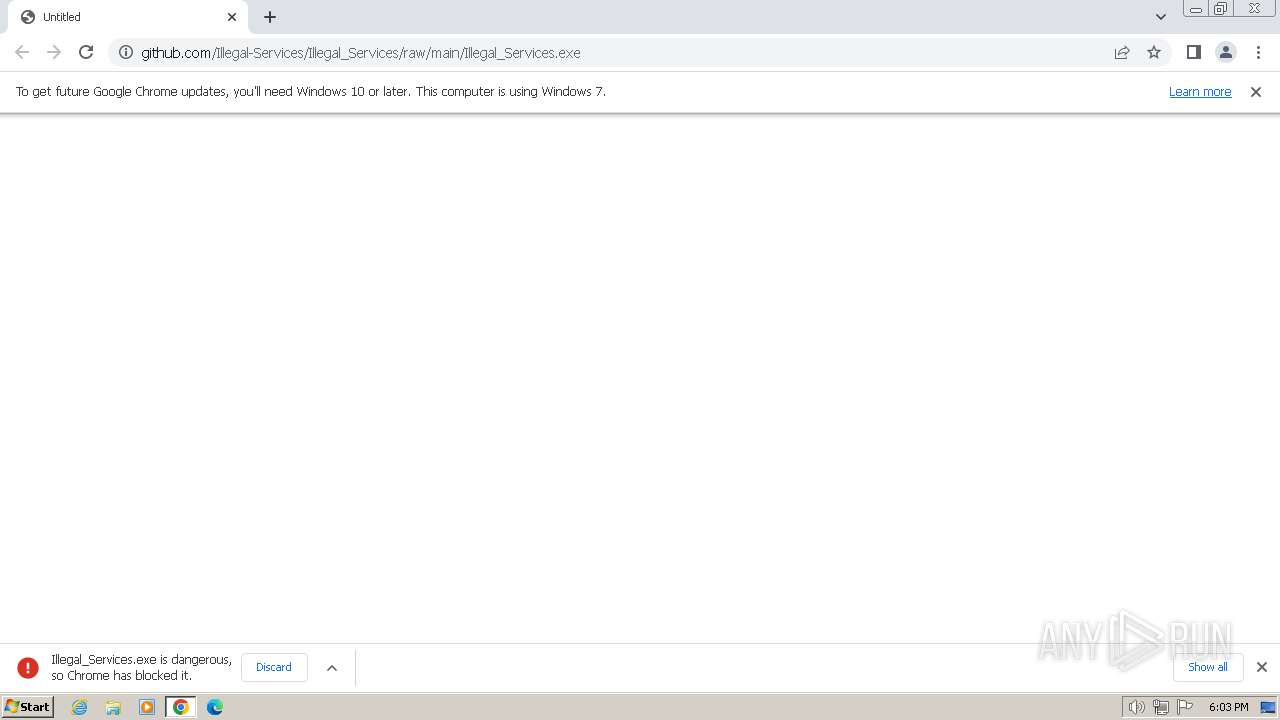
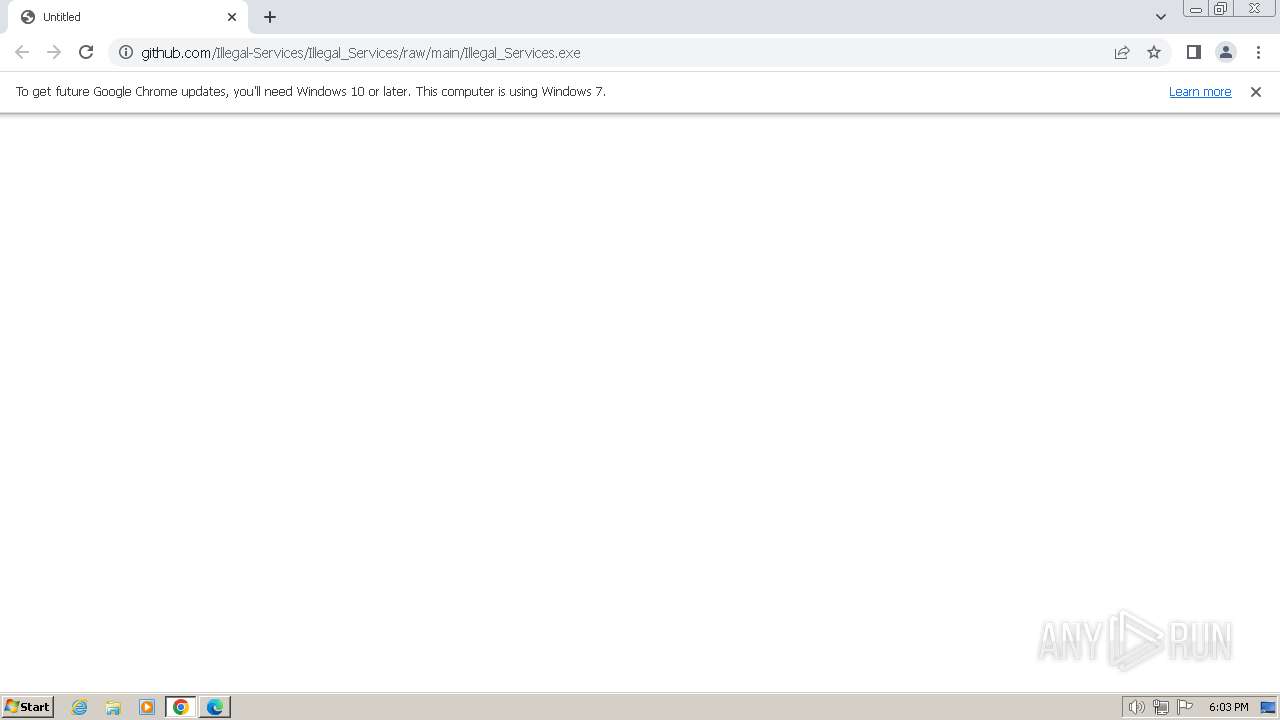
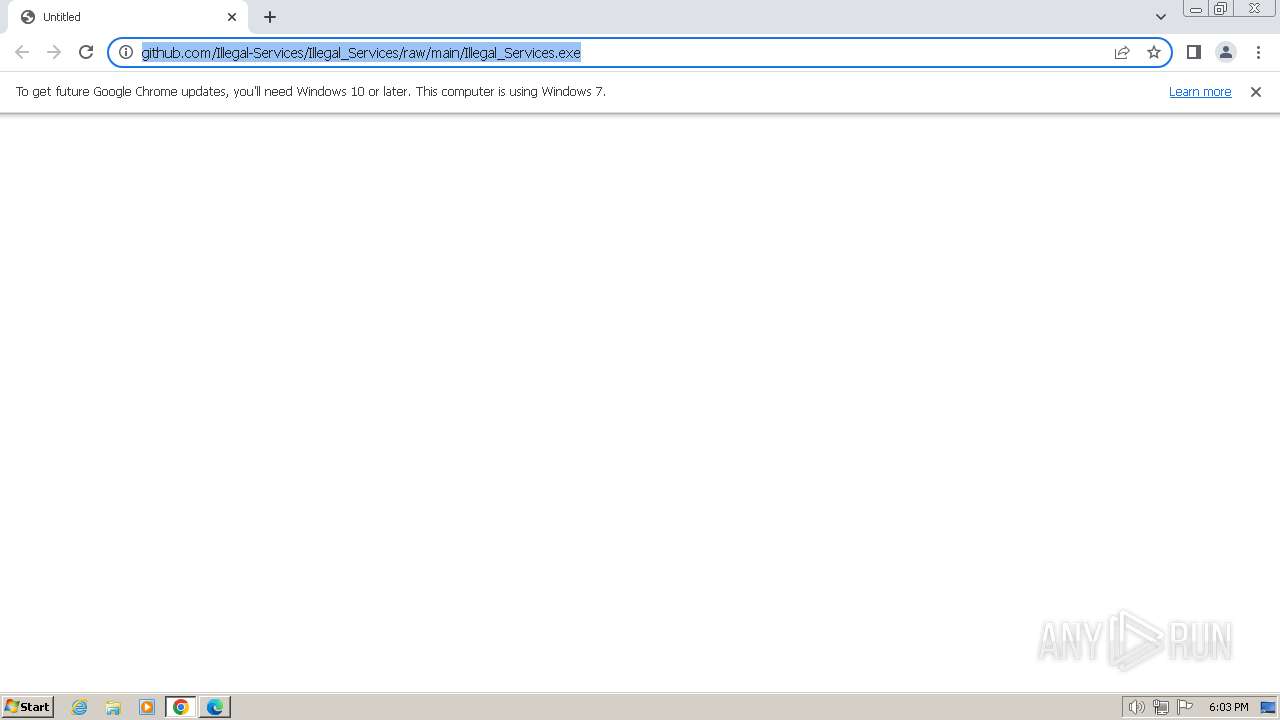
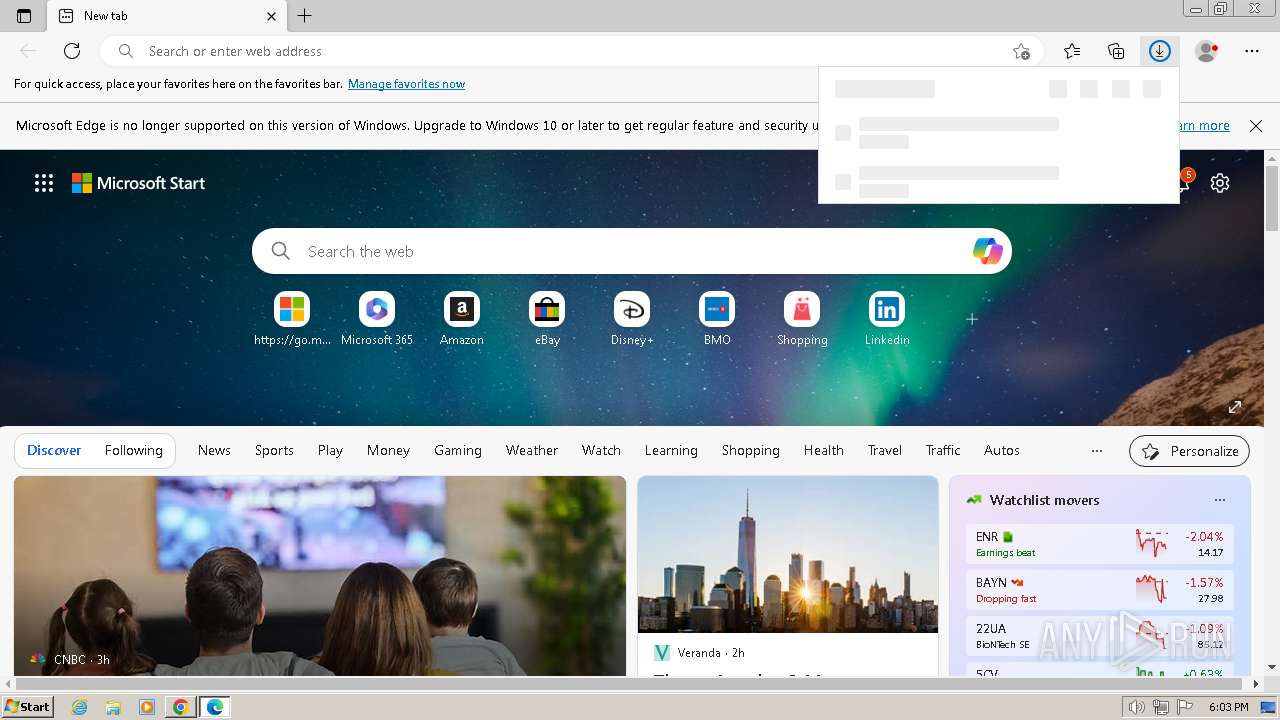
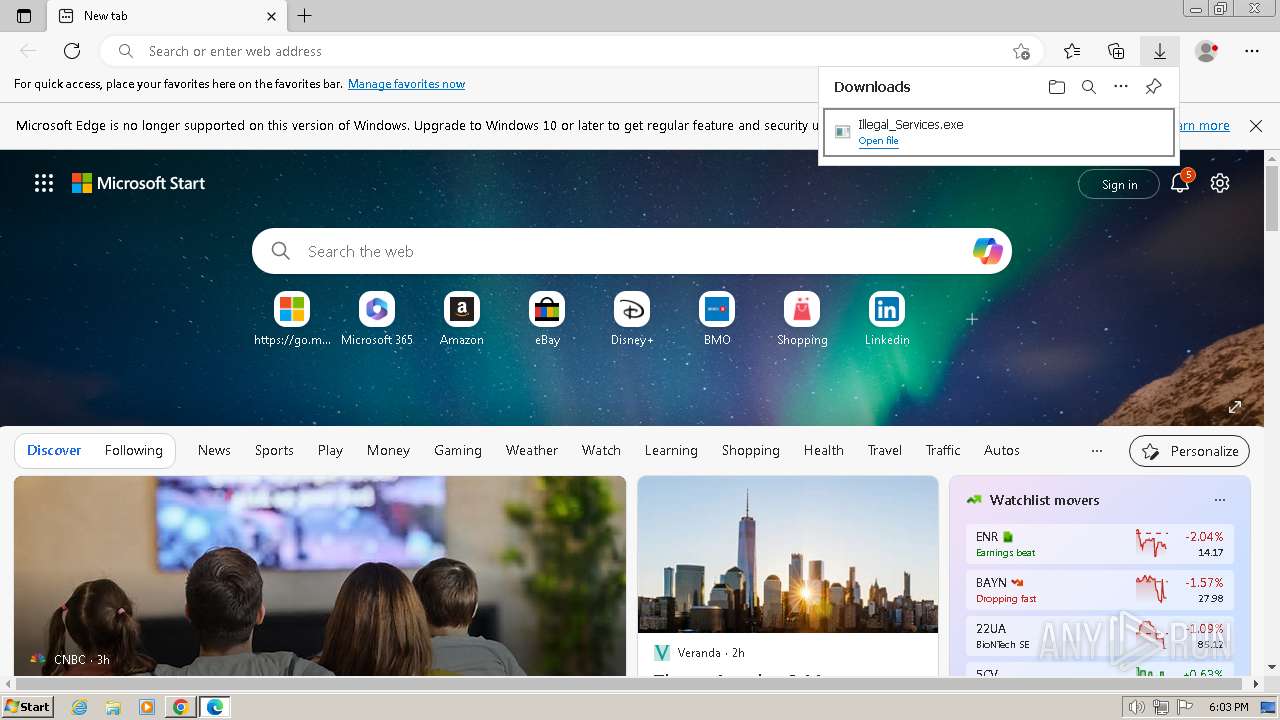
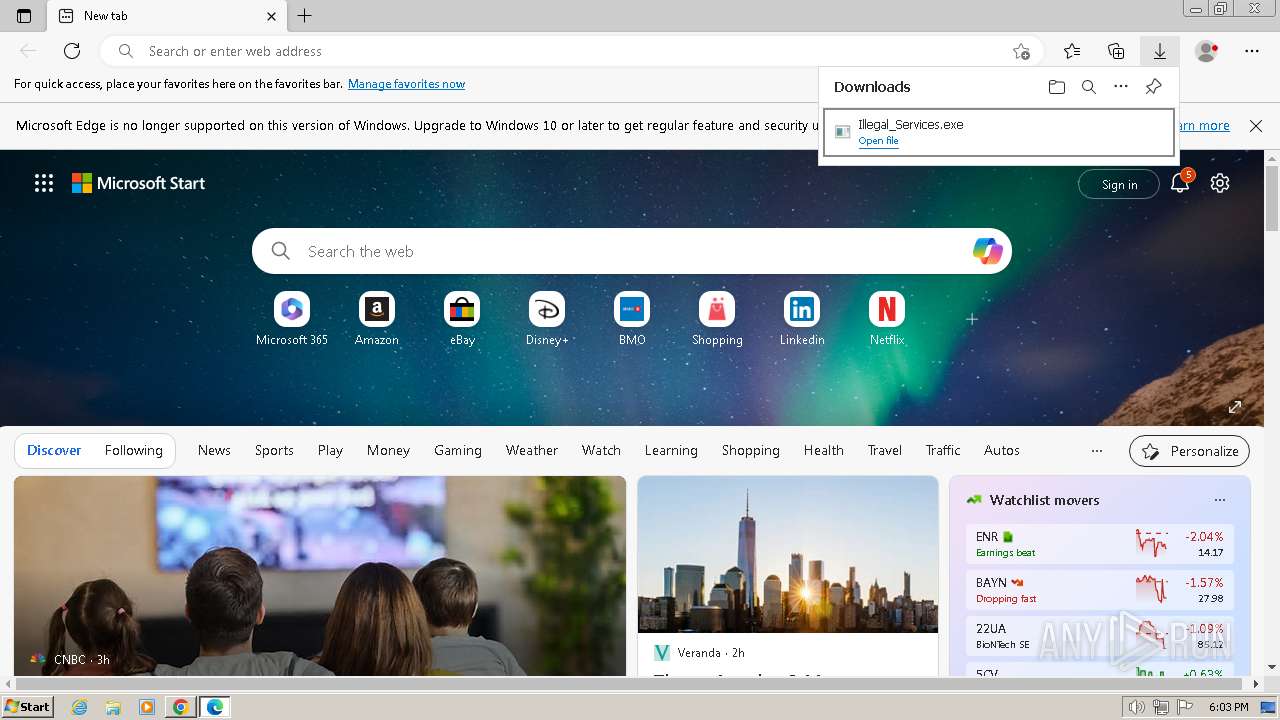
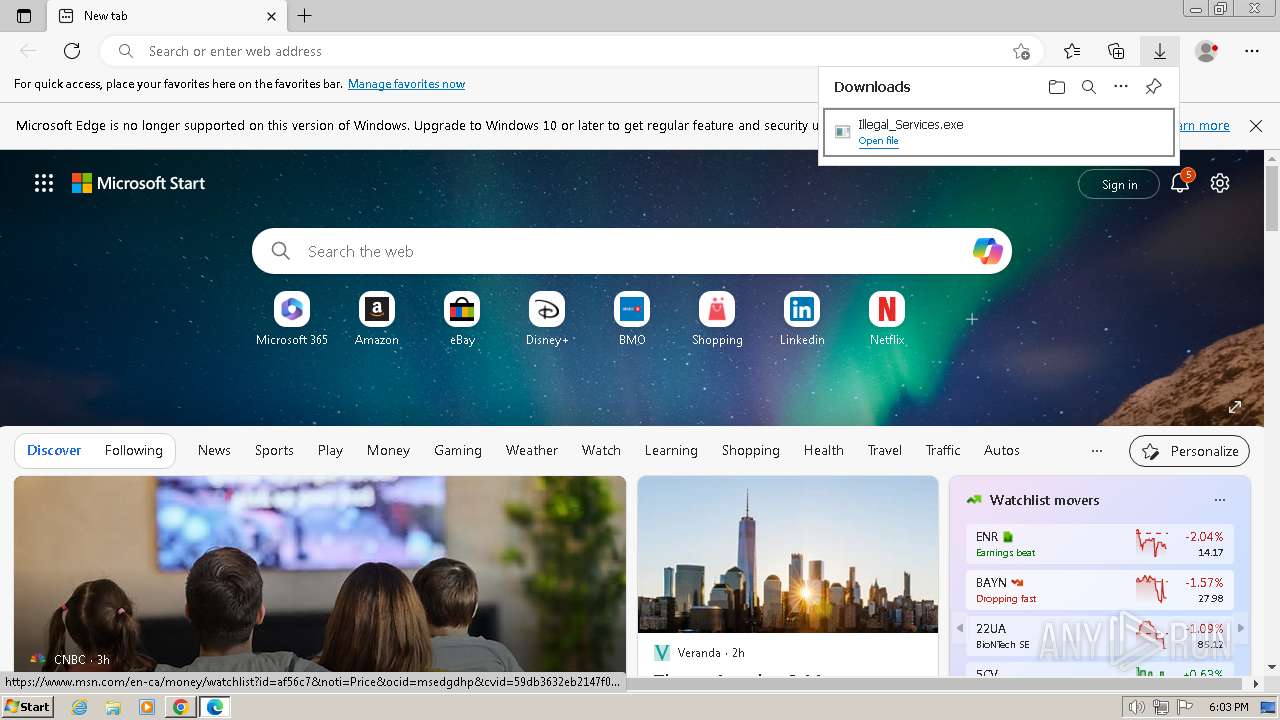
| URL: | https://github.com/Illegal-Services/Illegal_Services/raw/main/Illegal_Services.exe |
| Full analysis: | https://app.any.run/tasks/a0e2eb65-c3d3-47ff-b530-3d741a26d660 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 18:02:49 |
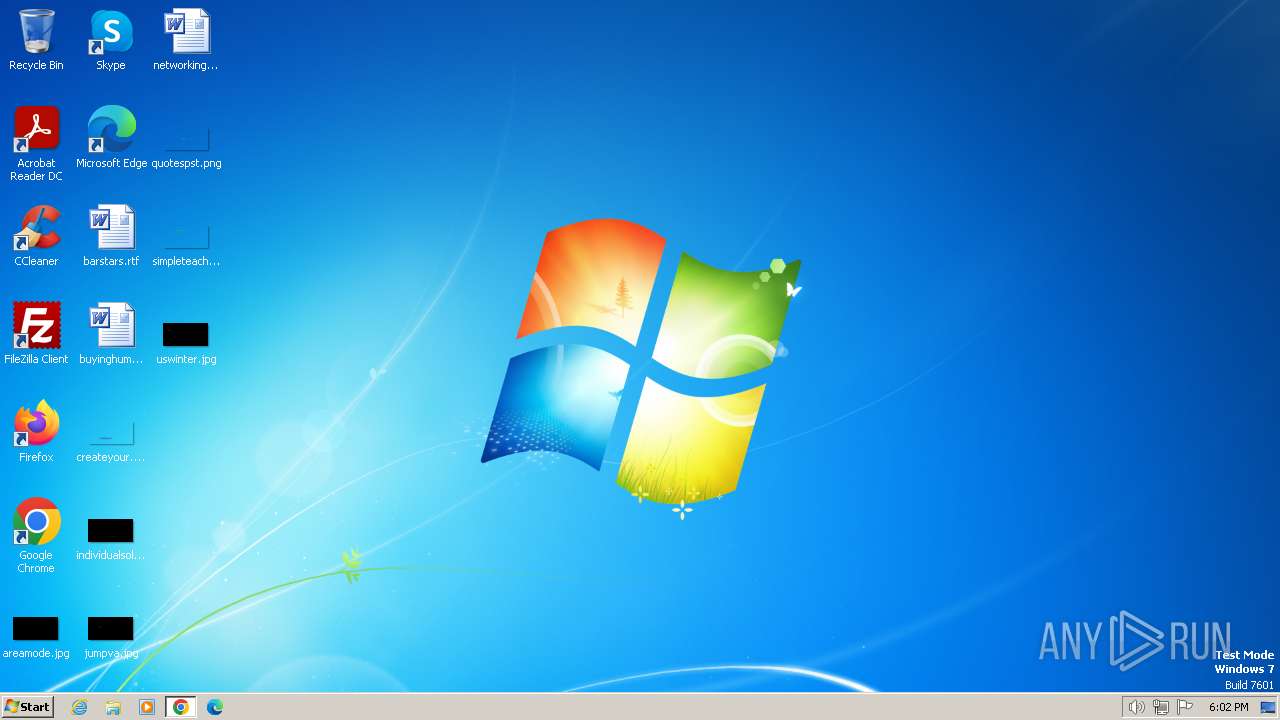
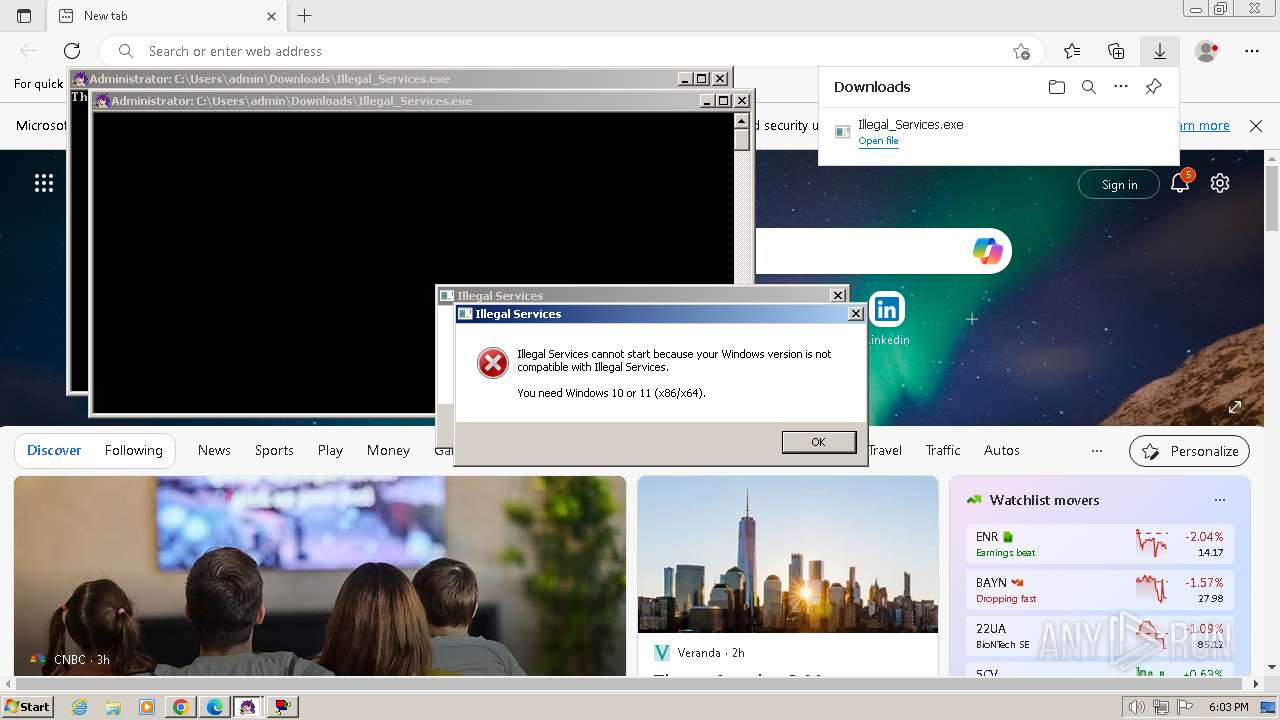
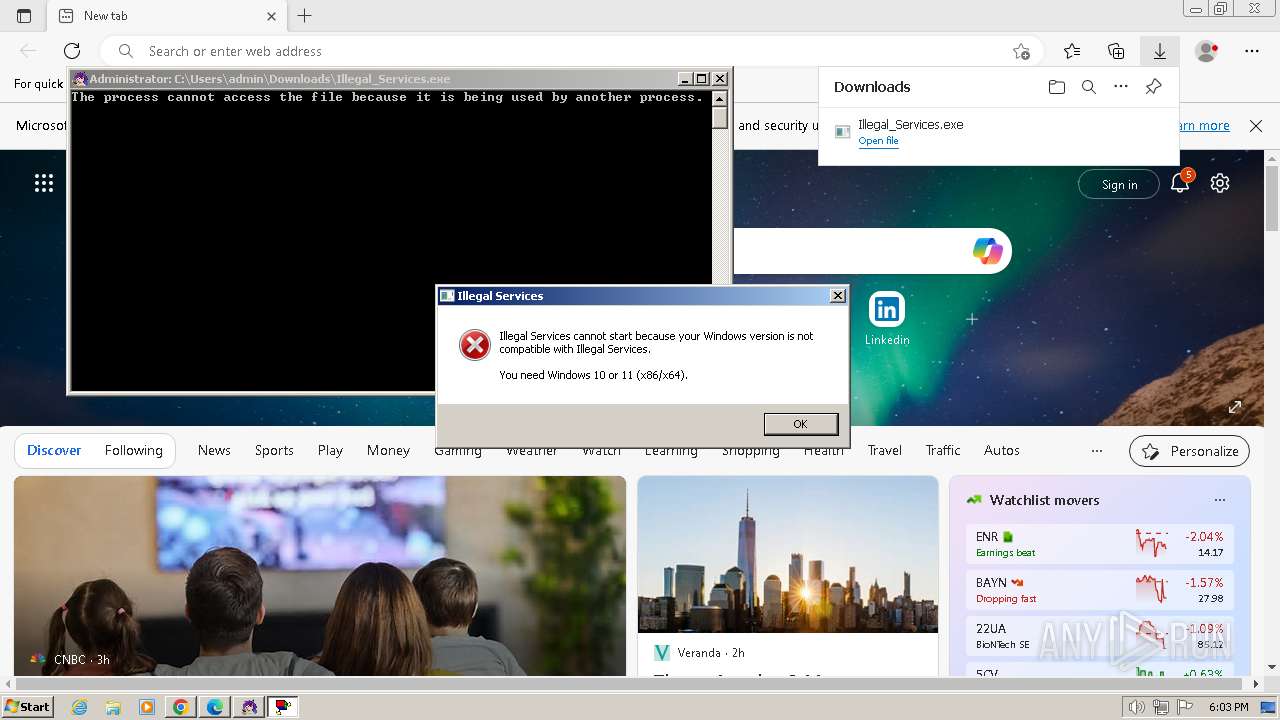
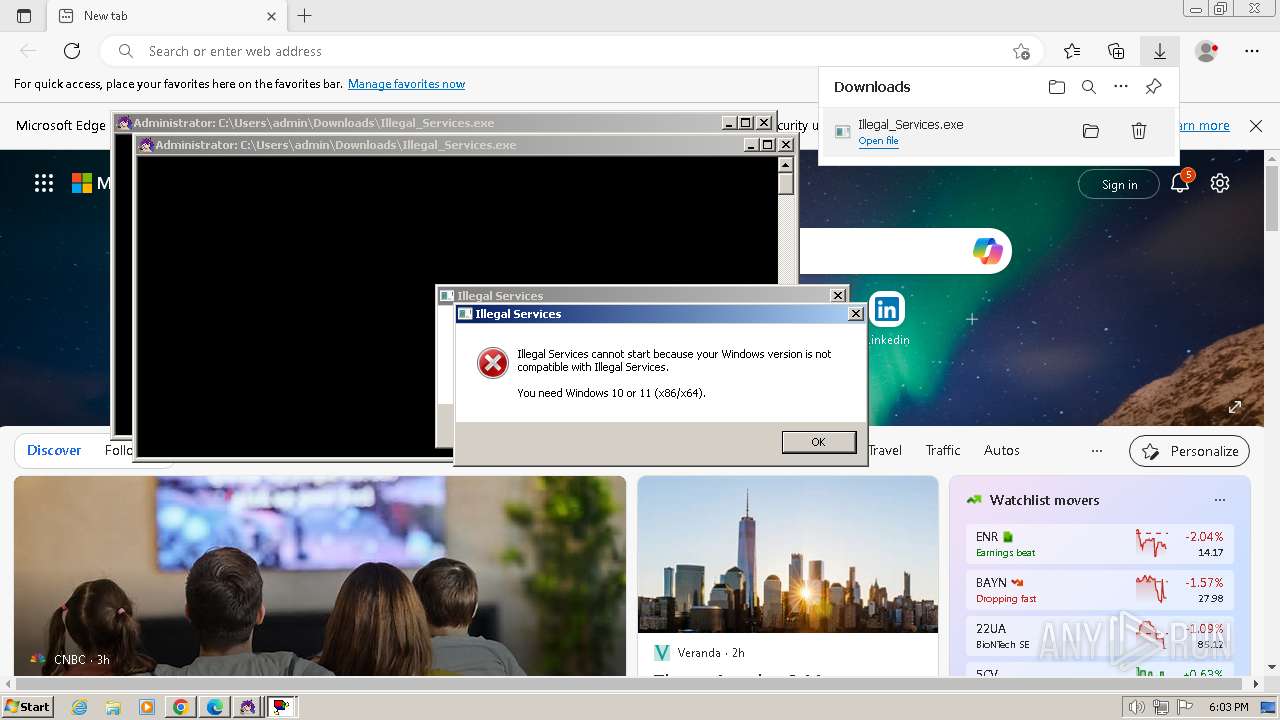
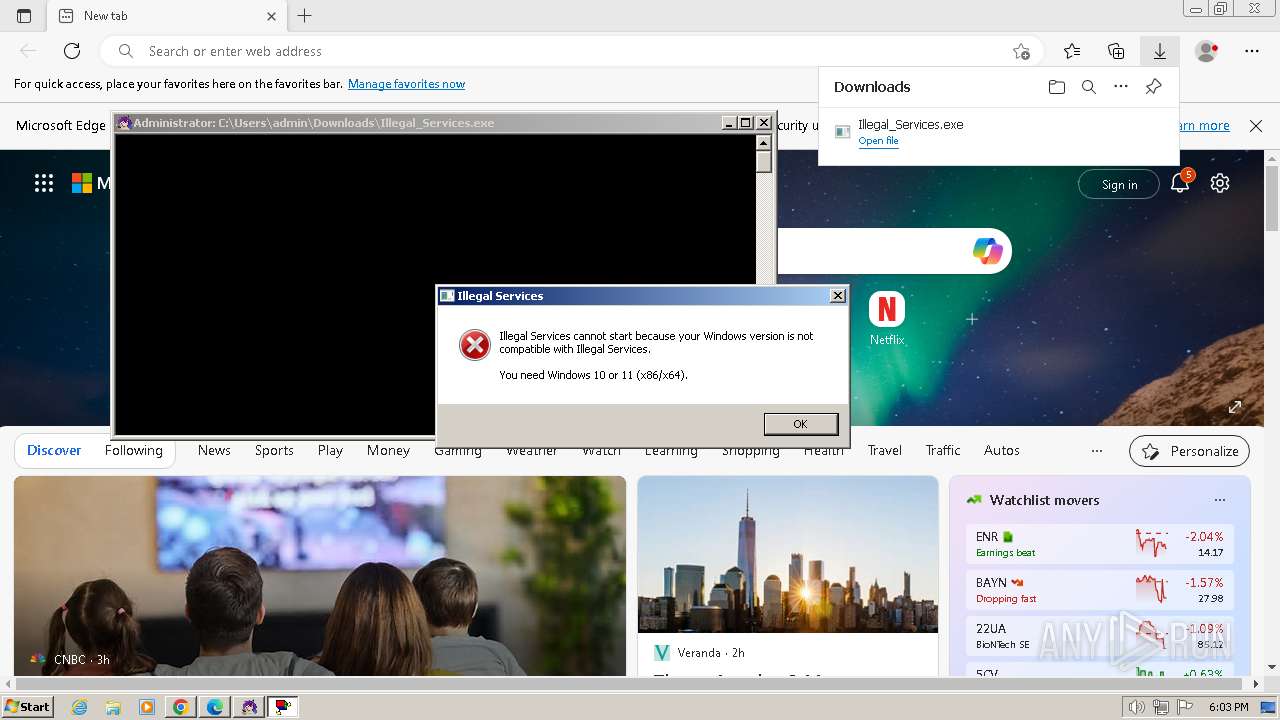
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C41B57933CD32BD1CDE04DB50FD9A3B1 |
| SHA1: | 101797BAB810A0EBF9BC7DC2D9A606A2C0BDC2E0 |
| SHA256: | CBE9DA45A95E8435682B486A586D0DE6AEC26FBA3DBCAD13CB37FCE113A800CB |
| SSDEEP: | 3:N8tEdEngI2AQeg6cbu6Zn:2uWJQLb |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process creates files with name similar to system file names
- msedge.exe (PID: 324)
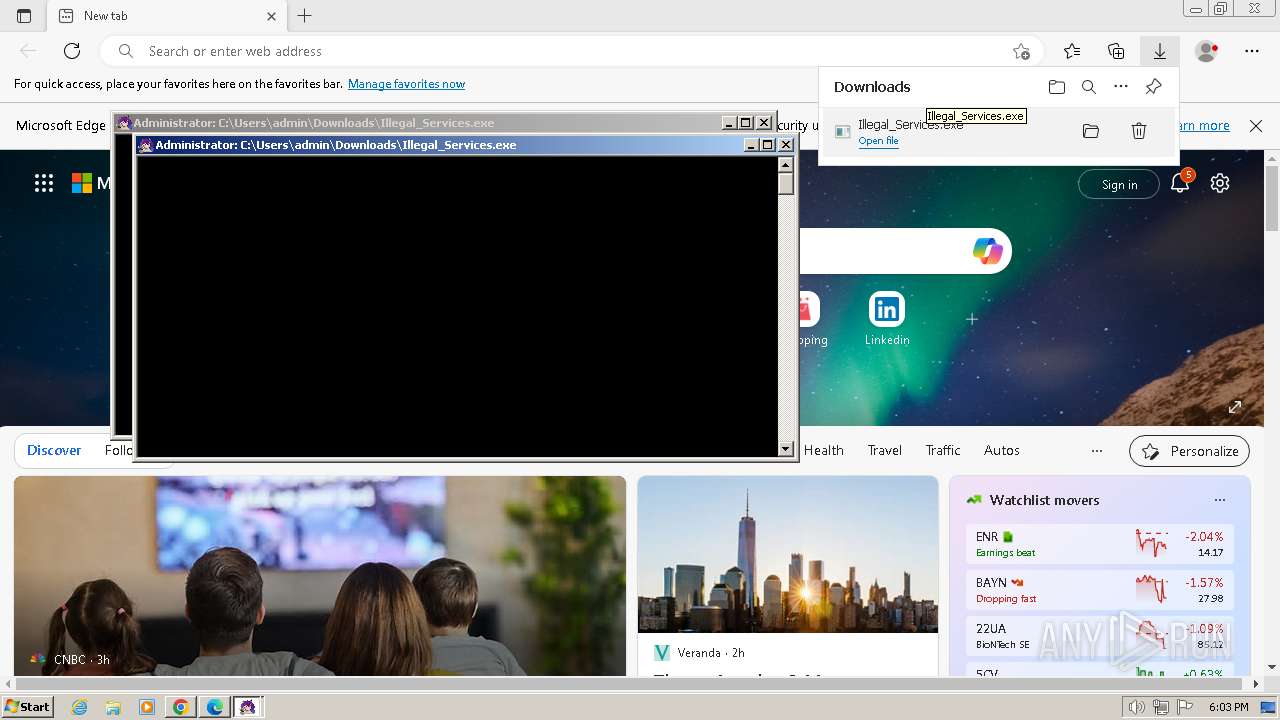
Starts CMD.EXE for commands execution
- Illegal_Services.exe (PID: 1792)
- Illegal_Services.exe (PID: 1844)
- cmd.exe (PID: 2788)
- cmd.exe (PID: 1336)
- forfiles.exe (PID: 2524)
- forfiles.exe (PID: 1072)
- Illegal_Services.exe (PID: 3472)
- cmd.exe (PID: 2308)
- forfiles.exe (PID: 2524)
- Illegal_Services.exe (PID: 3056)
- forfiles.exe (PID: 3128)
- cmd.exe (PID: 2512)
Executing commands from a ".bat" file
- Illegal_Services.exe (PID: 1792)
- Illegal_Services.exe (PID: 1844)
- Illegal_Services.exe (PID: 3472)
- Illegal_Services.exe (PID: 3056)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2788)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 2512)
Starts application with an unusual extension
- cmd.exe (PID: 3456)
- cmd.exe (PID: 2788)
- cmd.exe (PID: 3172)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 240)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2788)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 2512)
Application launched itself
- cmd.exe (PID: 1336)
- cmd.exe (PID: 2788)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 2512)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1336)
- cmd.exe (PID: 2788)
Reads the Internet Settings
- WMIC.exe (PID: 2612)
- WMIC.exe (PID: 2836)
- WMIC.exe (PID: 2568)
- WMIC.exe (PID: 3172)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2788)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 2512)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 1192)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 2088)
The process executes VB scripts
- cmd.exe (PID: 1336)
- cmd.exe (PID: 2788)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 2512)
INFO
Application launched itself
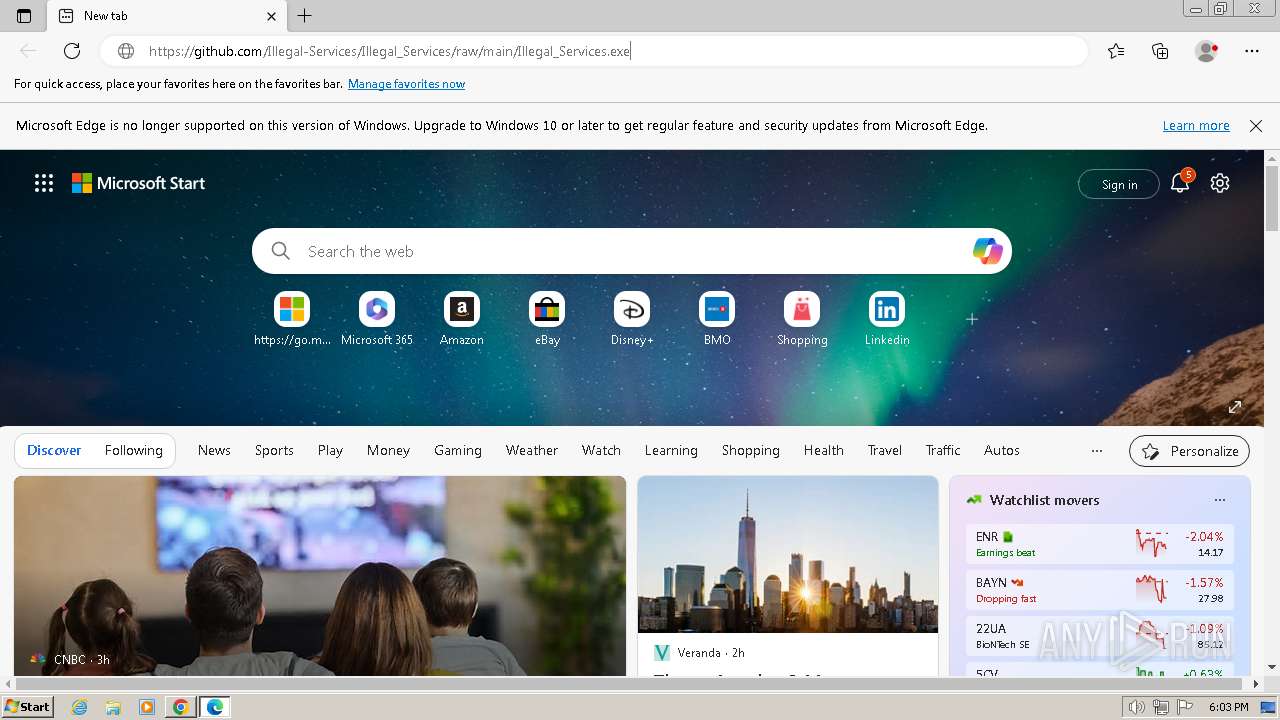
- msedge.exe (PID: 2968)
- chrome.exe (PID: 2472)
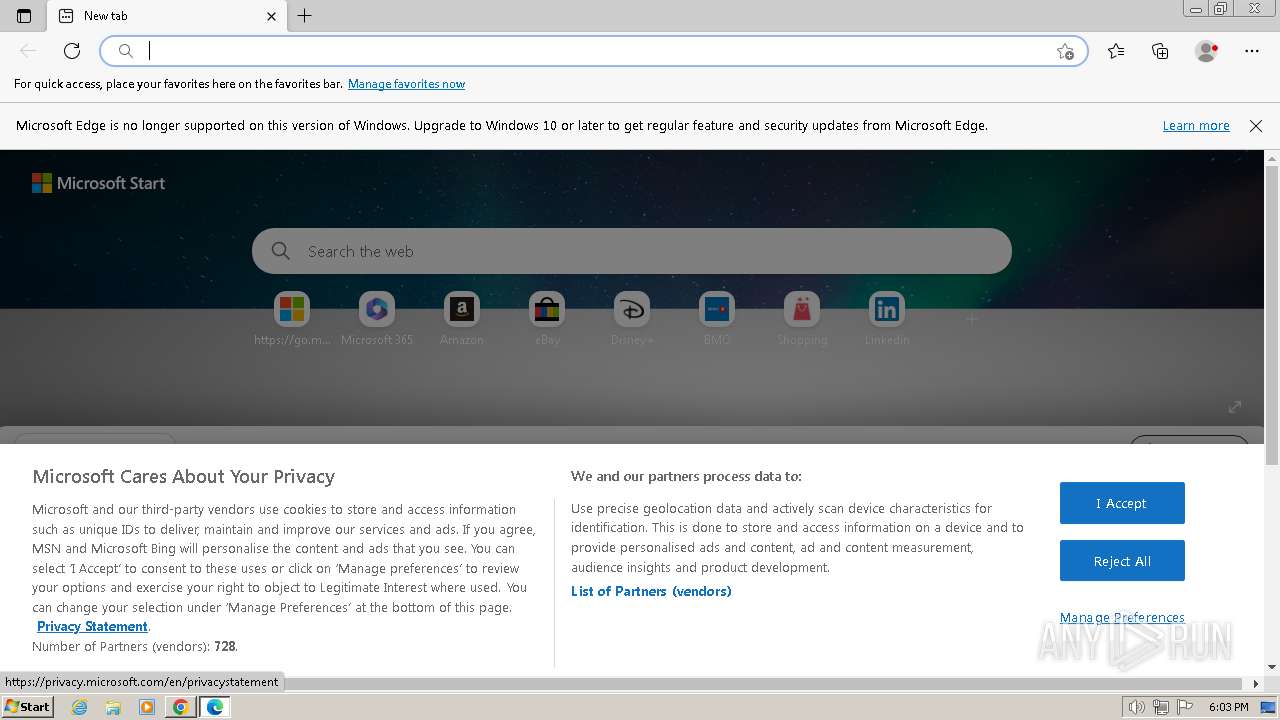
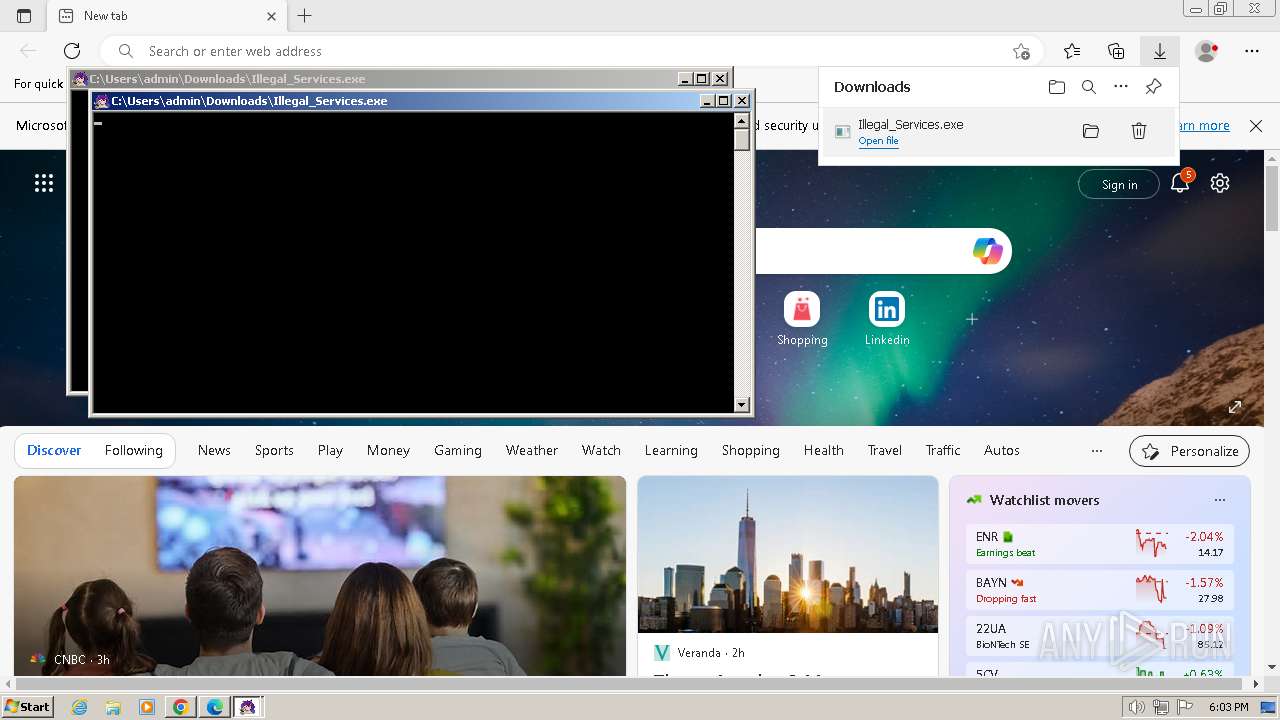
Manual execution by a user
- msedge.exe (PID: 2968)
Executable content was dropped or overwritten
- msedge.exe (PID: 2968)
- msedge.exe (PID: 1728)
- chrome.exe (PID: 2472)
Drops the executable file immediately after the start
- msedge.exe (PID: 2968)
- chrome.exe (PID: 2472)
- msedge.exe (PID: 1728)
The process uses the downloaded file
- msedge.exe (PID: 324)
- msedge.exe (PID: 2968)
- cmd.exe (PID: 1192)
- cmd.exe (PID: 3904)
- cmd.exe (PID: 4032)
- cmd.exe (PID: 1644)
Checks supported languages
- Illegal_Services.exe (PID: 1792)
- Illegal_Services.exe (PID: 1844)
- chcp.com (PID: 1172)
- chcp.com (PID: 3108)
- chcp.com (PID: 3524)
- chcp.com (PID: 2032)
- chcp.com (PID: 572)
- chcp.com (PID: 2088)
- chcp.com (PID: 584)
- chcp.com (PID: 3456)
- chcp.com (PID: 3380)
- chcp.com (PID: 1196)
- Illegal_Services.exe (PID: 3056)
- Illegal_Services.exe (PID: 3472)
- chcp.com (PID: 3764)
- chcp.com (PID: 2260)
- chcp.com (PID: 2984)
- chcp.com (PID: 3152)
- chcp.com (PID: 1560)
- chcp.com (PID: 1652)
Create files in a temporary directory
- Illegal_Services.exe (PID: 1792)
- Illegal_Services.exe (PID: 1844)
- Illegal_Services.exe (PID: 3472)
- Illegal_Services.exe (PID: 3056)
Dropped object may contain TOR URL's
- Illegal_Services.exe (PID: 1792)
- Illegal_Services.exe (PID: 1844)
- Illegal_Services.exe (PID: 3472)
- Illegal_Services.exe (PID: 3056)
Checks Windows language
- reg.exe (PID: 3508)
- reg.exe (PID: 240)
Checks operating system version
- cmd.exe (PID: 2788)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 2308)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1168)
- cscript.exe (PID: 2356)
- cscript.exe (PID: 2524)
- cscript.exe (PID: 3876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
198
Monitored processes
149
Malicious processes
9
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | reg query "HKLM\SYSTEM\CurrentControlSet\Control\Nls\Language" /v "InstallLanguage" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | C:\Windows\system32\cmd.exe /c chcp | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 324 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4160 --field-trial-handle=1348,i,16219769738958140635,3265976728848185641,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 532 | attrib +s +h +i "C:\Users\admin\AppData\Local\Temp\0OQLEFR3.bat" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | attrib +s +h +i "C:\Users\admin\AppData\Local\Temp\4TFJ49Y2.bat" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "C:\Users\admin\AppData\Local\Temp\03B9MPX0.bat" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1020 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "C:\Users\admin\AppData\Local\Temp\4TFJ49Y2.bat" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | forfiles /m "Illegal_Services.exe" /c "cmd /c echo 0x1B" | C:\Windows\System32\forfiles.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ForFiles - Executes a command on selected files Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
18 694
Read events
18 590
Write events
92
Delete events
12
Modification events
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2472) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
11
Suspicious files
224
Text files
137
Unknown types
120
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f491.TMP | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF17f8f6.TMP | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF17f627.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
| 2472 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
44
DNS requests
72
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3944 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | unknown |
2472 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3944 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
3944 | chrome.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
2472 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3944 | chrome.exe | 216.58.206.46:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
1728 | msedge.exe | 204.79.197.203:443 | ntp.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
github.com |
| shared |
raw.githubusercontent.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
assets.msn.com |
| whitelisted |
img-s-msn-com.akamaized.net |
| whitelisted |
sb.scorecardresearch.com |
| shared |