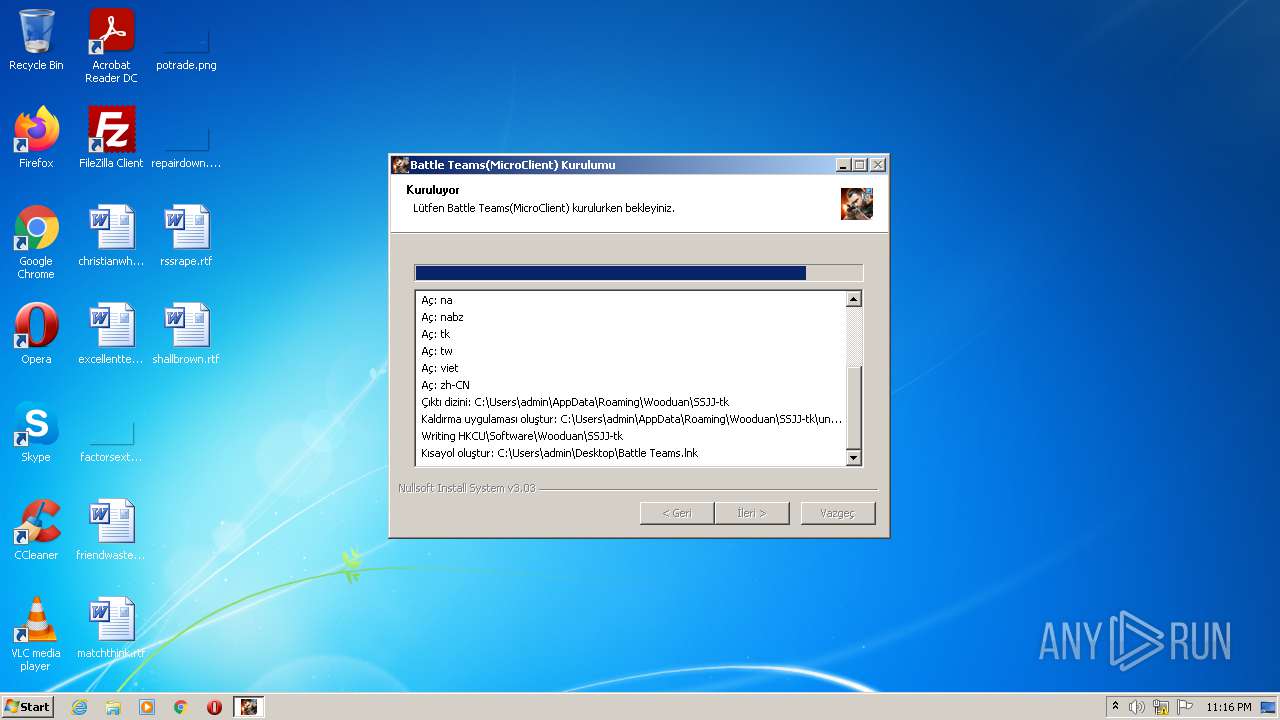
| File name: | battleteams-tk-Installer (1).exe |
| Full analysis: | https://app.any.run/tasks/1e4ff21e-a103-47bc-b994-353c78864b21 |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2021, 23:16:29 |
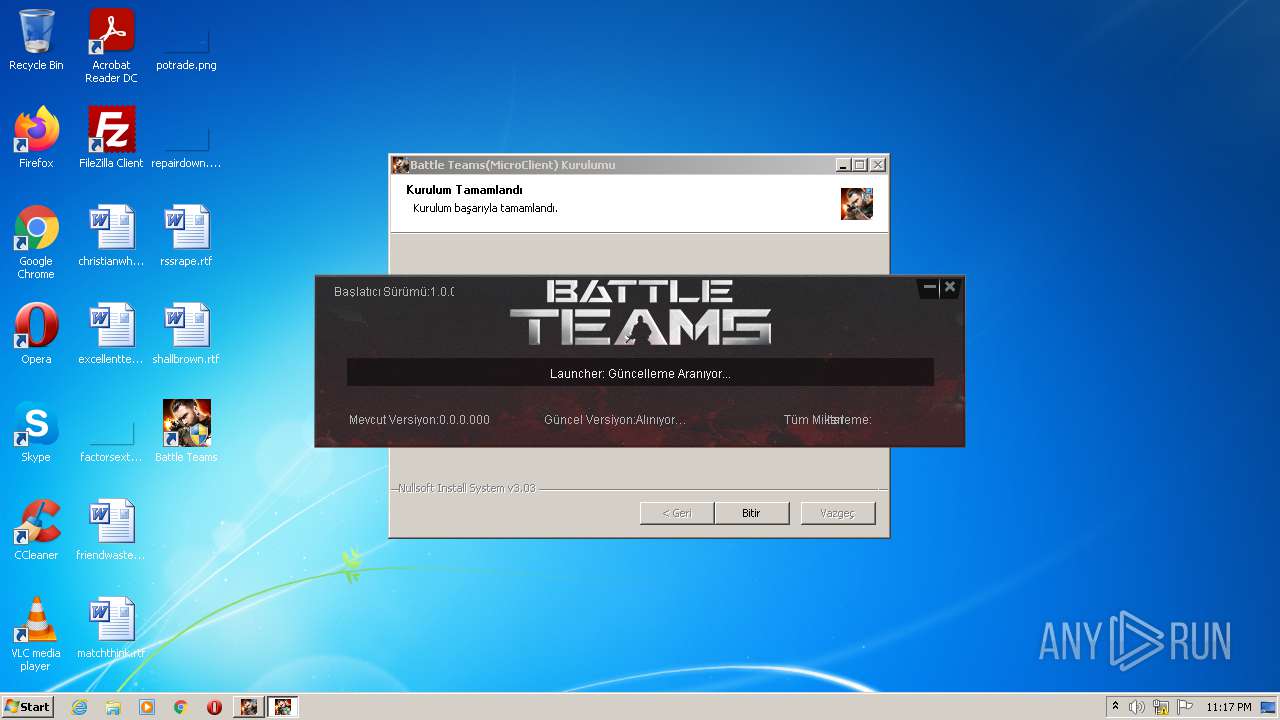
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | CFCE7236305497683C5710962DF20247 |
| SHA1: | DEB8538DE6FCD35E145B62DA53EB619241C0C265 |
| SHA256: | CBE44EC49AA08681B2D4E0F915FF0FB13D35FD4BDB33604DD47F8AD9AC6D12B5 |
| SSDEEP: | 49152:Y0t+Xo7jRFig7vhubhzS5wQV5r+oDGvdj402JSMbkcf9Vb07:Y0t6oJFDbhMzSzV5Lsdj4/1bfL07 |
MALICIOUS
Loads dropped or rewritten executable
- battleteams-tk-Installer (1).exe (PID: 3152)
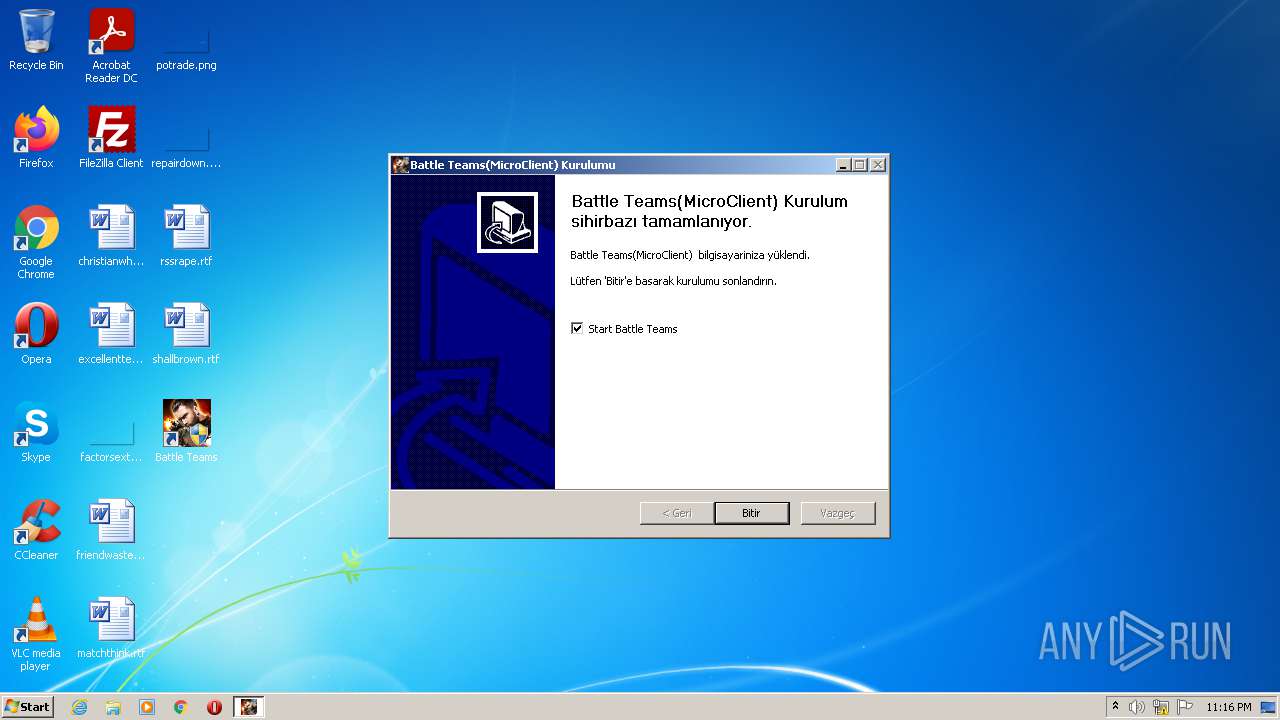
Application was dropped or rewritten from another process
- WDlauncher.exe (PID: 2792)
Drops executable file immediately after starts
- battleteams-tk-Installer (1).exe (PID: 3152)
SUSPICIOUS
Checks supported languages
- battleteams-tk-Installer (1).exe (PID: 3152)
- WDlauncher.exe (PID: 2792)
- WDlauncher.exe (PID: 3176)
Creates files in the user directory
- battleteams-tk-Installer (1).exe (PID: 3152)
- WDlauncher.exe (PID: 3176)
- WDlauncher.exe (PID: 2792)
Reads the computer name
- battleteams-tk-Installer (1).exe (PID: 3152)
- WDlauncher.exe (PID: 2792)
- WDlauncher.exe (PID: 3176)
Drops a file with too old compile date
- battleteams-tk-Installer (1).exe (PID: 3152)
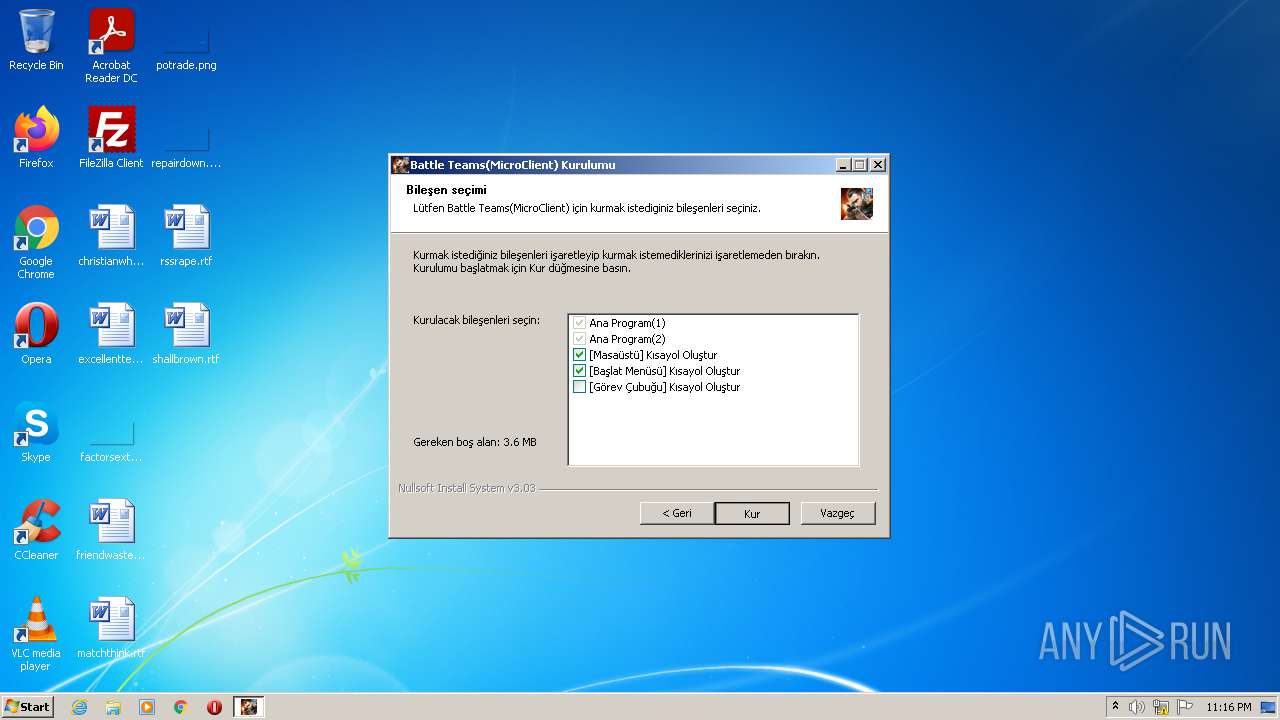
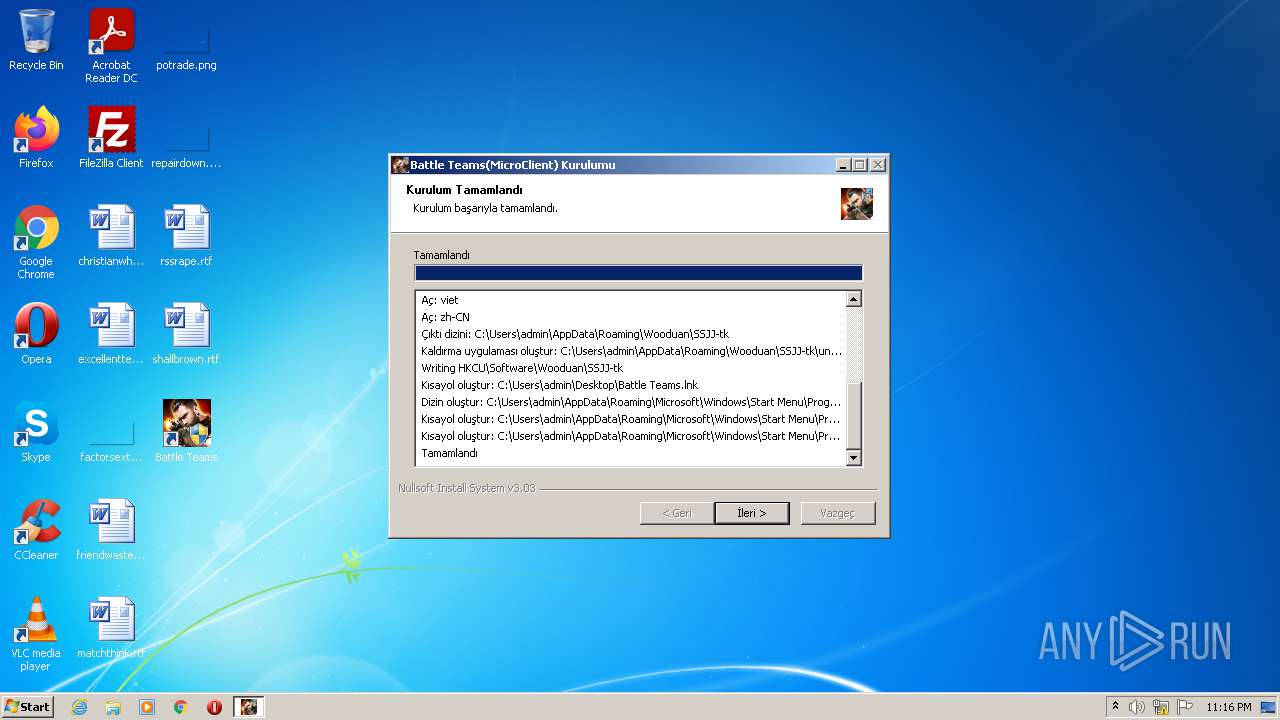
Creates a software uninstall entry
- battleteams-tk-Installer (1).exe (PID: 3152)
Executable content was dropped or overwritten
- battleteams-tk-Installer (1).exe (PID: 3152)
- WDlauncher.exe (PID: 2792)
Drops a file that was compiled in debug mode
- battleteams-tk-Installer (1).exe (PID: 3152)
- WDlauncher.exe (PID: 2792)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x34a5 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.13 |
| ProductVersionNumber: | 1.0.0.13 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
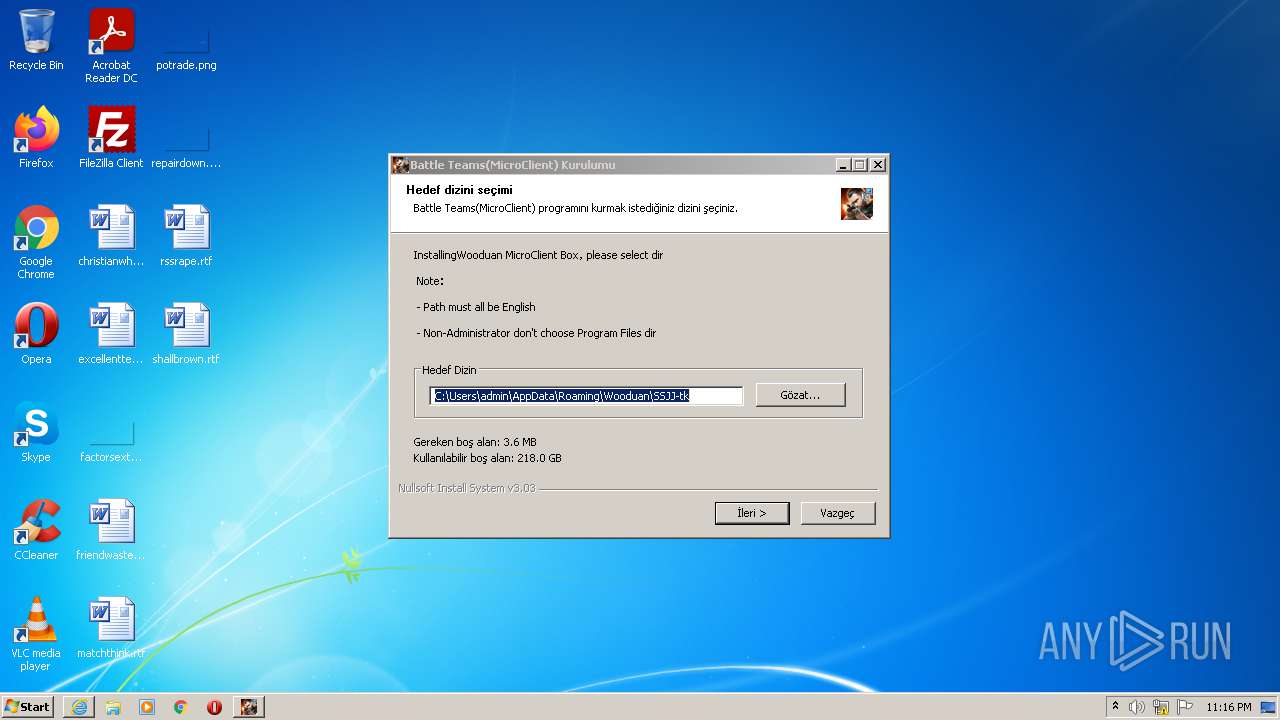
| Comments: | Wooduan MicroClient Box |
| CompanyName: | Wooduan |
| FileDescription: | tk |
| FileVersion: | 1.0.0.013 |
| LegalCopyright: | Zhejiang Wooduan Techonology Co., Ltd |
| ProductName: | Wooduan MicroClient Box |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:41 |
| Detected languages: |
|
| Comments: | Wooduan MicroClient Box |
| CompanyName: | Wooduan |
| FileDescription: | tk |
| FileVersion: | 1.0.0.013 |
| LegalCopyright: | Zhejiang Wooduan Techonology Co., Ltd |
| ProductName: | Wooduan MicroClient Box |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006409 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41622 |
.rdata | 0x00008000 | 0x0000138E | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14383 |
.data | 0x0000A000 | 0x00020358 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0044 |
.ndata | 0x0002B000 | 0x00029000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00054000 | 0x000167B0 | 0x00016800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.51707 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2963 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.56579 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 6.56964 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 6.47594 | 2440 | UNKNOWN | English - United States | RT_ICON |
5 | 6.32332 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.06384 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.65946 | 280 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2792 | "C:\Users\admin\AppData\Roaming\Wooduan\SSJJ-tk\WDlauncher.exe" | C:\Users\admin\AppData\Roaming\Wooduan\SSJJ-tk\WDlauncher.exe | battleteams-tk-Installer (1).exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Wooduan WD launcher Exit code: 0 Version: 1.0.0.013 Modules
| |||||||||||||||
| 3152 | "C:\Users\admin\AppData\Local\Temp\battleteams-tk-Installer (1).exe" | C:\Users\admin\AppData\Local\Temp\battleteams-tk-Installer (1).exe | Explorer.EXE | ||||||||||||
User: admin Company: Wooduan Integrity Level: MEDIUM Description: tk Exit code: 0 Version: 1.0.0.013 Modules
| |||||||||||||||
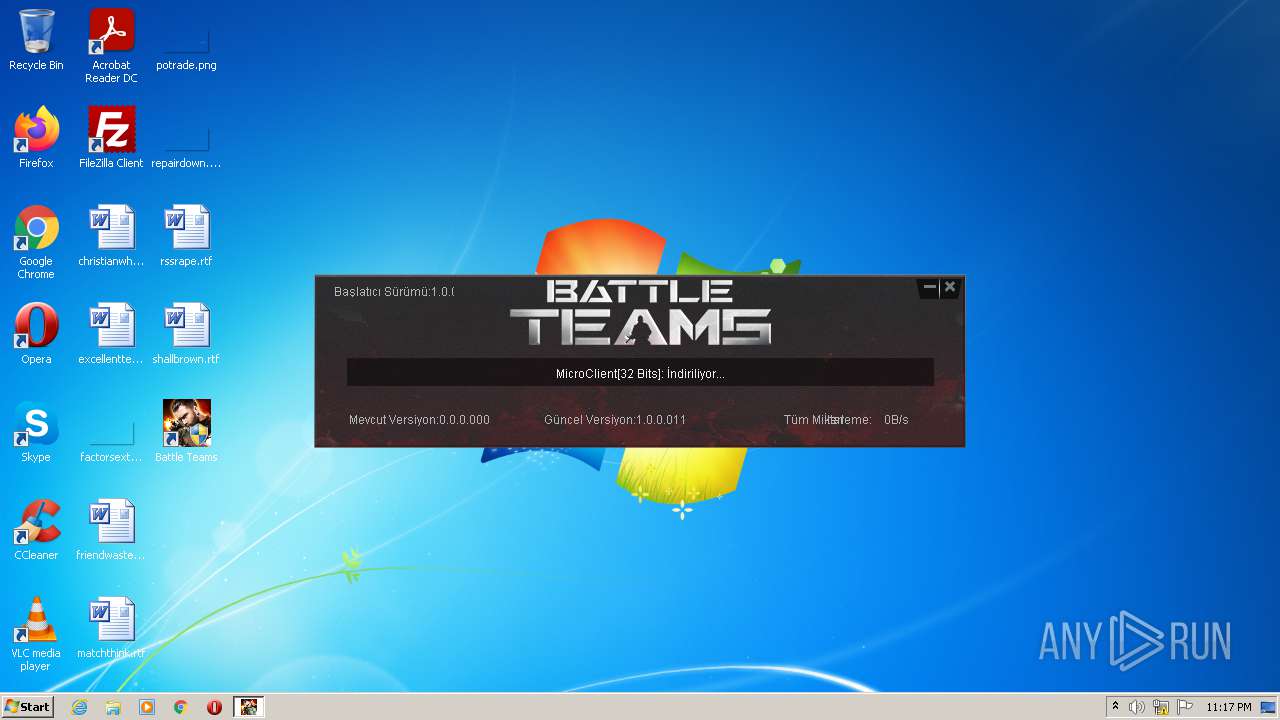
| 3176 | "C:\Users\admin\AppData\Roaming\Wooduan\SSJJ-tk\WDlauncher.exe" simu://micro/?um=1 | C:\Users\admin\AppData\Roaming\Wooduan\SSJJ-tk\WDlauncher.exe | WDlauncher.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Wooduan WD launcher Exit code: 0 Version: 1.0.0.011 Modules
| |||||||||||||||
Total events
2 207
Read events
2 152
Write events
55
Delete events
0
Modification events
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Wooduan\SSJJ-tk |
| Operation: | write | Name: | GUID |
Value: 1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | |||
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3152) battleteams-tk-Installer (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
8
Suspicious files
2
Text files
43
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\log_error[1] | text | |
MD5:D1AE9F3E669BB0CA4374498F9E486400 | SHA256:9076E29E9202CA1306B5A11AD6BEF1145B922DC40F80F6115606C11943608237 | |||
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Roaming\Wooduan\SSJJ-tk\platform.ini | ini | |
MD5:8E67305C881F6633F3E25217BD4A1FB9 | SHA256:DB4B9C13F4E2AF5E88565ECC54E3A54E836821519DA9C2DD810E9343CBA95C89 | |||
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Local\Temp\nsx18C1.tmp\System.dll | executable | |
MD5:75ED96254FBF894E42058062B4B4F0D1 | SHA256:A632D74332B3F08F834C732A103DAFEB09A540823A2217CA7F49159755E8F1D7 | |||
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\log_error[1] | text | |
MD5:D1AE9F3E669BB0CA4374498F9E486400 | SHA256:9076E29E9202CA1306B5A11AD6BEF1145B922DC40F80F6115606C11943608237 | |||
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Local\Temp\nsx18C1.tmp\IpConfig.dll | executable | |
MD5:A75E3775DAAC9958610CE1308E0BCA3B | SHA256:FE2093FF4BFA1D7259C922ACA1E7BB219C4D234E469942446D9E2F8086B7D720 | |||
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Local\Temp\nsa6DC9.tmp | text | |
MD5:D1AE9F3E669BB0CA4374498F9E486400 | SHA256:9076E29E9202CA1306B5A11AD6BEF1145B922DC40F80F6115606C11943608237 | |||
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Roaming\Wooduan\SSJJ-tk\res.zip | compressed | |
MD5:6CF3A74DBC01A419BBF89EB5DDBC3129 | SHA256:2033B5E80C20A80712C376F99FED2995DA90F3AF9DC07552F33470A1C17798CB | |||
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\log_error[1] | text | |
MD5:D1AE9F3E669BB0CA4374498F9E486400 | SHA256:9076E29E9202CA1306B5A11AD6BEF1145B922DC40F80F6115606C11943608237 | |||
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Local\Temp\nss198D.tmp | text | |
MD5:D1AE9F3E669BB0CA4374498F9E486400 | SHA256:9076E29E9202CA1306B5A11AD6BEF1145B922DC40F80F6115606C11943608237 | |||
| 3152 | battleteams-tk-Installer (1).exe | C:\Users\admin\AppData\Local\Temp\nsh317B.tmp | text | |
MD5:D1AE9F3E669BB0CA4374498F9E486400 | SHA256:9076E29E9202CA1306B5A11AD6BEF1145B922DC40F80F6115606C11943608237 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
27
DNS requests
2
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
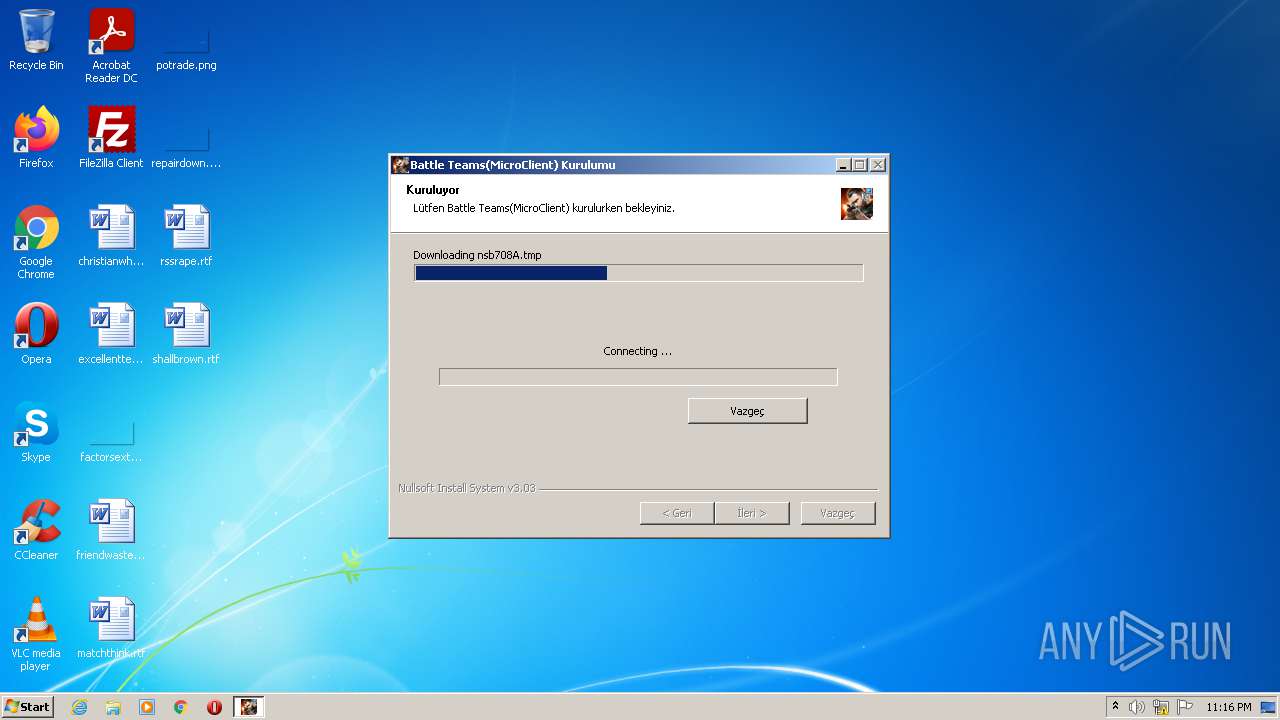
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=5.1.2.installer_start_succ&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=6.1.2.copy_file_succ&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=6.1.1.copy_file&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=6.2.1.set_registry&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=6.2.2.set_registry_succ&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=7.1.1.create_desktop_shortcut&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=7.2.2.create_startmenu_shortcut_succ&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=7.1.2.create_desktop_shortcut_succ&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=7.2.1.create_startmenu_shortcut&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
3152 | battleteams-tk-Installer (1).exe | GET | 200 | 111.230.127.48:80 | http://elk.wan5d.com/log_error?method=addMicoLog&src=installer&app=installer&ver=1.0.0.013&mac=12_A9_86_6C_77_DE&stage=8.4.2.run_repair_registry_succ&guid=1F3ABEE5-8A1B-4EFF-B0A7-8CD286A468BB | CN | text | 15 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2792 | WDlauncher.exe | 119.28.20.149:80 | — | Tencent Cloud Computing (Beijing) Co., Ltd | CN | unknown |
3152 | battleteams-tk-Installer (1).exe | 111.230.127.48:80 | elk.wan5d.com | Shenzhen Tencent Computer Systems Company Limited | CN | suspicious |
2792 | WDlauncher.exe | 101.33.11.45:80 | tkres.battleteams1.com | — | CN | unknown |
— | — | 119.28.20.149:80 | — | Tencent Cloud Computing (Beijing) Co., Ltd | CN | unknown |
— | — | 101.33.11.45:80 | tkres.battleteams1.com | — | CN | unknown |
3176 | WDlauncher.exe | 119.28.20.149:80 | — | Tencent Cloud Computing (Beijing) Co., Ltd | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
elk.wan5d.com |
| suspicious |
tkres.battleteams1.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3152 | battleteams-tk-Installer (1).exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |