| File name: | sysdiag-all-4.0.94.12.exe |
| Full analysis: | https://app.any.run/tasks/78c9e175-8192-4353-b057-7e3f3e885f71 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2019, 03:43:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A52845FFA4DE5743F4C166EAB64A29CF |
| SHA1: | EE380A7198A97184696F1118A5926382FDE22680 |
| SHA256: | CB618150768D2FFE337DA5548283F036B6E683353B70EC98842C52F6EF9D7E54 |
| SSDEEP: | 393216:AqdeXJPHRHu6fSvwWOmFCXIn32KDPcezQ/1ci8GBwQK9:5wZPxOtDF4XI3J7M/1nWQ0 |
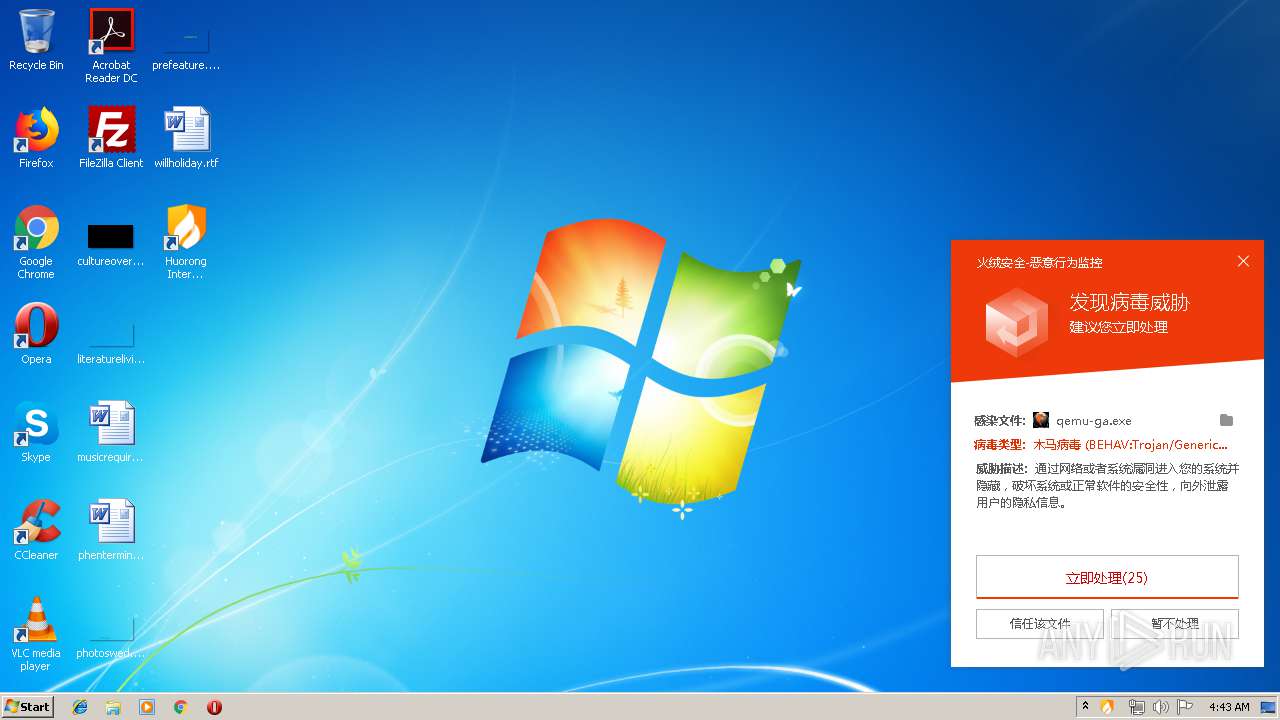
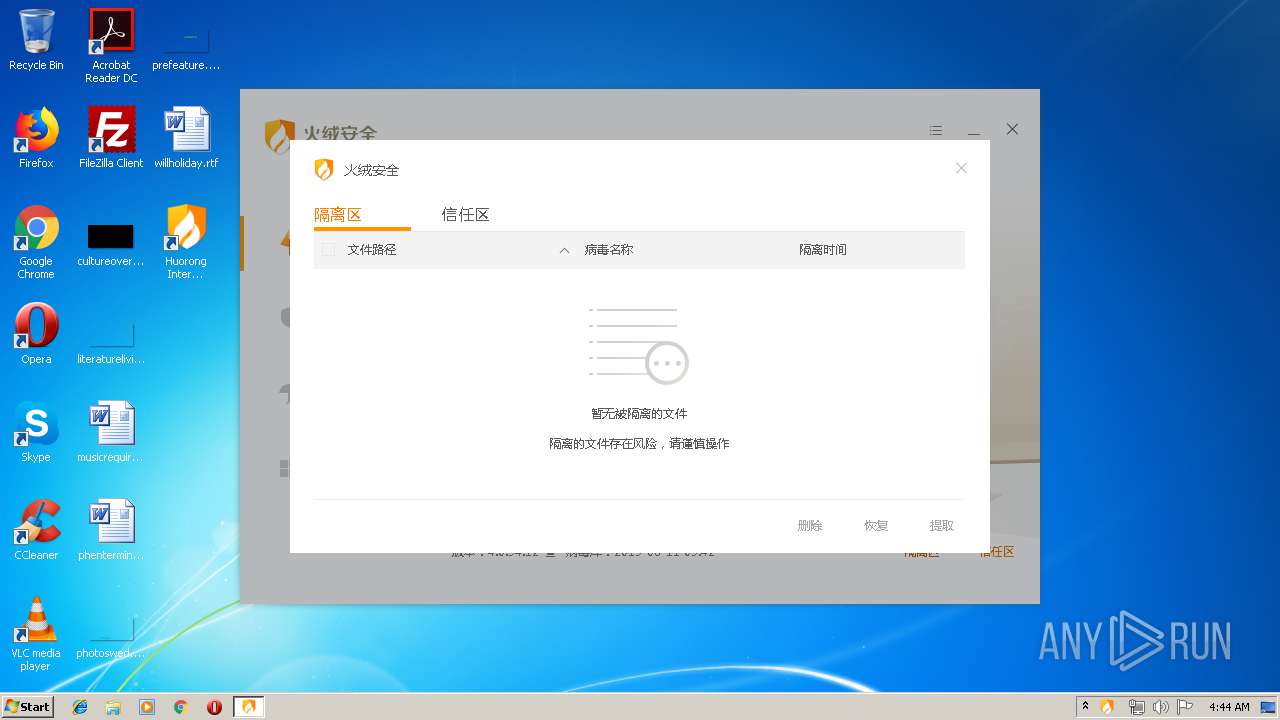
MALICIOUS
Loads dropped or rewritten executable
- sysdiag-all-4.0.94.12.exe (PID: 2224)
- ns645.tmp (PID: 3416)
- HipsDaemon.exe (PID: 2828)
- regsvr32.exe (PID: 692)
- usysdiag.exe (PID: 3356)
- HipsTray.exe (PID: 1480)
- HRUpdate.exe (PID: 3168)
- HipsMain.exe (PID: 3240)
- HipsMain.exe (PID: 2232)
- HipsTray.exe (PID: 3688)
Registers / Runs the DLL via REGSVR32.EXE
- nsFE13.tmp (PID: 1536)
Changes the autorun value in the registry
- sysdiag-all-4.0.94.12.exe (PID: 2224)
Starts NET.EXE for service management
- ns645.tmp (PID: 3416)
Application was dropped or rewritten from another process
- HipsDaemon.exe (PID: 2828)
- nsFE13.tmp (PID: 1536)
- nsFF6C.tmp (PID: 3592)
- ns68.tmp (PID: 2464)
- nsFFDA.tmp (PID: 3048)
- ns645.tmp (PID: 3416)
- usysdiag.exe (PID: 3356)
- wsctrl.exe (PID: 3588)
- HipsTray.exe (PID: 1480)
- HRUpdate.exe (PID: 3168)
- HipsMain.exe (PID: 3240)
- HipsMain.exe (PID: 2232)
- HipsTray.exe (PID: 3688)
SUSPICIOUS
Executable content was dropped or overwritten
- sysdiag-all-4.0.94.12.exe (PID: 2224)
Creates files in the Windows directory
- sysdiag-all-4.0.94.12.exe (PID: 2224)
- HipsDaemon.exe (PID: 2828)
Creates files in the driver directory
- sysdiag-all-4.0.94.12.exe (PID: 2224)
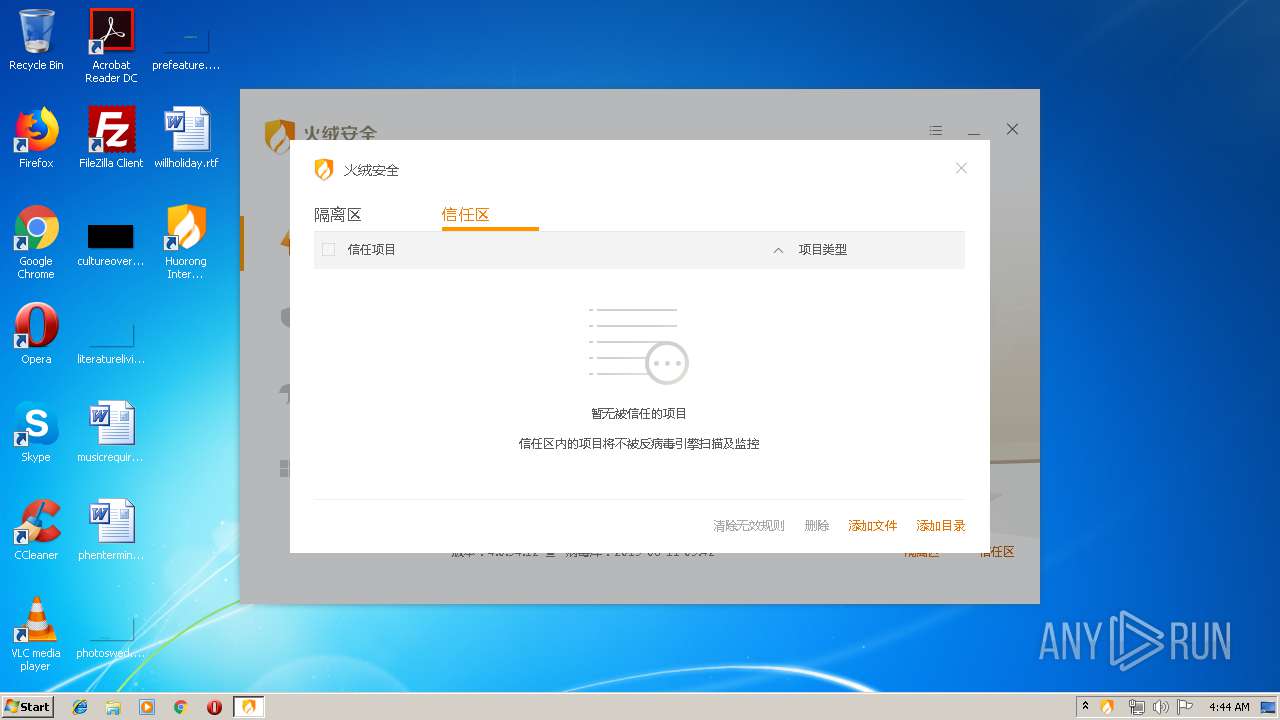
Creates a software uninstall entry
- sysdiag-all-4.0.94.12.exe (PID: 2224)
Starts SC.EXE for service management
- nsFF6C.tmp (PID: 3592)
- nsFFDA.tmp (PID: 3048)
- ns68.tmp (PID: 2464)
Creates COM task schedule object
- regsvr32.exe (PID: 692)
Starts application with an unusual extension
- sysdiag-all-4.0.94.12.exe (PID: 2224)
Creates or modifies windows services
- sysdiag-all-4.0.94.12.exe (PID: 2224)
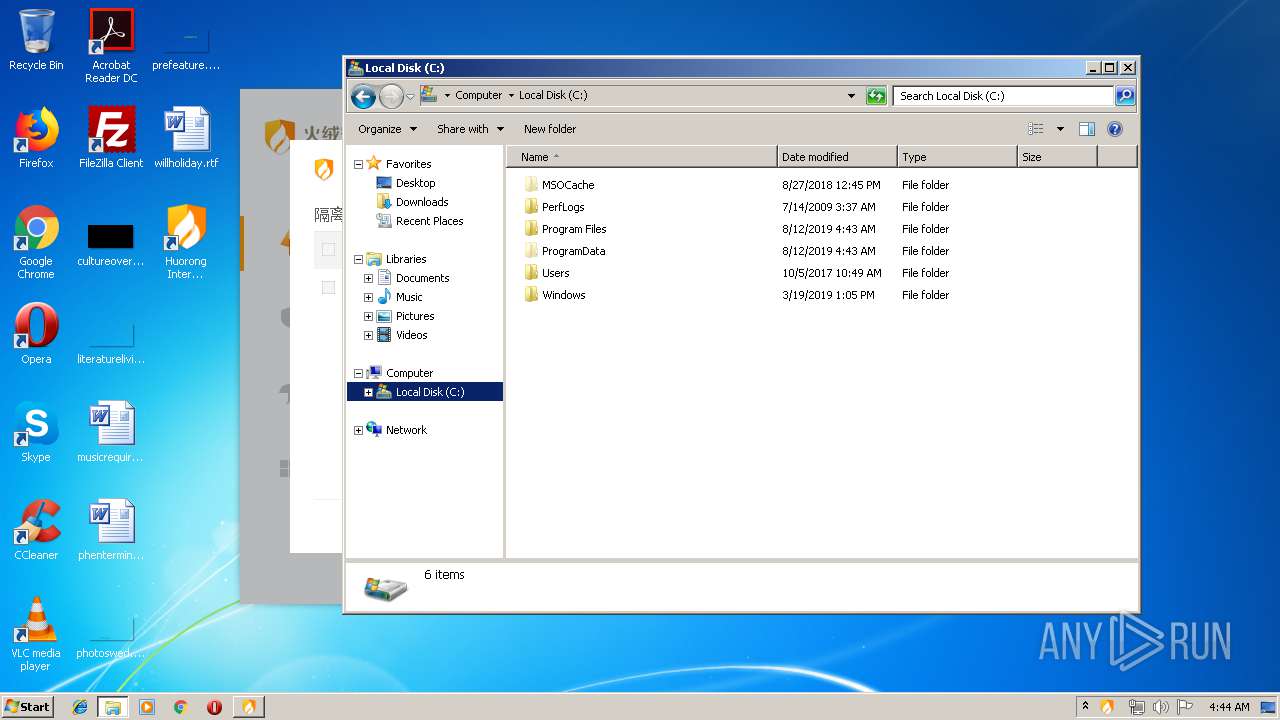
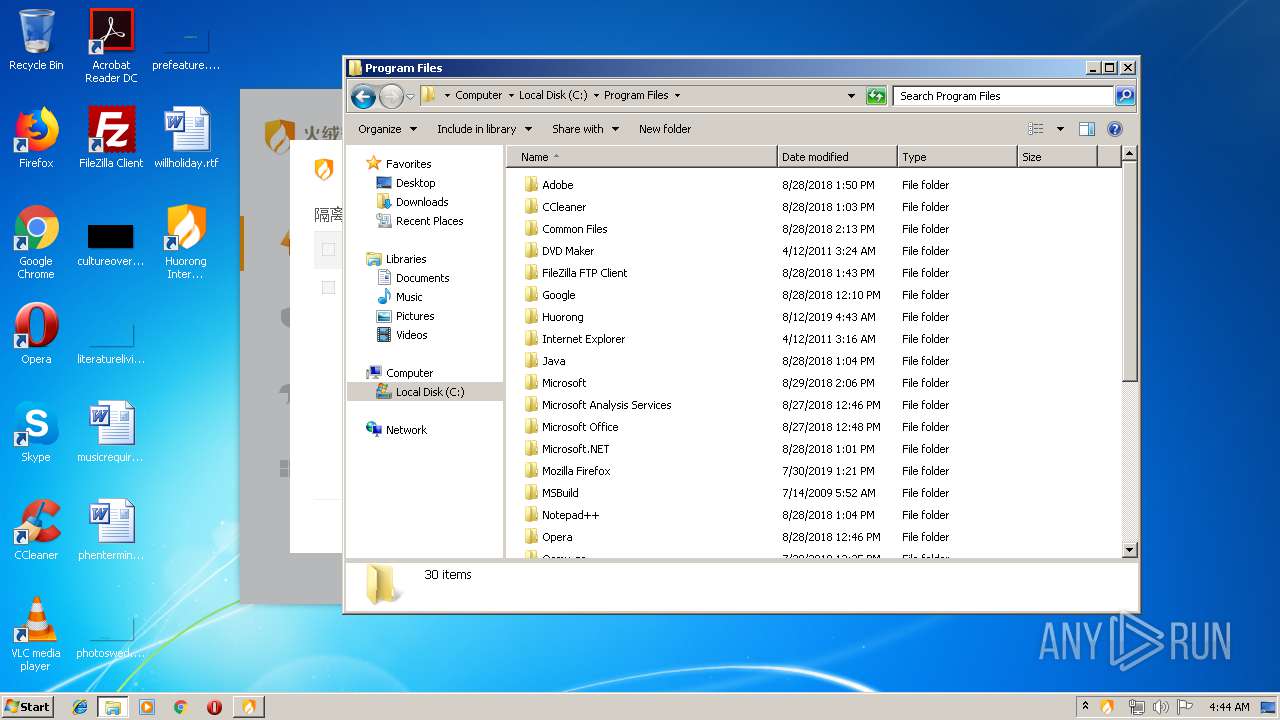
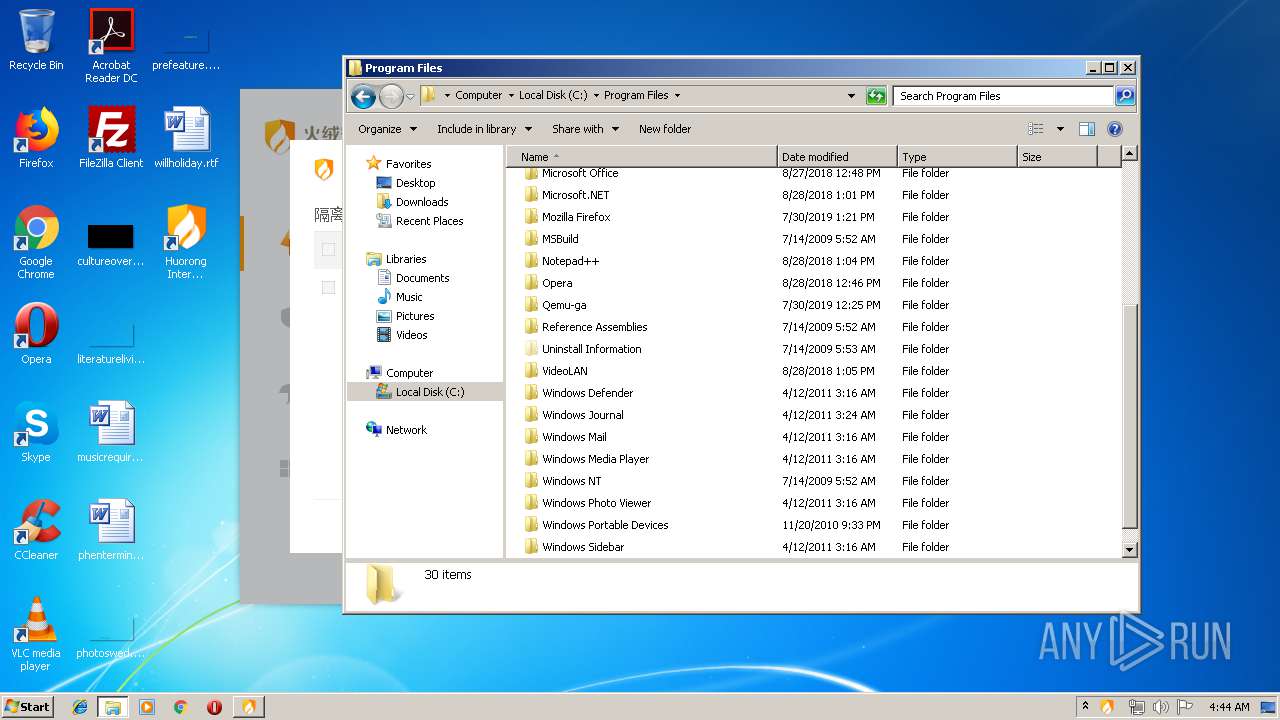
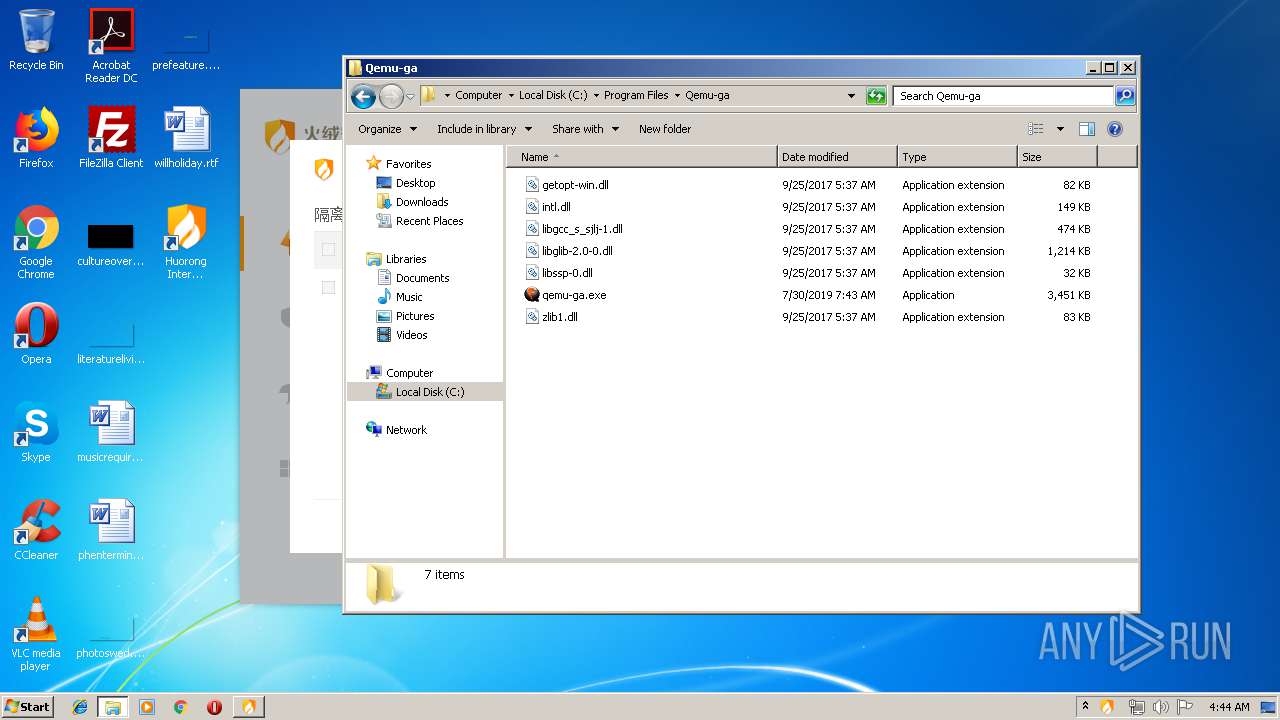
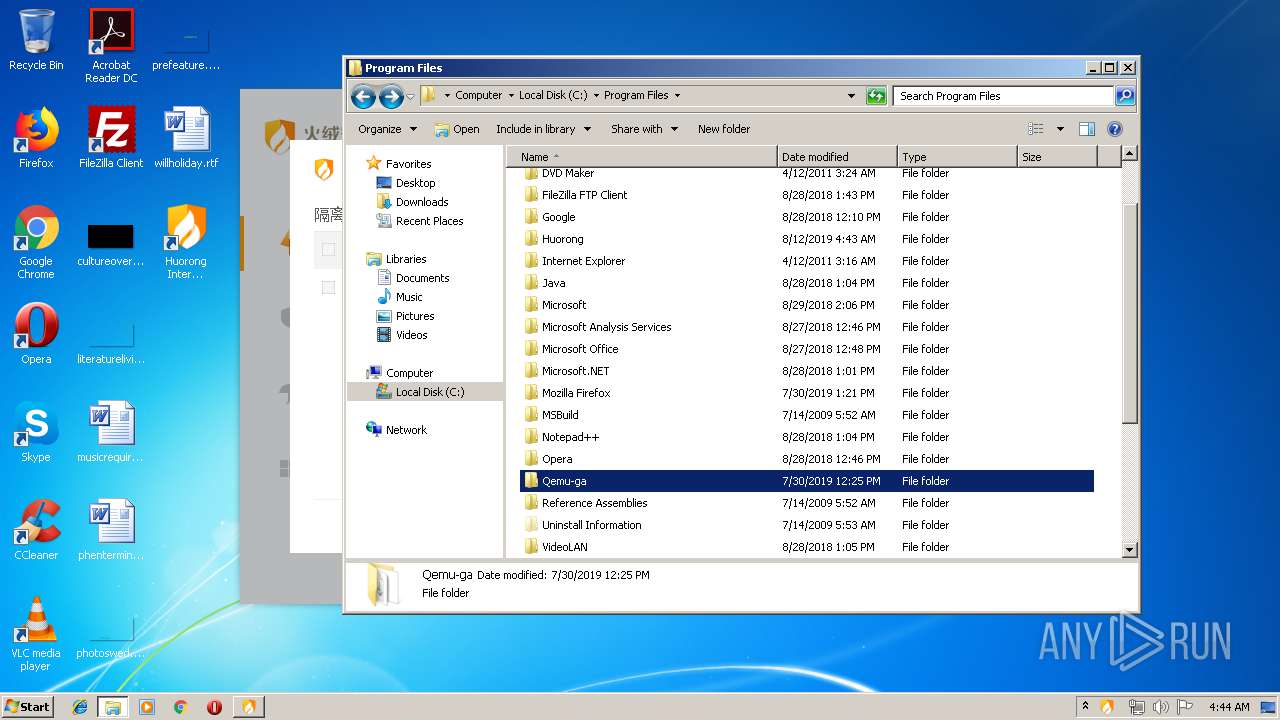
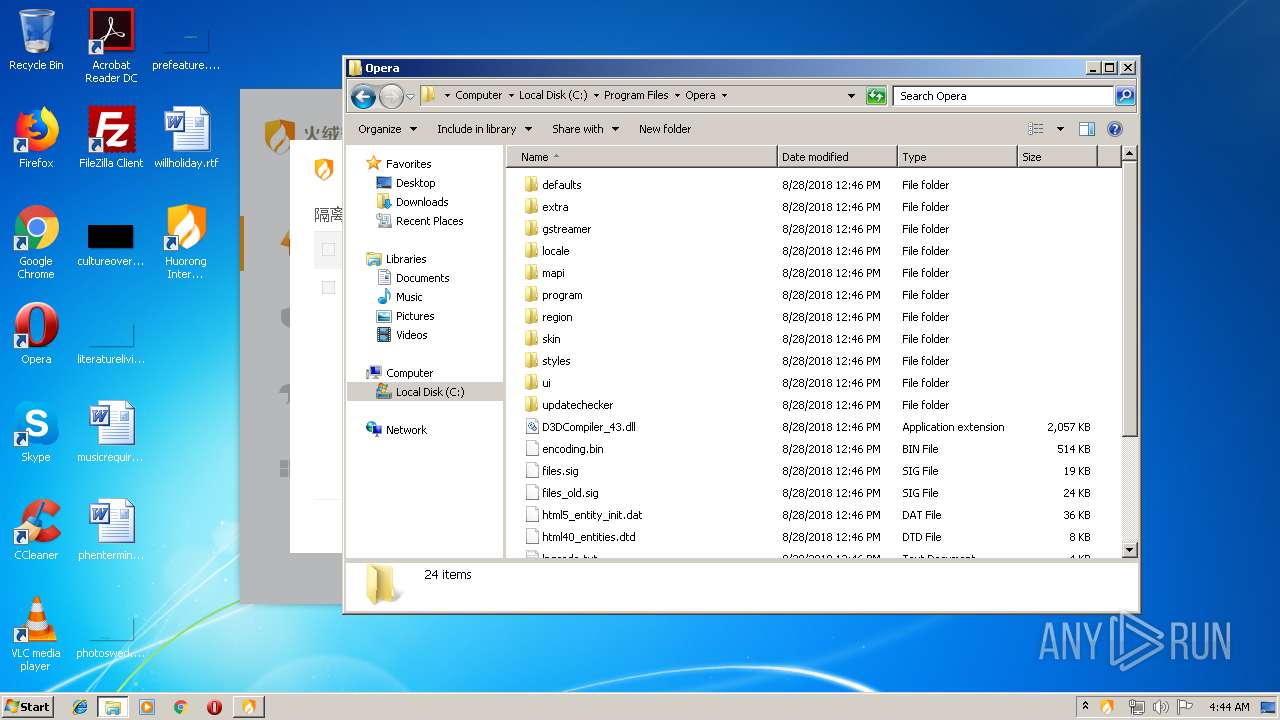
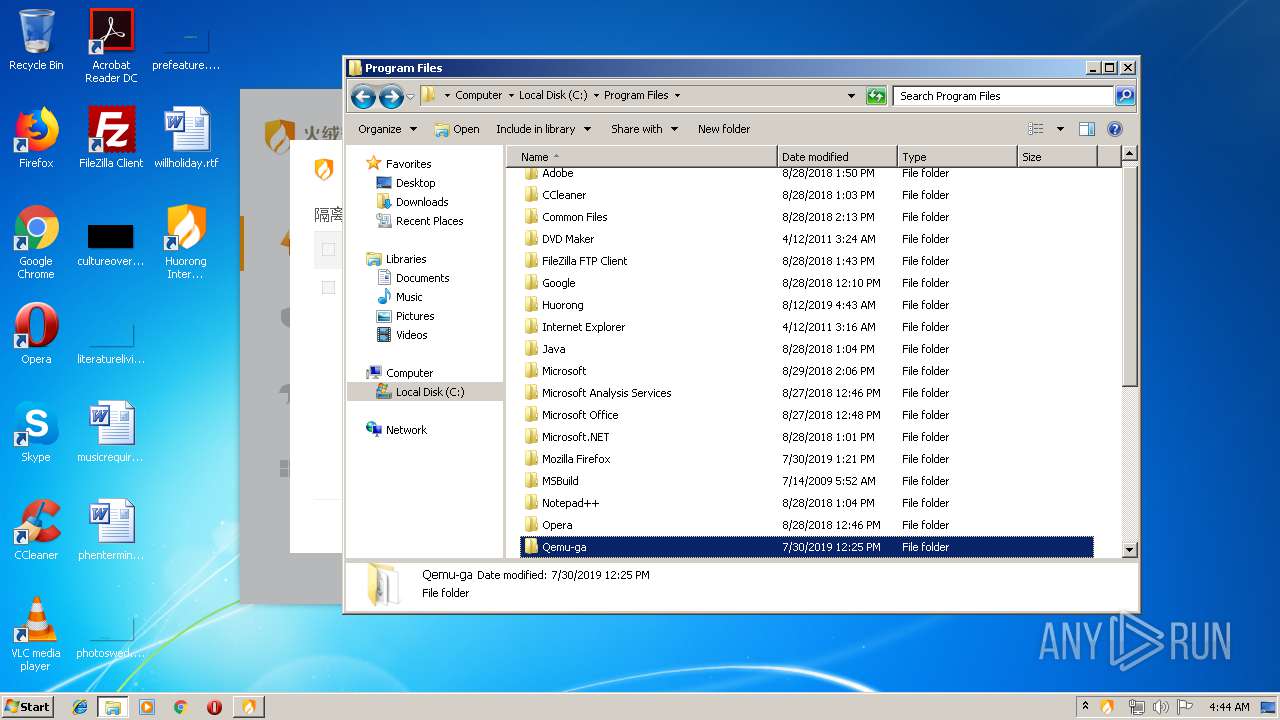
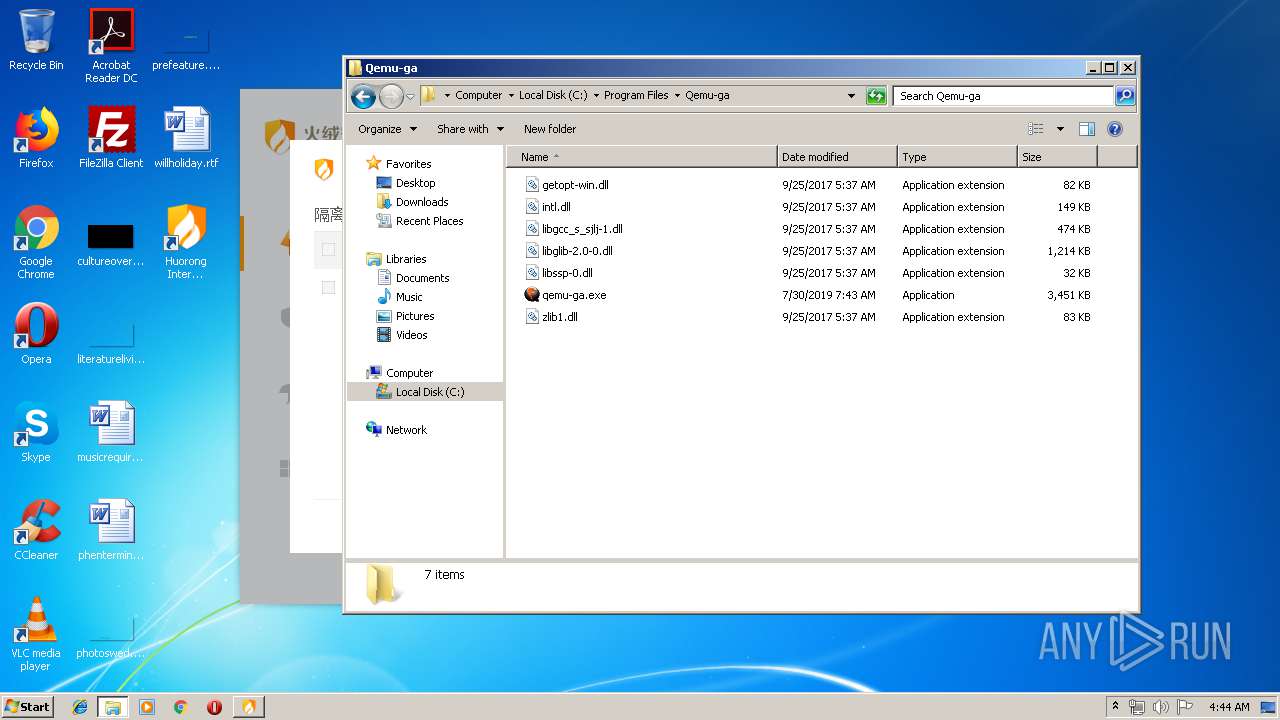
Creates files in the program directory
- sysdiag-all-4.0.94.12.exe (PID: 2224)
- HipsDaemon.exe (PID: 2828)
Executed as Windows Service
- HipsDaemon.exe (PID: 2828)
INFO
Dropped object may contain Bitcoin addresses
- sysdiag-all-4.0.94.12.exe (PID: 2224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.94.12 |
| ProductVersionNumber: | 4.0.94.12 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
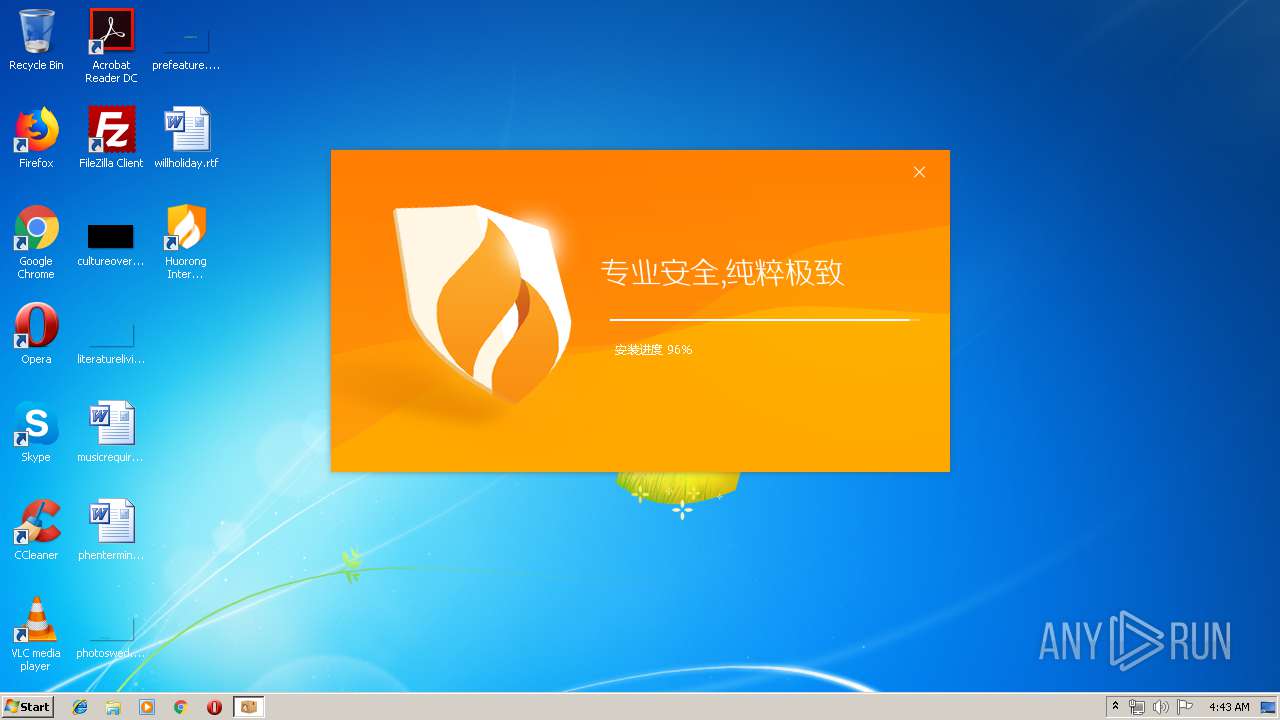
| CompanyName: | Beijing Huorong Network Technology Co., Ltd. |
| FileDescription: | Huorong Internet Security |
| FileVersion: | 4.0.94.12 |
| LegalCopyright: | Beijing Huorong Network Technology Co., Ltd. |
| ProductName: | Huorong Internet Security |
| ProductVersion: | 4.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| CompanyName: | 北京火绒网络科技有限公司 |
| FileDescription: | 火绒安全软件 |
| FileVersion: | 4.0.94.12 |
| LegalCopyright: | 北京火绒网络科技有限公司 |
| ProductName: | 火绒安全软件 |
| ProductVersion: | 4.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002F000 | 0x000132F0 | 0x00012600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.32112 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19512 | 727 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.73669 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.91979 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.85346 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 6.01038 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 6.21459 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 6.08787 | 1736 | UNKNOWN | English - United States | RT_ICON |
8 | 3.21795 | 1640 | UNKNOWN | English - United States | RT_ICON |
9 | 5.61994 | 1384 | UNKNOWN | English - United States | RT_ICON |
10 | 6.10414 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
64
Monitored processes
21
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 692 | regsvr32 /s "C:\Program Files\Huorong\Sysdiag\bin\HRShell.dll" | C:\Windows\system32\regsvr32.exe | — | nsFE13.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Huorong\Sysdiag\bin\HipsTray.exe" | C:\Program Files\Huorong\Sysdiag\bin\HipsTray.exe | — | sysdiag-all-4.0.94.12.exe | |||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Internet Security Tray Exit code: 0 Version: 0, 1, 0, 80 Modules
| |||||||||||||||
| 1536 | "C:\Users\admin\AppData\Local\Temp\nstEF3D.tmp\nsFE13.tmp" regsvr32 /s "C:\Program Files\Huorong\Sysdiag\bin\HRShell.dll" | C:\Users\admin\AppData\Local\Temp\nstEF3D.tmp\nsFE13.tmp | — | sysdiag-all-4.0.94.12.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1732 | sc description HipsDaemon "Huorong Internet Security Daemon" | C:\Windows\system32\sc.exe | — | ns68.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\Downloads\sysdiag-all-4.0.94.12.exe" | C:\Users\admin\Downloads\sysdiag-all-4.0.94.12.exe | explorer.exe | ||||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Internet Security Exit code: 0 Version: 4.0.94.12 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Huorong\Sysdiag\bin\HipsMain.exe" | C:\Program Files\Huorong\Sysdiag\bin\HipsMain.exe | — | sysdiag-all-4.0.94.12.exe | |||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Internet Security Main UI Exit code: 0 Version: 0, 1, 0, 106 Modules
| |||||||||||||||
| 2464 | "C:\Users\admin\AppData\Local\Temp\nstEF3D.tmp\ns68.tmp" sc description HipsDaemon "Huorong Internet Security Daemon" | C:\Users\admin\AppData\Local\Temp\nstEF3D.tmp\ns68.tmp | — | sysdiag-all-4.0.94.12.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2544 | sc config HipsDaemon binpath= "\"C:\Program Files\Huorong\Sysdiag\bin\HipsDaemon.exe\" -sHipsDaemon" type= own type= interact start= auto group= Base DisplayName= "Huorong Internet Security Daemon" | C:\Windows\system32\sc.exe | — | nsFFDA.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Huorong\Sysdiag\bin\HipsDaemon.exe" -sHipsDaemon | C:\Program Files\Huorong\Sysdiag\bin\HipsDaemon.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: SYSTEM Description: Huorong Internet Security Daemon Exit code: 0 Version: 4.0.0.1 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\Downloads\sysdiag-all-4.0.94.12.exe" | C:\Users\admin\Downloads\sysdiag-all-4.0.94.12.exe | — | explorer.exe | |||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: MEDIUM Description: Huorong Internet Security Exit code: 3221226540 Version: 4.0.94.12 | |||||||||||||||
Total events
476
Read events
381
Write events
95
Delete events
0
Modification events
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | DebugLevel |
Value: 1 | |||
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | DependOnService |
Value: FltMgr | |||
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Type |
Value: 1 | |||
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Tag |
Value: 2 | |||
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Group |
Value: PNP_TDI | |||
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | ImagePath |
Value: system32\DRIVERS\sysdiag.sys | |||
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | DisplayName |
Value: Huorong Internet Security Core Kext | |||
| (PID) Process: | (2224) sysdiag-all-4.0.94.12.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Description |
Value: Huorong Internet Security Core Kext | |||
Executable files
54
Suspicious files
48
Text files
4
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Program Files\Huorong\Sysdiag\bin\behavior.dll | executable | |
MD5:F1B0E119E0B184529F59FFDDA3D6A725 | SHA256:B64196343B8A92CB3CDE7C5989EDBDB8E6EEF6B7D39D6AB262426DE08394C798 | |||
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Windows\system32\drivers\hrfwdrv.sys | executable | |
MD5:3B0A1ED3804D86CAC190B16E4BEC3EB3 | SHA256:633519A94474364A9E6CC8007BCDB00E4247581ECC29B4CD700DB794C7F882F4 | |||
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Windows\system32\drivers\hrwfpdrv.sys | executable | |
MD5:75995E2485D41B7EBB3872BF89EBC1D1 | SHA256:DF42E036B4134B60AC5B325F0EC2F034EDB0419B9D83B3A1003ED958AF2862FD | |||
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Users\admin\AppData\Local\Temp\nstEF3D.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Program Files\Huorong\Sysdiag\bin\scenter.dll | executable | |
MD5:F47C078123E4E17D564678E4D695BFA2 | SHA256:D17ED82566FE8684571FC334BCBCFEE3D7BC8F09679DD38778CA916C988D37B1 | |||
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Program Files\Huorong\Sysdiag\bin\usysdiag.dll | executable | |
MD5:009D9D286B0AF2EF28B5B150FA678198 | SHA256:F6B7F2A9E239B93A68A7016C5525F172512CE031564484EF0409A8C33DC6350D | |||
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Users\admin\AppData\Local\Temp\nstEF3D.tmp\inst.ui | compressed | |
MD5:661E82FE4B0A76F9BD0E885F3DCBE12E | SHA256:6390C3B0C64A7F46D67AC89AFE27E084D464BB558B82287AFCE6F5DB5732797C | |||
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Program Files\Huorong\Sysdiag\bin\usysdiag.exe | executable | |
MD5:C018CC945E51AF4A144AD9587A321341 | SHA256:7B1EBC40F31DB5DA057E36B3DF102B41F8826DF193F77320EE80DC82D82A5E56 | |||
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Windows\System32\dtrampo.dll | executable | |
MD5:9EF5C395AE7F27B091E96068B6391227 | SHA256:ED695C898511EE655ED1A238A506BA1BF09EA22E2797AFF2D1DFD06C62A1DF91 | |||
| 2224 | sysdiag-all-4.0.94.12.exe | C:\Program Files\Huorong\Sysdiag\bin\wsctrl.exe | executable | |
MD5:19492EF5C343E4AD2815980268A71EDD | SHA256:18E0923BE01286942D9F2538D67B39CE63C3C8F20573CFE05A70203C136632EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3240 | HipsMain.exe | GET | — | 121.199.251.28:80 | http://update.huorong.cn/upgrade6/upgrade.php?type=chk&uid2=6C98E952AD4B0879D8E1EF011EDF0DAB00000000&instm=2019-08-12%2004%3A43&ver=4.0.94.12&pt=0&channel=0&client=0&confts=0&skq=00000552& | CN | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3240 | HipsMain.exe | 121.199.251.28:80 | update.huorong.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.huorong.cn |
| unknown |