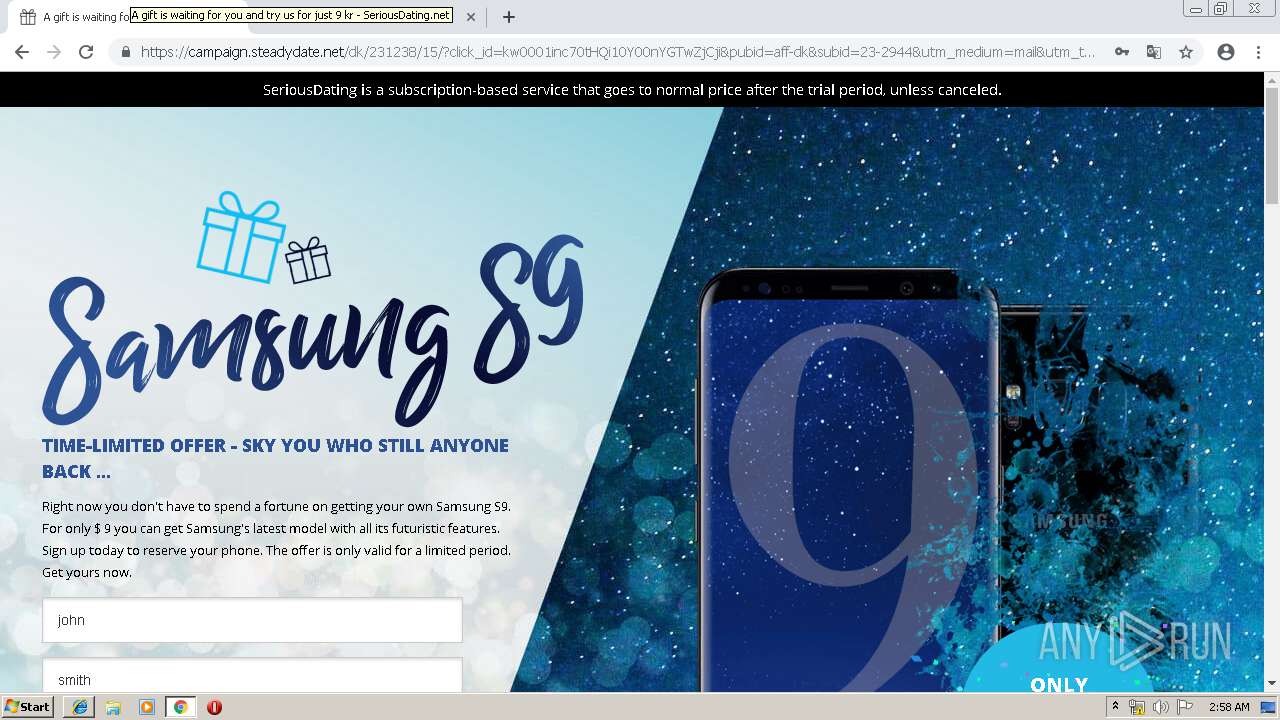
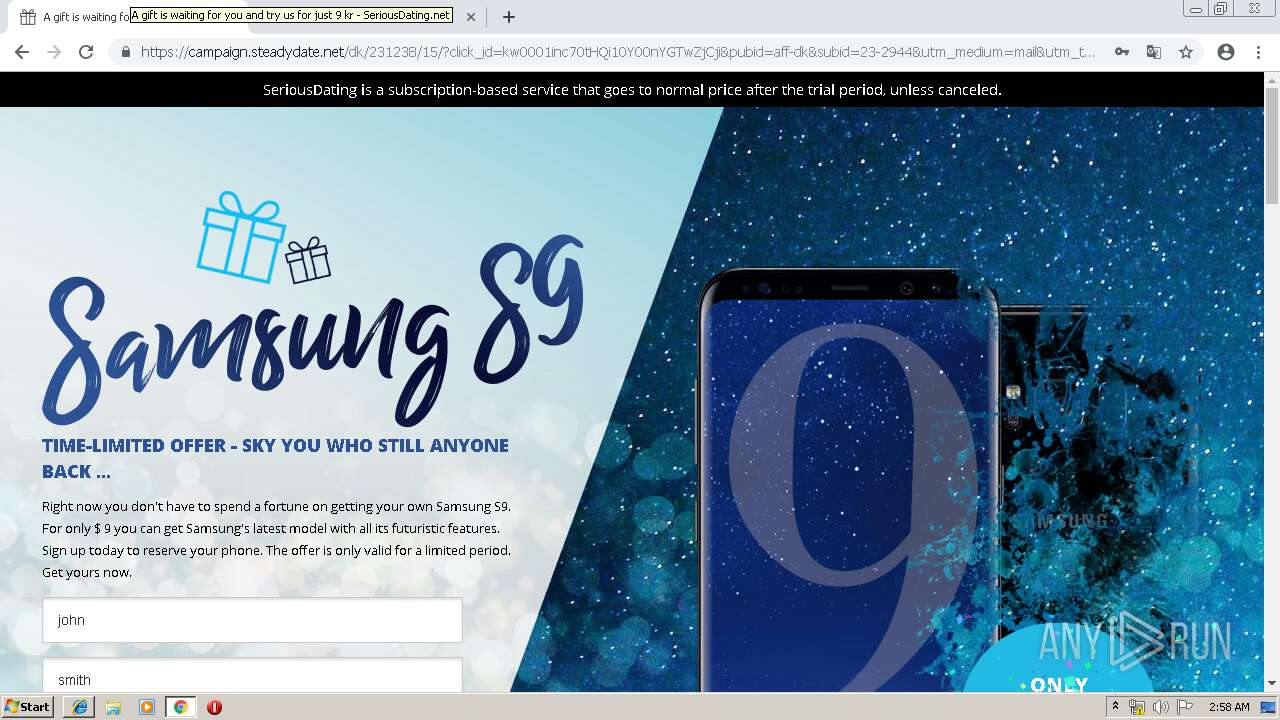
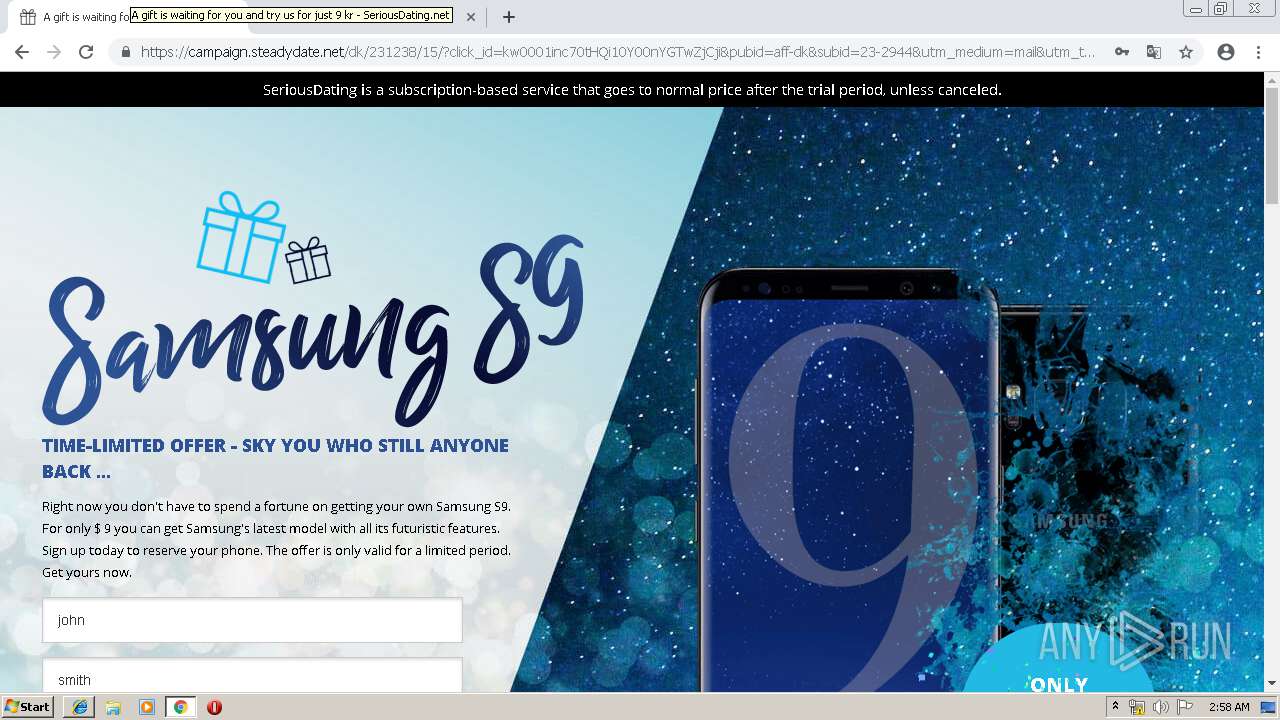
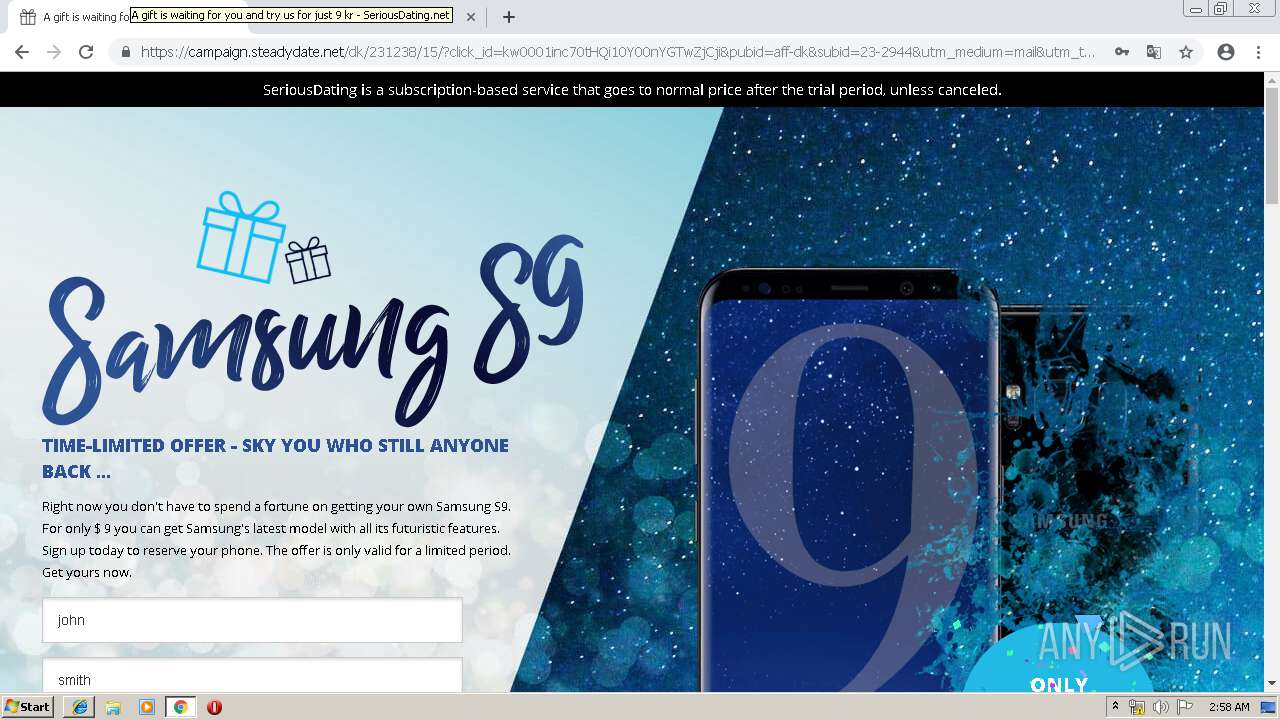
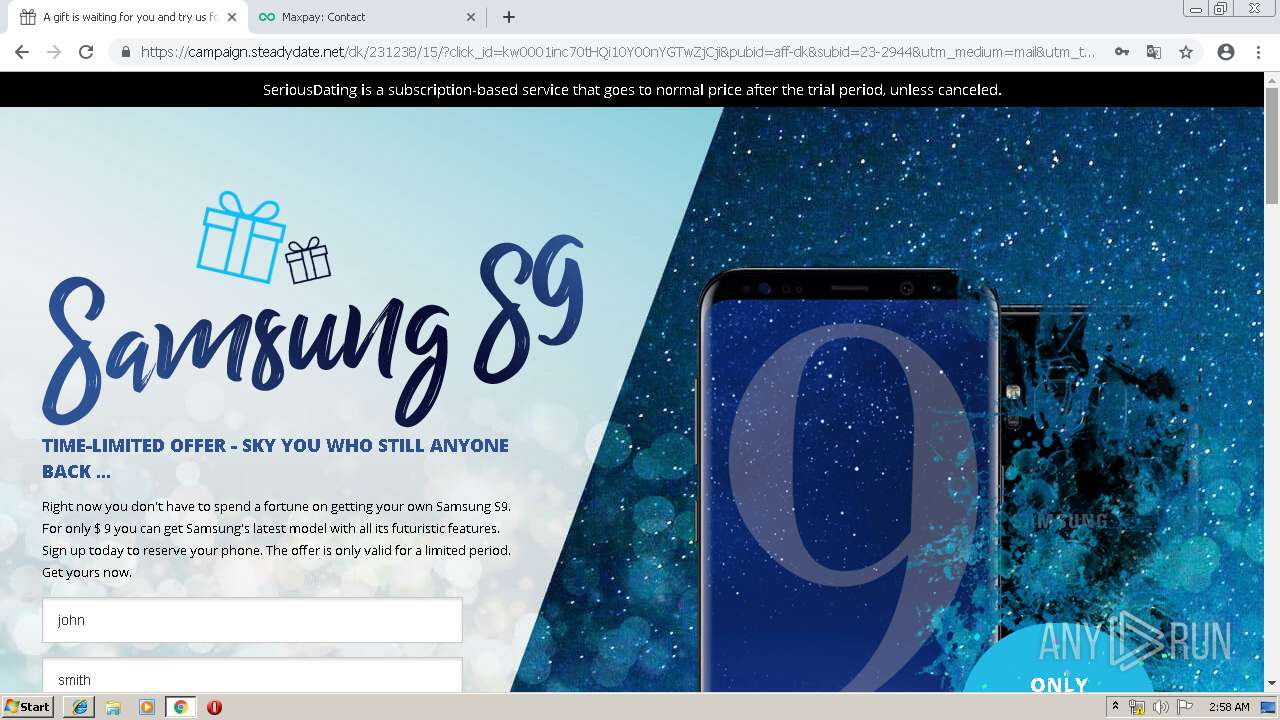
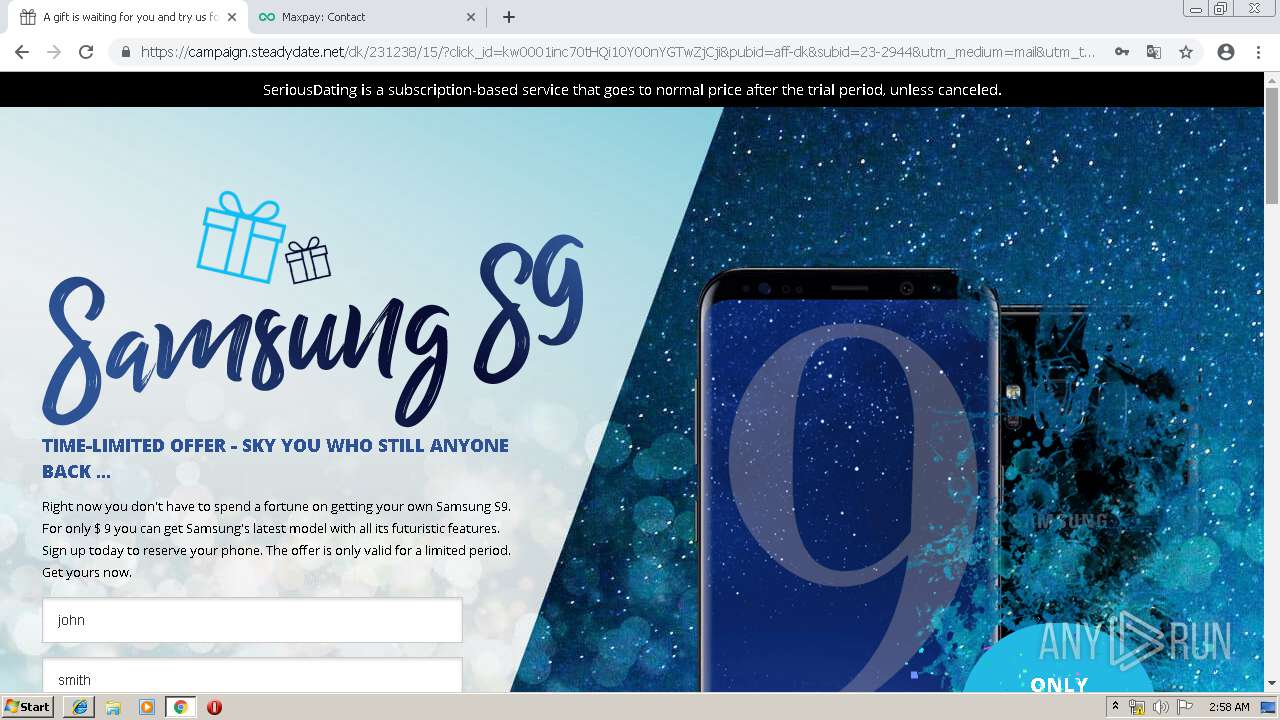
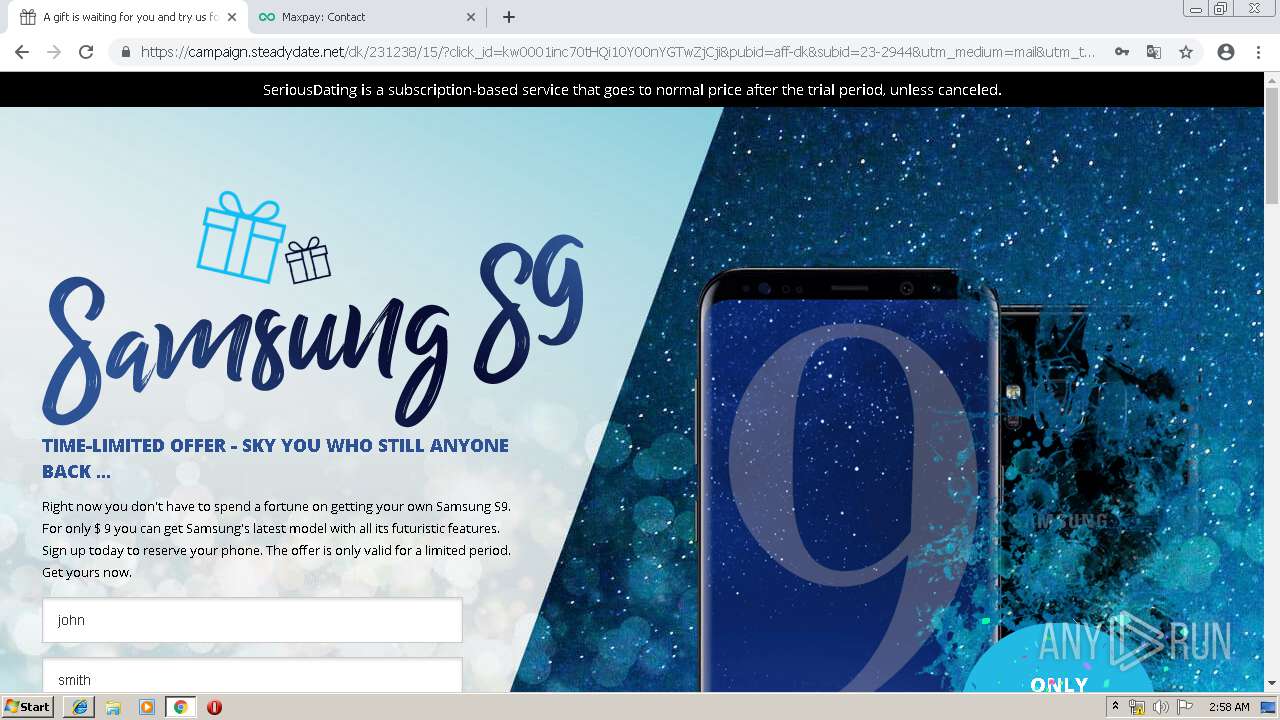
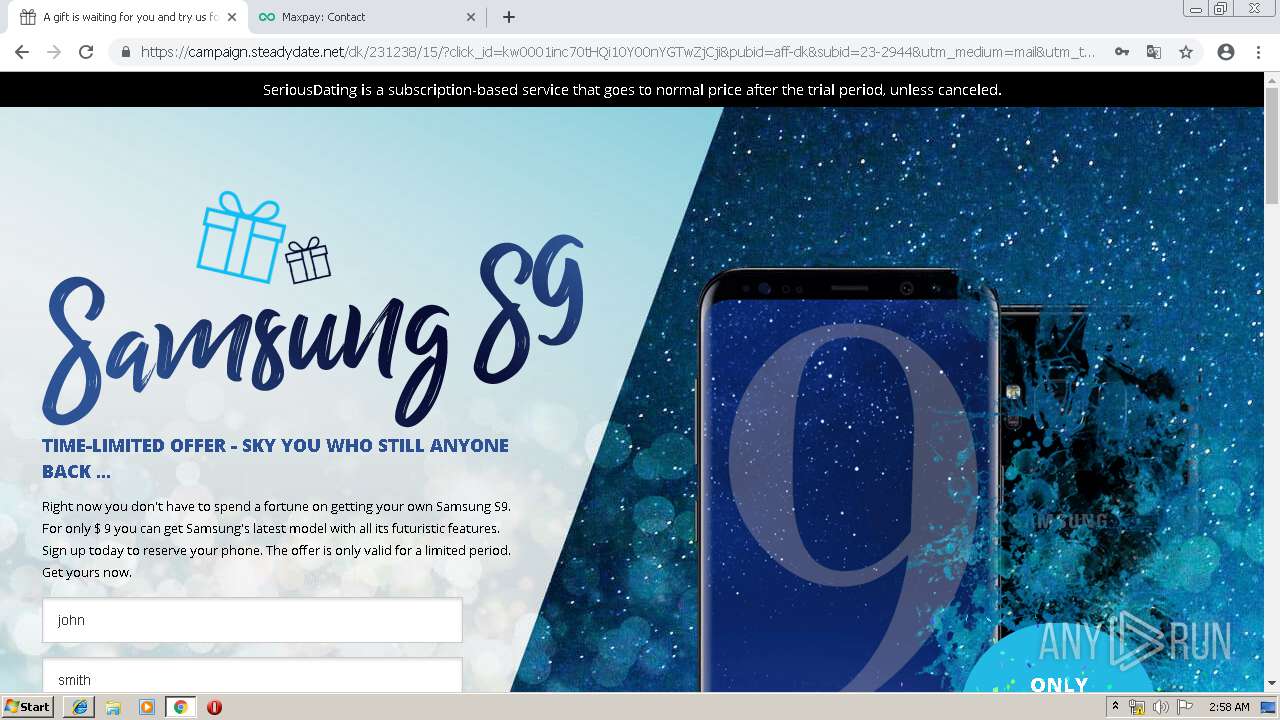
| URL: | http://h1.ripway.com/anniebluesky/blogustudent.png |
| Full analysis: | https://app.any.run/tasks/edf4dde9-8ab2-44ed-9f20-51a9bd543be8 |
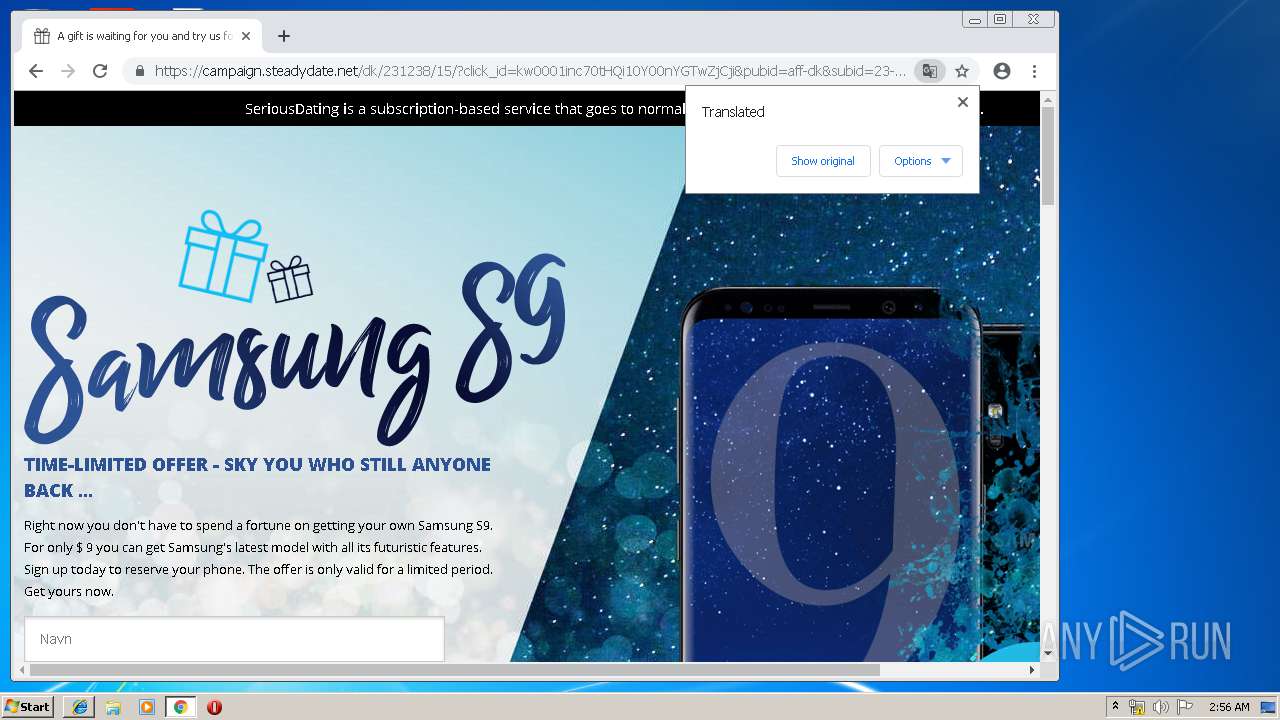
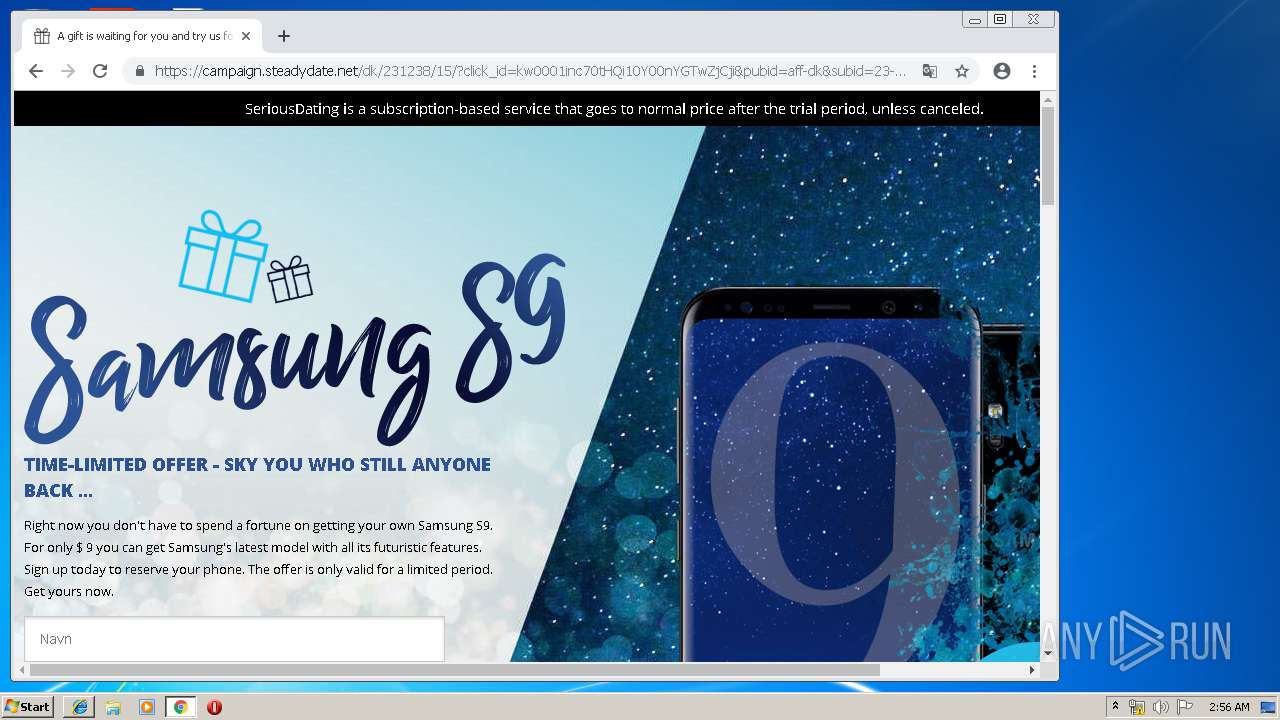
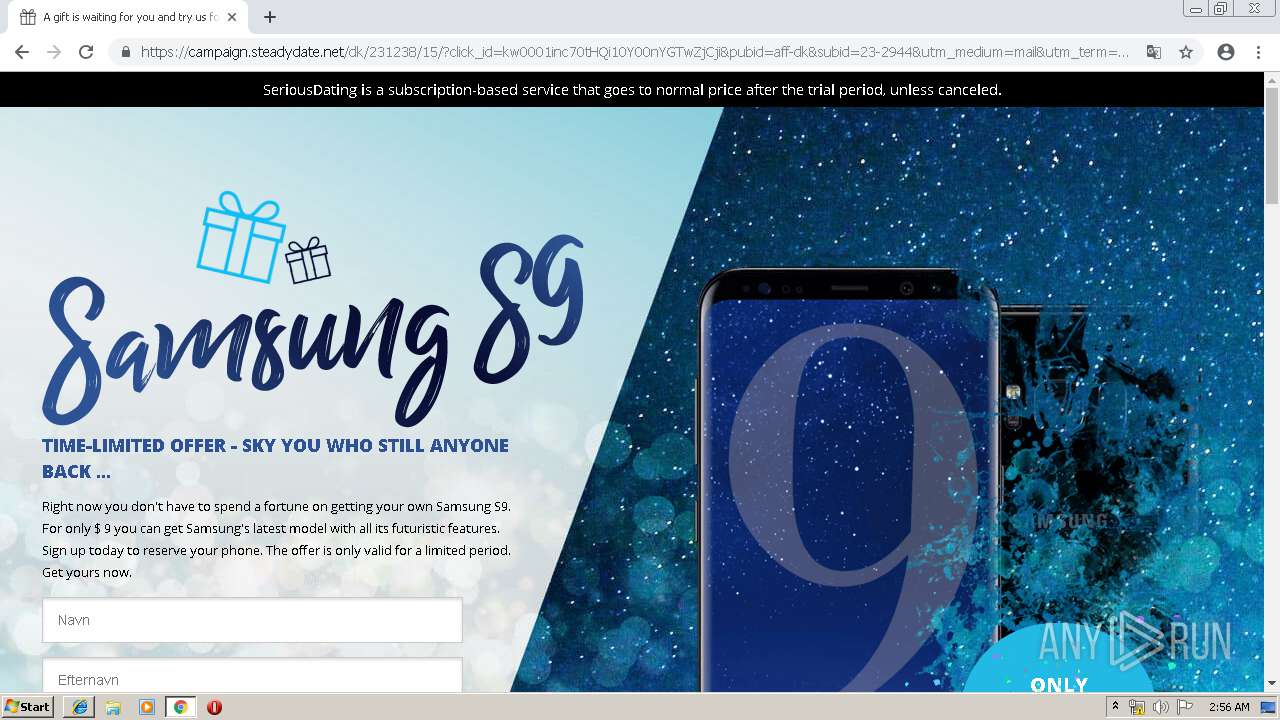
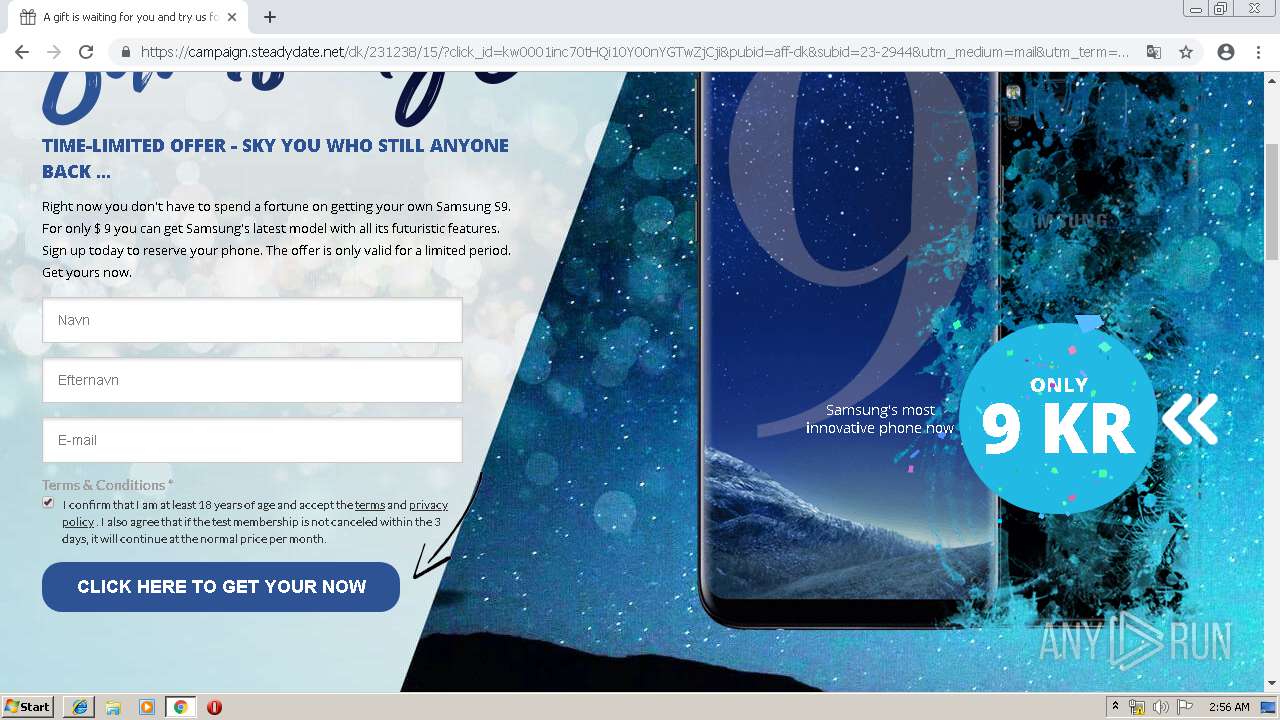
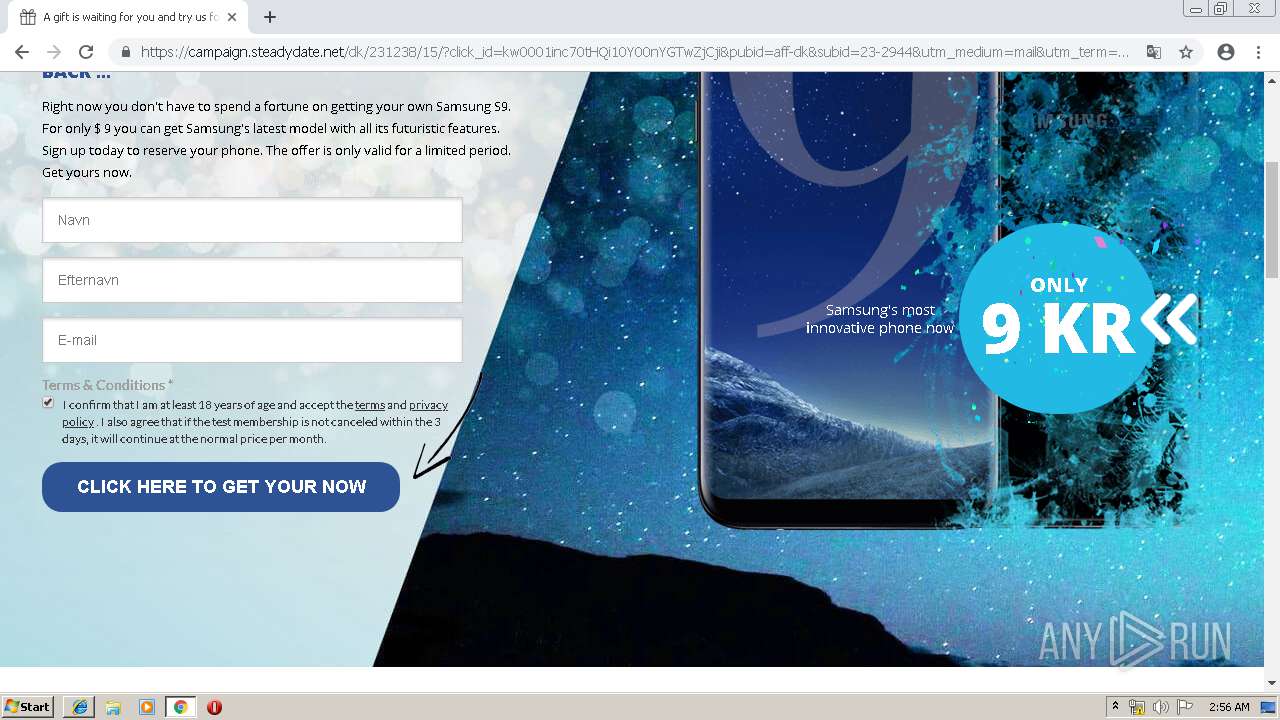
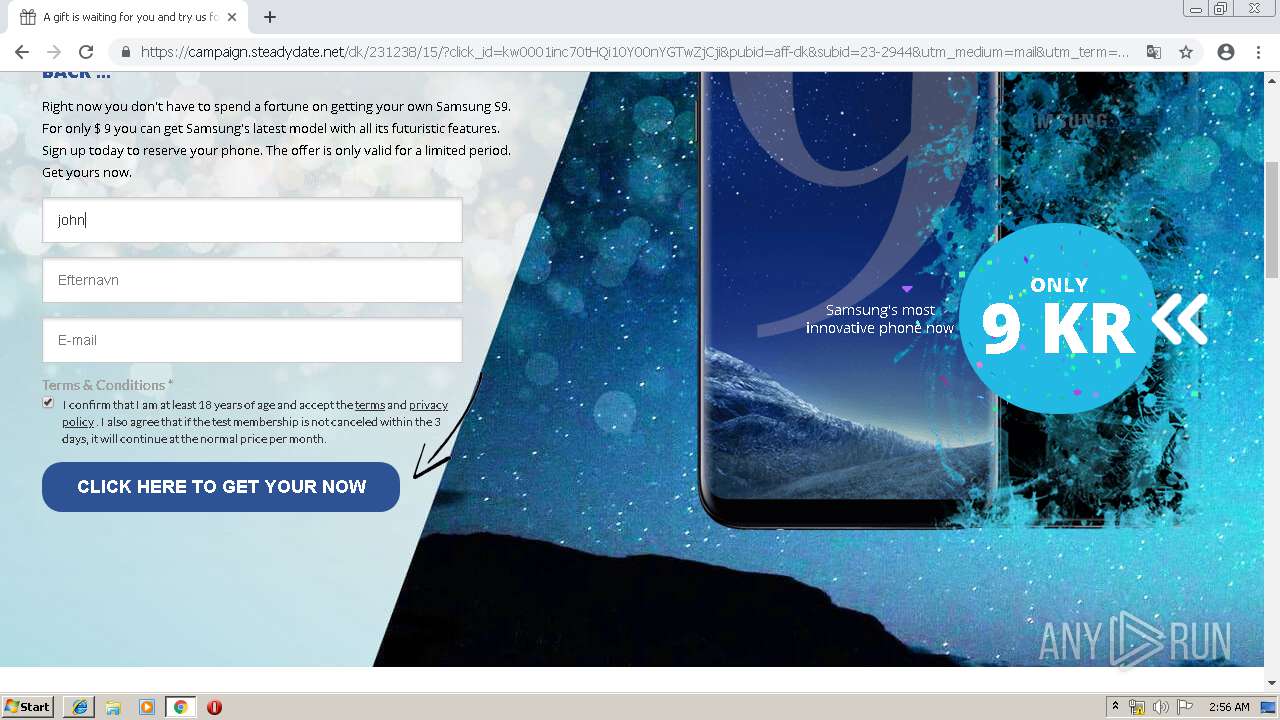
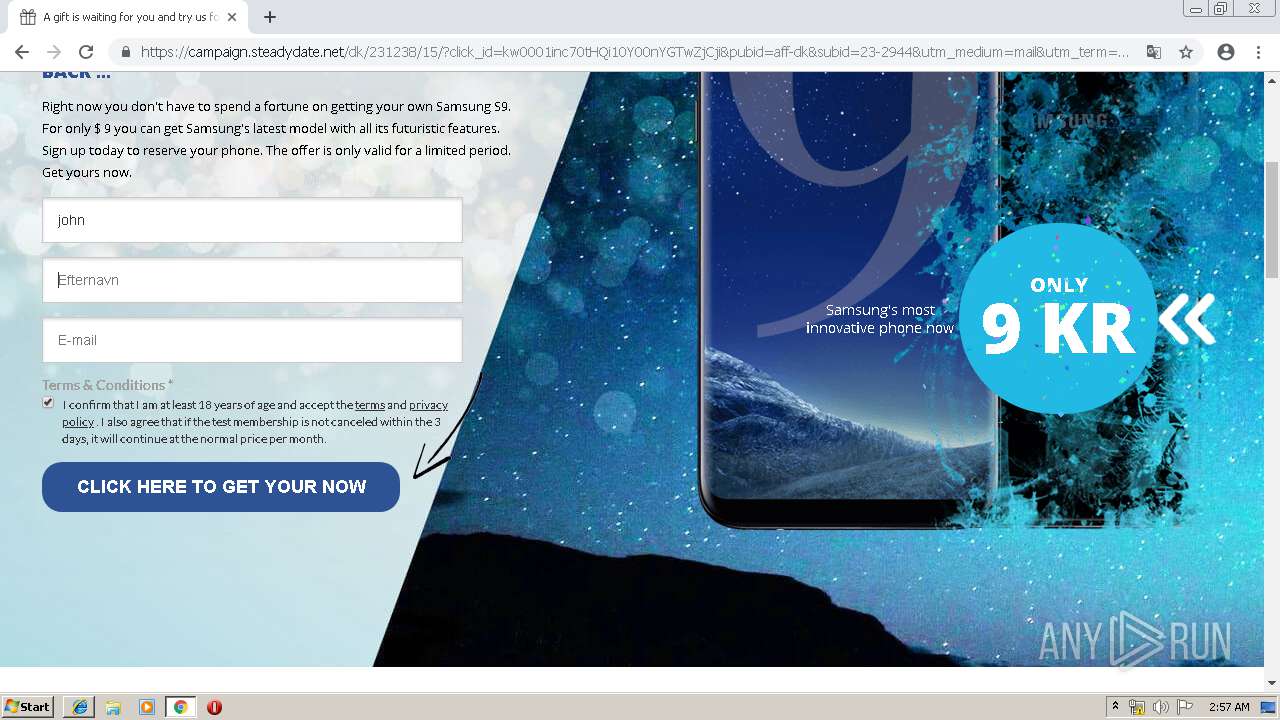
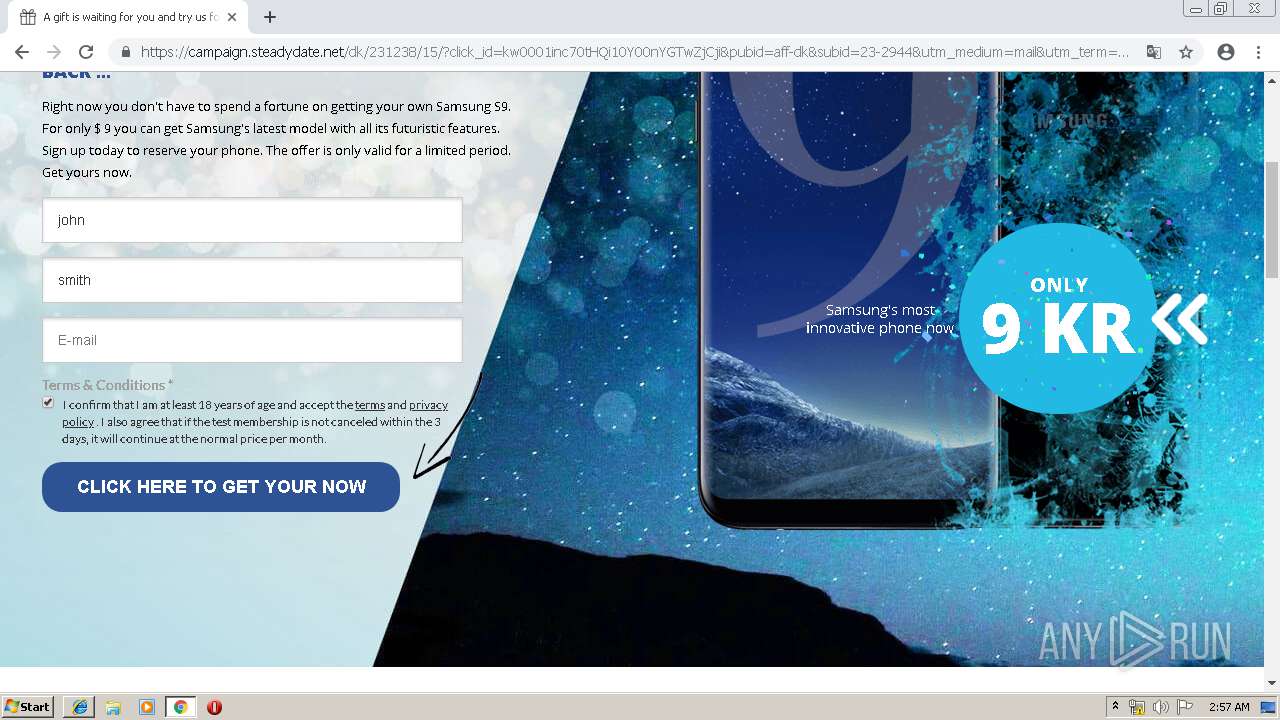
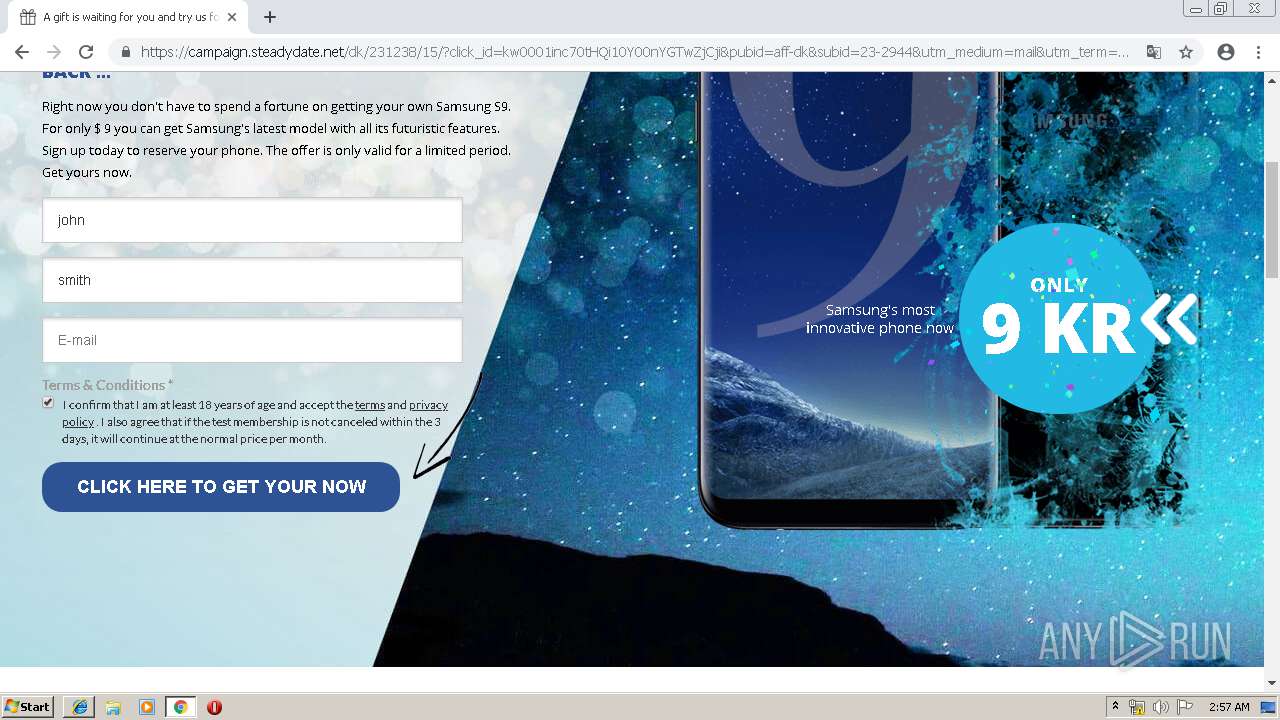
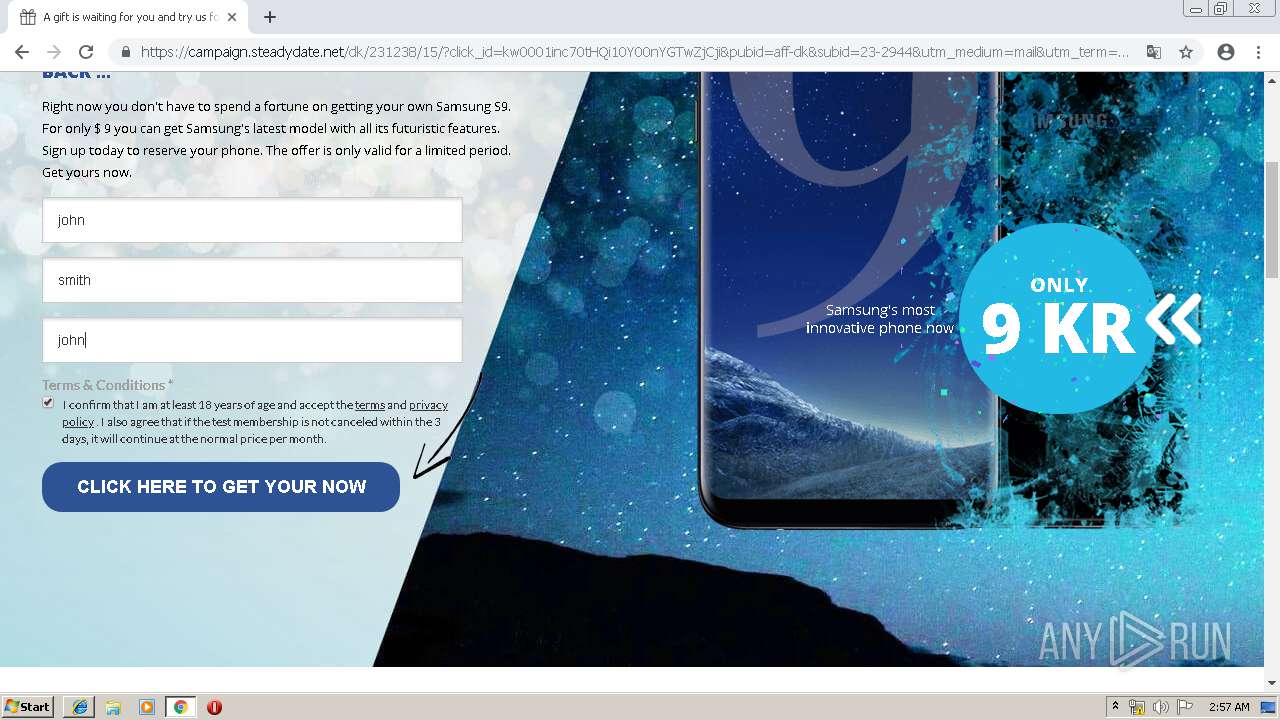
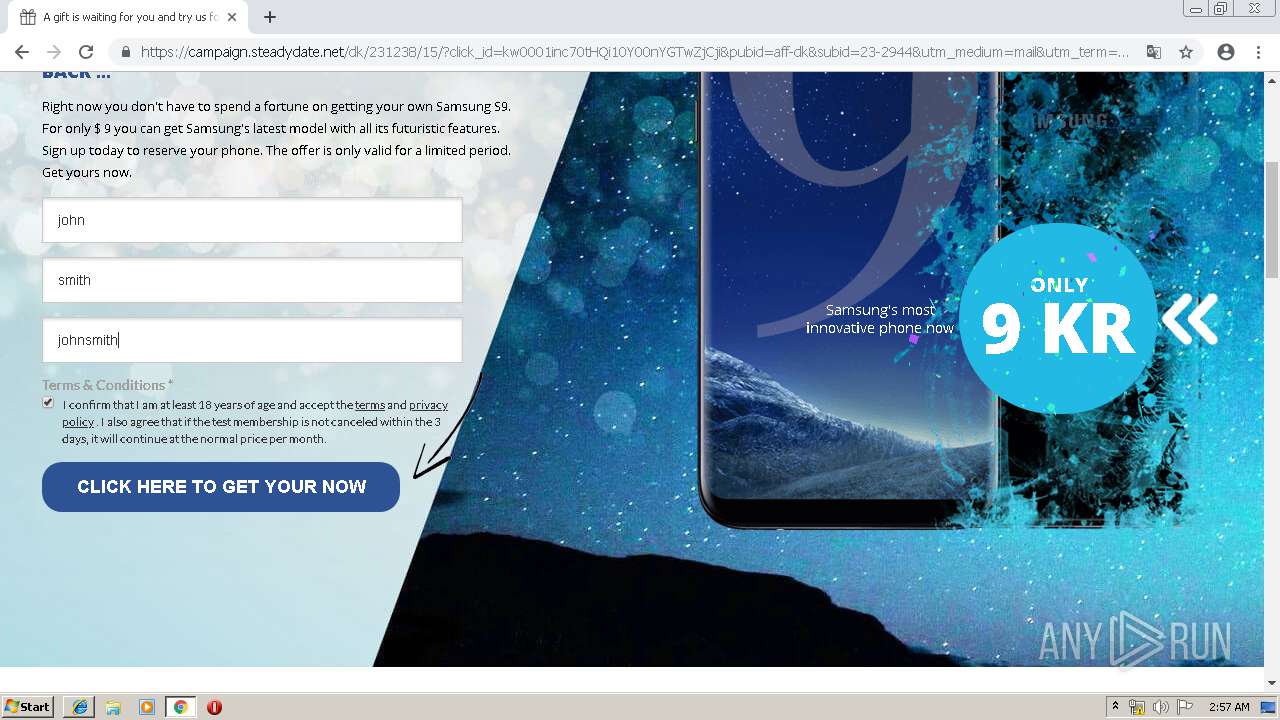
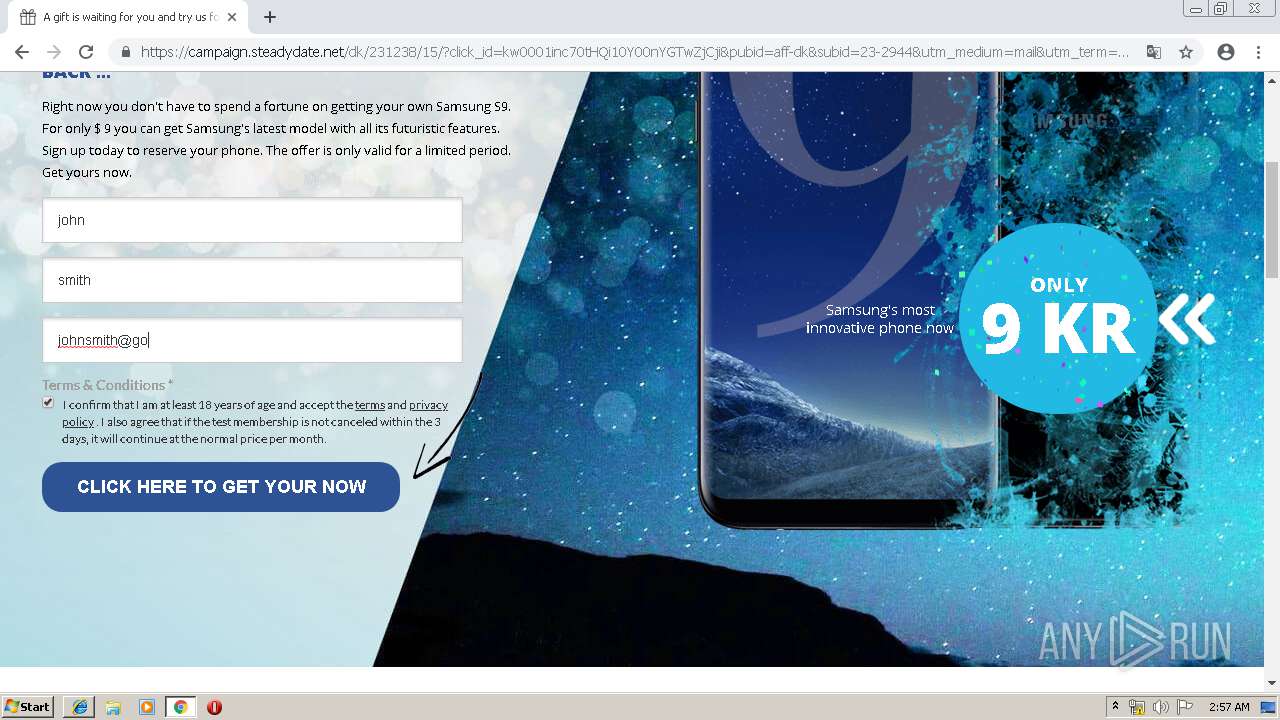
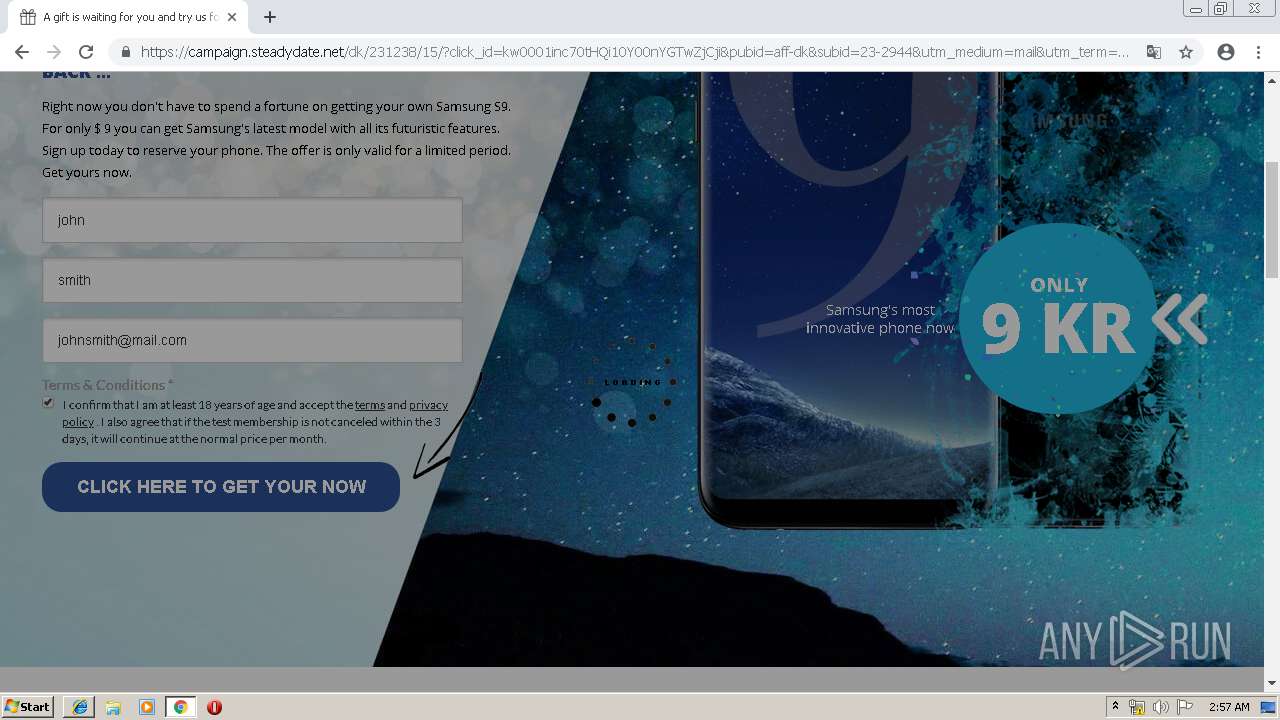
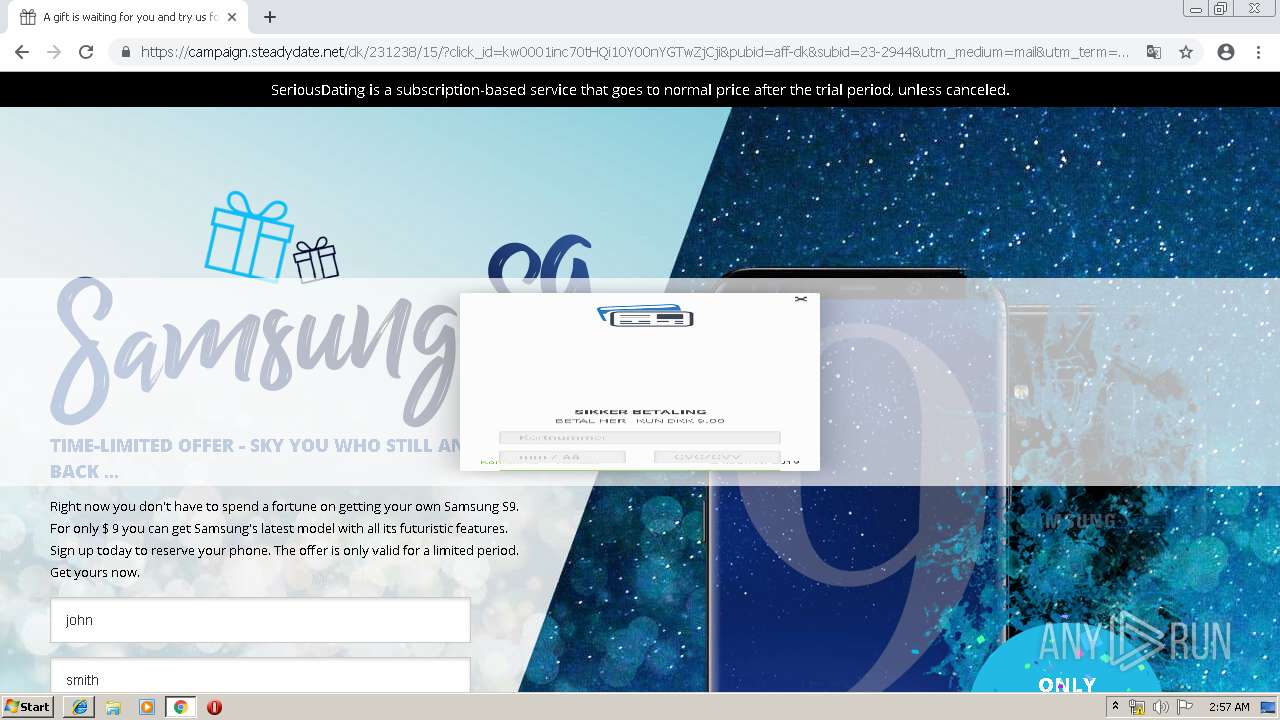
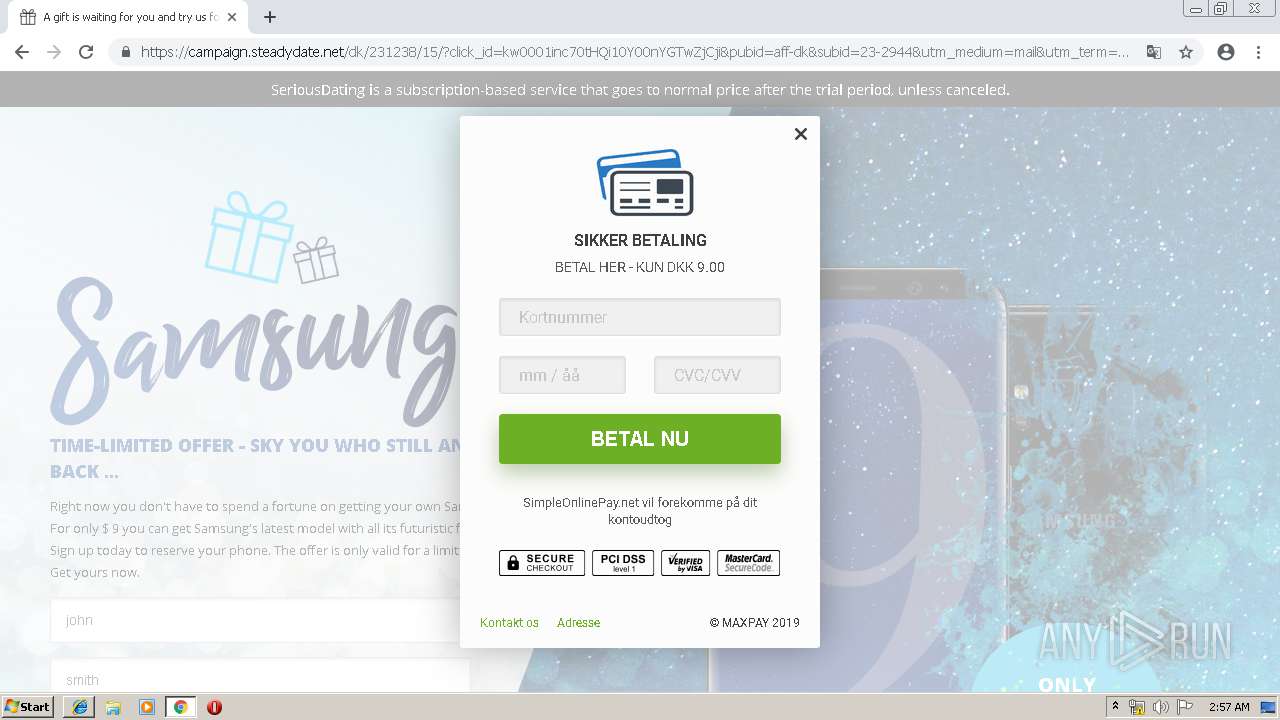
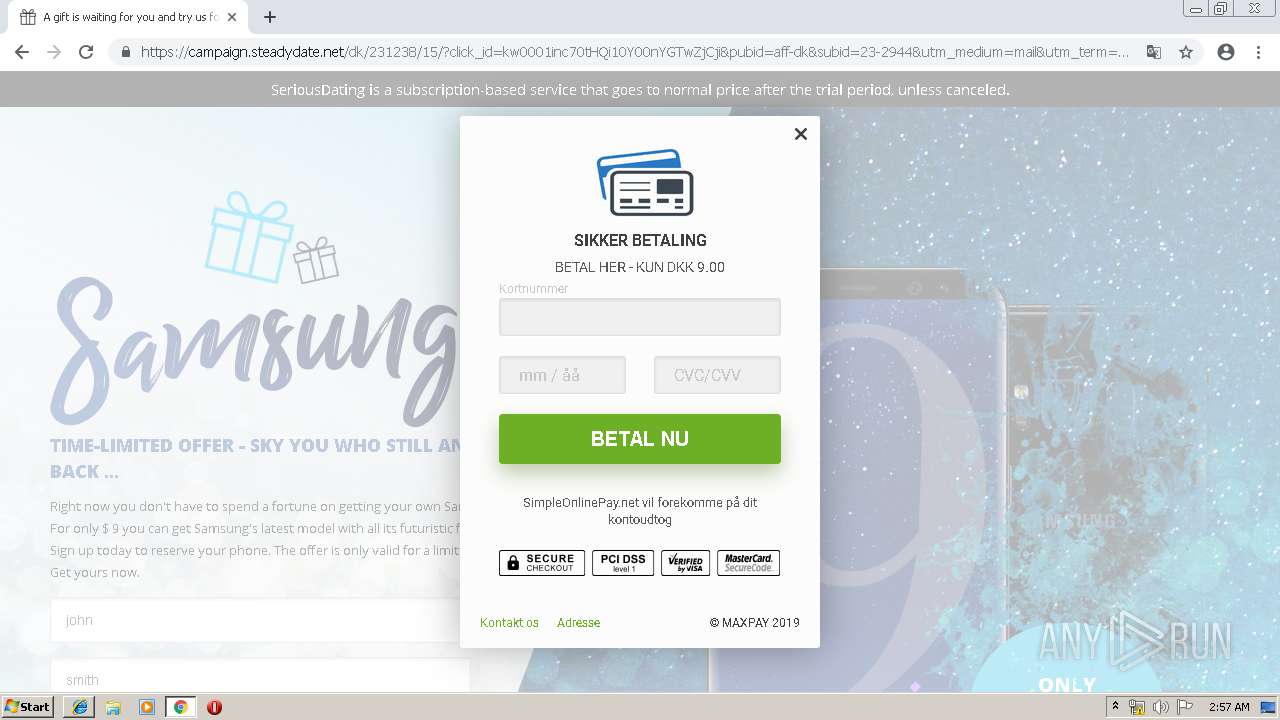
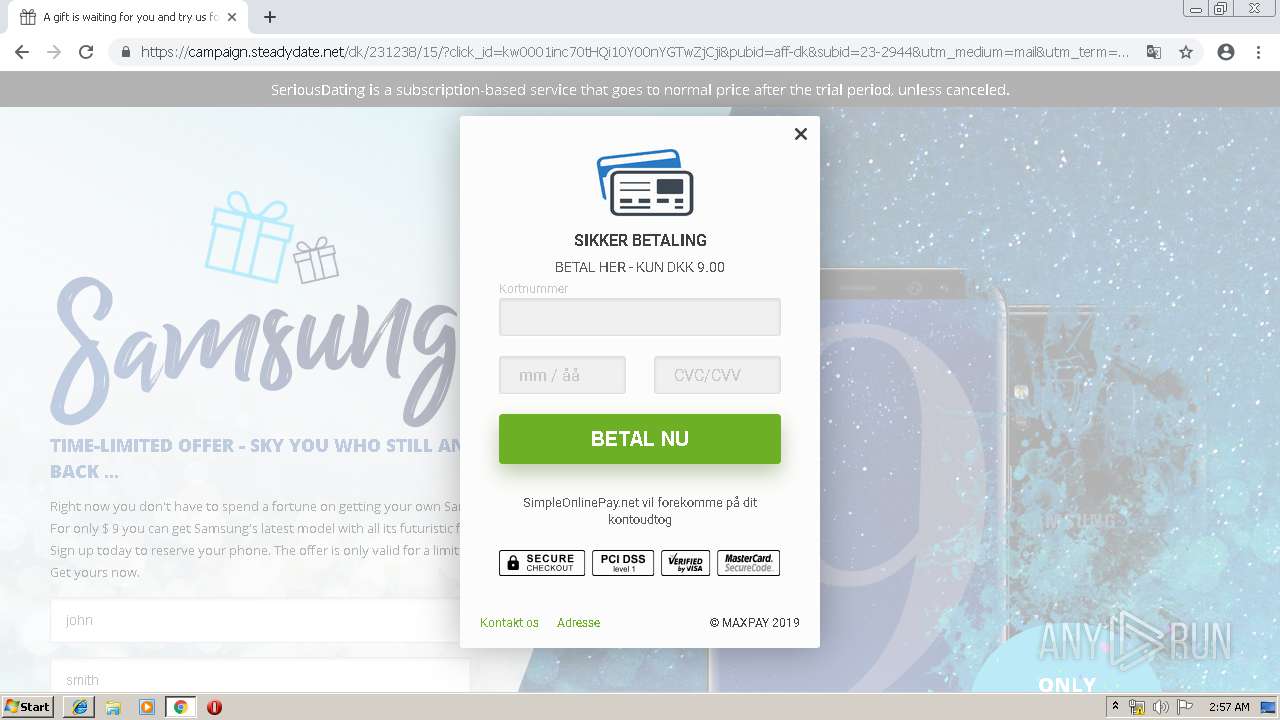
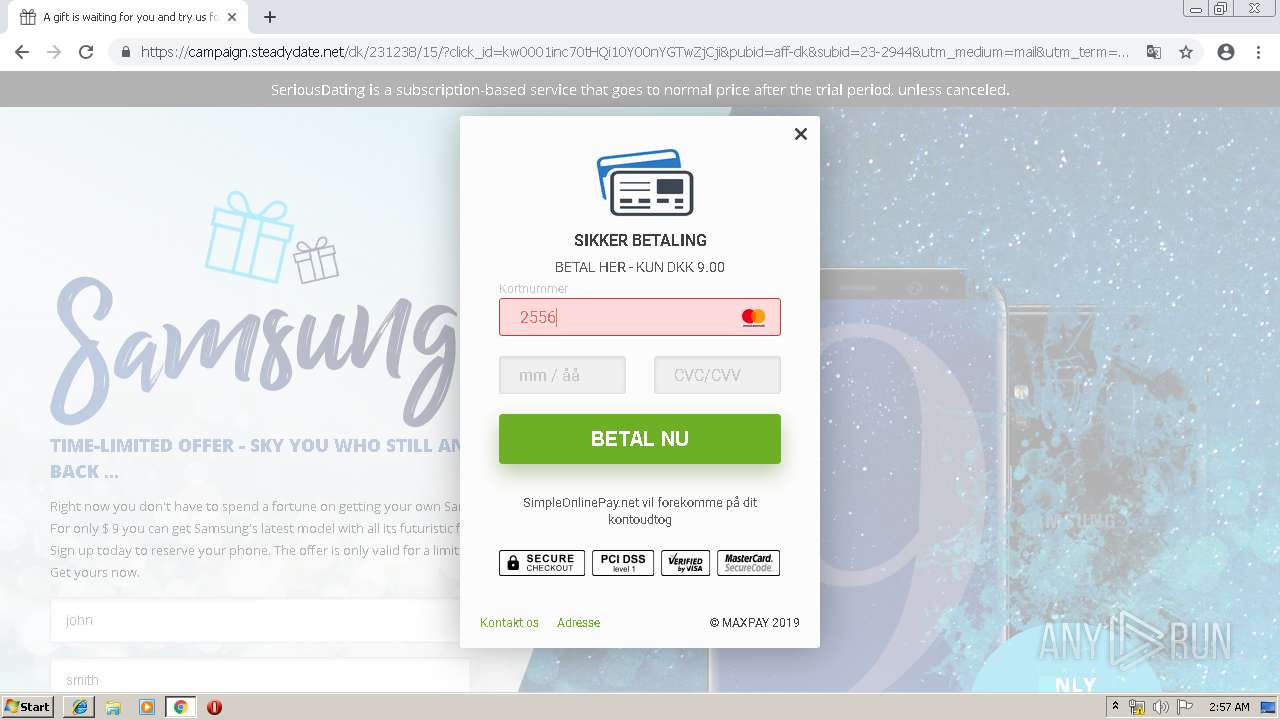
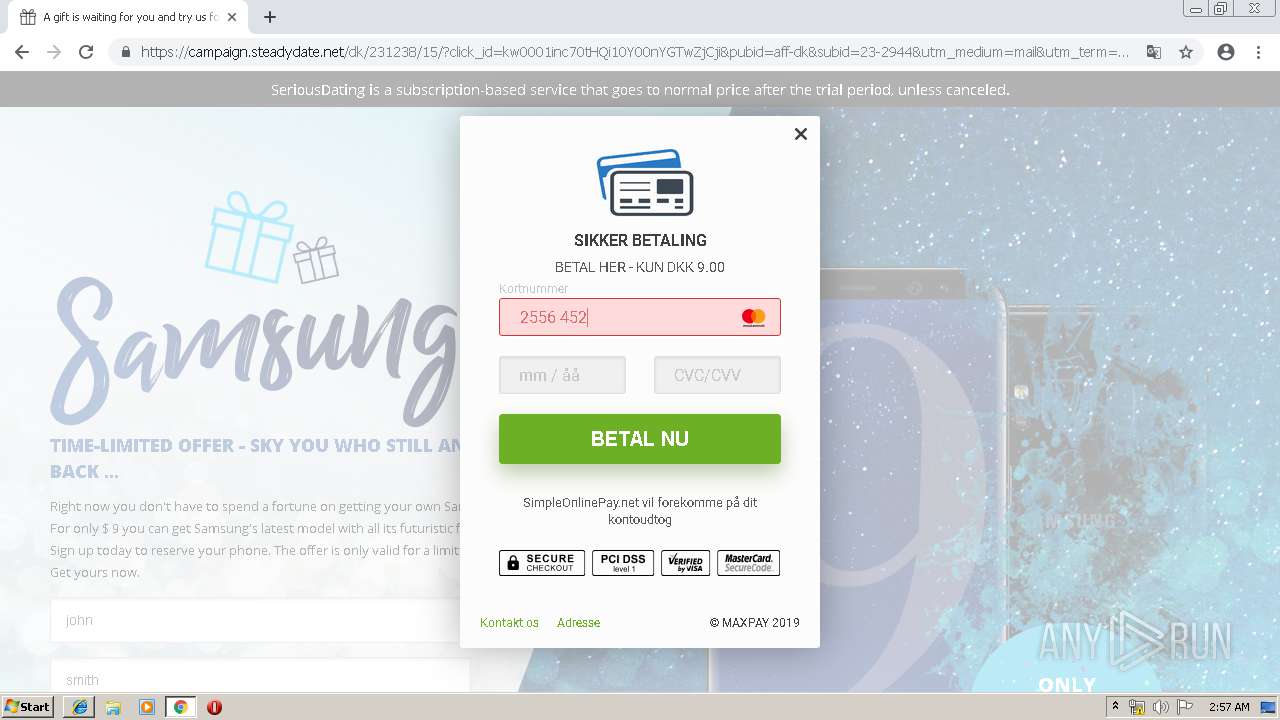
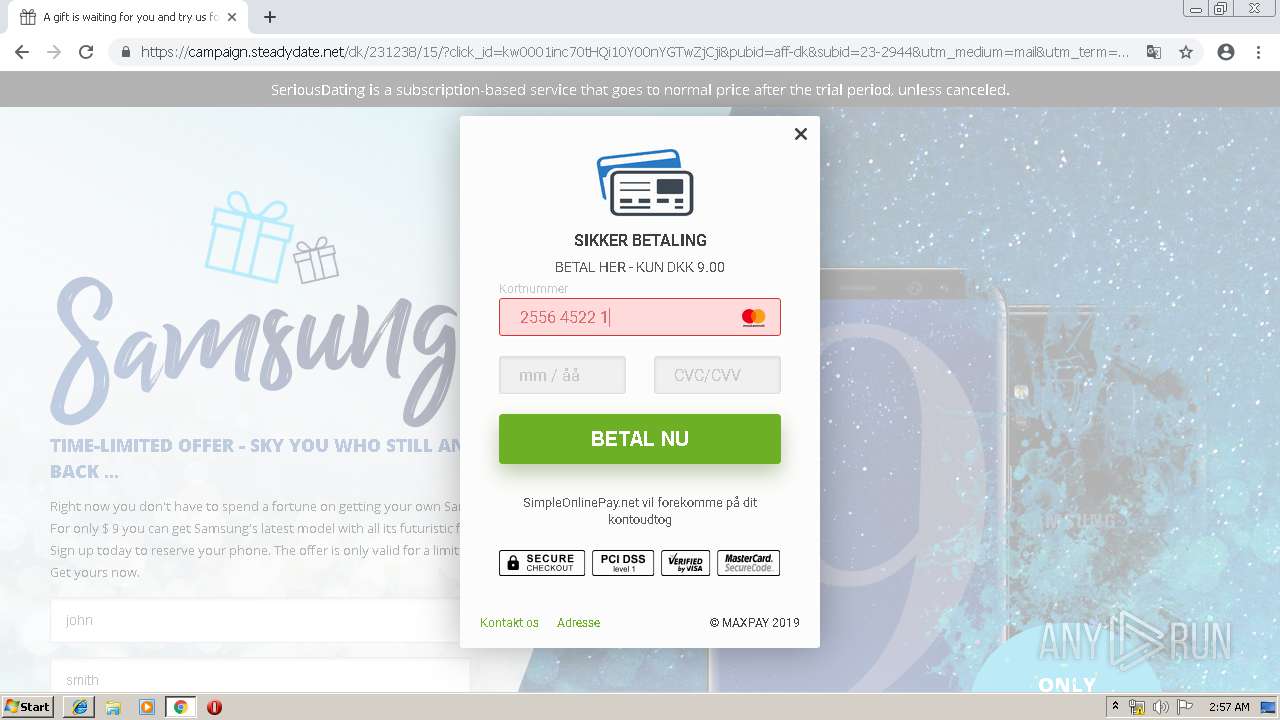
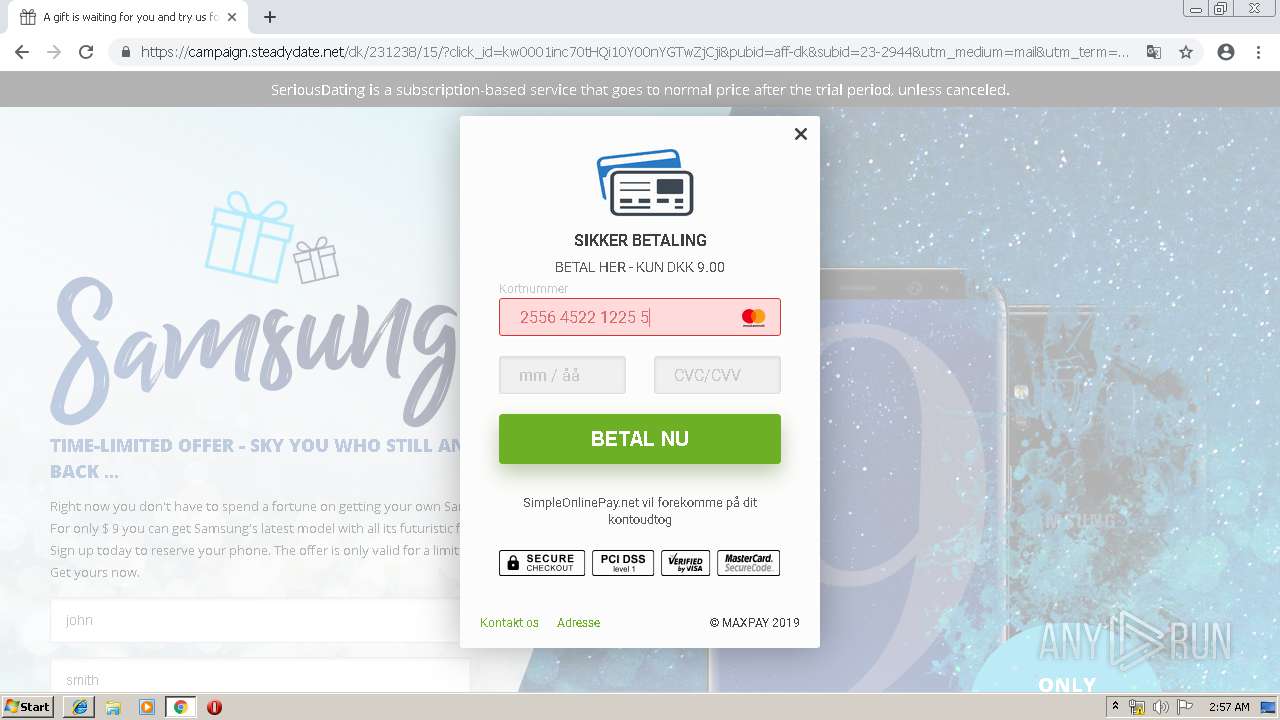
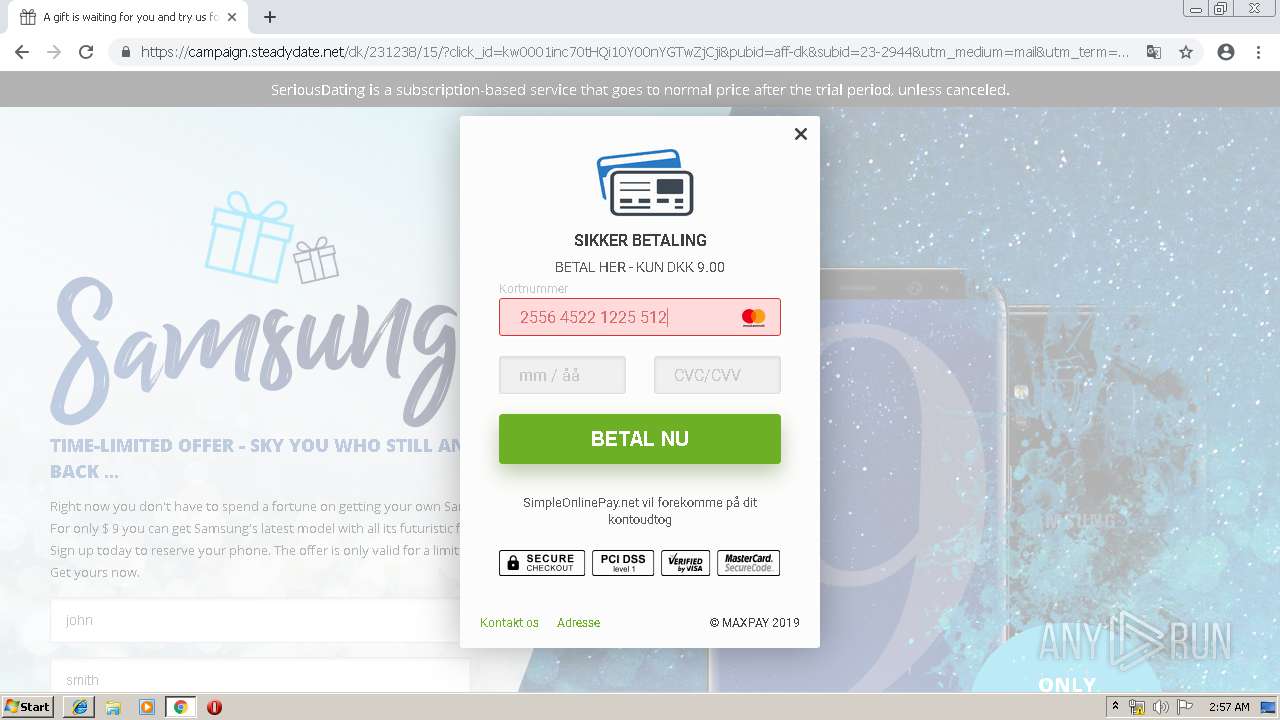
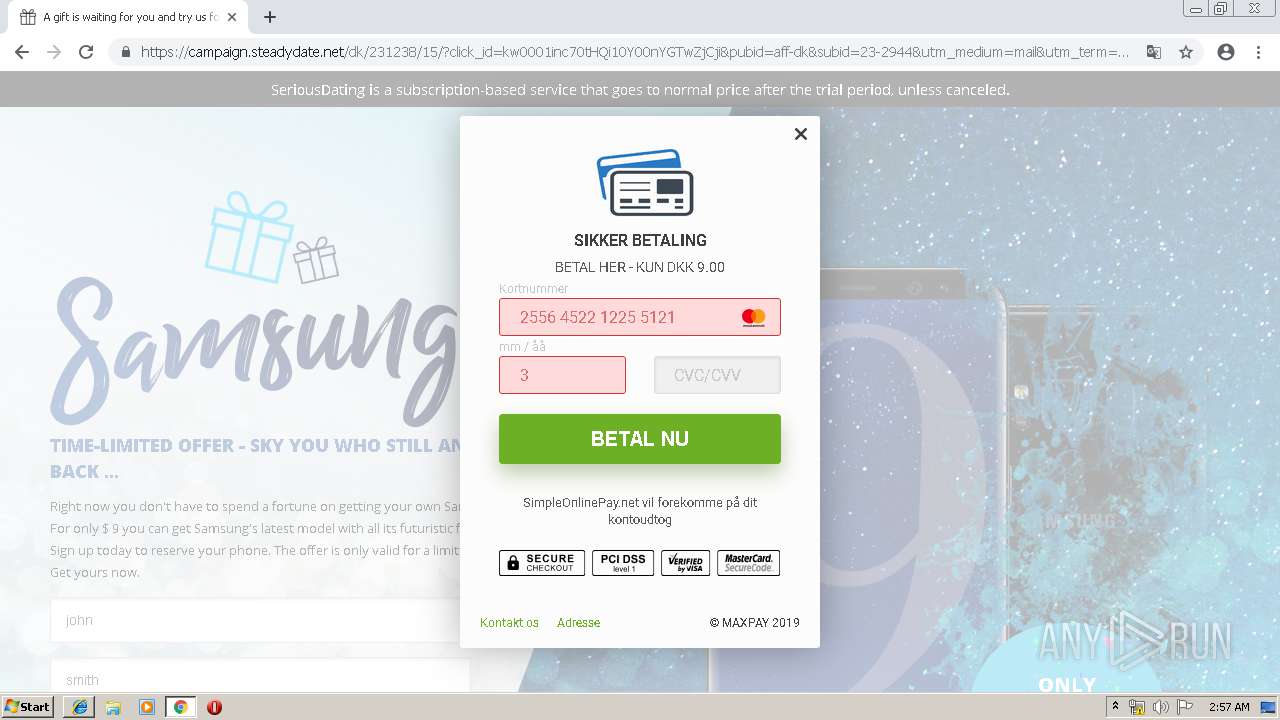
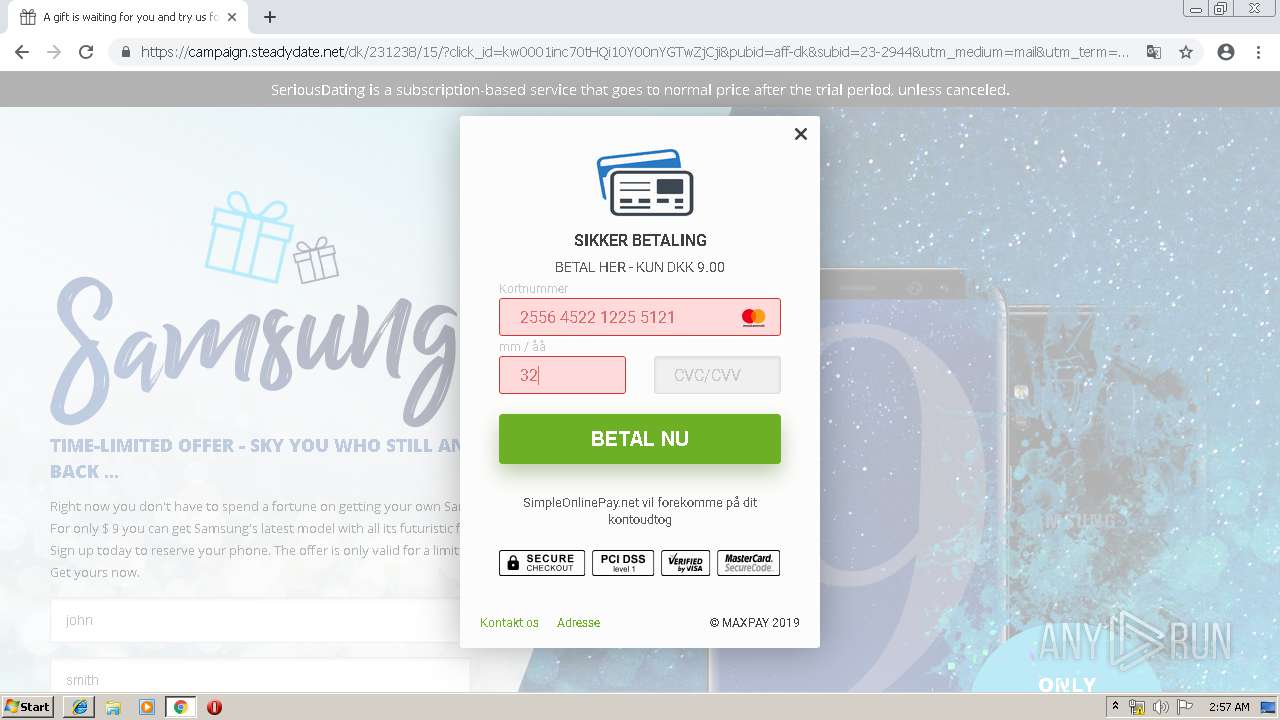
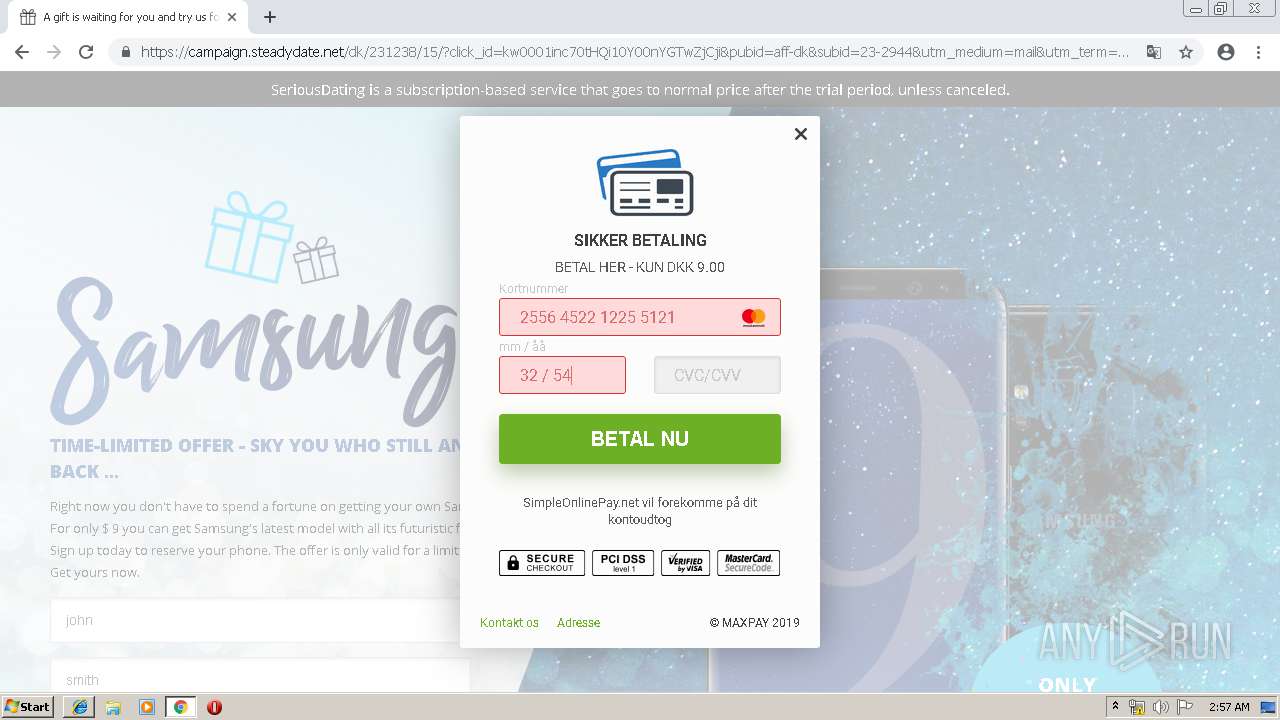
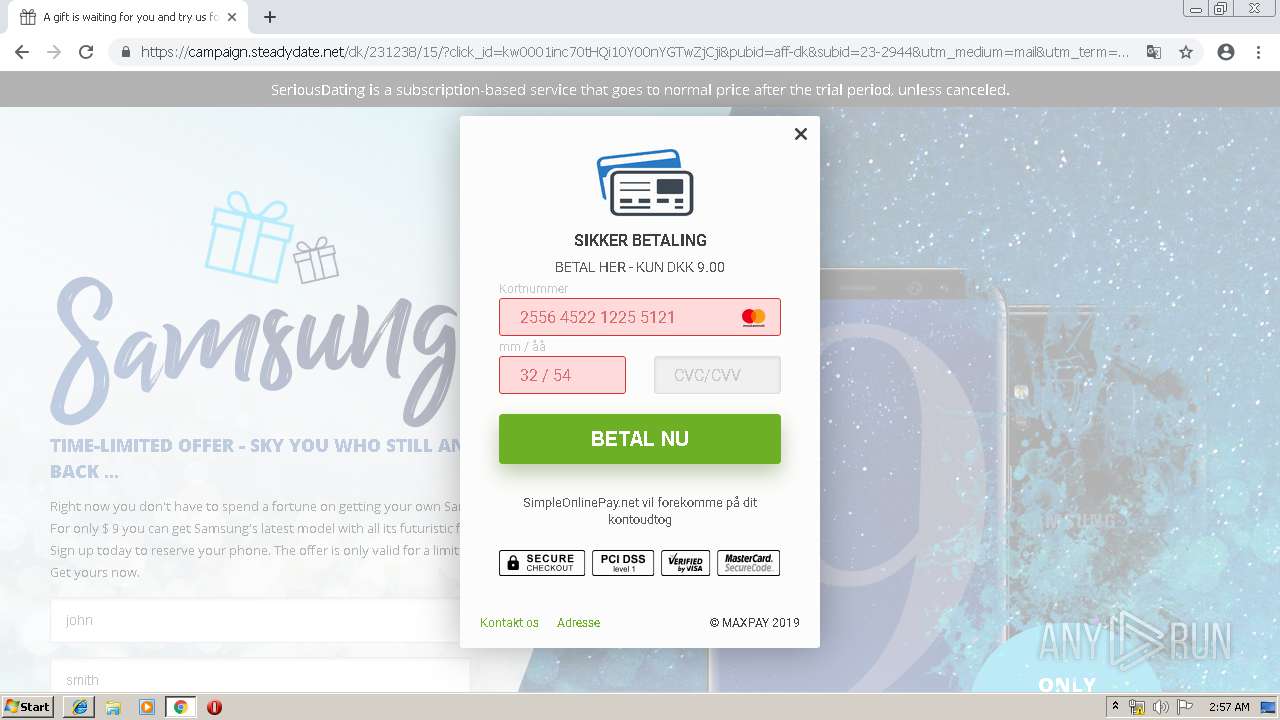
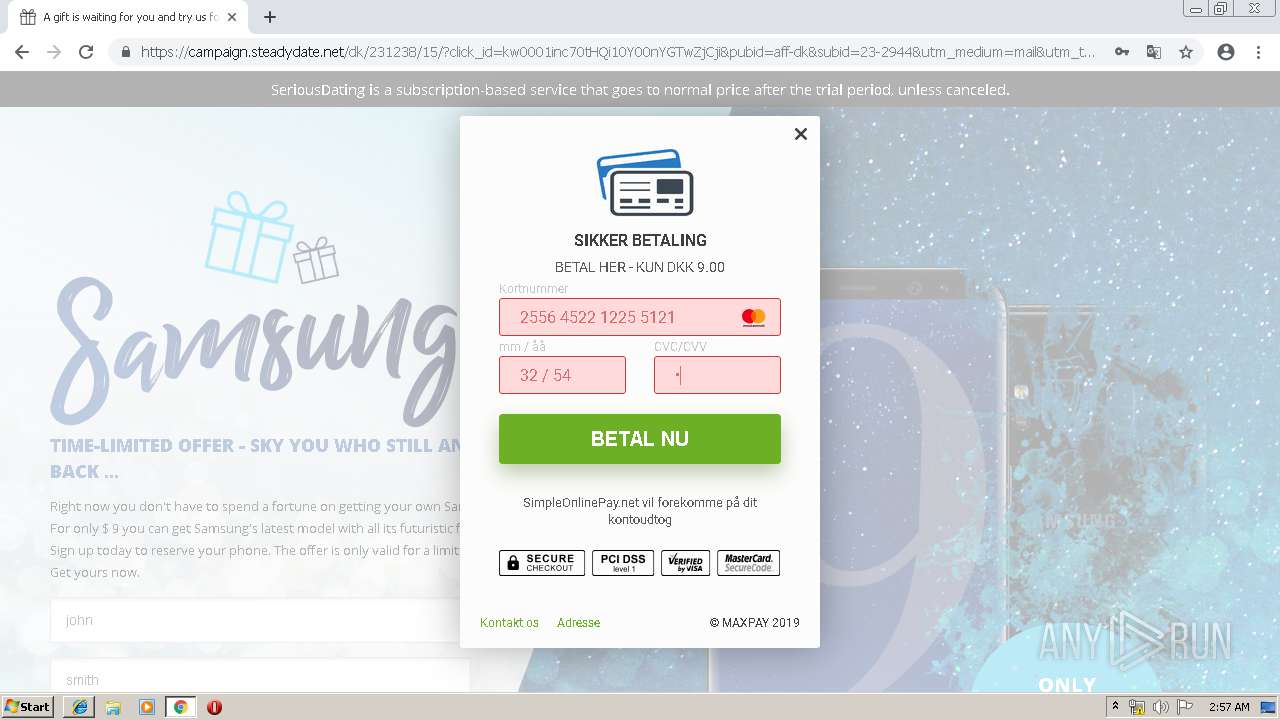
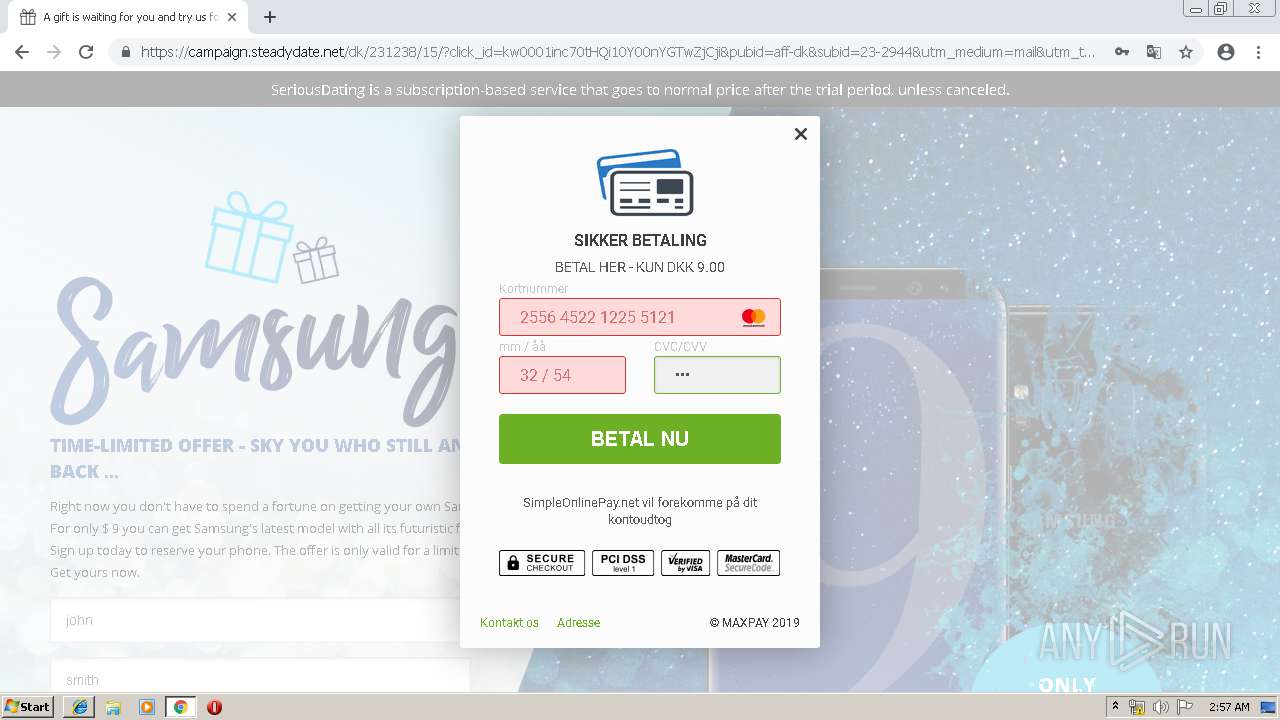
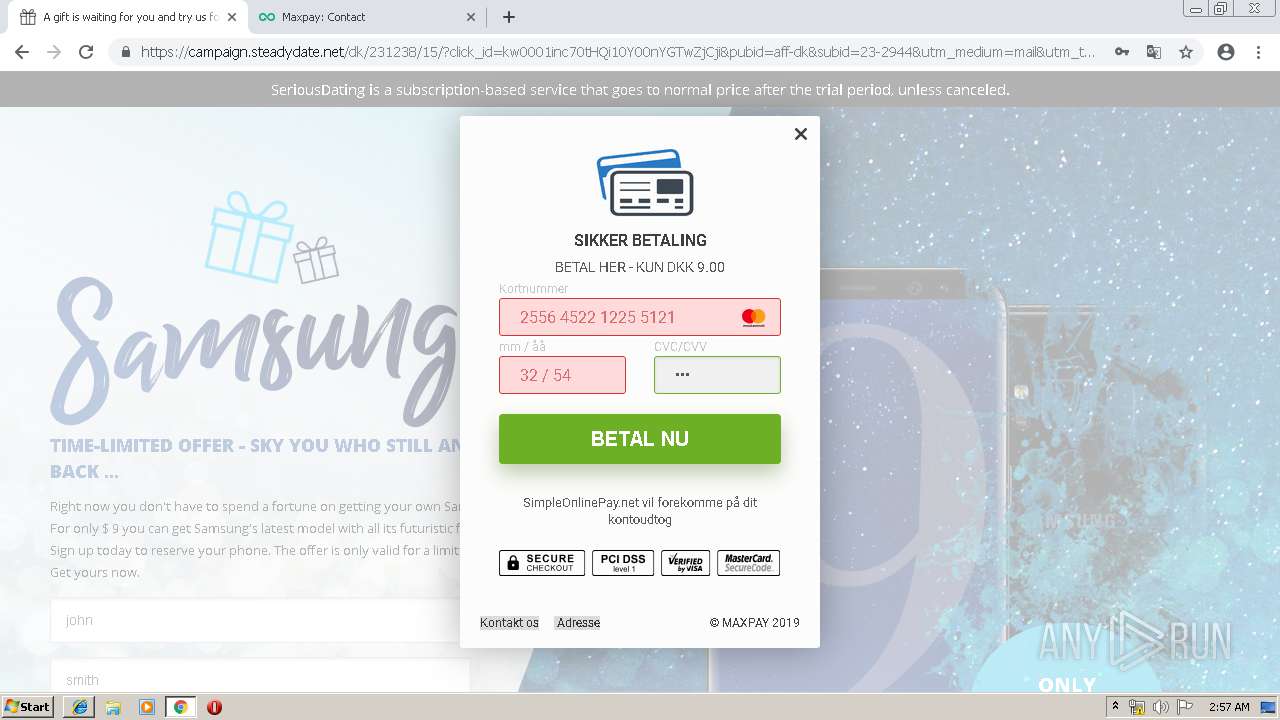
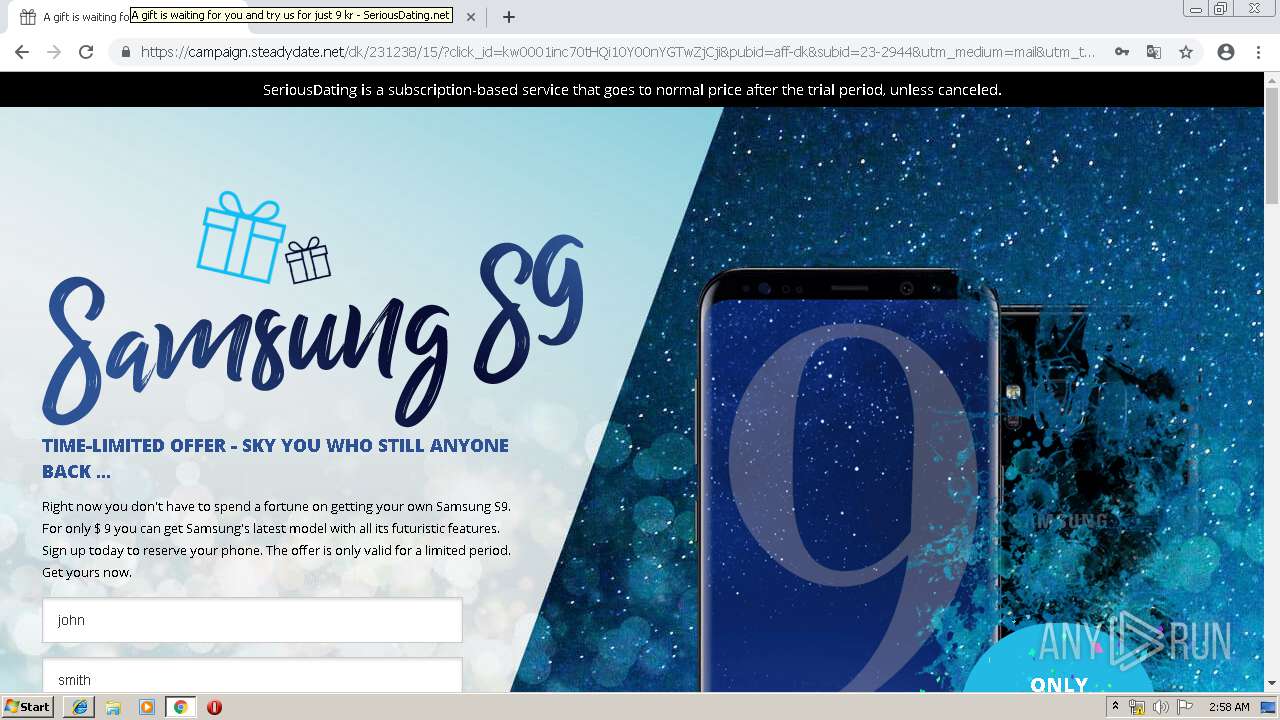
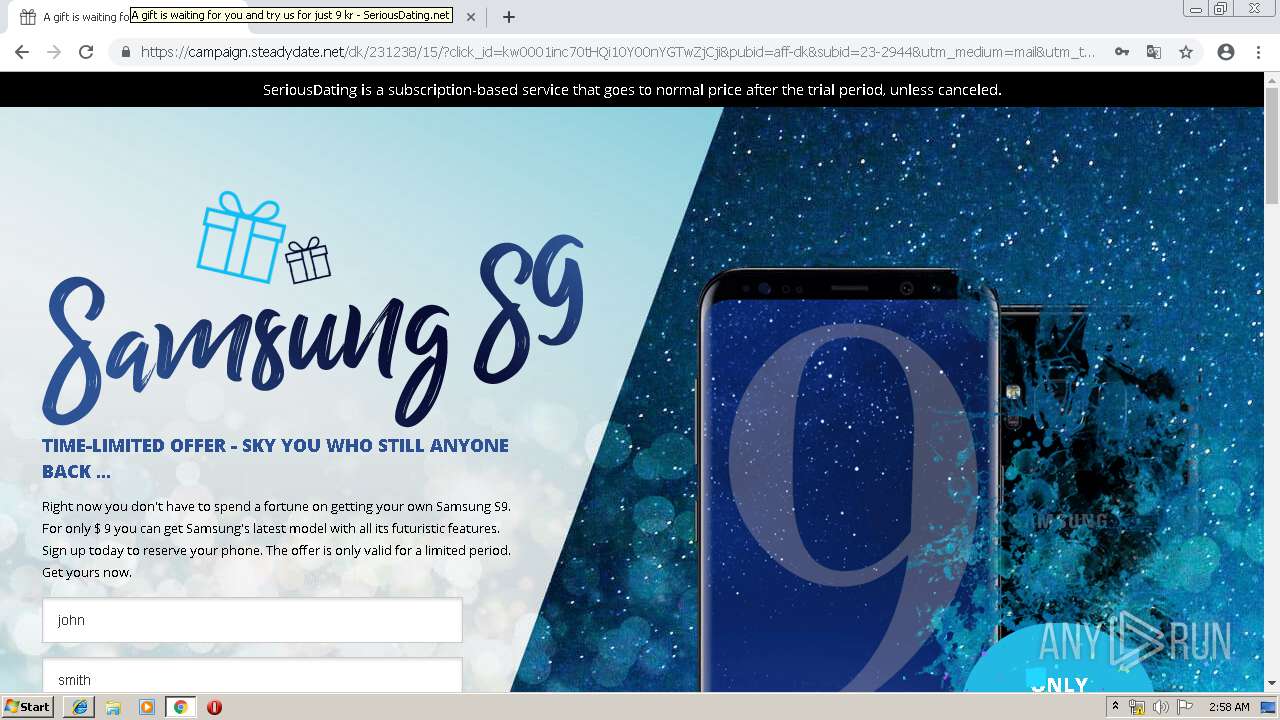
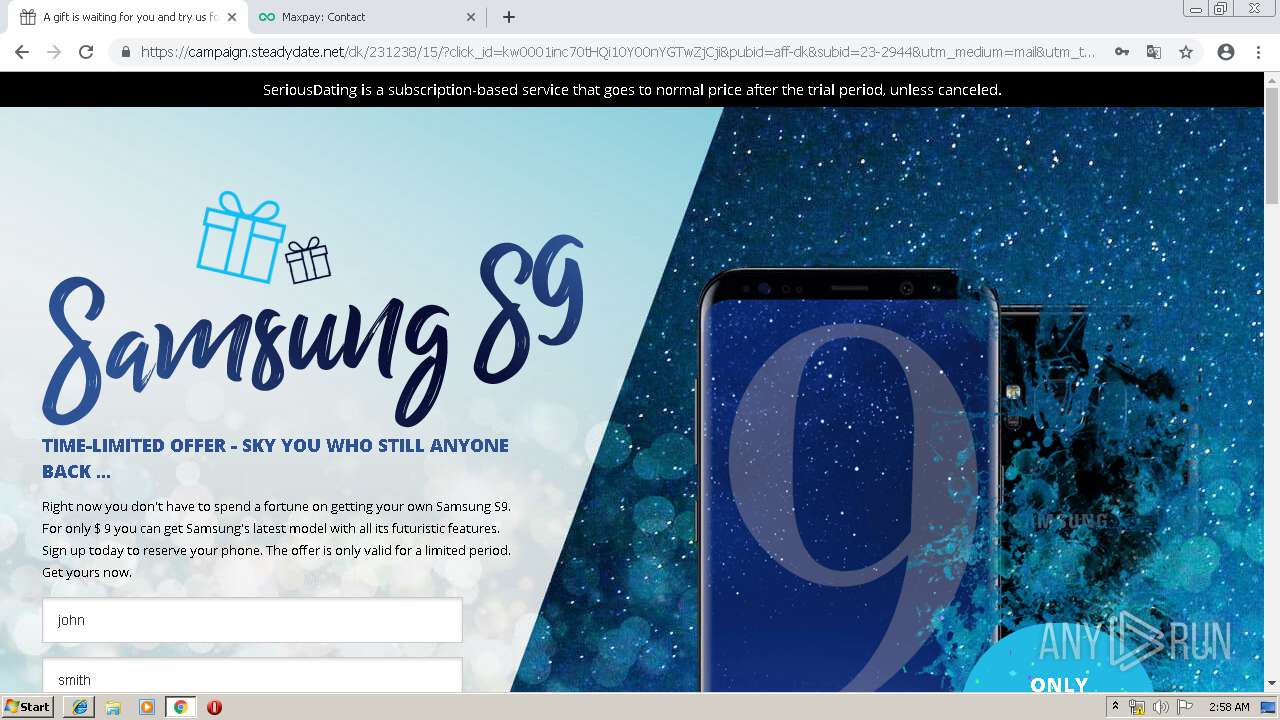
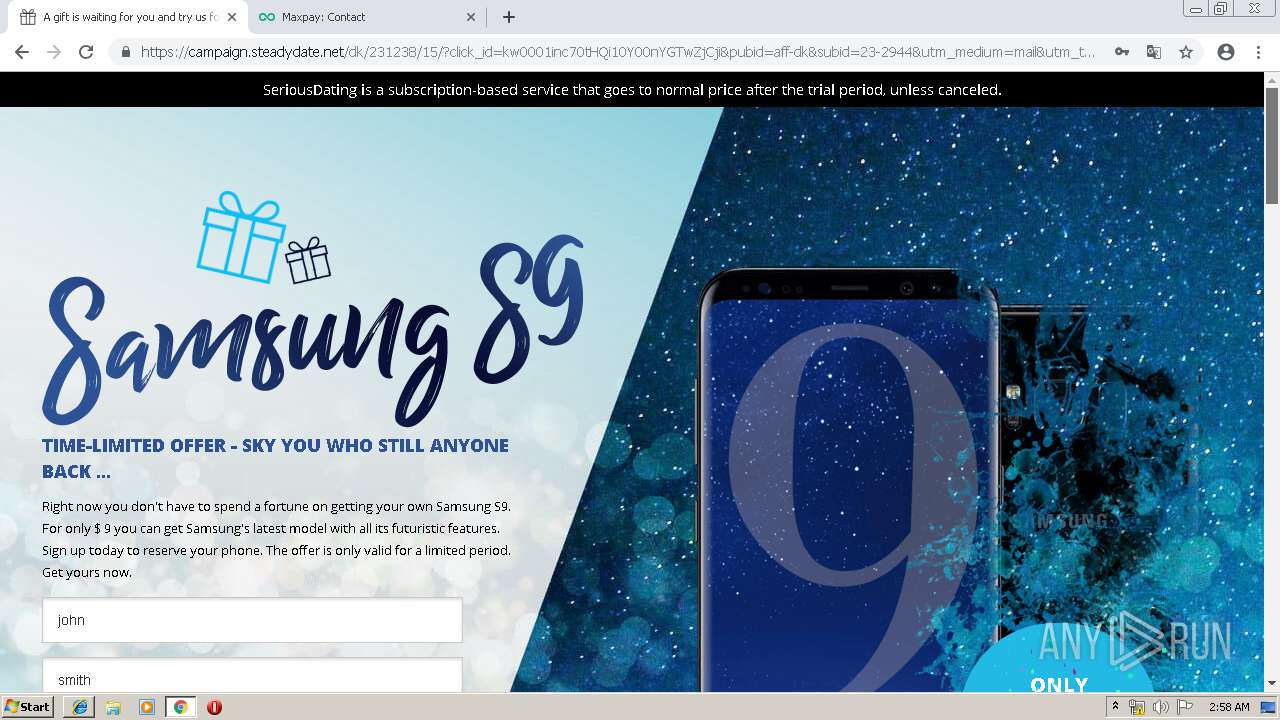
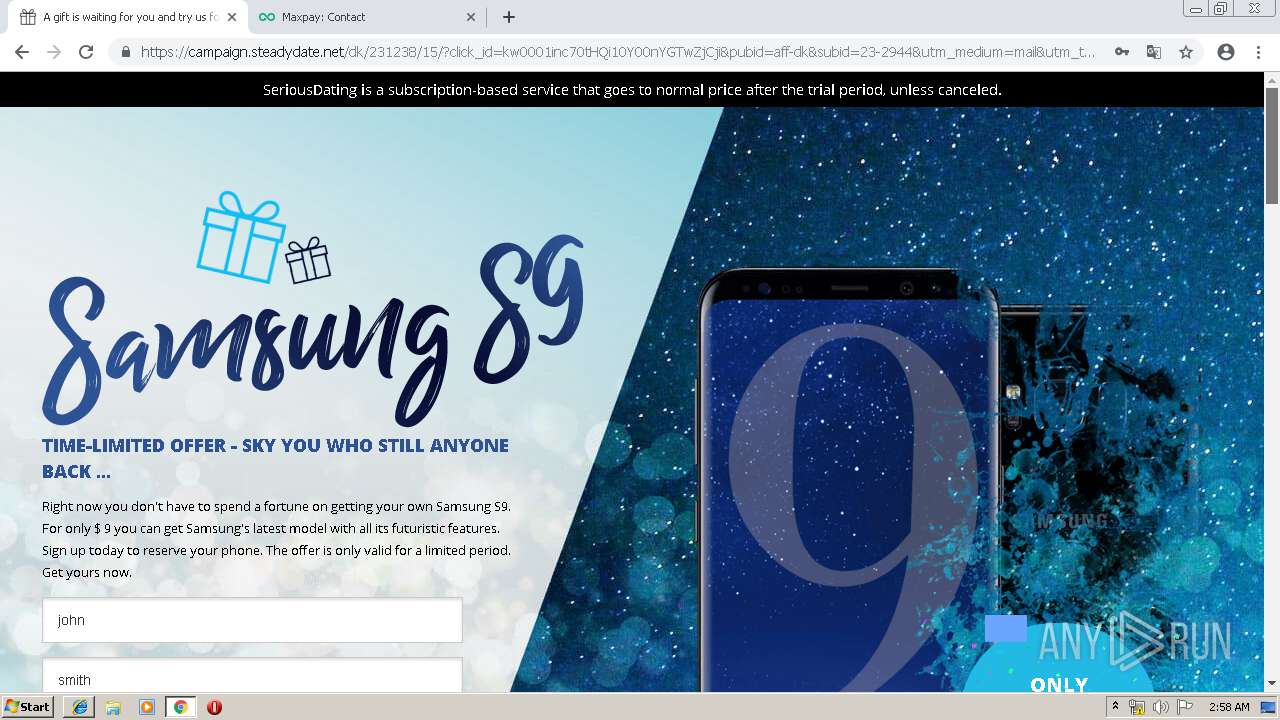
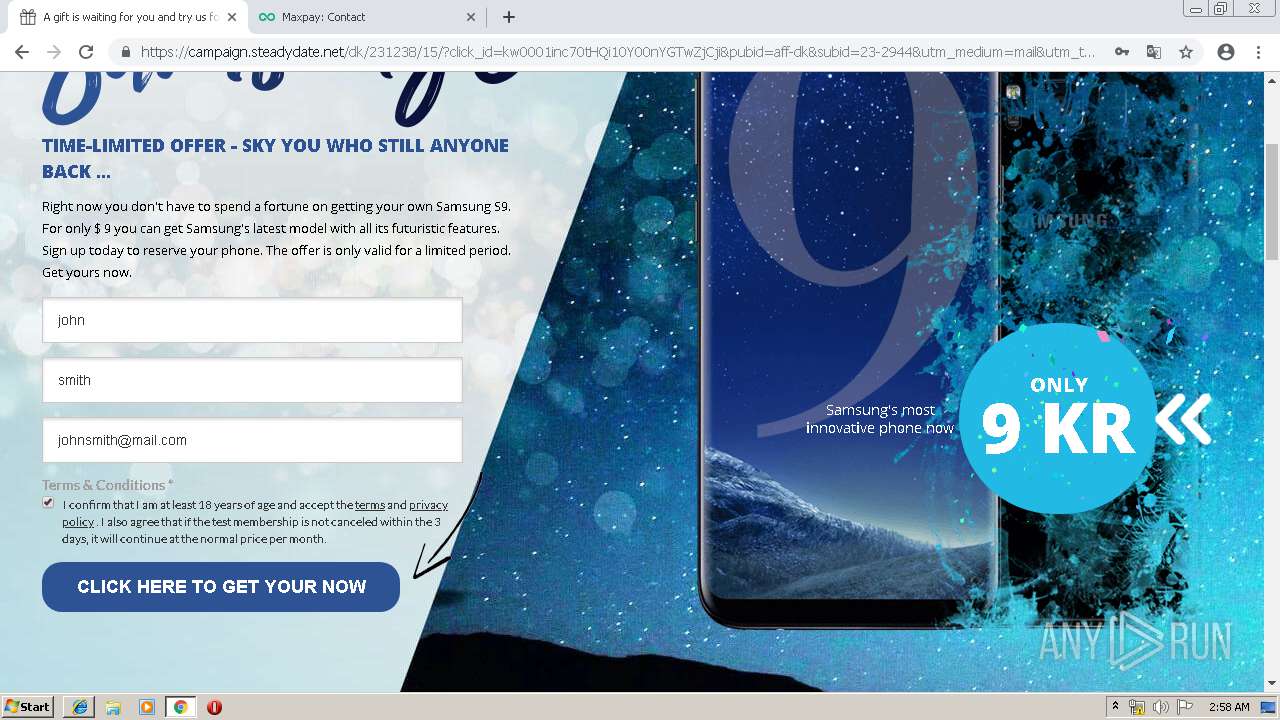
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 01:53:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BB7158A14FEEF3CBAD1A72FB335AAF40 |
| SHA1: | 0A5E90220AD87069B7FF3EDD312B5E07C5DD1072 |
| SHA256: | CBEB45A299C66F7F292C9F457D4B9D504A71501A12384AD29889611502891A4C |
| SSDEEP: | 3:N1KWUwVSBGGoBHfWzcEXBZ:CWFVq0/WzcEXBZ |
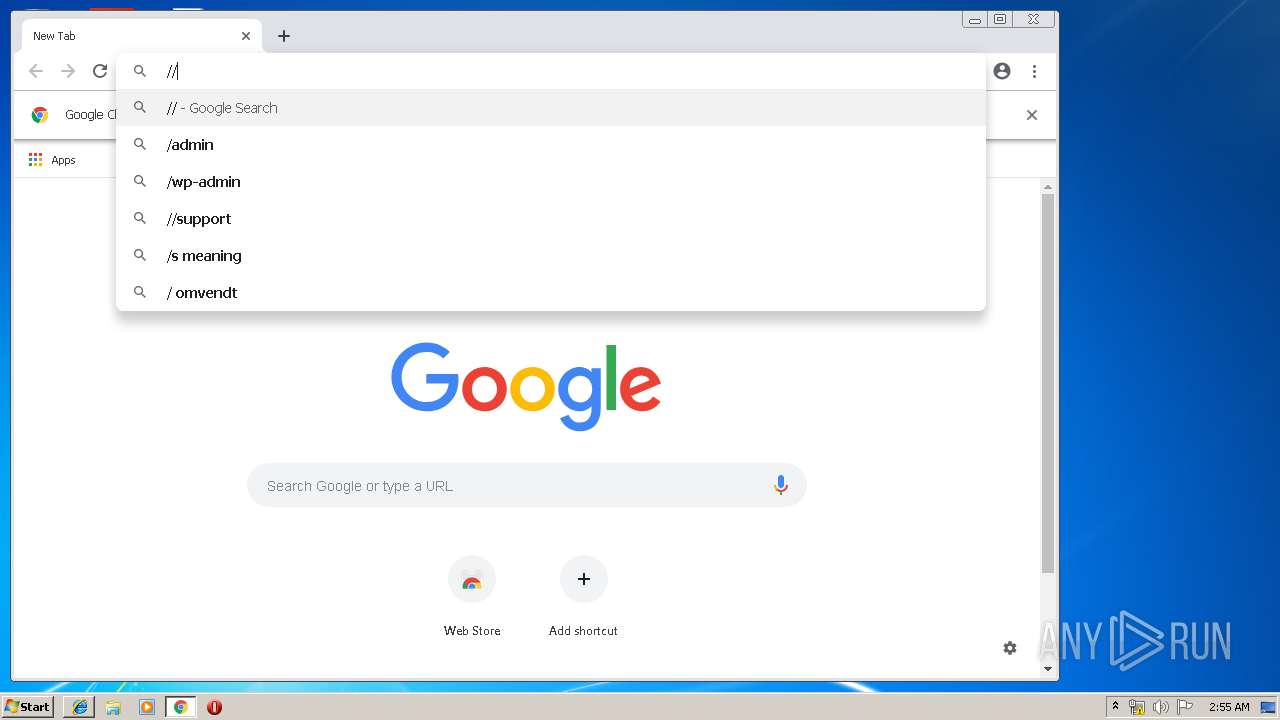
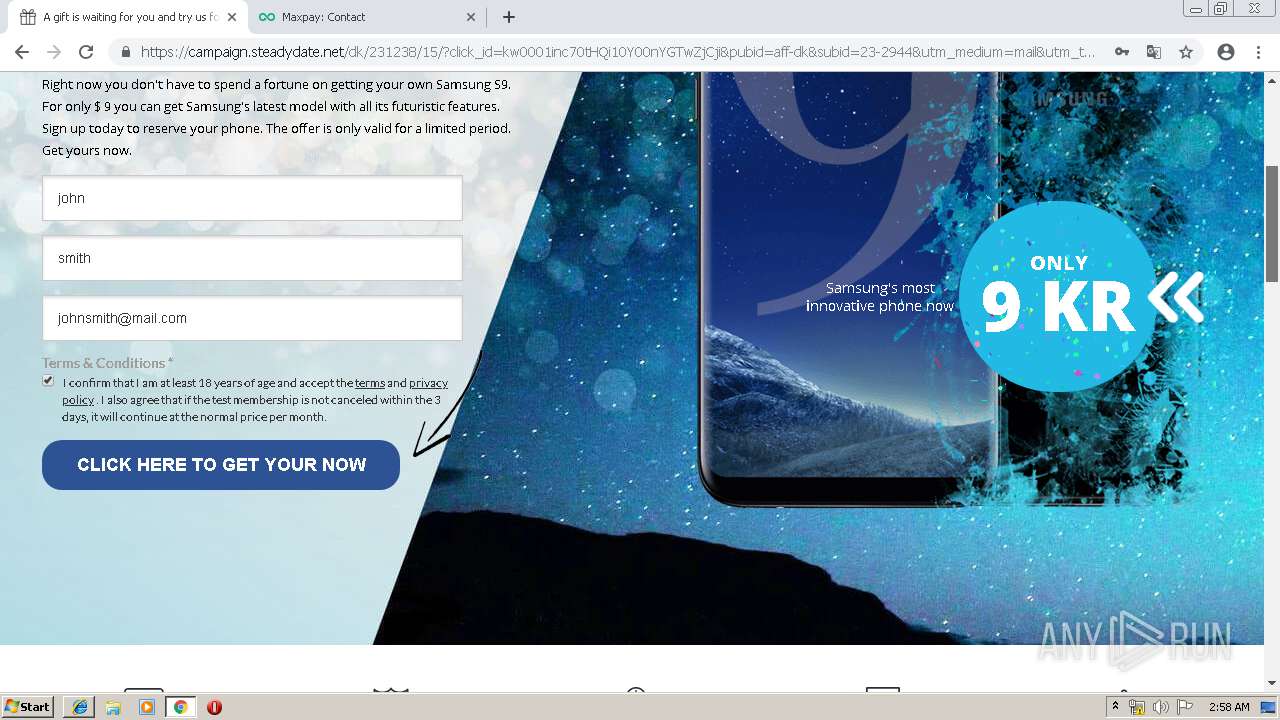
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 768)
INFO
Application launched itself
- iexplore.exe (PID: 1796)
- chrome.exe (PID: 768)
Reads Internet Cache Settings
- iexplore.exe (PID: 1796)
- iexplore.exe (PID: 3564)
Changes internet zones settings
- iexplore.exe (PID: 1796)
Reads internet explorer settings
- iexplore.exe (PID: 3564)
Reads settings of System Certificates
- iexplore.exe (PID: 1796)
Changes settings of System certificates
- iexplore.exe (PID: 1796)
Creates files in the user directory
- iexplore.exe (PID: 3564)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2380454740262206052,4990872207790509400,131072 --enable-features=PasswordImport --service-pipe-token=1965484496601725198 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1965484496601725198 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2380454740262206052,4990872207790509400,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4664050998981806538 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4664050998981806538 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,2380454740262206052,4990872207790509400,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15579312690551638714 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d6a0f18,0x6d6a0f28,0x6d6a0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2380454740262206052,4990872207790509400,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17967170063629723438 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17967170063629723438 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,2380454740262206052,4990872207790509400,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7263263457685873099 --mojo-platform-channel-handle=4580 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2380454740262206052,4990872207790509400,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11967736426940899051 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11967736426940899051 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,2380454740262206052,4990872207790509400,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14367041019759970001 --mojo-platform-channel-handle=2976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,2380454740262206052,4990872207790509400,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3337429491142411755 --mojo-platform-channel-handle=2692 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 048
Read events
861
Write events
179
Delete events
8
Modification events
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {0208C903-66FD-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070400040019000100360007009201 | |||
Executable files
0
Suspicious files
121
Text files
241
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\N6TT1MQO\blogustudent[1].png | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019042520190426\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@el.nasjsone[1].txt | — | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\35ZYMDEH\blogustudent[1].htm | html | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019042520190426\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3564 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\N6TT1MQO\caf[1].js | text | |
MD5:— | SHA256:— | |||
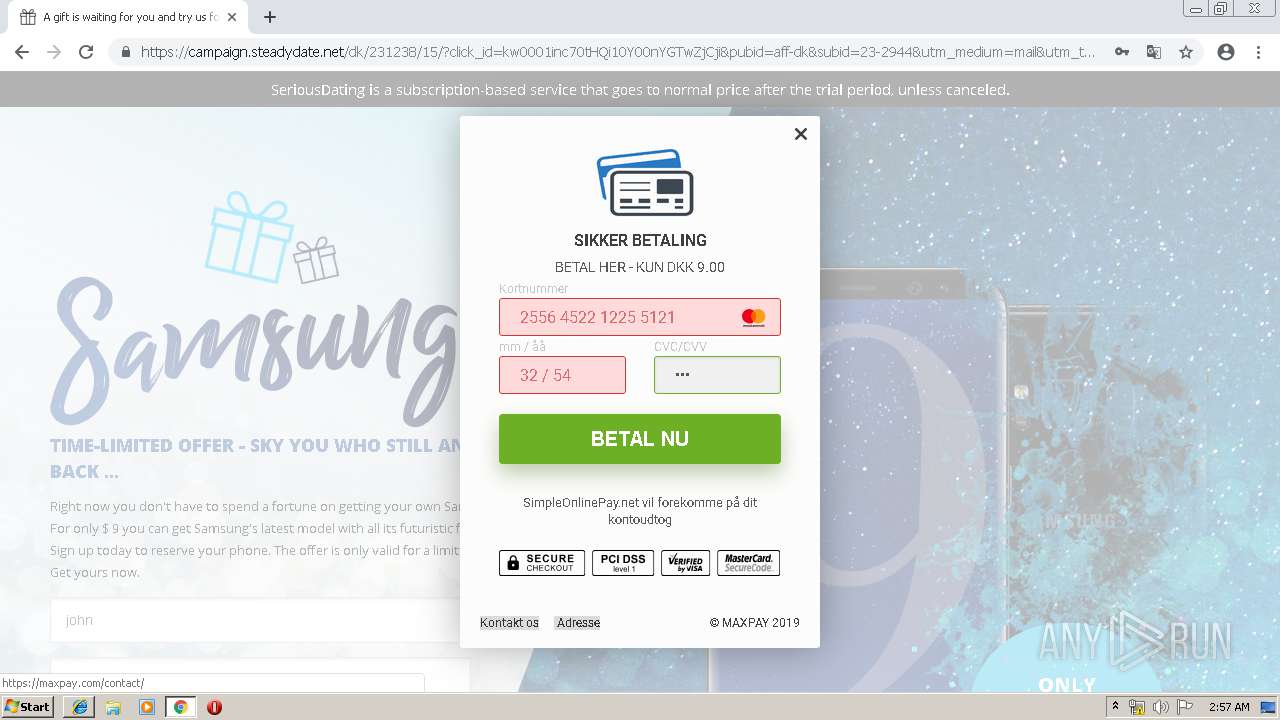
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
92
DNS requests
61
Threats
0
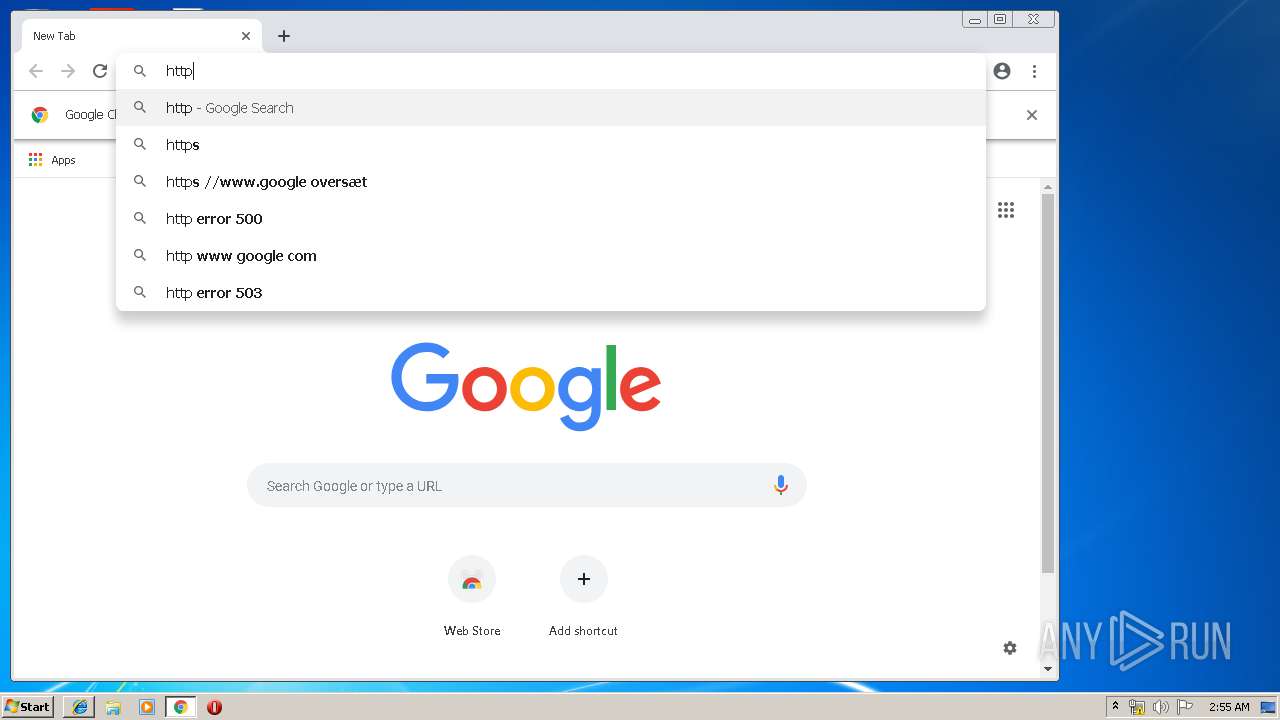
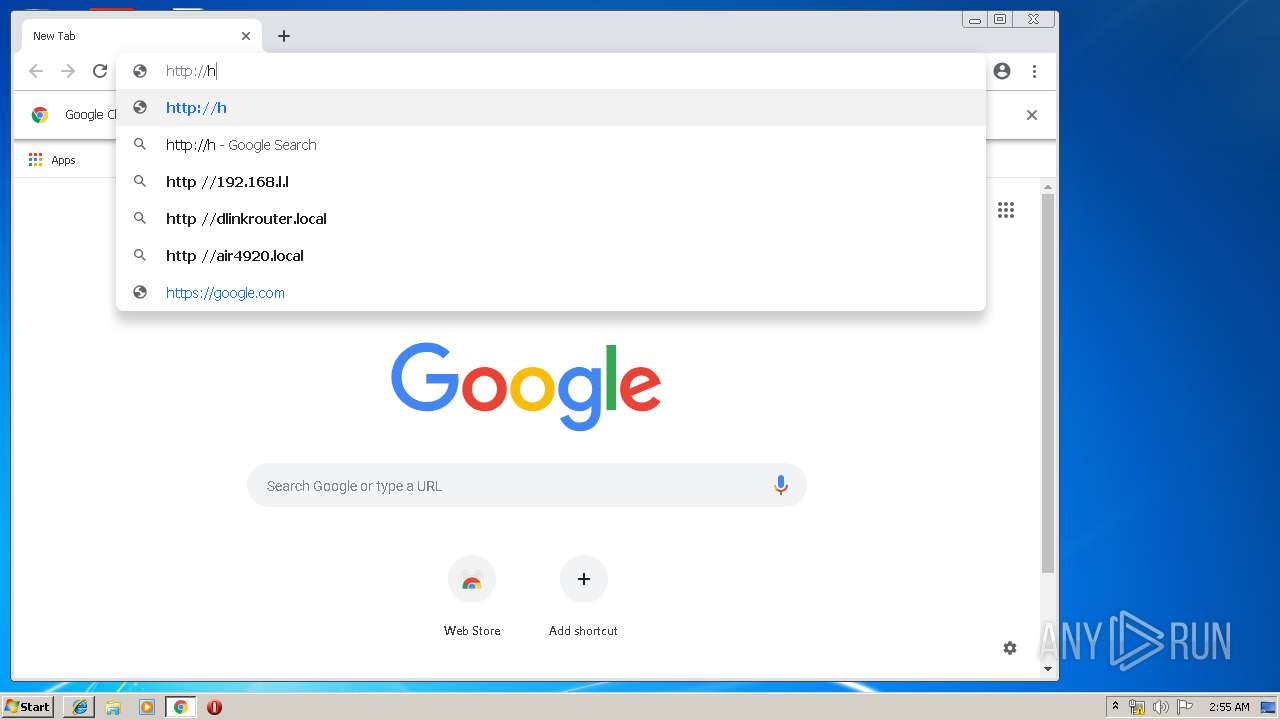
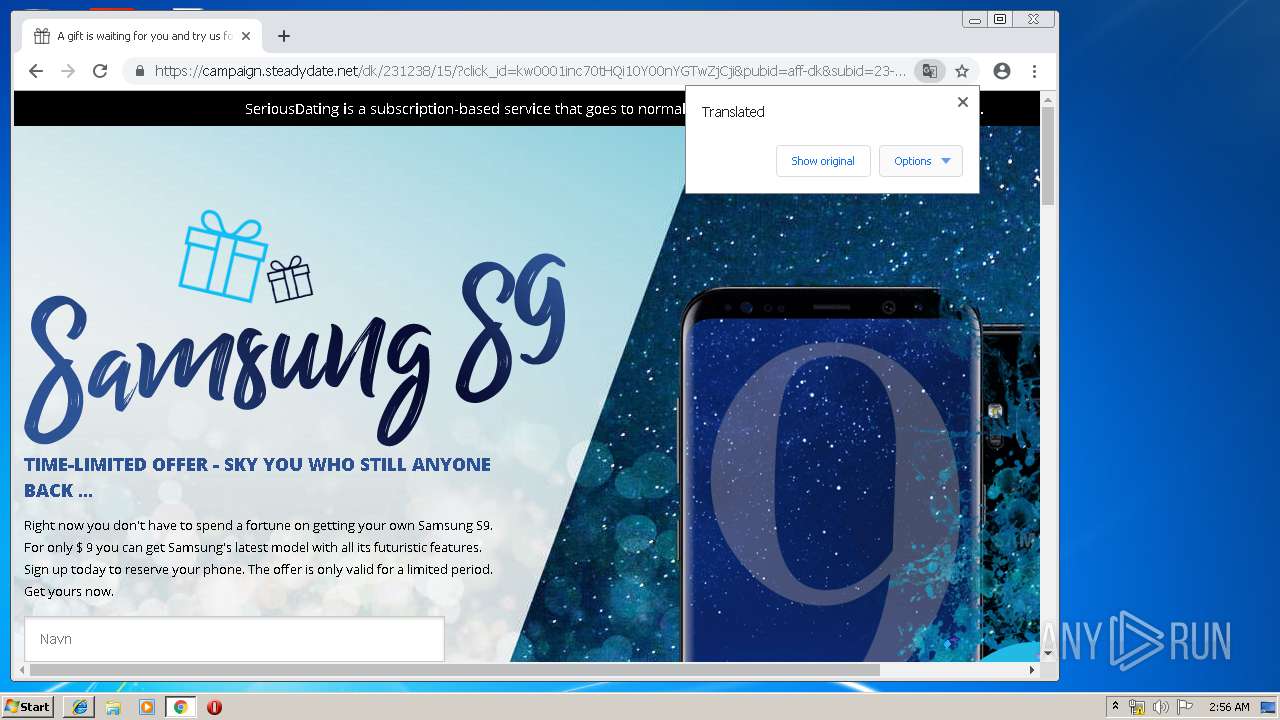
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
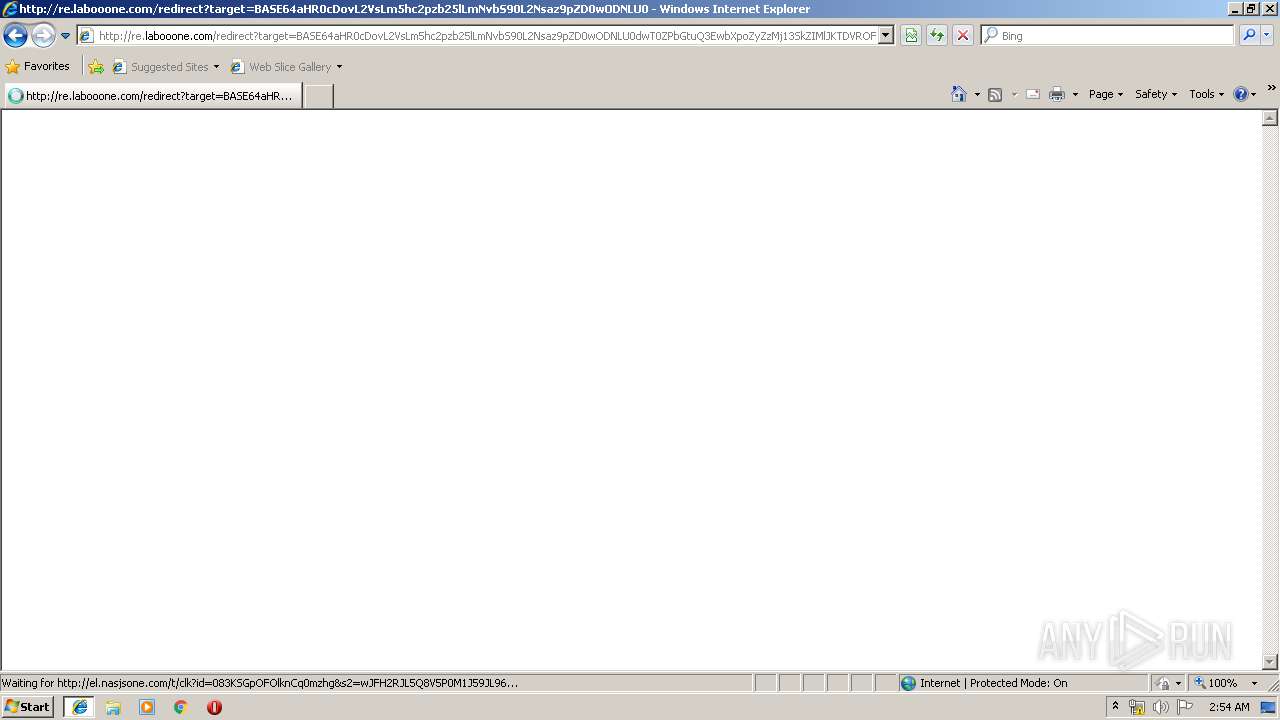
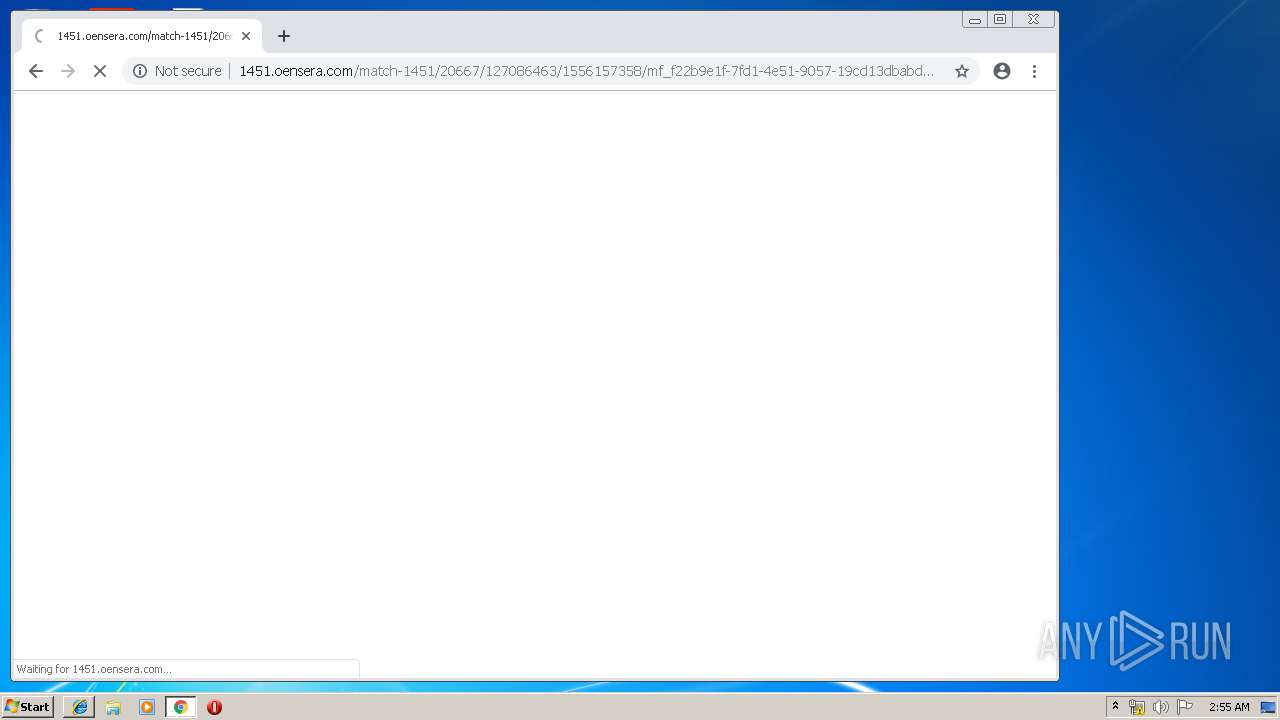
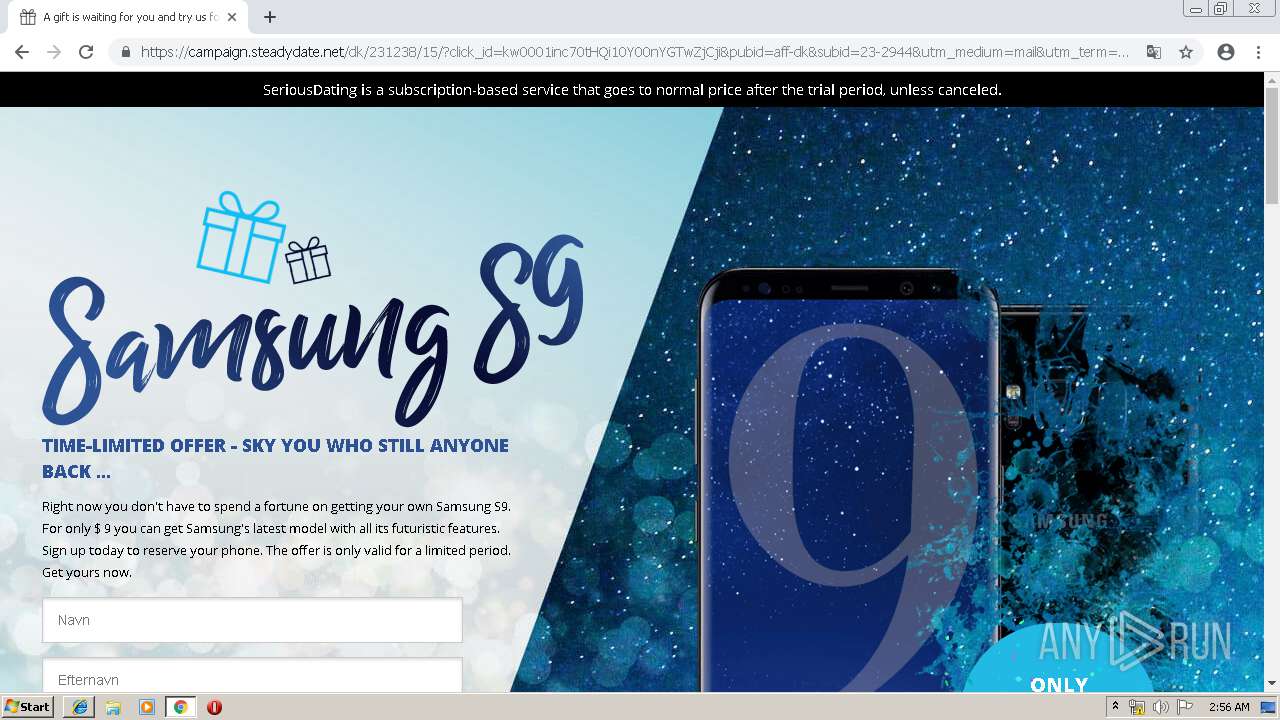
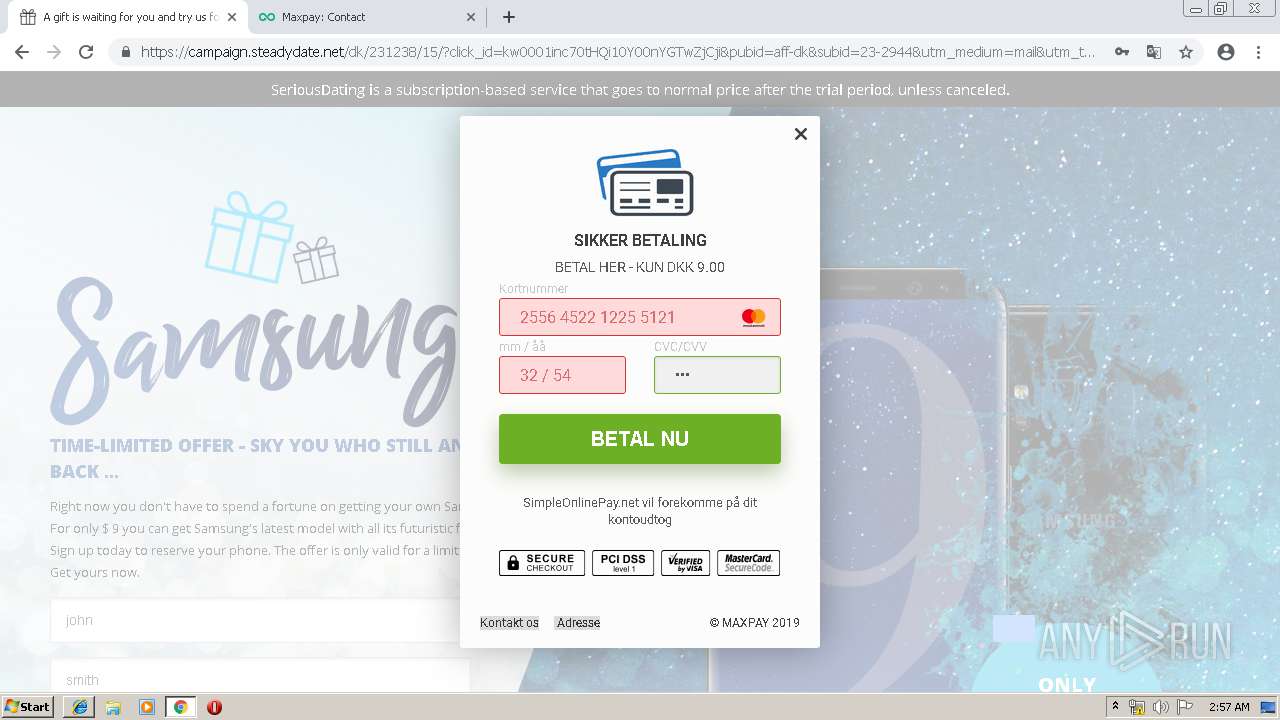
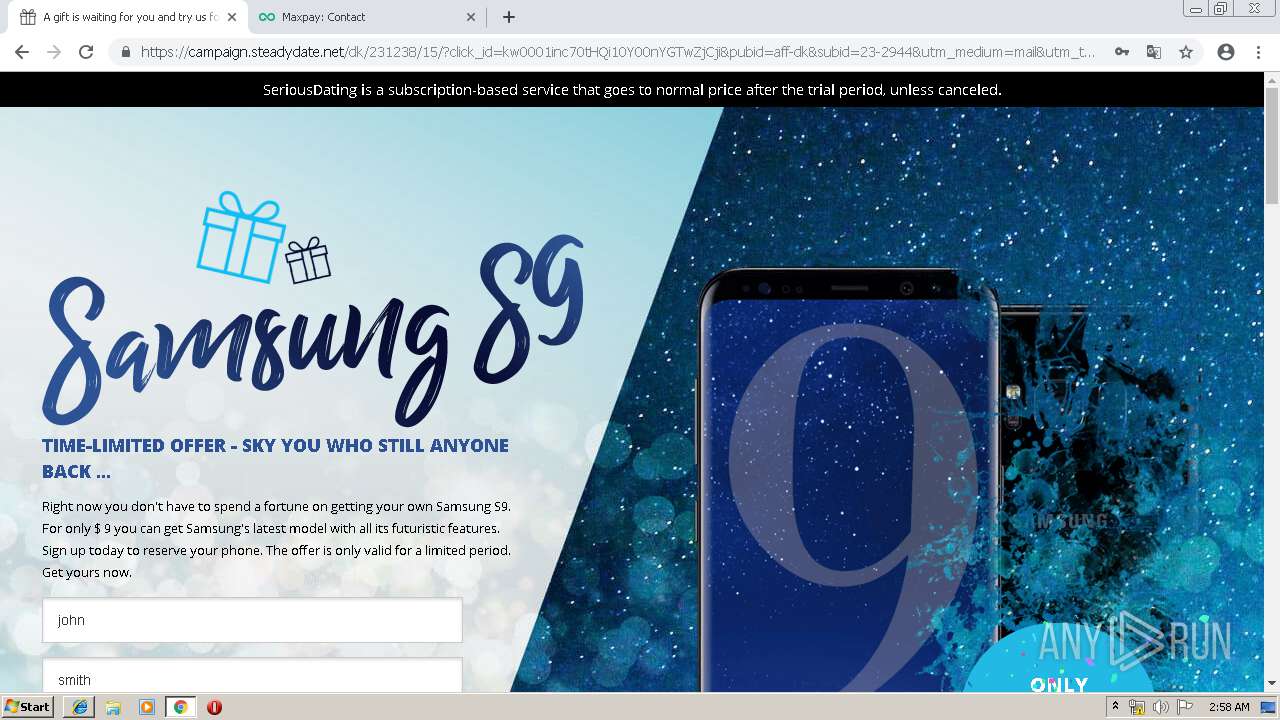
3564 | iexplore.exe | GET | 302 | 198.54.112.216:80 | http://1451.oensera.com/match-1451/20667/127086463/1556157249/mf_cf0d0114-3f5b-4450-bb9e-ecb6c932d568/YXBpeDIxLXJpcHdheS5jb20= | US | — | — | malicious |
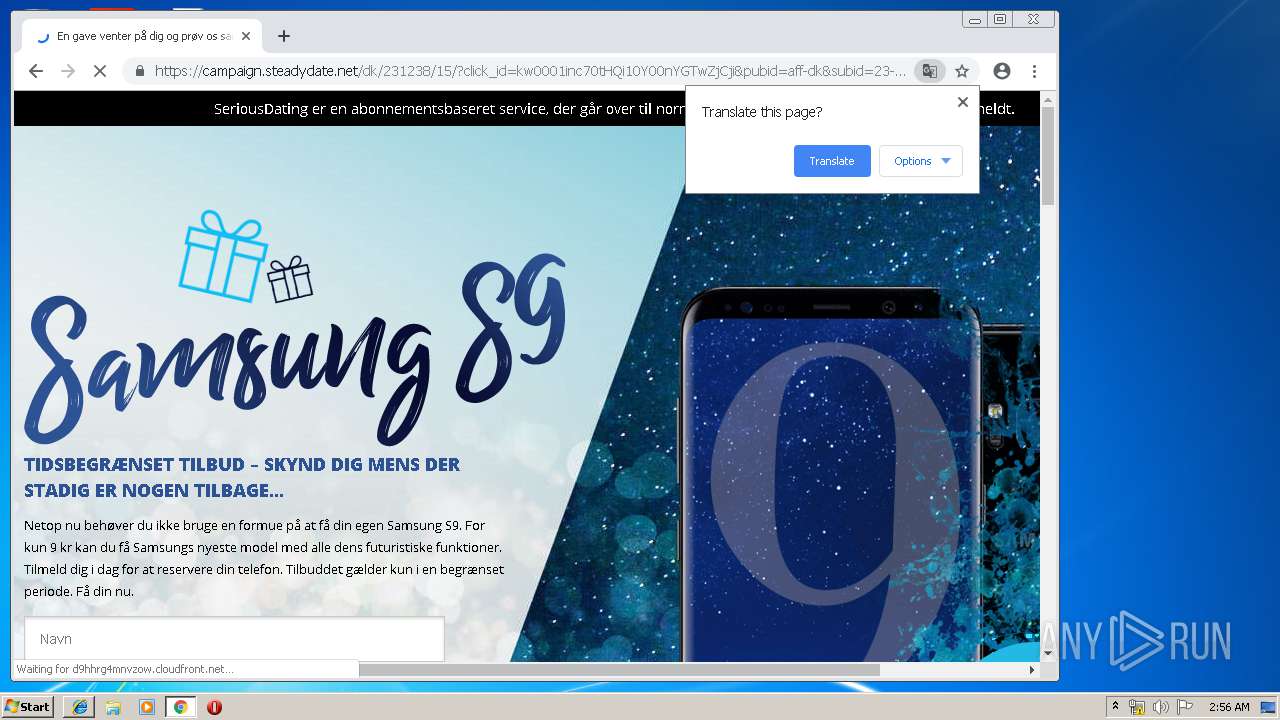
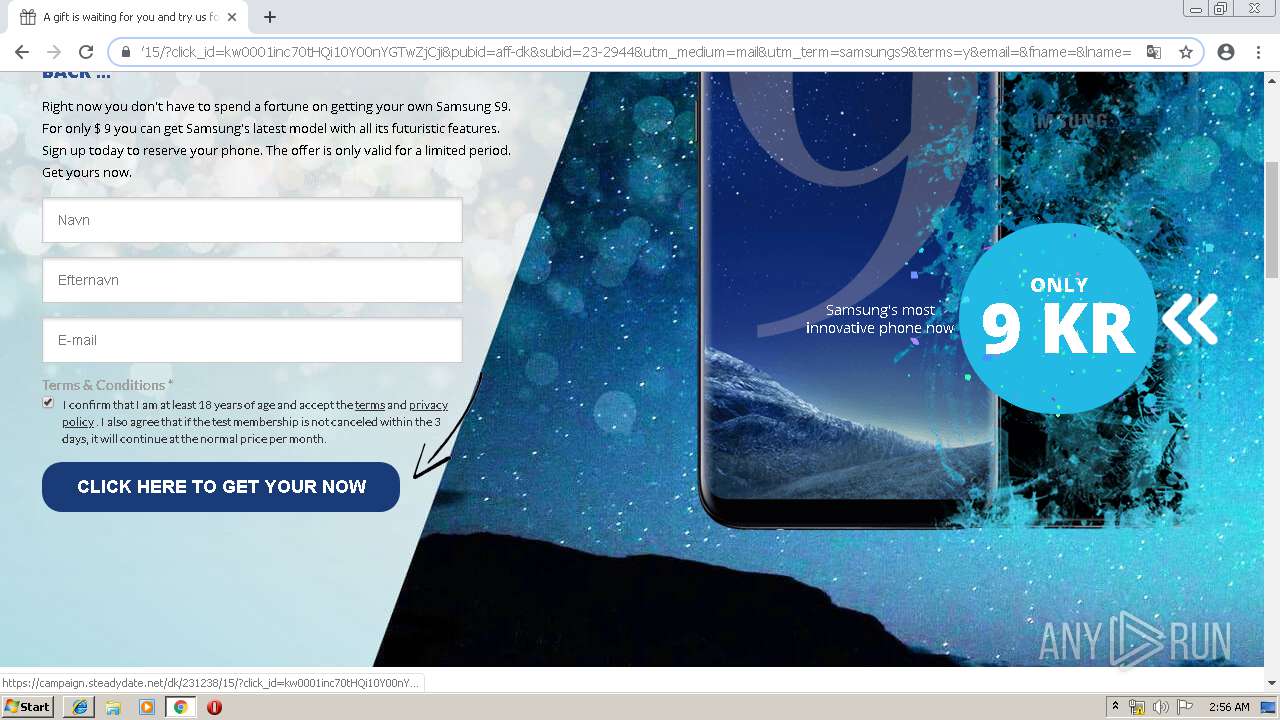
3564 | iexplore.exe | GET | 302 | 3.209.210.211:80 | http://el.nasjsone.com/t/clk?id=083KSGpOFOlknCq0mzhg&s2=wJFH2RJL5Q8V5P0M1J59JL96 | US | — | — | unknown |
3564 | iexplore.exe | GET | 200 | 199.59.242.151:80 | http://h1.ripway.com/glp?r=&u=http%3A%2F%2Fh1.ripway.com%2Fanniebluesky%2Fblogustudent.png&rw=1280&rh=720&ww=1276&wh=560&ie=8 | US | text | 7.91 Kb | whitelisted |
3564 | iexplore.exe | GET | 200 | 172.217.22.36:80 | http://www.google.com/adsense/domains/caf.js | US | text | 55.3 Kb | malicious |
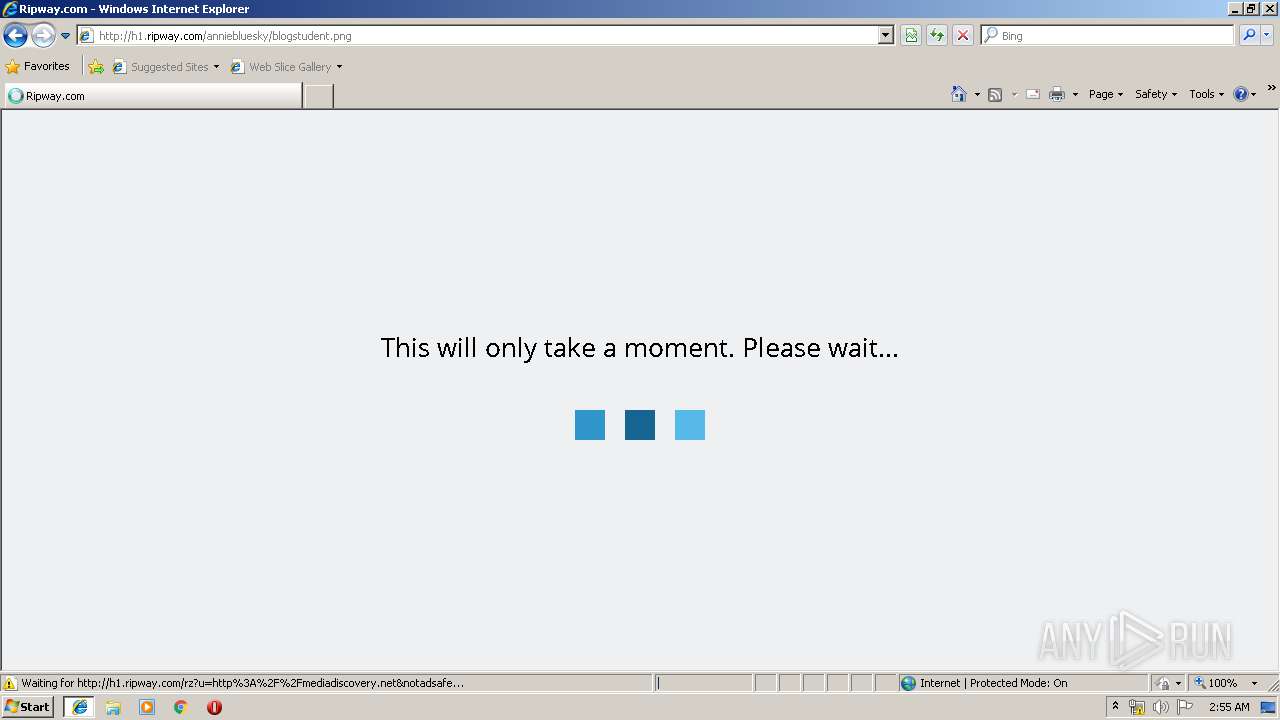
3564 | iexplore.exe | GET | 302 | 199.59.242.151:80 | http://h1.ripway.com/rz?u=http%3A%2F%2F1451.oensera.com%2Fmatch-1451%2F20667%2F127086463%2F1556157249%2Fmf_cf0d0114-3f5b-4450-bb9e-ecb6c932d568%2FYXBpeDIxLXJpcHdheS5jb20%3D%2Ffeed¬adsafe | US | text | 7.91 Kb | whitelisted |
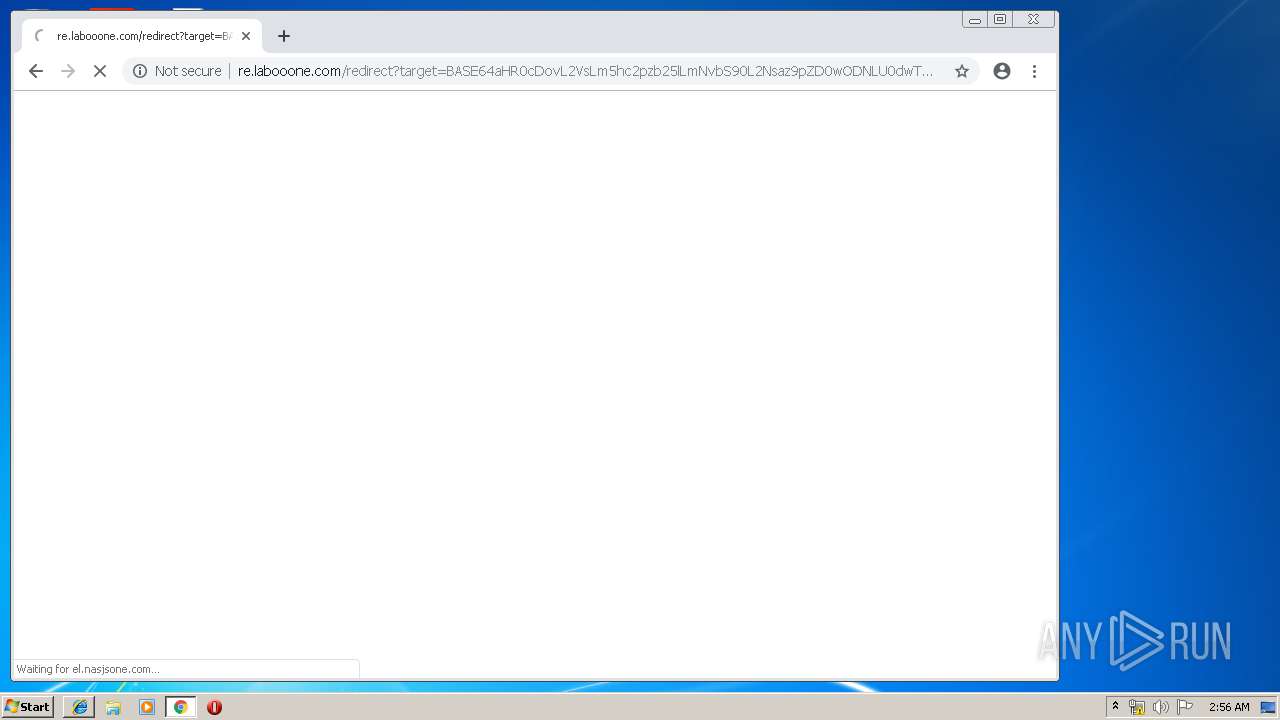
3564 | iexplore.exe | GET | 200 | 18.195.23.231:80 | http://re.labooone.com/redirect?target=BASE64aHR0cDovL2VsLm5hc2pzb25lLmNvbS90L2Nsaz9pZD0wODNLU0dwT0ZPbGtuQ3EwbXpoZyZzMj13SkZIMlJKTDVROFY1UDBNMUo1OUpMOTY&ts=1556157251389&hash=0VB9UEzFvpkMrNSzrPn5GM7As9rFeva1IXXJ7LdF5Rs&rm=D | DE | html | 292 b | shared |
3564 | iexplore.exe | GET | 200 | 198.54.112.216:80 | http://1451.oensera.com/match-1451/20667/127086463/1556157249/mf_cf0d0114-3f5b-4450-bb9e-ecb6c932d568/YXBpeDIxLXJpcHdheS5jb20=/feed | US | html | 317 b | malicious |
3564 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
3564 | iexplore.exe | POST | 200 | 199.59.242.151:80 | http://h1.ripway.com/gzb | US | text | 216 b | whitelisted |
1796 | iexplore.exe | GET | 404 | 199.59.242.151:80 | http://h1.ripway.com/favicon.ico | US | html | 3.93 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
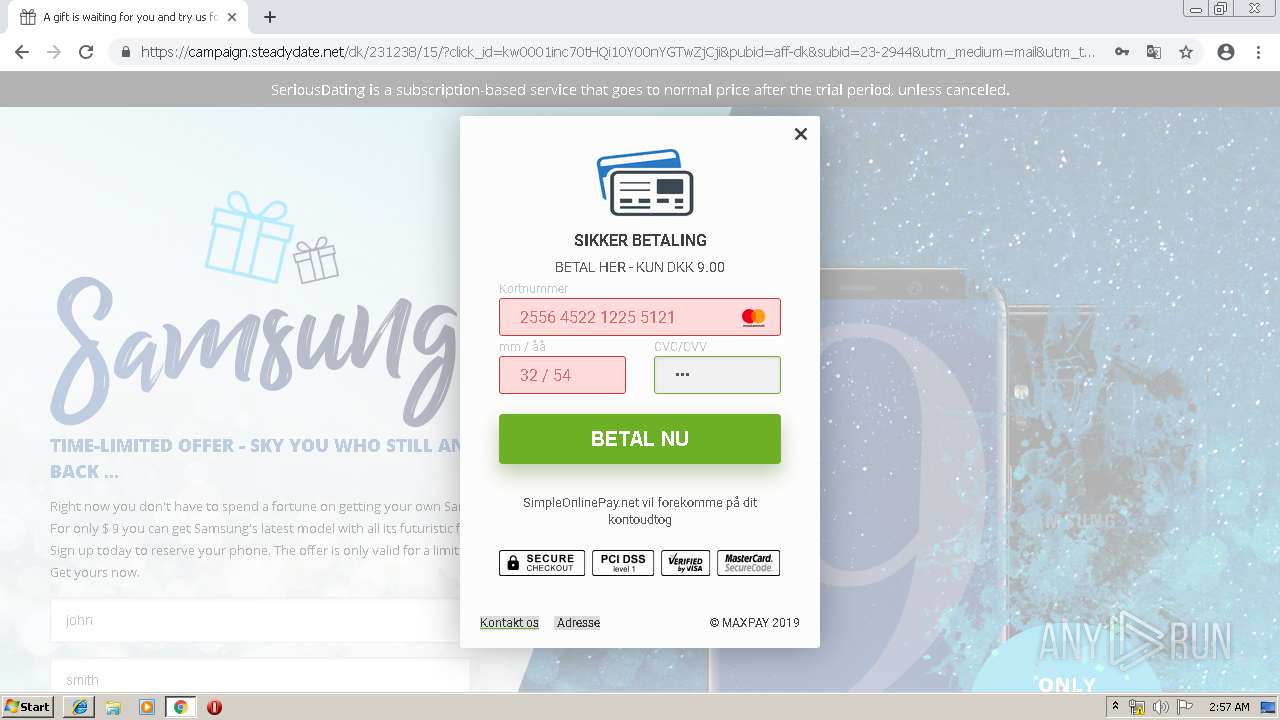
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3564 | iexplore.exe | 3.209.210.211:80 | el.nasjsone.com | — | US | unknown |
1796 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3564 | iexplore.exe | 199.59.242.151:80 | h1.ripway.com | Bodis, LLC | US | malicious |
3564 | iexplore.exe | 172.217.22.36:80 | www.google.com | Google Inc. | US | whitelisted |
1796 | iexplore.exe | 199.59.242.151:80 | h1.ripway.com | Bodis, LLC | US | malicious |
3564 | iexplore.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3564 | iexplore.exe | 198.54.112.216:80 | 1451.oensera.com | Namecheap, Inc. | US | malicious |
3564 | iexplore.exe | 13.250.190.221:443 | snd.cmpgns.net | Amazon.com, Inc. | SG | unknown |
3564 | iexplore.exe | 52.85.188.159:80 | x.ss2.us | Amazon.com, Inc. | US | whitelisted |
3564 | iexplore.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
h1.ripway.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
1451.oensera.com |
| malicious |
trk.zeetrackoo.com |
| shared |
re.labooone.com |
| shared |
el.nasjsone.com |
| unknown |
snd.cmpgns.net |
| unknown |