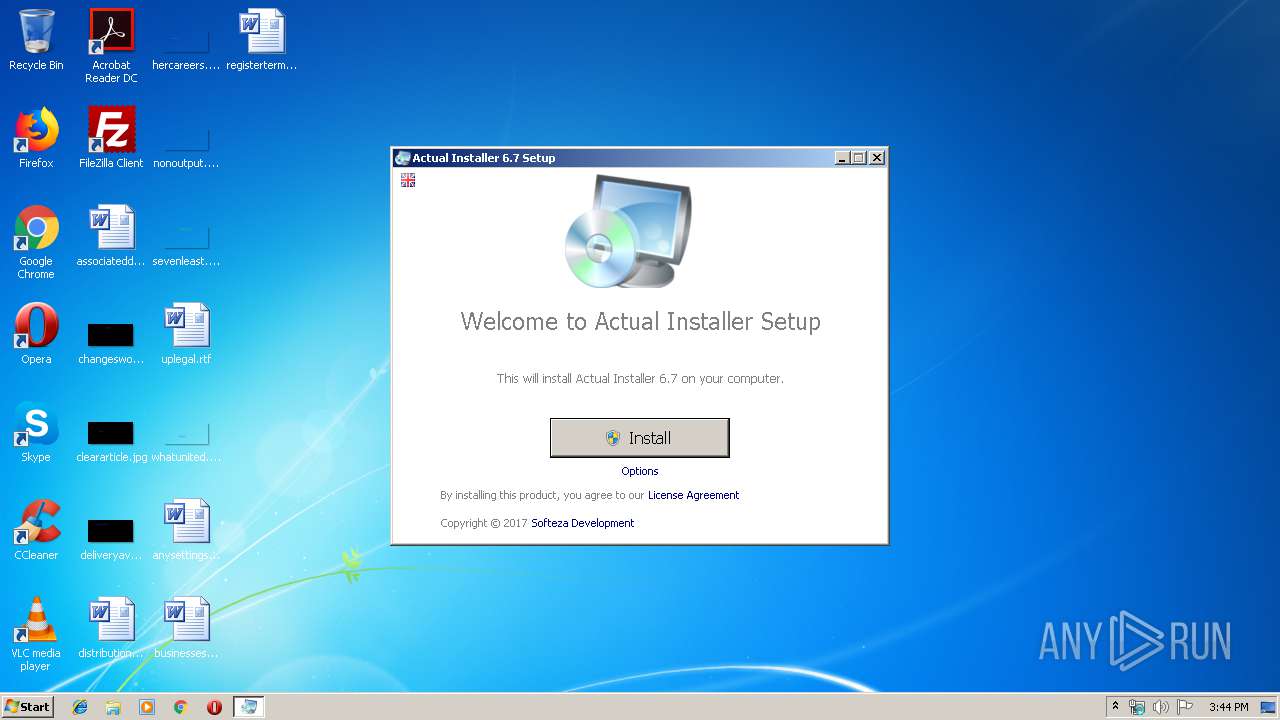
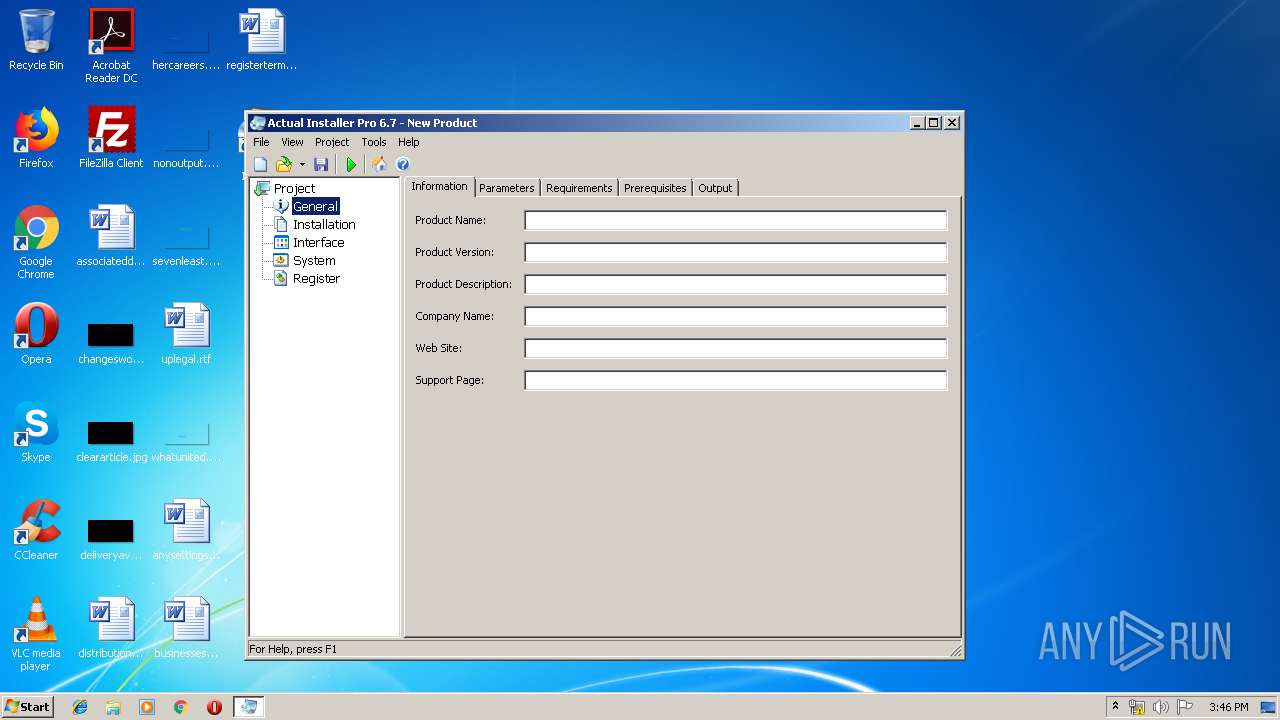
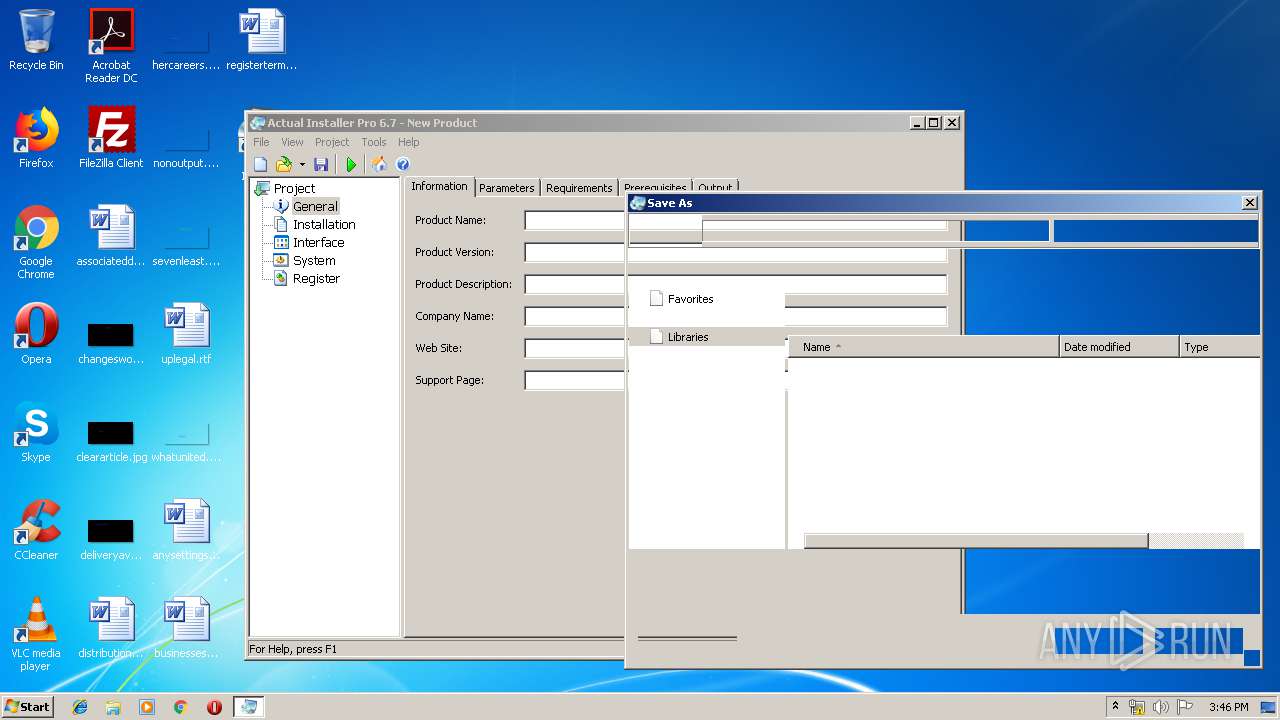
| File name: | Actual Installer Installation.exe |
| Full analysis: | https://app.any.run/tasks/e17ab4ec-ae3d-49eb-96ad-4f06ccb7ad66 |
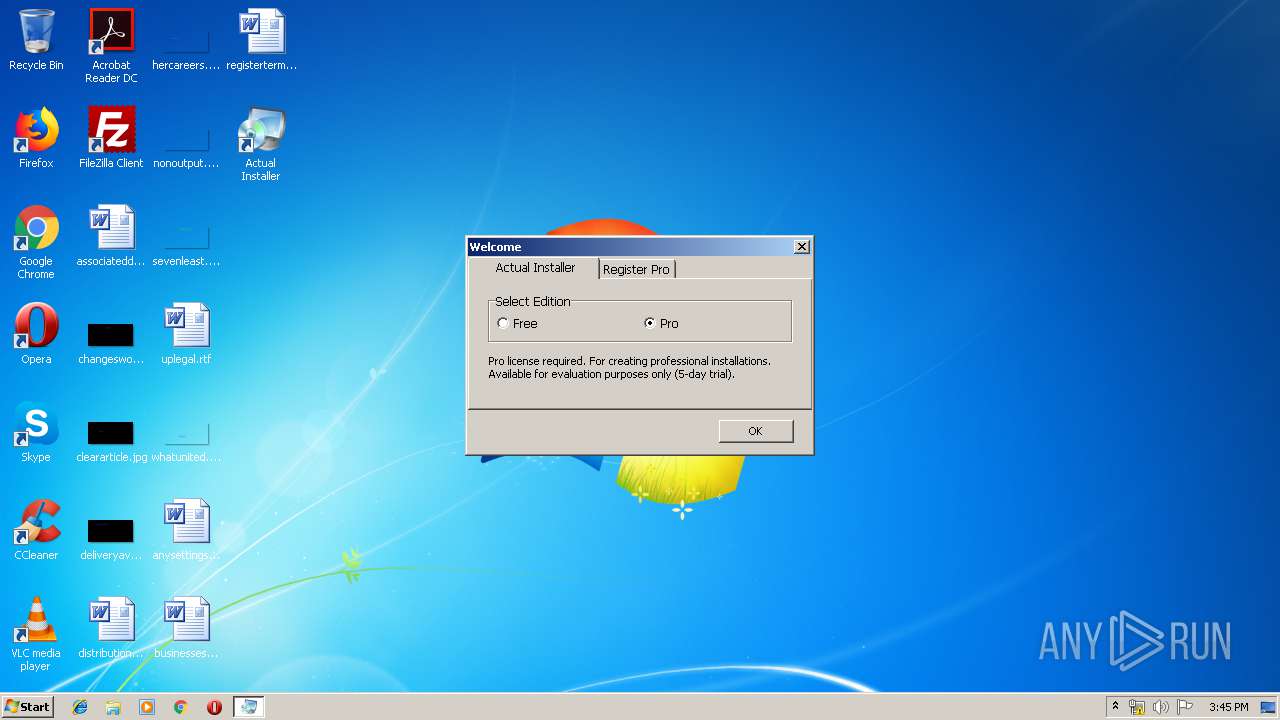
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 14:43:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 70FAC242DDB2FE635CF6EE38DE529192 |
| SHA1: | 36414486B002BBFC33F17DA2BE9BA9B73A170F8A |
| SHA256: | CBDD53ECEDFE14C3A0E993785858A9B4A3EDD37EE4FDBA23A226777432D73A72 |
| SSDEEP: | 393216:j/85fupRhRUnczfGKiSZJXTOrLZWeuoJN4qNe:j/85Wz/iYriSZJjE54qNe |
MALICIOUS
Application was dropped or rewritten from another process
- Downloader.exe (PID: 3256)
- actinst.exe (PID: 2052)
- Updater.exe (PID: 3428)
SUSPICIOUS
Reads Windows owner or organization settings
- Actual Installer Installation.exe (PID: 3340)
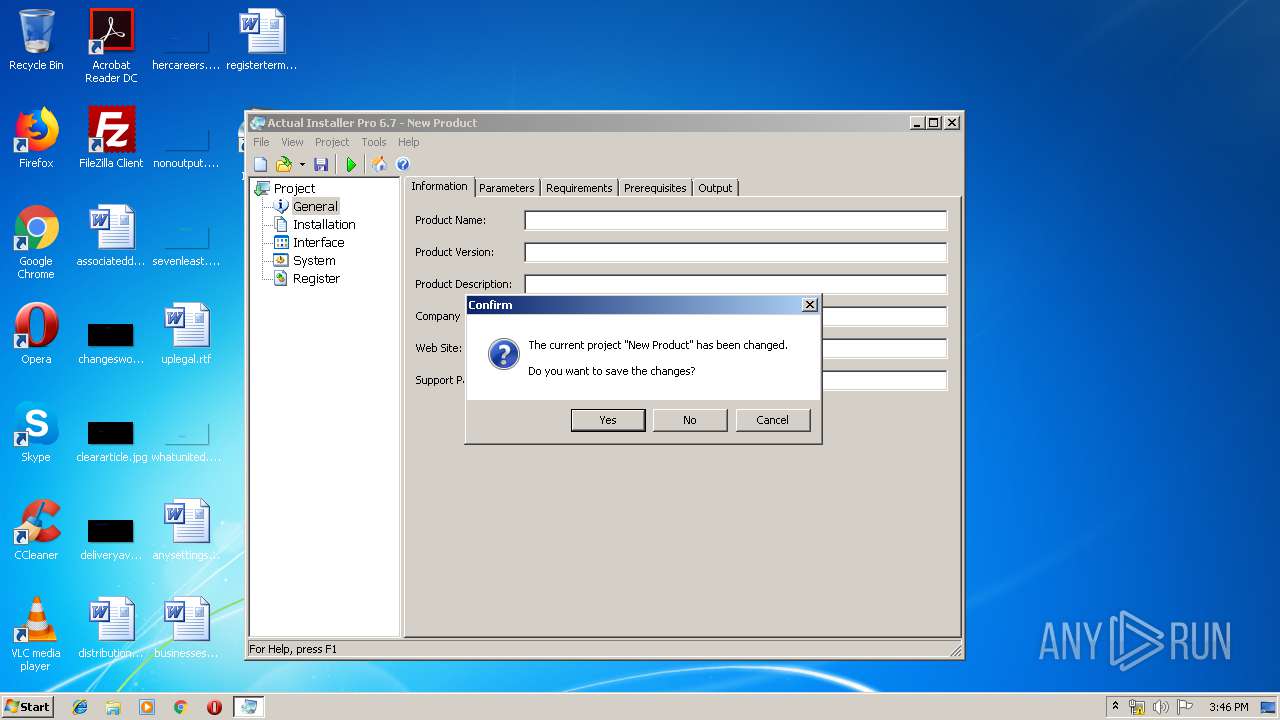
Application launched itself
- Actual Installer Installation.exe (PID: 3340)
Reads the Windows organization settings
- Actual Installer Installation.exe (PID: 3340)
Modifies the open verb of a shell class
- Actual Installer Installation.exe (PID: 3812)
Reads Environment values
- Actual Installer Installation.exe (PID: 3340)
Executable content was dropped or overwritten
- Actual Installer Installation.exe (PID: 3812)
Creates files in the program directory
- Actual Installer Installation.exe (PID: 3812)
Creates a software uninstall entry
- Actual Installer Installation.exe (PID: 3812)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (42.1) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (41.3) |
| .exe | | | Win32 Executable (generic) (7) |
| .exe | | | Win16/32 Executable Delphi generic (3.2) |
| .exe | | | Generic Win/DOS Executable (3.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:04:12 08:35:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 729088 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | 2301952 |
| EntryPoint: | 0x2e4ce0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.7.0.0 |
| ProductVersionNumber: | 6.7.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Softeza Development |
| FileDescription: | Actual Installer Installation |
| FileVersion: | 6.7 |
| LegalCopyright: | © Softeza Development |
| ProductName: | Actual Installer |
| ProductVersion: | 6.7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Apr-2017 06:35:11 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-Apr-2017 06:35:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00232000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00233000 | 0x000B2000 | 0x000B2000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92537 |
.rsrc | 0x002E5000 | 0x0002A000 | 0x00029E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.25842 |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
msvcrt.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
39
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
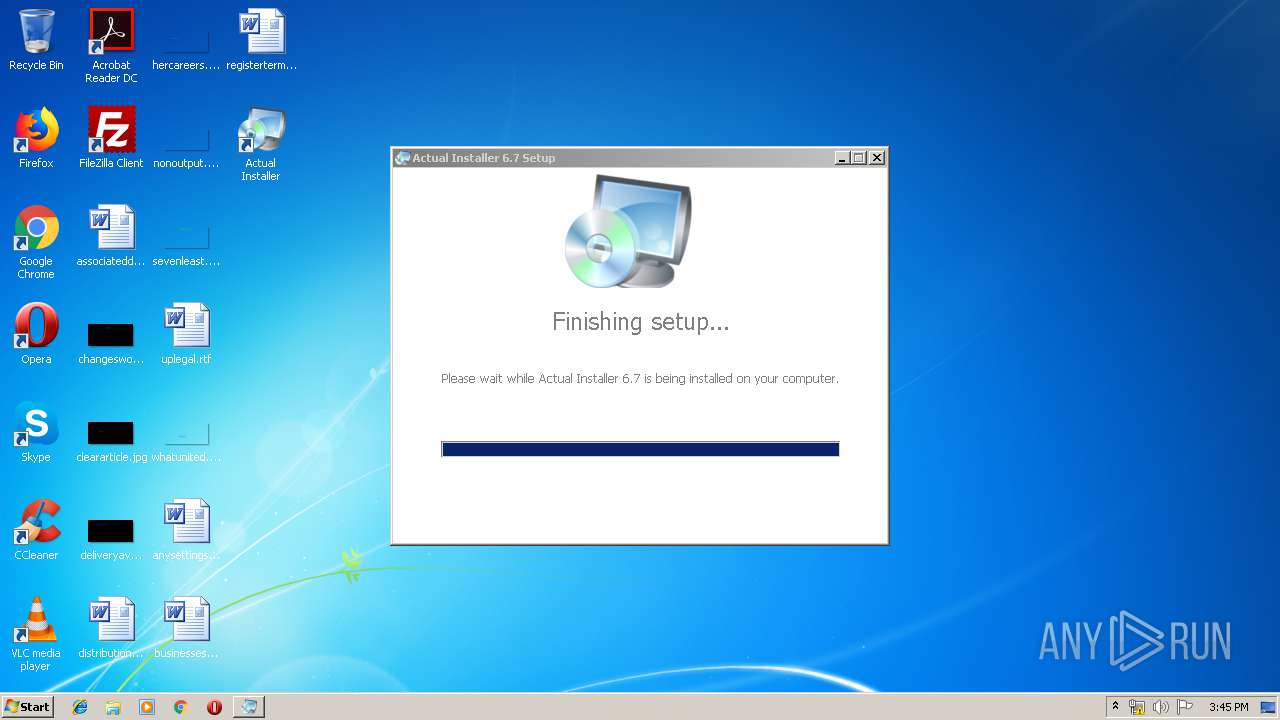
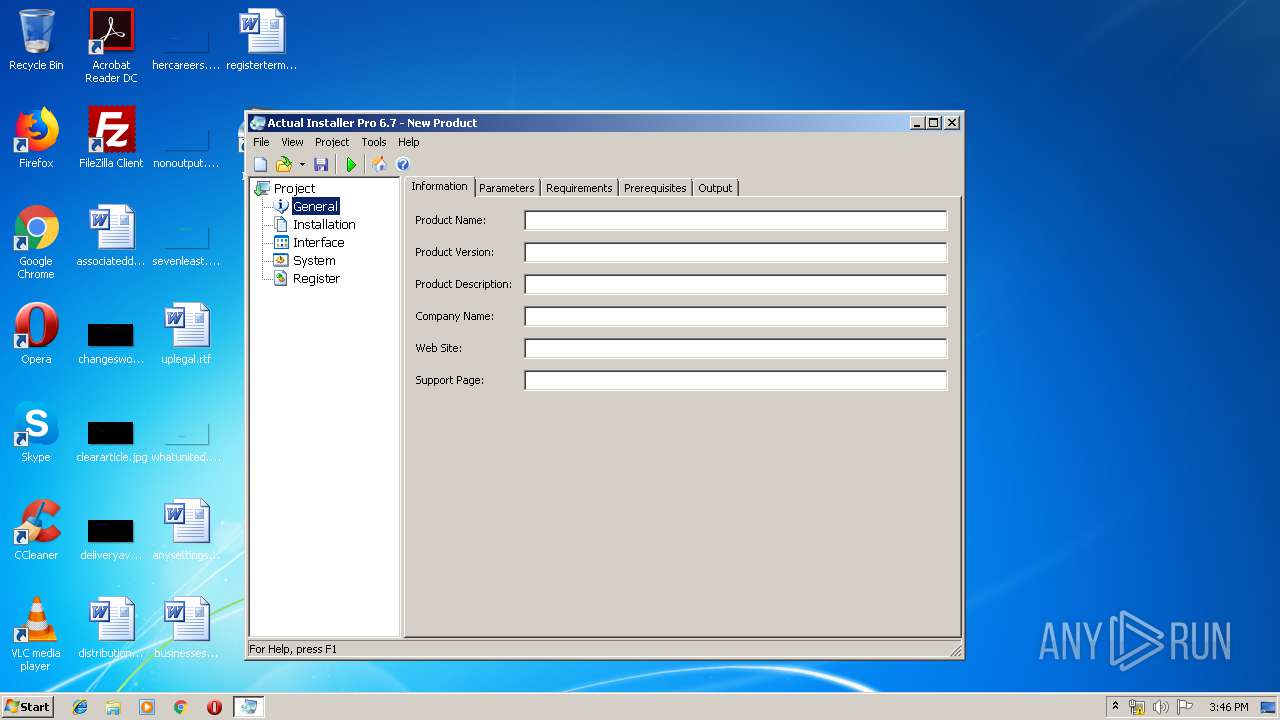
| 2052 | "C:\Program Files\Actual Installer\actinst.exe" | C:\Program Files\Actual Installer\actinst.exe | — | Actual Installer Installation.exe | |||||||||||
User: admin Company: Softeza Development Integrity Level: MEDIUM Description: Actual Installer Exit code: 0 Version: 6.7.0.0 Modules
| |||||||||||||||
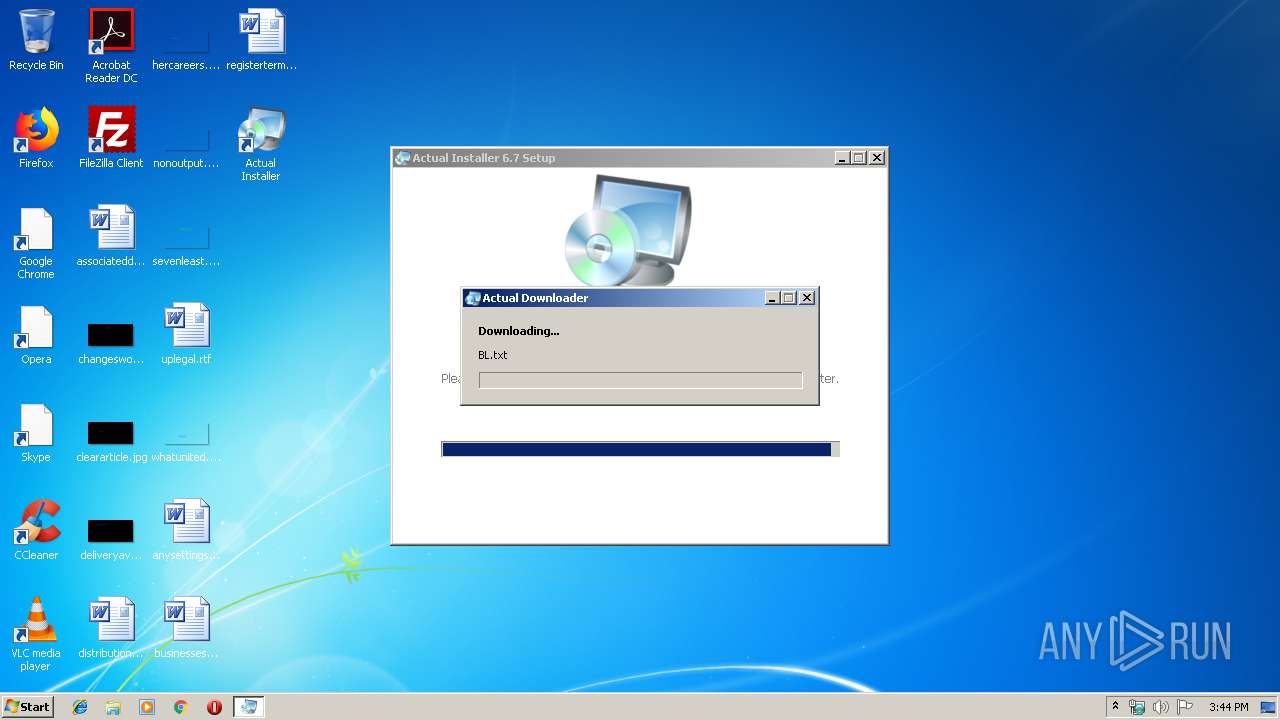
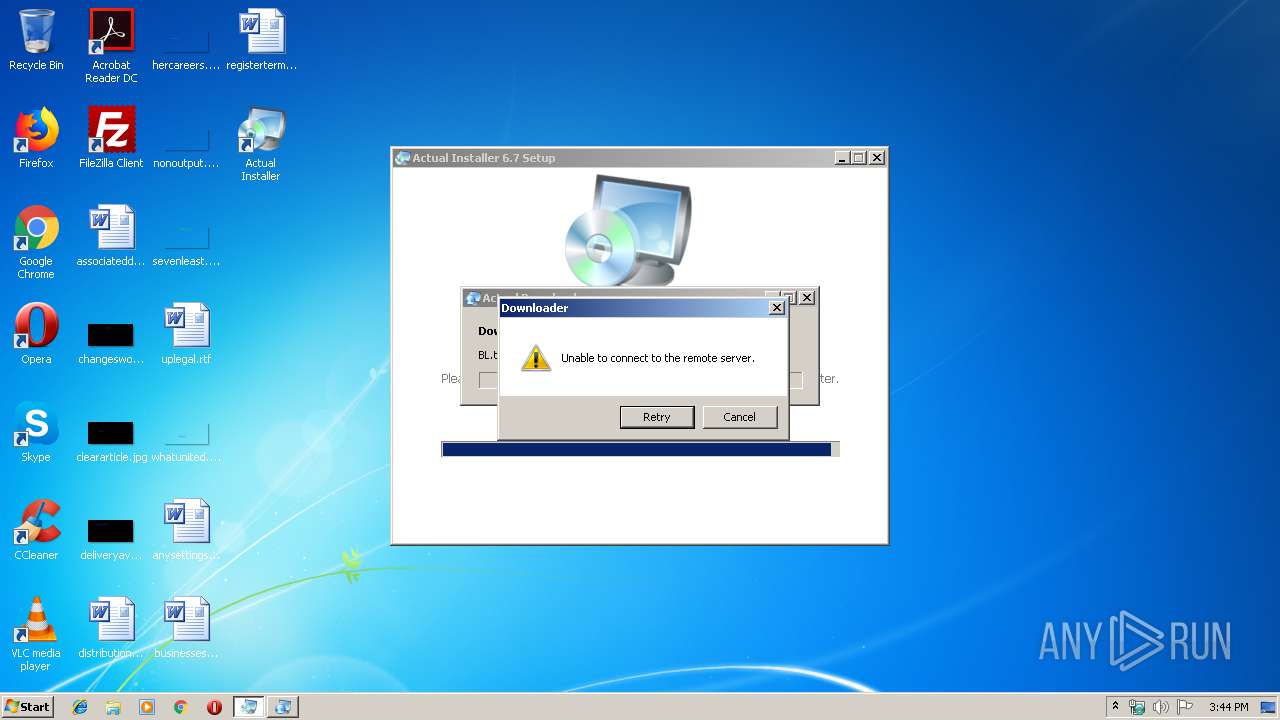
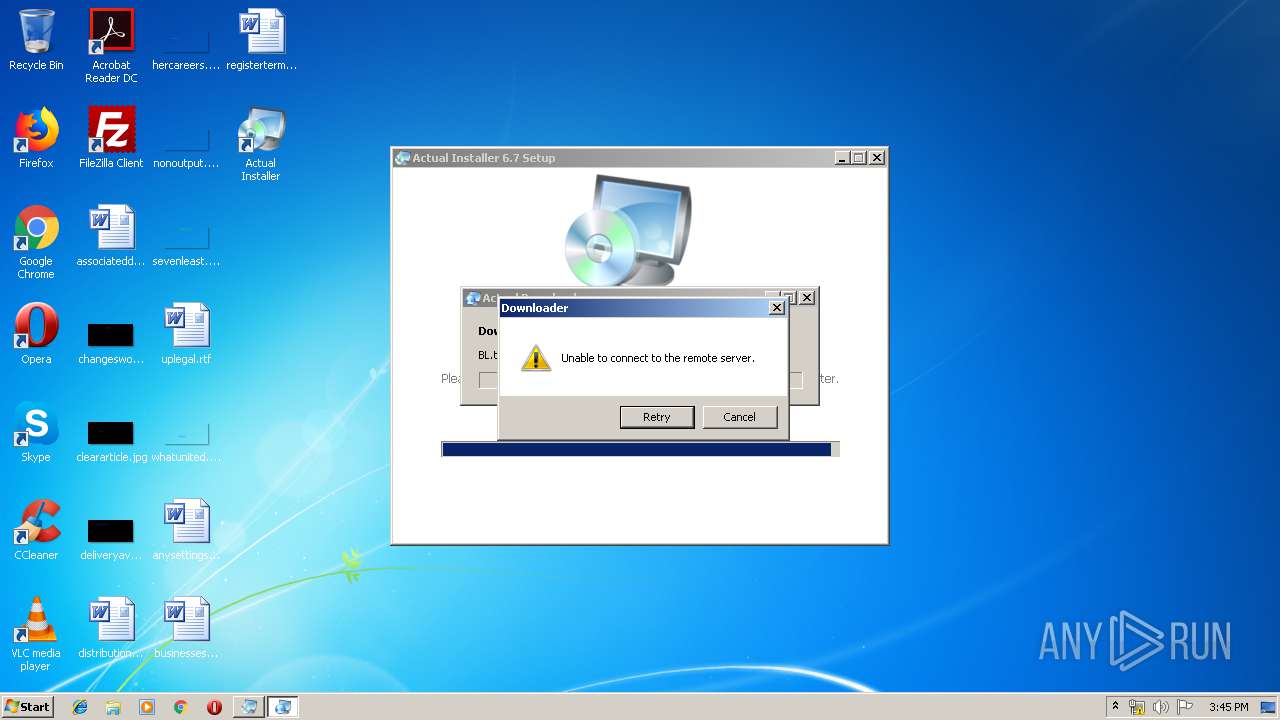
| 3256 | "C:\Program Files\Actual Installer\Downloader.exe" /S "http://www.actualinstaller.com/bl.txt" /D "C:\Program Files\Actual Installer\Data\BL.txt" | C:\Program Files\Actual Installer\Downloader.exe | Actual Installer Installation.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Actual Downloader Exit code: 2 Version: 1.6.0.0 Modules
| |||||||||||||||
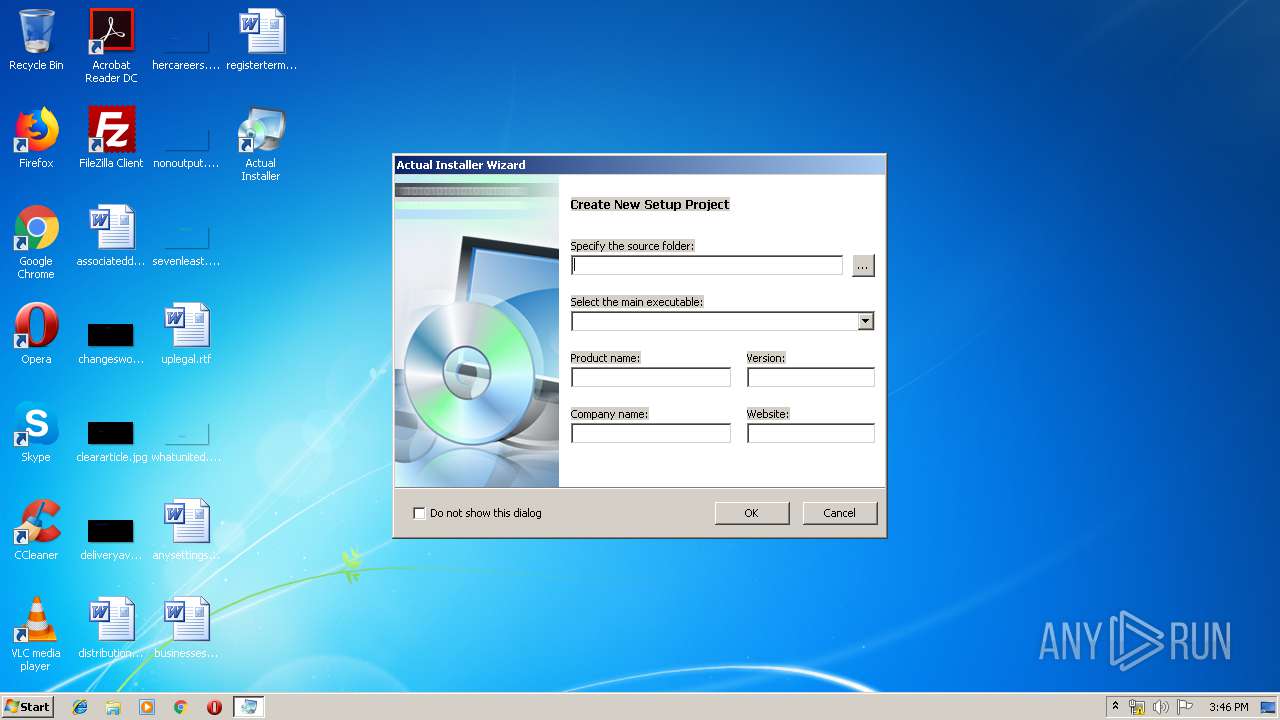
| 3340 | "C:\Users\admin\AppData\Local\Temp\Actual Installer Installation.exe" | C:\Users\admin\AppData\Local\Temp\Actual Installer Installation.exe | — | explorer.exe | |||||||||||
User: admin Company: Softeza Development Integrity Level: MEDIUM Description: Actual Installer Installation Exit code: 0 Version: 6.7 Modules
| |||||||||||||||
| 3428 | "C:\Program Files\Actual Installer\Updater.exe" /S | C:\Program Files\Actual Installer\Updater.exe | actinst.exe | ||||||||||||
User: admin Company: Softeza Development Integrity Level: MEDIUM Description: Actual Updater Exit code: 3 Version: 3.1.0.0 Modules
| |||||||||||||||
| 3812 | "C:\Users\admin\AppData\Local\Temp\Actual Installer Installation.exe" /RAD "C:\Users\admin\AppData\Local\Temp\AITMP730" | C:\Users\admin\AppData\Local\Temp\Actual Installer Installation.exe | Actual Installer Installation.exe | ||||||||||||
User: admin Company: Softeza Development Integrity Level: HIGH Description: Actual Installer Installation Exit code: 0 Version: 6.7 Modules
| |||||||||||||||
Total events
751
Read events
680
Write events
71
Delete events
0
Modification events
| (PID) Process: | (3340) Actual Installer Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3340) Actual Installer Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3812) Actual Installer Installation.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.aip |
| Operation: | write | Name: | |
Value: aipfile | |||
| (PID) Process: | (3812) Actual Installer Installation.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\aipfile |
| Operation: | write | Name: | |
Value: Actual Installer Project | |||
| (PID) Process: | (3812) Actual Installer Installation.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\aipfile\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\Actual Installer\actinst.exe,1 | |||
| (PID) Process: | (3812) Actual Installer Installation.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\aipfile\shell\open\command |
| Operation: | write | Name: | |
Value: C:\Program Files\Actual Installer\actinst.exe "%1" | |||
| (PID) Process: | (3812) Actual Installer Installation.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 57 | |||
| (PID) Process: | (3812) Actual Installer Installation.exe | Key: | HKEY_CURRENT_USER\Software\Softeza\Actual Installer\Settings |
| Operation: | write | Name: | OptionUpdateFileVersion |
Value: 1 | |||
| (PID) Process: | (3812) Actual Installer Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3812) Actual Installer Installation.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
13
Suspicious files
2
Text files
49
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3340 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\Chineseai.lng | text | |
MD5:— | SHA256:— | |||
| 3340 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\Dutchai.lng | text | |
MD5:— | SHA256:— | |||
| 3340 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\Germanai.lng | text | |
MD5:— | SHA256:— | |||
| 3340 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\Portugueseai.lng | text | |
MD5:— | SHA256:— | |||
| 3340 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\Italianai.lng | text | |
MD5:— | SHA256:— | |||
| 3340 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\Frenchai.lng | text | |
MD5:— | SHA256:— | |||
| 3340 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\Swedishai.lng | text | |
MD5:— | SHA256:— | |||
| 3340 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\Spanishai.lng | text | |
MD5:— | SHA256:— | |||
| 3340 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\aisetup.zip | compressed | |
MD5:— | SHA256:— | |||
| 3812 | Actual Installer Installation.exe | C:\Users\admin\AppData\Local\Temp\AITMP730\aidatafile.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
12
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3256 | Downloader.exe | GET | — | 184.168.19.99:80 | http://www.actualinstaller.com/bl.txt | US | — | — | suspicious |
3428 | Updater.exe | GET | 301 | 184.168.19.99:80 | http://www.actualinstaller.com/update_full.txt | US | html | 328 b | suspicious |
3256 | Downloader.exe | GET | 301 | 184.168.19.99:80 | http://www.actualinstaller.com/bl.txt | US | html | 319 b | suspicious |
3428 | Updater.exe | GET | 301 | 184.168.19.99:80 | http://www.actualinstaller.com/update_full.txt | US | html | 328 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3256 | Downloader.exe | 184.168.19.99:80 | www.actualinstaller.com | GoDaddy.com, LLC | US | suspicious |
3256 | Downloader.exe | 184.168.19.99:443 | www.actualinstaller.com | GoDaddy.com, LLC | US | suspicious |
3428 | Updater.exe | 184.168.19.99:80 | www.actualinstaller.com | GoDaddy.com, LLC | US | suspicious |
3428 | Updater.exe | 184.168.19.99:443 | www.actualinstaller.com | GoDaddy.com, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.actualinstaller.com |
| suspicious |
Threats
2 ETPRO signatures available at the full report