| File name: | 4ddig-for-windows_11724295397347179801.exe |
| Full analysis: | https://app.any.run/tasks/1905c1f2-15bc-437d-9f77-e46e741ab7ef |
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2024, 06:48:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 8E3B7ABC869962322BCE3E02B761E07E |
| SHA1: | 975F886581586B303BF9109C0B2F0190FC49A222 |
| SHA256: | CB81E1A7022CACB4833C635646878D5FC5FF75A027127E6B0652AA2DCE50EE9D |
| SSDEEP: | 98304:vSBm3O8AMl5640fMlUV6q7cIdmjwrG4B2Pq+0fhgcIvuO0uOAEQvdPNR7YGeX/fo:9I26XI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks Windows Trust Settings
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- Tenorshare 4DDiG.exe (PID: 2572)
Reads the Windows owner or organization settings
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
Executable content was dropped or overwritten
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- AnyDataRecovery_4ddig_10.1.8.exe (PID: 6668)
- Tenorshare 4DDiG.exe (PID: 2572)
- 7z.exe (PID: 6632)
Drops the executable file immediately after the start
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- AnyDataRecovery_4ddig_10.1.8.exe (PID: 6668)
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- Tenorshare 4DDiG.exe (PID: 2572)
- TenorshareUpdateAssistantService.exe (PID: 4592)
- 7z.exe (PID: 6632)
Checks for external IP
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- svchost.exe (PID: 2256)
Reads security settings of Internet Explorer
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- NetFrameCheck.exe (PID: 4016)
- Tenorshare 4DDiG.exe (PID: 2572)
- TenorshareUpdateAssistantService.exe (PID: 4592)
Potential Corporate Privacy Violation
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- Tenorshare 4DDiG.exe (PID: 2572)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2252)
- cmd.exe (PID: 6924)
Reads the date of Windows installation
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- NetFrameCheck.exe (PID: 4016)
- Tenorshare 4DDiG.exe (PID: 2572)
- TenorshareUpdateAssistantService.exe (PID: 4592)
Starts CMD.EXE for commands execution
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- Tenorshare 4DDiG.exe (PID: 2572)
- TenorshareUpdateAssistantService.exe (PID: 4592)
The process drops C-runtime libraries
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 7148)
- cmd.exe (PID: 1644)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 5300)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 3692)
- cmd.exe (PID: 2616)
- cmd.exe (PID: 5524)
- cmd.exe (PID: 5708)
Drops 7-zip archiver for unpacking
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- Tenorshare 4DDiG.exe (PID: 2572)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 368)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 2580)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 3832)
- cmd.exe (PID: 6052)
- cmd.exe (PID: 1680)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 1744)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 5956)
- cmd.exe (PID: 6300)
- cmd.exe (PID: 6256)
- cmd.exe (PID: 6396)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 5888)
Process drops legitimate windows executable
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
Creates a software uninstall entry
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- Tenorshare 4DDiG.exe (PID: 2572)
Searches for installed software
- Tenorshare 4DDiG.exe (PID: 2572)
Changes Internet Explorer settings (feature browser emulation)
- Tenorshare 4DDiG.exe (PID: 2572)
The process deletes folder without confirmation
- Tenorshare 4DDiG.exe (PID: 2572)
Executes as Windows Service
- TenorshareUpdateAssistantService.exe (PID: 4592)
Executes application which crashes
- TenorshareUpdateAssistantService.exe (PID: 4592)
INFO
UPX packer has been detected
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
Creates files or folders in the user directory
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- Tenorshare 4DDiG.exe (PID: 2572)
Checks supported languages
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- AnyDataRecovery_4ddig_10.1.8.exe (PID: 6668)
- Tenorshare 4DDiG.exe (PID: 2572)
- NetFrameCheck.exe (PID: 4016)
- TaskbarTest.exe (PID: 2136)
- MsgSupportService.exe (PID: 4024)
- UpdateService.exe (PID: 608)
- DeviceViewerService.exe (PID: 3800)
- identity_helper.exe (PID: 6760)
- svcmgr.exe (PID: 7148)
- TenorshareUpdateAssistantService.exe (PID: 4592)
- TenorshareUpdateAssistant.exe (PID: 6468)
- svcmgr.exe (PID: 5520)
- 7z.exe (PID: 6632)
- svcmgr.exe (PID: 6272)
- identity_helper.exe (PID: 6668)
- svcmgr.exe (PID: 2136)
Checks proxy server information
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- Tenorshare 4DDiG.exe (PID: 2572)
Reads the computer name
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- NetFrameCheck.exe (PID: 4016)
- Tenorshare 4DDiG.exe (PID: 2572)
- TaskbarTest.exe (PID: 2136)
- UpdateService.exe (PID: 608)
- MsgSupportService.exe (PID: 4024)
- DeviceViewerService.exe (PID: 3800)
- identity_helper.exe (PID: 6760)
- svcmgr.exe (PID: 7148)
- svcmgr.exe (PID: 5520)
- TenorshareUpdateAssistantService.exe (PID: 4592)
- 7z.exe (PID: 6632)
- svcmgr.exe (PID: 6272)
- identity_helper.exe (PID: 6668)
- svcmgr.exe (PID: 2136)
Create files in a temporary directory
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- AnyDataRecovery_4ddig_10.1.8.exe (PID: 6668)
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- Tenorshare 4DDiG.exe (PID: 2572)
Reads Environment values
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- Tenorshare 4DDiG.exe (PID: 2572)
- identity_helper.exe (PID: 6760)
- identity_helper.exe (PID: 6668)
Reads the machine GUID from the registry
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- Tenorshare 4DDiG.exe (PID: 2572)
- TaskbarTest.exe (PID: 2136)
- UpdateService.exe (PID: 608)
- MsgSupportService.exe (PID: 4024)
Creates files in the program directory
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- NetFrameCheck.exe (PID: 4016)
- UpdateService.exe (PID: 608)
- Tenorshare 4DDiG.exe (PID: 2572)
- DeviceViewerService.exe (PID: 3800)
- MsgSupportService.exe (PID: 4024)
- svcmgr.exe (PID: 7148)
- TenorshareUpdateAssistantService.exe (PID: 4592)
- 7z.exe (PID: 6632)
Reads the software policy settings
- 4ddig-for-windows_11724295397347179801.exe (PID: 6676)
- Tenorshare 4DDiG.exe (PID: 2572)
- TenorshareUpdateAssistantService.exe (PID: 4592)
- WerFault.exe (PID: 2768)
Process checks computer location settings
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
- NetFrameCheck.exe (PID: 4016)
- Tenorshare 4DDiG.exe (PID: 2572)
Creates a software uninstall entry
- AnyDataRecovery_4ddig_10.1.8.tmp (PID: 3164)
Disables trace logs
- Tenorshare 4DDiG.exe (PID: 2572)
Reads Microsoft Office registry keys
- Tenorshare 4DDiG.exe (PID: 2572)
- msedge.exe (PID: 4528)
- msedge.exe (PID: 6344)
- msedge.exe (PID: 3448)
Application launched itself
- msedge.exe (PID: 4528)
- msedge.exe (PID: 6344)
- msedge.exe (PID: 3448)
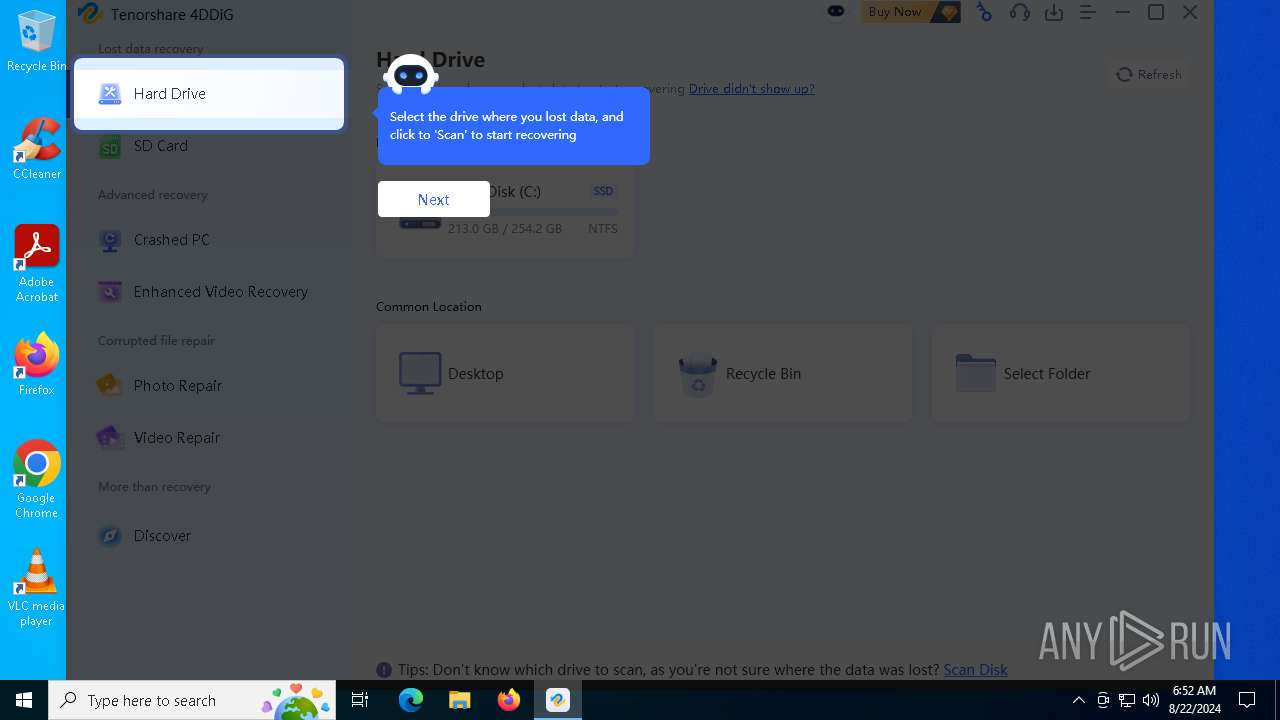
Manual execution by a user
- msedge.exe (PID: 6344)
.NET Reactor protector has been detected
- Tenorshare 4DDiG.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:04:02 04:13:48+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1454080 |
| InitializedDataSize: | 630784 |
| UninitializedDataSize: | 2342912 |
| EntryPoint: | 0x39f9f0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.8.4.5 |
| ProductVersionNumber: | 2.8.4.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Tenorshare |
| FileDescription: | Tenorshare 4DDiG |
| FileVersion: | 2.8.4.5 |
| LegalCopyright: | Copyright © 2007-2024 TENORSHARE(HONGKONG)LIMITED All Rights Reserved. |
| ProductName: | 20240402121317 |
| ProductVersion: | 2.8.4.5 |
Total processes
341
Monitored processes
199
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5012 --field-trial-handle=2332,i,10084870807924996307,9684885246853441525,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 252 | taskkill /f /t /im "TaskbarTest.exe" | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | taskkill /f /t /im "DeviceViewerService.exe" | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | "C:\WINDOWS\system32\cmd.exe" /c netsh advfirewall firewall add rule name="Tenorshare 4DDiG_NetFrameCheck" dir=out action=allow program="C:\Program Files (x86)\Tenorshare\Tenorshare 4DDiG\NetFrameCheck.exe" enable=yes | C:\Windows\SysWOW64\cmd.exe | — | AnyDataRecovery_4ddig_10.1.8.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | taskkill /f /t /im "Mp4FrameScanService.exe" | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | netsh advfirewall firewall add rule name="Tenorshare 4DDiG_UpdateService" dir=in action=allow program="C:\Program Files (x86)\Tenorshare\Tenorshare 4DDiG\UpdateService.exe" enable=yes | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 400 | taskkill /f /t /im "DataPreviewService.exe" | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
55 746
Read events
55 483
Write events
246
Delete events
17
Modification events
| (PID) Process: | (6676) 4ddig-for-windows_11724295397347179801.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Tenorshare\Downloader2.5.0 |
| Operation: | write | Name: | GA_PC |
Value: 1 | |||
| (PID) Process: | (6676) 4ddig-for-windows_11724295397347179801.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6676) 4ddig-for-windows_11724295397347179801.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6676) 4ddig-for-windows_11724295397347179801.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6676) 4ddig-for-windows_11724295397347179801.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6676) 4ddig-for-windows_11724295397347179801.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GuidGuidold |
| Operation: | write | Name: | guid |
Value: 1A1D6BA7-9571-452E-979C-531F1600FD54 | |||
| (PID) Process: | (6676) 4ddig-for-windows_11724295397347179801.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GuidGuidold |
| Operation: | write | Name: | user_id |
Value: 1001 | |||
| (PID) Process: | (3164) AnyDataRecovery_4ddig_10.1.8.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 5C0C0000FBB3CA805FF4DA01 | |||
| (PID) Process: | (3164) AnyDataRecovery_4ddig_10.1.8.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 7D0C79560A227C582528A490C36A9D96E3D33C6C6483DDBADD49721F08C6A7D5 | |||
| (PID) Process: | (3164) AnyDataRecovery_4ddig_10.1.8.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
Executable files
512
Suspicious files
345
Text files
183
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6676 | 4ddig-for-windows_11724295397347179801.exe | C:\Users\admin\AppData\Local\Temp\AnyDataRecovery_4ddig\AnyDataRecovery_4ddig_10.1.8.exe | — | |
MD5:— | SHA256:— | |||
| 6676 | 4ddig-for-windows_11724295397347179801.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3E3E9689537B6B136ECF210088069D55_EF6C9357BB54DDB629FD2D79F1594F95 | binary | |
MD5:FF30414C66412BA4053CC4E82323050B | SHA256:EB450306BA03F11C50278A787F73D48BD948BA3339A5C803B7AA42CBF4A83ED8 | |||
| 6676 | 4ddig-for-windows_11724295397347179801.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3E3E9689537B6B136ECF210088069D55_EF6C9357BB54DDB629FD2D79F1594F95 | binary | |
MD5:B07113D9CED5613667DF7E52950725FC | SHA256:47CA7A6EAD7EF7433E7A60830E266980DFDB667B9B3CD61721B749A749C1B5BD | |||
| 6676 | 4ddig-for-windows_11724295397347179801.exe | C:\Users\admin\AppData\Local\Temp\AnyDataRecovery_4ddig\galog.json | binary | |
MD5:03BDC9E076B465F0D1198D8F8E7E8ABB | SHA256:487ACCCEB120DE8F3220F4F57A24734F14C47E1A6F5E9F133D7296F2AC55CB4B | |||
| 6668 | AnyDataRecovery_4ddig_10.1.8.exe | C:\Users\admin\AppData\Local\Temp\is-FGNBR.tmp\AnyDataRecovery_4ddig_10.1.8.tmp | executable | |
MD5:E14905188B05532183C5EDB95ECF5DD5 | SHA256:B4E77FDA37E556B7B1E9910534D3F6339FF9DEBD82CCF0F59FDEDC02C40B8CC5 | |||
| 3164 | AnyDataRecovery_4ddig_10.1.8.tmp | C:\Users\admin\AppData\Local\Temp\is-590P9.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 6676 | 4ddig-for-windows_11724295397347179801.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_234E9B04AA8520A2E6CE0C38C9A1AE0D | binary | |
MD5:DB2F234E7466FAEB7592E17AD0BB10E9 | SHA256:7697C315F9DD896491B75324C36C6A4A62A9CF15780C11F0FC75E9EA936BF20B | |||
| 6676 | 4ddig-for-windows_11724295397347179801.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_FB287BEB63DB9E8D59A799779773B97C | der | |
MD5:9C1A110E6E36877C39A55812E443C0E7 | SHA256:63B47FBE6D6BE583F93A43EA5AF3214A929F176980EEE5595C28CA54E9B78F6F | |||
| 6676 | 4ddig-for-windows_11724295397347179801.exe | C:\Users\admin\AppData\Local\Temp\AnyDataRecovery_4ddig\AnyDataRecovery_4ddig_10.1.8.exe.db | text | |
MD5:5B264966A4145776A8F6A59D7D14E6A5 | SHA256:668ADDB98F99F4D3C58A29A054089ADD005FF109ABC2117117F8DF640589DC42 | |||
| 3164 | AnyDataRecovery_4ddig_10.1.8.tmp | C:\Program Files (x86)\Tenorshare\Tenorshare 4DDiG\unins000.exe | executable | |
MD5:E14905188B05532183C5EDB95ECF5DD5 | SHA256:B4E77FDA37E556B7B1E9910534D3F6339FF9DEBD82CCF0F59FDEDC02C40B8CC5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
273
DNS requests
121
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6676 | 4ddig-for-windows_11724295397347179801.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/csv | unknown | — | — | shared |
6676 | 4ddig-for-windows_11724295397347179801.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAhflMAthXvozBT%2FU%2B2iPio%3D | unknown | — | — | whitelisted |
7108 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2572 | Tenorshare 4DDiG.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6836 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6676 | 4ddig-for-windows_11724295397347179801.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEARYZUnCRNUh%2FxJ46JuiO9M%3D | unknown | — | — | whitelisted |
6676 | 4ddig-for-windows_11724295397347179801.exe | GET | 301 | 104.17.192.141:80 | http://www.tenorshare.com/downloads/service/softwarelog.txt | unknown | — | — | whitelisted |
2572 | Tenorshare 4DDiG.exe | GET | 301 | 104.18.24.249:80 | http://update.tenorshare.com/update?&a=u&lang=en&pid=2959&platform=win&v=10.1.8.1&verify=2C48F818CECFF1031C40B3EEA6DC8A5B&package_type=2 | unknown | — | — | whitelisted |
6676 | 4ddig-for-windows_11724295397347179801.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTjzY2p9Pa8oibmj%2BNSMWsz63kmWgQUuhbZbU2FL3MpdpovdYxqII%2BeyG8CEAVEr%2FOUnQg5pr%2FbP1%2FlYRY%3D | unknown | — | — | whitelisted |
2572 | Tenorshare 4DDiG.exe | GET | 200 | 142.250.184.227:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1556 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5284 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6676 | 4ddig-for-windows_11724295397347179801.exe | 104.18.24.249:443 | update.tenorshare.com | CLOUDFLARENET | — | unknown |
6676 | 4ddig-for-windows_11724295397347179801.exe | 104.18.3.37:443 | data-service.afirstsoft.cn | CLOUDFLARENET | — | unknown |
6676 | 4ddig-for-windows_11724295397347179801.exe | 104.17.192.141:80 | www.tenorshare.com | CLOUDFLARENET | — | unknown |
6676 | 4ddig-for-windows_11724295397347179801.exe | 104.17.192.141:443 | www.tenorshare.com | CLOUDFLARENET | — | unknown |
6676 | 4ddig-for-windows_11724295397347179801.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6676 | 4ddig-for-windows_11724295397347179801.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
update.tenorshare.com |
| unknown |
data-service.afirstsoft.cn |
| unknown |
www.tenorshare.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ip-api.com |
| shared |
www.google-analytics.com |
| whitelisted |
analytics.afirstsoft.cn |
| unknown |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6676 | 4ddig-for-windows_11724295397347179801.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
2256 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6676 | 4ddig-for-windows_11724295397347179801.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
6676 | 4ddig-for-windows_11724295397347179801.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6648 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6648 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6648 | msedge.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6648 | msedge.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2572 | Tenorshare 4DDiG.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3 ETPRO signatures available at the full report