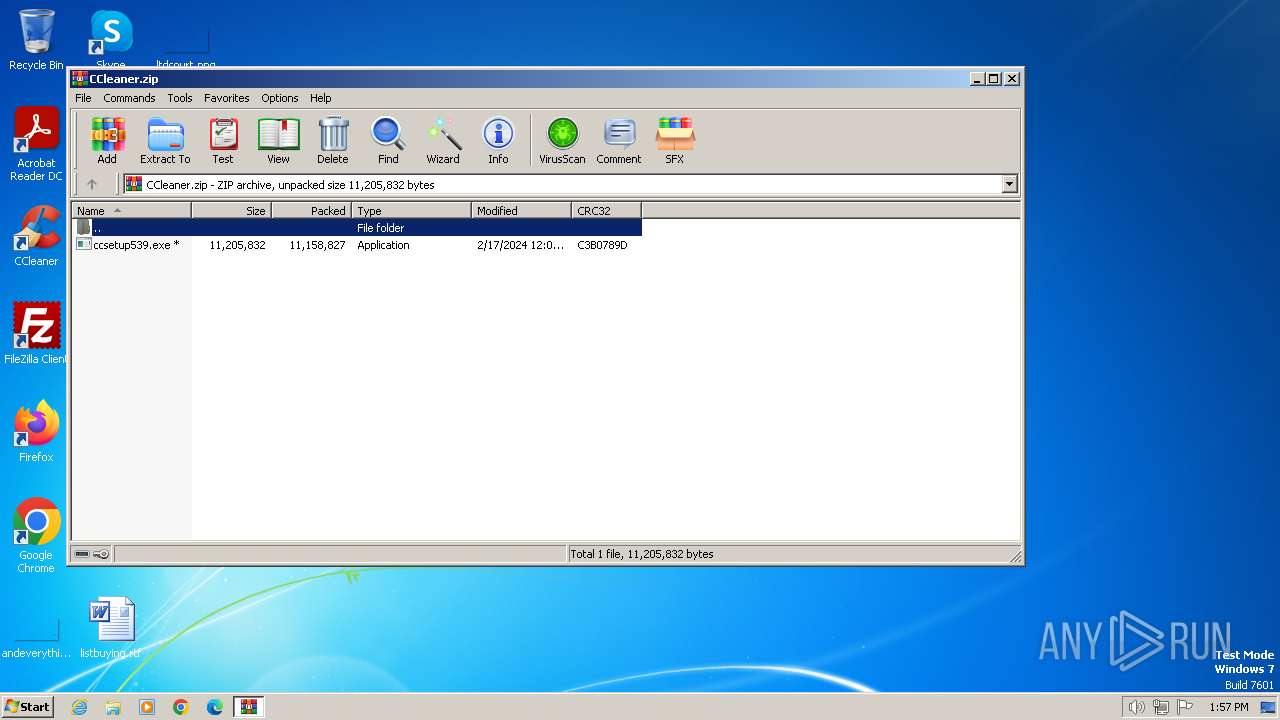
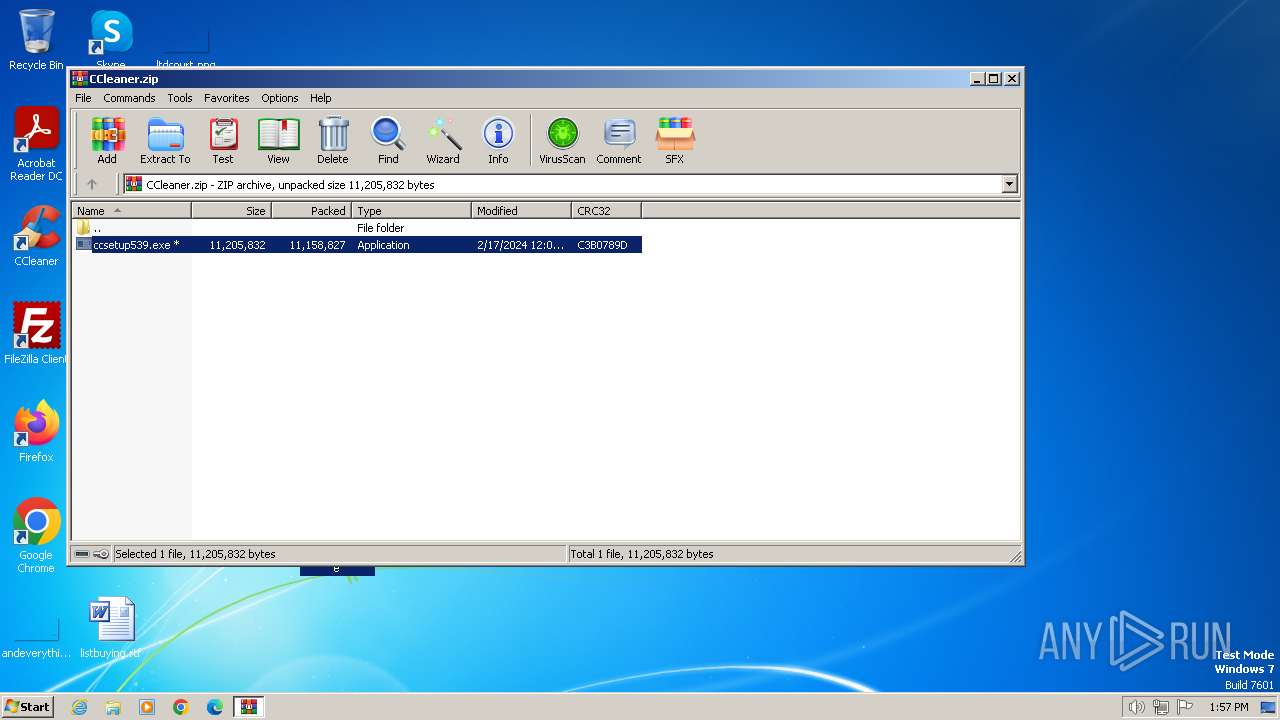
| File name: | CCleaner.zip |
| Full analysis: | https://app.any.run/tasks/d443853b-27e8-457a-92e2-a7995d2189e5 |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2024, 13:57:12 |
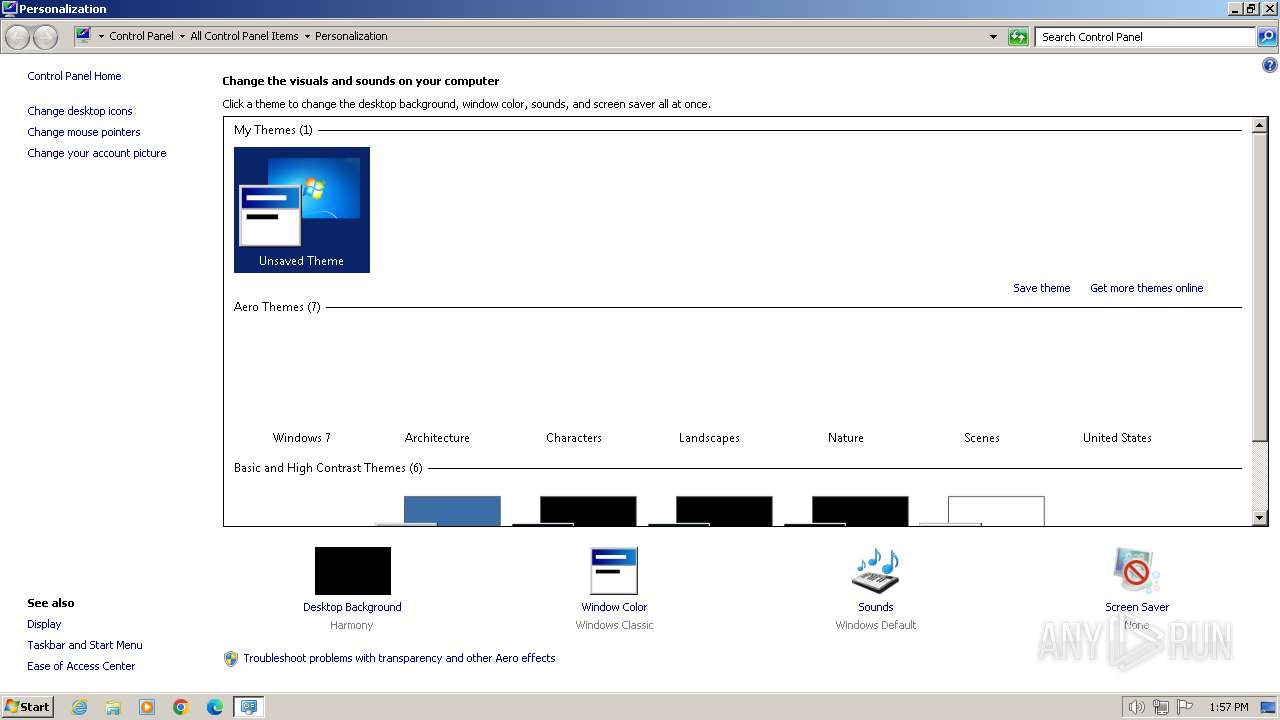
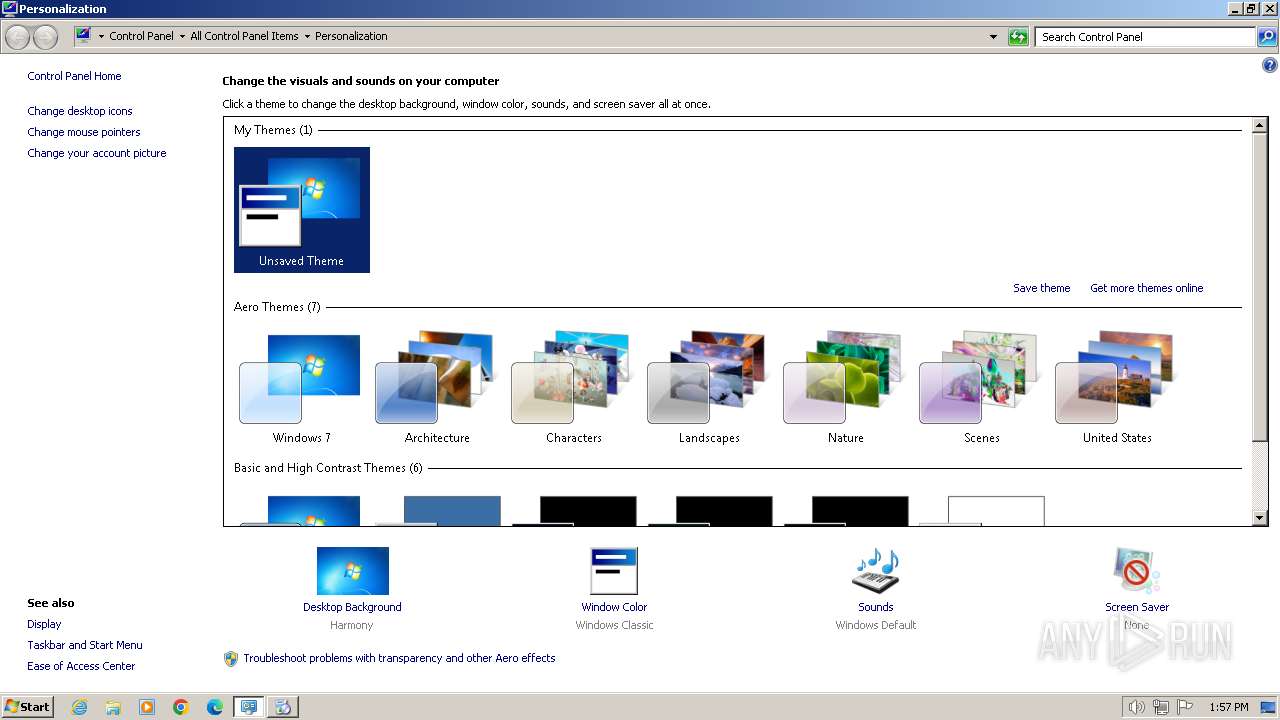
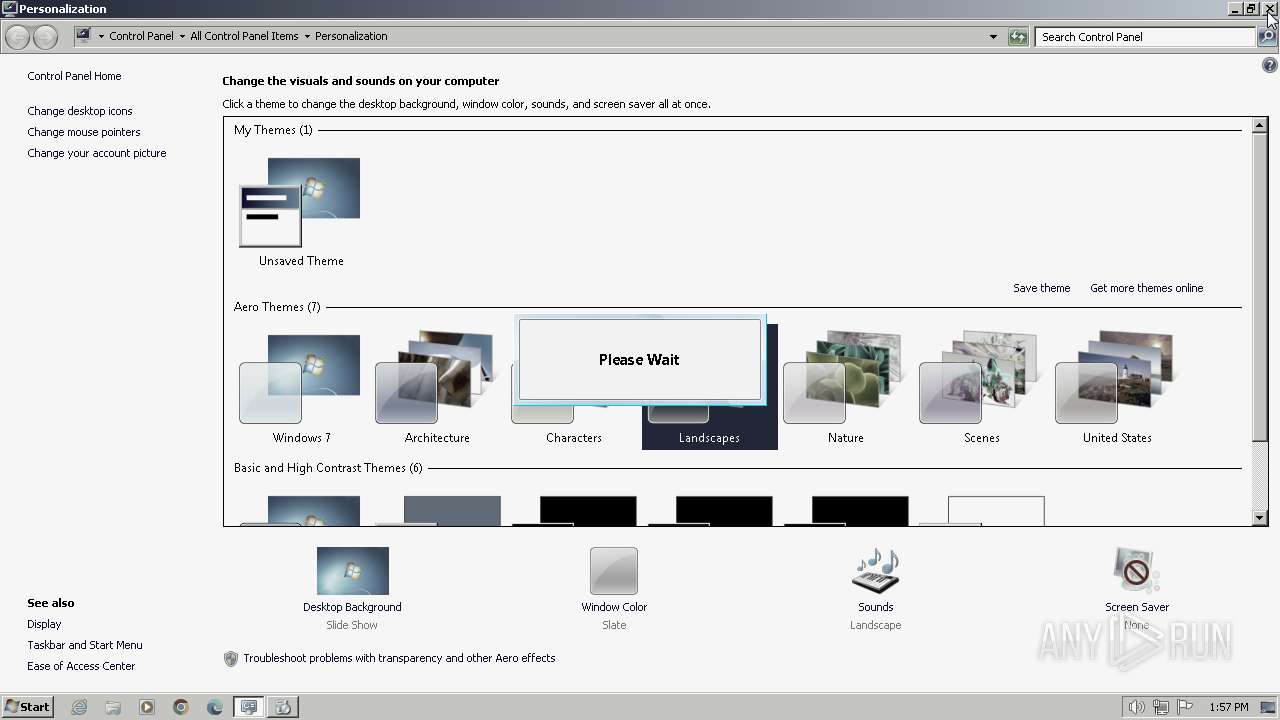
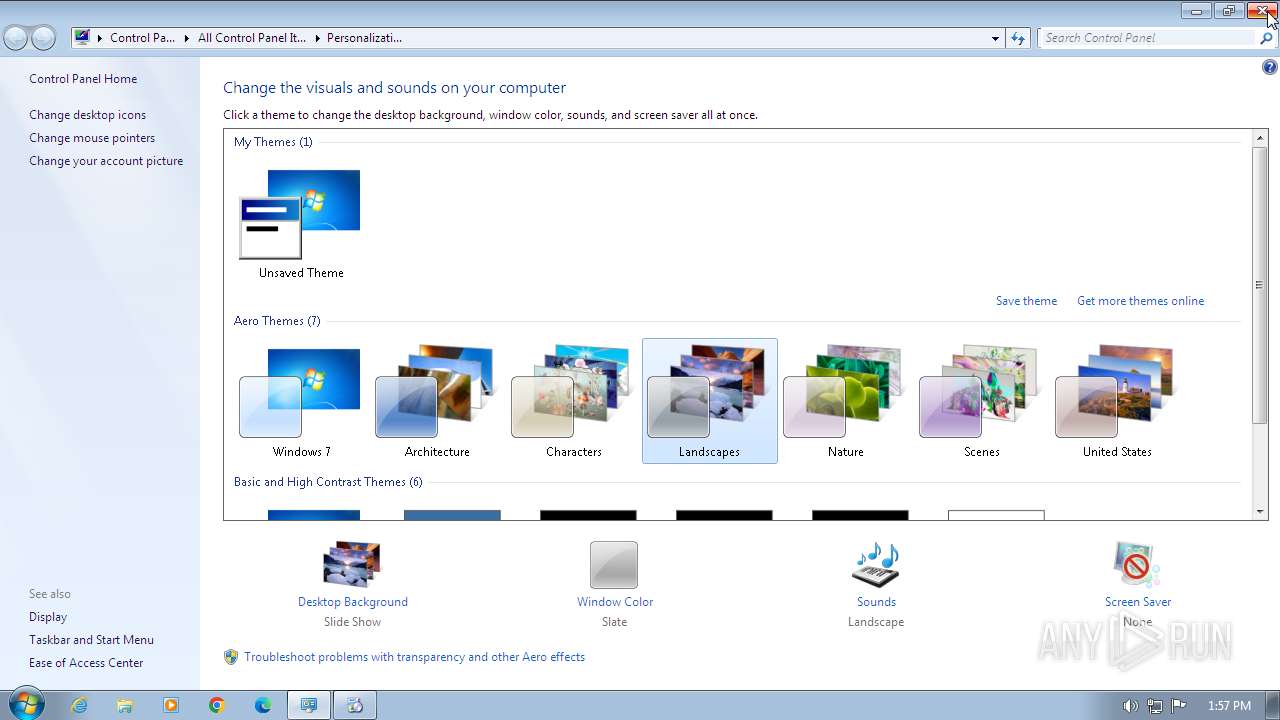
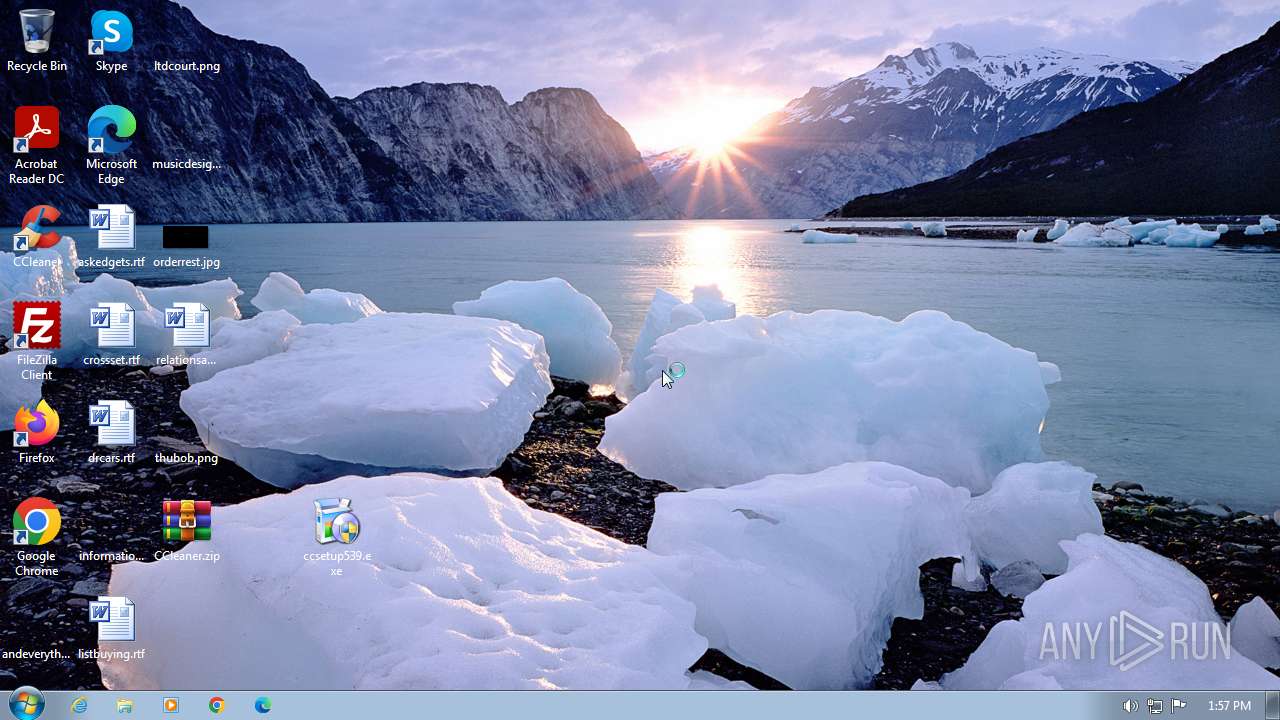
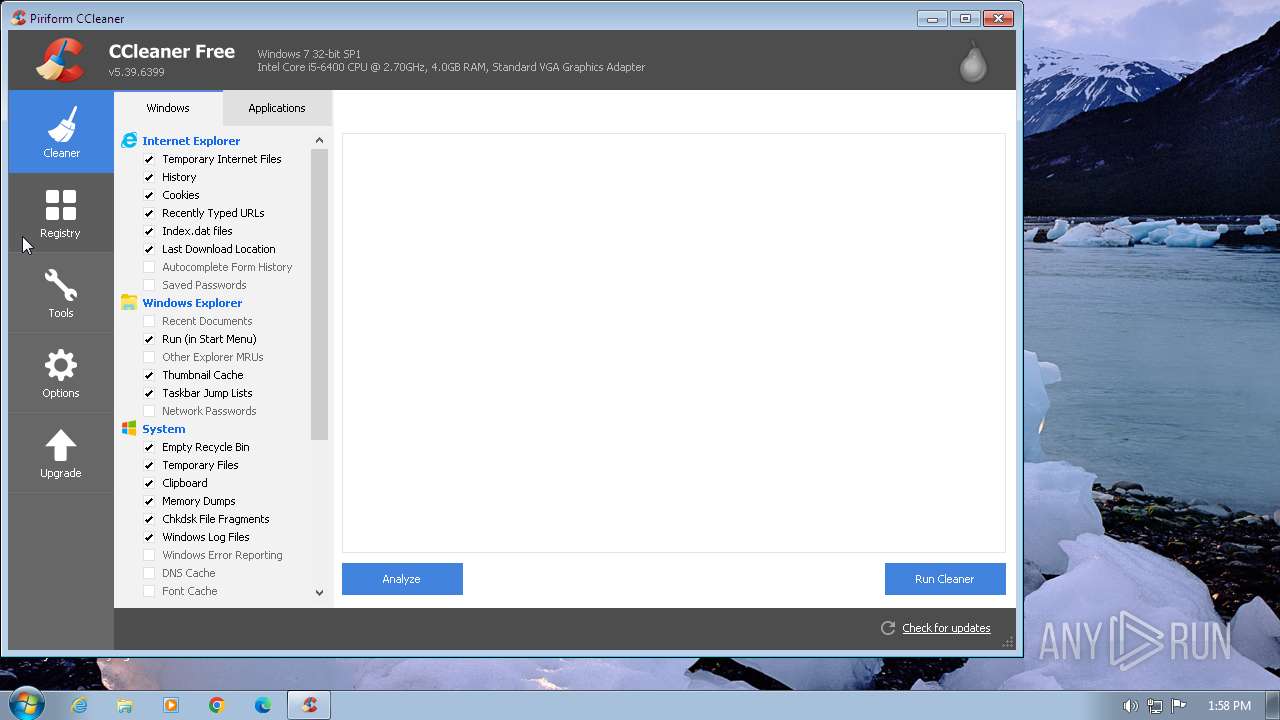
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 53F302FCB23E06EB5BF0EFD91F37366D |
| SHA1: | E157654E4AF361388A766A72A8A48AFFD984273D |
| SHA256: | CB9DB32A9FED33366AB095093D9A08BD85A6D340BAFA00CA5ED7C49ABB832631 |
| SSDEEP: | 98304:rxxsmWS8mHGNMy+2B98cDx5WhmZauHoaguGRYql9ob/6cNS6J/tpKHlTwF5Behri:tLN4t04W/wYPNmjwGFWdc73RsYxr1 |
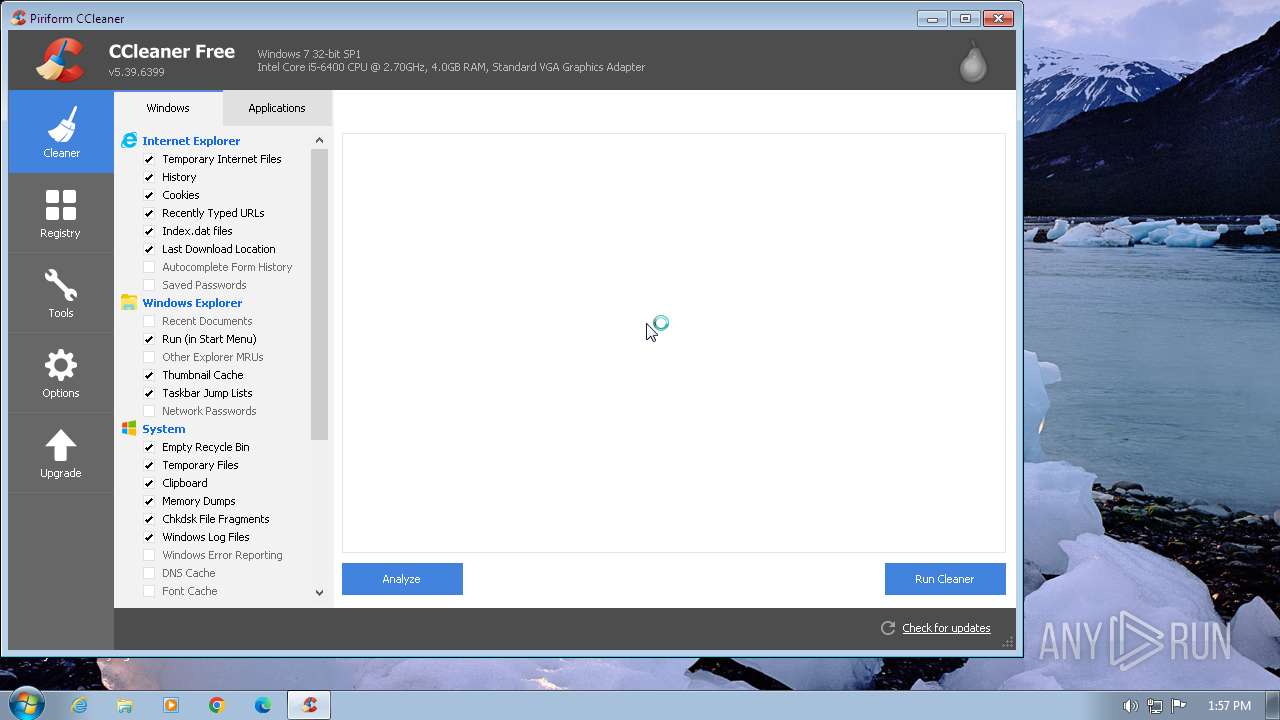
MALICIOUS
Steals credentials from Web Browsers
- taskhost.exe (PID: 2904)
- ccsetup539.exe (PID: 4008)
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
Actions looks like stealing of personal data
- ccsetup539.exe (PID: 4008)
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
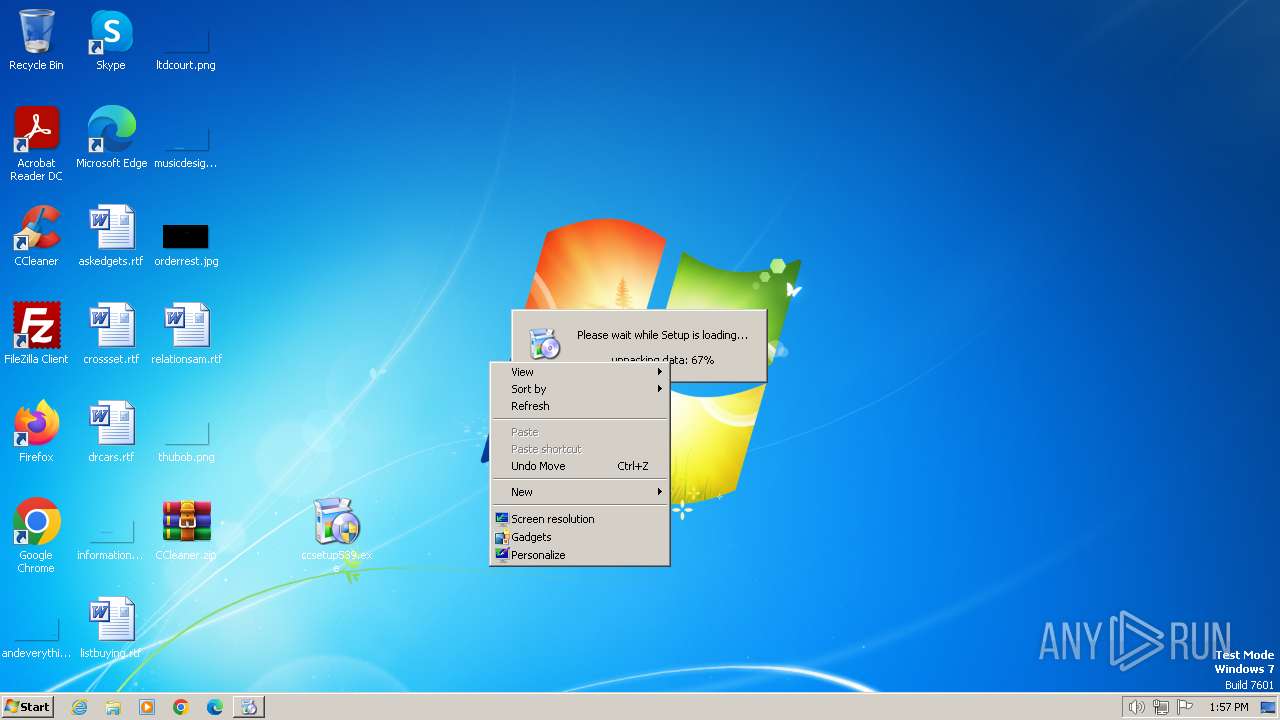
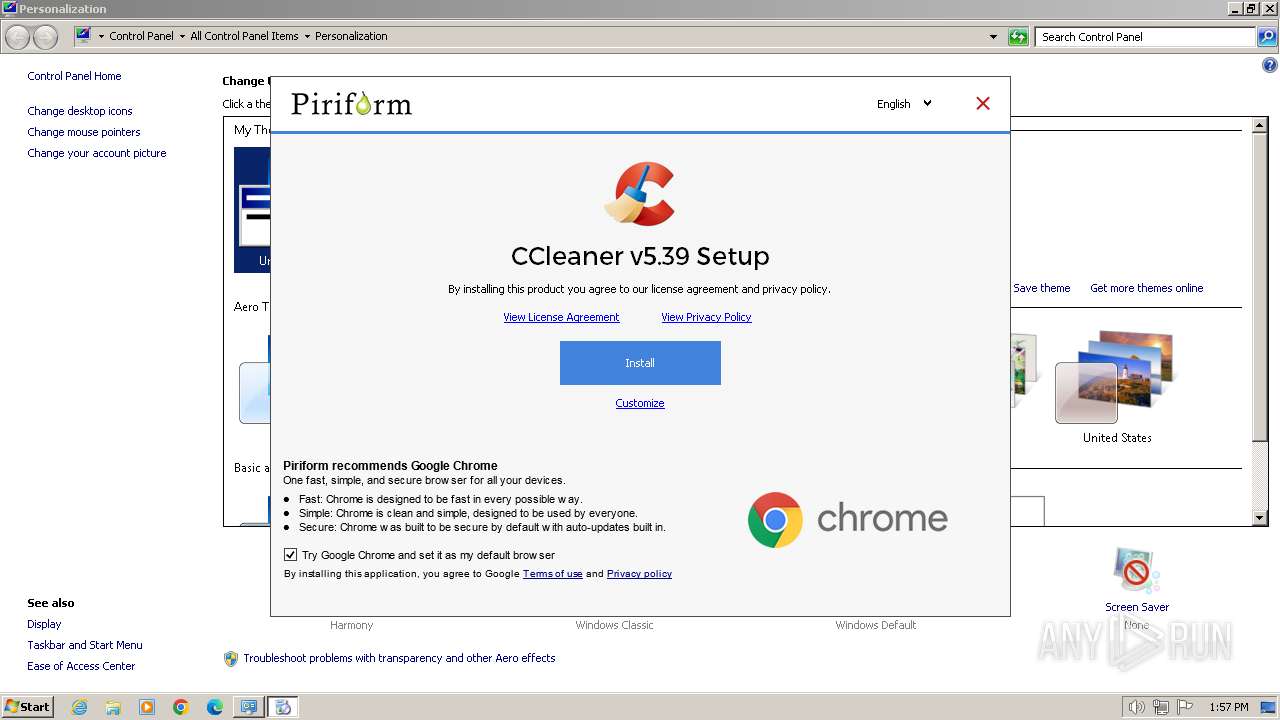
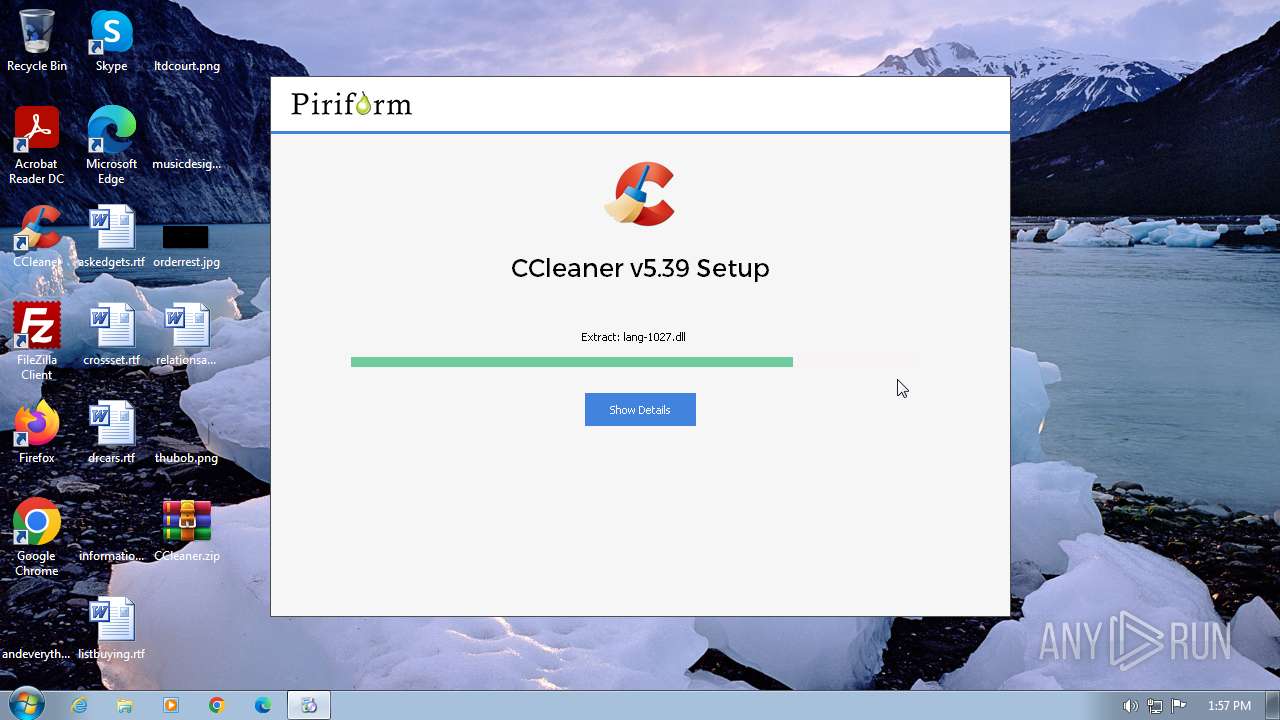
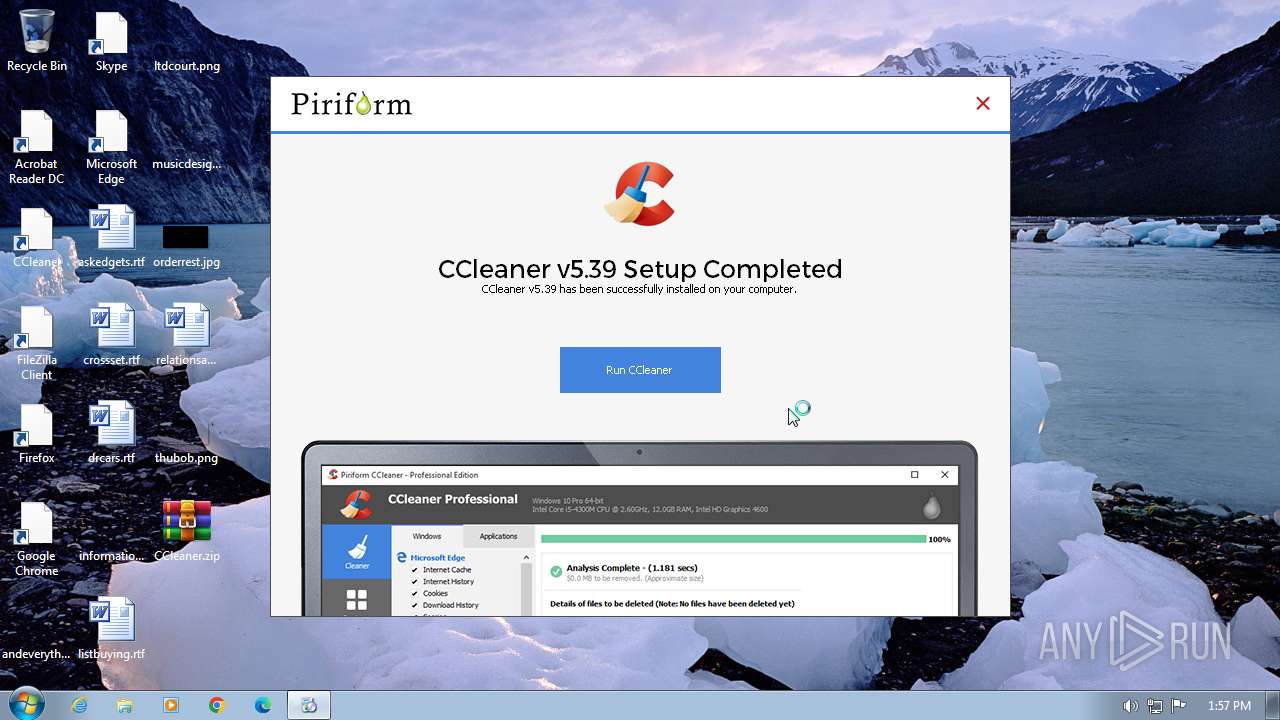
Drops the executable file immediately after the start
- ccsetup539.exe (PID: 4008)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- ccsetup539.exe (PID: 4008)
Executable content was dropped or overwritten
- ccsetup539.exe (PID: 4008)
The process creates files with name similar to system file names
- ccsetup539.exe (PID: 4008)
Starts application with an unusual extension
- ccsetup539.exe (PID: 4008)
Reads the Internet Settings
- ccsetup539.exe (PID: 4008)
- taskhost.exe (PID: 2904)
- CCUpdate.exe (PID: 480)
Non-standard symbols in registry
- ccsetup539.exe (PID: 4008)
Reads browser cookies
- ccsetup539.exe (PID: 4008)
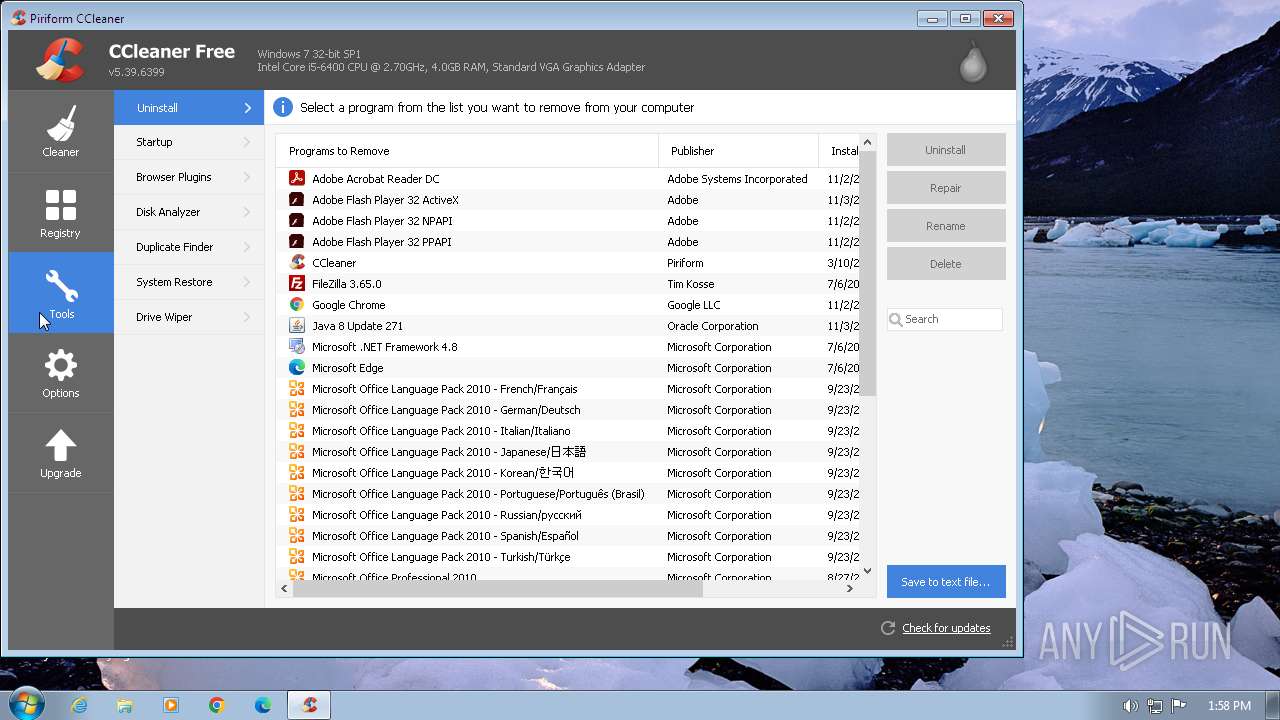
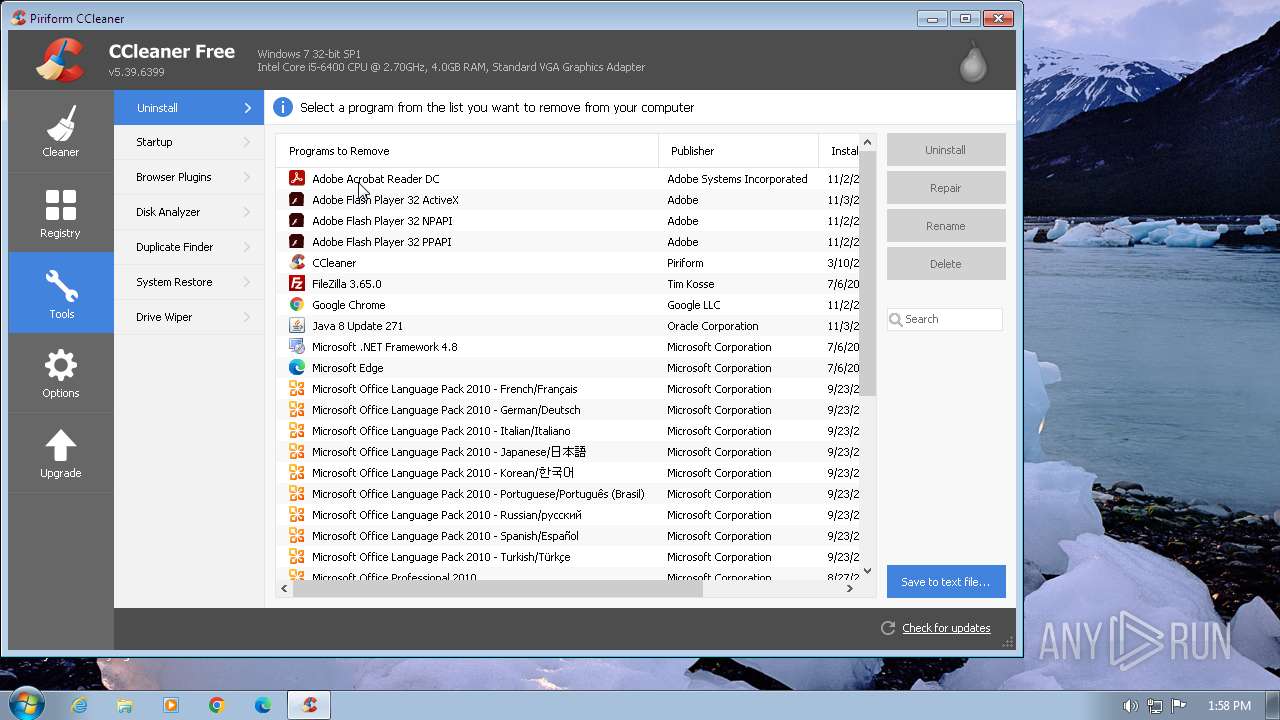
Creates a software uninstall entry
- ccsetup539.exe (PID: 4008)
Process drops legitimate windows executable
- ccsetup539.exe (PID: 4008)
Executes as Windows Service
- taskhost.exe (PID: 2904)
Process requests binary or script from the Internet
- ccsetup539.exe (PID: 4008)
The process verifies whether the antivirus software is installed
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
Reads the date of Windows installation
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
Reads Internet Explorer settings
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
- ccsetup539.exe (PID: 4008)
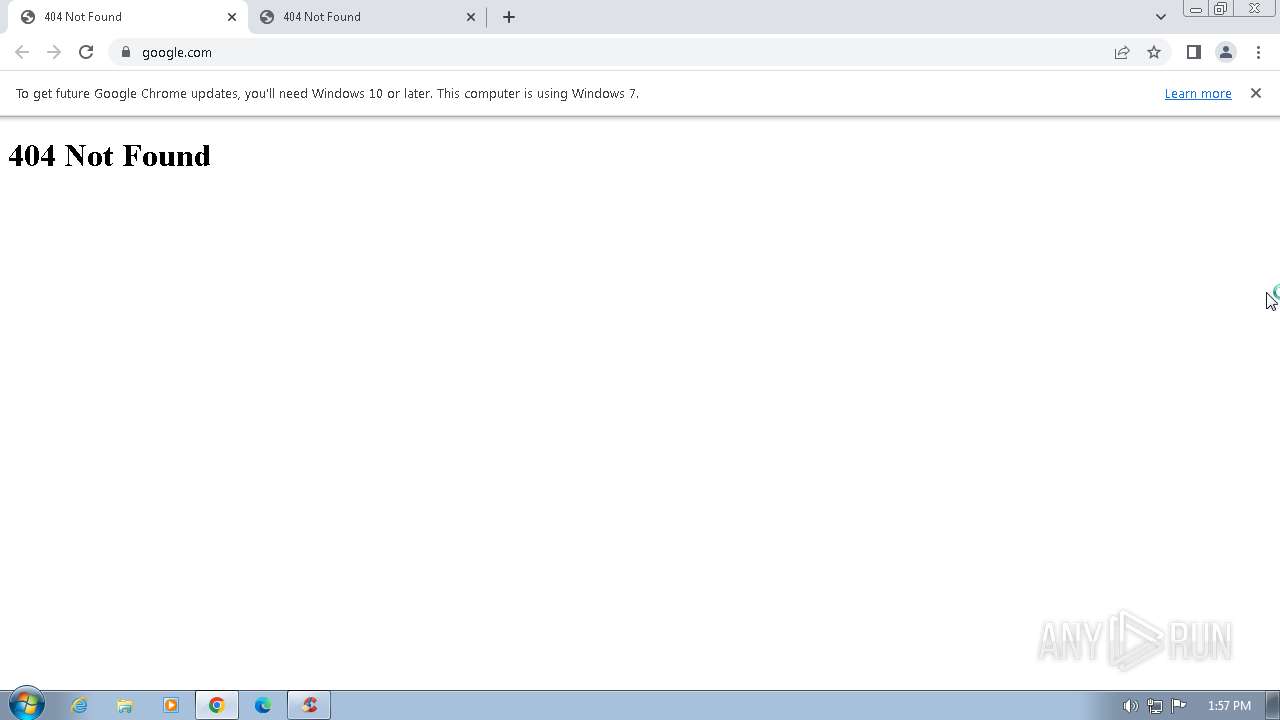
Checks for external IP
- CCUpdate.exe (PID: 480)
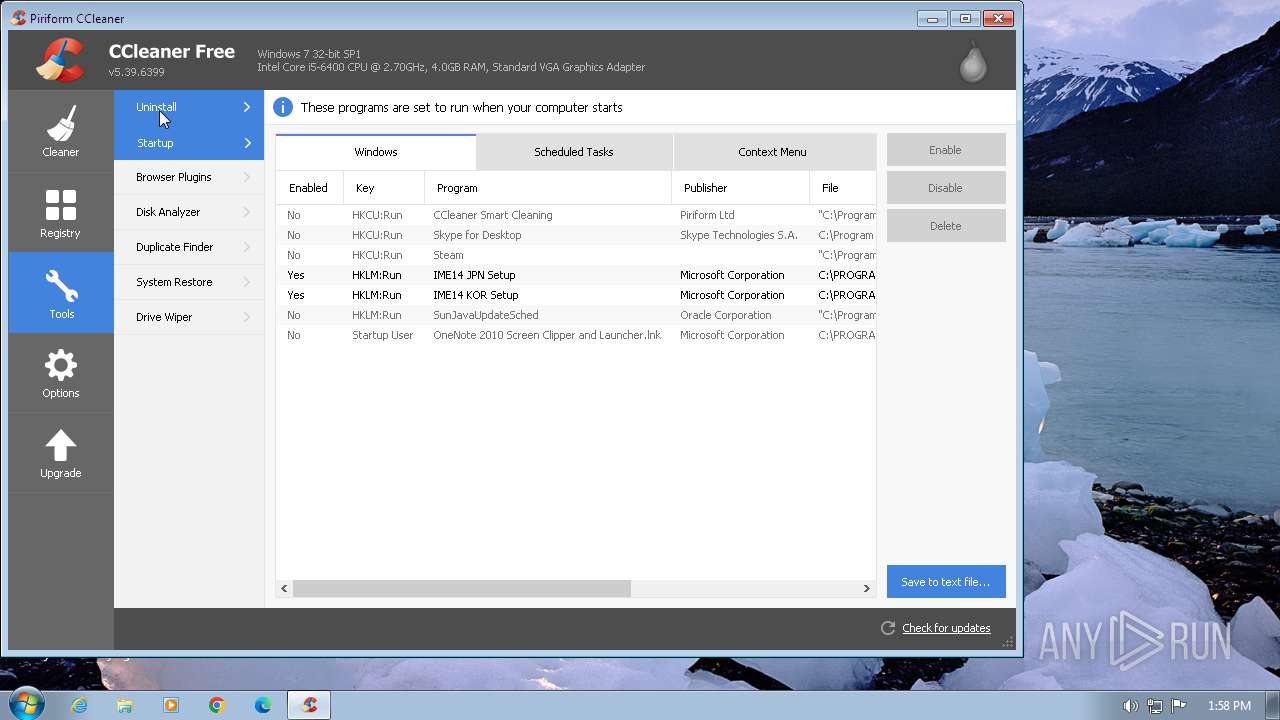
The process executes via Task Scheduler
- CCleaner.exe (PID: 2864)
Searches for installed software
- CCleaner.exe (PID: 2864)
Reads security settings of Internet Explorer
- ccsetup539.exe (PID: 4008)
Reads Microsoft Outlook installation path
- ccsetup539.exe (PID: 4008)
INFO
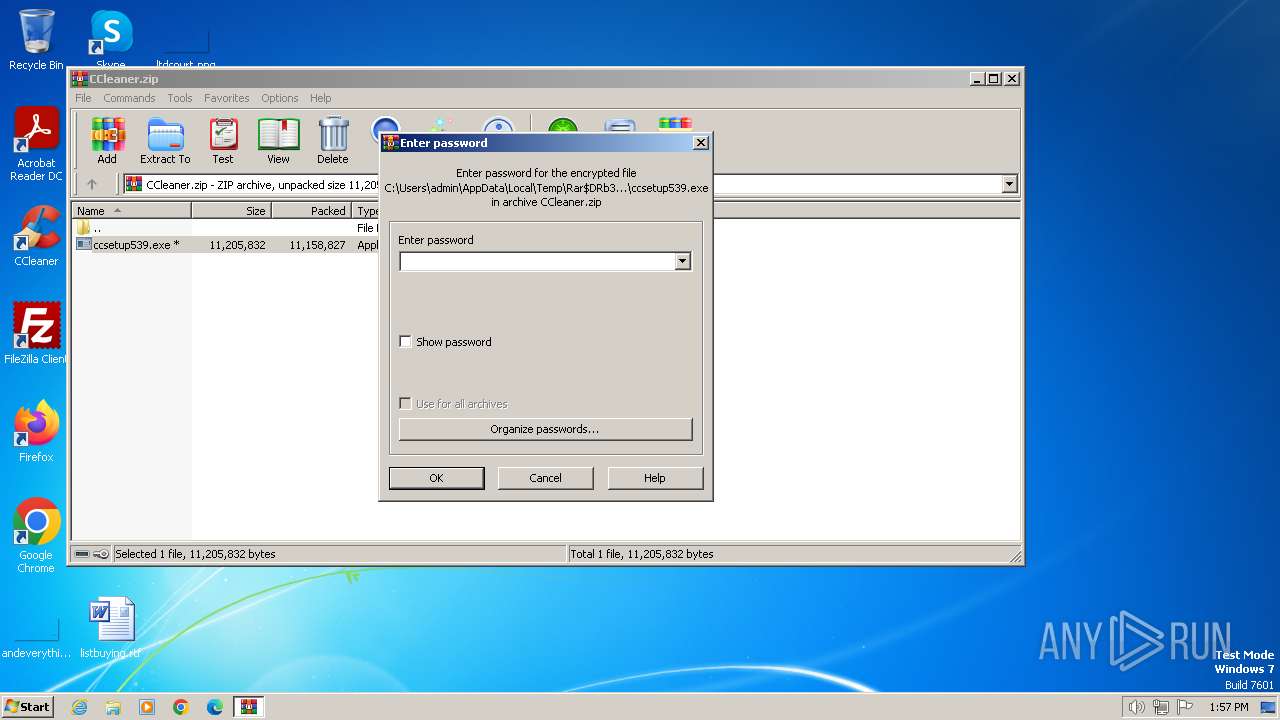
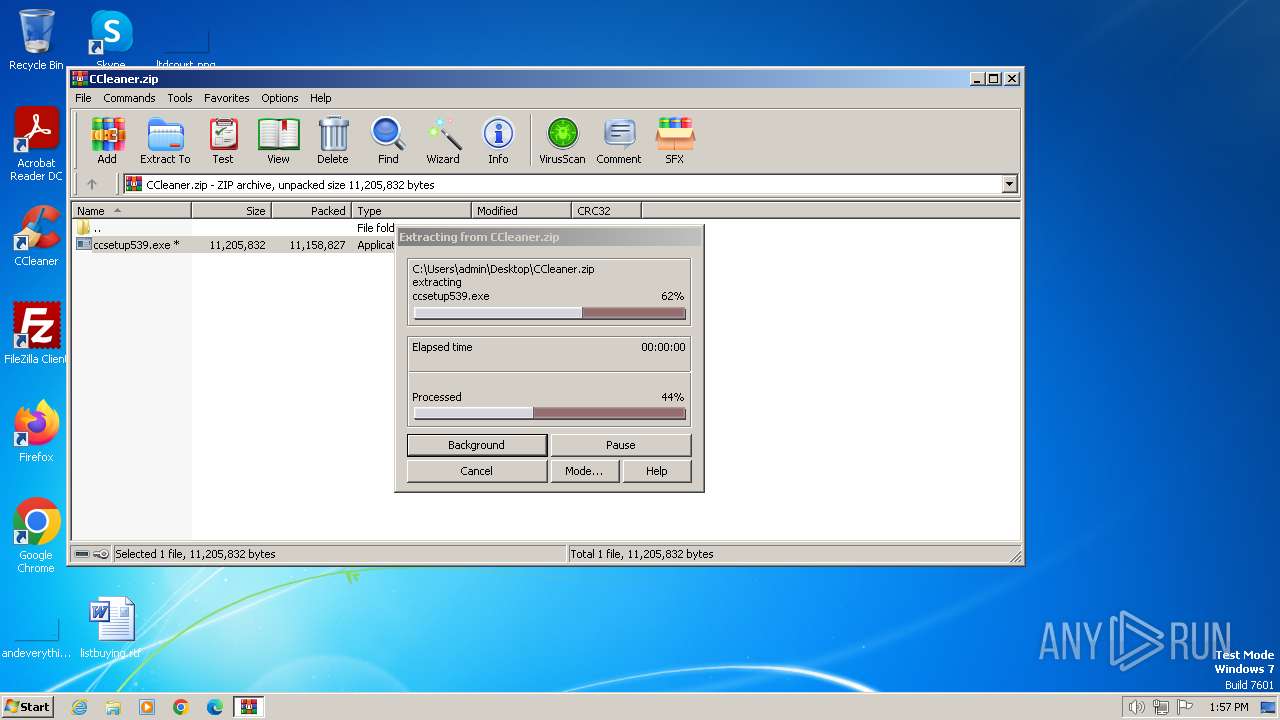
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3864)
Checks supported languages
- ccsetup539.exe (PID: 4008)
- ns320A.tmp (PID: 3996)
- ns42C5.tmp (PID: 1900)
- CCleaner.exe (PID: 1484)
- CCUpdate.exe (PID: 480)
- CCleaner.exe (PID: 3764)
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
Reads the computer name
- ccsetup539.exe (PID: 4008)
- CCUpdate.exe (PID: 480)
- CCleaner.exe (PID: 1484)
- CCleaner.exe (PID: 3764)
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3864)
Manual execution by a user
- ccsetup539.exe (PID: 4008)
- ccsetup539.exe (PID: 3944)
- CCleaner.exe (PID: 3764)
Create files in a temporary directory
- ccsetup539.exe (PID: 4008)
Reads the machine GUID from the registry
- ccsetup539.exe (PID: 4008)
- CCUpdate.exe (PID: 480)
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
Reads Environment values
- ccsetup539.exe (PID: 4008)
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
Creates files or folders in the user directory
- ccsetup539.exe (PID: 4008)
- taskhost.exe (PID: 2904)
Reads product name
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
Reads CPU info
- CCleaner.exe (PID: 2480)
- CCleaner.exe (PID: 2864)
Application launched itself
- chrome.exe (PID: 2640)
Checks proxy server information
- ccsetup539.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:02:16 19:05:44 |
| ZipCRC: | 0xc3b0789d |
| ZipCompressedSize: | 11158827 |
| ZipUncompressedSize: | 11205832 |
| ZipFileName: | ccsetup539.exe |
Total processes
72
Monitored processes
24
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\CCleaner\CCUpdate.exe" /reg | C:\Program Files\CCleaner\CCUpdate.exe | ccsetup539.exe | ||||||||||||
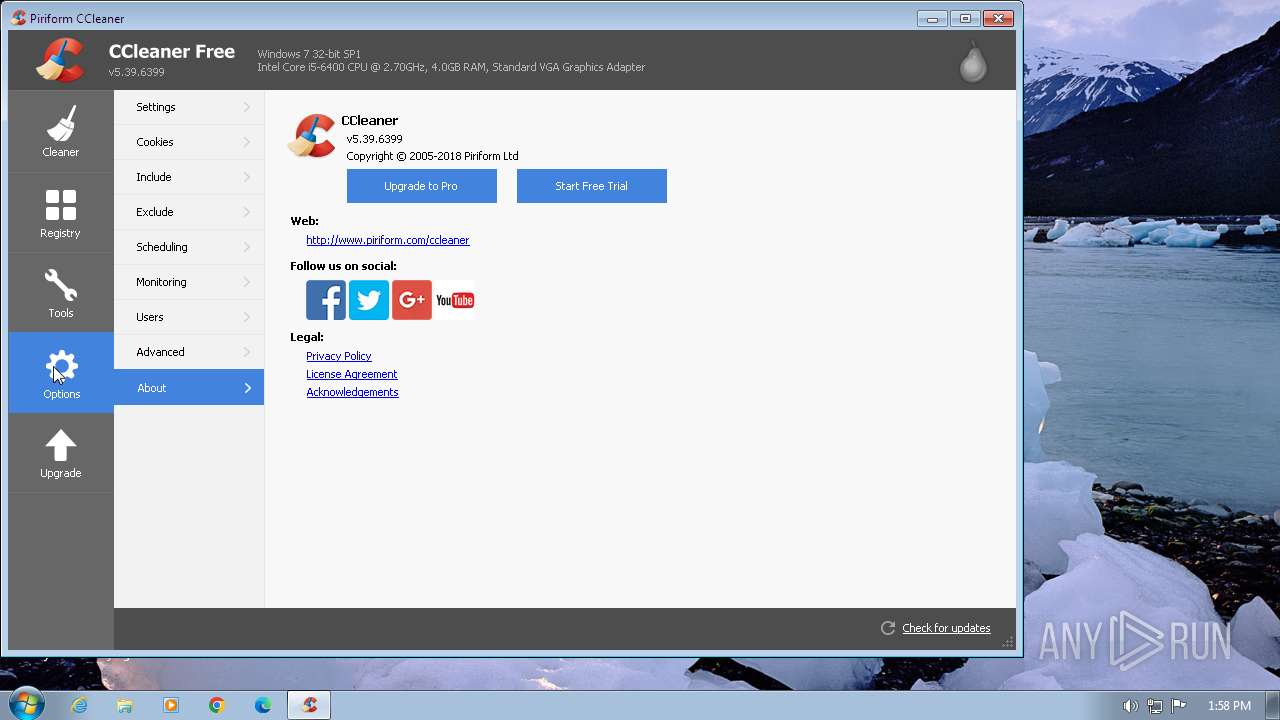
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner emergency updater Exit code: 1460 Version: 18.1.183.0 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a138b38,0x6a138b48,0x6a138b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\CCleaner\CCleaner.exe" /createSkipUAC 6.14.10584 | C:\Program Files\CCleaner\CCleaner.exe | — | ccsetup539.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5.39.108.6399 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1468 --field-trial-handle=1188,i,6400423058189900172,16594855907852413787,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1900 | "C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\ns42C5.tmp" ping -n 1 -w 5000 www.piriform.com | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\ns42C5.tmp | — | ccsetup539.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2180 --field-trial-handle=1188,i,6400423058189900172,16594855907852413787,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1440 --field-trial-handle=1188,i,6400423058189900172,16594855907852413787,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | ccsetup539.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5.39.108.6399 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --new-window "http://www.google.com" "http://www.piriform.com/go/app_releasenotes?p=1&v=5.39.6399&l=1033&b=1&a=0" | C:\Program Files\Google\Chrome\Application\chrome.exe | ccsetup539.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3536 --field-trial-handle=1188,i,6400423058189900172,16594855907852413787,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
33 578
Read events
33 314
Write events
241
Delete events
23
Modification events
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\CCleaner.zip | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3864) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
132
Suspicious files
26
Text files
82
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\System.dll | executable | |
MD5:41A3C964232EDD2D7D5EDEA53E8245CD | SHA256:8B65FEC615C7B371C23F8F7F344B12DC5085E40A556F96DB318ED757494D62D5 | |||
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\g\gcombo\ComboOffer_1031.html | html | |
MD5:7BFEF739A458A6C54378FC4EEAB2E30D | SHA256:4786ECF1484B6D5463D31B57EA4B6314906C2F81ADC99B7145B5770140921868 | |||
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\g\gcombo\ComboOffer_1036.html | html | |
MD5:C69DA1C2761D758F92603D59F4ADDB28 | SHA256:4BD2DFB0D9D60F7B83942D8F43A45597BBBBA427359FE5497267BDC87B17C904 | |||
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\g\gtapi_signed.dll | executable | |
MD5:61BC40D1FAD9E0FAA9A07219B90BA0E4 | SHA256:89E157A4F61D7D18180CB7F901C0095DA3B7A5CC5A9FD58D710099E5F0EE505A | |||
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\g\gcombo\ComboOffer_1033.html | html | |
MD5:016F10E3840423FD75A776923AA3E57D | SHA256:C89B3683C75B641526524E2397D9BEB24F5BBD0D813D60CEB2B5B8896AE17659 | |||
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\g\gcombo\ComboOffer_1026.html | html | |
MD5:31F4AFA1E87F0243C43B0203B89D50B1 | SHA256:34C5182D004DF6016042423E040A79F597E9286F5F75F38C0A821FC06494C702 | |||
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\g\gcombo\ComboOffer_1030.html | html | |
MD5:74FB5C6592947C542FD036FE1D332AAF | SHA256:63B9E98CBD2CA35590318A0307145A5BC541CAC4E06EF93D6C0095E5692E5172 | |||
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\g\gcombo\ComboOffer_1025.html | html | |
MD5:3876777E8E7B73A9A1113402FE54ACA9 | SHA256:06EE0D941530D5BF86009E7DF0D15DD5767BE6DDA2F955F2AEDBD220EDB261B6 | |||
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\g\gcombo\ComboOffer_1035.html | html | |
MD5:9CB61E718D2C7B5E4BE6D44F871EF640 | SHA256:2940229BC3044B84FA8F613A071AFEEAD25BDA3FCB2D598506CAA43128398B06 | |||
| 4008 | ccsetup539.exe | C:\Users\admin\AppData\Local\Temp\nsf27A9.tmp\g\gcombo\ComboOffer_1038.html | html | |
MD5:7F6619F86770AE2DD1D8184E8CD95757 | SHA256:98975EA1660FD6C28BA74F5ED6B1491294ABBE13D11E54D21DB4FBEBE162E359 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
19
DNS requests
23
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4008 | ccsetup539.exe | GET | 404 | 23.215.23.231:80 | http://service.piriform.com/installcheck.aspx?p=1&v=5.39.6399&vx=6.14.10584&l=1033&b=1&o=6.1W3&g=9&i=1&a=0&e=0&n=ccsetup539.exe&id=003&mk=IH82-8AEJ-BB4F-FSU3-EWAI-2TTB-7NKN-5AZH-HZ8S&mx=97B7721C4994E2556FF6A439510F665DF3233A637833016FDA6B2D652A6FC9CD&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | unknown | xml | 341 b | unknown |
480 | CCUpdate.exe | GET | 404 | 104.124.11.59:80 | http://emupdate.avcdn.net/files/emupdate/pong.txt | unknown | xml | 341 b | unknown |
480 | CCUpdate.exe | GET | 404 | 34.149.149.62:80 | http://ip-info.ff.avast.com/v2/info | unknown | xml | 341 b | unknown |
480 | CCUpdate.exe | GET | 404 | 104.124.11.59:80 | http://emupdate.avcdn.net/files/emupdate/pong.txt | unknown | xml | 341 b | unknown |
480 | CCUpdate.exe | GET | 404 | 104.124.11.59:80 | http://emupdate.avcdn.net/files/emupdate/pong.txt | unknown | xml | 341 b | unknown |
— | — | GET | 404 | 49.13.77.253:443 | https://49.13.77.253/chrome-variations/seed?osname=win&channel=stable&milestone=109 | unknown | — | 341 b | unknown |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | — | 341 b | unknown |
— | — | GET | 404 | 49.13.77.253:443 | https://49.13.77.253/ | unknown | — | 341 b | unknown |
2192 | chrome.exe | GET | 404 | 23.215.23.231:80 | http://www.piriform.com/go/app_releasenotes?p=1&v=5.39.6399&l=1033&b=1&a=0 | unknown | xml | 341 b | unknown |
2192 | chrome.exe | GET | 404 | 23.215.23.231:80 | http://www.piriform.com/favicon.ico | unknown | xml | 341 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4008 | ccsetup539.exe | 23.215.23.231:80 | www.piriform.com | Akamai International B.V. | US | unknown |
3528 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
480 | CCUpdate.exe | 34.149.149.62:80 | ip-info.ff.avast.com | GOOGLE | US | unknown |
480 | CCUpdate.exe | 104.124.11.59:80 | emupdate.avcdn.net | Akamai International B.V. | DE | unknown |
2640 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2192 | chrome.exe | 216.58.206.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.piriform.com |
| whitelisted |
service.piriform.com |
| whitelisted |
ip-info.ff.avast.com |
| whitelisted |
emupdate.avcdn.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
accounts.google.com |
| shared |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
480 | CCUpdate.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup (avast .com) |
4 ETPRO signatures available at the full report