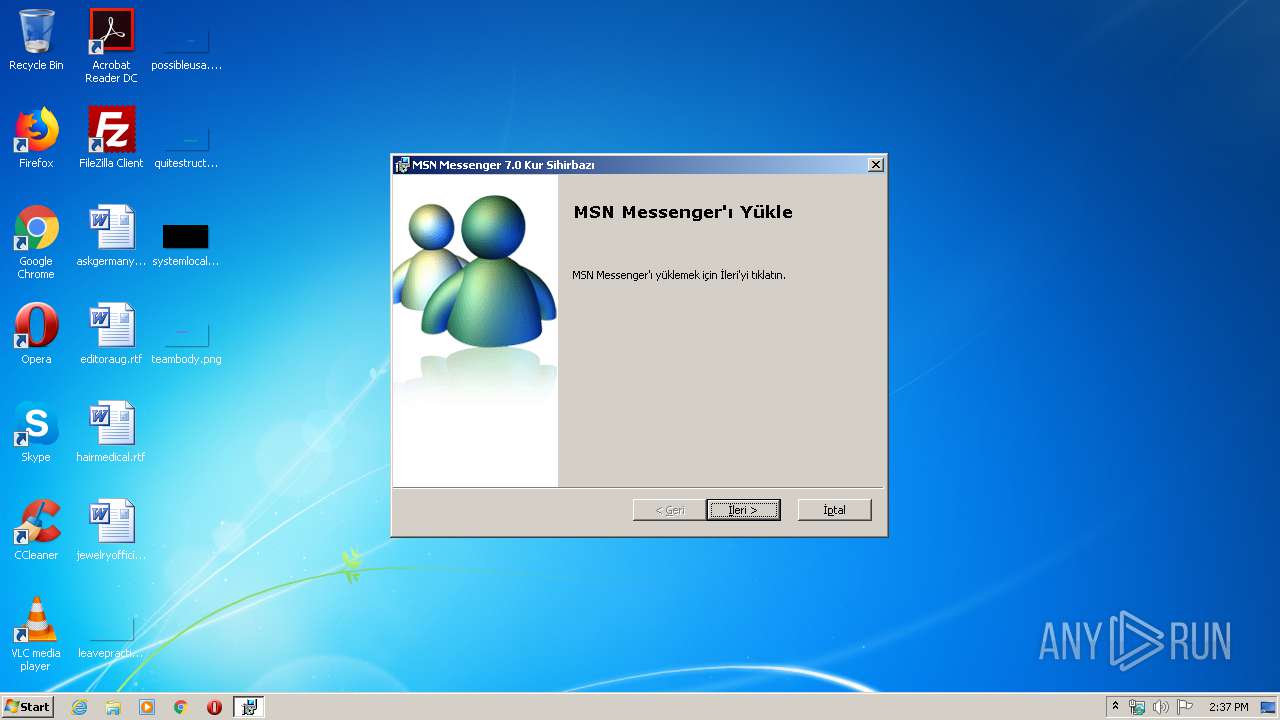
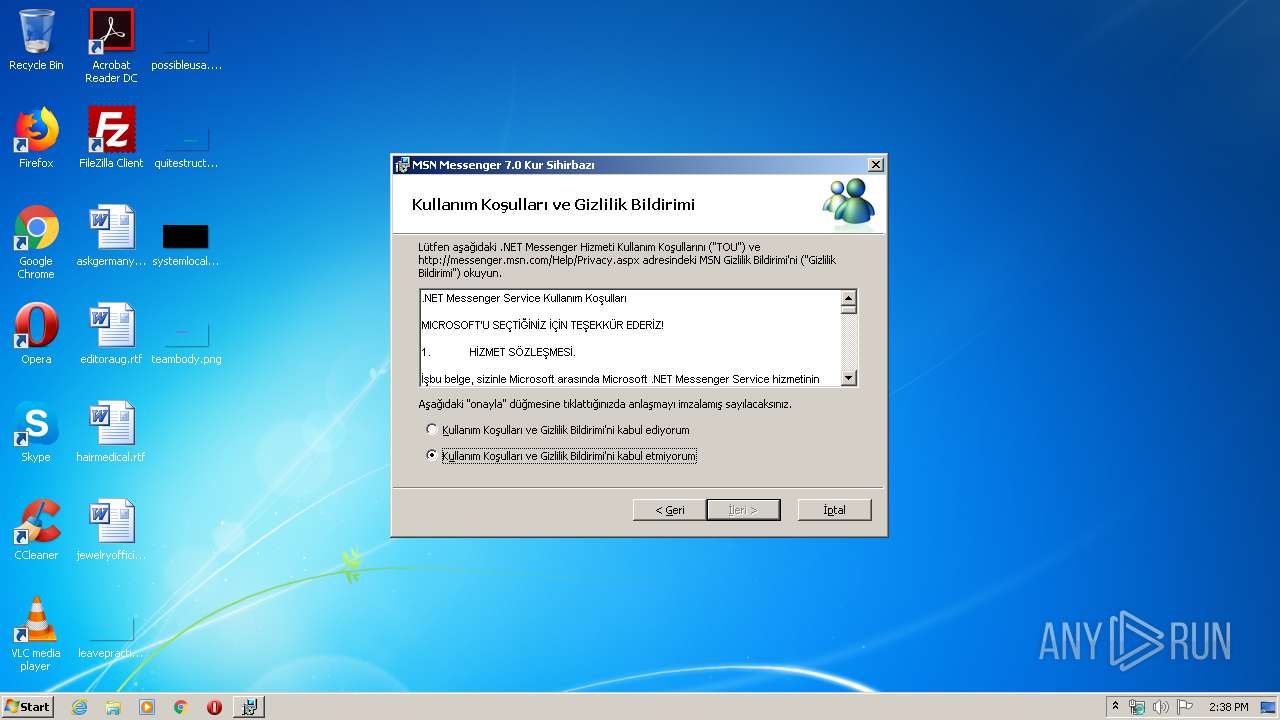
| File name: | msn-7.0.0820-tr.exe |
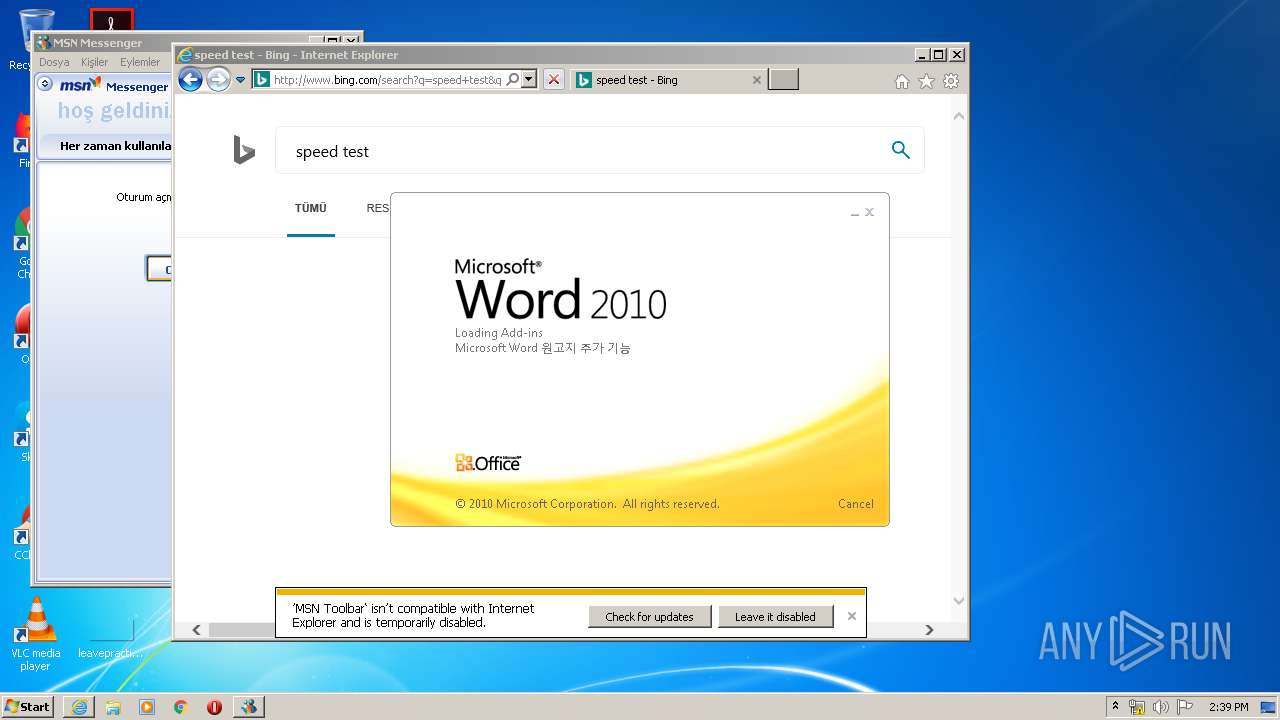
| Full analysis: | https://app.any.run/tasks/79ae6a41-f9ef-49c0-aeed-7517c77fd2e6 |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2020, 13:37:26 |
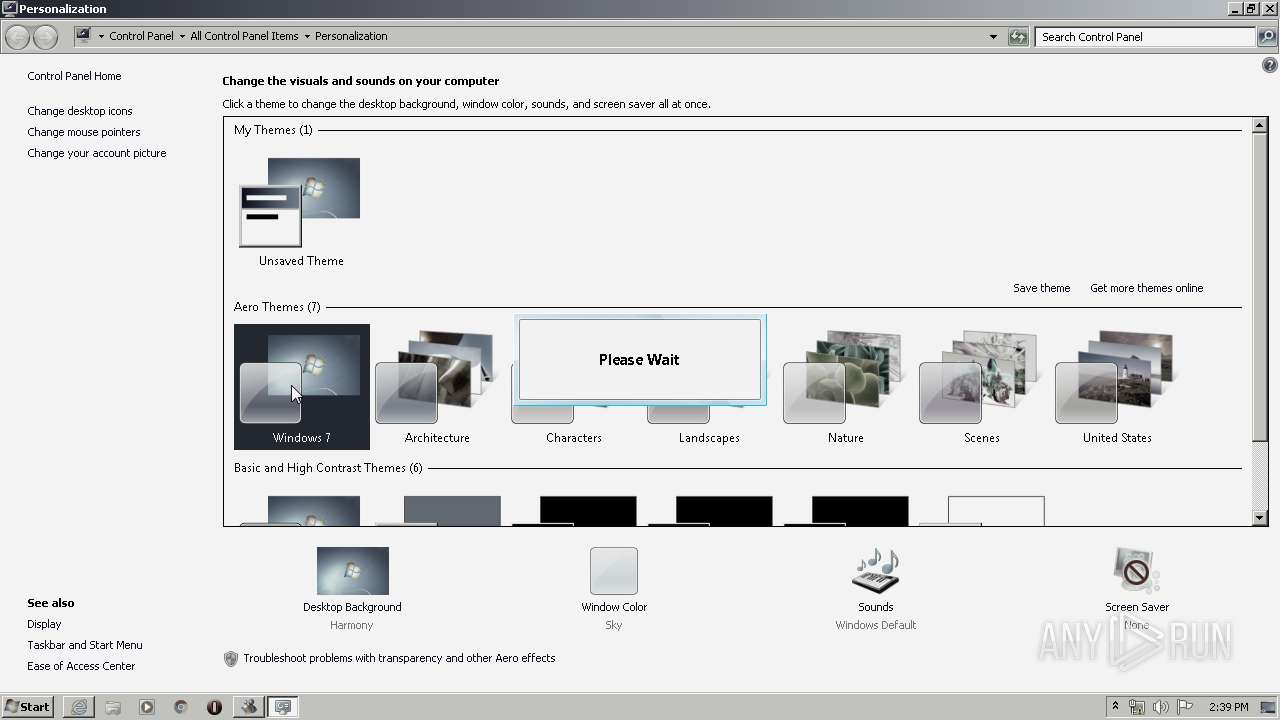
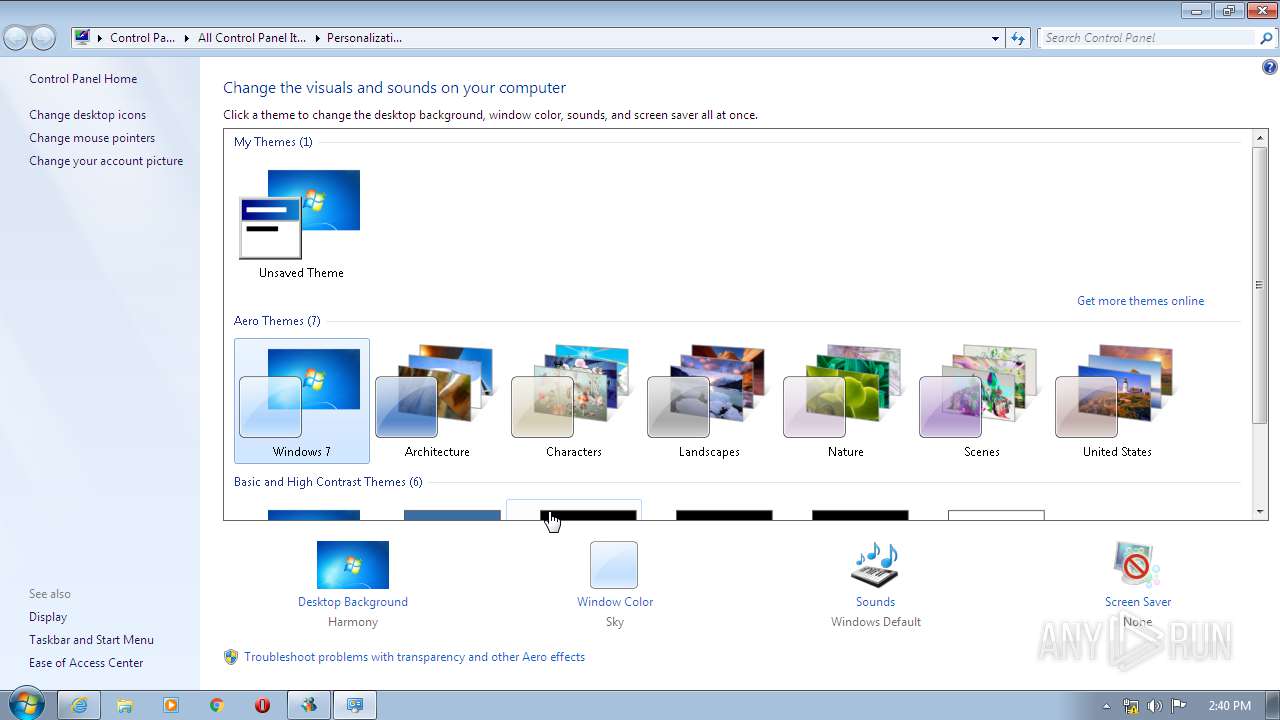
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | FC24BADE7FDA71096B790455158E565C |
| SHA1: | 473F996D1AA24CD2859D75DB711AAB63FCAE62BE |
| SHA256: | CBE80471AAD9277968F9B1E1252371402A0D0EDF6657BFFFE13194AD6B2723F8 |
| SSDEEP: | 196608:sPikz4UmHxeTGtovDfz3InlMD/QTMvKzFpWRdEFgVa7hS1ueBC7Iy8:sPD4qdLc4/V4WYgOvLh8 |
MALICIOUS
Changes the autorun value in the registry
- msn-7.0.0820-tr.exe (PID: 2480)
- msnsearch.exe (PID: 3720)
- WinSat.exe (PID: 3340)
- WinSat.exe (PID: 2748)
- WinSat.exe (PID: 3072)
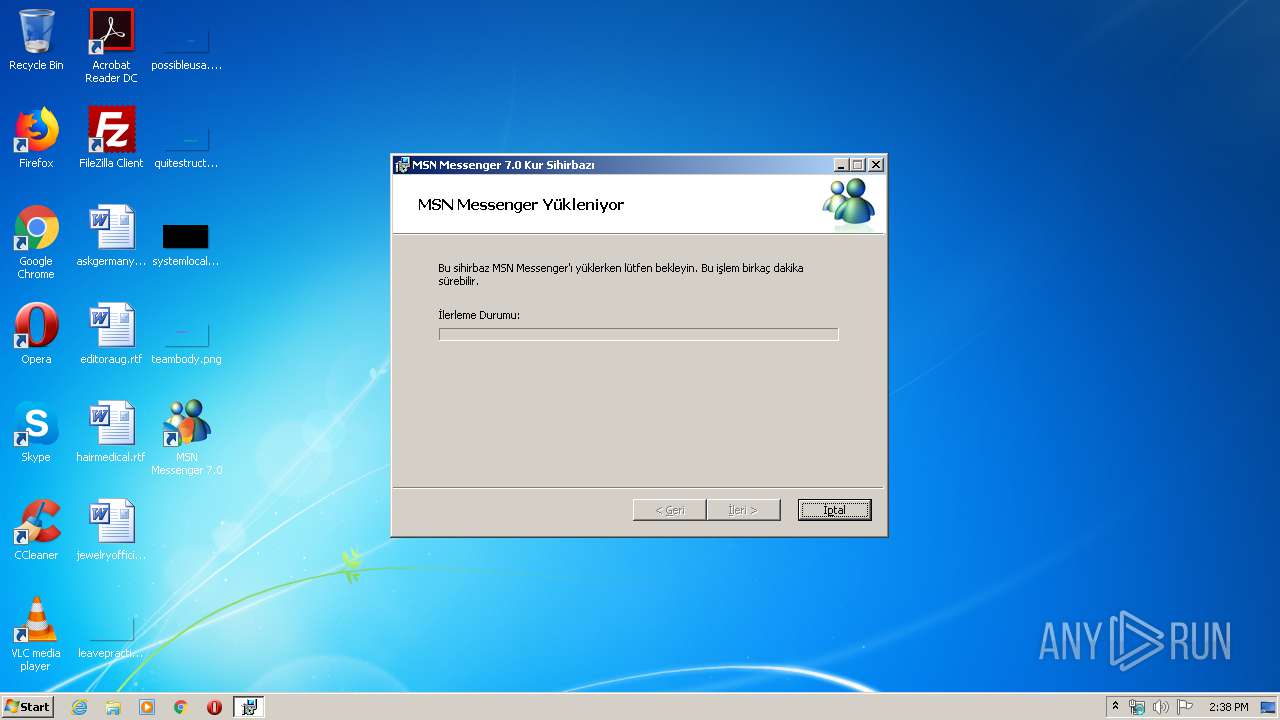
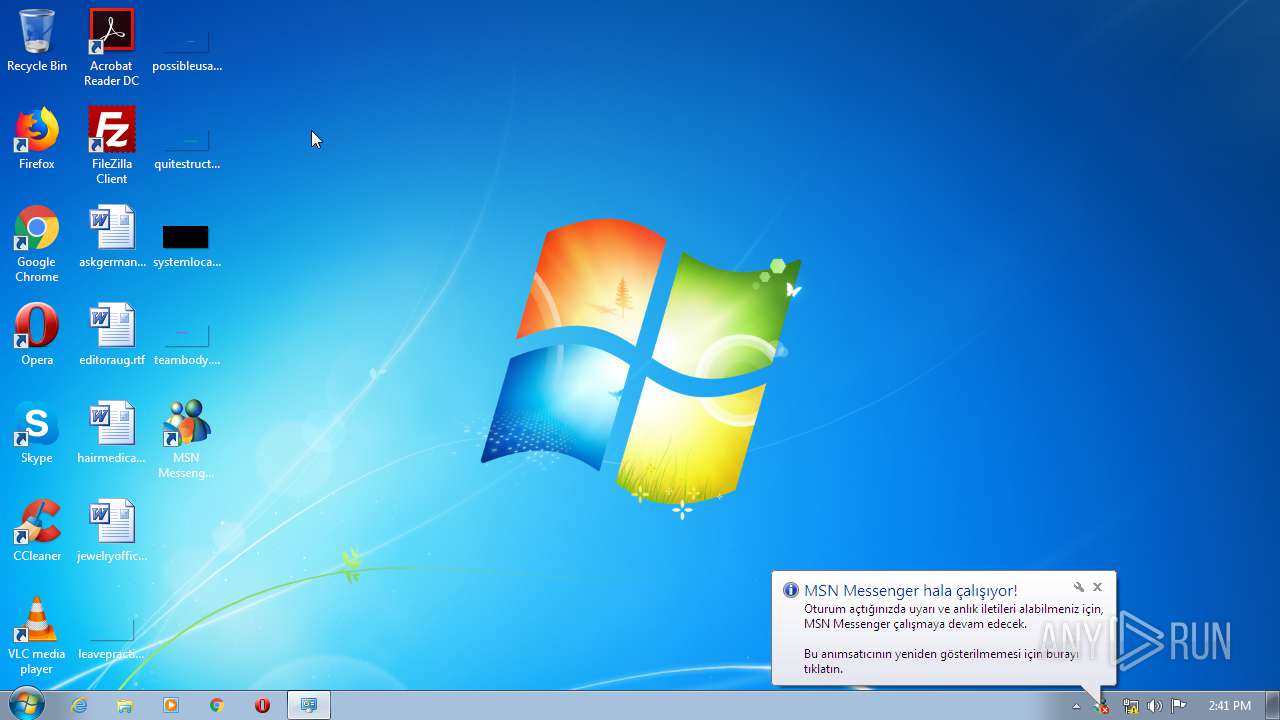
Application was dropped or rewritten from another process
- bootstrap.exe (PID: 348)
- msnsearch.exe (PID: 3720)
- mtbs.exe (PID: 3508)
- msnmsgr.exe (PID: 1784)
- mtbs.exe (PID: 3096)
Loads dropped or rewritten executable
- bootstrap.exe (PID: 348)
- msnmsgr.exe (PID: 1784)
- mtbs.exe (PID: 3508)
- iexplore.exe (PID: 3120)
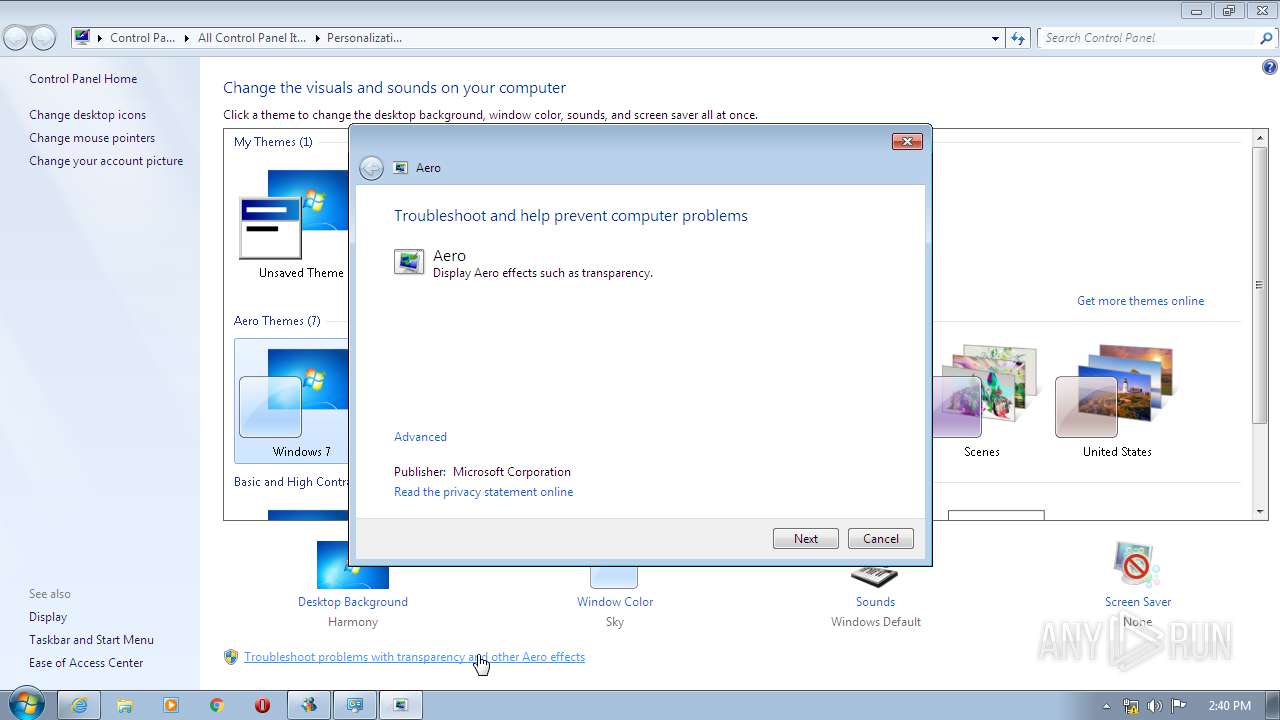
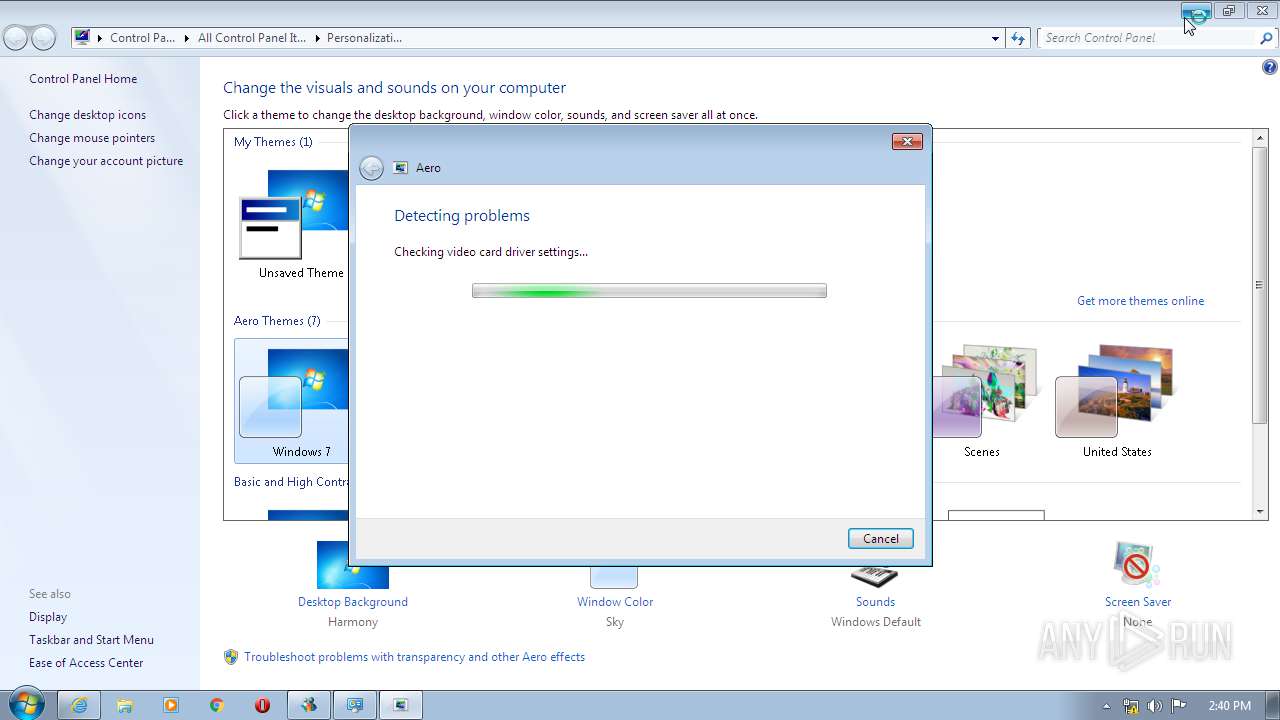
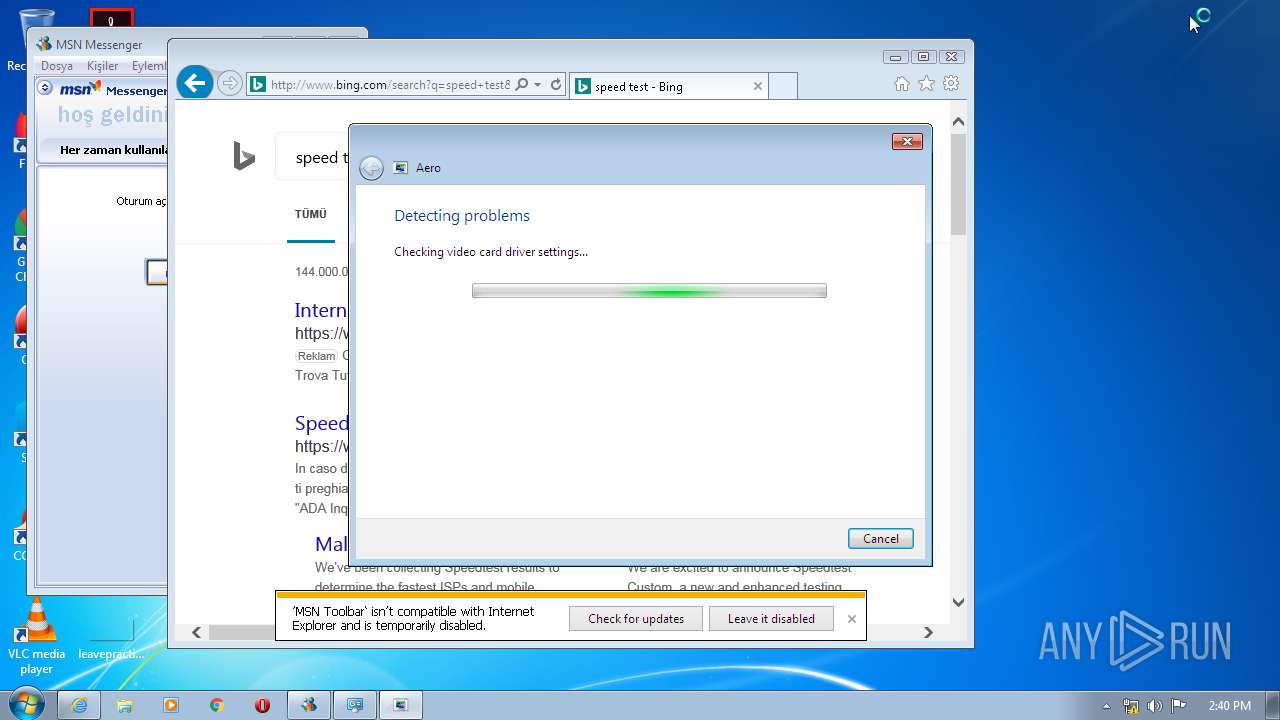
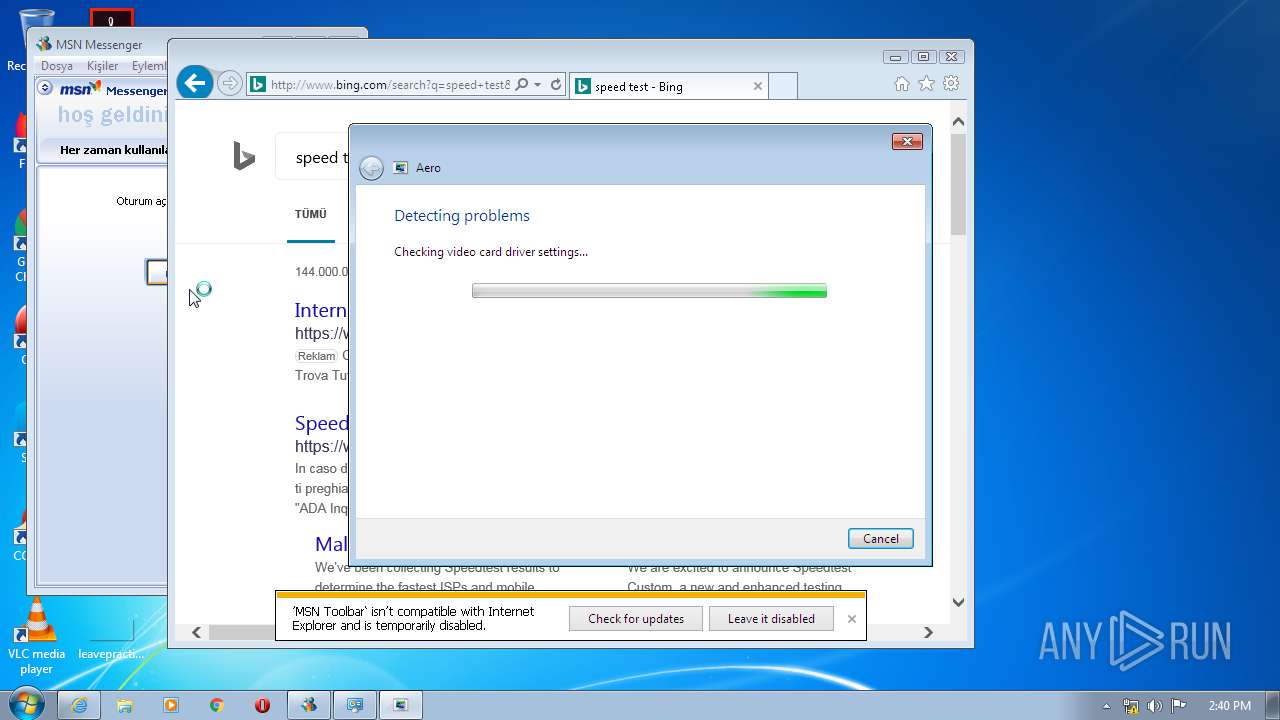
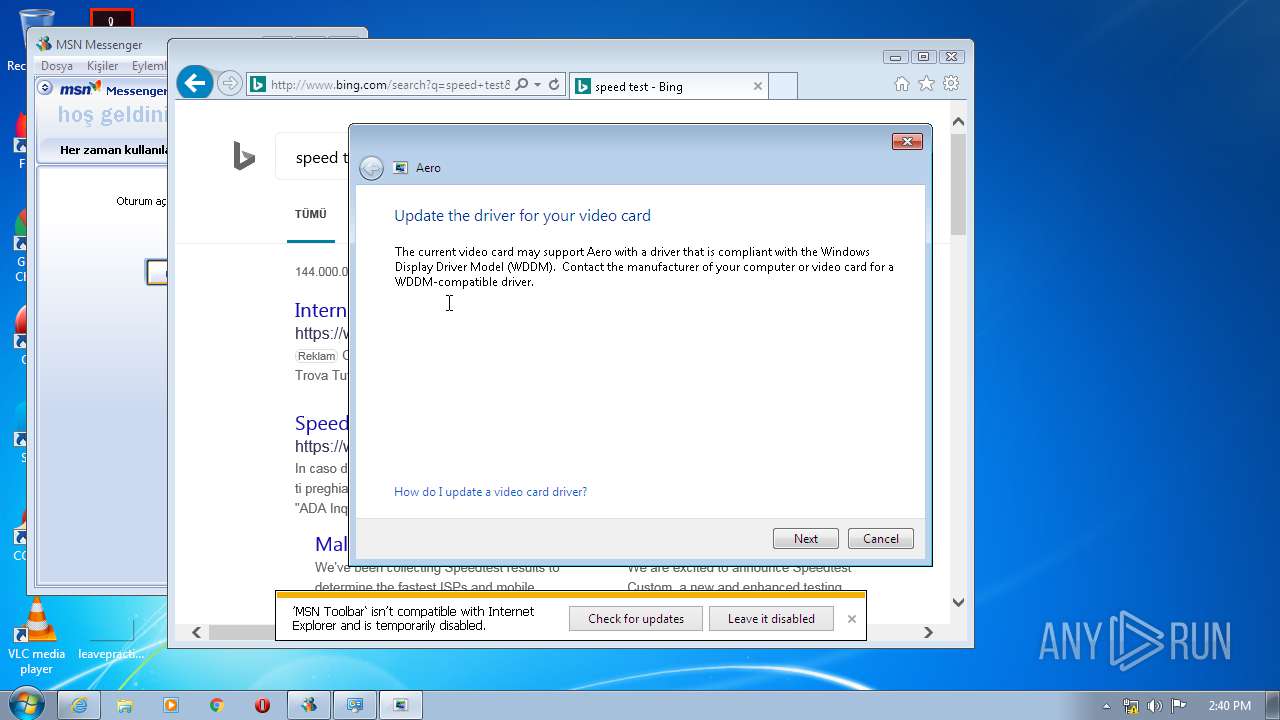
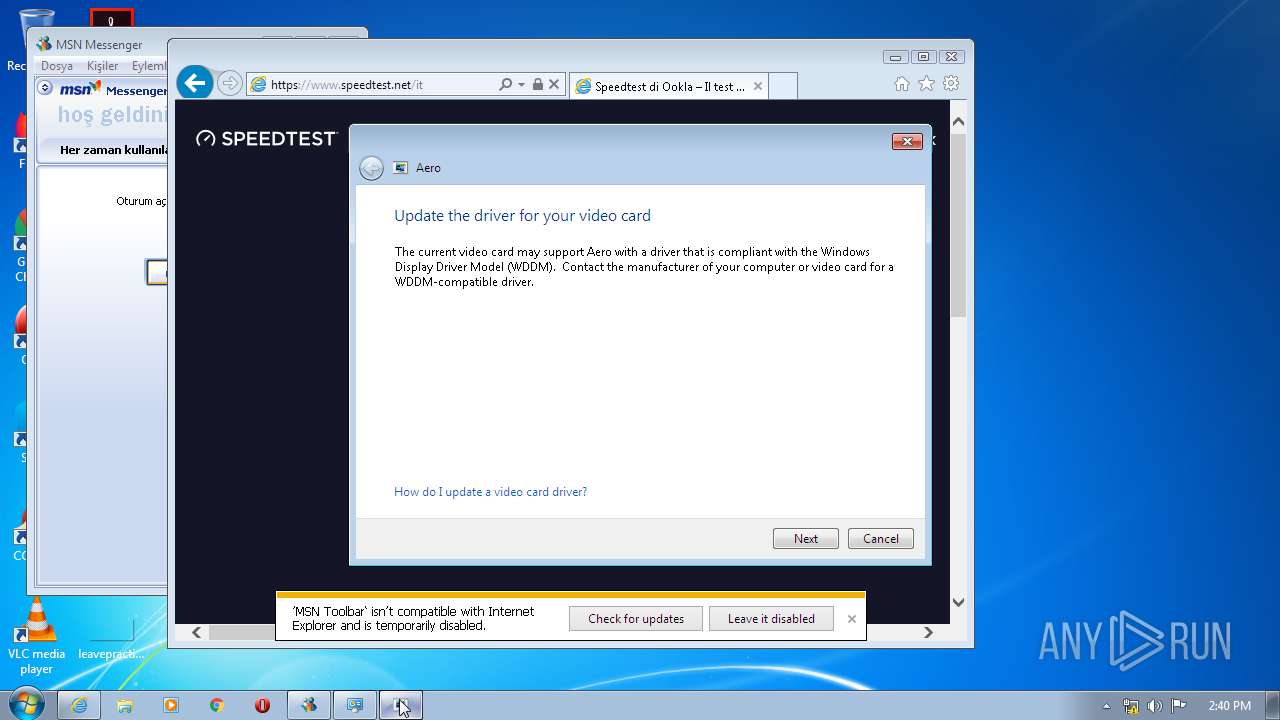
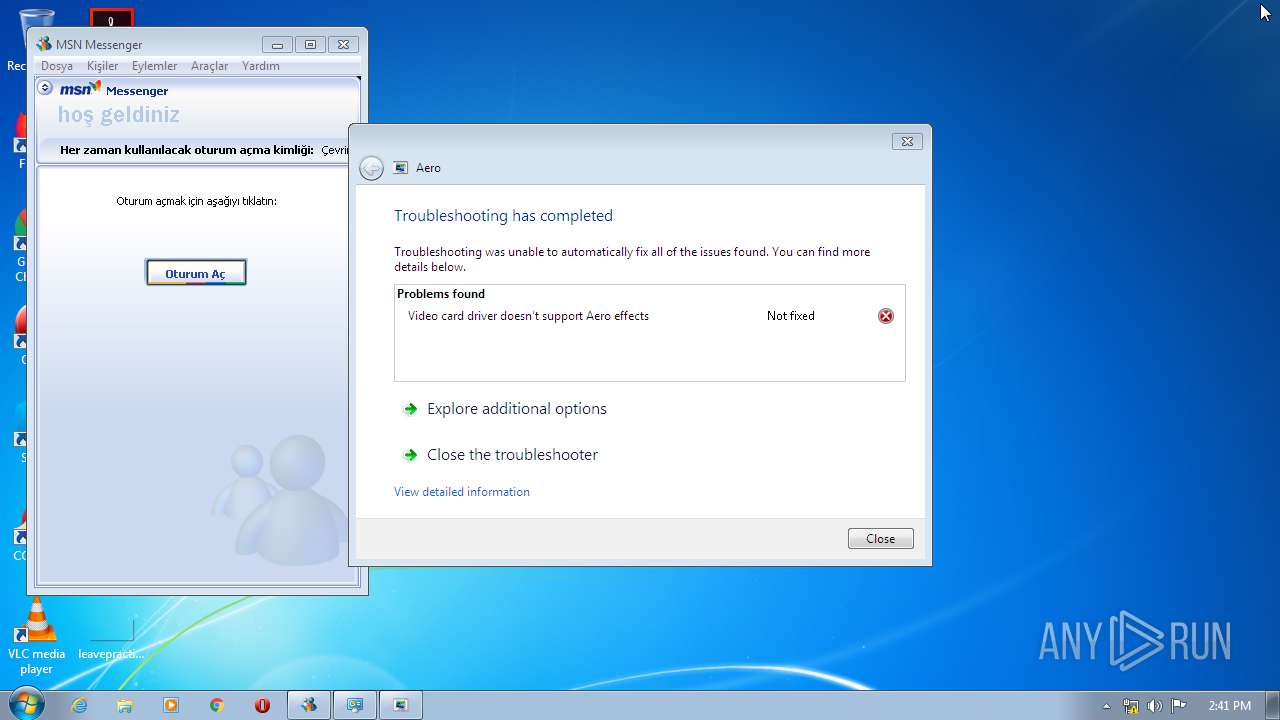
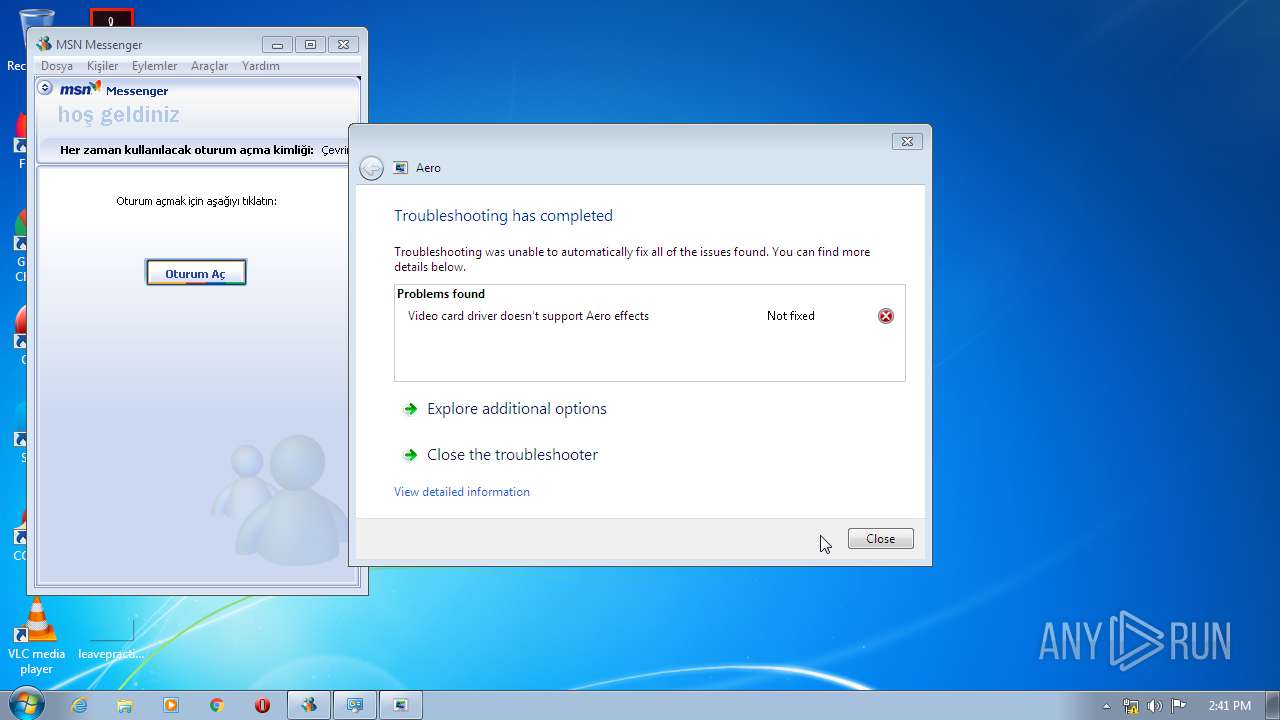
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2468)
- sdiagnhost.exe (PID: 2996)
SUSPICIOUS
Executable content was dropped or overwritten
- bootstrap.exe (PID: 348)
- msn-7.0.0820-tr.exe (PID: 2480)
- msiexec.exe (PID: 3360)
- mtbs.exe (PID: 3508)
- msnsearch.exe (PID: 3720)
- msdt.exe (PID: 3036)
Creates files in the user directory
- msiexec.exe (PID: 3360)
Creates COM task schedule object
- msiexec.exe (PID: 3360)
- mtbs.exe (PID: 3508)
Executed as Windows Service
- vssvc.exe (PID: 3848)
Changes the autorun value in the registry
- msiexec.exe (PID: 3360)
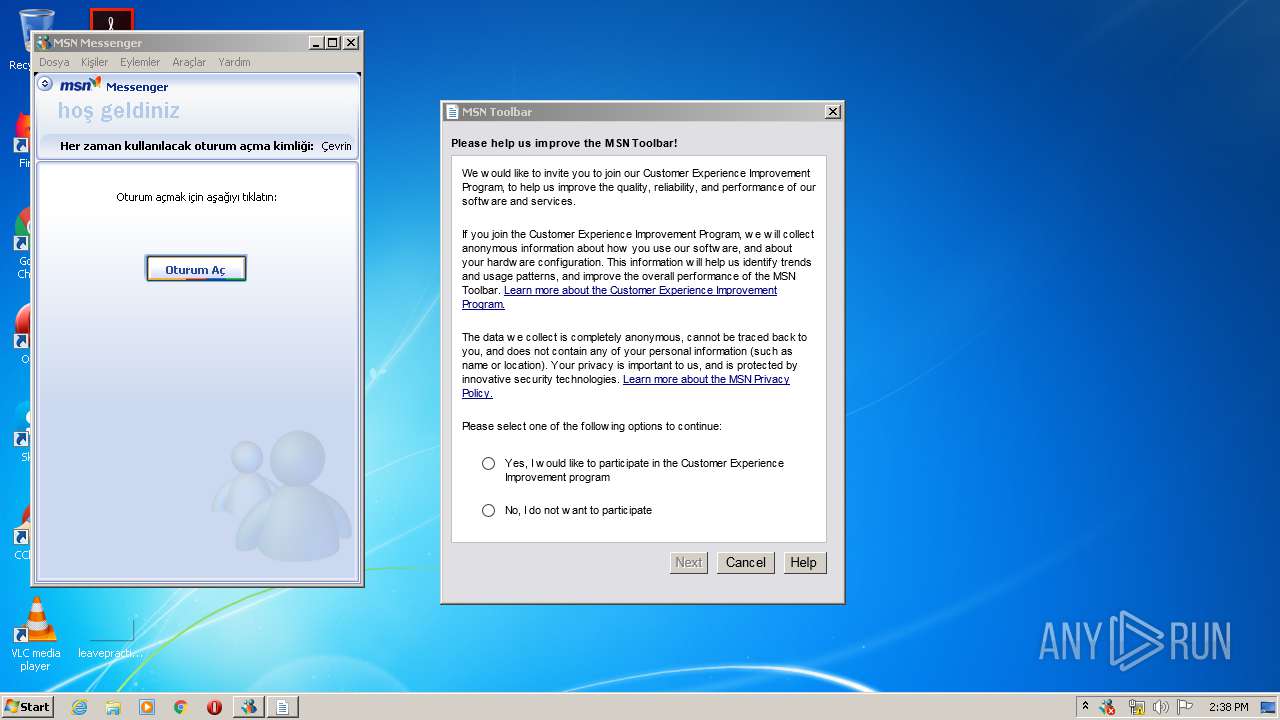
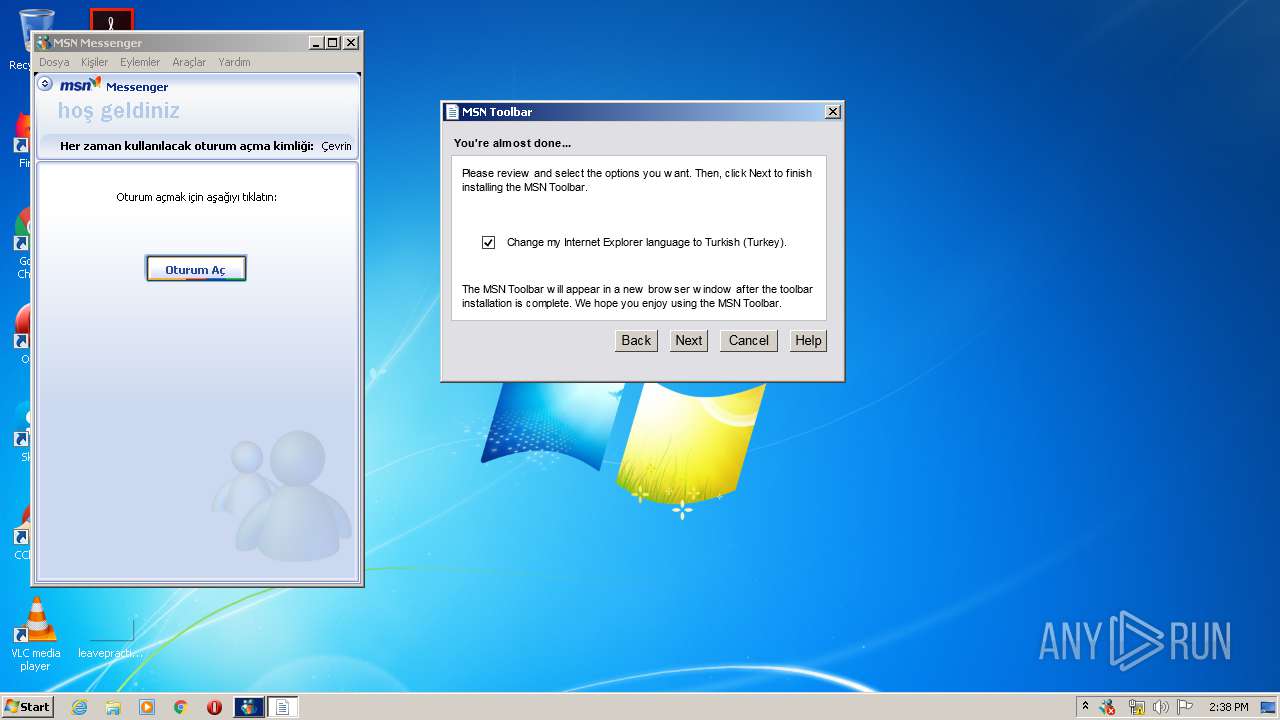
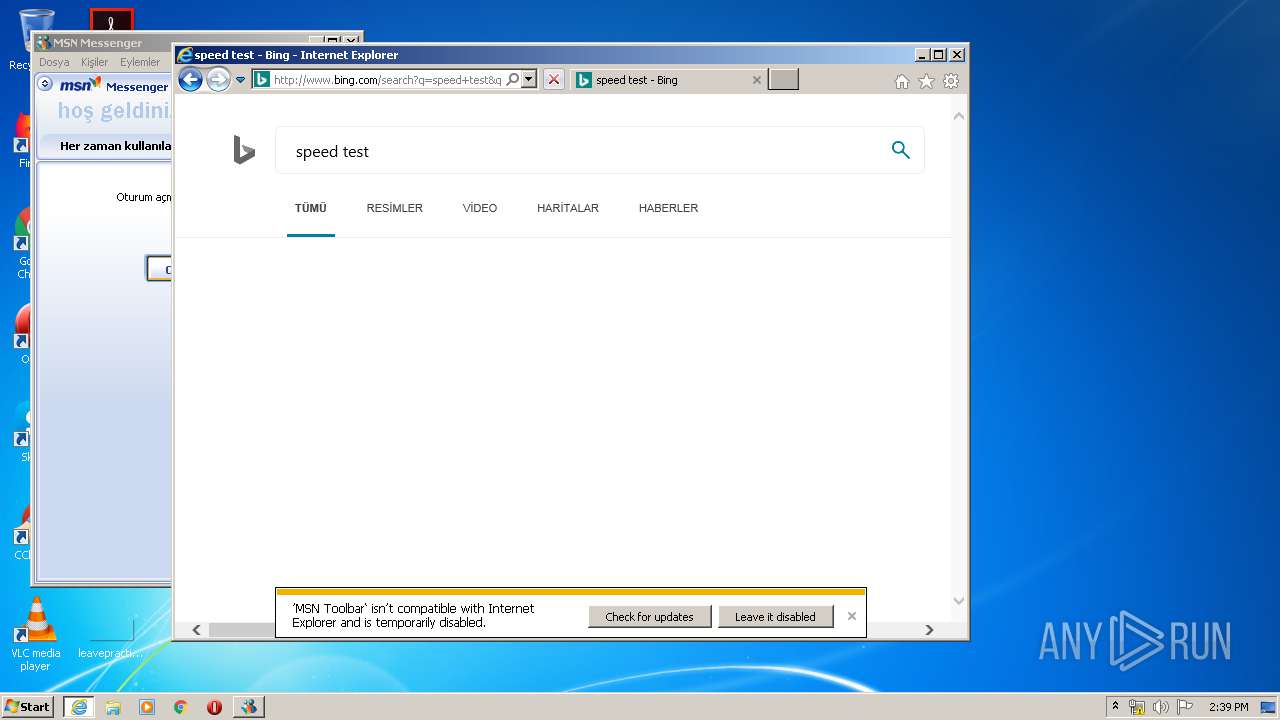
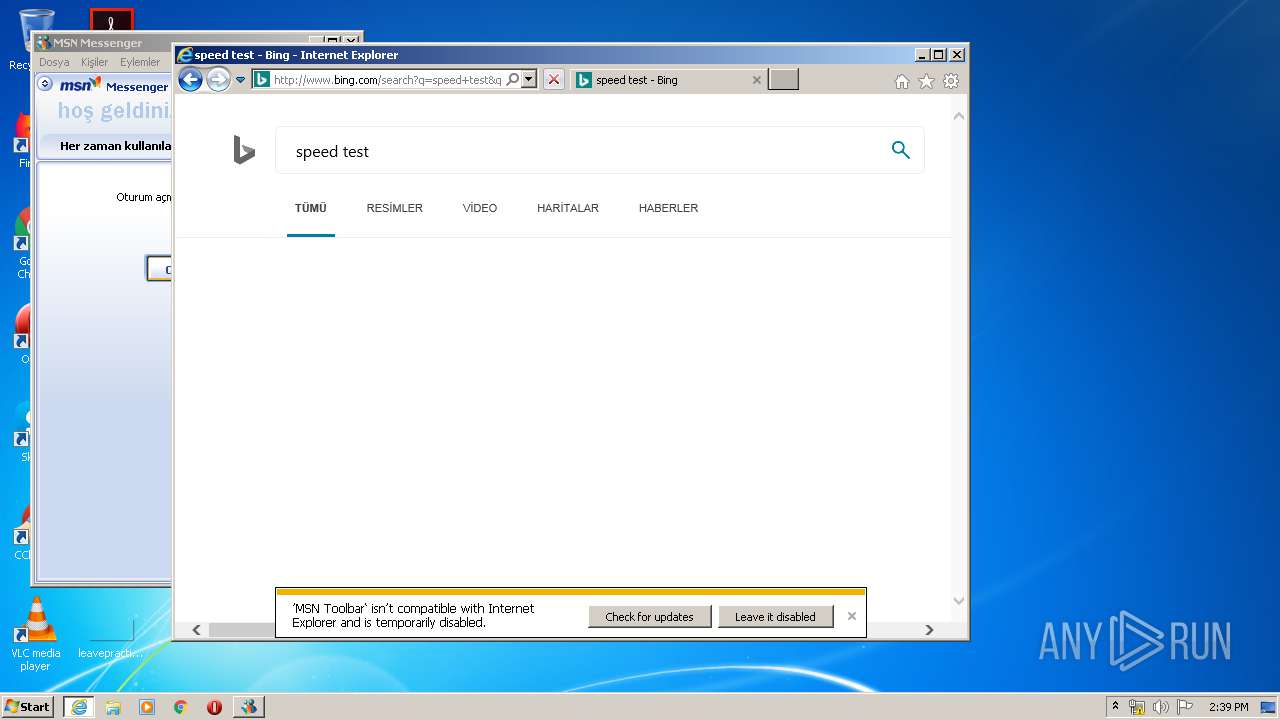
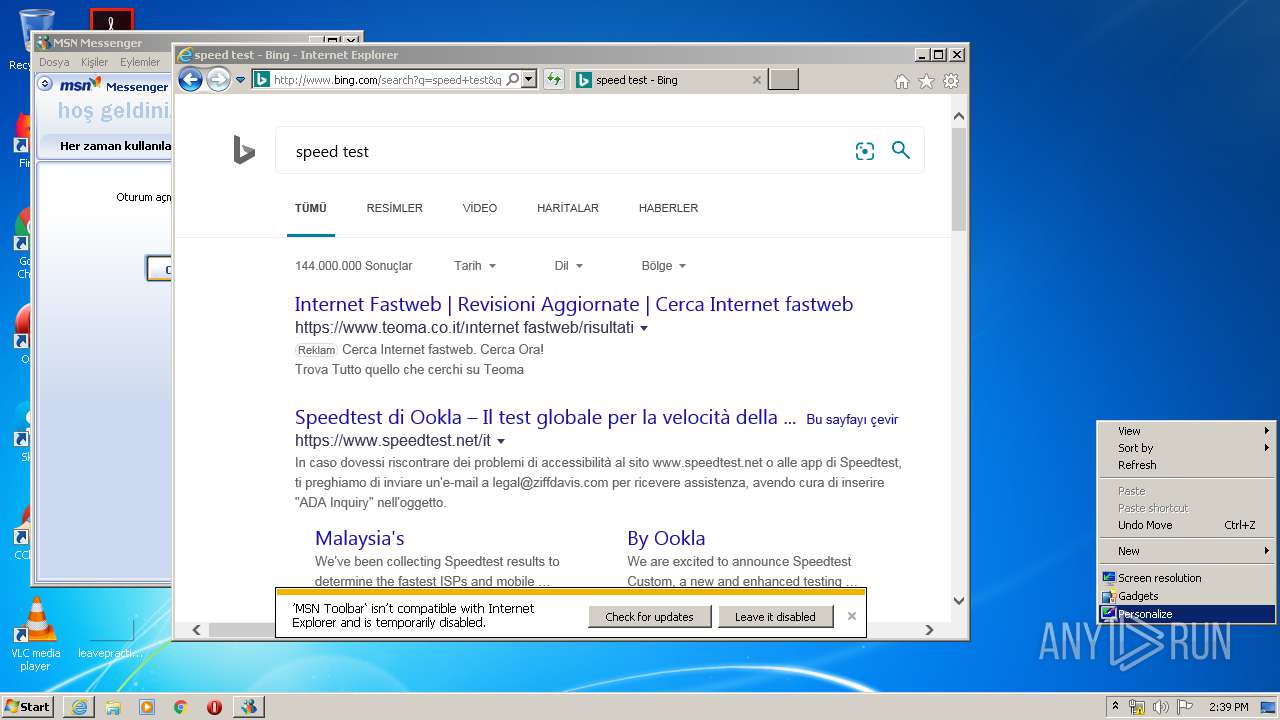
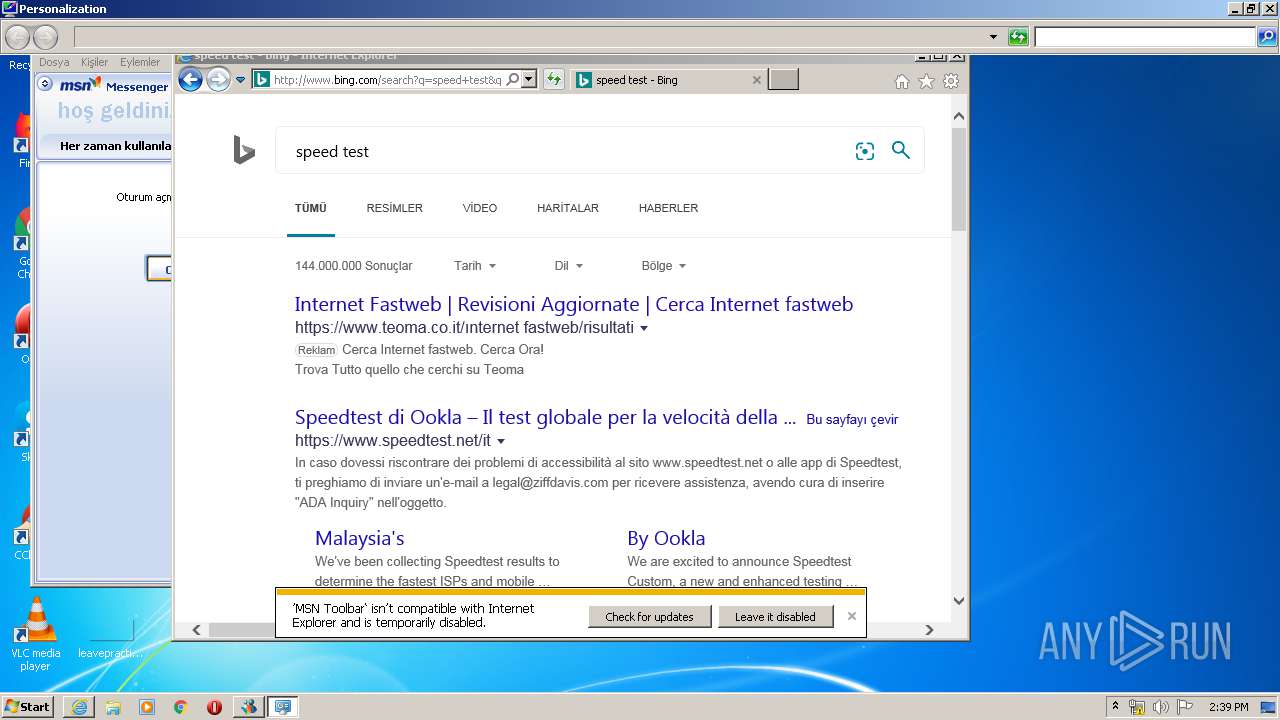
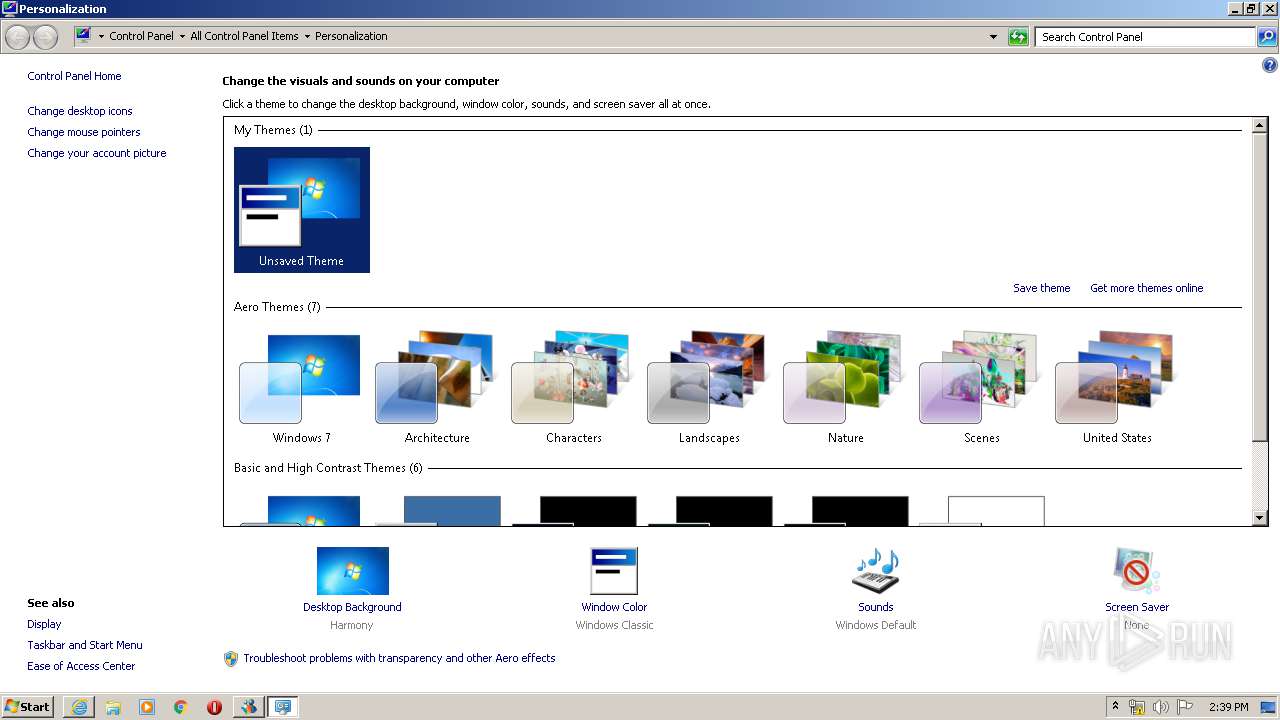
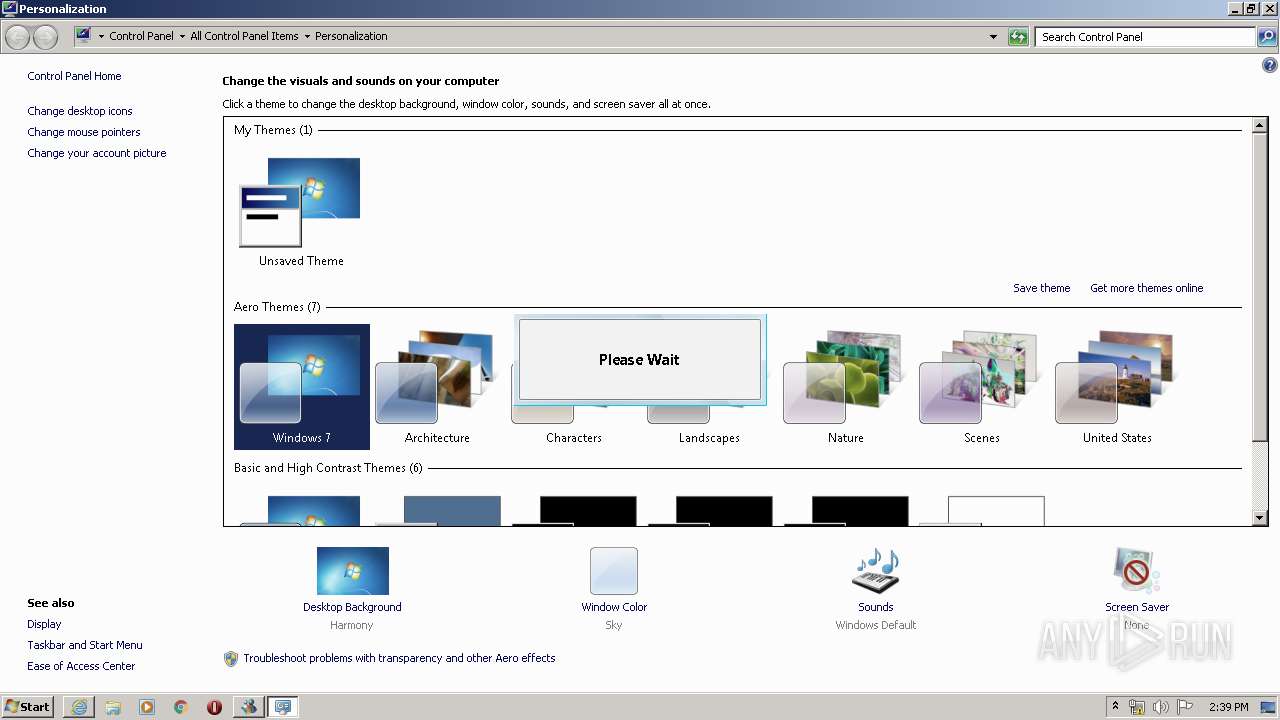
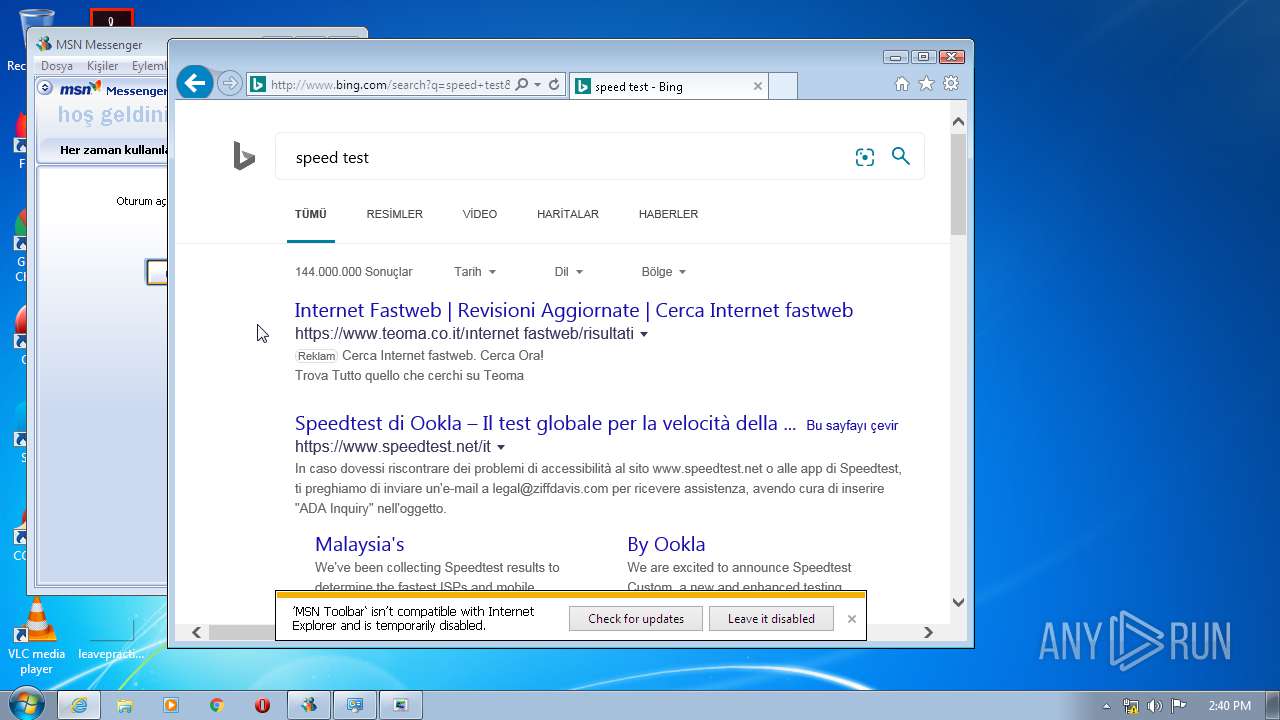
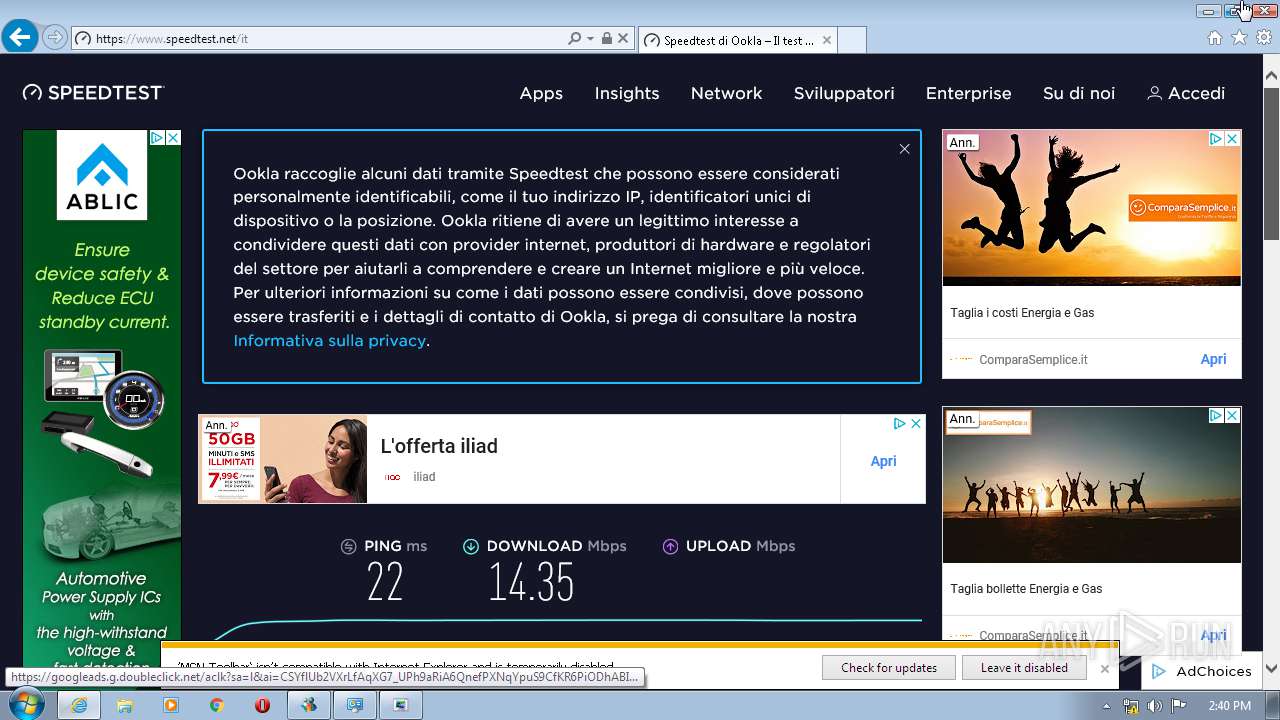
Changes the started page of IE
- msiexec.exe (PID: 3360)
Creates files in the program directory
- mtbs.exe (PID: 3508)
- msdt.exe (PID: 3036)
Reads internet explorer settings
- mtbs.exe (PID: 3508)
- msnmsgr.exe (PID: 1784)
Executed via COM
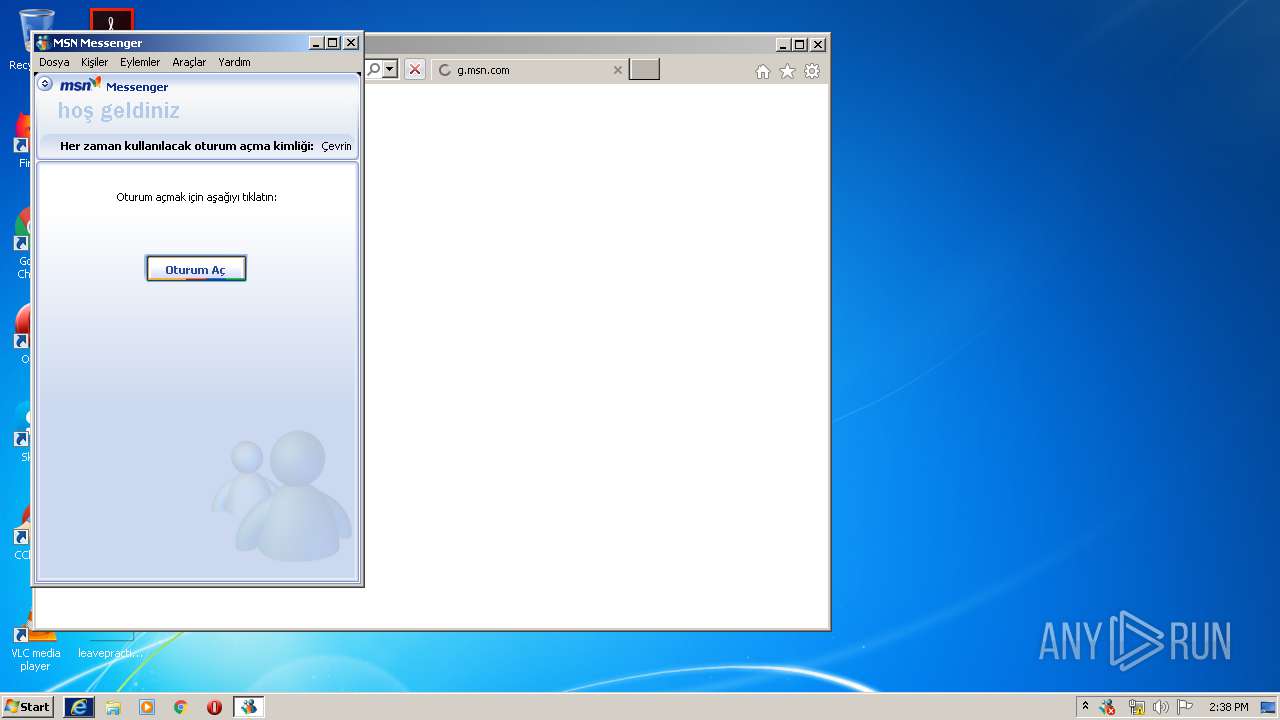
- iexplore.exe (PID: 3120)
- sdiagnhost.exe (PID: 2468)
- sdiagnhost.exe (PID: 2996)
Reads Internet Cache Settings
- msnmsgr.exe (PID: 1784)
Creates a software uninstall entry
- mtbs.exe (PID: 3508)
Creates files in the Windows directory
- msdt.exe (PID: 3036)
- WinSat.exe (PID: 3340)
- WinSat.exe (PID: 3072)
Application launched itself
- msdt.exe (PID: 3860)
Low-level read access rights to disk partition
- WinSat.exe (PID: 2748)
- WinSat.exe (PID: 3340)
- WinSat.exe (PID: 3072)
Removes files from Windows directory
- msdt.exe (PID: 3036)
INFO
Application launched itself
- msiexec.exe (PID: 3360)
- iexplore.exe (PID: 3120)
Creates files in the program directory
- msiexec.exe (PID: 3360)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3820)
- MsiExec.exe (PID: 332)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3848)
Searches for installed software
- msiexec.exe (PID: 3360)
Creates a software uninstall entry
- msiexec.exe (PID: 3360)
Reads Internet Cache Settings
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 2120)
Changes internet zones settings
- iexplore.exe (PID: 3120)
Creates files in the user directory
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3120)
- WINWORD.EXE (PID: 3556)
Reads internet explorer settings
- iexplore.exe (PID: 2120)
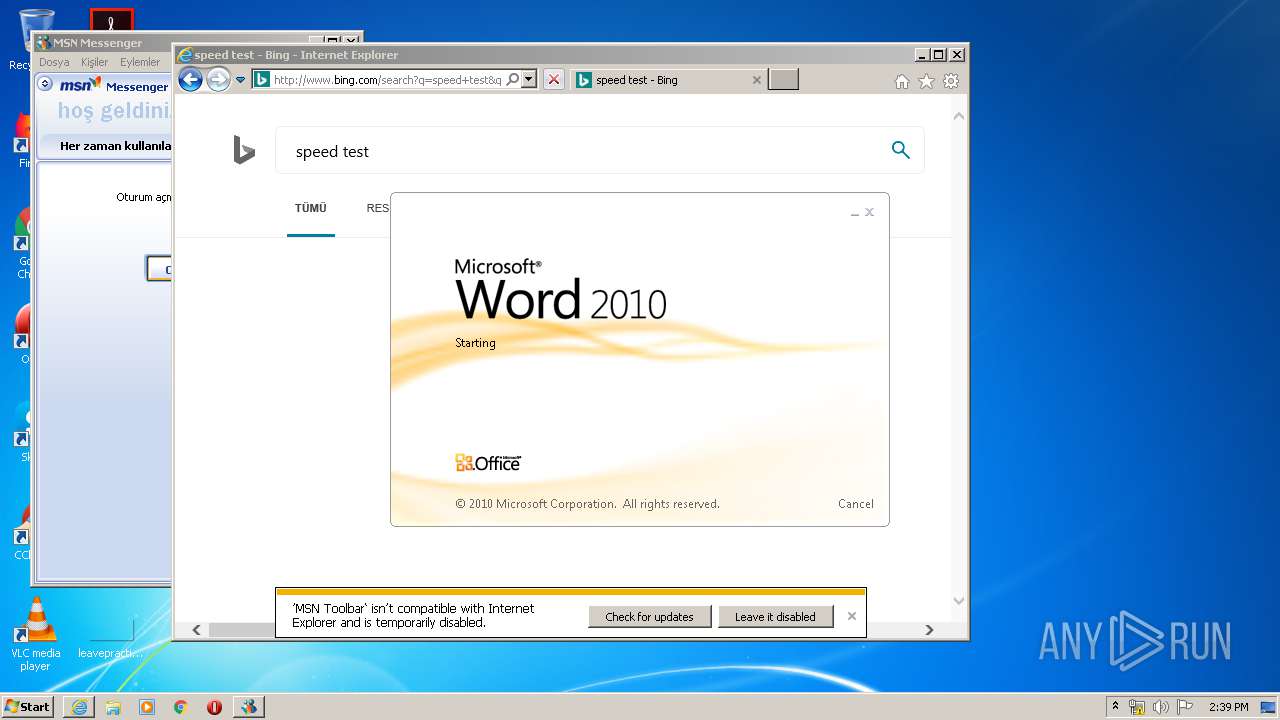
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3556)
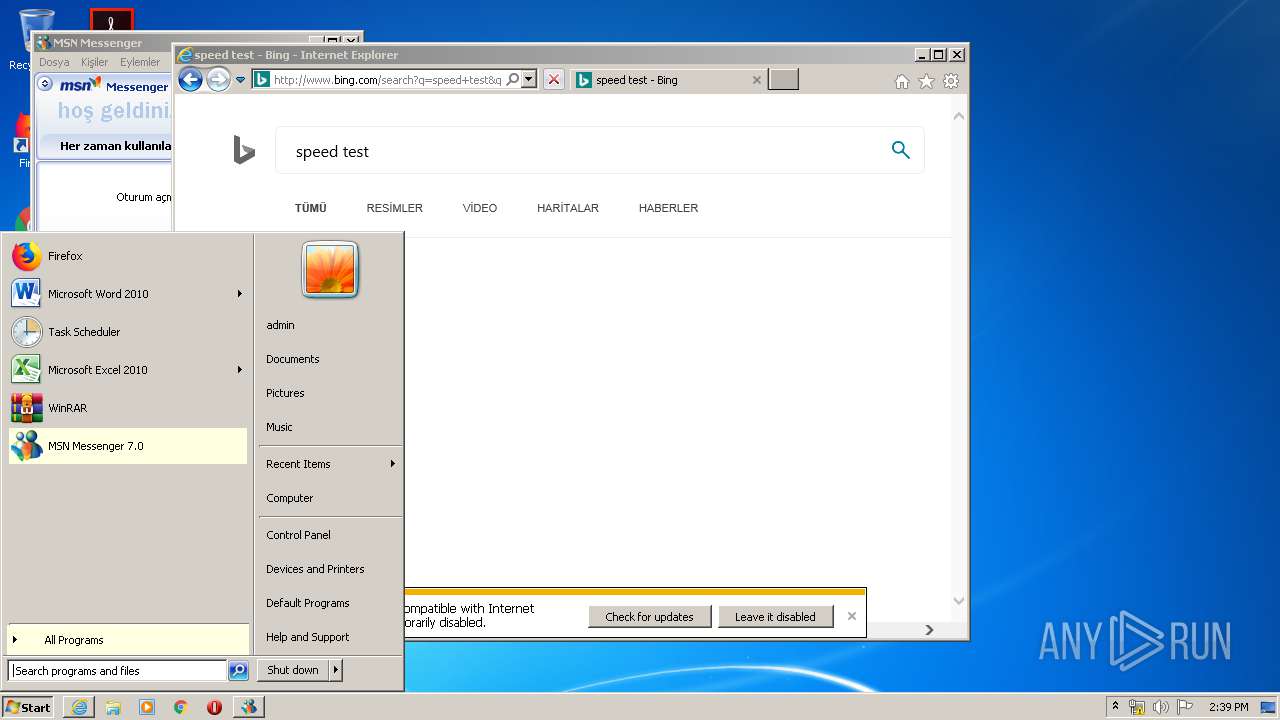
Manual execution by user
- WINWORD.EXE (PID: 3556)
- msdt.exe (PID: 3860)
Reads settings of System Certificates
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3120)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2120)
Changes settings of System certificates
- iexplore.exe (PID: 2120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:08:29 13:23:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7 |
| CodeSize: | 34816 |
| InitializedDataSize: | 10801152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5ae4 |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.2800.1106 |
| ProductVersionNumber: | 6.0.2800.1106 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Turkish |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Kabin Ayıklayıcısı |
| FileVersion: | 6.00.2800.1106 |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. Tüm hakları saklıdır. |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft® Windows® İşletim Sistemi |
| ProductVersion: | 6.00.2800.1106 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Aug-2002 11:23:17 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Kabin Ayıklayıcısı |
| FileVersion: | 6.00.2800.1106 |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. Tüm hakları saklıdır. |
| OriginalFilename: | WEXTRACT.EXE |
| ProductName: | Microsoft® Windows® İşletim Sistemi |
| ProductVersion: | 6.00.2800.1106 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-Aug-2002 11:23:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000086E6 | 0x00008800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5734 |
.data | 0x0000A000 | 0x00001BE4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.18428 |
.rsrc | 0x0000C000 | 0x00A4D000 | 0x00A4CC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99962 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.45336 | 1016 | Latin 1 / Western European | Turkish - Turkey | RT_VERSION |
2 | 3.53793 | 296 | Latin 1 / Western European | Turkish - Turkey | RT_ICON |
63 | 2.8173 | 144 | Latin 1 / Western European | Turkish - Turkey | RT_STRING |
76 | 3.56513 | 1288 | Latin 1 / Western European | Turkish - Turkey | RT_STRING |
77 | 3.53457 | 1478 | Latin 1 / Western European | Turkish - Turkey | RT_STRING |
80 | 3.53045 | 1206 | Latin 1 / Western European | Turkish - Turkey | RT_STRING |
83 | 3.54802 | 1216 | Latin 1 / Western European | Turkish - Turkey | RT_STRING |
85 | 3.45904 | 818 | Latin 1 / Western European | Turkish - Turkey | RT_STRING |
2001 | 3.50539 | 796 | Latin 1 / Western European | Turkish - Turkey | RT_DIALOG |
2002 | 3.23759 | 398 | Latin 1 / Western European | Turkish - Turkey | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
86
Monitored processes
32
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | C:\Windows\system32\MsiExec.exe -Embedding 76E14903C25E0FF1B65985322452C1C7 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\bootstrap.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\bootstrap.exe | msn-7.0.0820-tr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSN Messenger Setup Bootstrap Exit code: 0 Version: 7.0.0820 Modules
| |||||||||||||||
| 552 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ftbnbopo.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 944 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ruxl_21w.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 1168 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES40AD.tmp" "c:\Users\admin\AppData\Local\Temp\CSC40AC.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1492 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\upr1x0f3.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 1784 | "C:\Program Files\MSN Messenger\msnmsgr.exe" | C:\Program Files\MSN Messenger\msnmsgr.exe | — | bootstrap.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSN Messenger Exit code: 0 Version: 7.0.0820 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3120 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2468 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\AppData\Local\Temp\msn-7.0.0820-tr.exe" | C:\Users\admin\AppData\Local\Temp\msn-7.0.0820-tr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Kabin Ayıklayıcısı Exit code: 0 Version: 6.00.2800.1106 Modules
| |||||||||||||||
Total events
7 716
Read events
4 012
Write events
3 516
Delete events
188
Modification events
| (PID) Process: | (2480) msn-7.0.0820-tr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000028D03AEF6112D601200D0000780C0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000028D03AEF6112D601200D0000780C0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 34 | |||
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000681B87EF6112D601200D0000780C0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3360) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000681B87EF6112D601200D0000280E0000E8030000010000000000000000000000B825F70A24BF0B43B95F8A5CA762BA8C0000000000000000 | |||
| (PID) Process: | (3848) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000092909CEF6112D601080F0000740D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3848) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000092909CEF6112D601080F0000380B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3848) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000092909CEF6112D601080F0000700F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3848) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000092909CEF6112D601080F0000940C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
35
Suspicious files
233
Text files
366
Unknown types
130
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | msn-7.0.0820-tr.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\MsnMsgs.msi | — | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\Windows\Installer\a765f1.msi | — | |
MD5:— | SHA256:— | |||
| 3848 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\Windows\Installer\MSI7891.tmp | — | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFF8EBB54DFD6CCF50.TMP | — | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\Program Files\MSN Messenger\custsat.dll | executable | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\Program Files\MSN Messenger\mailtmpl.txt | text | |
MD5:— | SHA256:— | |||
| 348 | bootstrap.exe | C:\Users\admin\AppData\Local\Temp\MSIF9E9.tmp | executable | |
MD5:— | SHA256:— | |||
| 3360 | msiexec.exe | C:\Program Files\MSN Messenger\license.rtf | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
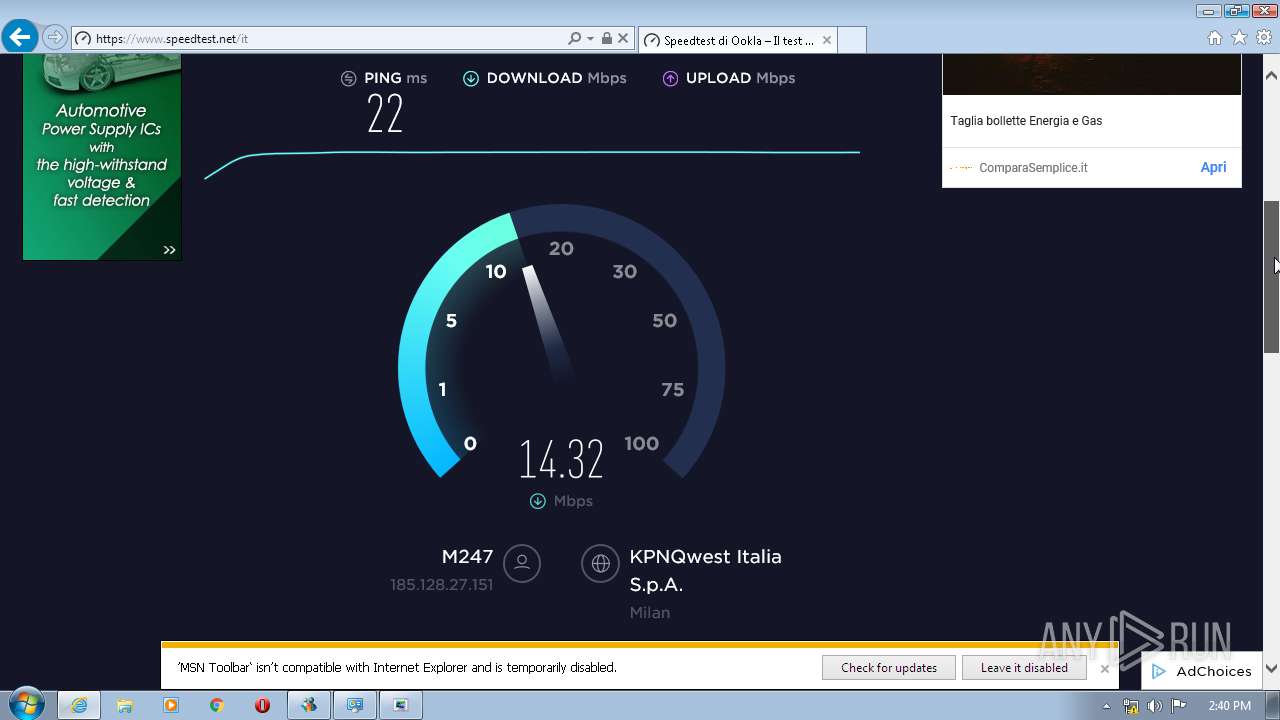
HTTP(S) requests
234
TCP/UDP connections
235
DNS requests
98
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
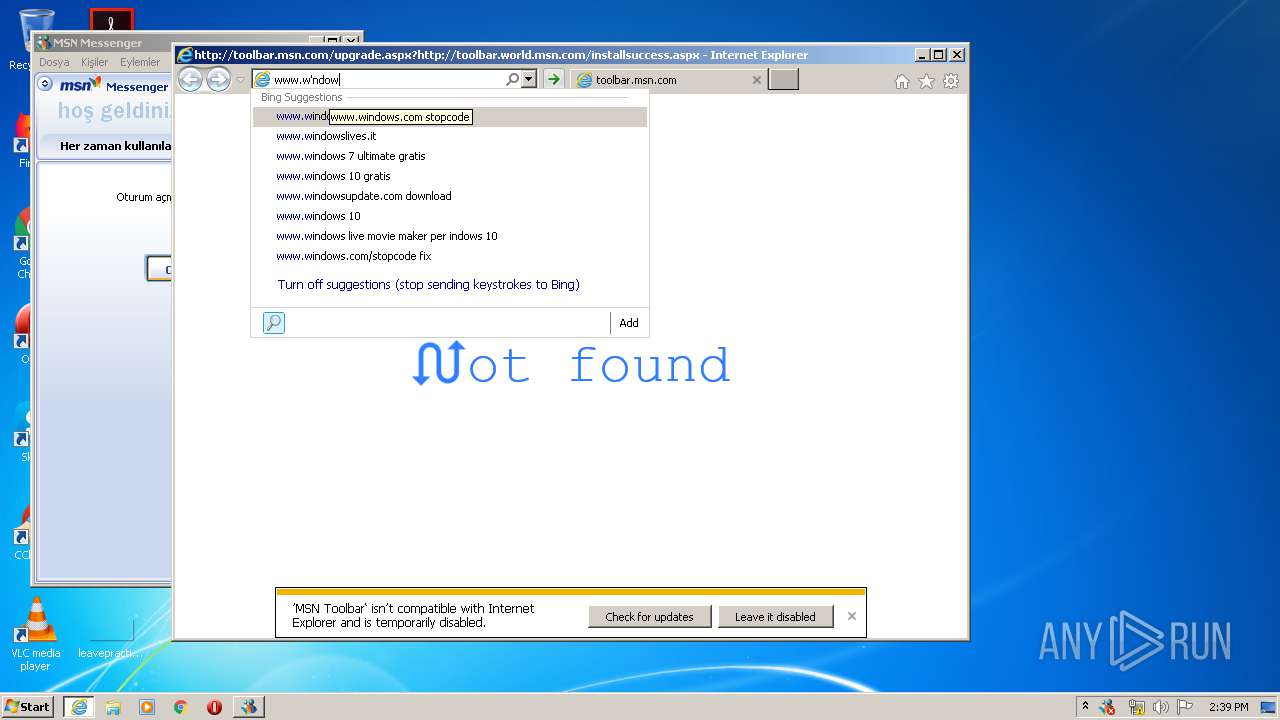
2120 | iexplore.exe | GET | 302 | 40.81.30.101:80 | http://g.msn.com/8SE/1?http://toolbar.world.msn.com/installsuccess.aspx&&FORM=TOOLBR&DI=2999&CM=MsgrInstall | US | — | — | whitelisted |
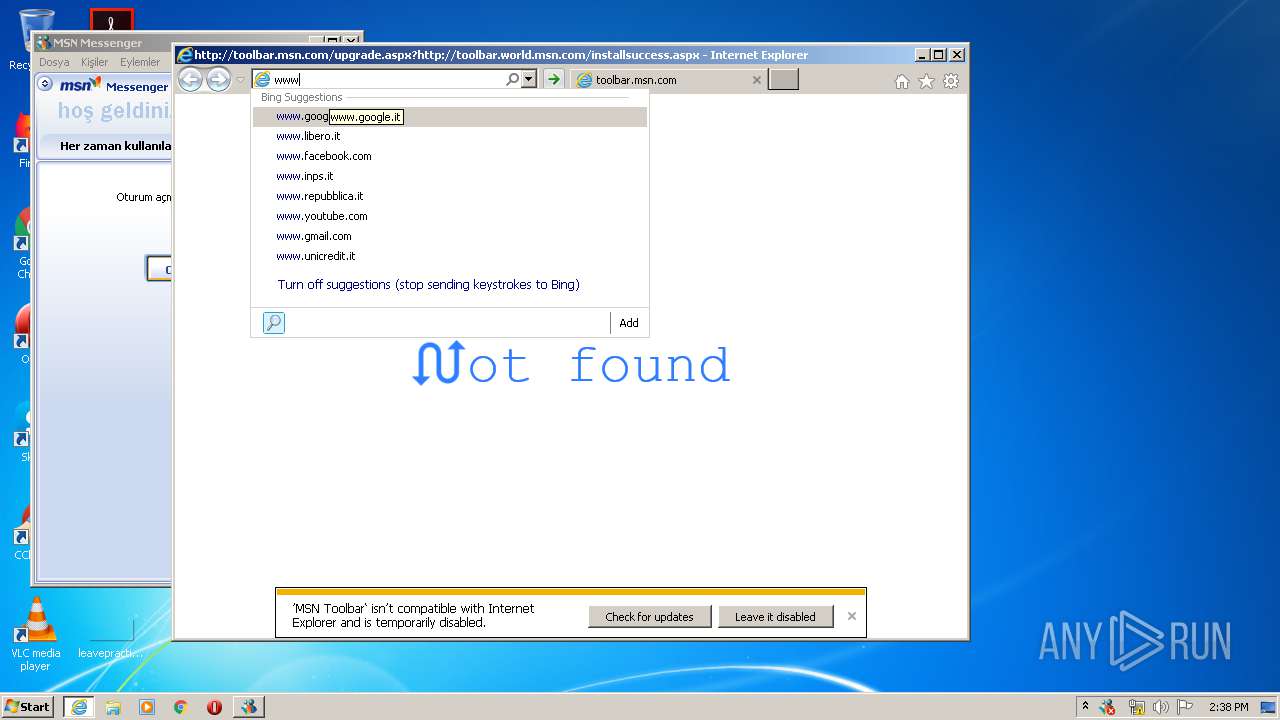
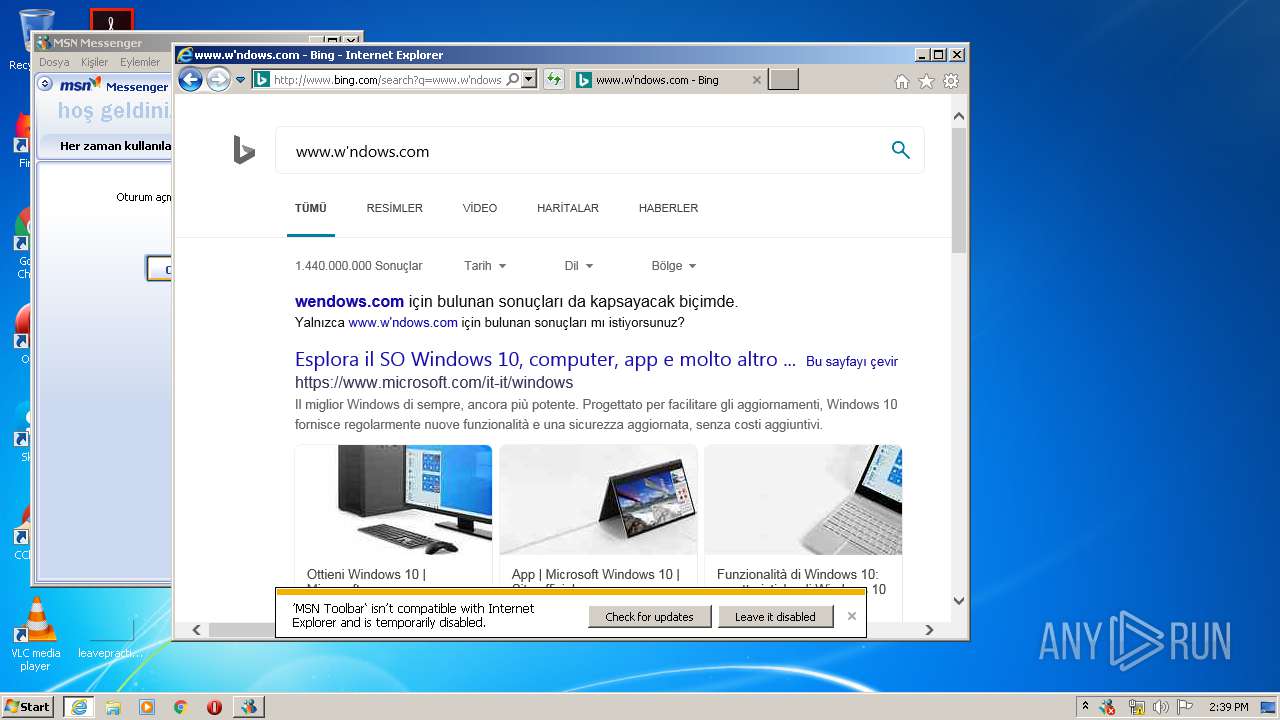
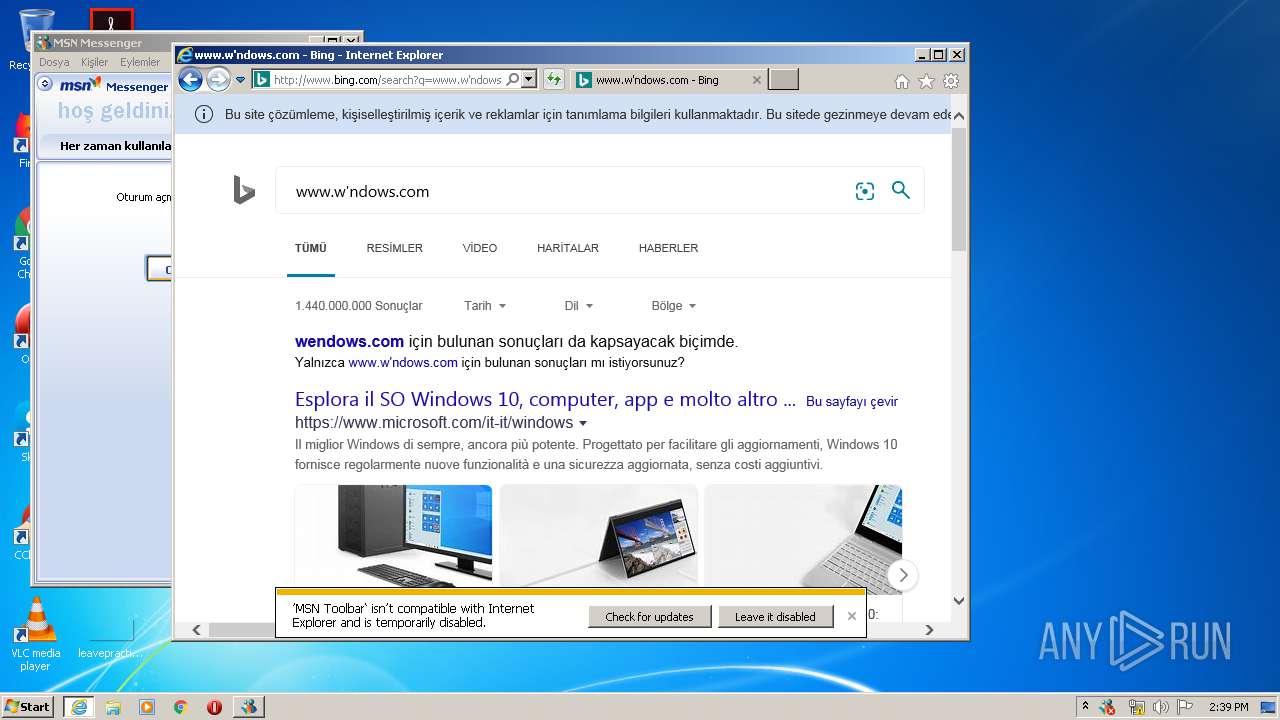
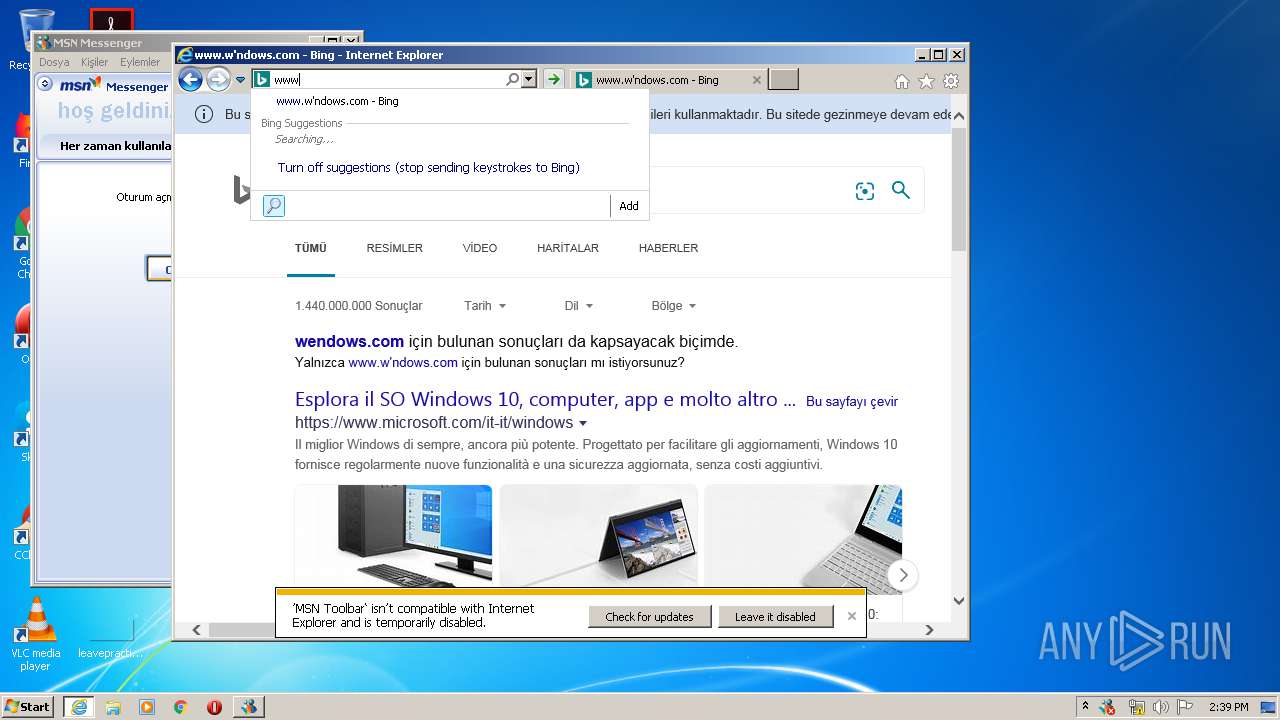
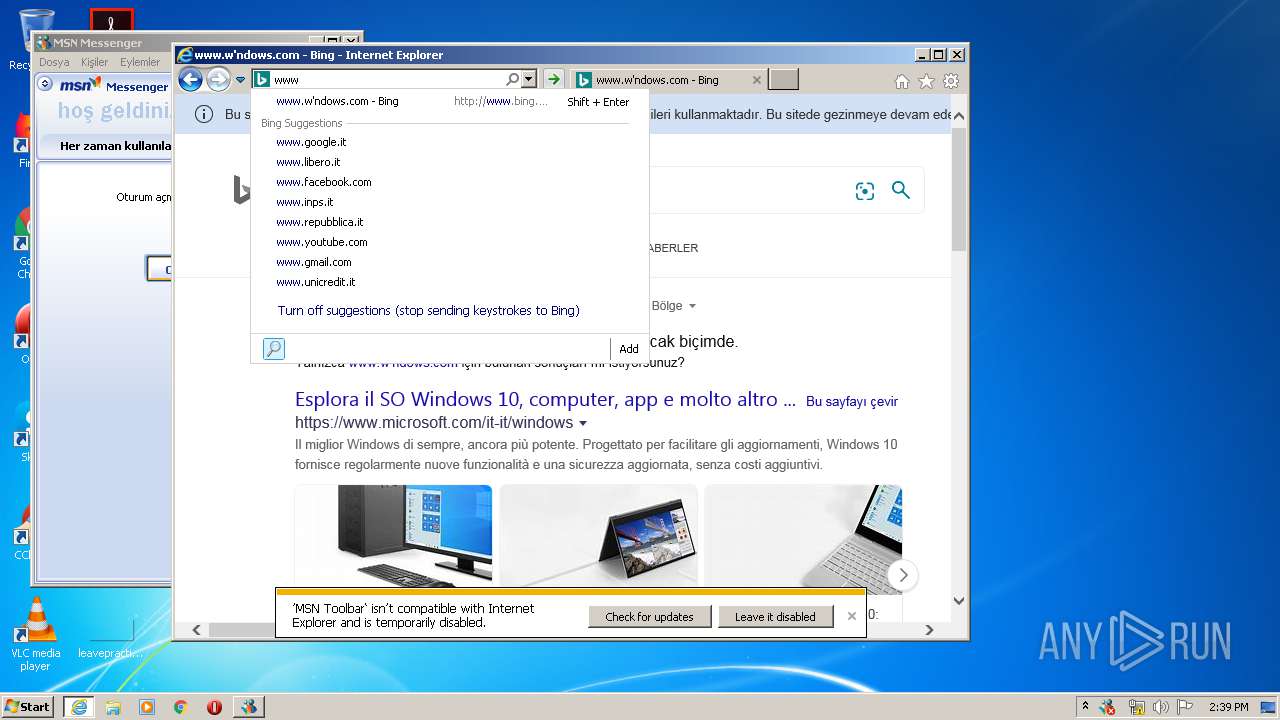
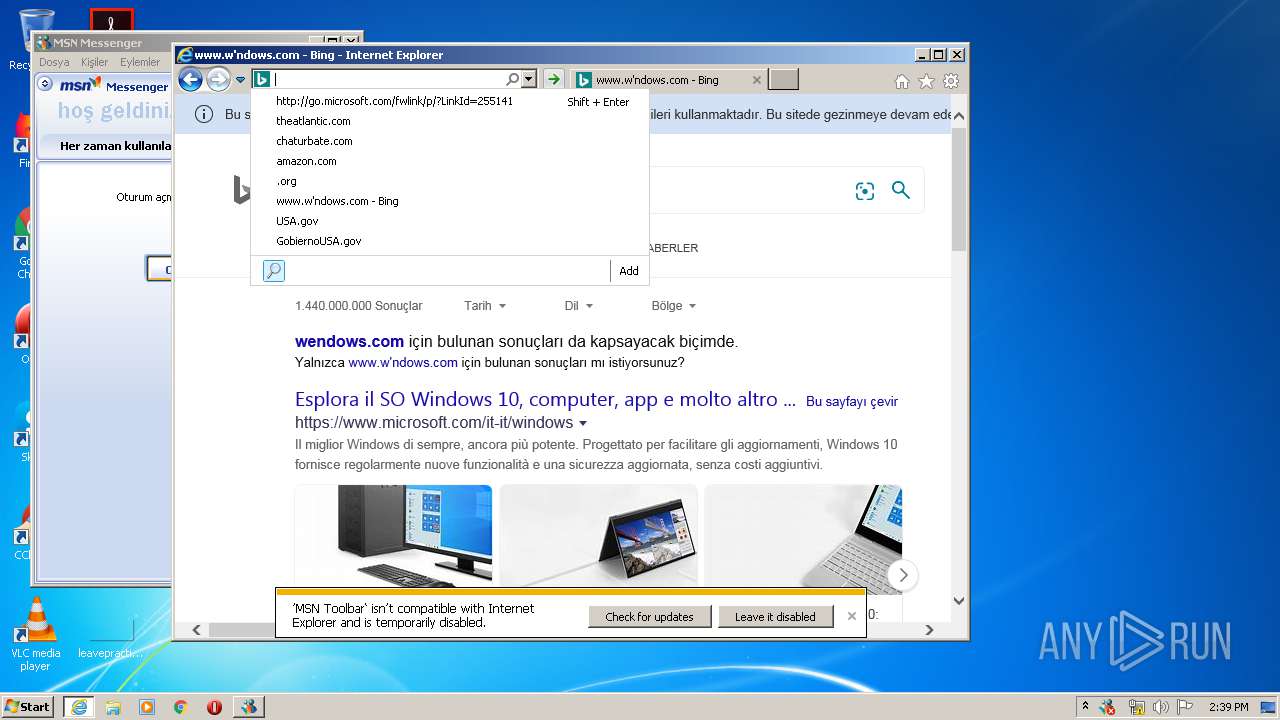
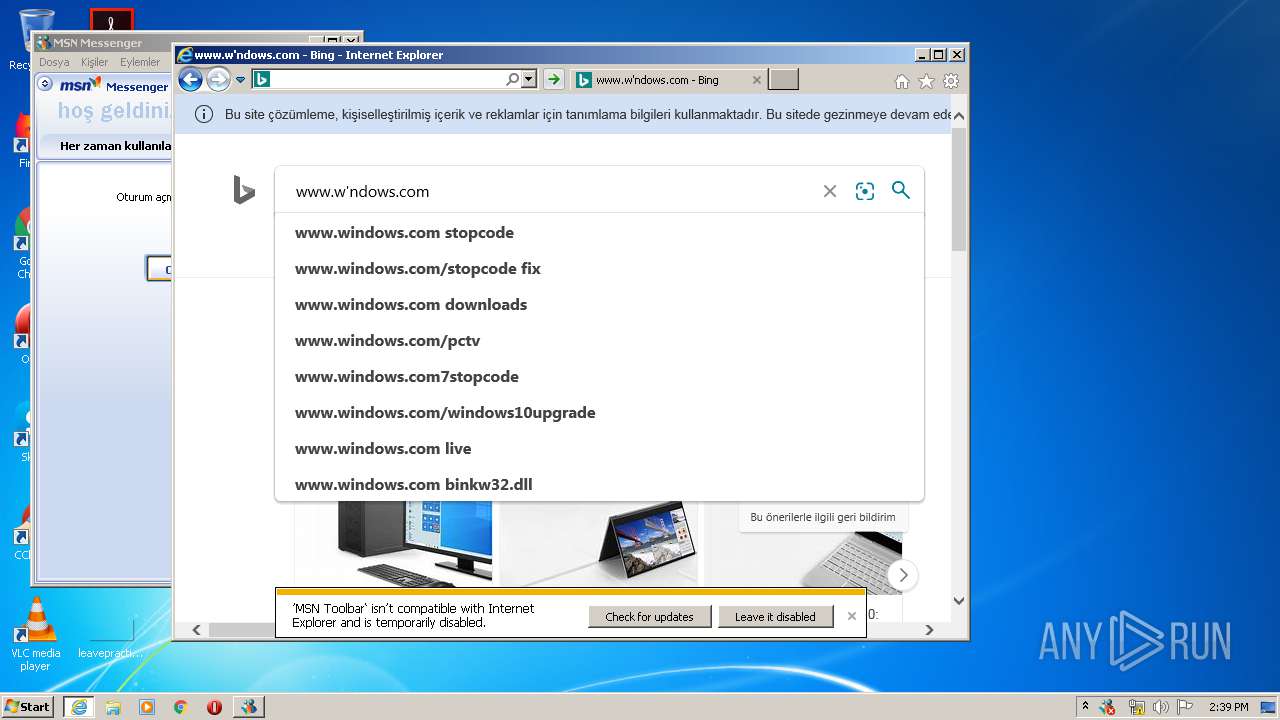
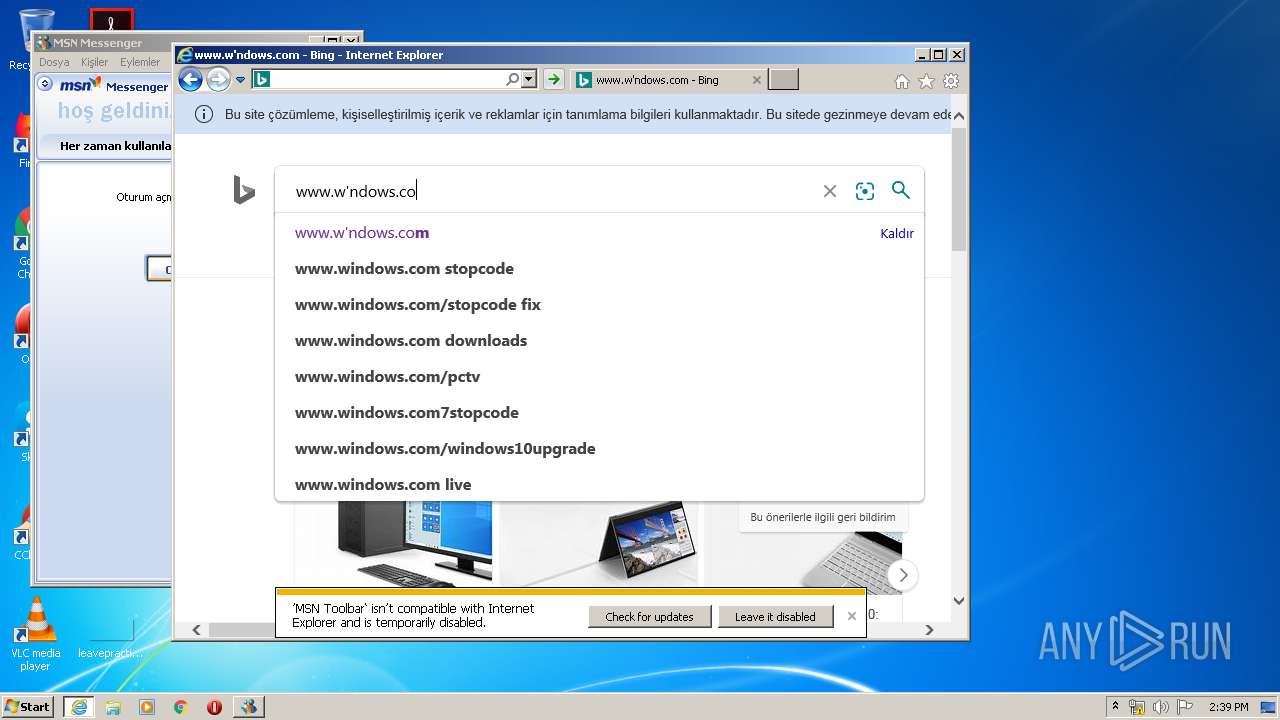
2120 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=www.w'ndows.c&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=tr | US | — | — | whitelisted |
2120 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=w&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=tr | US | xml | 241 b | whitelisted |
2120 | iexplore.exe | GET | 404 | 13.77.161.179:80 | http://toolbar.msn.com/upgrade.aspx?http://toolbar.world.msn.com/installsuccess.aspx | US | html | 2.83 Kb | whitelisted |
2120 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=www.w'ndow&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=tr | US | xml | 268 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=www.w'ndoww&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=tr | US | xml | 169 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=www.w'ndows.co&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=tr | US | xml | 250 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=www.w'nd&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=tr | US | xml | 246 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=ww&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=tr | US | xml | 241 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=www&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=tr | US | xml | 241 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | iexplore.exe | 204.79.197.222:80 | fp.msedge.net | Microsoft Corporation | US | whitelisted |
2120 | iexplore.exe | 2.16.106.96:80 | a4.bing.com | Akamai International B.V. | — | whitelisted |
2120 | iexplore.exe | 40.81.30.101:80 | g.msn.com | Microsoft Corporation | US | whitelisted |
2120 | iexplore.exe | 13.77.161.179:80 | toolbar.msn.com | Microsoft Corporation | US | whitelisted |
3120 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2120 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
2120 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2120 | iexplore.exe | 20.190.129.160:443 | login.microsoftonline.com | Microsoft Corporation | US | malicious |
2120 | iexplore.exe | 40.90.137.124:443 | login.live.com | Microsoft Corporation | US | unknown |
2120 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
runonce.msn.com |
| whitelisted |
g.msn.com |
| whitelisted |
toolbar.msn.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
15b399b47e6ec6bd50a308d3e6a53181.clo.footprintdns.com |
| unknown |
www2.bing.com |
| whitelisted |
07d39cfd12510ec9d5ad12331a8e2ead.clo.footprintdns.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2120 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
mtbs.exe | *** Assertion: Unknown IE Build Format (A) ***
|
mtbs.exe | *** Assertion: Unknown IE Major Version ***
|
mtbs.exe | 10990 OS: 0x6, 0x1
|
mtbs.exe | *** Assertion: Unknown IE Major Version ***
|
mtbs.exe | *** Assertion: Unknown IE Major Version ***
|
mtbs.exe | 10999 OS: 0x6, 0x1
|
mtbs.exe | 10999 http://g.msn.com/8SE/1?http://toolbar.world.msn.com/installsuccess.aspx&&FORM=TOOLBR&DI=2999&CM=MsgrInstall
|
mtbs.exe | 10999 Navigating to:
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|