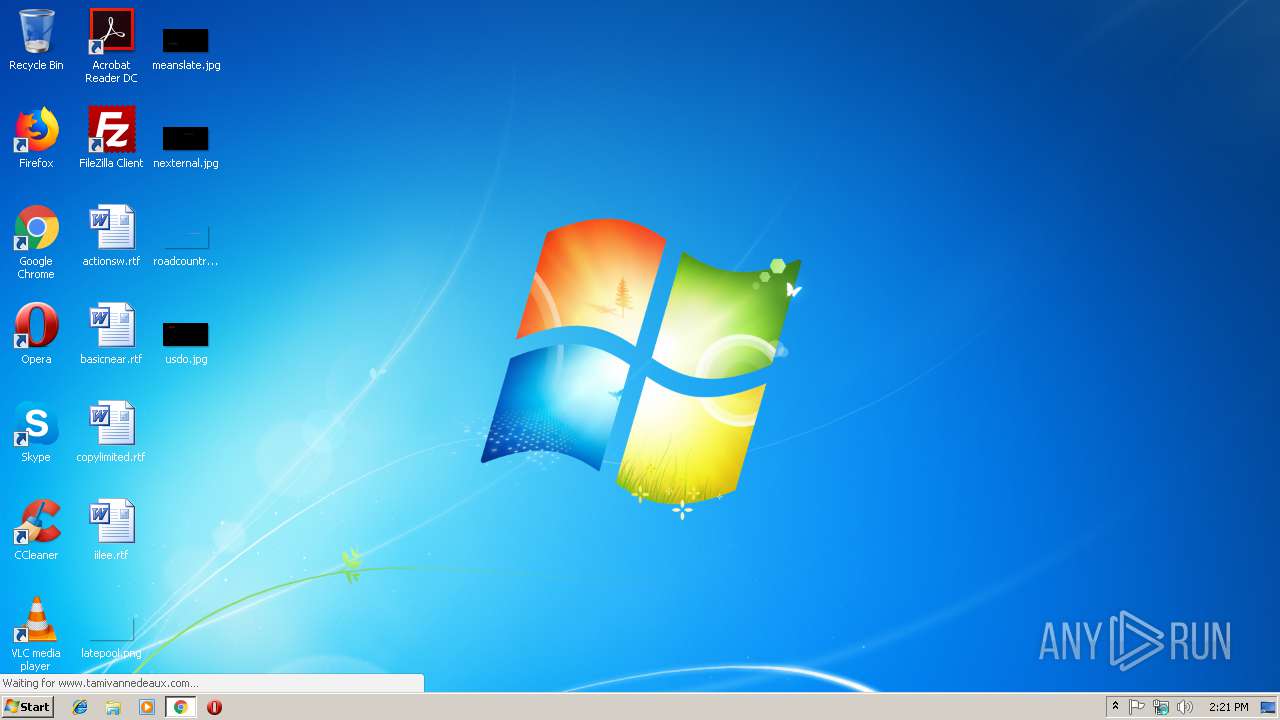
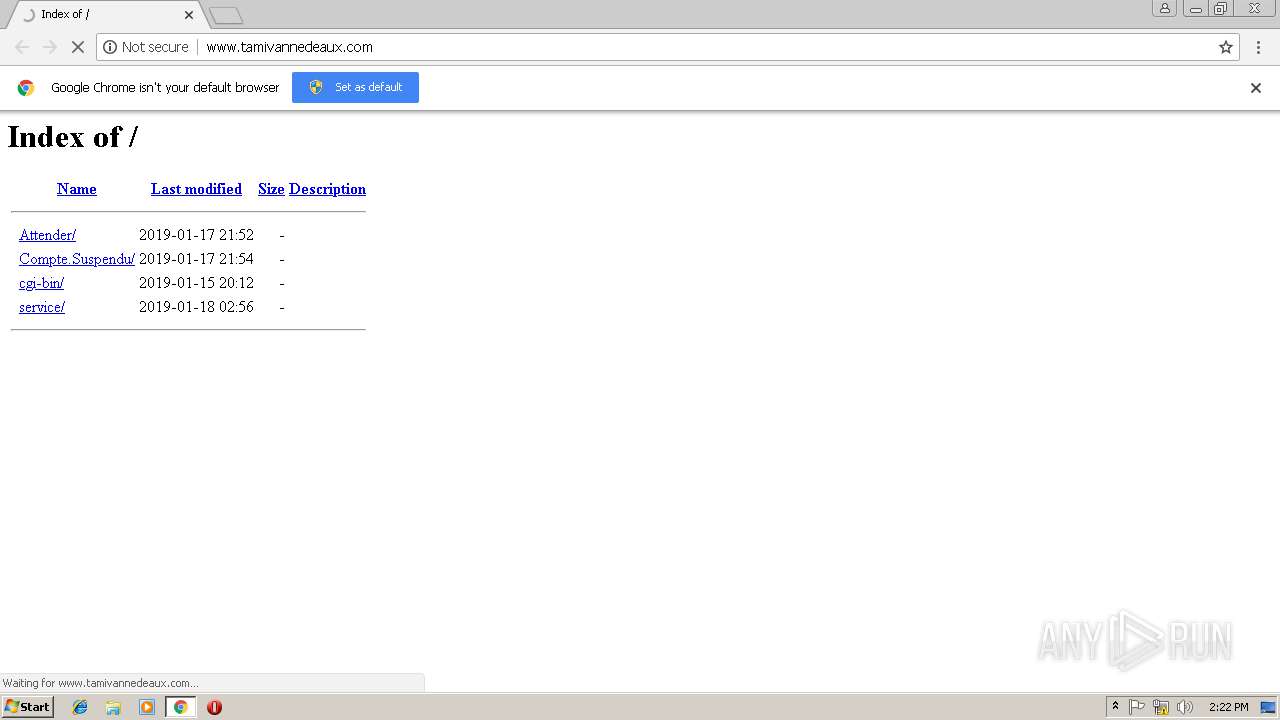
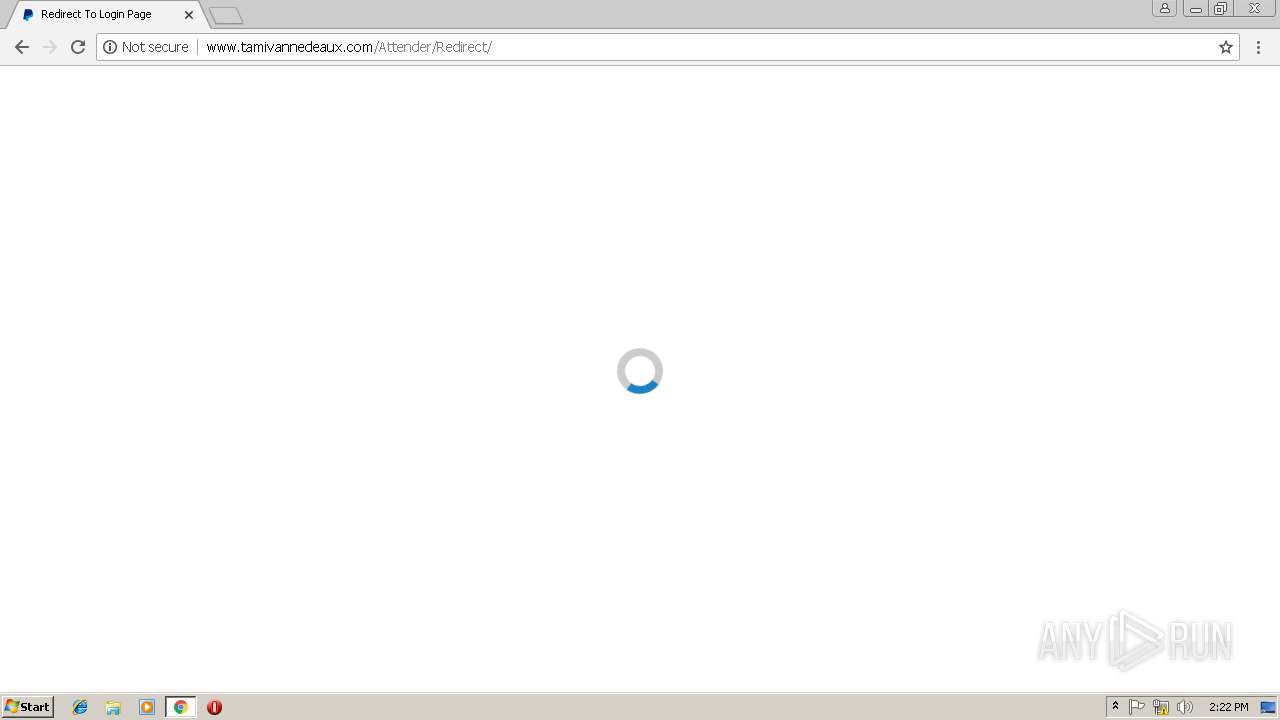
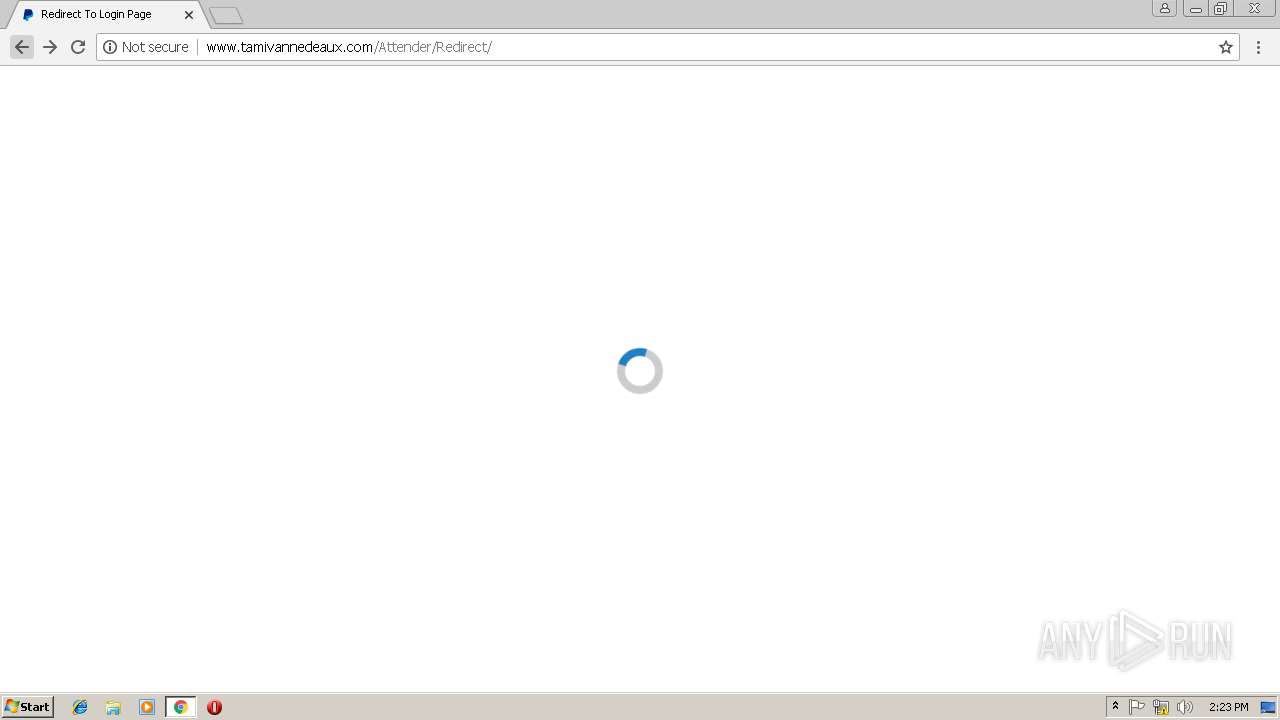
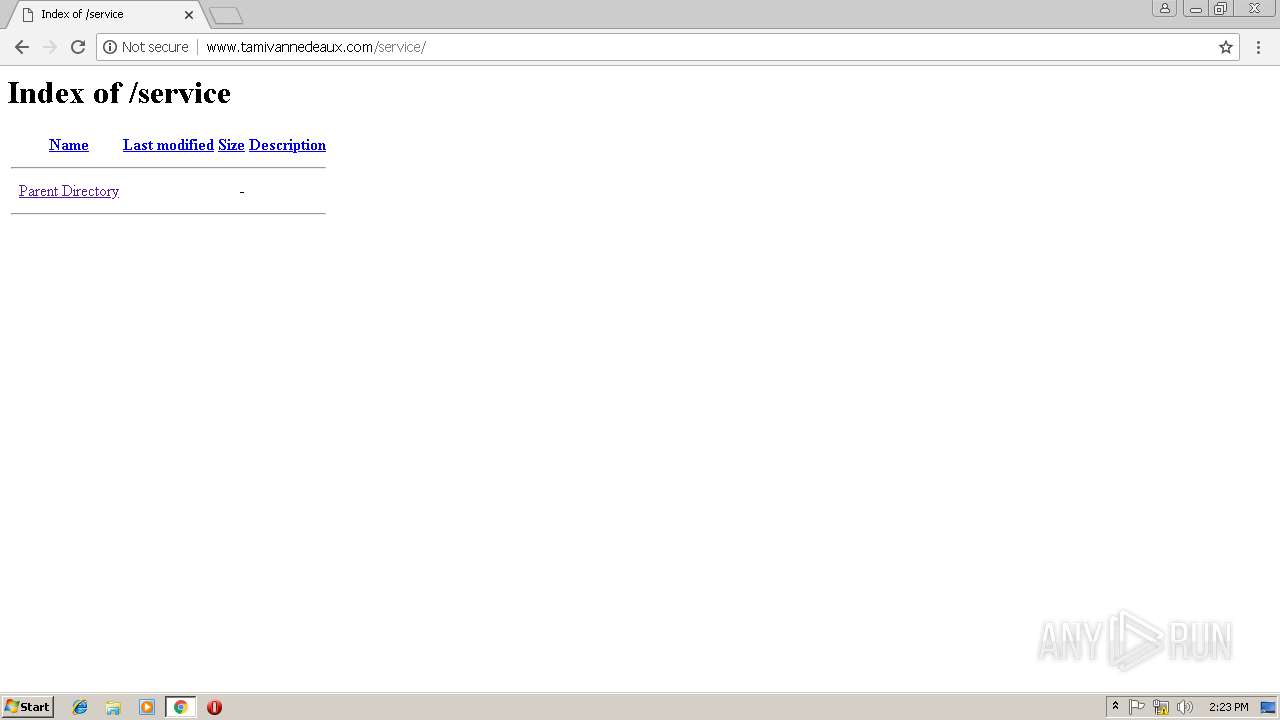
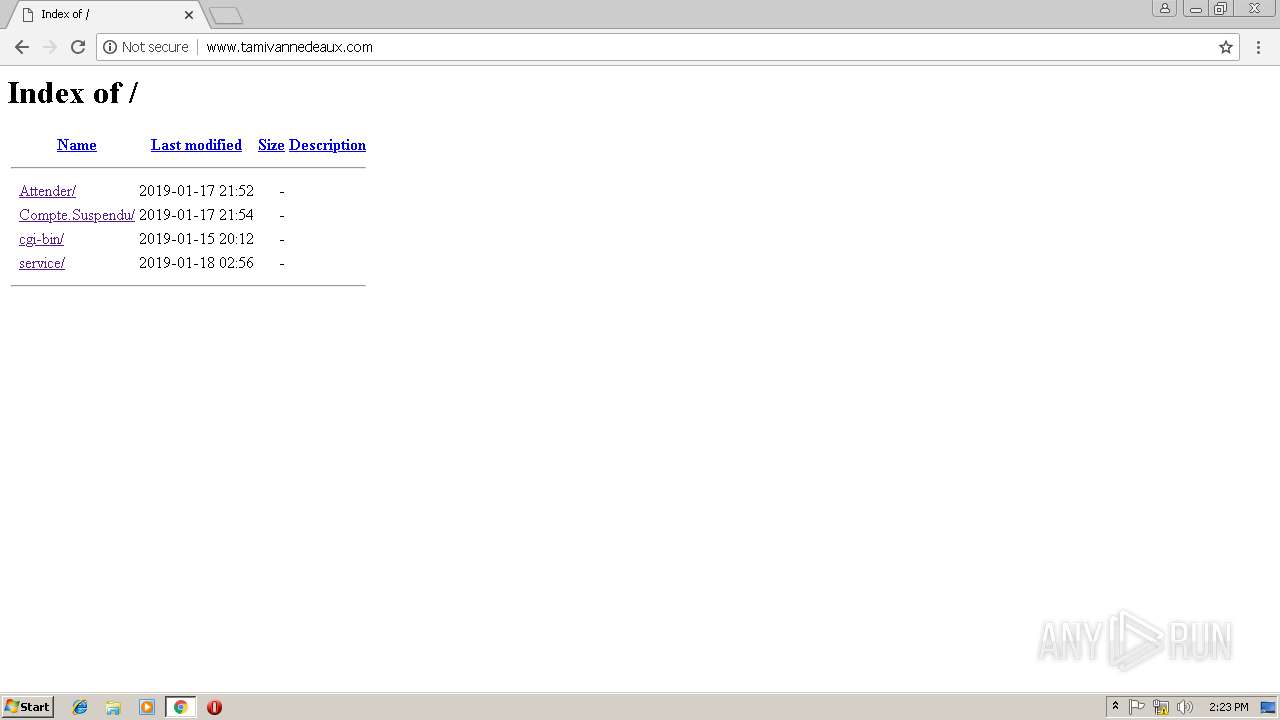
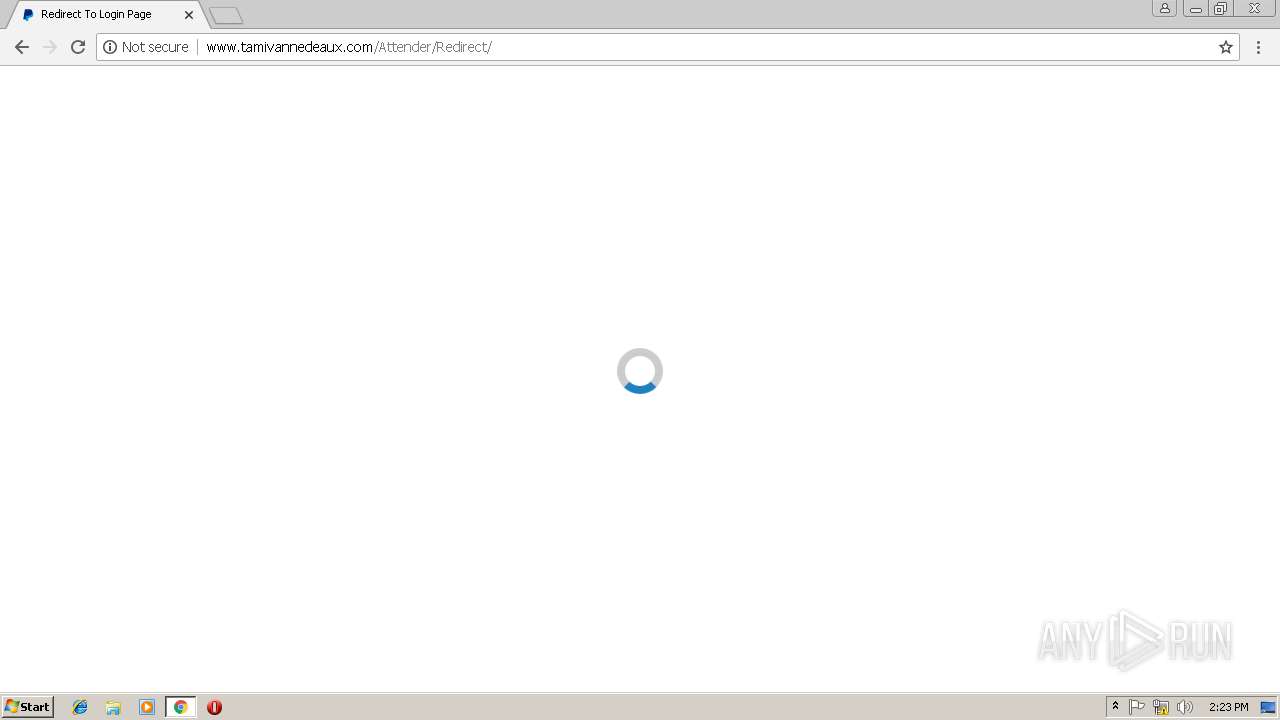
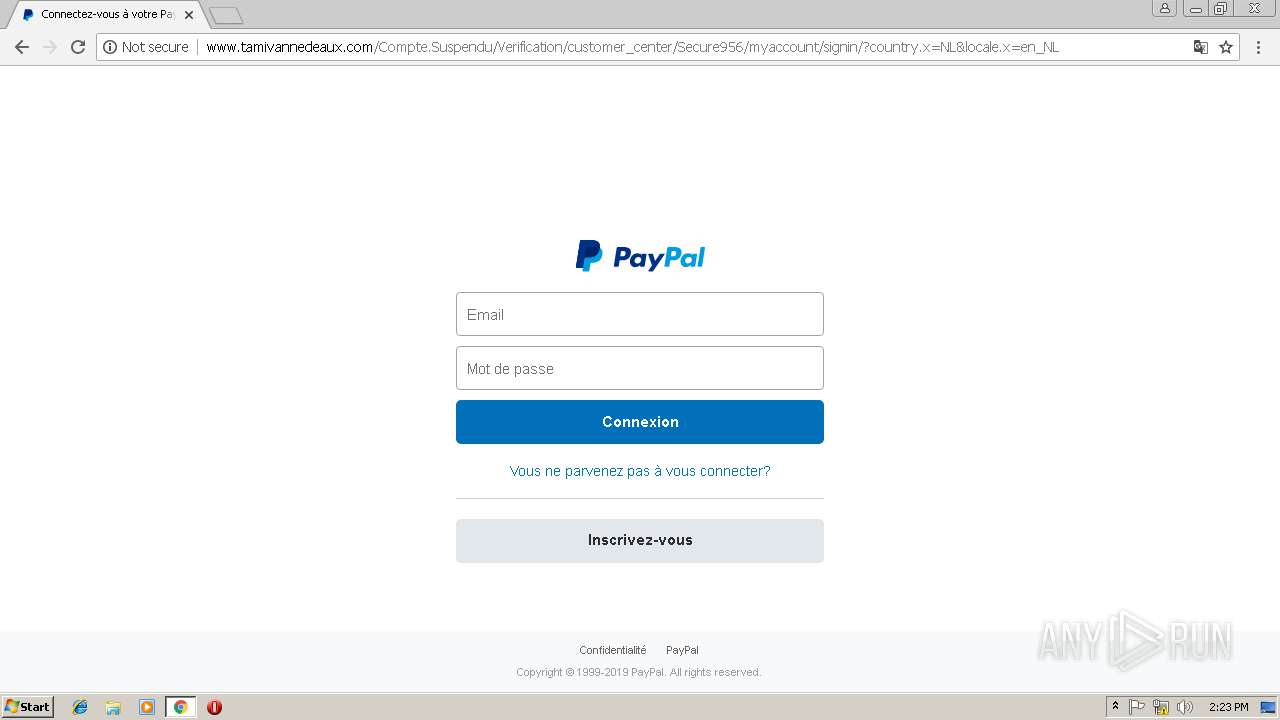
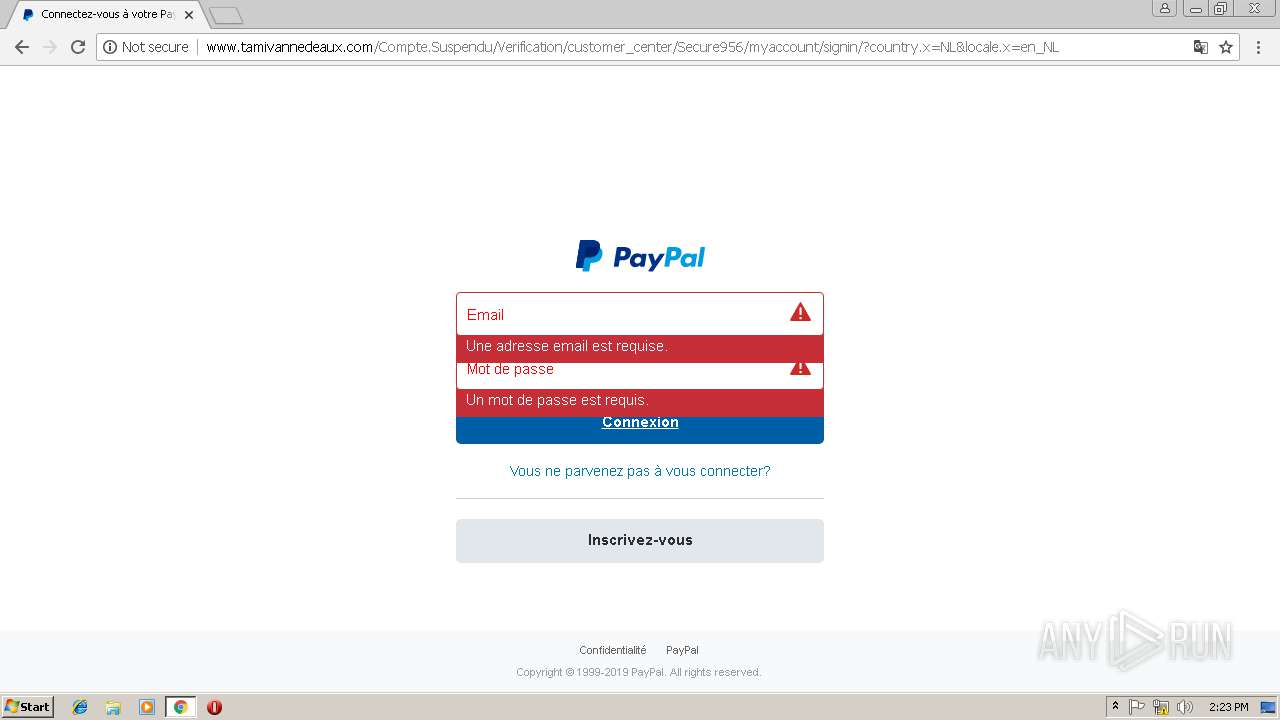
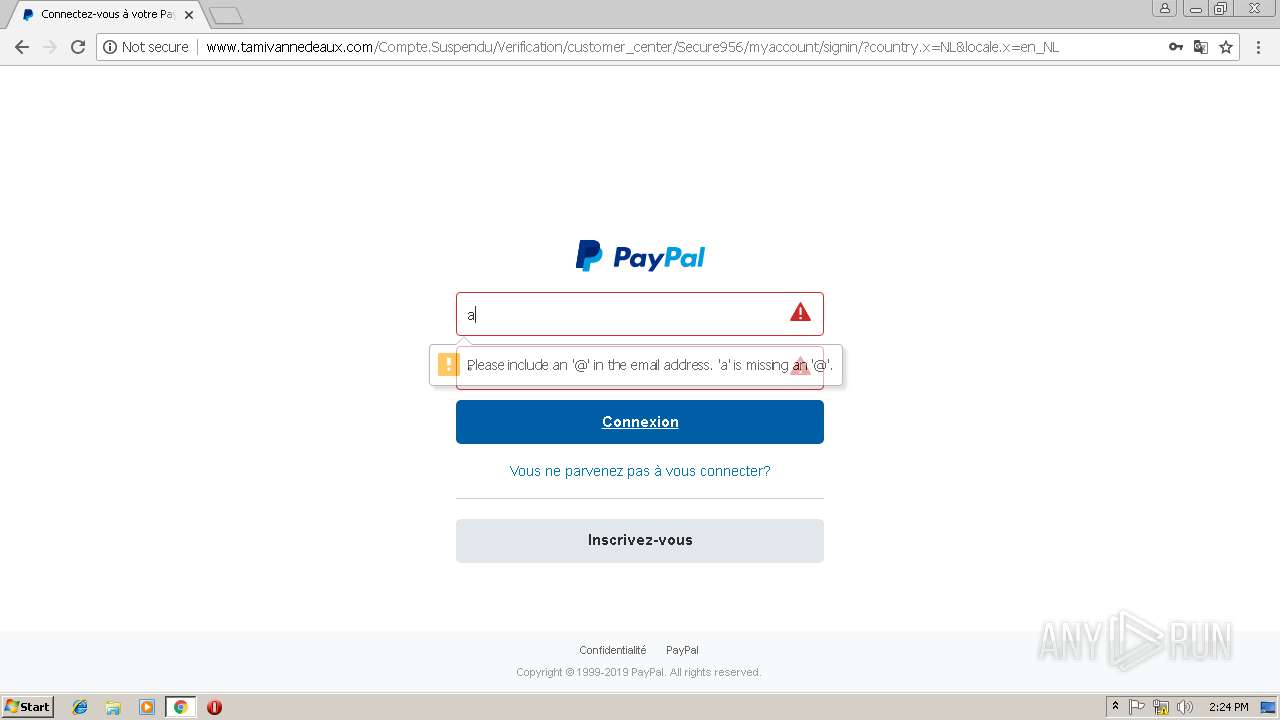
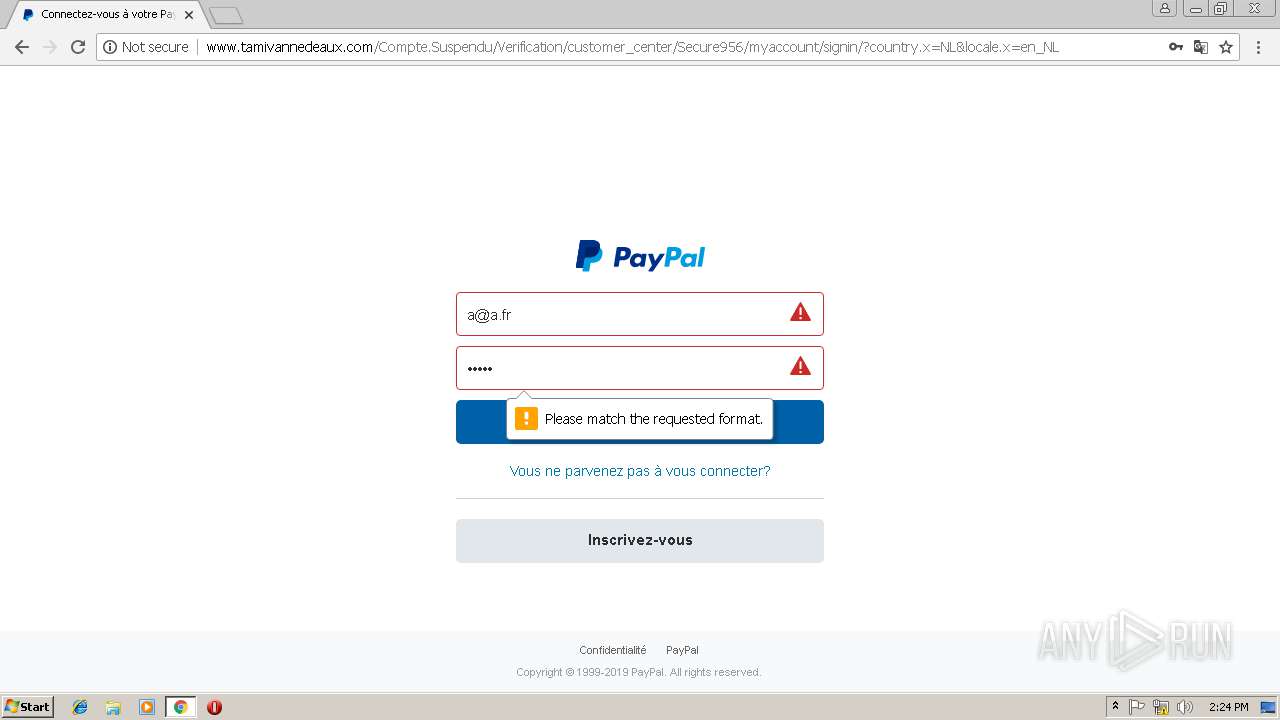
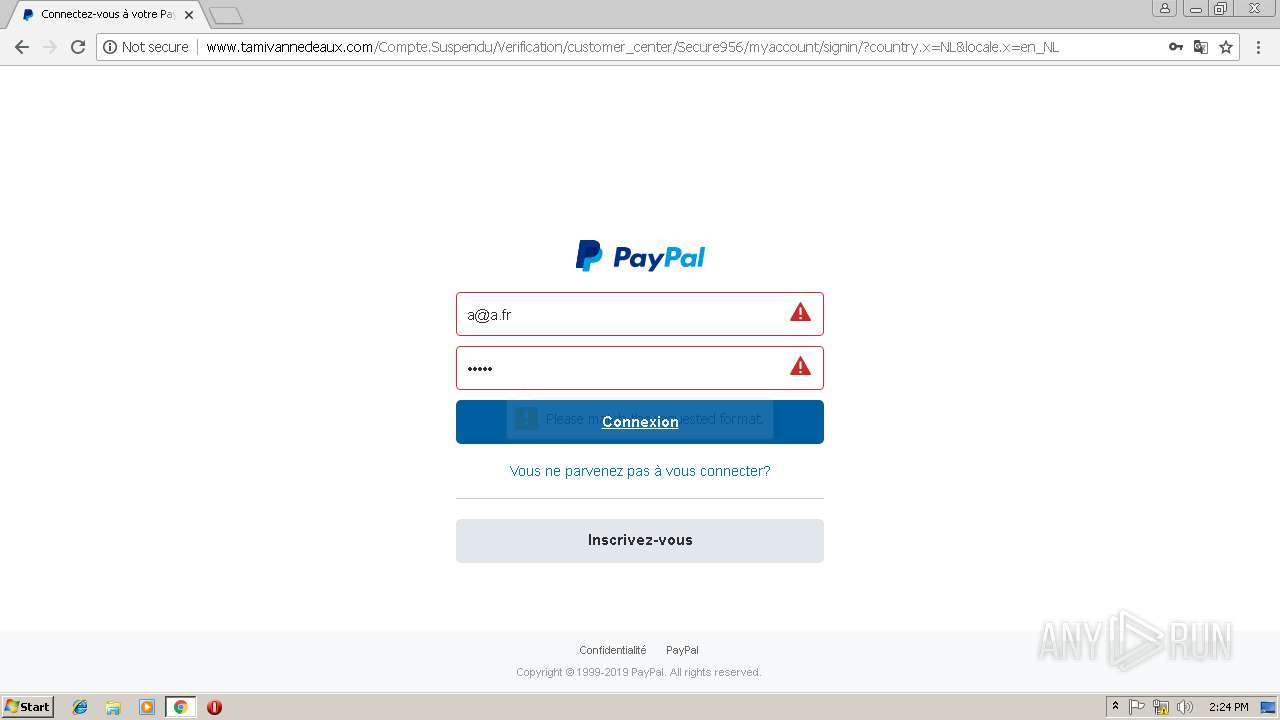
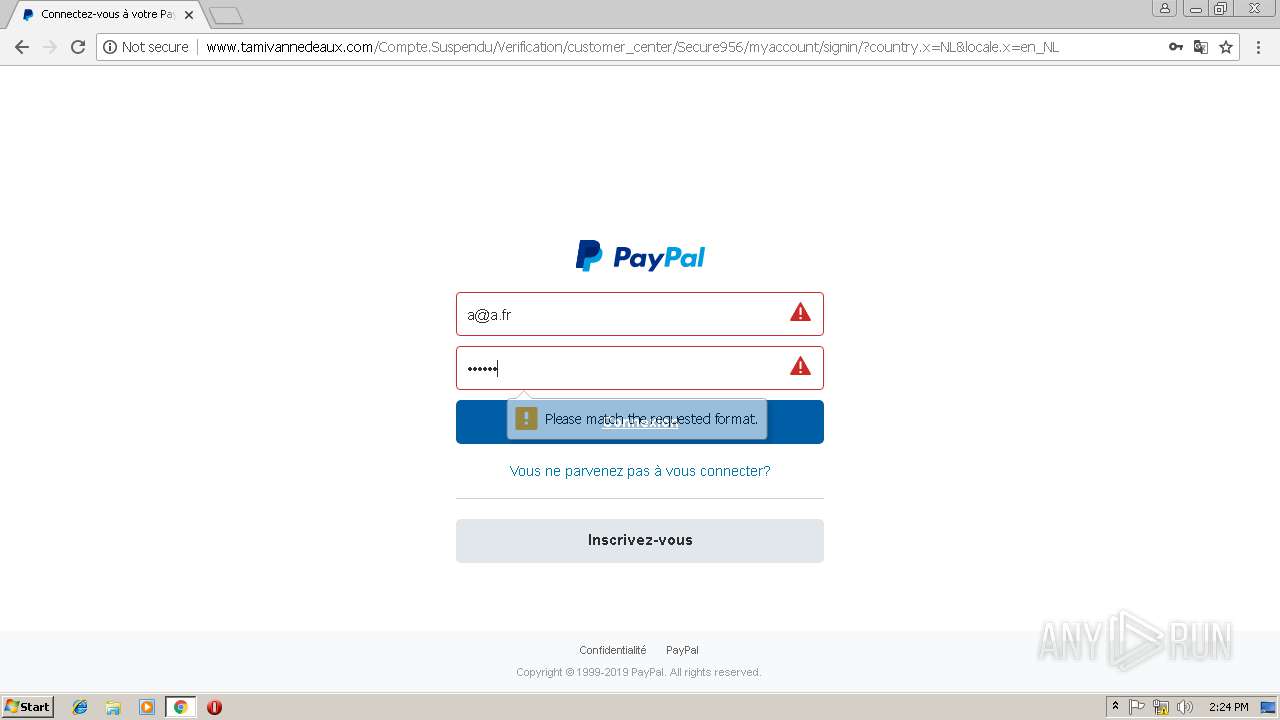
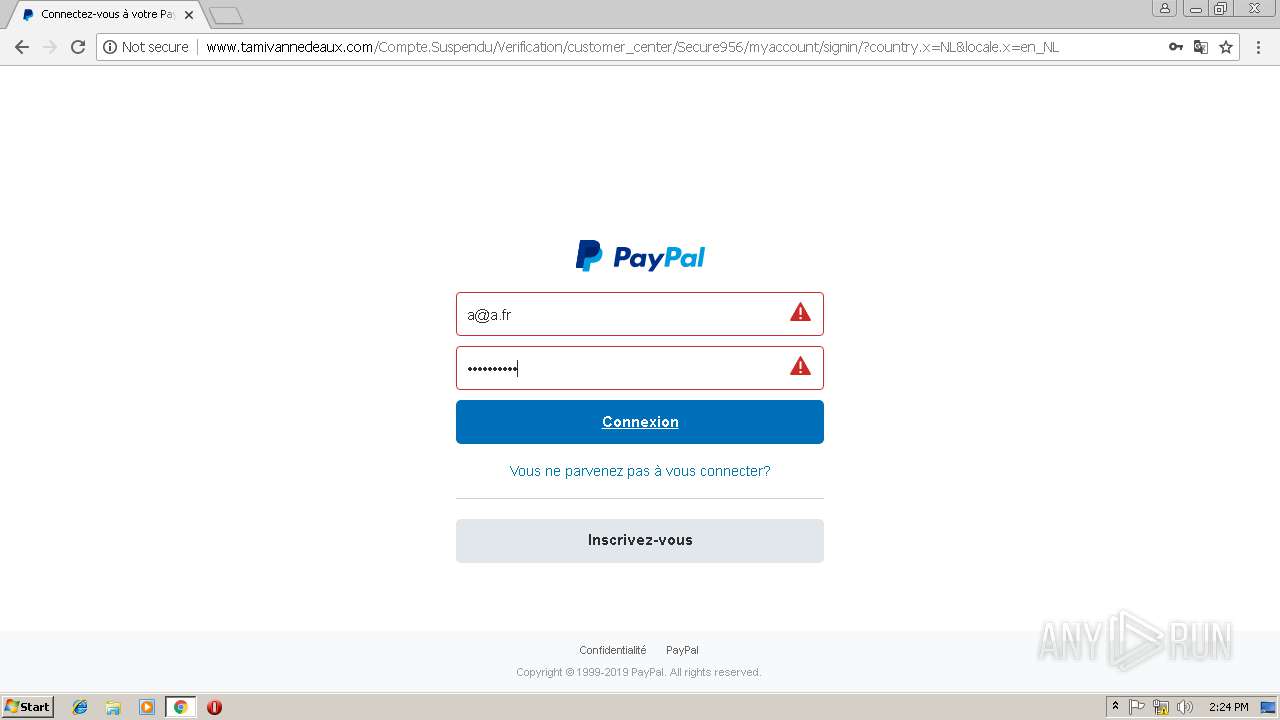
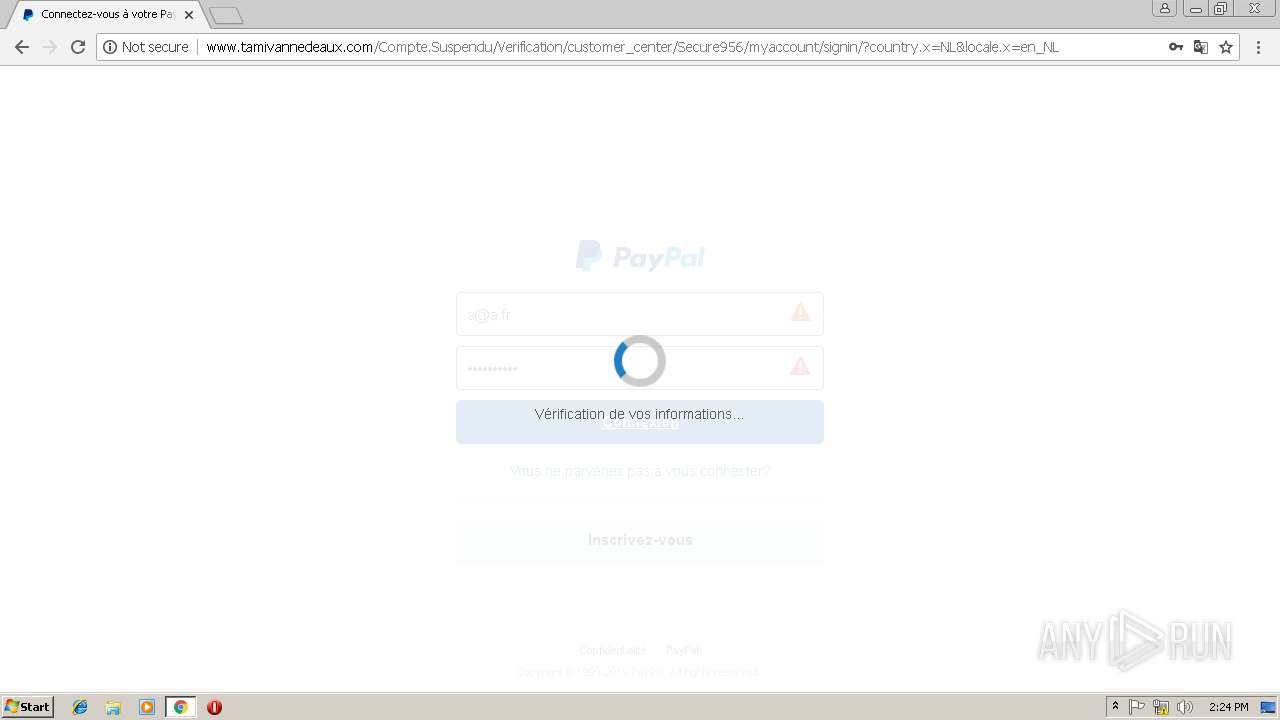
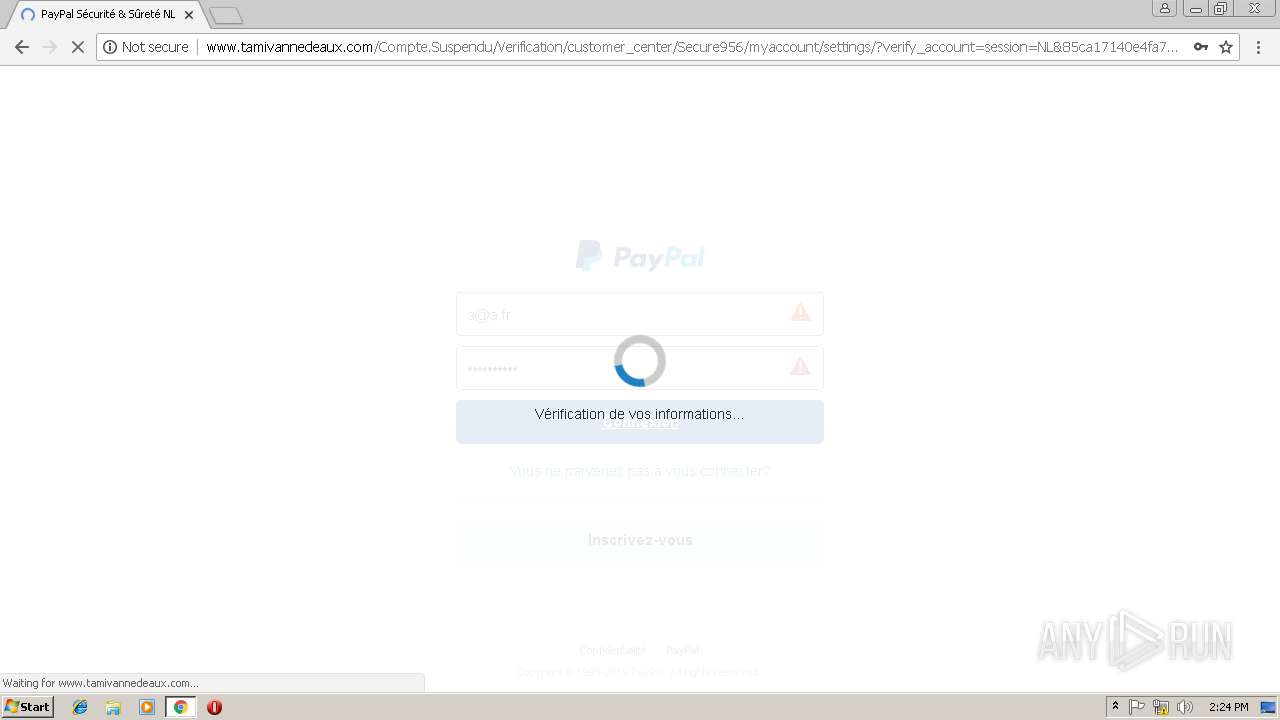
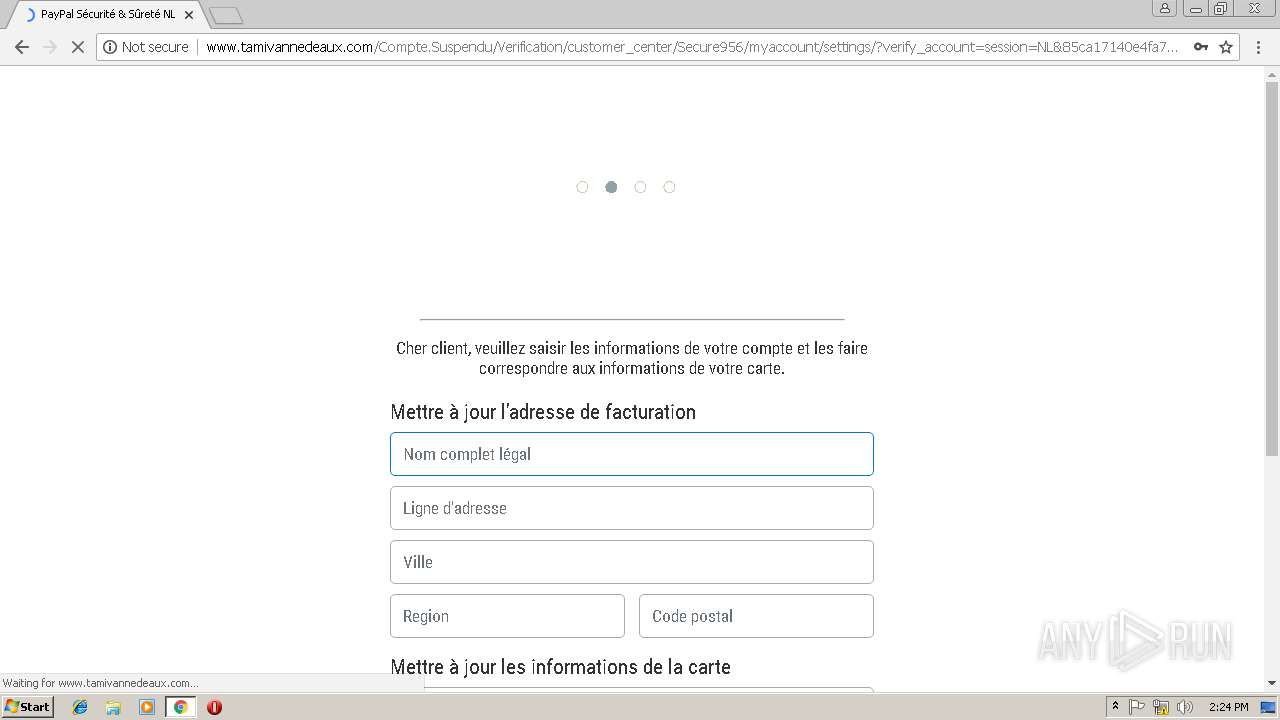
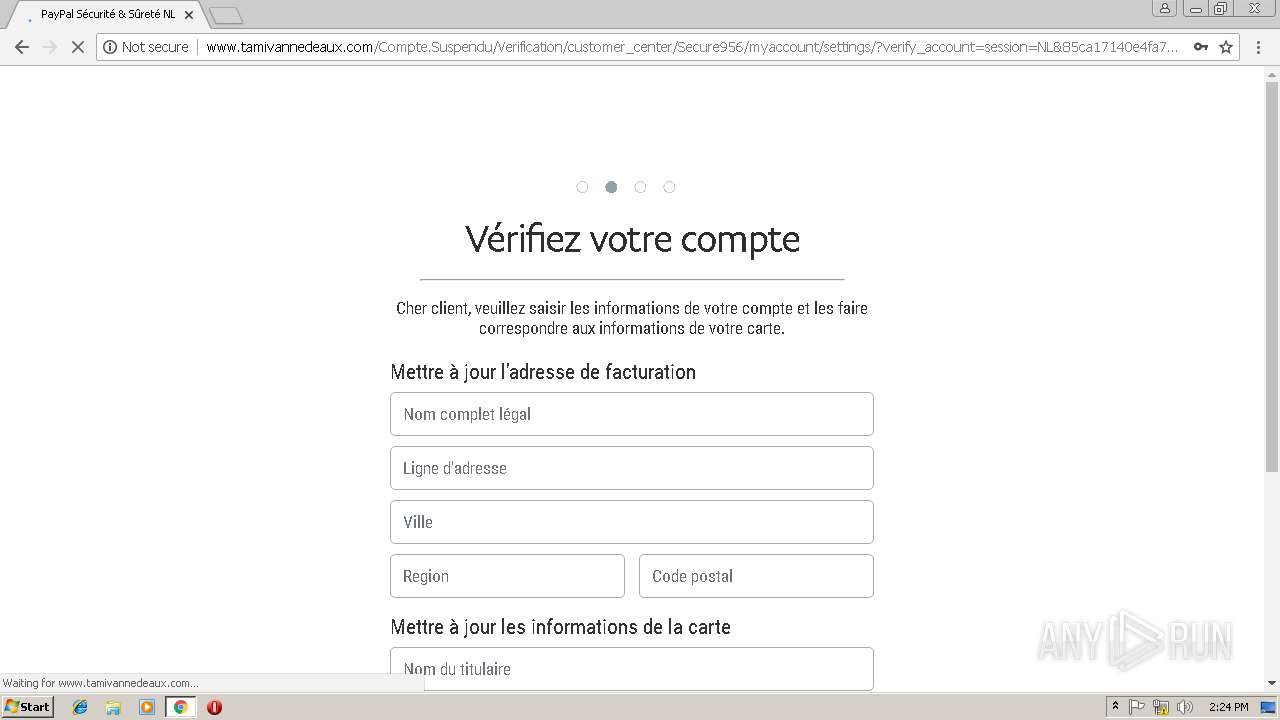
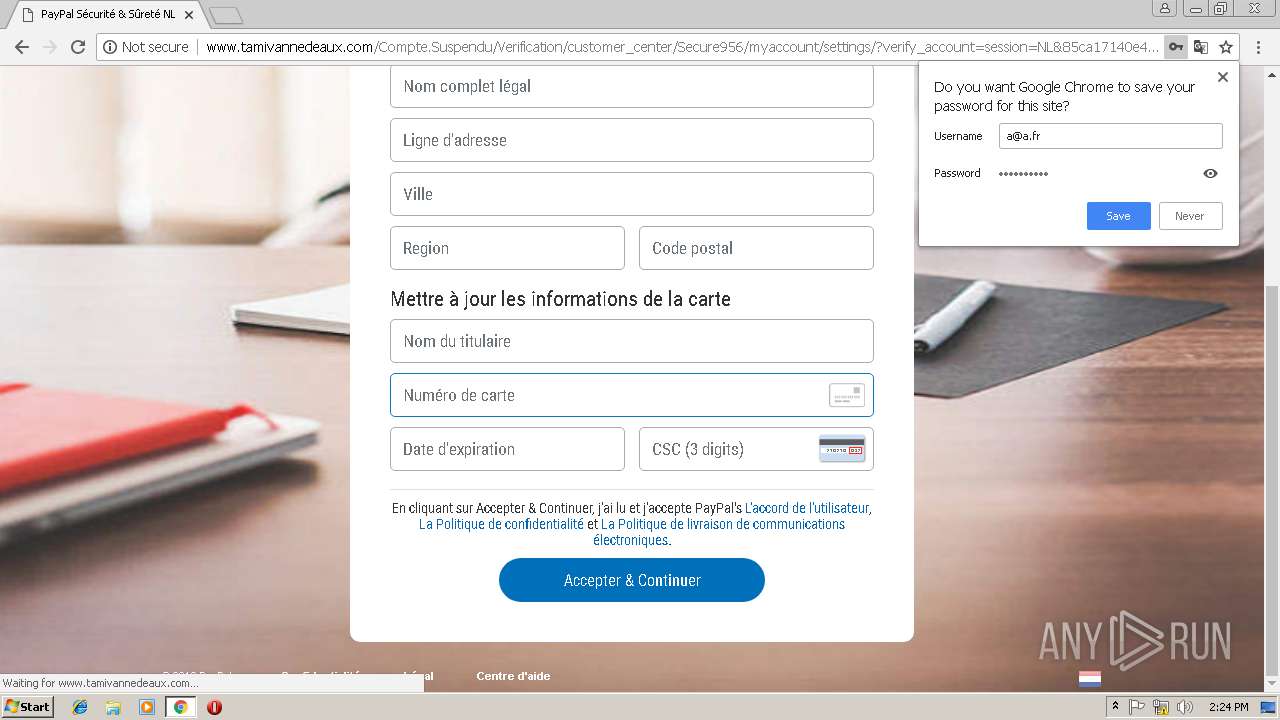
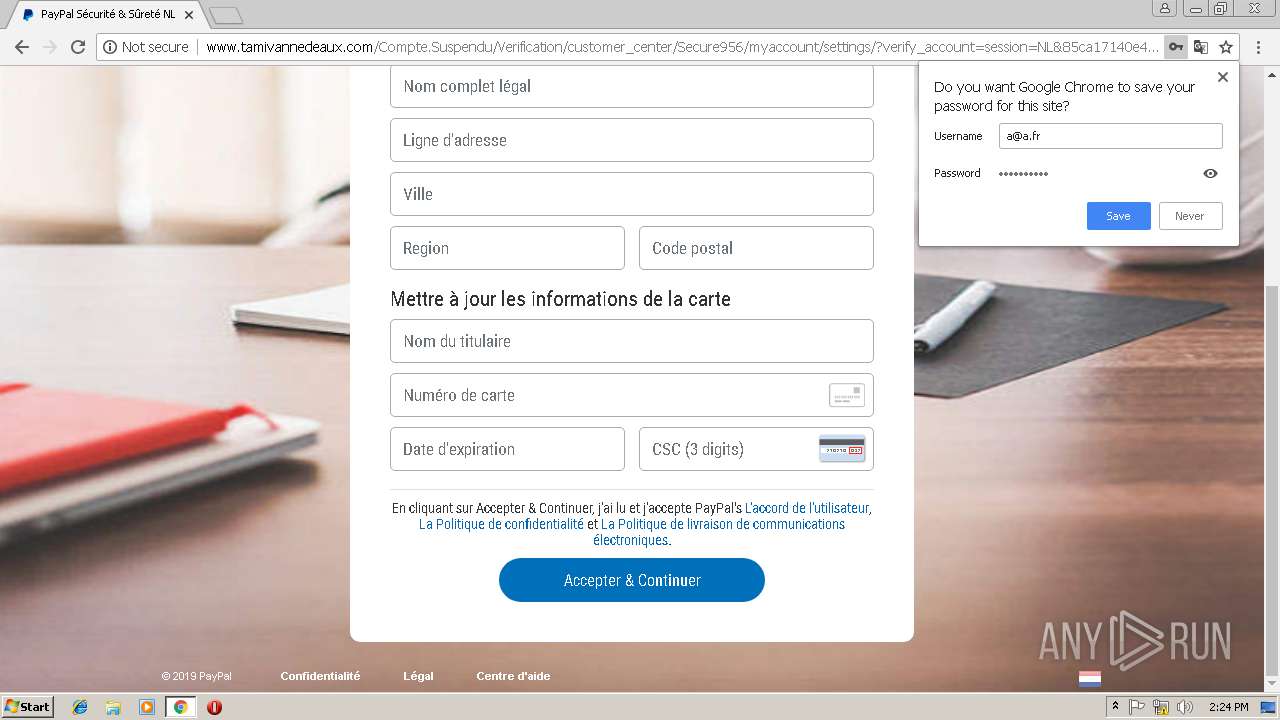
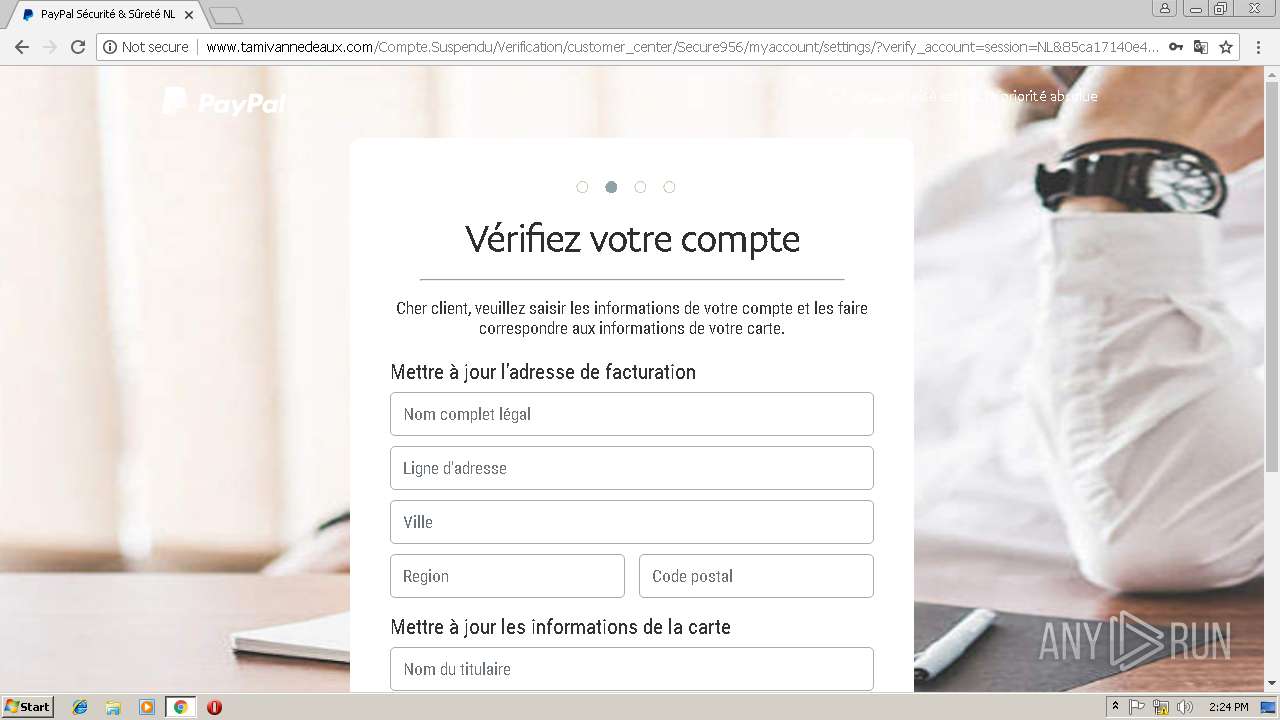
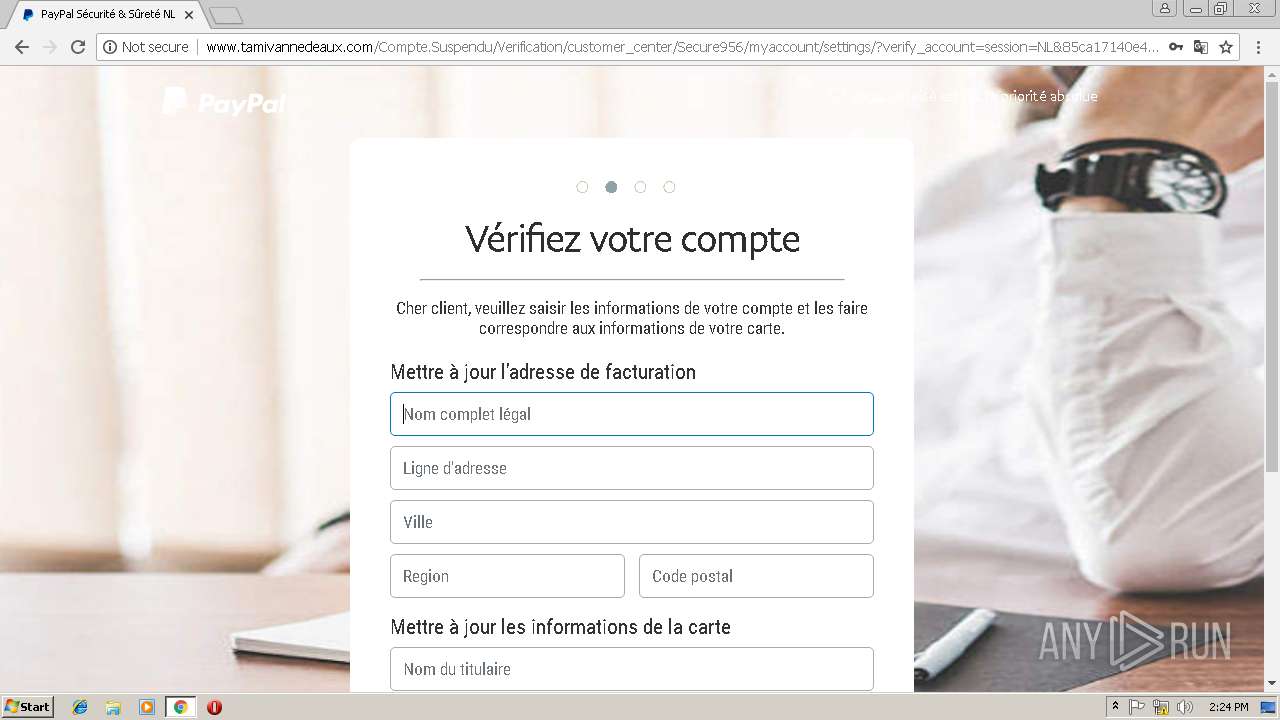
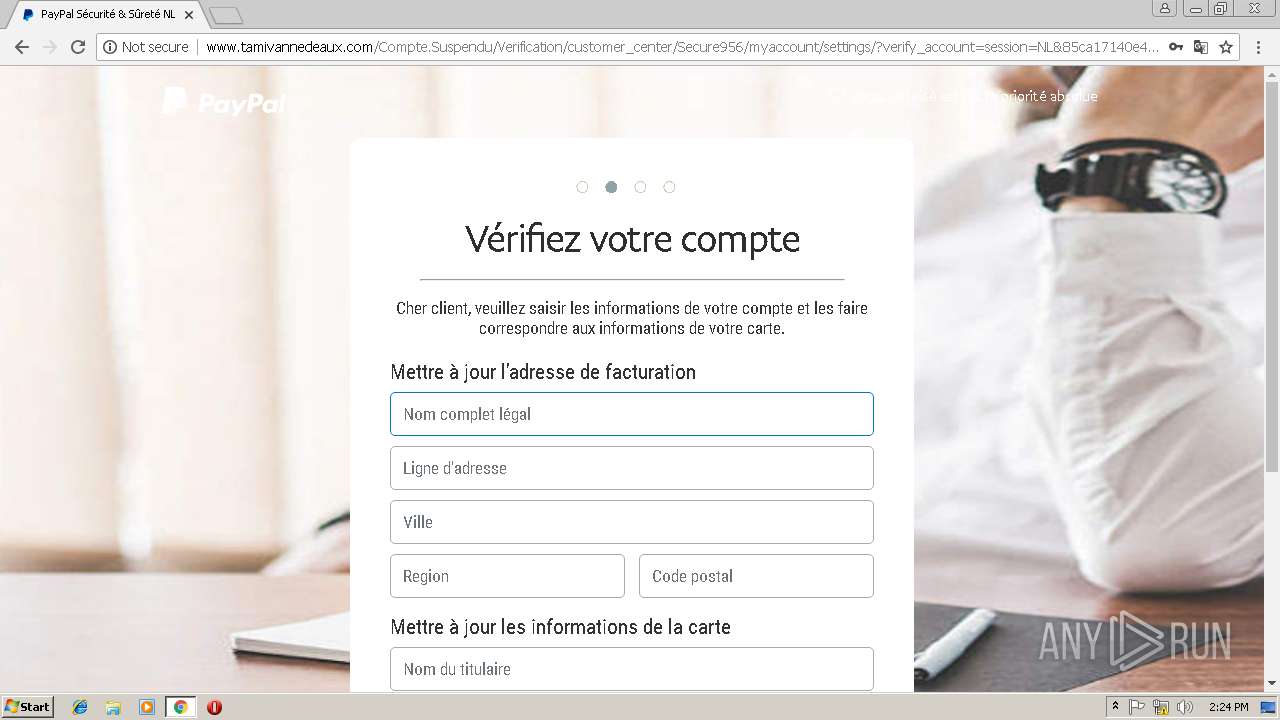
| URL: | http://www.tamivannedeaux.com |
| Full analysis: | https://app.any.run/tasks/e62ed10f-bf79-4594-9176-4cb97e2e1a04 |
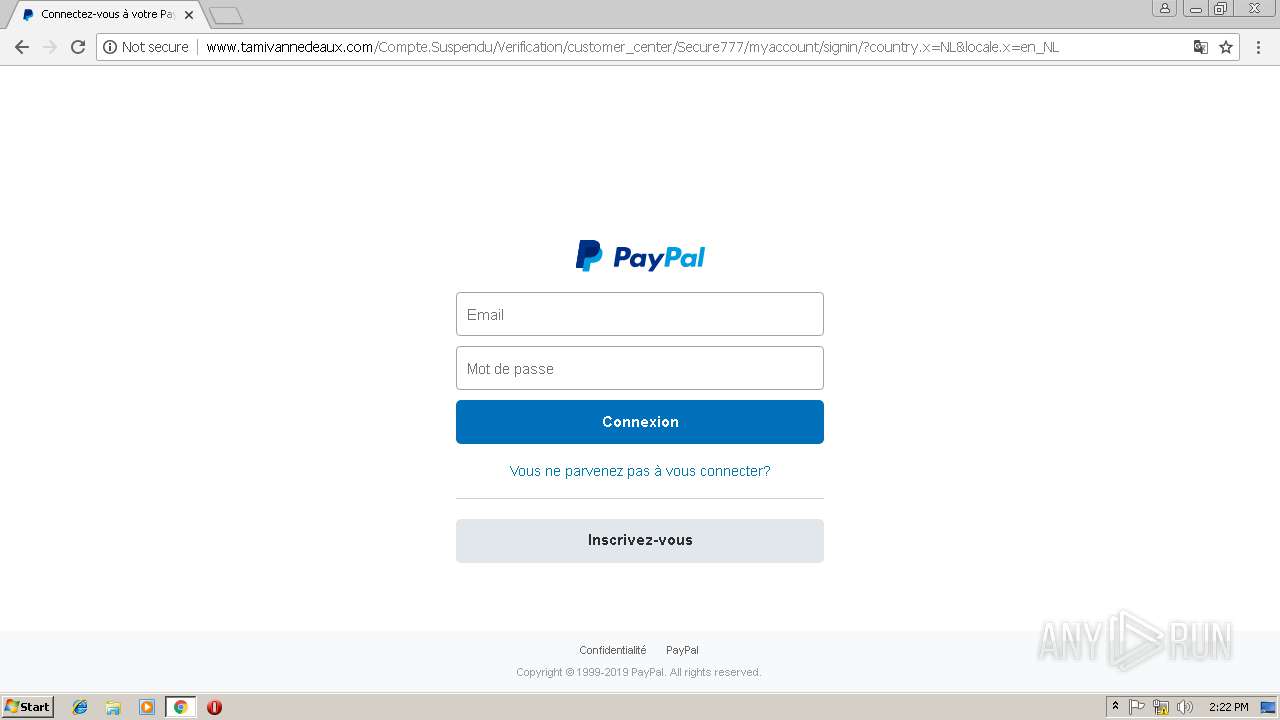
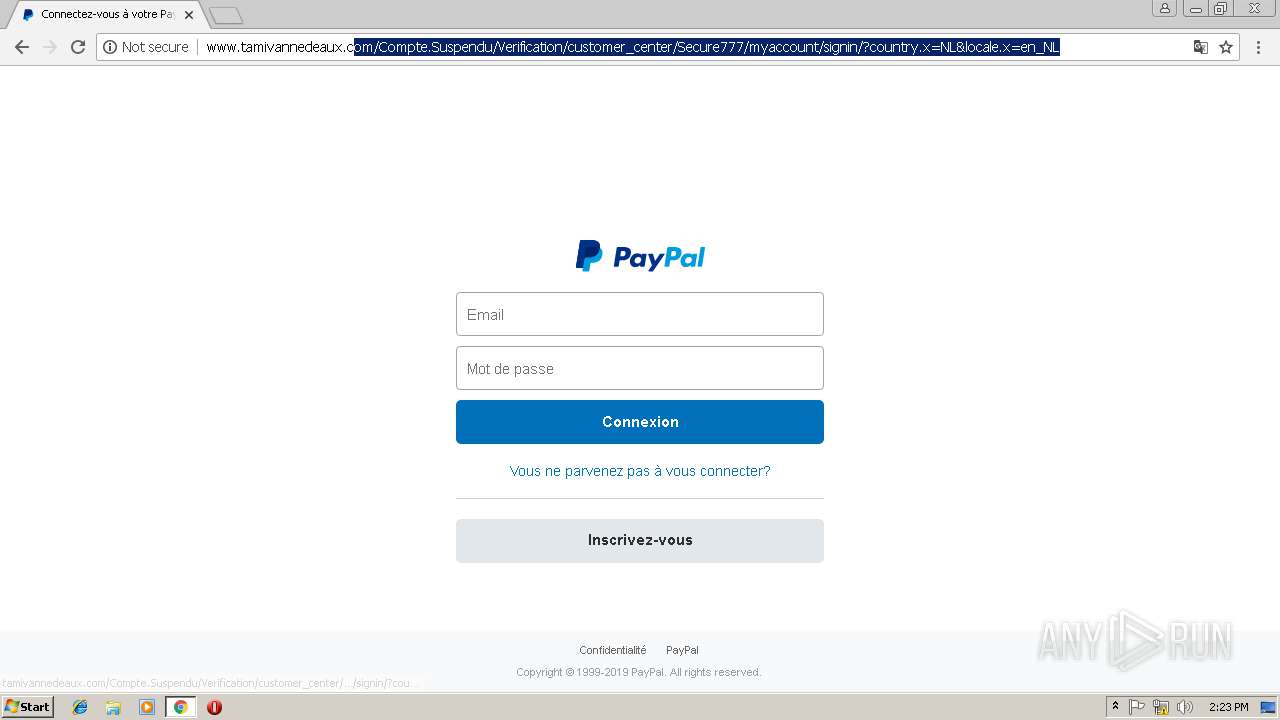
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 14:20:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F689AB2C13A17D978B4AC37810BF0175 |
| SHA1: | 6B96654DB76E47931070D0DEAA27B53BEE781AFC |
| SHA256: | CBEA6FCDAD25151EBD21F70BFB520281A3F757CA2CF176B7A3DE3E9E82B86DB0 |
| SSDEEP: | 3:N1KJS4YskQGKIn:Cc4YskQGKIn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AA494380577D90A2CDEFA9D0D1E41C19 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=0ABBBD81091EF6DA801F8159E0062962 --mojo-platform-channel-handle=2944 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=06F0A89E26151B7EC37DAD82D462C525 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=06F0A89E26151B7EC37DAD82D462C525 --renderer-client-id=4 --mojo-platform-channel-handle=1896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9296E81ED66E6388C216E9C7BA92A4DC --mojo-platform-channel-handle=2560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3028 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.tamivannedeaux.com | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=C1C7B89F1C6E299A1806F17A521DA61B --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C1C7B89F1C6E299A1806F17A521DA61B --renderer-client-id=3 --mojo-platform-channel-handle=2064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=A6381229C331E673F4959CC6F601E027 --mojo-platform-channel-handle=2660 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x700d00b0,0x700d00c0,0x700d00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=A7676A66F15D4A71C9983BAFCE097BBD --mojo-platform-channel-handle=2384 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
524
Read events
459
Write events
61
Delete events
4
Modification events
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3024-13192640462908750 |
Value: 259 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3024-13192640462908750 |
Value: 259 | |||
| (PID) Process: | (3024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
15
Text files
120
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c6a484de-d67a-4c9d-b966-e6a0837a8f8f.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20e870.TMP | text | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF20e870.TMP | text | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old~RF20e8ed.TMP | text | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\909ff781-8828-459d-b831-ca463de97e48.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF20ebdb.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
43
DNS requests
16
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
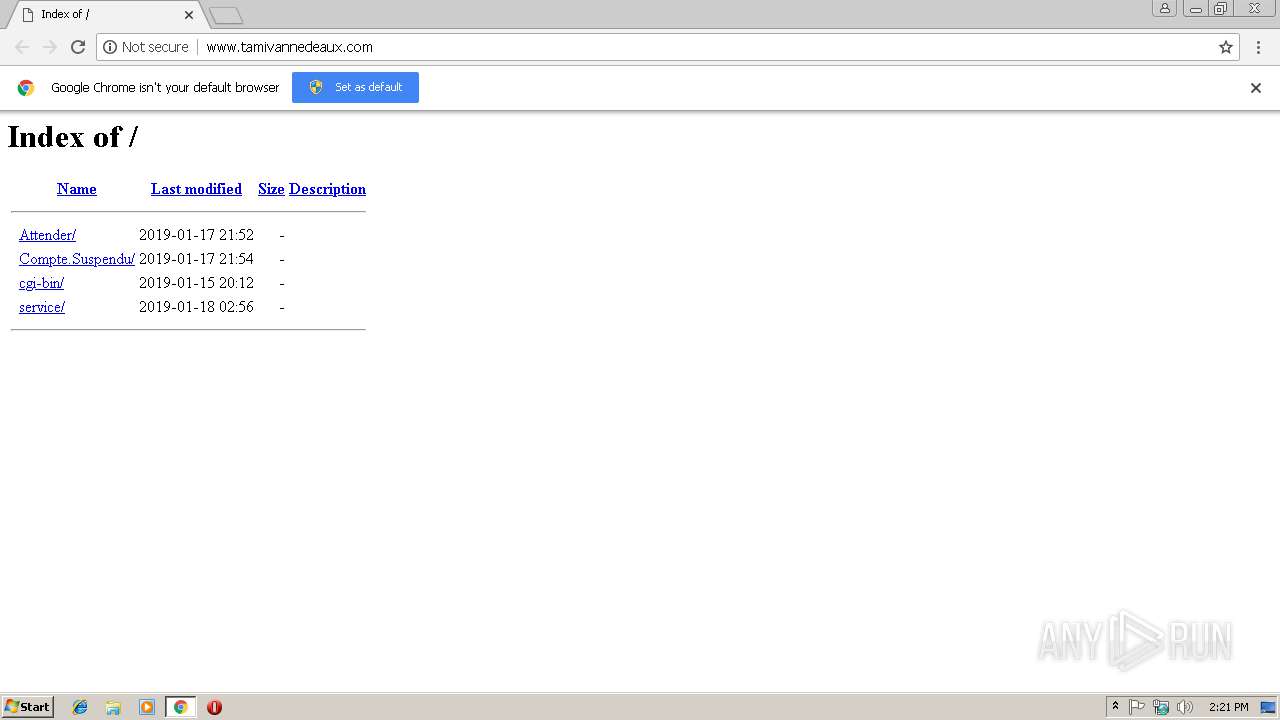
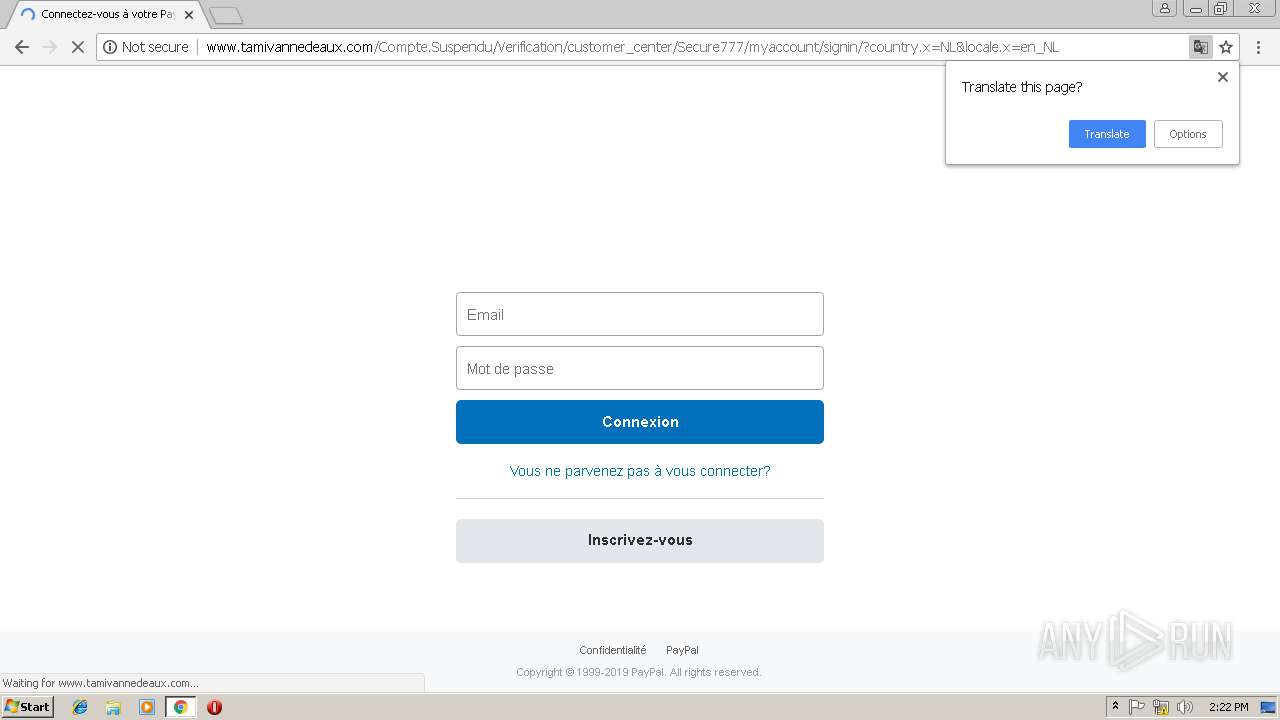
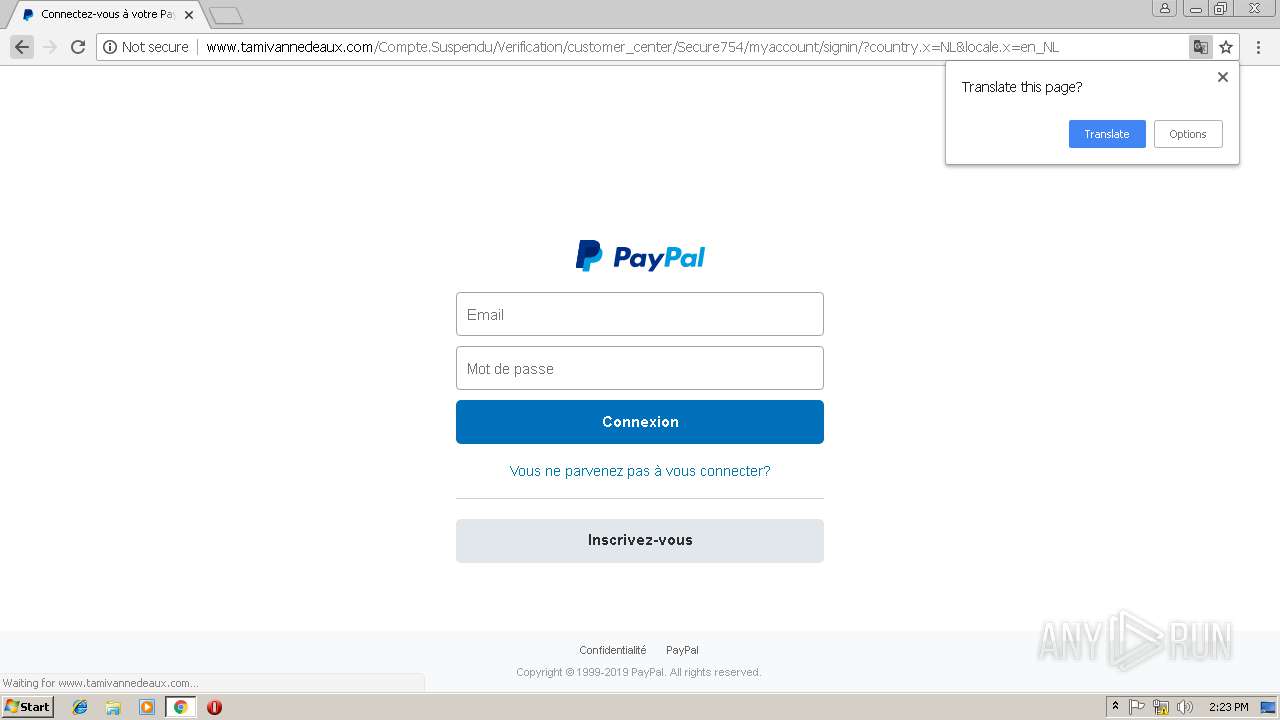
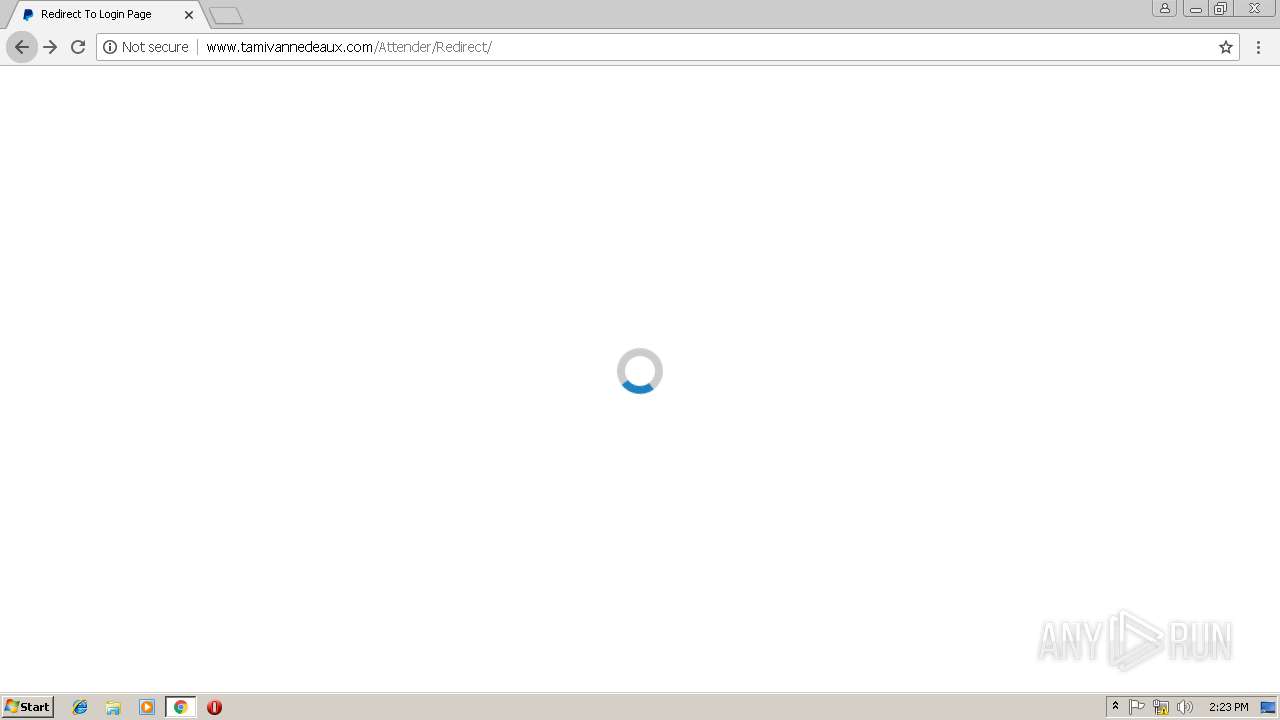
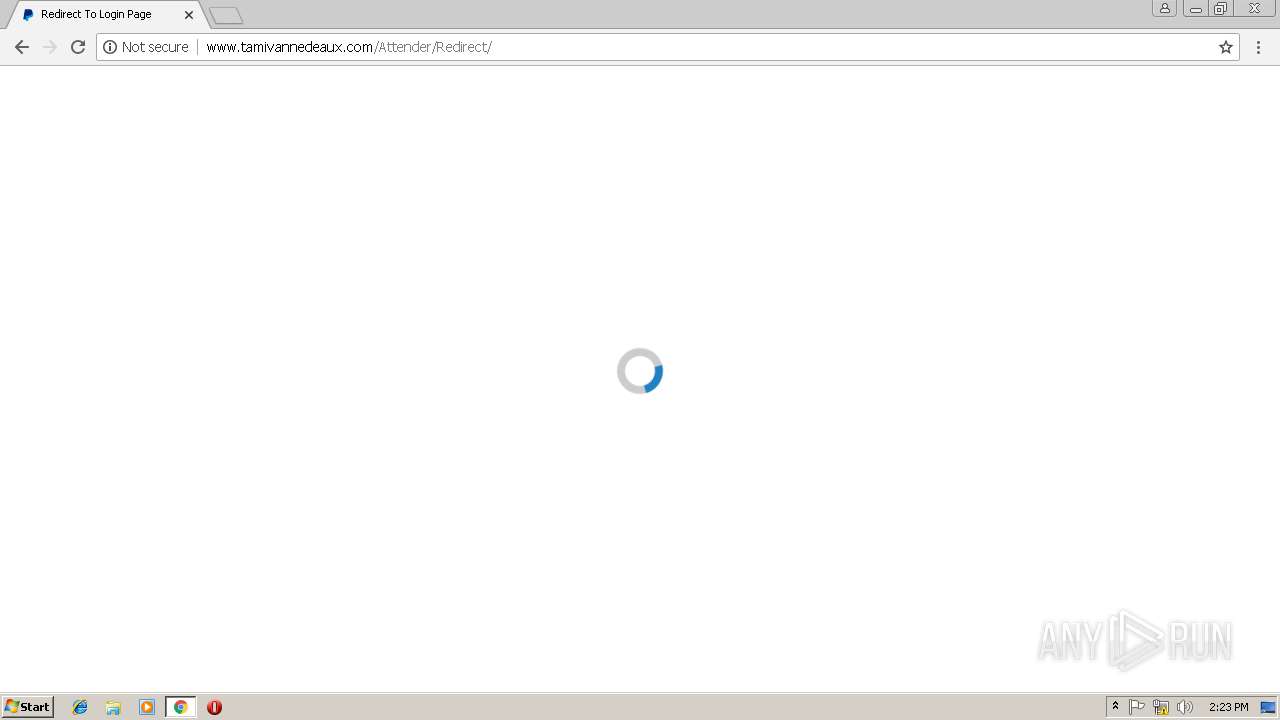
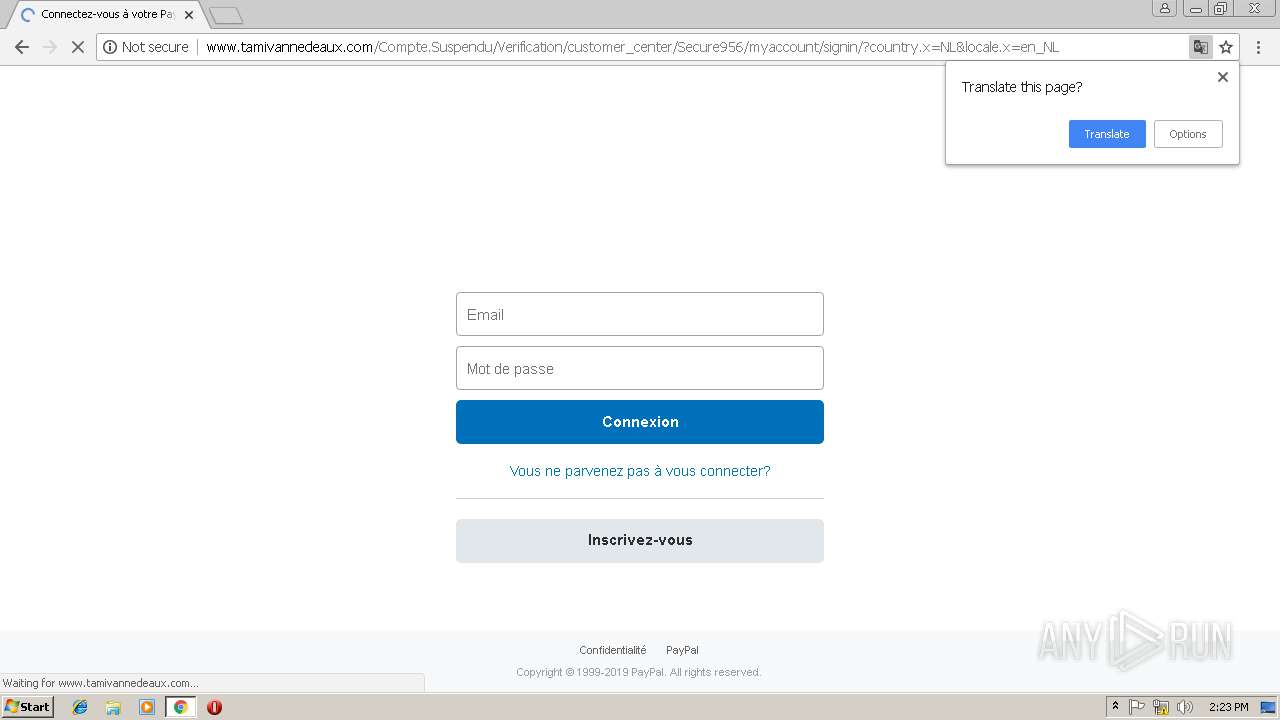
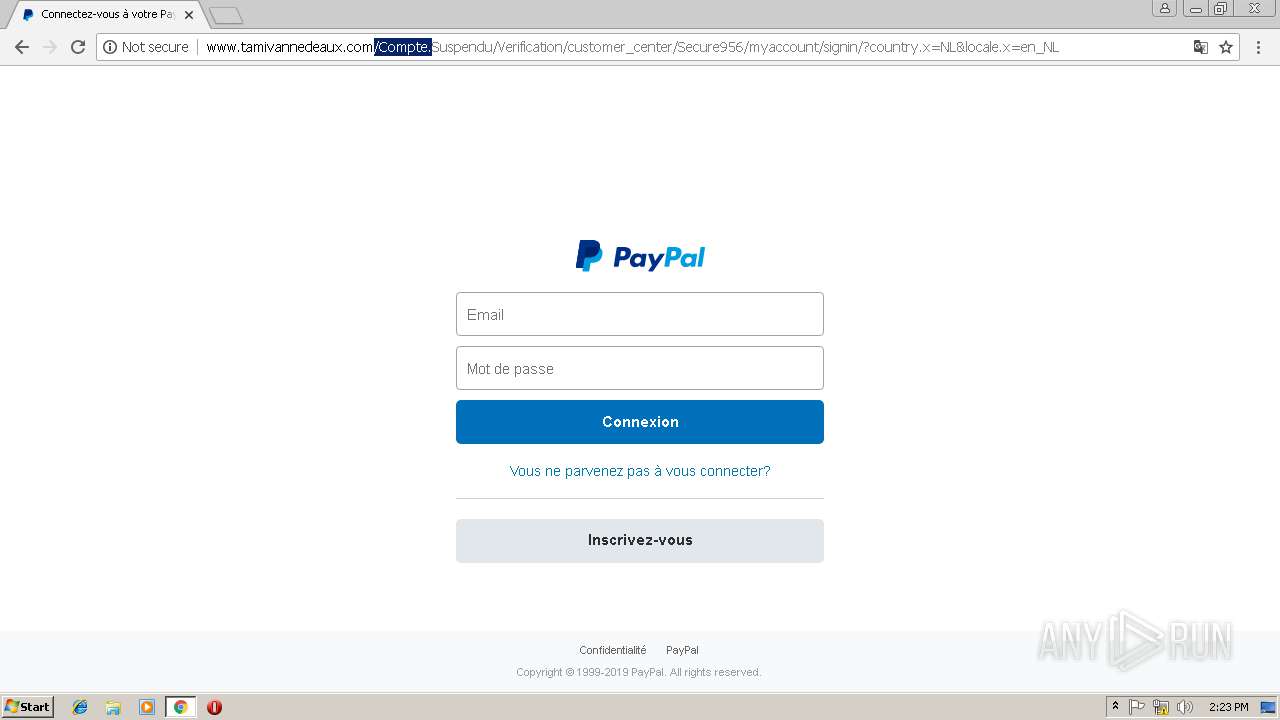
3024 | chrome.exe | GET | — | 91.212.150.239:80 | http://www.tamivannedeaux.com/Compte.Suspendu/Verification | RU | — | — | malicious |
3024 | chrome.exe | GET | 302 | 91.212.150.239:80 | http://www.tamivannedeaux.com/Compte.Suspendu/ | RU | — | — | malicious |
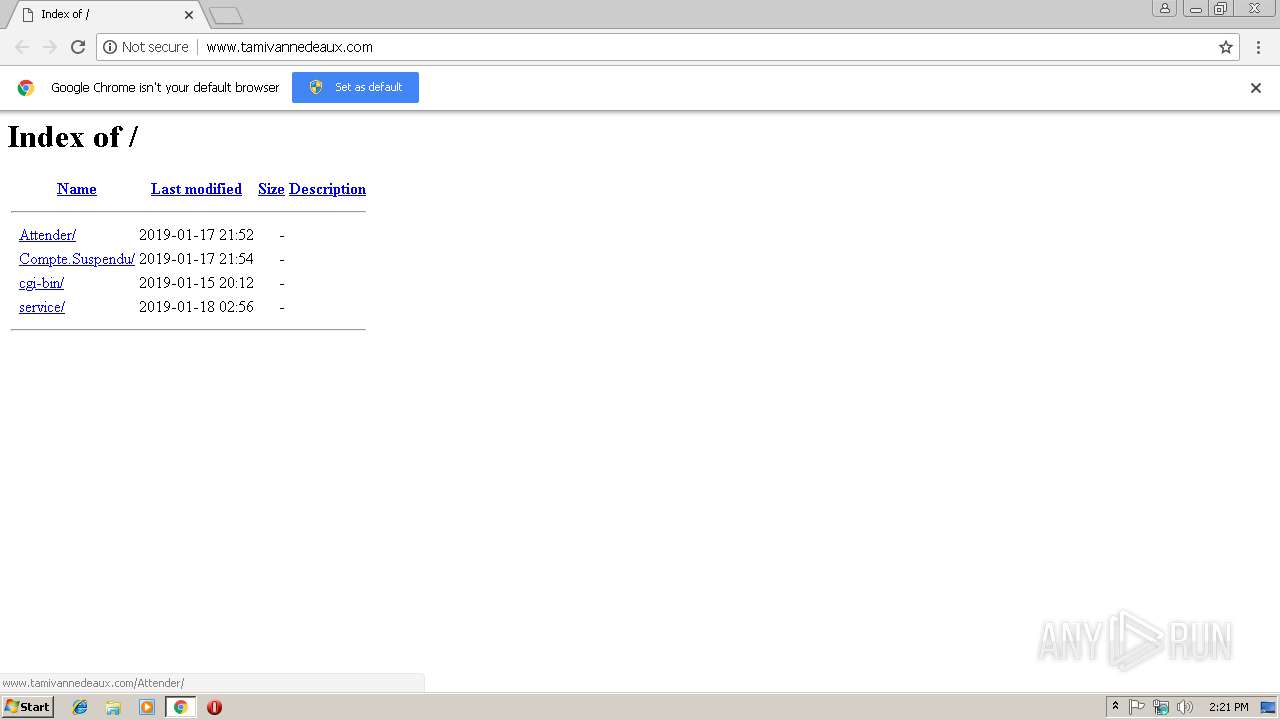
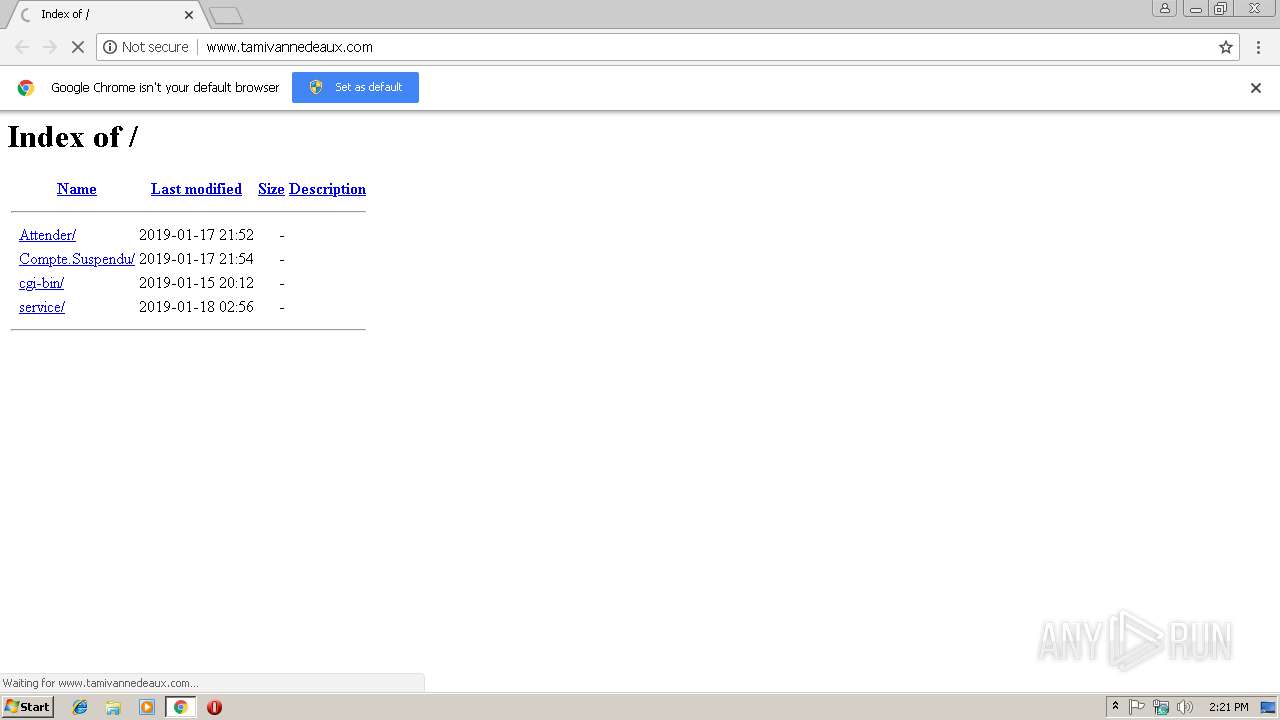
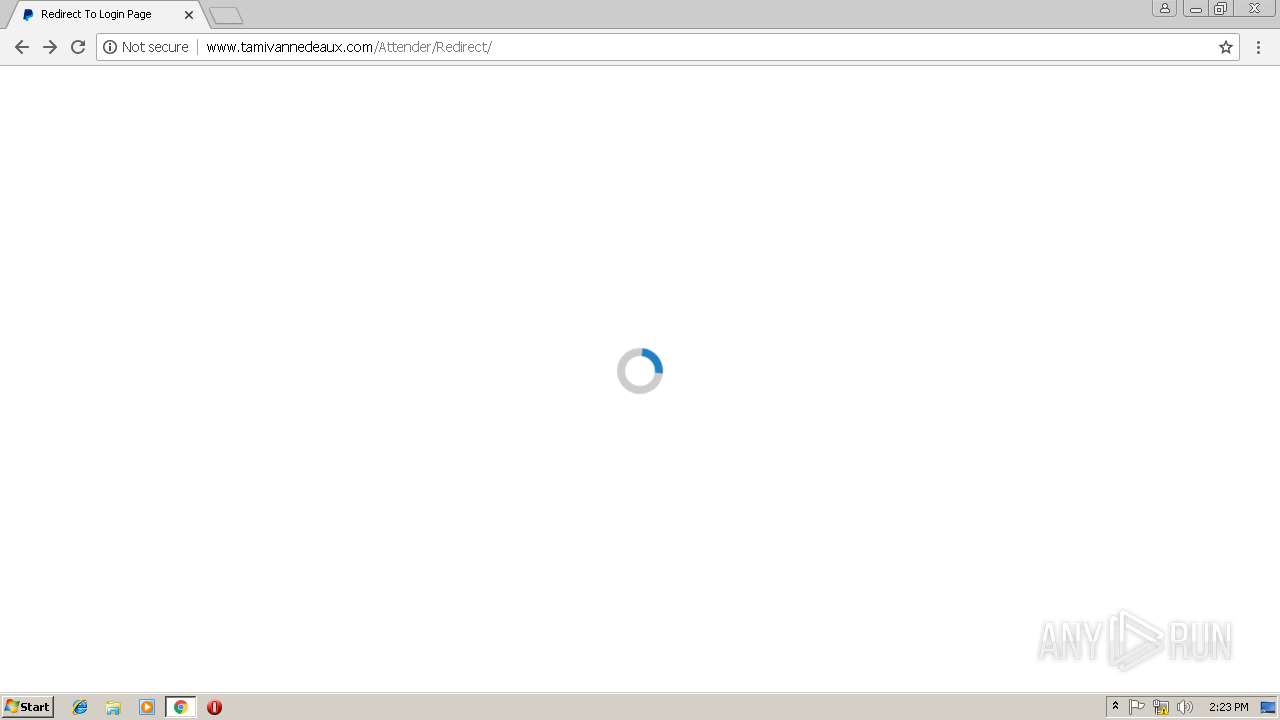
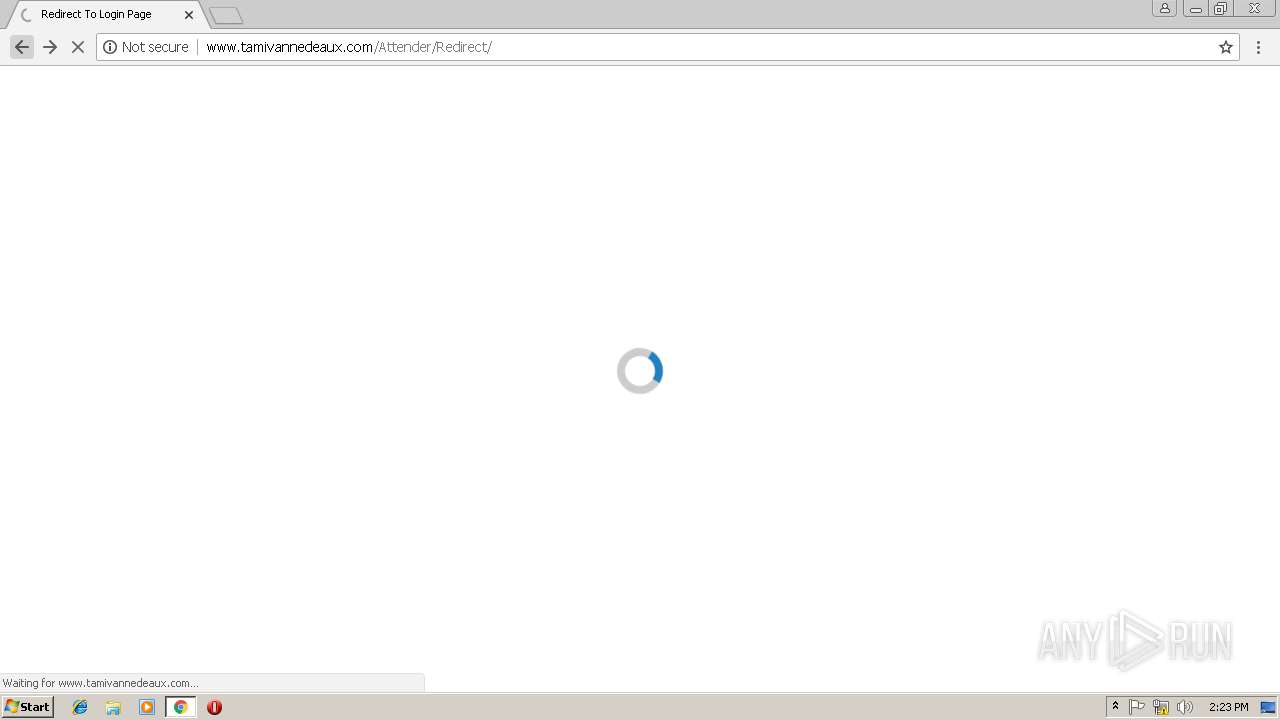
3024 | chrome.exe | GET | 302 | 91.212.150.239:80 | http://www.tamivannedeaux.com/Attender/ | RU | — | — | malicious |
3024 | chrome.exe | GET | — | 91.212.150.239:80 | http://www.tamivannedeaux.com/Attender/ | RU | — | — | malicious |
3024 | chrome.exe | GET | — | 91.212.150.239:80 | http://www.tamivannedeaux.com/Compte.Suspendu | RU | — | — | malicious |
3024 | chrome.exe | GET | 301 | 91.212.150.239:80 | http://www.tamivannedeaux.com/Attender/Redirect | RU | html | 256 b | malicious |
3024 | chrome.exe | GET | 200 | 91.212.150.239:80 | http://www.tamivannedeaux.com/Attender/Redirect/css/yass-rotate.css | RU | text | 46.4 Kb | malicious |
3024 | chrome.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEHiupDHBXOt1ew2KYQp0jmc%3D | NL | der | 1.71 Kb | shared |
3024 | chrome.exe | GET | 200 | 91.212.150.239:80 | http://www.tamivannedeaux.com/Attender/Redirect/ | RU | html | 1.15 Kb | malicious |
3024 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3024 | chrome.exe | 91.212.150.239:80 | www.tamivannedeaux.com | NForce Entertainment B.V. | RU | suspicious |
3024 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 216.58.208.35:80 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 2.18.232.222:443 | www.paypalobjects.com | Akamai International B.V. | — | whitelisted |
3024 | chrome.exe | 23.51.123.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
3024 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
3024 | chrome.exe | 172.217.16.138:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
www.tamivannedeaux.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.paypalobjects.com |
| whitelisted |
s.symcd.com |
| shared |
ocsp.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
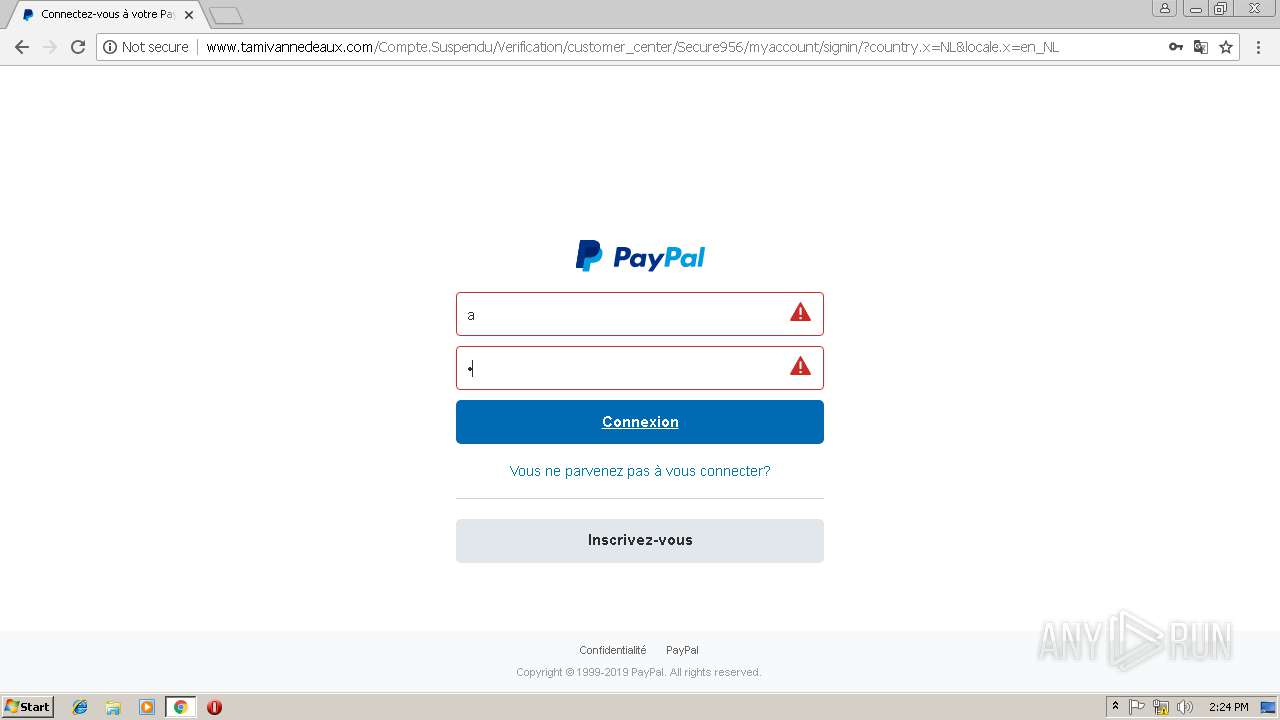
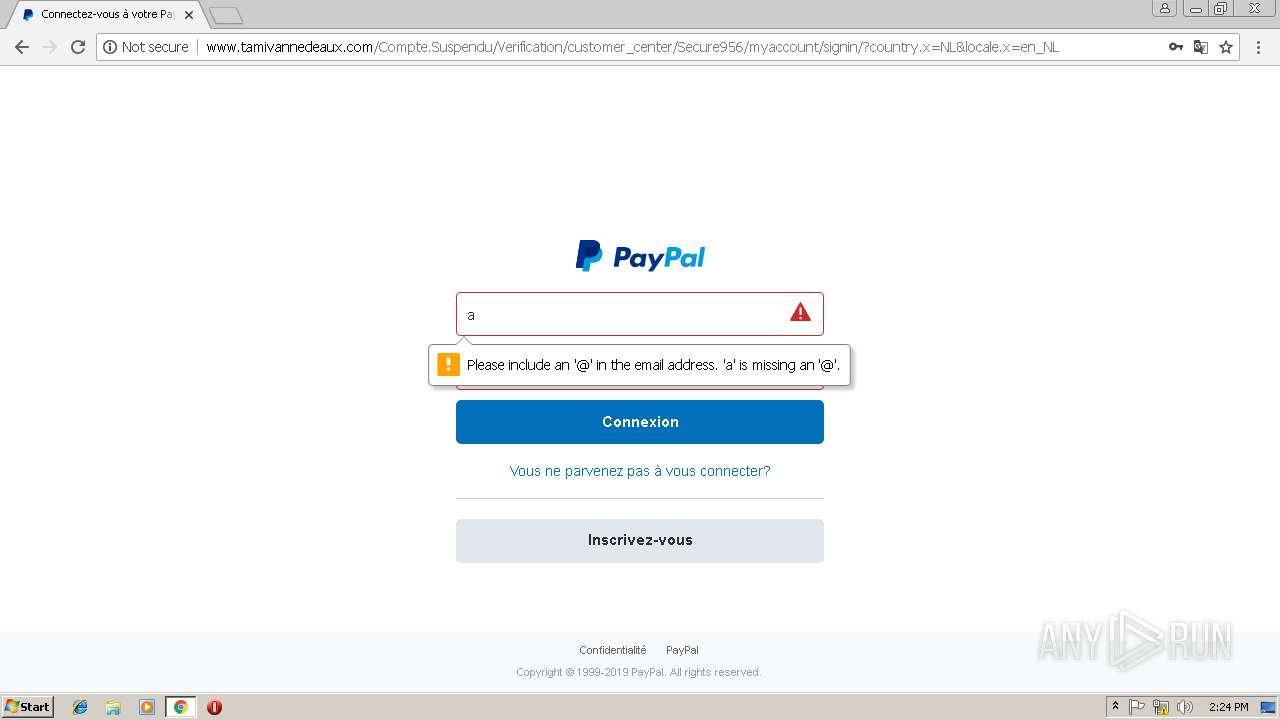
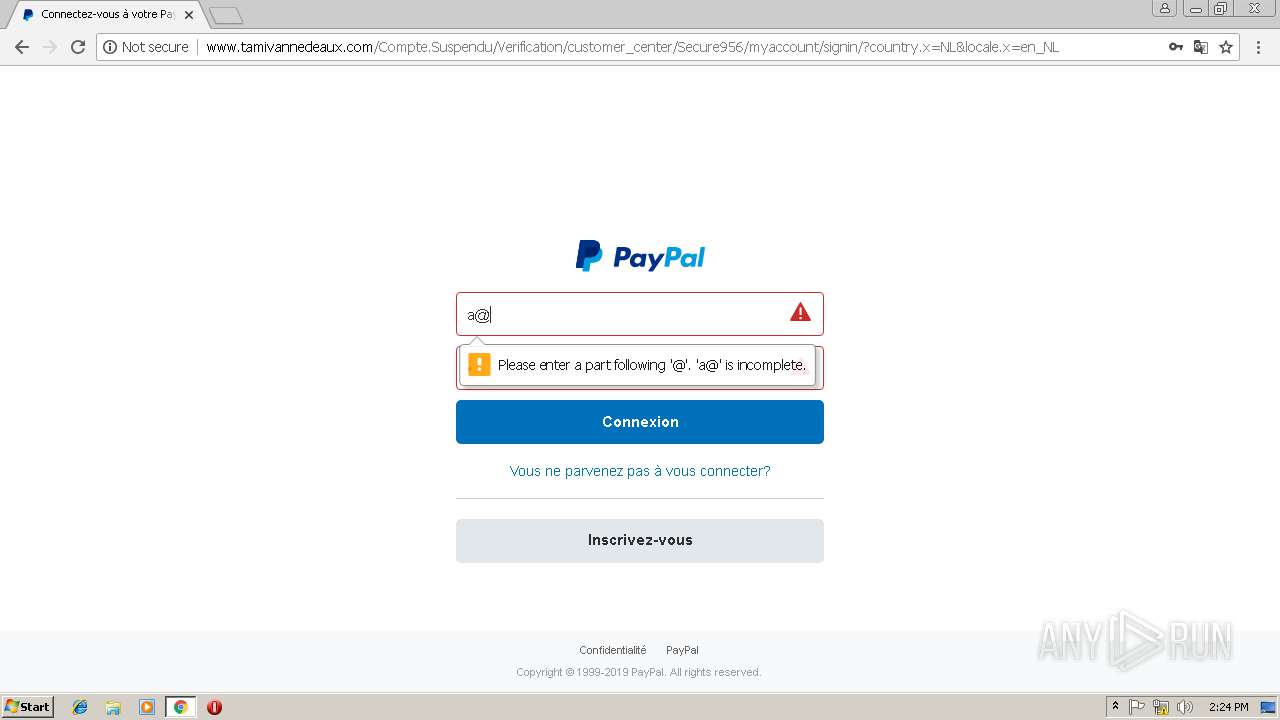
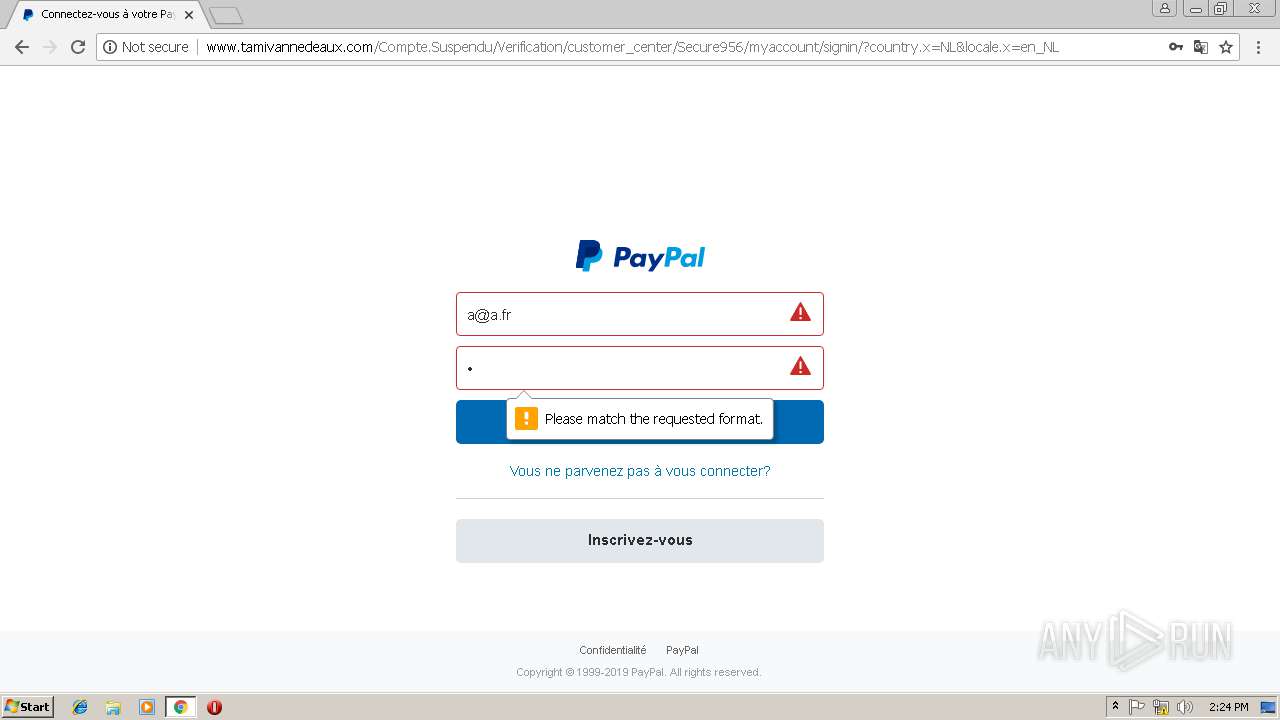
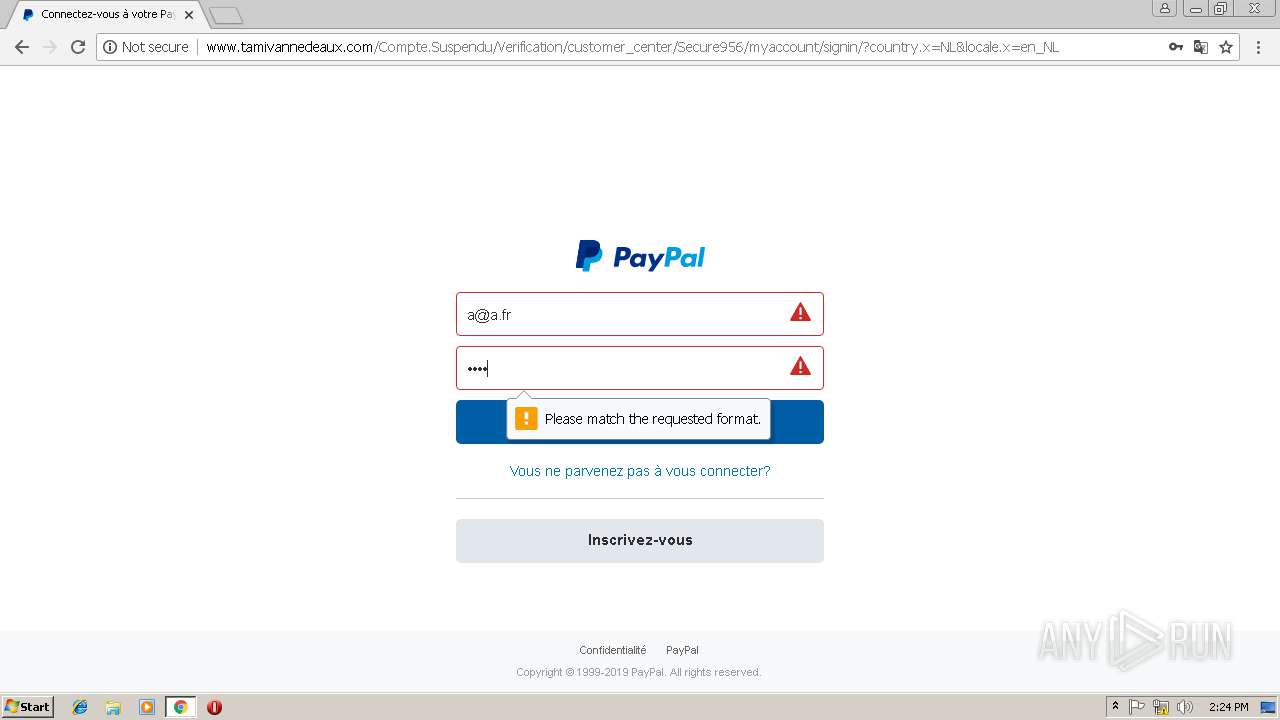
3024 | chrome.exe | A Network Trojan was detected | ET INFO Suspicious HTML Hex Obfuscated Title - Possible Phishing Landing Jun 28 2017 |
3024 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Paypal Phishing Landing Jun 28 2017 |
4 ETPRO signatures available at the full report