| File name: | file |
| Full analysis: | https://app.any.run/tasks/b357cf24-225a-46c5-8d6a-19c17497d7af |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 05:00:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 1FF4738B61A63E5FDBB0C62E38CA255D |
| SHA1: | 5E8FDEB78683E34504CF55C12771A52559A82BF7 |
| SHA256: | CB93F9385BDFAC9C0125B40BD7BFA832119FD8ED1BE5397051CA45694EE34D5A |
| SSDEEP: | 3072:J1igAkHnjkQ6KSwXNXL4oNF5bYZpHCXvkWvLgsKNkhILAU0OY3giLa:egAkHnjkQBSwXN7v98HiXvNgsUO3giLa |
MALICIOUS
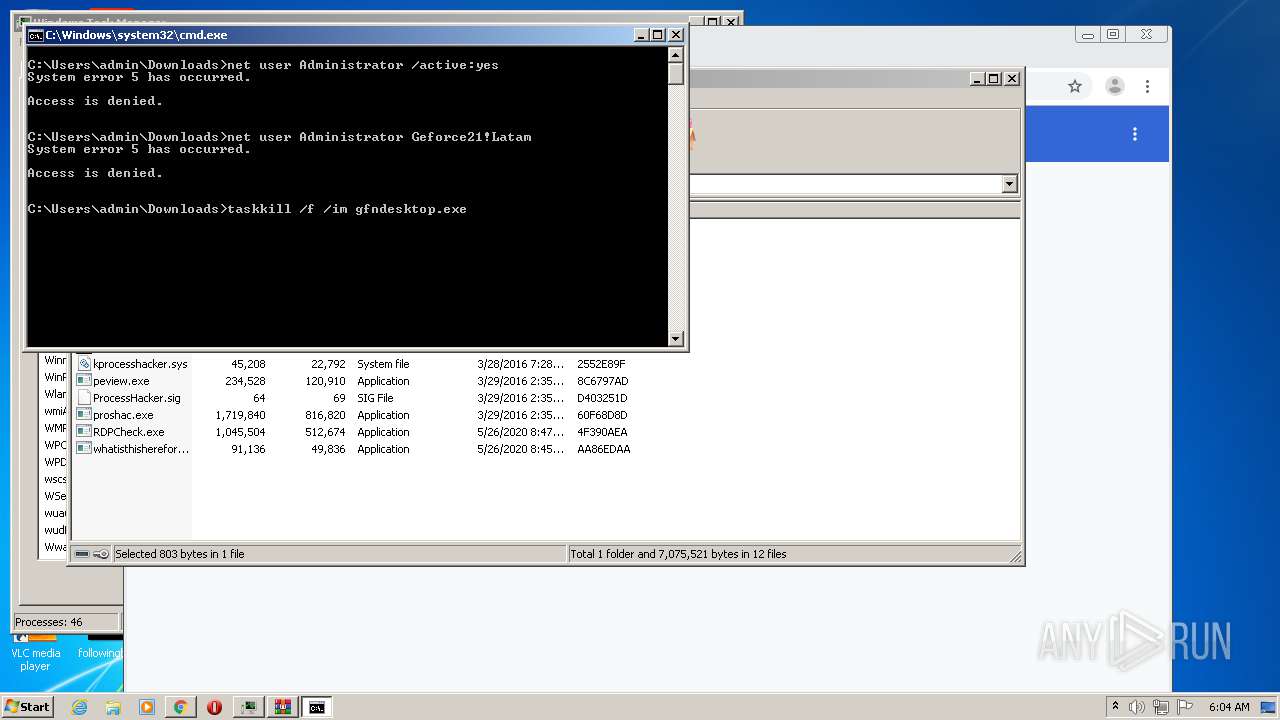
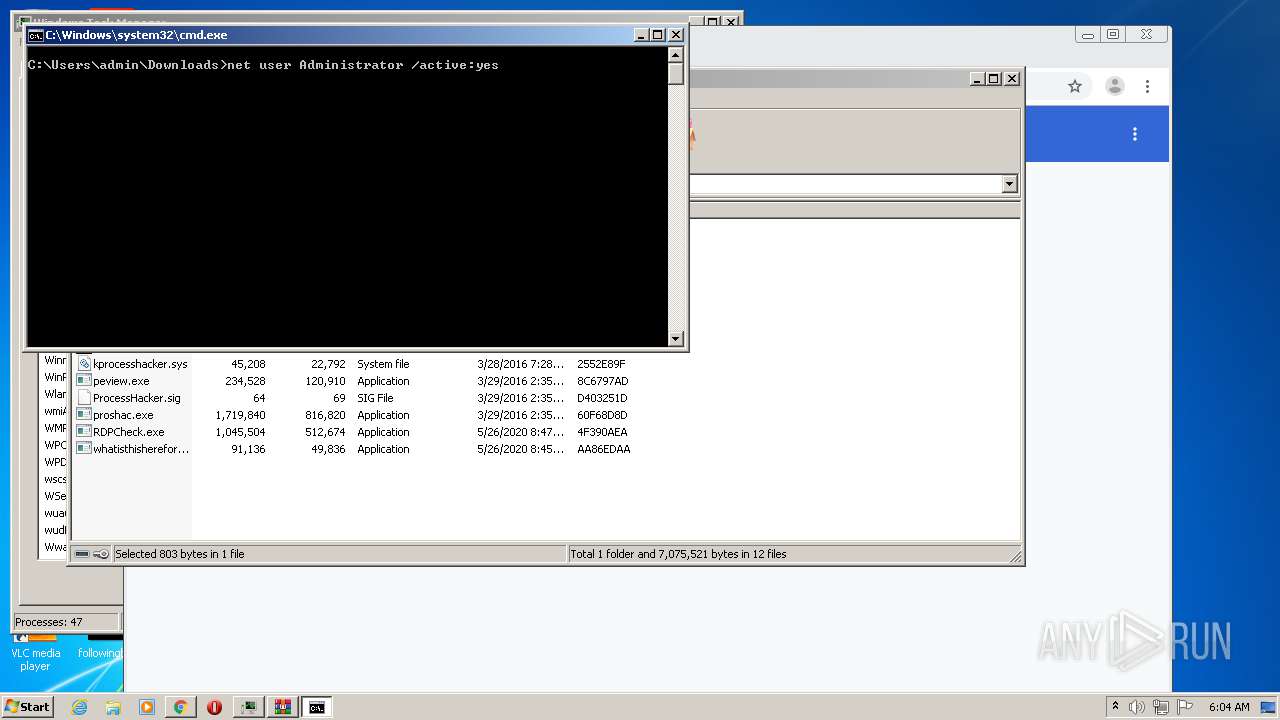
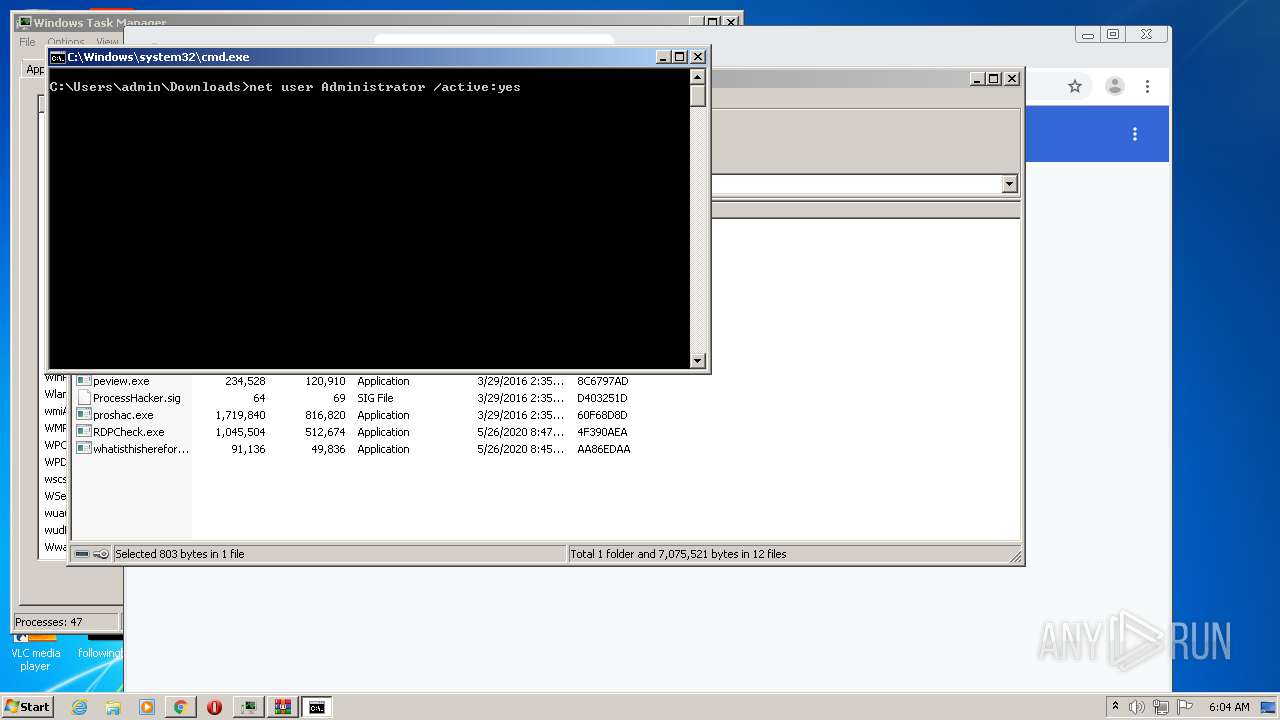
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 4068)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 3048)
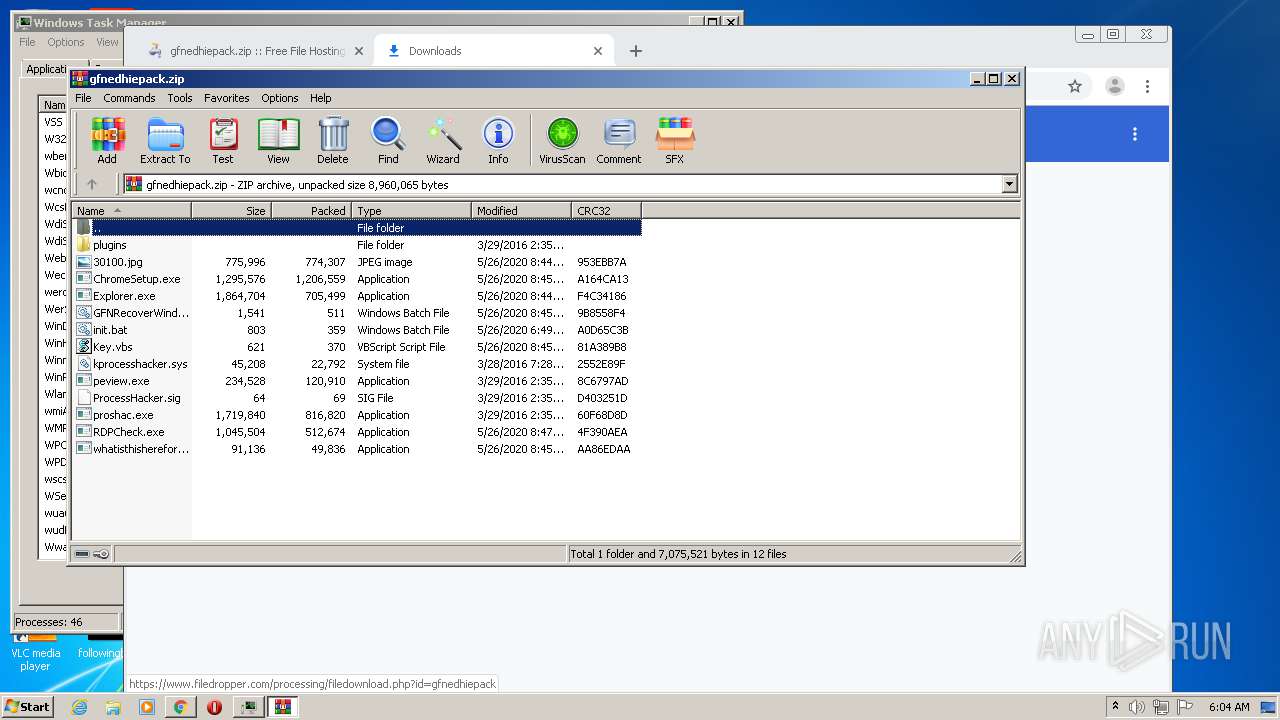
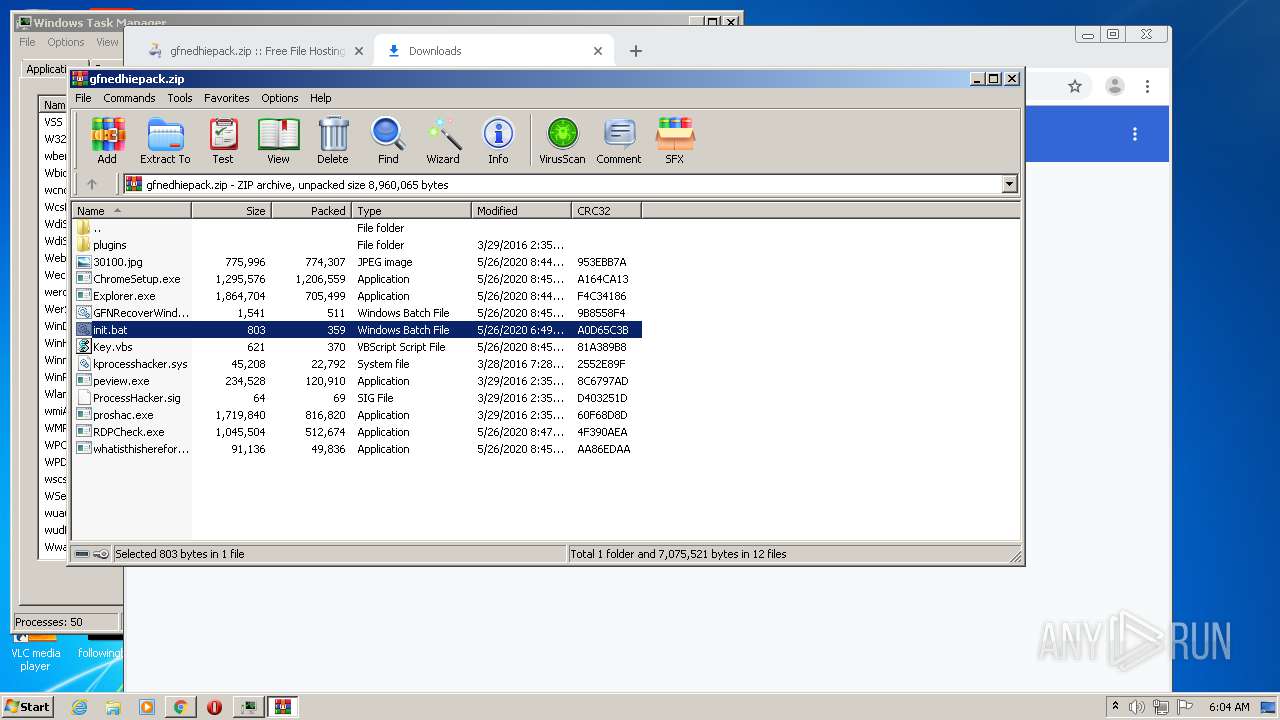
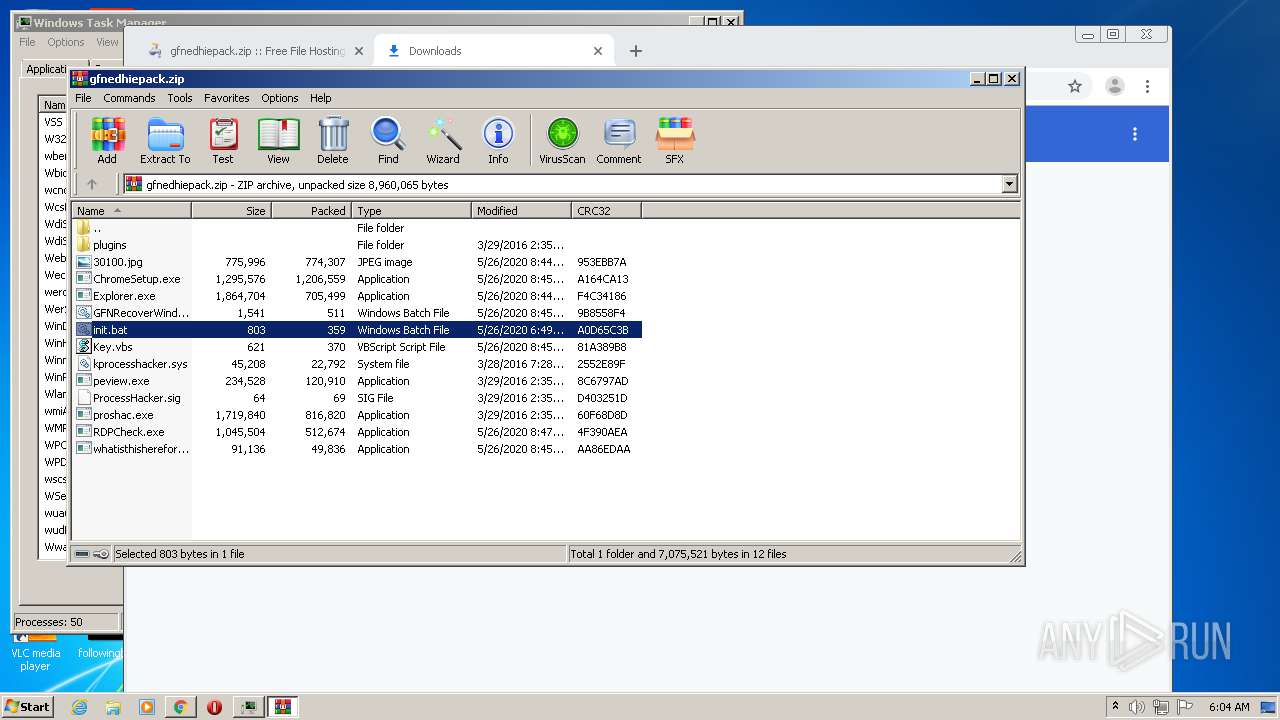
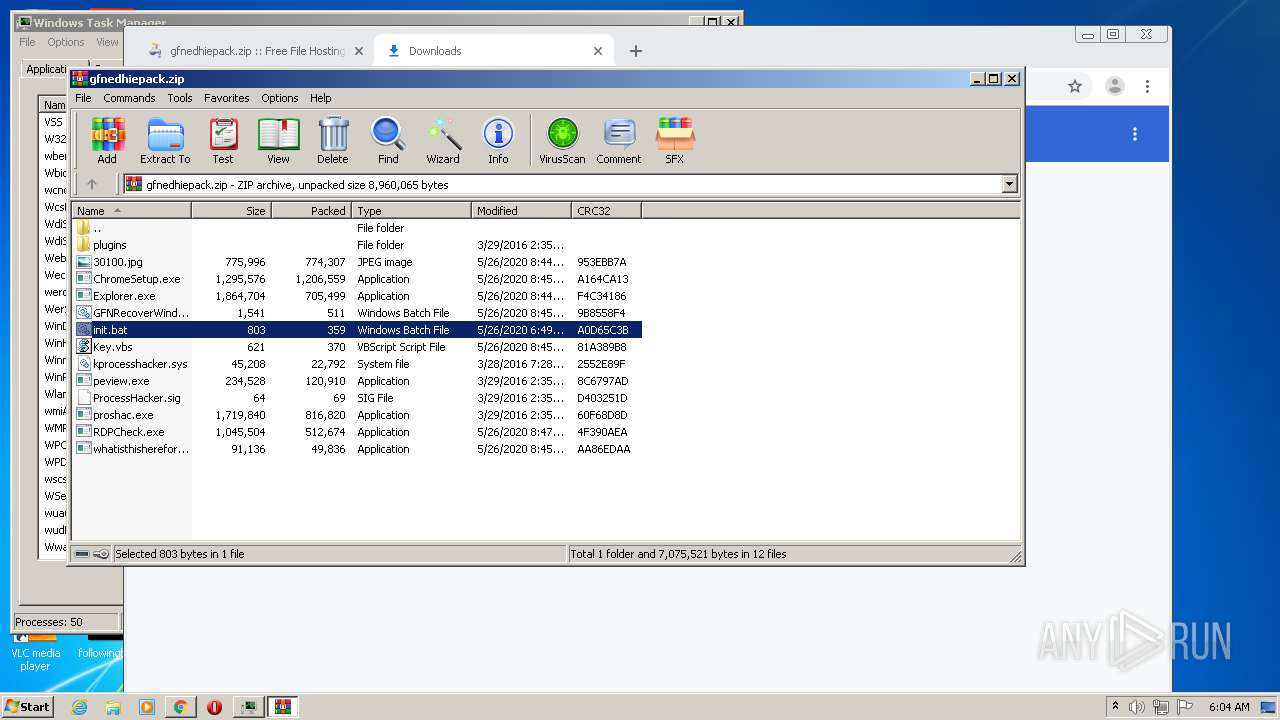
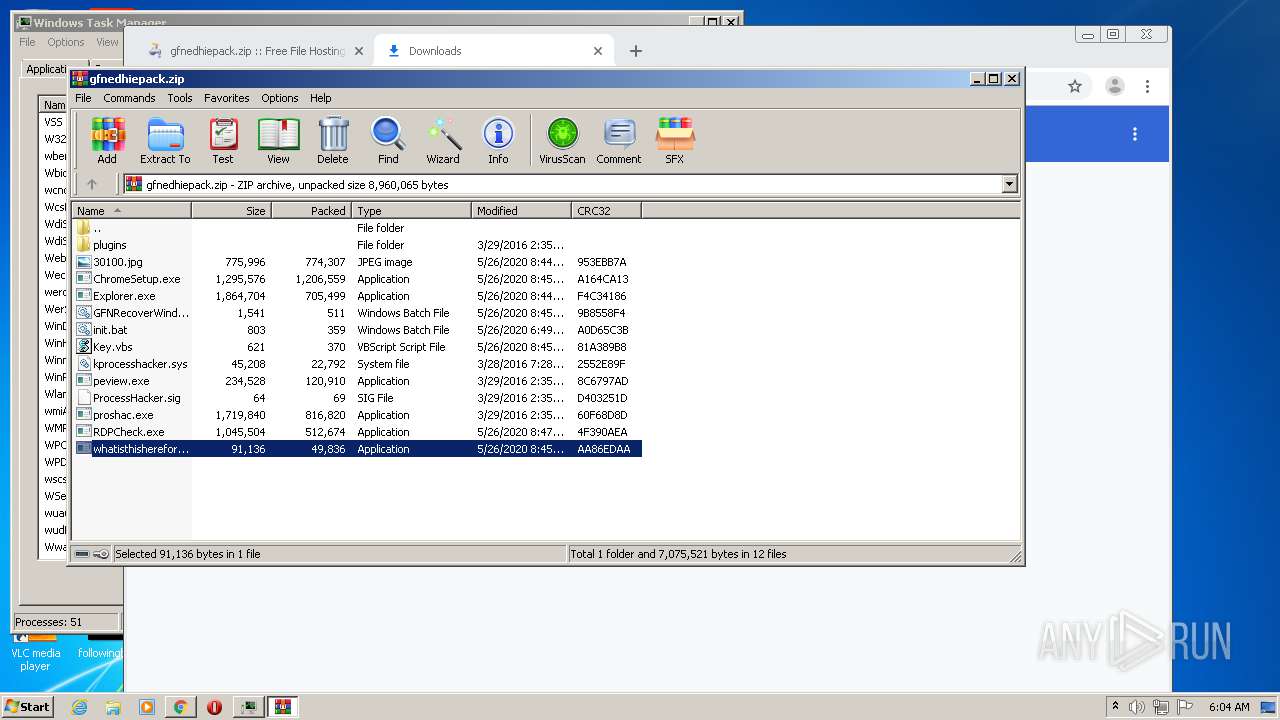
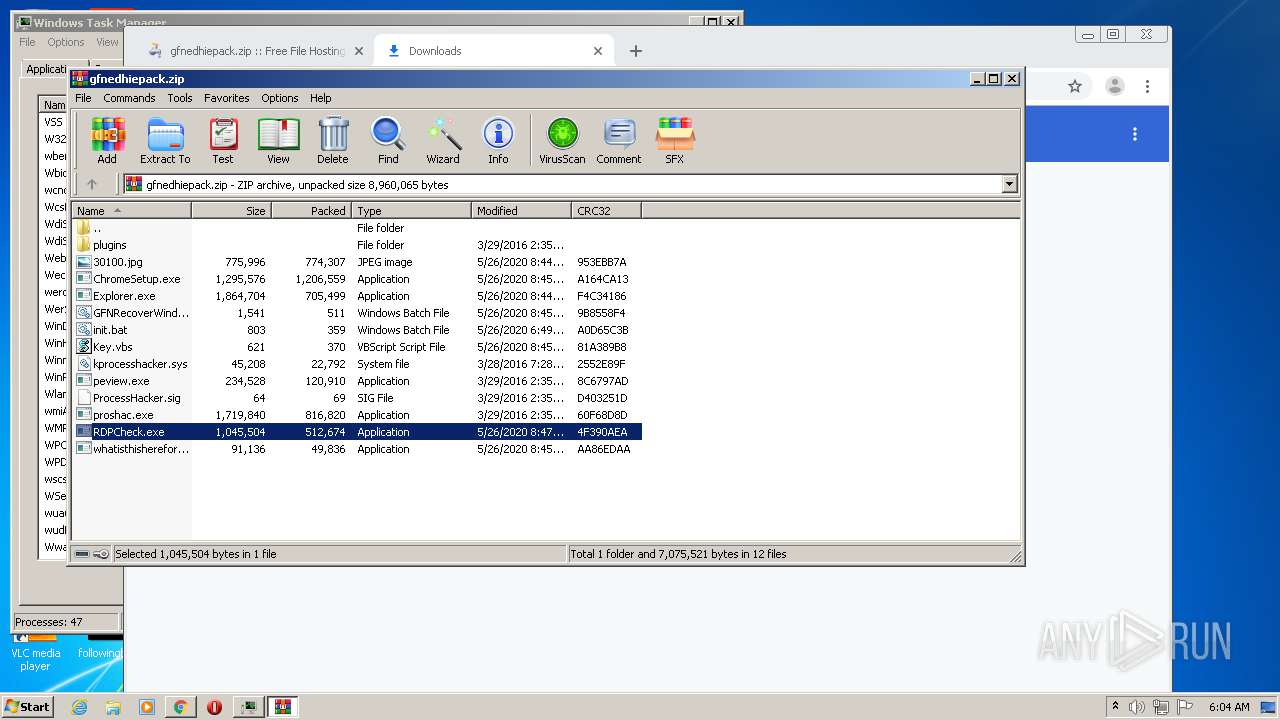
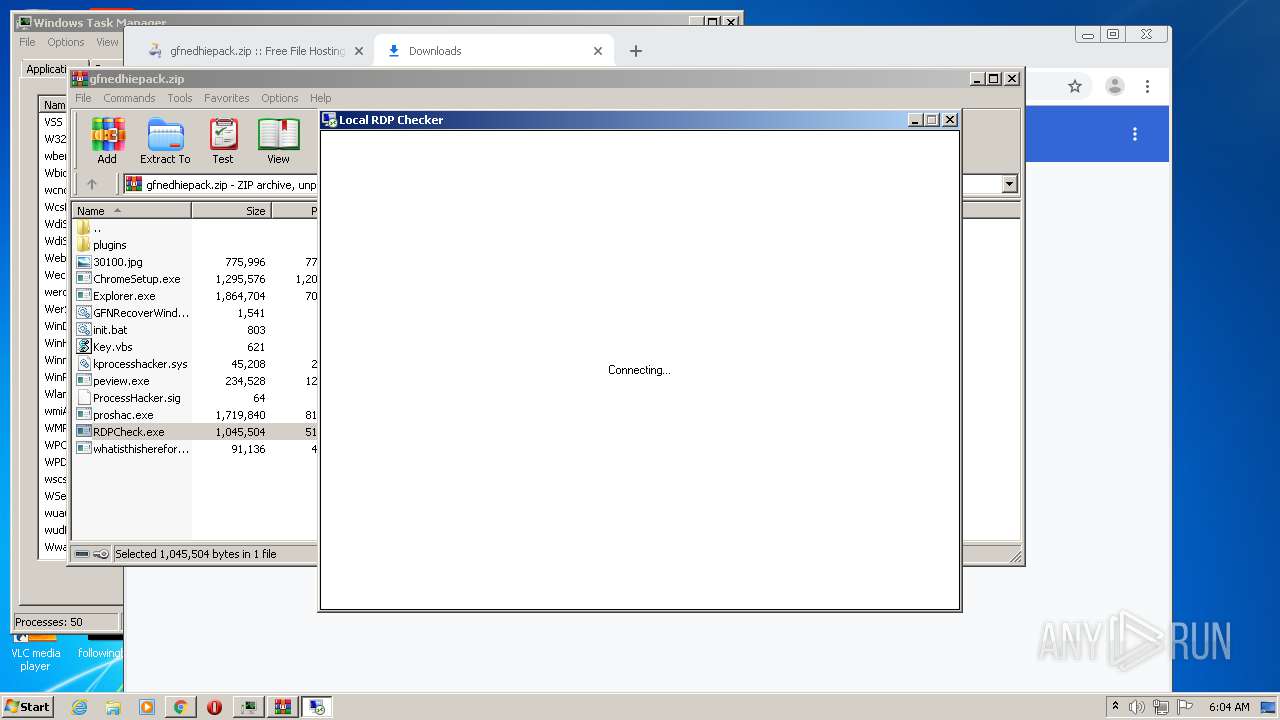
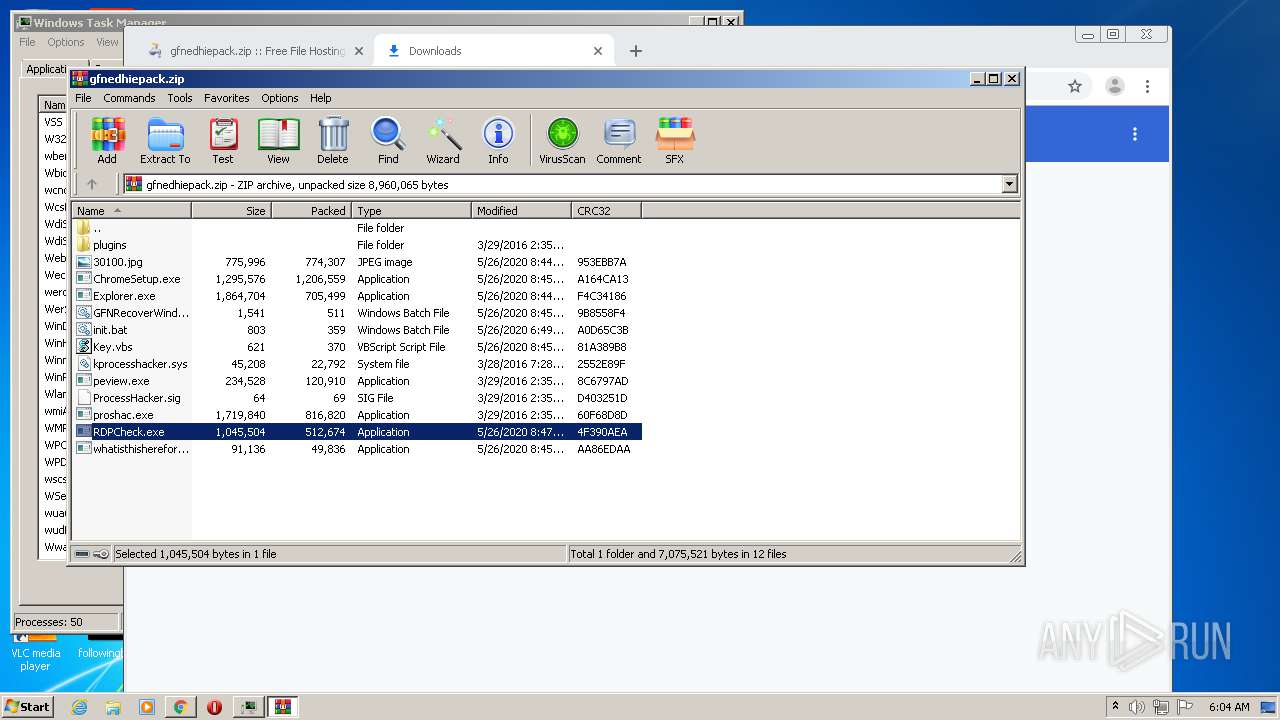
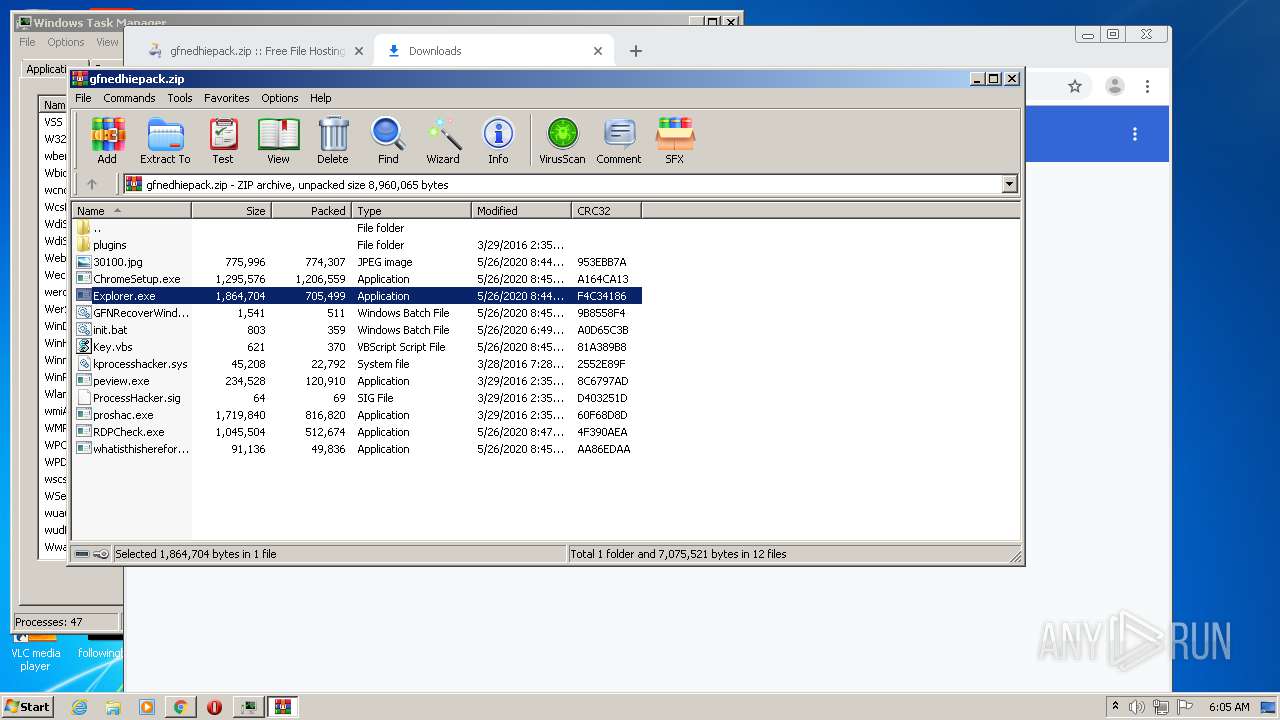
Application was dropped or rewritten from another process
- RDPCheck.exe (PID: 3744)
- RDPCheck.exe (PID: 2088)
- whatisthisherefor.exe (PID: 3864)
SUSPICIOUS
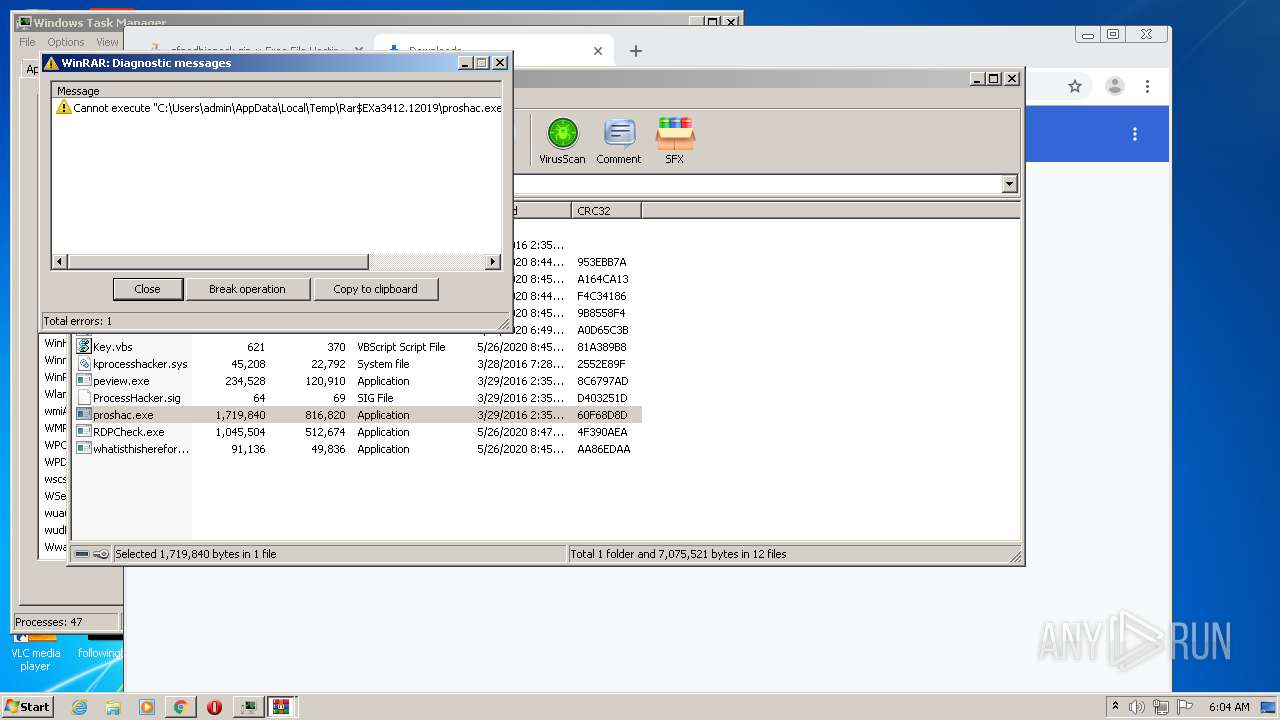
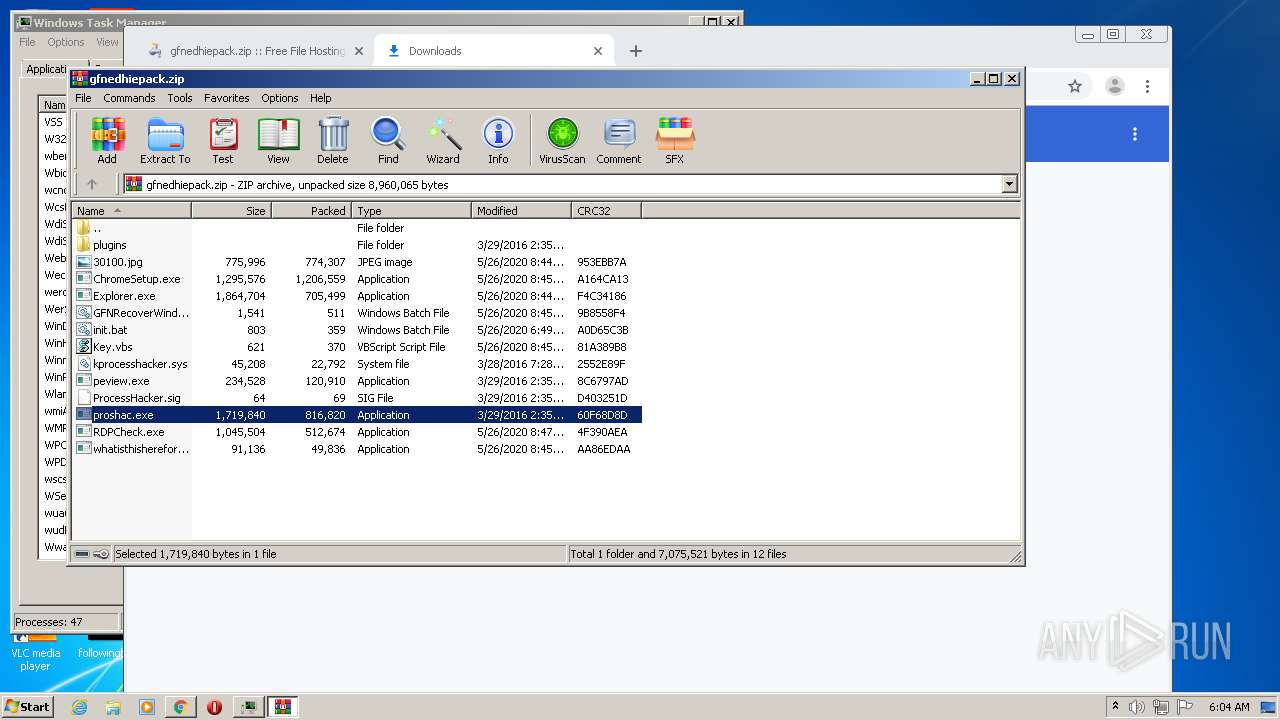
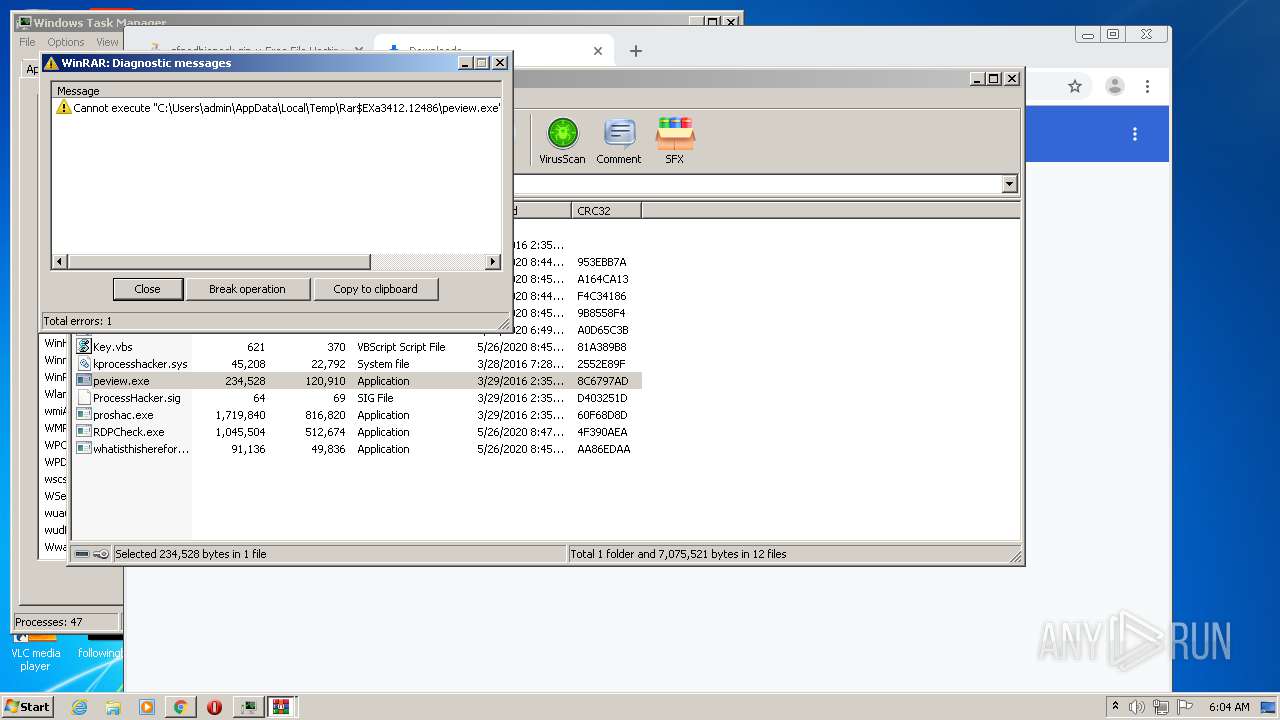
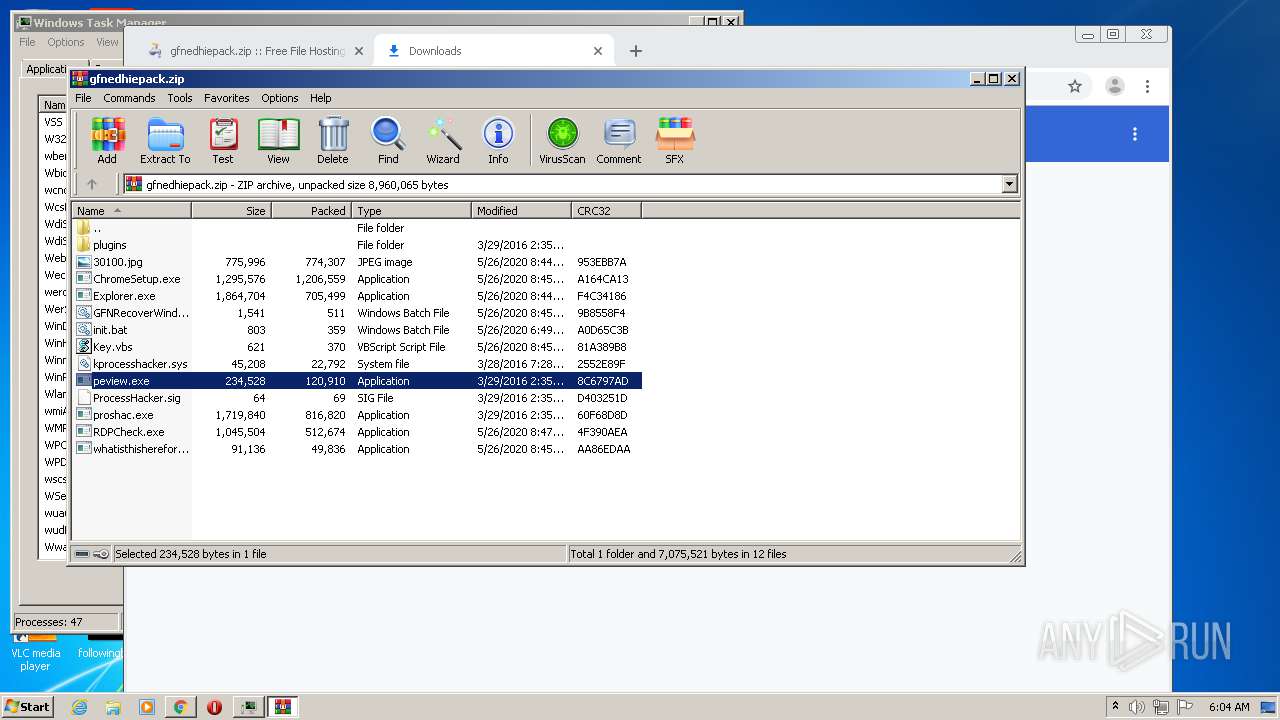
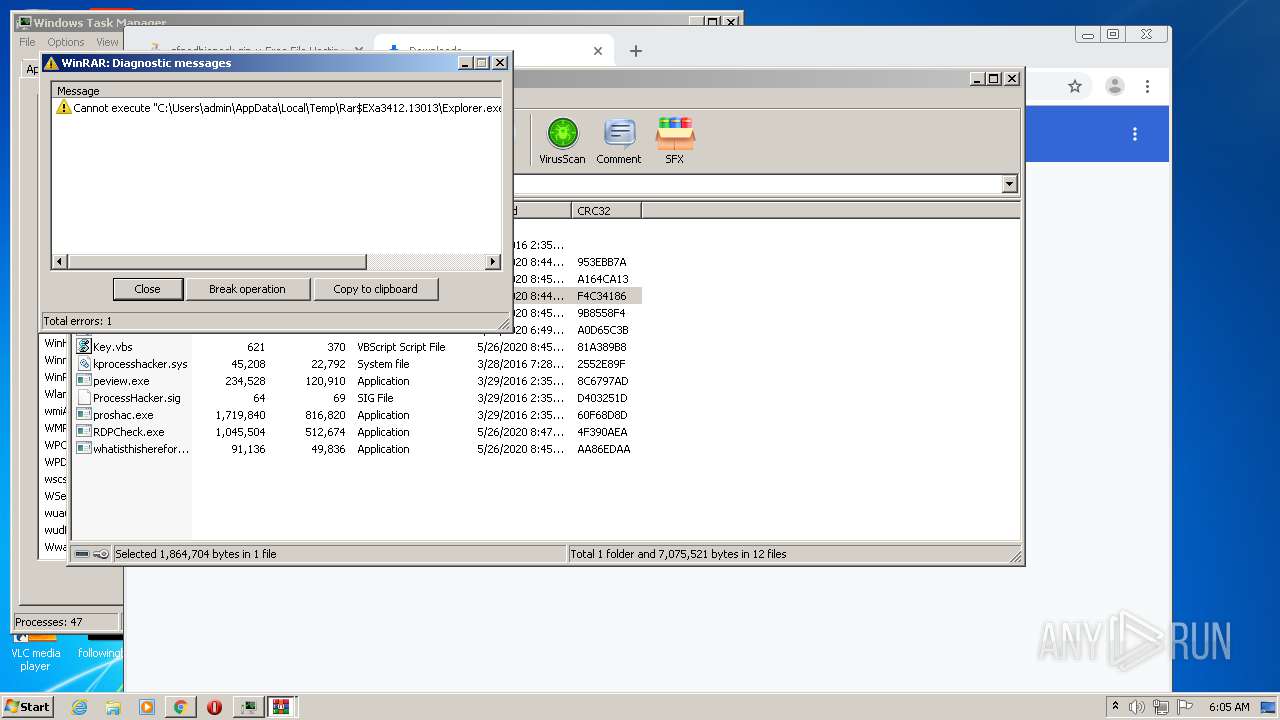
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3412)
- whatisthisherefor.exe (PID: 3864)
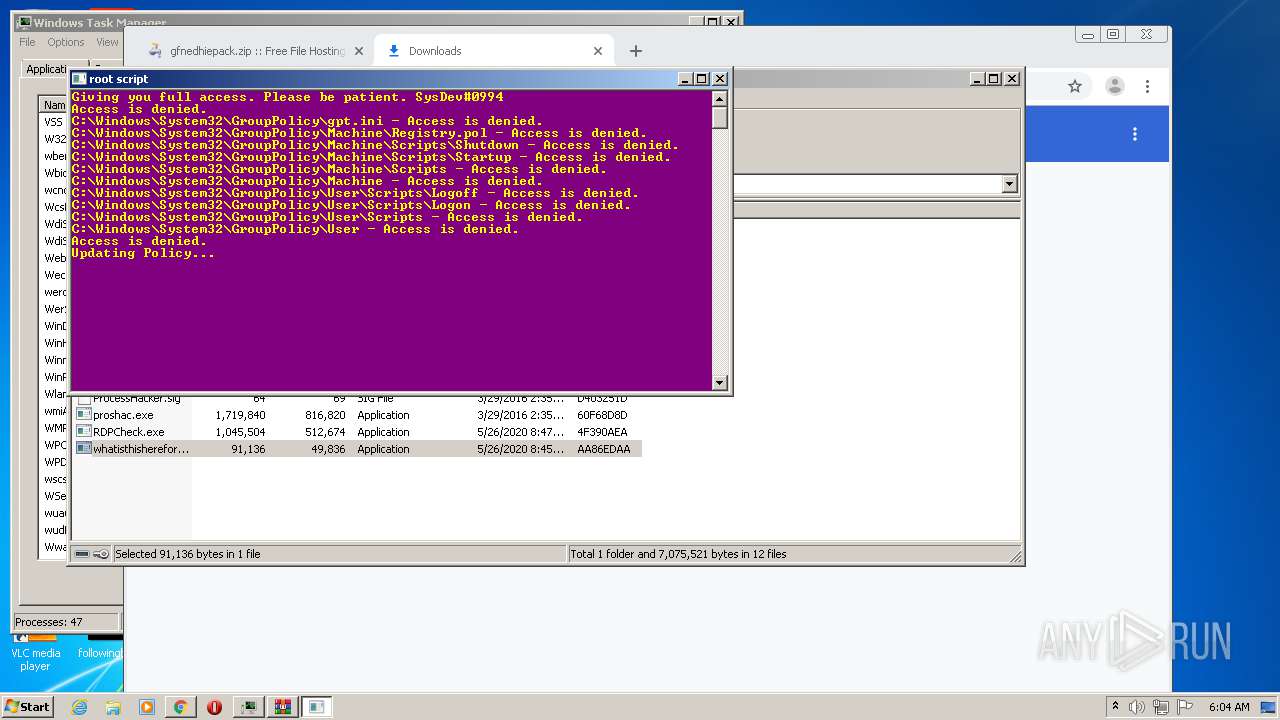
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2116)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 3048)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2116)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 3048)
Creates executable files which already exist in Windows
- WinRAR.exe (PID: 3412)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3412)
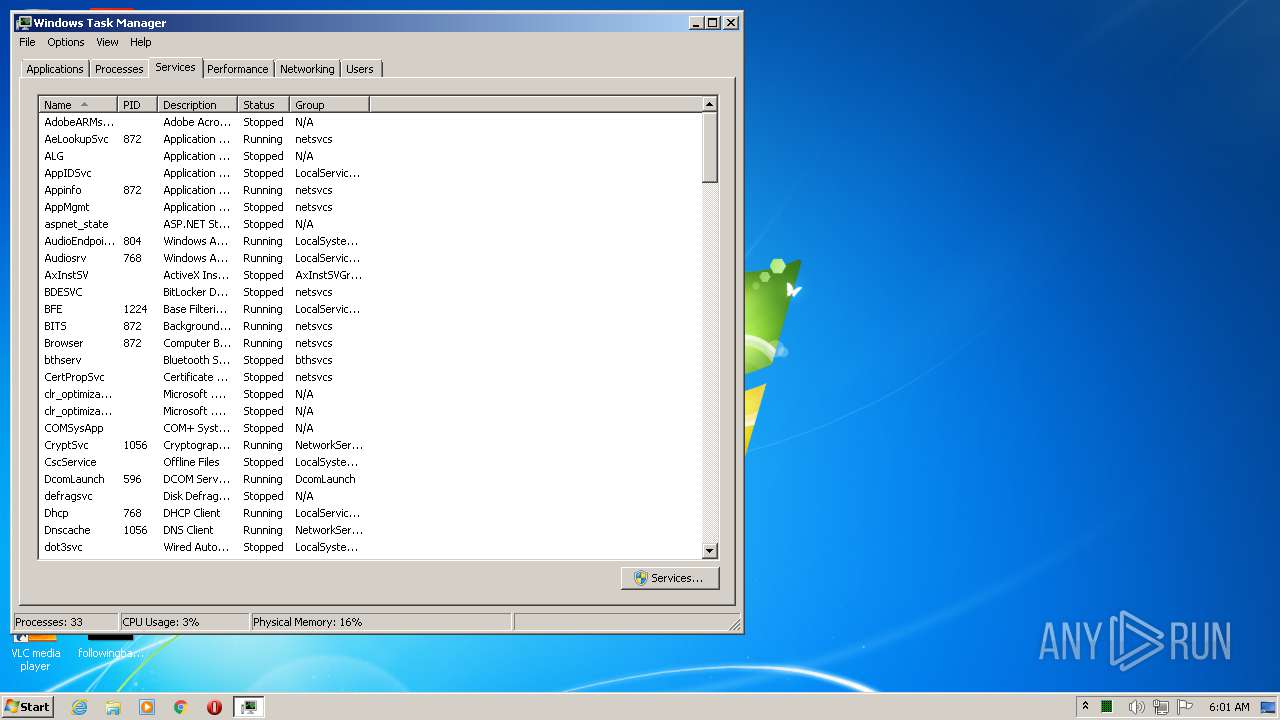
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2280)
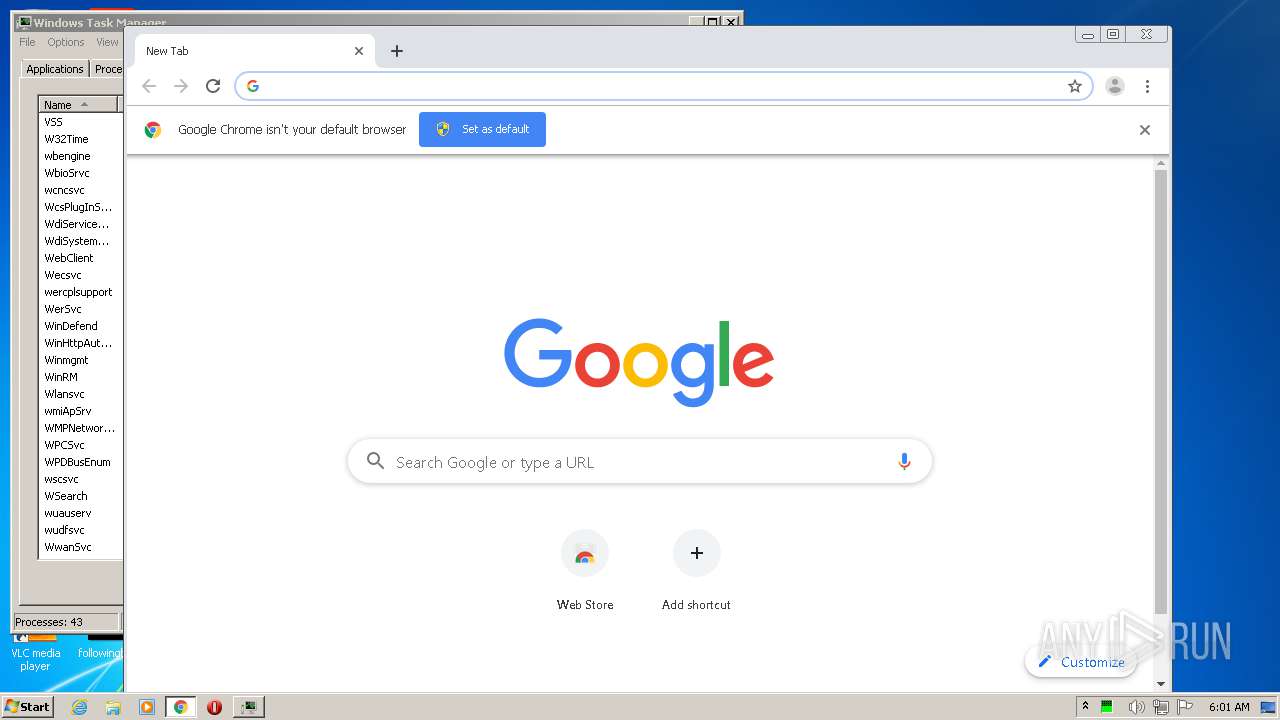
- chrome.exe (PID: 2284)
Reads internet explorer settings
- iexplore.exe (PID: 312)
- iexplore.exe (PID: 3024)
Reads settings of System Certificates
- iexplore.exe (PID: 312)
- iexplore.exe (PID: 3024)
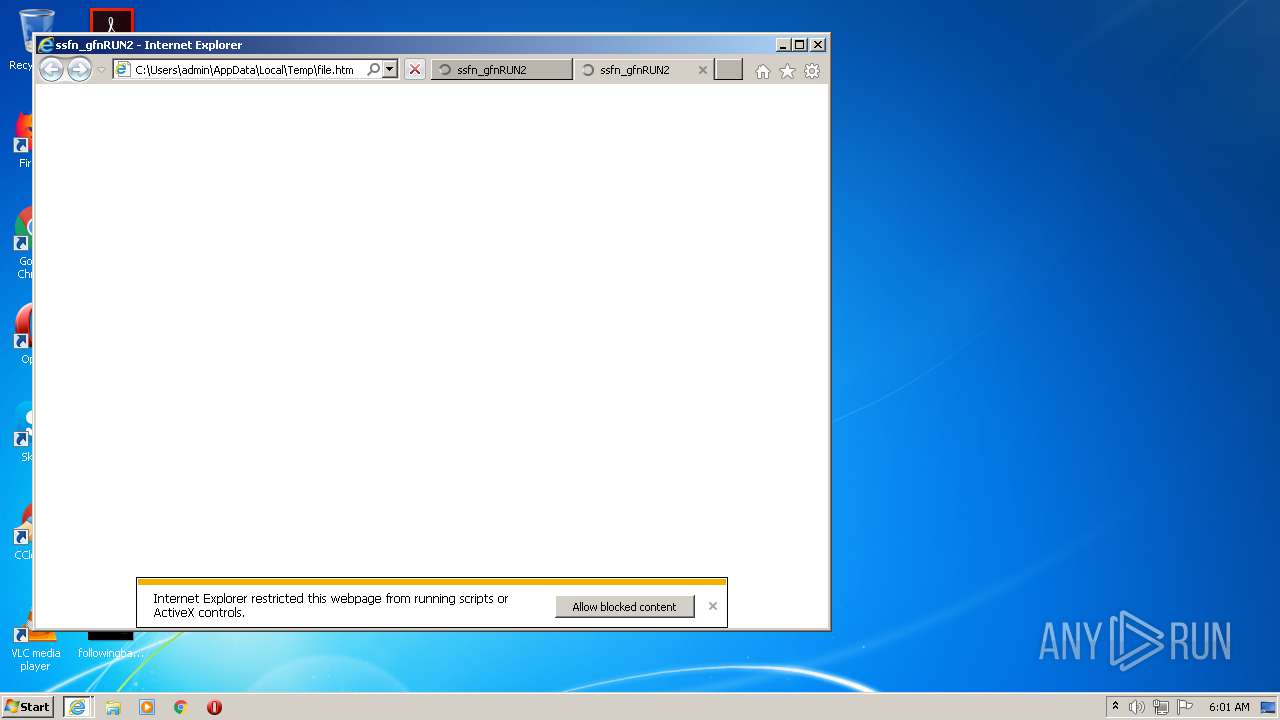
Changes internet zones settings
- iexplore.exe (PID: 2280)
Adds / modifies Windows certificates
- iexplore.exe (PID: 312)
- iexplore.exe (PID: 3024)
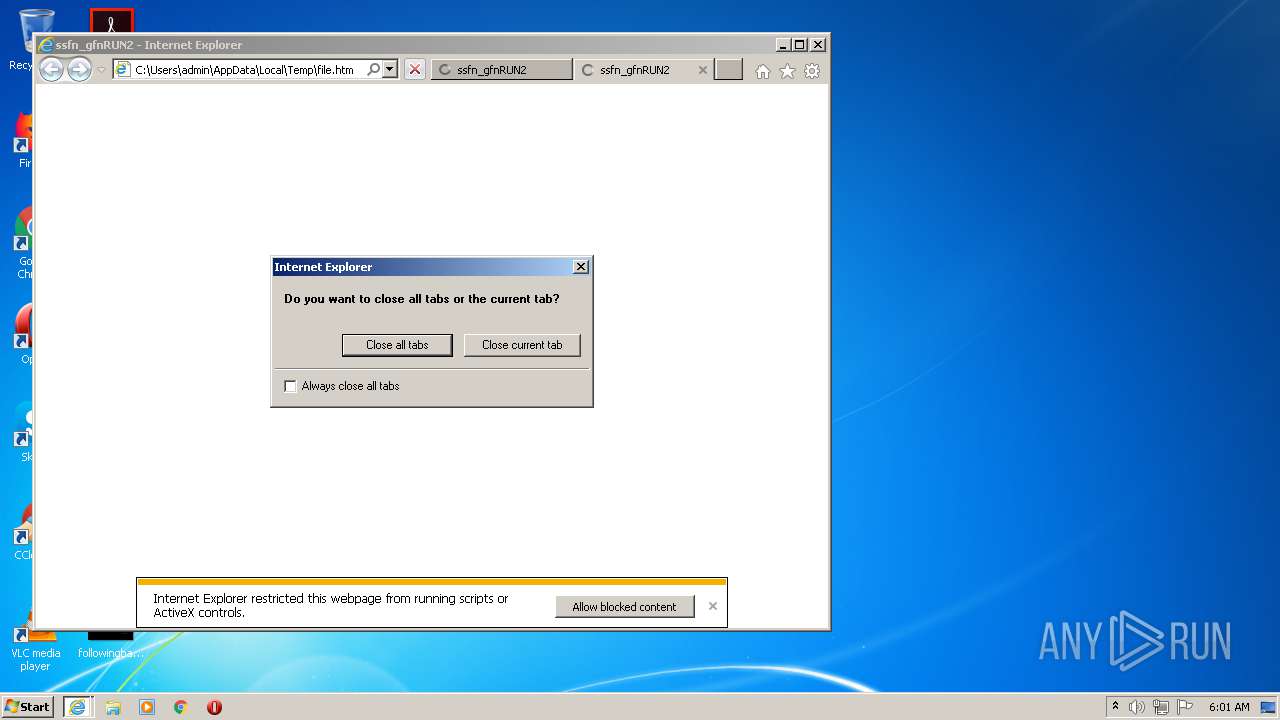
Application launched itself
- iexplore.exe (PID: 2280)
- chrome.exe (PID: 2284)
Changes settings of System certificates
- iexplore.exe (PID: 3024)
- iexplore.exe (PID: 312)
- chrome.exe (PID: 2628)
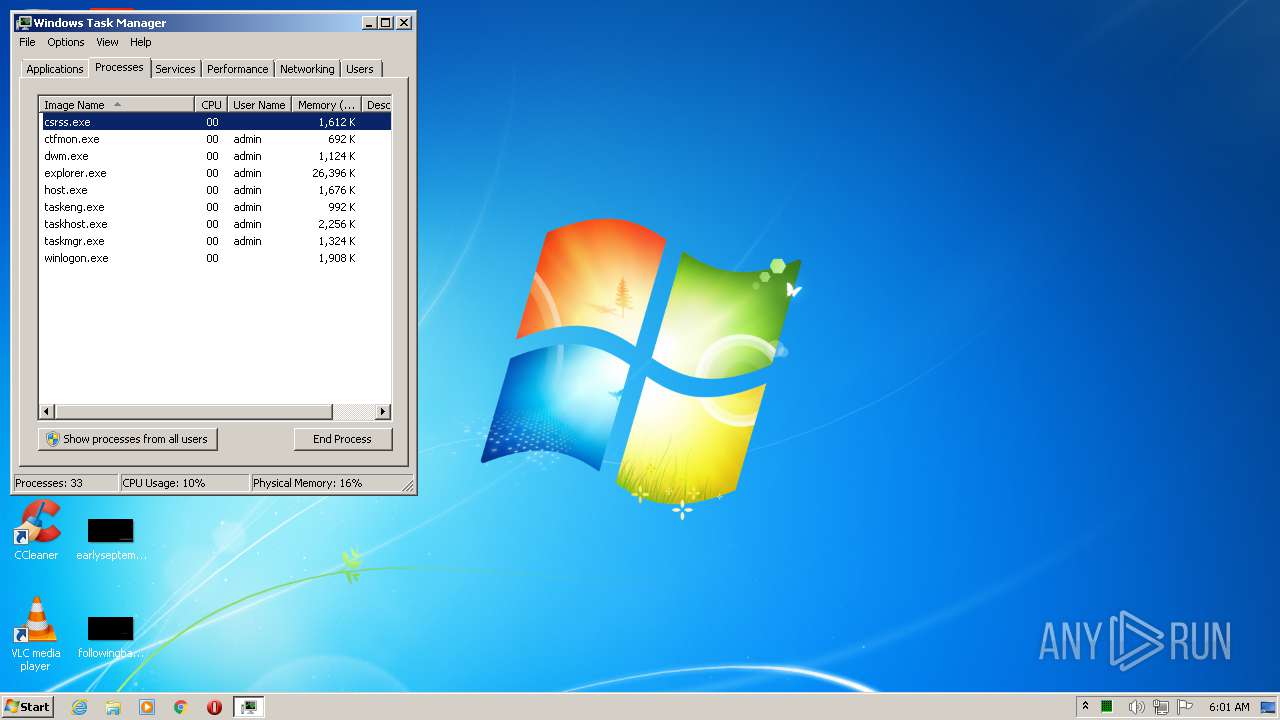
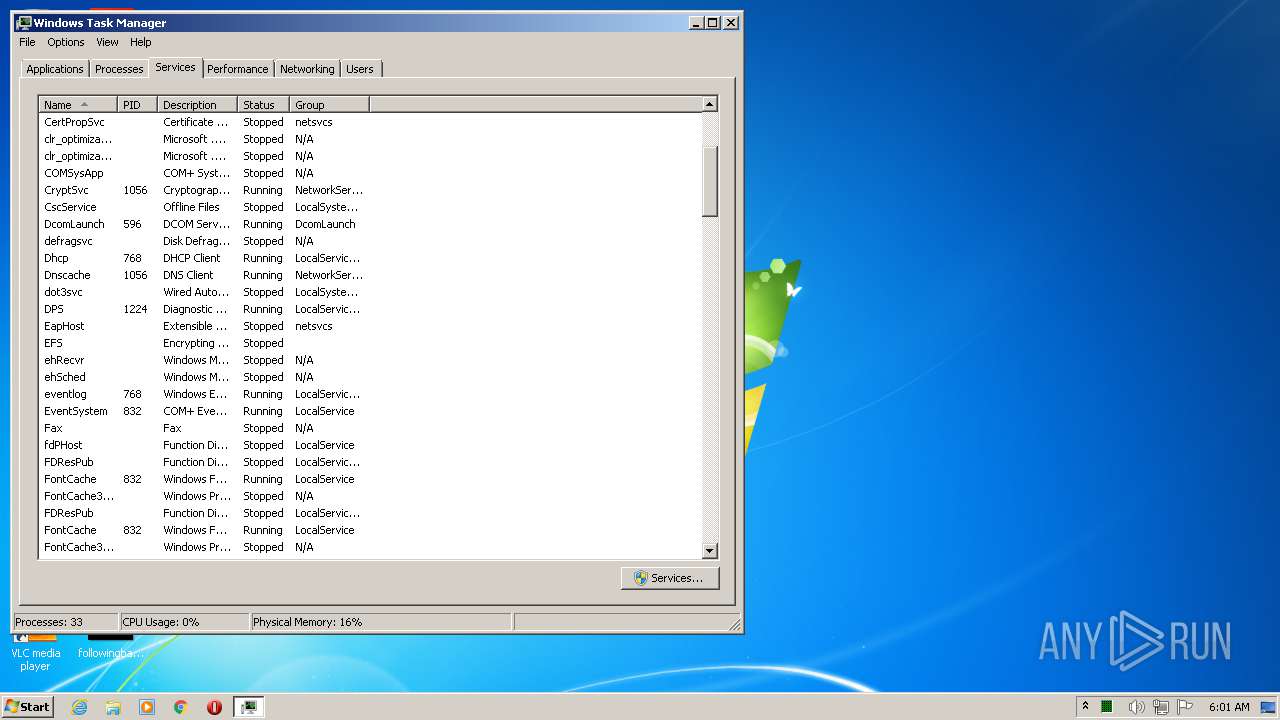
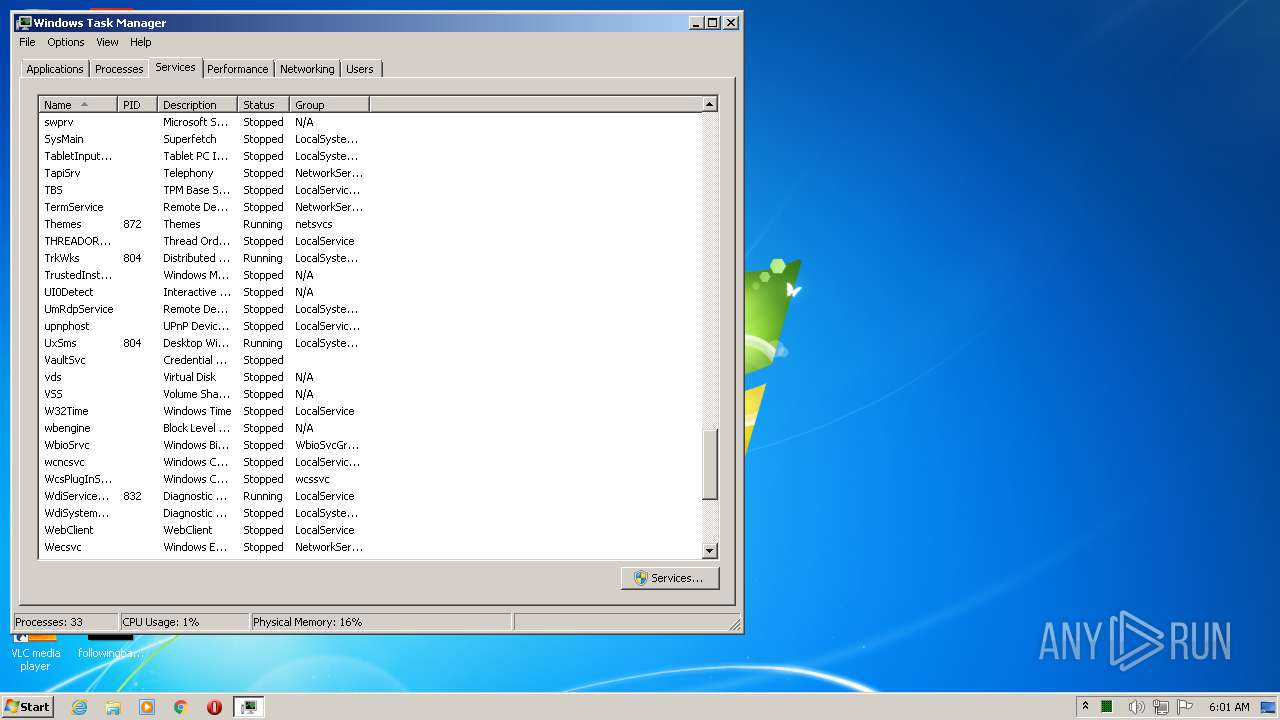
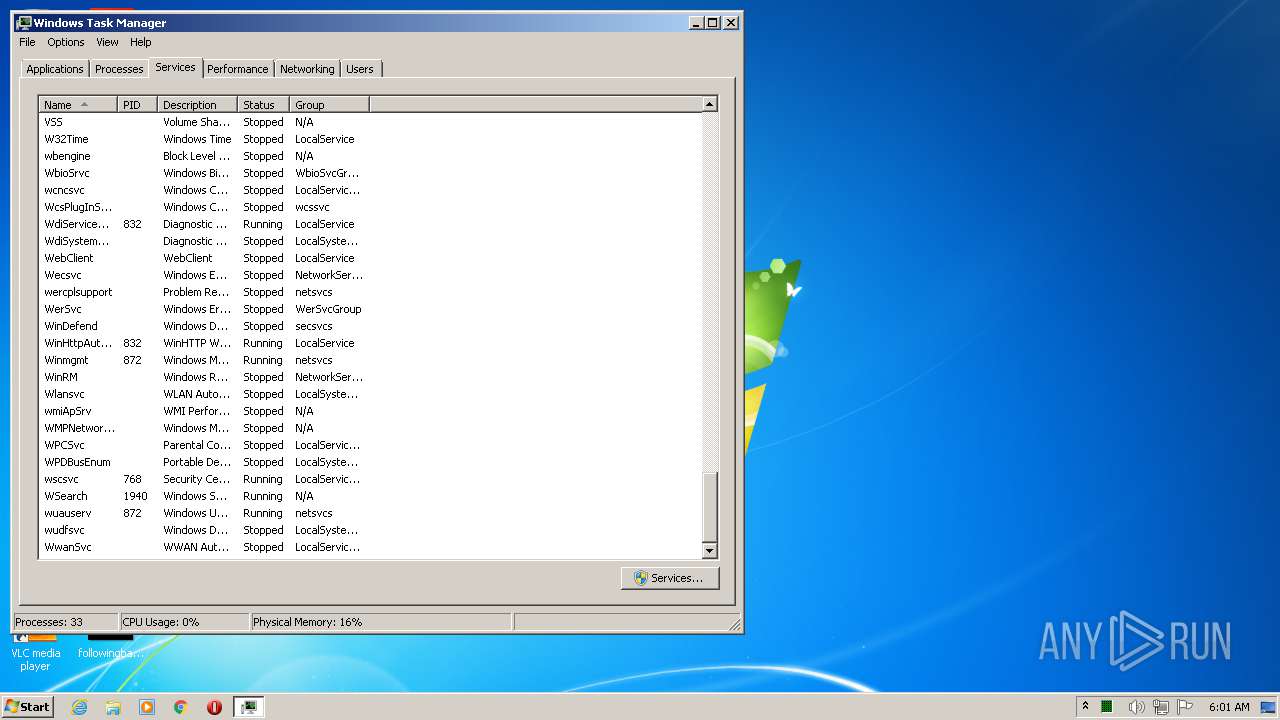
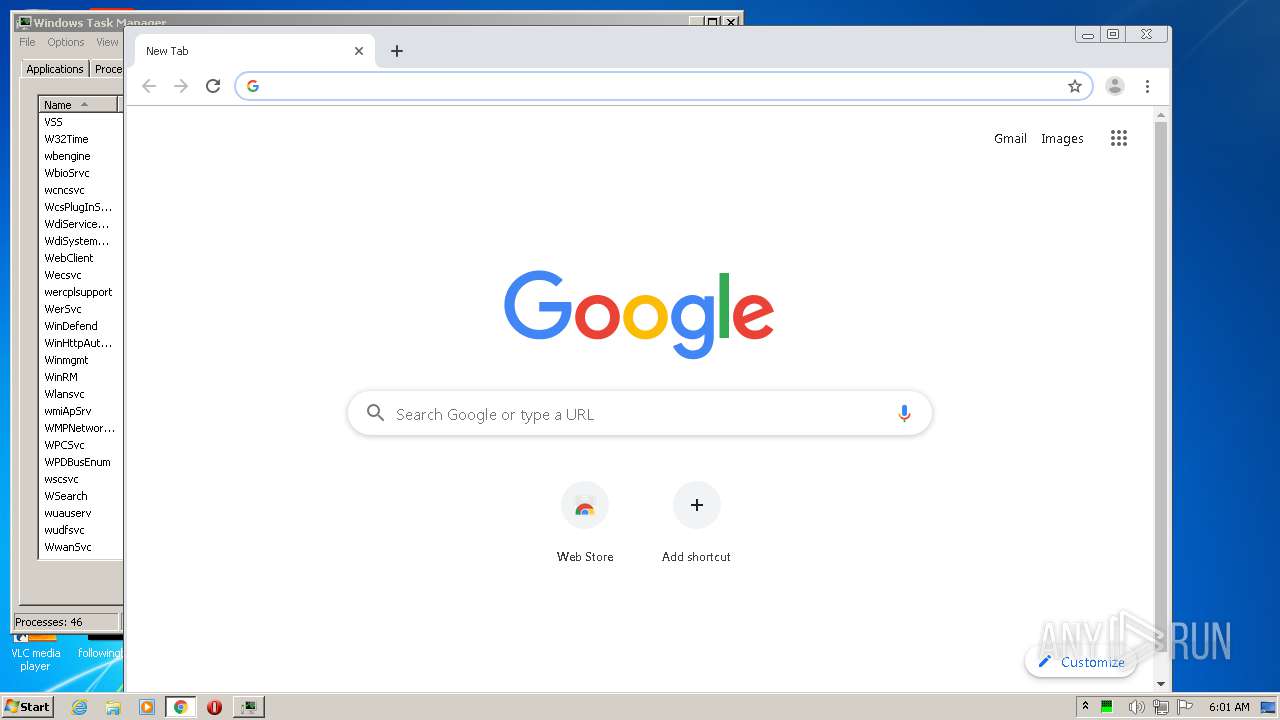
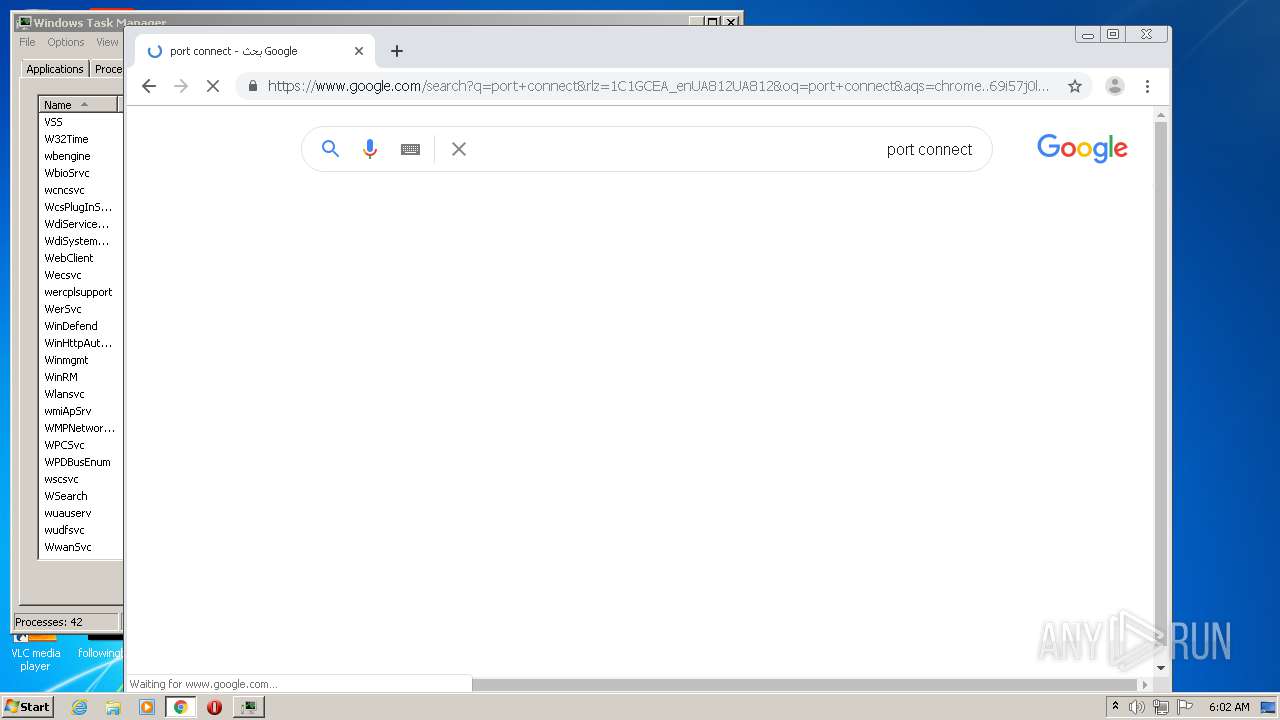
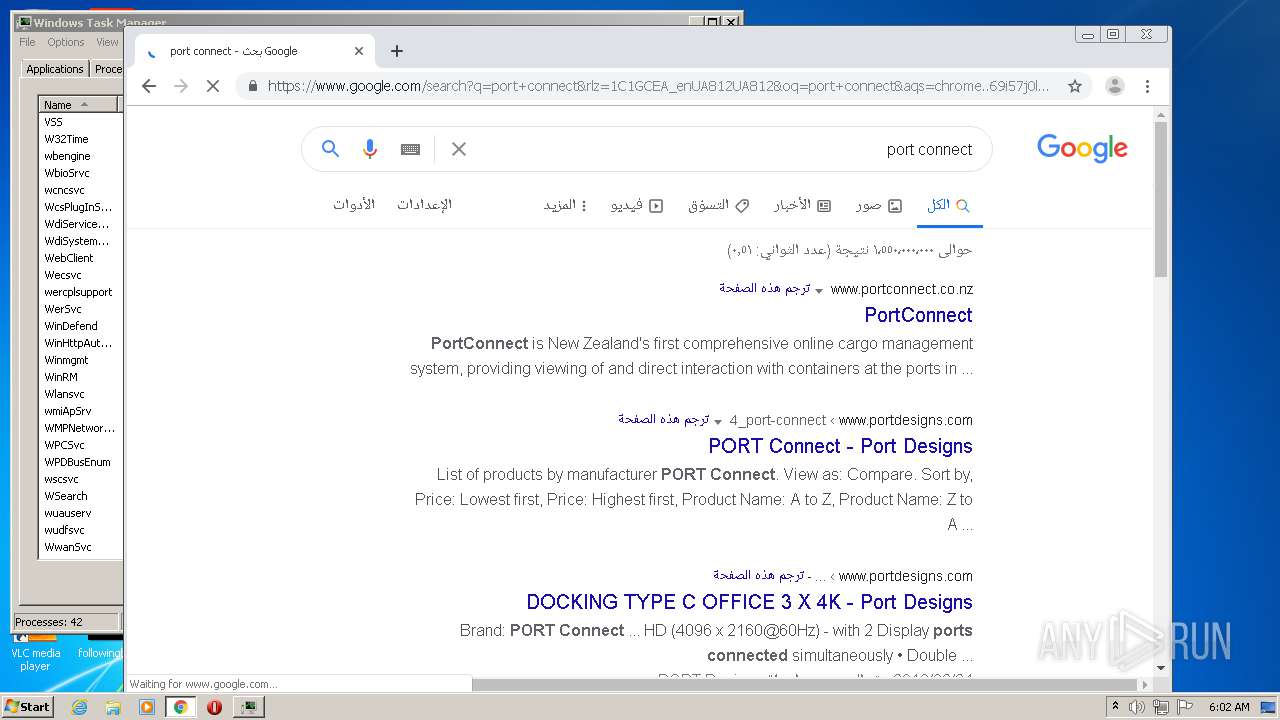
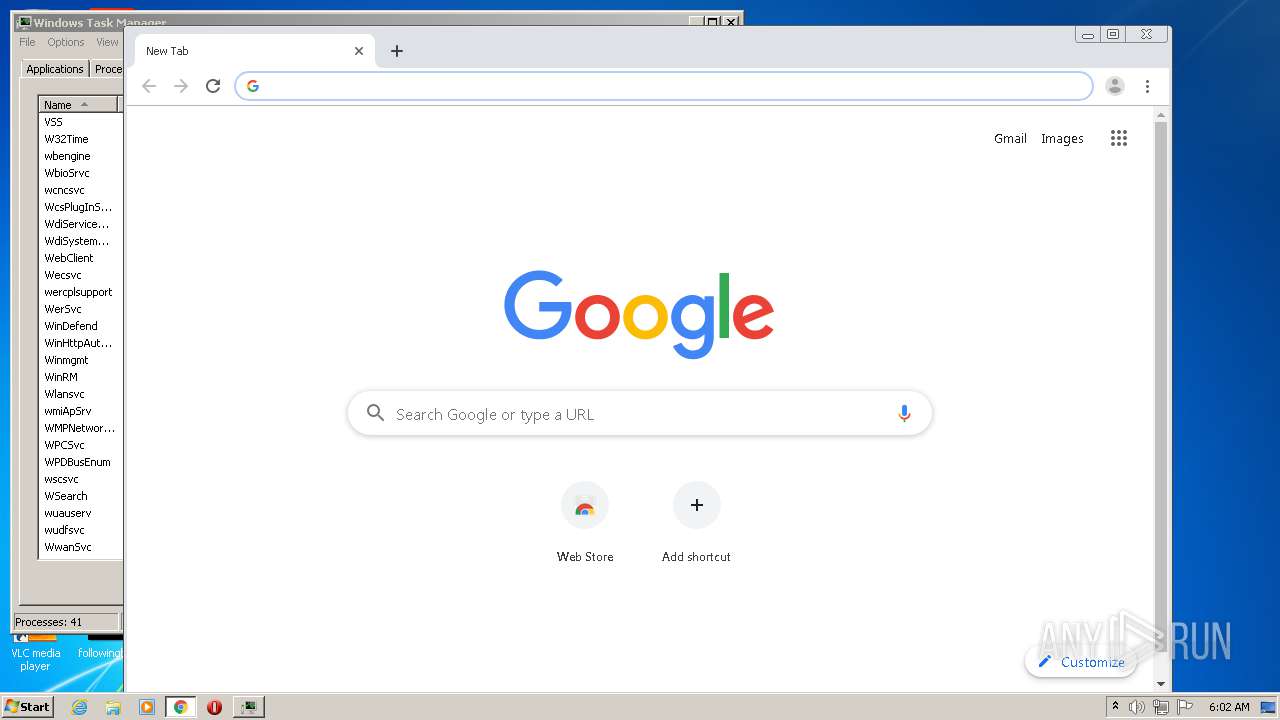
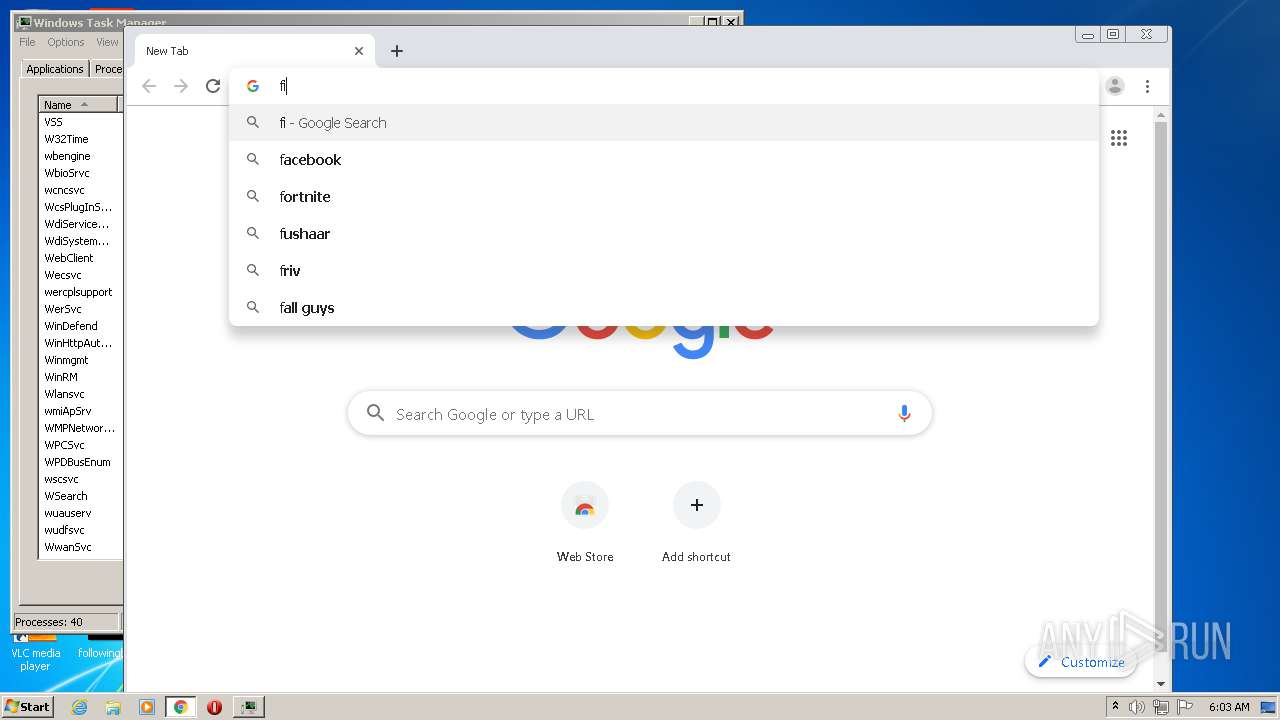
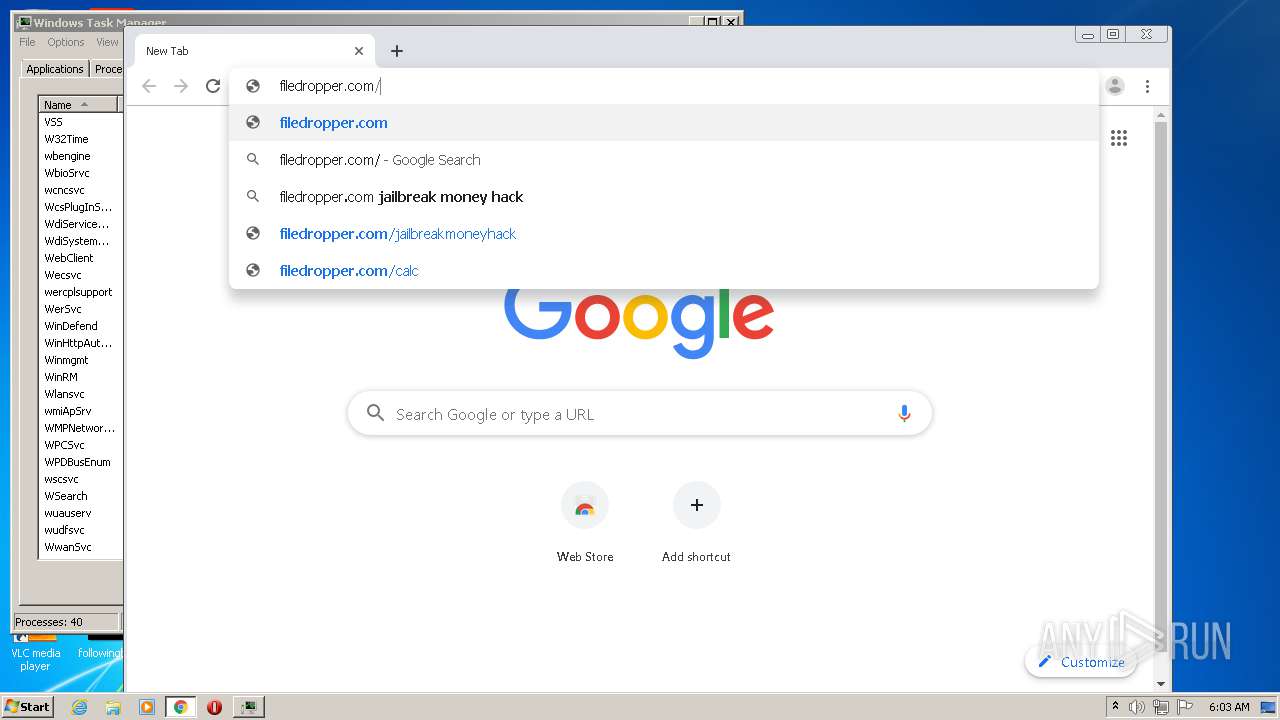
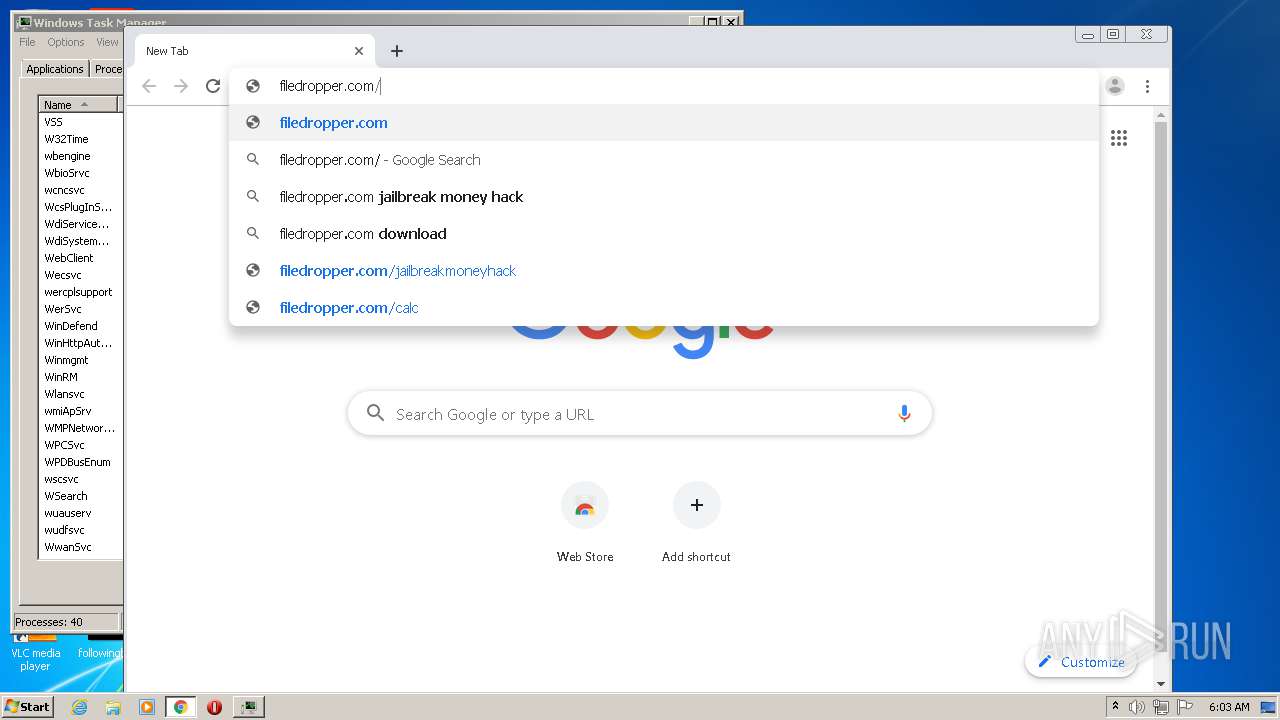
Manual execution by user
- taskmgr.exe (PID: 3692)
- chrome.exe (PID: 2284)
Reads the hosts file
- chrome.exe (PID: 2628)
- chrome.exe (PID: 2284)
Creates files in the user directory
- chrome.exe (PID: 2284)
Modifies the open verb of a shell class
- chrome.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
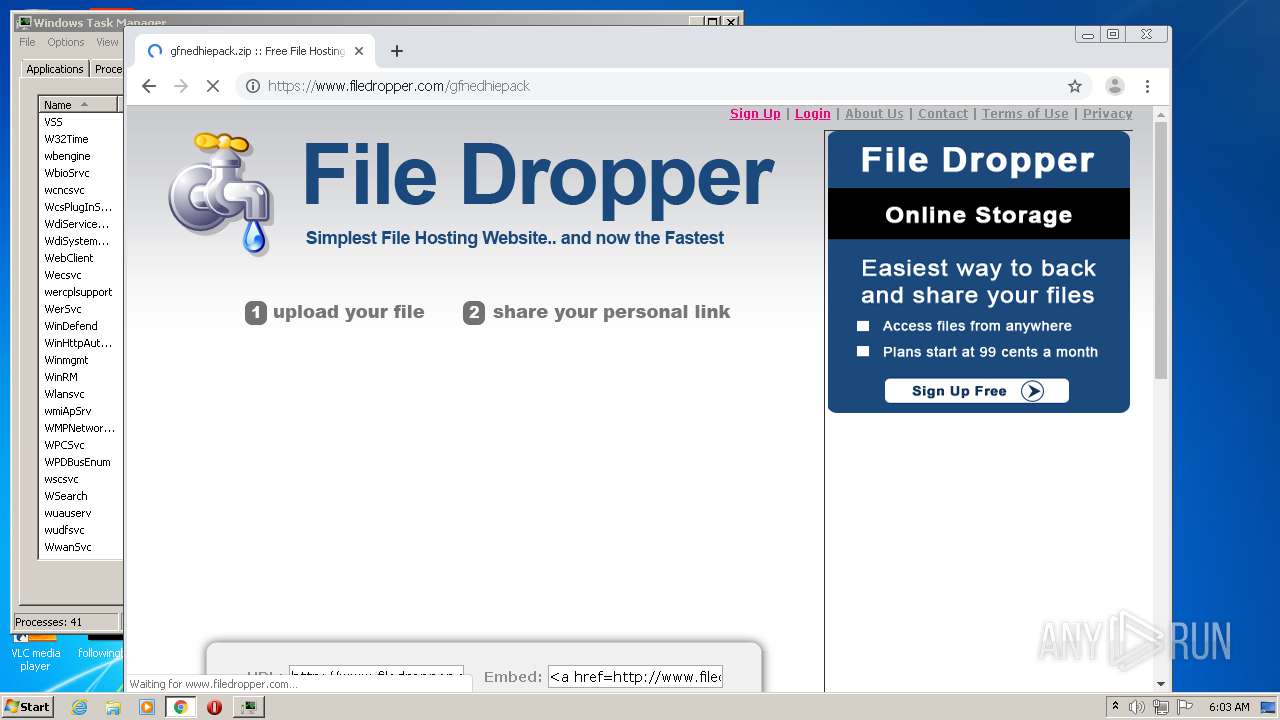
| twitterCard: | summary_large_image |
|---|---|
| twitterSite: | @MediaFire |
| twitterUrl: | http://www.mediafire.com/file/i0hl83myi4z7sdy/ssfn_gfnRUN2.bat/file |
| twitterTitle: | ssfn_gfnRUN2 |
| twitterImage: | https://static.mediafire.com/images/filetype/download/web.jpg |
| twitterDescription: | - |
Total processes
127
Monitored processes
80
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2280 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 444 | REG ADD HKLM\SOFTWARE\Policies\Microsoft\Windows\Personalization /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 556 | C:\Windows\system32\net1 user Administrator Geforce21!Latam | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 612 | net user Administrator Geforce21!Latam | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 624 | REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v legalnoticetext /t REG_SZ /d "El script ya se ejecuto iweputas" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8162957199024936116,1824315680177445520,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1678142822568324554 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,8162957199024936116,1824315680177445520,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15001026172548597040 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | REG ADD HKLM\SOFTWARE\Policies\Microsoft\Windows\Personalization /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f15a9d0,0x6f15a9e0,0x6f15a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8162957199024936116,1824315680177445520,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8055561005748049470 --mojo-platform-channel-handle=3376 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 472
Read events
2 165
Write events
295
Delete events
12
Modification events
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3133370950 | |||
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30840550 | |||
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2280) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
95
Suspicious files
143
Text files
155
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2280 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabE967.tmp | — | |
MD5:— | SHA256:— | |||
| 312 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarE968.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabEA51.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabEA52.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarEA53.tmp | — | |
MD5:— | SHA256:— | |||
| 3024 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarEA54.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA06F144A815676F4.TMP | — | |
MD5:— | SHA256:— | |||
| 2280 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB7AFC27F54252BF9.TMP | — | |
MD5:— | SHA256:— | |||
| 2280 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC73C3A7E617E0981.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
100
DNS requests
58
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
312 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAyDrs7o0RpNCAAAAABXoKo%3D | US | der | 471 b | whitelisted |
1056 | svchost.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCEyAAASWxwt68EQiA3cUAAAABJbE%3D | US | der | 1.75 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
312 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
312 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAyDrs7o0RpNCAAAAABXoKo%3D | US | der | 471 b | whitelisted |
312 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1056 | svchost.exe | GET | 200 | 67.27.159.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 2.21.38.54:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | FR | der | 813 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAKXB1YM1Knrv%2BJy8eCW2II%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
312 | iexplore.exe | 216.58.212.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
4 | System | 216.58.207.46:445 | translate.google.com | Google Inc. | US | whitelisted |
2280 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 216.58.207.46:139 | translate.google.com | Google Inc. | US | whitelisted |
312 | iexplore.exe | 172.217.22.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3024 | iexplore.exe | 216.58.212.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
4 | System | 104.16.203.237:445 | static.mediafire.com | Cloudflare Inc | US | unknown |
4 | System | 104.16.202.237:445 | static.mediafire.com | Cloudflare Inc | US | unknown |
1056 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1056 | svchost.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
static.mediafire.com |
| shared |
dns.msftncsi.com |
| shared |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |