| URL: | http://www.mcubemems.com/wp-content/uploads/2016/11/MS1001.apk |
| Full analysis: | https://app.any.run/tasks/c5117cf6-5167-4004-9c61-3bf6de7f4540 |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2020, 11:21:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 09E43C19869A54EC64731C1128BD4467 |
| SHA1: | BDFDFBDEA40BB0D3B8C6A8F9A21EF2DF06DA429B |
| SHA256: | CB7721B7B38AE8D9E9331BE9109C9C832DE5022A5155FDBE027DF8C08638E2D2 |
| SSDEEP: | 3:N1KJS4UStSVOlAQyXAUE:Cc4USgVOlAZQp |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2356)
- iexplore.exe (PID: 2804)
- iexplore.exe (PID: 3772)
Creates files in the user directory
- iexplore.exe (PID: 2804)
- iexplore.exe (PID: 3772)
Changes internet zones settings
- iexplore.exe (PID: 2356)
Reads internet explorer settings
- iexplore.exe (PID: 2804)
- iexplore.exe (PID: 3772)
Application launched itself
- iexplore.exe (PID: 2356)
Reads settings of System Certificates
- iexplore.exe (PID: 3772)
- iexplore.exe (PID: 2356)
Changes settings of System certificates
- iexplore.exe (PID: 2356)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2356 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.mcubemems.com/wp-content/uploads/2016/11/MS1001.apk" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2356 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3772 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2356 CREDAT:595210 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 248
Read events
1 031
Write events
3 499
Delete events
1 718
Modification events
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2212059634 | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30804796 | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2356) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
80
Text files
66
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2804 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3F2F.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar3F30.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:1CB7C2FC7D01363D0DDC9E510DCF087C | SHA256:A700915336EB7237BDB6D850E07BBE332EBC941BD529A7C083D4084114F41B74 | |||
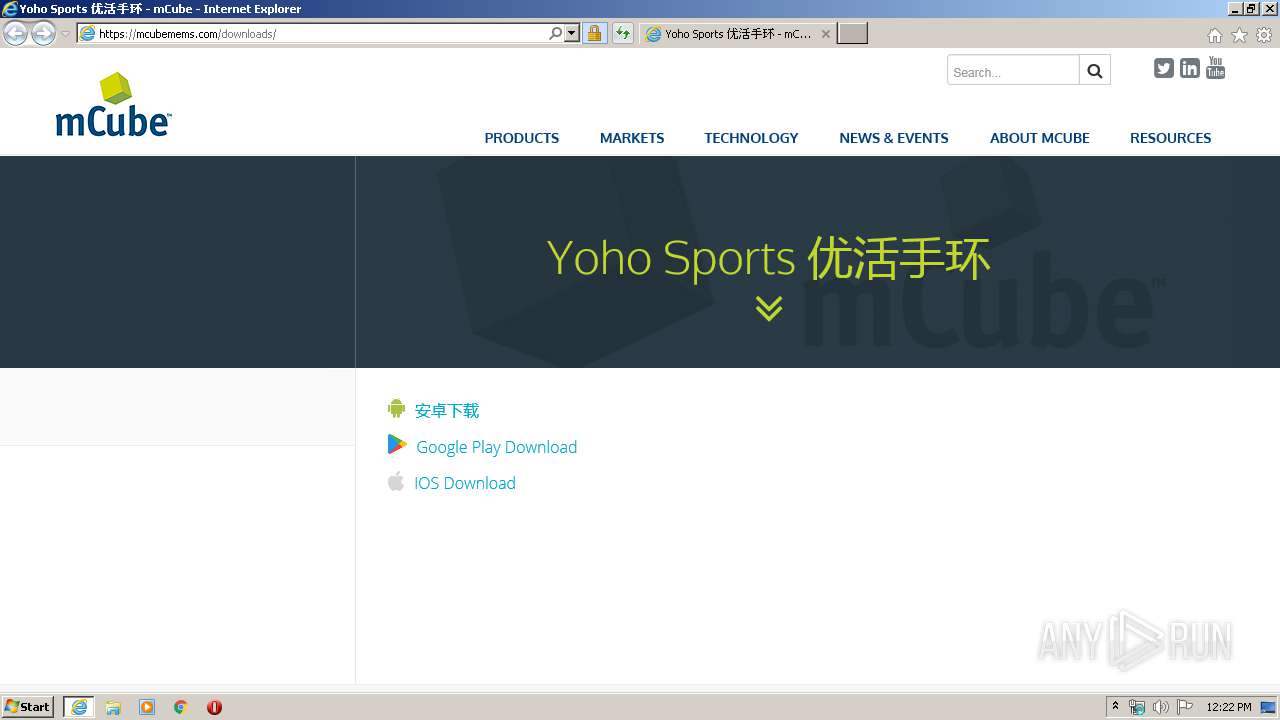
| 2804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\downloads[1].htm | html | |
MD5:6C1365B0E01CCE4ABD4C3FEE9ACAEB89 | SHA256:20EFA6072A2EA273B0A0BE46F16F0A5CFA413695F503F037403C20CDE4968050 | |||
| 2804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\style[1].css | text | |
MD5:DCE5D54FF17E4336D0C5153961C2FAE0 | SHA256:238B0199AC0D26C23DD70951C7DAE96B0413407844CA9030A078DB0F6F3EC626 | |||
| 2804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\bootstrap.min[1].css | text | |
MD5:99D6E03922ADB5802C1D9205FA945A25 | SHA256:AA7EE64EE6FA57A60553972915F97D64CD92BF487812F9E6F70AC824070E345B | |||
| 2804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:A1BDD4945CFEF57284F5E2B13645E3D5 | SHA256:A04B2539F9652400844EDE1032FF2E6EA7825A60EBBE8231A26D0261BEA0299B | |||
| 2804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\MS1001[1].htm | html | |
MD5:CD2E0E43980A00FB6A2742D3AFD803B8 | SHA256:BD9DF047D51943ACC4BC6CF55D88EDB5B6785A53337EE2A0F74DD521AEDDE87D | |||
| 2804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5457A8CE4B2A7499F8299A013B6E1C7C_CBB16B7A61CE4E298043181730D3CE9B | binary | |
MD5:28A632E963F468D76C9D2096996A04A3 | SHA256:A59C67A4BECD5011FDD37F26B792D0FA9B8E4A6A196C3C0D82B465584AB02721 | |||
| 2804 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5457A8CE4B2A7499F8299A013B6E1C7C_CBB16B7A61CE4E298043181730D3CE9B | der | |
MD5:8BA922805BC0F4385B2E143E0C05702B | SHA256:AB373EECCE6592EDAF2BCEBC499E2A8A0BB9177B9E4B14456440E7B83145D0BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
92
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2804 | iexplore.exe | GET | 301 | 67.225.162.146:80 | http://www.mcubemems.com/wp-content/uploads/2016/11/MS1001.apk | US | html | 178 b | unknown |
2804 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2804 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2804 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2804 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2804 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDy4NKedukSQwgAAAAAMgpY | US | der | 472 b | whitelisted |
2804 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQC71JgJax1YIwIAAAAAXGhg | US | der | 472 b | whitelisted |
2804 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQC71JgJax1YIwIAAAAAXGhg | US | der | 472 b | whitelisted |
2804 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQC71JgJax1YIwIAAAAAXGhg | US | der | 472 b | whitelisted |
2804 | iexplore.exe | GET | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2804 | iexplore.exe | 67.225.162.146:80 | www.mcubemems.com | Liquid Web, L.L.C | US | unknown |
2804 | iexplore.exe | 67.225.162.146:443 | www.mcubemems.com | Liquid Web, L.L.C | US | unknown |
2804 | iexplore.exe | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
2804 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2804 | iexplore.exe | 172.217.16.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2804 | iexplore.exe | 192.0.77.37:443 | c0.wp.com | Automattic, Inc | US | suspicious |
2804 | iexplore.exe | 216.58.206.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2804 | iexplore.exe | 216.58.210.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2804 | iexplore.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2356 | iexplore.exe | 67.225.162.146:443 | www.mcubemems.com | Liquid Web, L.L.C | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mcubemems.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
mcubemems.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
c0.wp.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |