| File name: | LMIRescue.exe |
| Full analysis: | https://app.any.run/tasks/bd7df345-ff1f-4deb-b283-663b8031dbaa |
| Verdict: | Suspicious activity |
| Analysis date: | January 19, 2020, 16:44:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 986A2825D1D41A862990205B00D6651E |
| SHA1: | 2CACB915D1184B5F20DF9A612E643945E64F6215 |
| SHA256: | CB77A4E2AC7843D8E7CAC673422E9FF8C3F80D39ED5705C0788D4111F2E9C46F |
| SSDEEP: | 49152:5Ae49jsvHXDItLN7trxLL5DjxYdId/AtS7frN0bZGI/s:Ges2HXDcLfrxxPOKdIYDmb6 |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 352)
- ctfmon.exe (PID: 708)
- LMI_Rescue.exe (PID: 2864)
- DllHost.exe (PID: 2356)
Application was dropped or rewritten from another process
- LMI_Rescue.exe (PID: 2864)
Changes the autorun value in the registry
- LMI_Rescue.exe (PID: 2864)
SUSPICIOUS
Executable content was dropped or overwritten
- LMIRescue.exe (PID: 956)
INFO
Reads settings of System Certificates
- LMI_Rescue.exe (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:07 10:41:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 80384 |
| InitializedDataSize: | 2096640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3c00 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.11.417.2117 |
| ProductVersionNumber: | 7.11.417.2117 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | LogMeIn, Inc. |
| FileDescription: | LogMeIn Rescue |
| FileVersion: | 7.11.417 |
| InternalName: | Rescue |
| LegalCopyright: | Copyright © 2005-2018 LogMeIn, Inc. US patents pending. |
| OriginalFileName: | LMIRescue.exe |
| ProductName: | LogMeIn Rescue |
| ProductVersion: | 7.11.417 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Mar-2019 09:41:00 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | LogMeIn, Inc. |
| FileDescription: | LogMeIn Rescue |
| FileVersion: | 7.11.417 |
| InternalName: | Rescue |
| LegalCopyright: | Copyright © 2005-2018 LogMeIn, Inc. US patents pending. |
| OriginalFilename: | LMIRescue.exe |
| ProductName: | LogMeIn Rescue |
| ProductVersion: | 7.11.417 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 07-Mar-2019 09:41:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001394B | 0x00013A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62938 |
.rdata | 0x00015000 | 0x00006DCA | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.28398 |
.data | 0x0001C000 | 0x000017E8 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.05438 |
.gfids | 0x0001E000 | 0x000000AC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.4653 |
.rsrc | 0x0001F000 | 0x001F73E8 | 0x001F7400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.9993 |
.reloc | 0x00217000 | 0x00001180 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.54654 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2384 | 1077 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.21887 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
10000 | 5.04239 | 420 | Latin 1 / Western European | English - United States | RT_RCDATA |
10001 | 5.40254 | 7606 | Latin 1 / Western European | English - United States | RT_RCDATA |
10006 | 2.71862 | 894 | Latin 1 / Western European | English - United States | RT_RCDATA |
32000 | 7.99992 | 2047355 | Latin 1 / Western European | English - United States | RT_RCDATA |
IDI_RESCUE | 2.38595 | 34 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
36
Monitored processes
5
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 708 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Users\admin\Desktop\LMIRescue.exe" | C:\Users\admin\Desktop\LMIRescue.exe | explorer.exe | ||||||||||||
User: admin Company: LogMeIn, Inc. Integrity Level: MEDIUM Description: LogMeIn Rescue Exit code: 0 Version: 7.11.417 Modules
| |||||||||||||||
| 2356 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\LMI_Rescue.exe" | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\LMI_Rescue.exe | LMIRescue.exe | ||||||||||||
User: admin Company: LogMeIn, Inc. Integrity Level: MEDIUM Description: LogMeIn Rescue Exit code: 0 Version: 7.11.417 Modules
| |||||||||||||||
Total events
879
Read events
861
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2864) LMI_Rescue.exe | Key: | HKEY_CLASSES_ROOT\Applications\LMI_Rescue.exe |
| Operation: | write | Name: | IsHostApp |
Value: | |||
| (PID) Process: | (2864) LMI_Rescue.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | *LogMeInRescue_2270699220 |
Value: "C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\LMI_Rescue.exe" -runonce reboot | |||
| (PID) Process: | (2864) LMI_Rescue.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2864) LMI_Rescue.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2864) LMI_Rescue.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2864) LMI_Rescue.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (2864) LMI_Rescue.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (2864) LMI_Rescue.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (2356) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
Executable files
6
Suspicious files
36
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 956 | LMIRescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\logo.bmp | image | |
MD5:— | SHA256:— | |||
| 956 | LMIRescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\RescueWinRTLib.dll | executable | |
MD5:FDCDB3078CC75C395D2BB874BE31E373 | SHA256:2326A4AFF877BE4E8327DA666C70BB1CA470C9375184C7E18E5D83DD86012EB0 | |||
| 956 | LMIRescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\rahook.dll | executable | |
MD5:FFE784EBCA0B49748134160A1F0F387F | SHA256:74BD758A23B2420104401B0D6C24CDED240720E988BF184CD4F55CBE8B50CB66 | |||
| 956 | LMIRescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\LMI_RescueRC.exe | executable | |
MD5:C2B3918B262FD9ADEEAF4D6ED6753532 | SHA256:DC06B9884DE7EF876BCE15A68F281110CD248080F1D0E9B7E1FC3ACC1D5C52DF | |||
| 2864 | LMI_Rescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\rescue.info | binary | |
MD5:— | SHA256:— | |||
| 2864 | LMI_Rescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\rescue.log | binary | |
MD5:— | SHA256:— | |||
| 956 | LMIRescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\rescue.ico | image | |
MD5:— | SHA256:— | |||
| 2864 | LMI_Rescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\session.log | text | |
MD5:— | SHA256:— | |||
| 956 | LMIRescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\params.txt | text | |
MD5:— | SHA256:— | |||
| 2864 | LMI_Rescue.exe | C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\chatlog.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
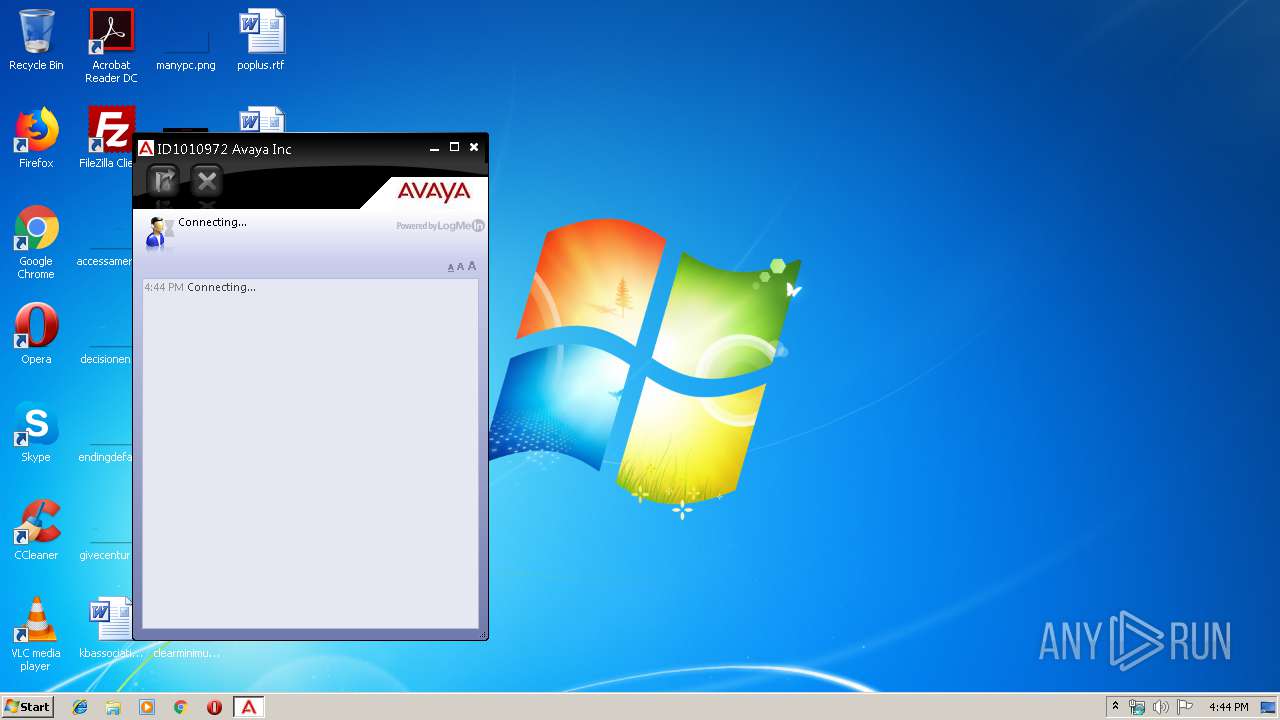
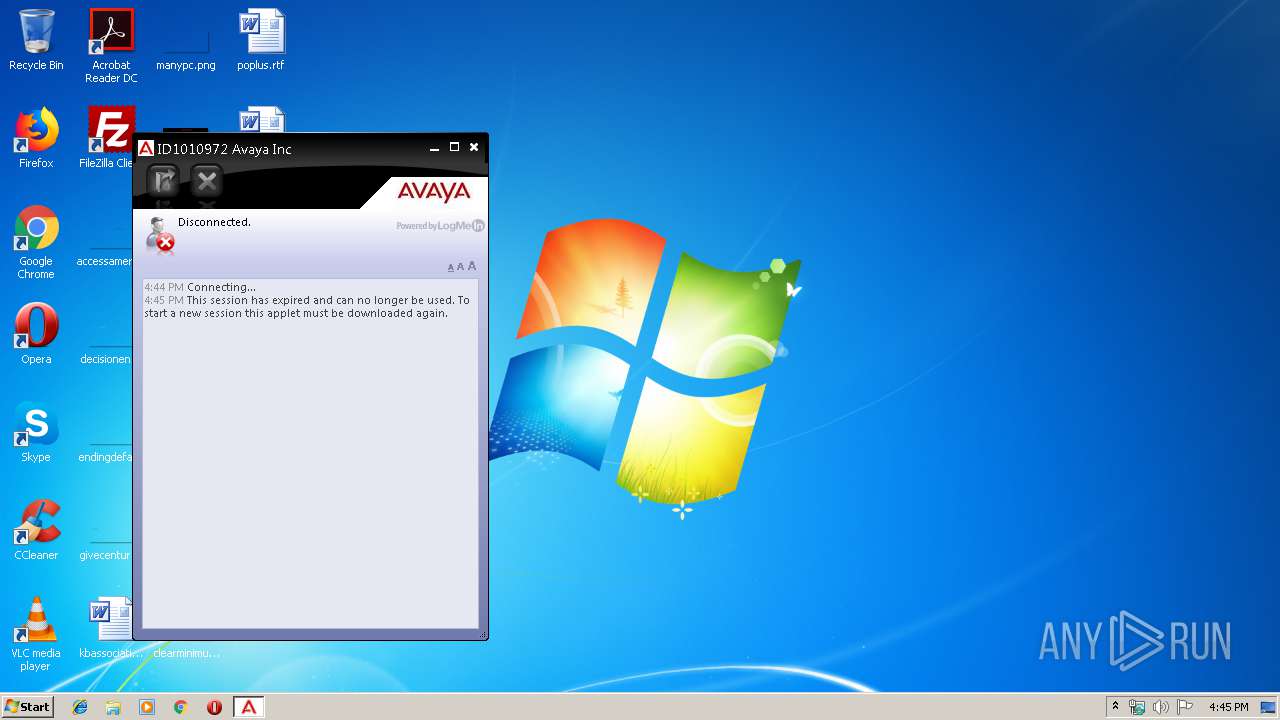
2864 | LMI_Rescue.exe | 64.74.18.244:443 | secure.logmeinrescue.com | LogMeIn, Inc. | US | unknown |
2864 | LMI_Rescue.exe | 64.74.17.133:443 | control.app03-05.logmeinrescue.com | LogMeIn, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
secure.logmeinrescue.com |
| whitelisted |
control.app03-05.logmeinrescue.com |
| unknown |
Threats
Process | Message |
|---|---|
LMI_Rescue.exe | 2020-01-19 16:44:58.227 - Info - Rescue - Main - [0x00000e6c] Main - WritePath: C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\ |
LMI_Rescue.exe | 2020-01-19 16:44:58.227 - Info - Rescue - Main - [0x00000e6c] Main - ======== STARTED 7.11.417.2117 ======== |
LMI_Rescue.exe | 2020-01-19 16:44:58.227 - Info - Rescue - Main - [0x00000e6c] Main - Binary: C:\Users\admin\AppData\Local\LogMeIn Rescue Applet\LMIR0EB88001.tmp\LMI_Rescue.exe |
LMI_Rescue.exe | 2020-01-19 16:44:58.243 - Info - Rescue - Keyboard - [0x00000e6c] Main - Checking keyboard state... |
LMI_Rescue.exe | 2020-01-19 16:44:58.243 - Info - Rescue - Message - [0x00000e6c] Main - IPC connection ID: (f0ae85e3-2b95-73a4-2083-edbe612f60d6) |
LMI_Rescue.exe | 2020-01-19 16:44:58.243 - Info - Rescue - InitUserInfo - [0x00000e6c] Main - Name: admin; Domain: USER-PC |
LMI_Rescue.exe | 2020-01-19 16:44:58.618 - Info - Rescue - Proxy - [0x00000e6c] Main - Initialization: First |
LMI_Rescue.exe | 2020-01-19 16:44:58.618 - Info - Rescue - Proxy - [0x00000e6c] Main - Initialization: Detect |
LMI_Rescue.exe | 2020-01-19 16:44:58.618 - Info - Rescue - Proxy - [0x00000e6c] Main - Initialization: Use OS settings |
LMI_Rescue.exe | 2020-01-19 16:44:58.696 - Info - Rescue - Main - [0x00000e6c] Main - Rescue Applet: 7.11.417.2117 |