| File name: | WD_PROXKey_new.exe |
| Full analysis: | https://app.any.run/tasks/72d5c985-b1f9-40cb-928a-2aeef2246595 |
| Verdict: | Malicious activity |
| Analysis date: | March 17, 2022, 15:09:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | ECB8B6A30E361249531C64F0219690A2 |
| SHA1: | 640747D9B6DD464BDE0A0D85E52CD1A4BDD3E41D |
| SHA256: | CB9BDE6B479D258BCC9A0DF23FE0E6F17D570A9E55DE3F753DF535E5274CC37D |
| SSDEEP: | 49152:ytIFzqnmYhbg7Awol34HPrydgJujhJE3KADomDyWQwBeU+s:ytqkKo94HPrX2JNmDZQwBeU+s |
MALICIOUS
Drops executable file immediately after starts
- WD_PROXKey_new.exe (PID: 1264)
Changes the autorun value in the registry
- WD_PROXKey_new.exe (PID: 1264)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 2400)
Changes settings of System certificates
- SPPKCSUtil.exe (PID: 3532)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3204)
- WD_PROXKey_new.exe (PID: 1264)
- SPMonitor.exe (PID: 2732)
- SP_CertMND.exe (PID: 3400)
- WDAdmintool.exe (PID: 2528)
Application was dropped or rewritten from another process
- SP_CertMND.exe (PID: 3400)
- SPPKCSUtil.exe (PID: 2460)
- SPPKCSUtil.exe (PID: 3532)
- WDKSPconfig.exe (PID: 580)
- SPSocketServer.exe (PID: 3924)
- SPMonitor.exe (PID: 2732)
- registCCID.exe (PID: 2300)
- WDAdmintool.exe (PID: 2528)
Actions looks like stealing of personal data
- SPPKCSUtil.exe (PID: 3532)
- SPPKCSUtil.exe (PID: 2460)
Steals credentials from Web Browsers
- SPPKCSUtil.exe (PID: 3532)
- SPPKCSUtil.exe (PID: 2460)
SUSPICIOUS
Reads the computer name
- WD_PROXKey_new.exe (PID: 1264)
- SPMonitor.exe (PID: 2732)
- SPPKCSUtil.exe (PID: 3532)
- SPPKCSUtil.exe (PID: 2460)
- SP_CertMND.exe (PID: 3400)
- WDAdmintool.exe (PID: 2528)
Checks supported languages
- WD_PROXKey_new.exe (PID: 1264)
- SPMonitor.exe (PID: 2732)
- cmd.exe (PID: 2916)
- nsD5CA.tmp (PID: 2064)
- registCCID.exe (PID: 2300)
- cmd.exe (PID: 2400)
- SPPKCSUtil.exe (PID: 3532)
- WDKSPconfig.exe (PID: 580)
- SP_CertMND.exe (PID: 3400)
- SPSocketServer.exe (PID: 3924)
- SPPKCSUtil.exe (PID: 2460)
- WDAdmintool.exe (PID: 2528)
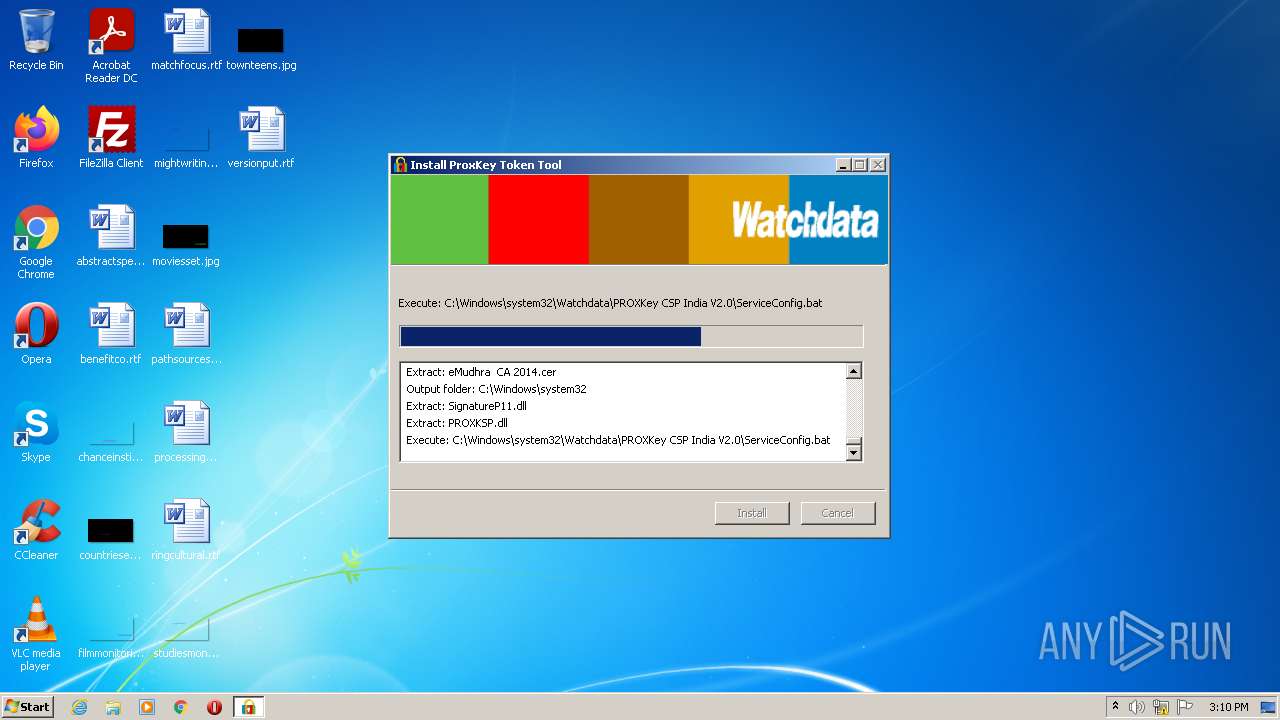
Drops a file with too old compile date
- WD_PROXKey_new.exe (PID: 1264)
Creates a directory in Program Files
- WD_PROXKey_new.exe (PID: 1264)
Creates files in the Windows directory
- WD_PROXKey_new.exe (PID: 1264)
Drops a file that was compiled in debug mode
- WD_PROXKey_new.exe (PID: 1264)
Executable content was dropped or overwritten
- WD_PROXKey_new.exe (PID: 1264)
Creates files in the program directory
- WD_PROXKey_new.exe (PID: 1264)
Executed as Windows Service
- SPMonitor.exe (PID: 2732)
Starts CMD.EXE for commands execution
- WD_PROXKey_new.exe (PID: 1264)
- nsD5CA.tmp (PID: 2064)
Starts SC.EXE for service management
- cmd.exe (PID: 2916)
Drops a file with a compile date too recent
- WD_PROXKey_new.exe (PID: 1264)
Loads DLL from Mozilla Firefox
- SPPKCSUtil.exe (PID: 3532)
- SPPKCSUtil.exe (PID: 2460)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3204)
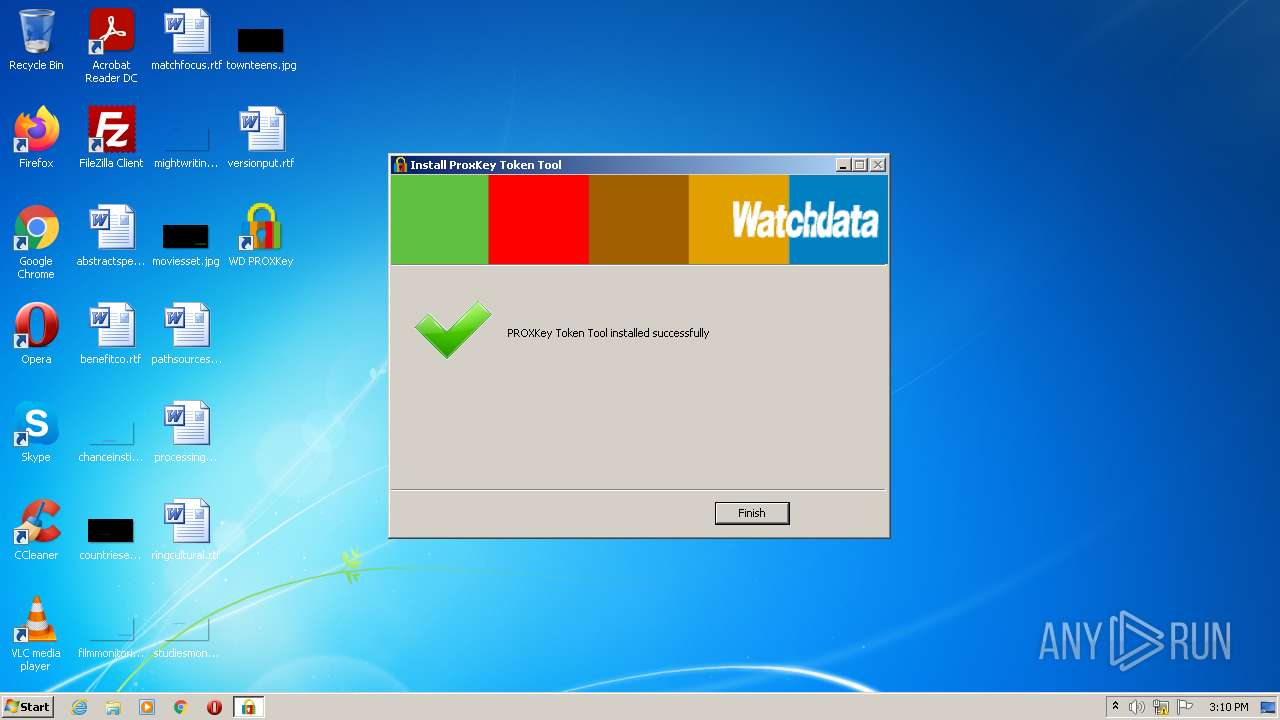
Creates a software uninstall entry
- WD_PROXKey_new.exe (PID: 1264)
Starts application with an unusual extension
- WD_PROXKey_new.exe (PID: 1264)
Creates files in the user directory
- SPPKCSUtil.exe (PID: 3532)
- SPPKCSUtil.exe (PID: 2460)
INFO
Dropped object may contain Bitcoin addresses
- WD_PROXKey_new.exe (PID: 1264)
Reads the computer name
- sc.exe (PID: 2068)
Checks supported languages
- sc.exe (PID: 2068)
- regsvr32.exe (PID: 3204)
Reads settings of System Certificates
- SPPKCSUtil.exe (PID: 3532)
- SPPKCSUtil.exe (PID: 2460)
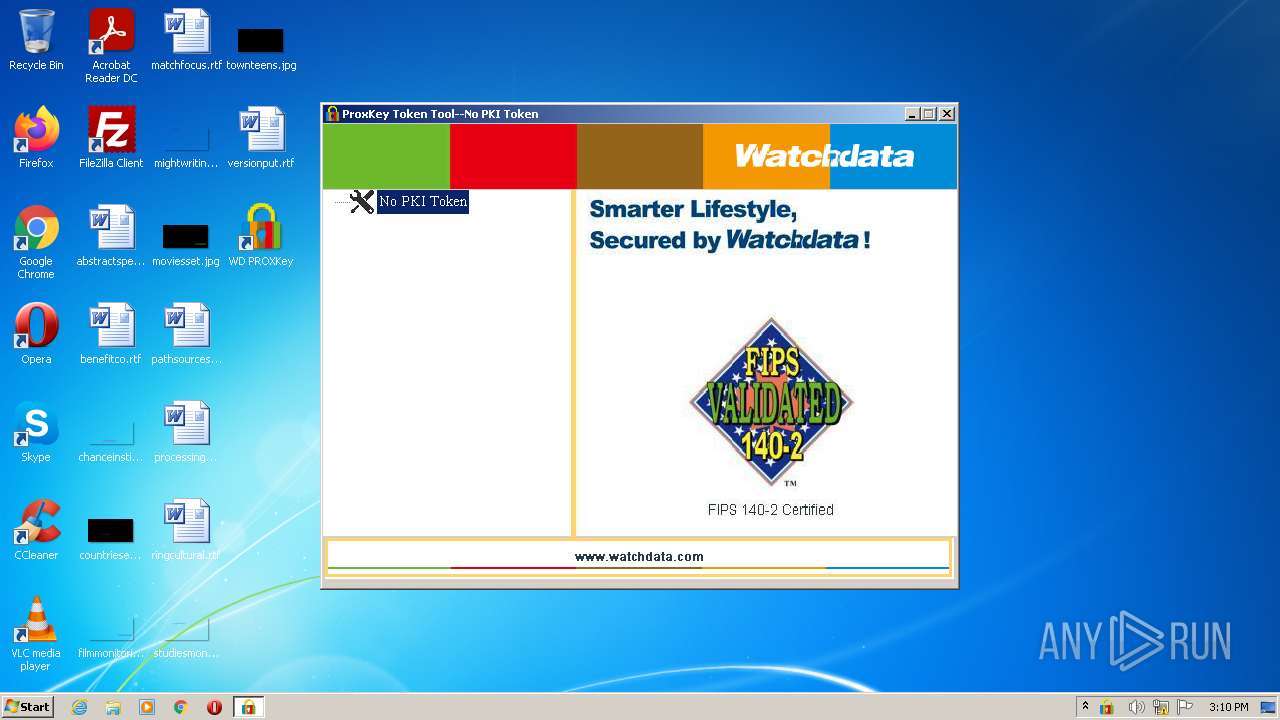
Manual execution by user
- WDAdmintool.exe (PID: 2528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 5.0.5.0 |
|---|---|
| ProductName: | ProxKey |
| LegalCopyright: | Copyright (c) 2007 Watchdata Technologies Pte. Ltd. All rights reserved. |
| FileVersion: | 5.0.5.0 |
| FileDescription: | ProxKey |
| CompanyName: | Watchdata Technologies Pte. Ltd. |
| Comments: | ProxKey |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 5.0.5.0 |
| FileVersionNumber: | 5.0.5.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x354b |
| UninitializedDataSize: | 16896 |
| InitializedDataSize: | 431104 |
| CodeSize: | 25600 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2010:04:10 14:19:31+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Apr-2010 12:19:31 |
| Detected languages: |
|
| Comments: | ProxKey |
| CompanyName: | Watchdata Technologies Pte. Ltd. |
| FileDescription: | ProxKey |
| FileVersion: | 5.0.5.0 |
| LegalCopyright: | Copyright (c) 2007 Watchdata Technologies Pte. Ltd. All rights reserved. |
| ProductName: | ProxKey |
| ProductVersion: | 5.0.5.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Apr-2010 12:19:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000063A2 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48045 |
.rdata | 0x00008000 | 0x000018F2 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.88829 |
.data | 0x0000A000 | 0x0006669C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.42988 |
.ndata | 0x00071000 | 0x000E9000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0015A000 | 0x00001E60 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.40806 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21494 | 966 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 1.97188 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.62164 | 448 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.90207 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
55
Monitored processes
15
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files\Watchdata\WD PROXKey\WDKSPconfig.exe" -register | C:\Program Files\Watchdata\WD PROXKey\WDKSPconfig.exe | — | WD_PROXKey_new.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1264 | "C:\Users\admin\AppData\Local\Temp\WD_PROXKey_new.exe" | C:\Users\admin\AppData\Local\Temp\WD_PROXKey_new.exe | Explorer.EXE | ||||||||||||
User: admin Company: Watchdata Technologies Pte. Ltd. Integrity Level: HIGH Description: ProxKey Exit code: 0 Version: 5.0.5.0 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\AppData\Local\Temp\nsxD135.tmp\nsD5CA.tmp" C:\Windows\system32\cmd.exe /C regsvr32 /s "C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\WDCtr.dll" | C:\Users\admin\AppData\Local\Temp\nsxD135.tmp\nsD5CA.tmp | — | WD_PROXKey_new.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2068 | sc failure SPMonitor reset= 0 actions= restart/3000/restart/3000/restart/3000 | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\registCCID.exe" | C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\registCCID.exe | — | WD_PROXKey_new.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2400 | C:\Windows\system32\cmd.exe /C regsvr32 /s "C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\WDCtr.dll" | C:\Windows\system32\cmd.exe | — | nsD5CA.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Watchdata\WD PROXKey\SPPKCSUtil.exe" -install | C:\Program Files\Watchdata\WD PROXKey\SPPKCSUtil.exe | SP_CertMND.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SPPKCSUtil Microsoft Basic Application Exit code: 0 Version: 3, 43, 0, 2 Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Watchdata\WD PROXKey\WDAdmintool.exe" | C:\Program Files\Watchdata\WD PROXKey\WDAdmintool.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: USB Token Tool Exit code: 0 Version: 4, 0, 0, 0 Modules
| |||||||||||||||
| 2732 | "C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\SPMonitor.exe" | C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\SPMonitor.exe | services.exe | ||||||||||||
User: SYSTEM Company: Watchdata Integrity Level: SYSTEM Description: WD_Ultimate_V1.0 Exit code: 0 Version: 3, 4, 0, 0 Modules
| |||||||||||||||
| 2916 | C:\Windows\system32\cmd.exe /c ""C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\ServiceConfig.bat"" | C:\Windows\system32\cmd.exe | — | WD_PROXKey_new.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
8 317
Read events
8 251
Write events
66
Delete events
0
Modification events
| (PID) Process: | (1264) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\nsxD135.tmp\nsProcessW.dll | |||
| (PID) Process: | (1264) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WD_Stdcertm |
Value: C:\Windows\System32\Watchdata\PROXKey CSP India V2.0\SP_CertMND.exe | |||
| (PID) Process: | (1264) WD_PROXKey_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WD_SPSocketServer |
Value: C:\Windows\System32\Watchdata\PROXKey CSP India V2.0\SPSocketServer.exe | |||
| (PID) Process: | (3204) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WDBSBCtrl.WDBSBSrcCtrl.1 |
| Operation: | write | Name: | (default) |
Value: WDBSBSrcCtrl Class | |||
| (PID) Process: | (3204) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WDBSBCtrl.WDBSBSrcCtrl.1\CLSID |
| Operation: | write | Name: | (default) |
Value: {B3FB9D3C-352D-4F7E-8AE6-43EB19792BFE} | |||
| (PID) Process: | (3204) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WDBSBCtrl.WDBSBSrcCtrl |
| Operation: | write | Name: | (default) |
Value: WDBSBSrcCtrl Class | |||
| (PID) Process: | (3204) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WDBSBCtrl.WDBSBSrcCtrl\CLSID |
| Operation: | write | Name: | (default) |
Value: {B3FB9D3C-352D-4F7E-8AE6-43EB19792BFE} | |||
| (PID) Process: | (3204) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WDBSBCtrl.WDBSBSrcCtrl\CurVer |
| Operation: | write | Name: | (default) |
Value: WDBSBCtrl.WDBSBSrcCtrl.1 | |||
| (PID) Process: | (3204) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B3FB9D3C-352D-4F7E-8AE6-43EB19792BFE} |
| Operation: | write | Name: | (default) |
Value: WDBSBSrcCtrl Class | |||
| (PID) Process: | (3204) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B3FB9D3C-352D-4F7E-8AE6-43EB19792BFE}\ProgID |
| Operation: | write | Name: | (default) |
Value: WDBSBCtrl.WDBSBSrcCtrl.1 | |||
Executable files
36
Suspicious files
131
Text files
13
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1264 | WD_PROXKey_new.exe | C:\Users\admin\AppData\Local\Temp\nsxD135.tmp\nsProcessW.dll | executable | |
MD5:F0438A894F3A7E01A4AAE8D1B5DD0289 | SHA256:30C6C3DD3CC7FCEA6E6081CE821ADC7B2888542DAE30BF00E881C0A105EB4D11 | |||
| 1264 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\Protect.sig | binary | |
MD5:A25627F4F52B73EED3713CADACC0C491 | SHA256:D716BC2A3E84E2EDB9B370742D70B00BA76B59A0D1AB5BA4A012F2E307DA7A2C | |||
| 1264 | WD_PROXKey_new.exe | C:\Users\admin\AppData\Local\Temp\nsxD135.tmp\modern-header.bmp | image | |
MD5:80913BB1E48109B1C51875A8623BCDA3 | SHA256:AA4BBD56F4053557221B0F158FCD3B699B5D41A8C94A002E787DF20CDFD6967E | |||
| 1264 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\Protectini.ini | text | |
MD5:18F2A646D983DD0A259B9125D9D5BAE7 | SHA256:C97CC62E28FD727E82B0E06BB46960036BE66DECCB6F2D89CB5A53DB50B52D8A | |||
| 1264 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\Ajax Loader(1).gif | image | |
MD5:EC24D1C3A261C84E8895BAD01485F5CE | SHA256:DDA4D8BA5C625C048CE3284CC49827990874C68B3CEA2D15C341D1053934510D | |||
| 1264 | WD_PROXKey_new.exe | C:\Users\admin\AppData\Local\Temp\nsxD135.tmp\UserInfo.dll | executable | |
MD5:D16E06C5DE8FB8213A0464568ED9852F | SHA256:728472BA312AE8AF7F30D758AB473E0772477A68FCD1D2D547DAFE6D8800D531 | |||
| 1264 | WD_PROXKey_new.exe | C:\Windows\system32\SPNSIS.dll | executable | |
MD5:EE5E22C927B76B5C5E9C716EDAF5BEC6 | SHA256:D3BAD3DECA819FABBE75F16EE1AE88EFAE57C613E0F554068173A5BFCABFE8D1 | |||
| 1264 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\UIResE3.dll | executable | |
MD5:2A20DD1983F9D30C9F0887CF34CA91FB | SHA256:19112C6EEF7FFC162245D7E19C8601FA49CCD239076AC32D3FE0AD9D0AFB3E0B | |||
| 1264 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\USBTokenDiagnosticTool.exe | executable | |
MD5:297A3D0154F6844CD8D4EA33405BC06A | SHA256:B9DA209CC30EC366F05F6B5A41C3CBDB251A2DC490D68FE9880C9E4D21FAB469 | |||
| 1264 | WD_PROXKey_new.exe | C:\Windows\system32\Watchdata\PROXKey CSP India V2.0\TokenMgr.dll | executable | |
MD5:1F493134C28A789C3ADDB898C40270B7 | SHA256:B0321E01ACC06BBFFD910993C8D6CA4B6C8A552A3768D479F1A91C2AE48A5829 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
SPMonitor.exe | [2732]:Enter GetCCIDDriverFile...
|
SPMonitor.exe | [2732]:Out GetCCIDDriverFile, succeed!
|
SPMonitor.exe | [2732]:Enter SetupDiEnumDeviceInfo...
|
SPMonitor.exe | [2732]:Out SetupDiEnumDeviceInfo, iWaitUpdateTime = 0
|
WDAdmintool.exe | [2528]:NDGetSlotList:0
|
WDAdmintool.exe | [2528]:g_DeviceNum:0
|
WDAdmintool.exe | [2528]:NDGetSlotList:0
|
WDAdmintool.exe | [2528]:g_DeviceNum:0
|