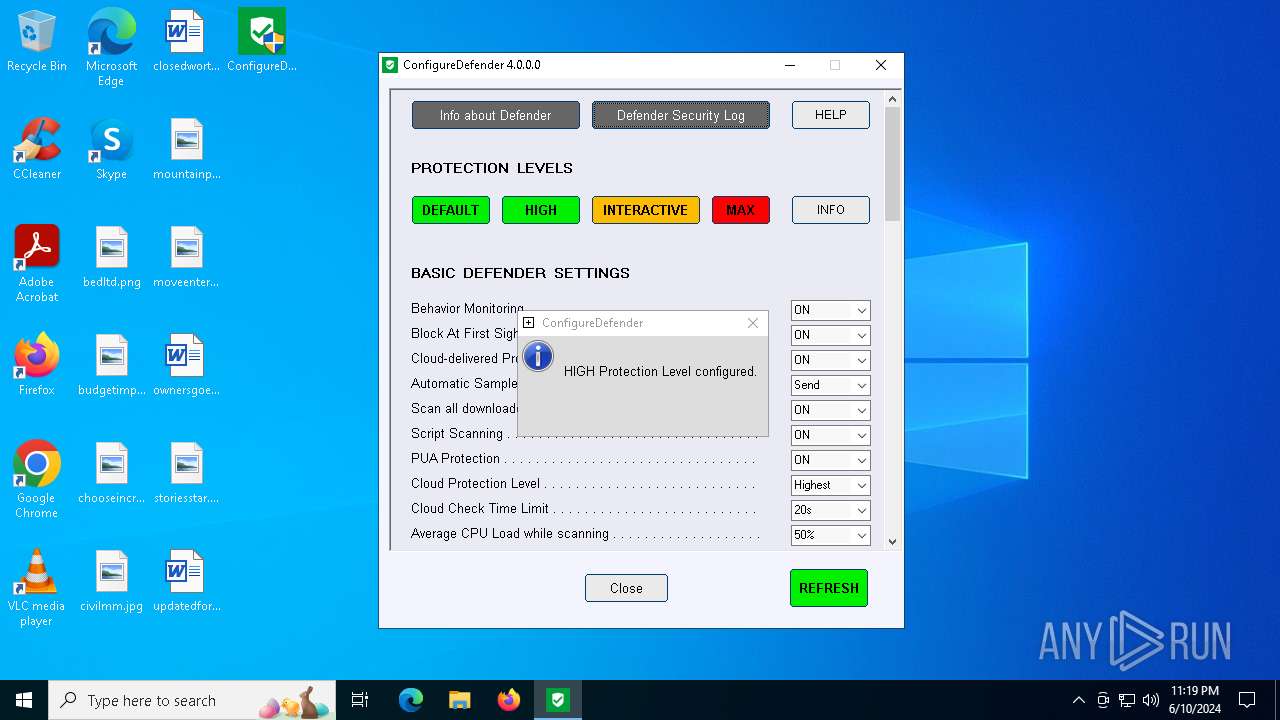
| File name: | ConfigureDefender.exe |
| Full analysis: | https://app.any.run/tasks/d839e255-051a-4535-bd5f-127da51ec0e5 |
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2024, 23:19:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 9913D5F652DBF25D363FF3D7B5CD1FC2 |
| SHA1: | 151DE1E486BCF572B9334472355F3623EA10B05A |
| SHA256: | CB97E869FA64EB7C797A1B817F20D63CBD8310A26F4249C5727BE2B776C98F16 |
| SSDEEP: | 98304:M4b/mrCfWSzXyASLCV6Zd1aYimWNdPUaV0M+6NYHkpjtb0QwnMwivGBJHRgt1iYb:5zd/t |
MALICIOUS
Drops the executable file immediately after the start
- ConfigureDefender.exe (PID: 6412)
- ConfigureDefender.exe (PID: 6996)
Run PowerShell with an invisible window
- powershell.exe (PID: 6504)
- powershell.exe (PID: 7060)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 6216)
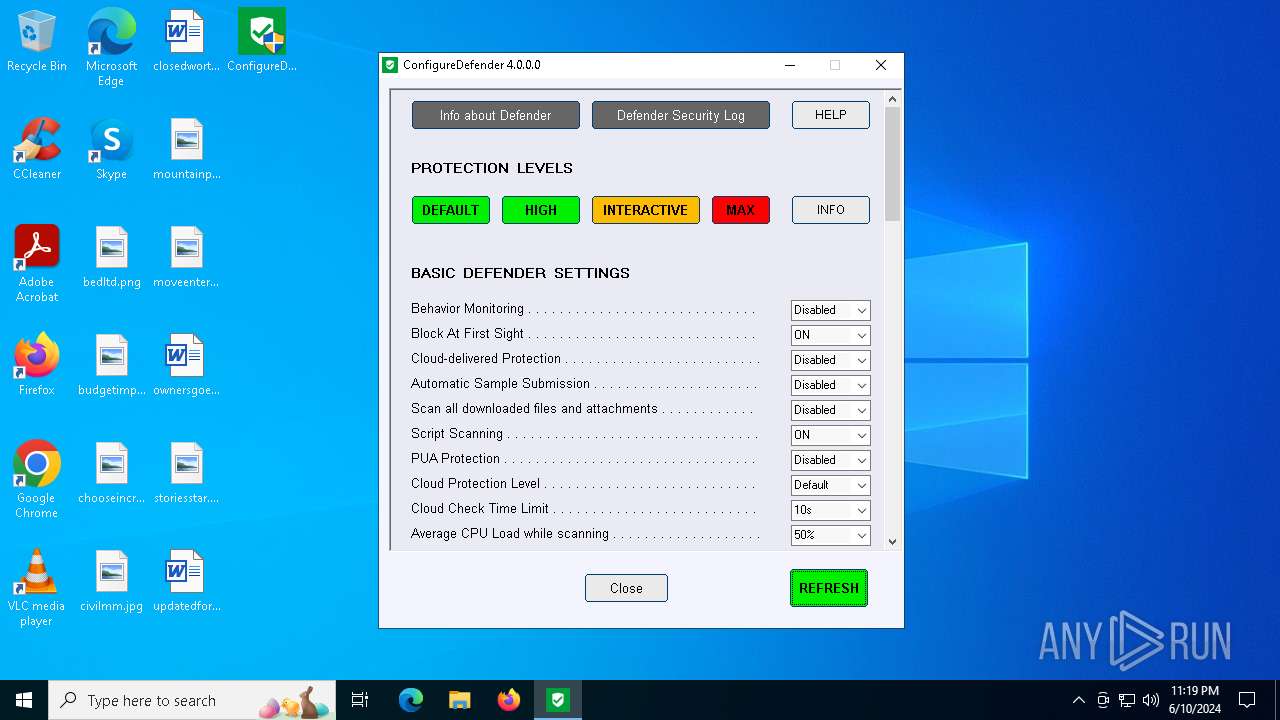
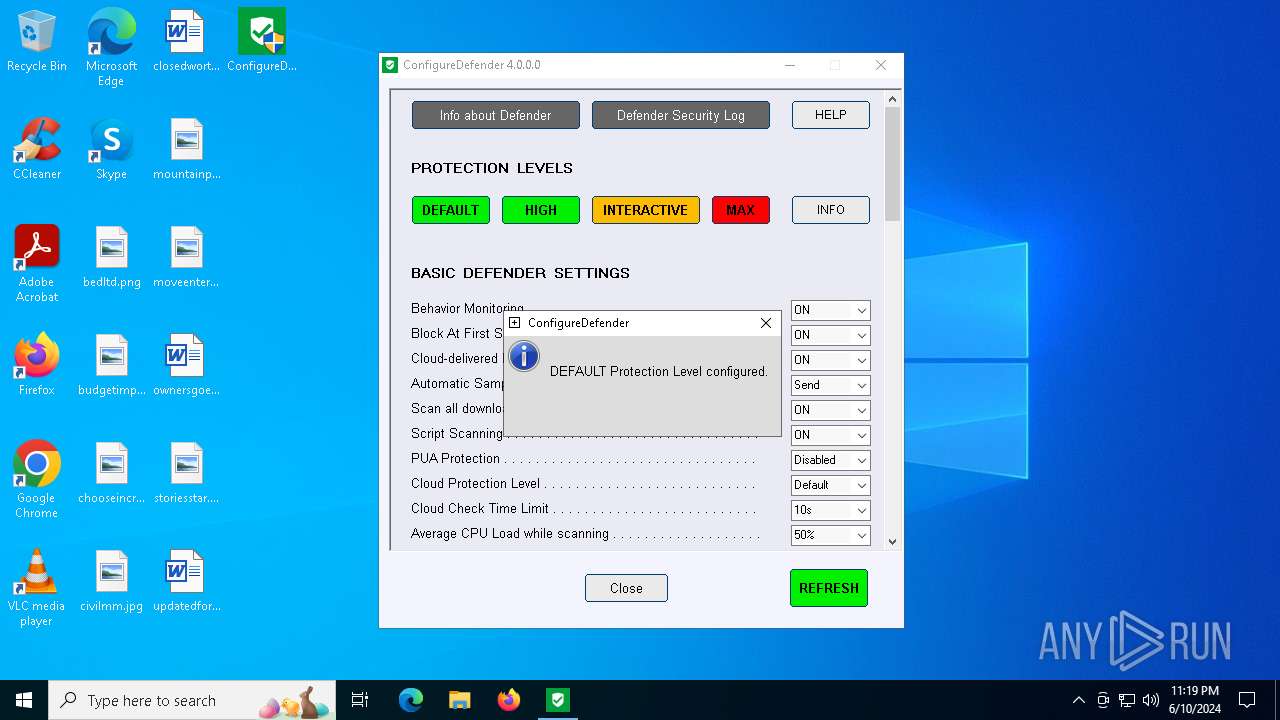
Windows Defender preferences modified via 'Set-MpPreference'
- ConfigureDefender_x64.exe (PID: 7032)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- ConfigureDefender.exe (PID: 6412)
- ConfigureDefender.exe (PID: 6996)
The process creates files with name similar to system file names
- ConfigureDefender.exe (PID: 6412)
- ConfigureDefender.exe (PID: 6996)
Executable content was dropped or overwritten
- ConfigureDefender.exe (PID: 6412)
- ConfigureDefender.exe (PID: 6996)
Starts POWERSHELL.EXE for commands execution
- ConfigureDefender_x64.exe (PID: 6472)
- ConfigureDefender_x64.exe (PID: 7032)
Script disables Windows Defender's behavior monitoring
- ConfigureDefender_x64.exe (PID: 6472)
- ConfigureDefender_x64.exe (PID: 7032)
The process hide an interactive prompt from the user
- ConfigureDefender_x64.exe (PID: 6472)
- ConfigureDefender_x64.exe (PID: 7032)
Query Microsoft Defender preferences
- ConfigureDefender_x64.exe (PID: 6472)
- ConfigureDefender_x64.exe (PID: 7032)
Script disables Windows Defender's real-time protection
- ConfigureDefender_x64.exe (PID: 6472)
- ConfigureDefender_x64.exe (PID: 7032)
INFO
Checks supported languages
- ConfigureDefender.exe (PID: 6412)
- ConfigureDefender_x64.exe (PID: 6472)
- ConfigureDefender.exe (PID: 6996)
- ConfigureDefender_x64.exe (PID: 7032)
Create files in a temporary directory
- ConfigureDefender.exe (PID: 6412)
- ConfigureDefender.exe (PID: 6996)
Reads Environment values
- ConfigureDefender_x64.exe (PID: 6472)
- ConfigureDefender_x64.exe (PID: 7032)
Reads mouse settings
- ConfigureDefender_x64.exe (PID: 6472)
- ConfigureDefender_x64.exe (PID: 7032)
Reads the computer name
- ConfigureDefender_x64.exe (PID: 6472)
- ConfigureDefender_x64.exe (PID: 7032)
Manual execution by a user
- ConfigureDefender.exe (PID: 6996)
- ConfigureDefender.exe (PID: 6948)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6216)
- powershell.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
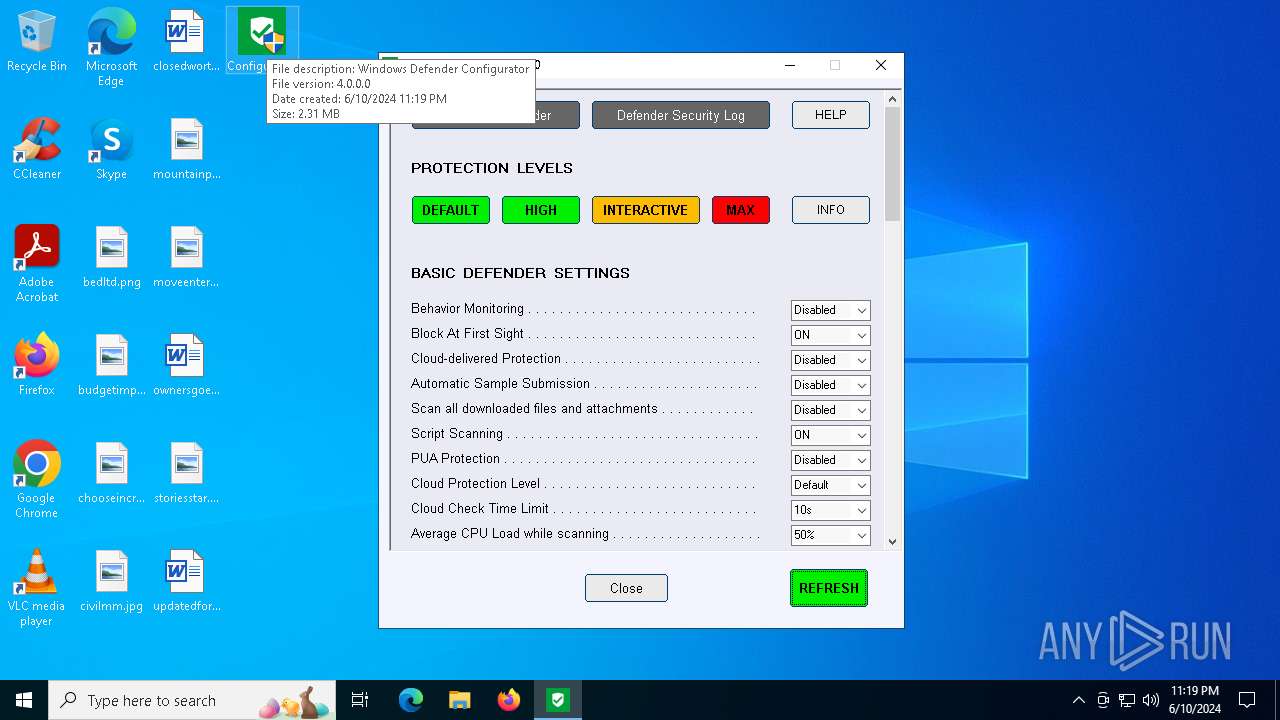
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Windows Defender Configurator |
| LegalCopyright: | Copyright * Andrzej Pluta (@Andy Ful) |
| ProductName: | ConfigureDefender |
Total processes
131
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3700 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\PowerShell -NonInteractive -WindowStyle hidden -command Set-MpPreference -EnableNetworkProtection Disabled; Set-MpPreference -EnableControlledFolderAccess Disabled; Set-MpPreference -DisableRealtimeMonitoring 0; Set-MpPreference -DisableBehaviorMonitoring 0; Set-MpPreference -DisableBlockAtFirstSeen 0; Set-MpPreference -MAPSReporting 2; Set-MpPreference -SubmitSamplesConsent 1; Set-MpPreference -DisableIOAVProtection 0; Set-MpPreference -DisableScriptScanning 0; Set-MpPreference -PUAProtection Disabled; Set-MpPreference -ScanAvgCPULoadFactor 50; $get = (Get-Mppreference).AttackSurfaceReductionRules_Ids; Remove-MpPreference -AttackSurfaceReductionRules_Ids $get; Remove-MpPreference -AttackSurfaceReductionOnlyExclusions $env:SystemRoot'\assembly'; Remove-MpPreference -AttackSurfaceReductionOnlyExclusions $env:SystemRoot'\Microsoft.NET\Framework\*\NativeImages'; Remove-MpPreference -AttackSurfaceReductionOnlyExclusions $env:SystemRoot'\WinSxS\*\*.ni.dll'; Remove-MpPreference -AttackSurfaceReductionOnlyExclusions $env:ProgramData'\Microsoft\Windows Defender'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ConfigureDefender_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3712 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6216 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\PowerShell -NonInteractive -WindowStyle hidden -command Set-MpPreference -EnableNetworkProtection Enabled; Set-MpPreference -EnableControlledFolderAccess Disabled; Set-MpPreference -DisableRealtimeMonitoring 0; Set-MpPreference -DisableBehaviorMonitoring 0; Set-MpPreference -DisableBlockAtFirstSeen 0; Set-MpPreference -MAPSReporting 2; Set-MpPreference -SubmitSamplesConsent 1; Set-MpPreference -DisableIOAVProtection 0; Set-MpPreference -DisableScriptScanning 0; Set-MpPreference -PUAProtection Enabled; Set-MpPreference -ScanAvgCPULoadFactor 50; Set-MpPreference -AttackSurfaceReductionRules_Ids BE9BA2D9-53EA-4CDC-84E5-9B1EEEE46550,D4F940AB-401B-4EFC-AADC-AD5F3C50688A,3B576869-A4EC-4529-8536-B80A7769E899,75668C1F-73B5-4CF0-BB93-3ECF5CB7CC84,D3E037E1-3EB8-44C8-A917-57927947596D,5BEB7EFE-FD9A-4556-801D-275E5FFC04CC,92E97FA1-2EDF-4476-BDD6-9DD0B4DDDC7B,01443614-cd74-433a-b99e-2ecdc07bfc25,c1db55ab-c21a-4637-bb3f-a12568109d35,9e6c4e1f-7d60-472f-ba1a-a39ef669e4b2,d1e49aac-8f56-4280-b9ba-993a6d77406c,b2b3f03d-6a65-4f7b-a9c7-1c7ef74a9ba4,26190899-1602-49e8-8b27-eb1d0a1ce869,7674ba52-37eb-4a4f-a9a1-f0f9a1619a2c,e6db77e5-3df2-4cf1-b95a-636979351e5b,56a863a9-875e-4185-98a7-b882c64b5ce5 -AttackSurfaceReductionRules_Actions Enabled,Enabled,Enabled,Enabled,Enabled,Enabled,Enabled,Disabled,Enabled,Disabled,Disabled,Enabled,Enabled,Enabled,Enabled,Warn; Remove-MpPreference -AttackSurfaceReductionOnlyExclusions $env:SystemRoot'\assembly'; Remove-MpPreference -AttackSurfaceReductionOnlyExclusions $env:SystemRoot'\Microsoft.NET\Framework\*\NativeImages'; Remove-MpPreference -AttackSurfaceReductionOnlyExclusions $env:SystemRoot'\WinSxS\*\*.ni.dll'; Remove-MpPreference -AttackSurfaceReductionOnlyExclusions $env:ProgramData'\Microsoft\Windows Defender'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ConfigureDefender_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6364 | "C:\Users\admin\Desktop\ConfigureDefender.exe" | C:\Users\admin\Desktop\ConfigureDefender.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows Defender Configurator Exit code: 3221226540 Modules
| |||||||||||||||
| 6412 | "C:\Users\admin\Desktop\ConfigureDefender.exe" | C:\Users\admin\Desktop\ConfigureDefender.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Windows Defender Configurator Exit code: 0 Modules
| |||||||||||||||
| 6472 | "C:\WINDOWS\Temp\241538342459015213\0\ConfigureDefender_x64.exe" | C:\Windows\Temp\241538342459015213\0\ConfigureDefender_x64.exe | — | ConfigureDefender.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Utility for configuring Defender antivirus on Windows 10 Exit code: 0 Version: 4.0.0.0 Modules
| |||||||||||||||
| 6504 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\PowerShell -NonInteractive -WindowStyle hidden $Preferences=Get-MpPreference;$path='HKLM:\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP'; New-ItemProperty -Path $path -Name 'PreferencesTest' -Value $Preferences.DisableRealtimeMonitoring -PropertyType String -Force | Out-Null; function SetRegistryKey ([string]$name){$svalue=$Preferences.$name;New-ItemProperty -Path $path -Name $name -Value $svalue -PropertyType DWORD -Force | Out-Null}; SetRegistryKey('EnableNetworkProtection'); SetRegistryKey( 'EnableControlledFolderAccess');SetRegistryKey('DisableRealtimeMonitoring'); SetRegistryKey('DisableBehaviorMonitoring'); SetRegistryKey('DisableBlockAtFirstSeen'); SetRegistryKey('MAPSReporting');SetRegistryKey('SubmitSamplesConsent');SetRegistryKey('DisableIOAVProtection'); SetRegistryKey('DisableScriptScanning'); SetRegistryKey('PUAProtection'); SetRegistryKey('ScanAvgCPULoadFactor'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | ConfigureDefender_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6948 | "C:\Users\admin\Desktop\ConfigureDefender.exe" | C:\Users\admin\Desktop\ConfigureDefender.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows Defender Configurator Exit code: 3221226540 Modules
| |||||||||||||||
Total events
24 853
Read events
24 801
Write events
34
Delete events
18
Modification events
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | PreferencesTest |
Value: True | |||
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | EnableNetworkProtection |
Value: 0 | |||
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | EnableControlledFolderAccess |
Value: 0 | |||
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | DisableBlockAtFirstSeen |
Value: 0 | |||
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | MAPSReporting |
Value: 0 | |||
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | SubmitSamplesConsent |
Value: 2 | |||
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | DisableIOAVProtection |
Value: 1 | |||
| (PID) Process: | (6504) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\safer_Hard_Configurator\Defender\TEMP |
| Operation: | write | Name: | DisableScriptScanning |
Value: 0 | |||
Executable files
6
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6996 | ConfigureDefender.exe | C:\Users\admin\AppData\Local\Temp\nst7146.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 3700 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_105cfria.siz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6996 | ConfigureDefender.exe | C:\WINDOWS\Temp\241538342459015213\0\ConfigureDefender_x64.exe | executable | |
MD5:0F8EE39A0E3662205AA268C9A44F694F | SHA256:5B431D9BE209A84B0E6C366BB676956C5E2B6A6B8D9D525A062B1931F4F30AAD | |||
| 3700 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ylyew0yr.ehp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6412 | ConfigureDefender.exe | C:\WINDOWS\Temp\241538342459015213\0\ConfigureDefender_x64.exe | executable | |
MD5:0F8EE39A0E3662205AA268C9A44F694F | SHA256:5B431D9BE209A84B0E6C366BB676956C5E2B6A6B8D9D525A062B1931F4F30AAD | |||
| 7060 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mjzqjapn.wpf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6996 | ConfigureDefender.exe | C:\Users\admin\AppData\Local\Temp\nst7146.tmp\nsRandom.dll | executable | |
MD5:AB467B8DFAA660A0F0E5B26E28AF5735 | SHA256:DB267D9920395B4BADC48DE04DF99DFD21D579480D103CAE0F48E6578197FF73 | |||
| 6412 | ConfigureDefender.exe | C:\Users\admin\AppData\Local\Temp\nsd3E20.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 6504 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kf43ilks.3kl.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6216 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mvbgcgrq.k1d.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5380 | svchost.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | unknown |
5380 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
— | — | POST | 200 | 20.44.10.123:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5380 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4856 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5140 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4364 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
5380 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5140 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5140 | MoUsoCoreWorker.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
5380 | svchost.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
5456 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |