| File name: | DuckDnsInst.exe |
| Full analysis: | https://app.any.run/tasks/02b153a0-acdd-4742-94c0-1d0382dd8b35 |
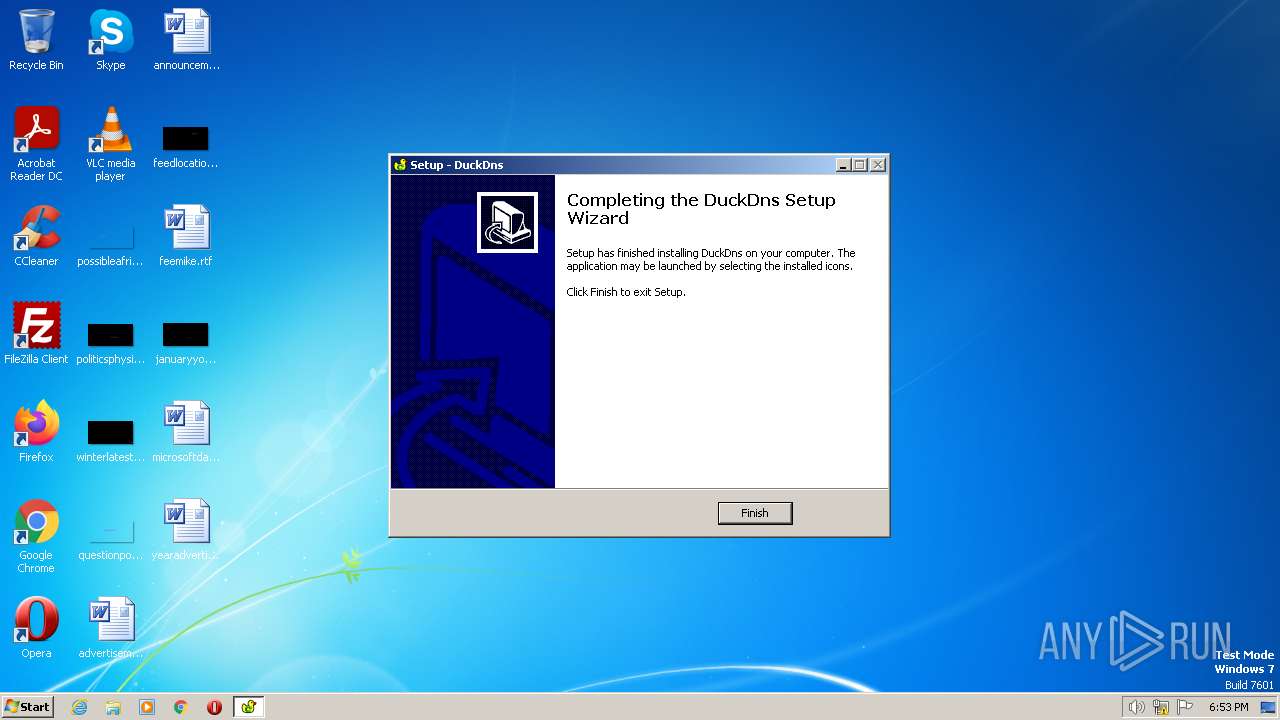
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2023, 17:53:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 12C26AB43202D2EF17553EEB17376C2A |
| SHA1: | 0B6226071AB1711BBBFACA2CDAD6783D2658D797 |
| SHA256: | CB56BFFB224D9BCFF0753D58995C25F6F944BCB075560019CD87283E3B443AA3 |
| SSDEEP: | 12288:RQi9zSYMvrOK9BOKjHol+yFnWVOjTPlxsU807BN/9+FJeyuAJMX7QYQ:RQiE7eORaEOjRxsUrLUoJi |
MALICIOUS
Create files in the Startup directory
- DuckDnsInst.tmp (PID: 2384)
SUSPICIOUS
Executable content was dropped or overwritten
- DuckDnsInst.exe (PID: 2700)
- DuckDnsInst.exe (PID: 3956)
- DuckDnsInst.tmp (PID: 2384)
Reads the Windows owner or organization settings
- DuckDnsInst.tmp (PID: 2384)
Checks for Java to be installed
- DuckDns.exe (PID: 3916)
INFO
Checks supported languages
- DuckDnsInst.exe (PID: 3956)
- DuckDnsInst.tmp (PID: 2092)
- DuckDnsInst.exe (PID: 2700)
- DuckDnsInst.tmp (PID: 2384)
- DuckDns.exe (PID: 3916)
- javaw.exe (PID: 4028)
Reads the computer name
- DuckDnsInst.tmp (PID: 2092)
- DuckDnsInst.tmp (PID: 2384)
- javaw.exe (PID: 4028)
Create files in a temporary directory
- DuckDnsInst.exe (PID: 3956)
- DuckDnsInst.exe (PID: 2700)
- DuckDnsInst.tmp (PID: 2384)
- javaw.exe (PID: 4028)
The process checks LSA protection
- DuckDnsInst.tmp (PID: 2092)
- DuckDnsInst.tmp (PID: 2384)
- icacls.exe (PID: 312)
- javaw.exe (PID: 4028)
Creates files in the program directory
- DuckDnsInst.tmp (PID: 2384)
- javaw.exe (PID: 4028)
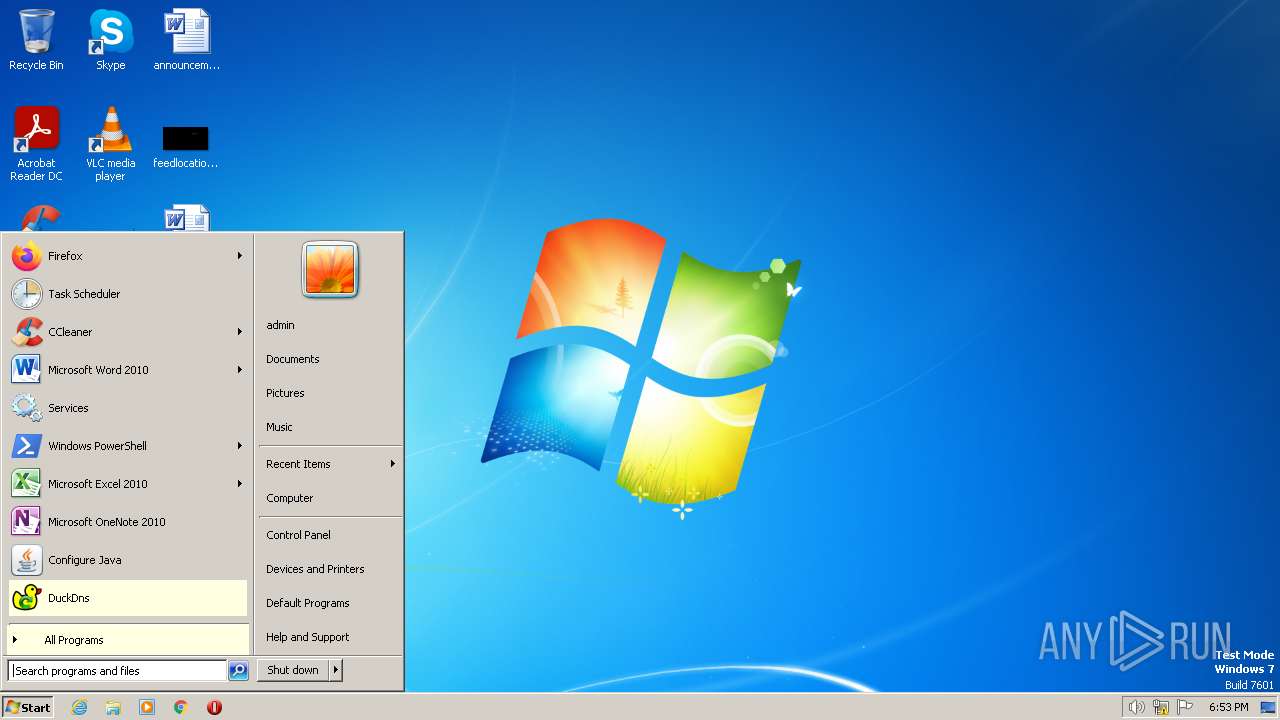
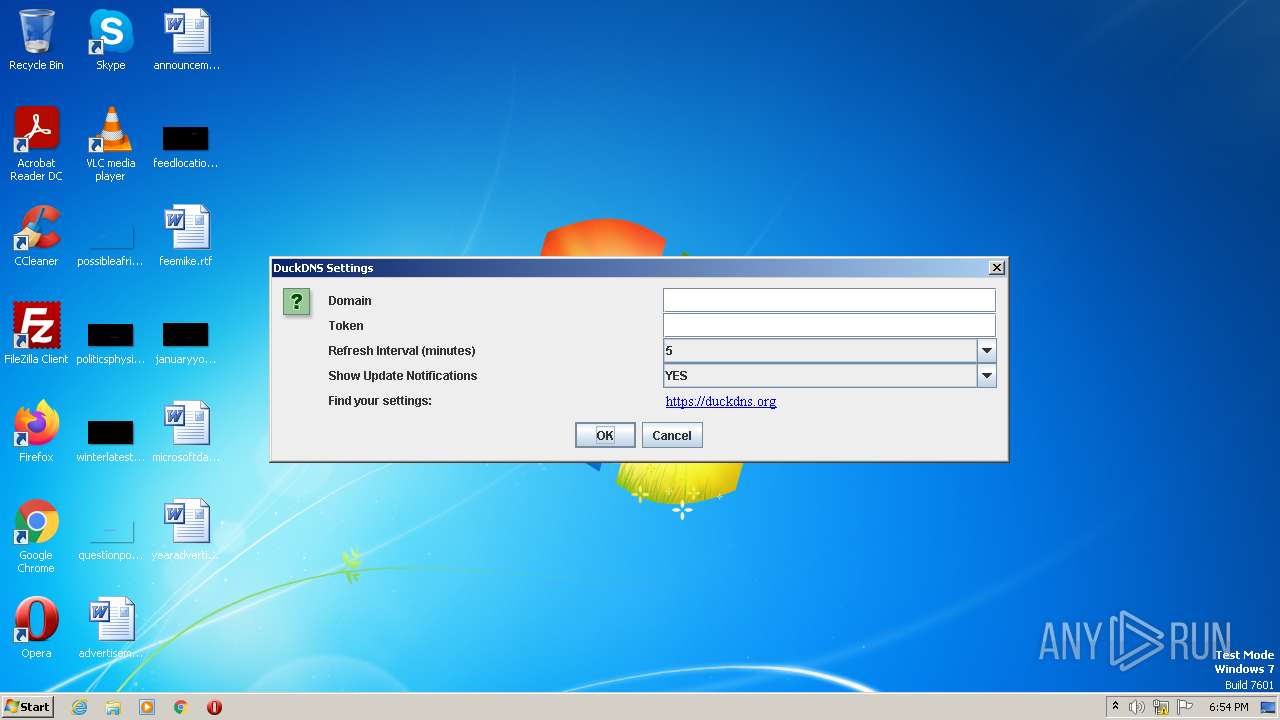
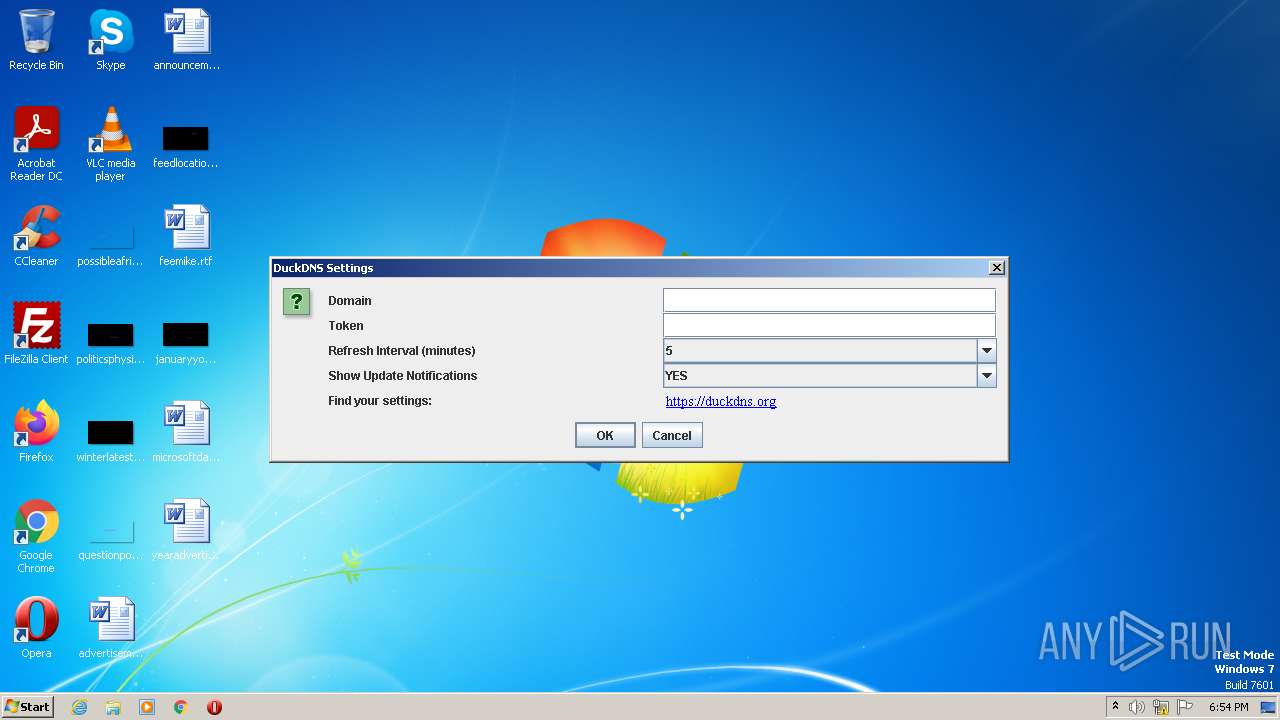
Manual execution by a user
- DuckDns.exe (PID: 3916)
Reads the machine GUID from the registry
- javaw.exe (PID: 4028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (71.1) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.1) |
| .scr | | | Windows screen saver (8.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
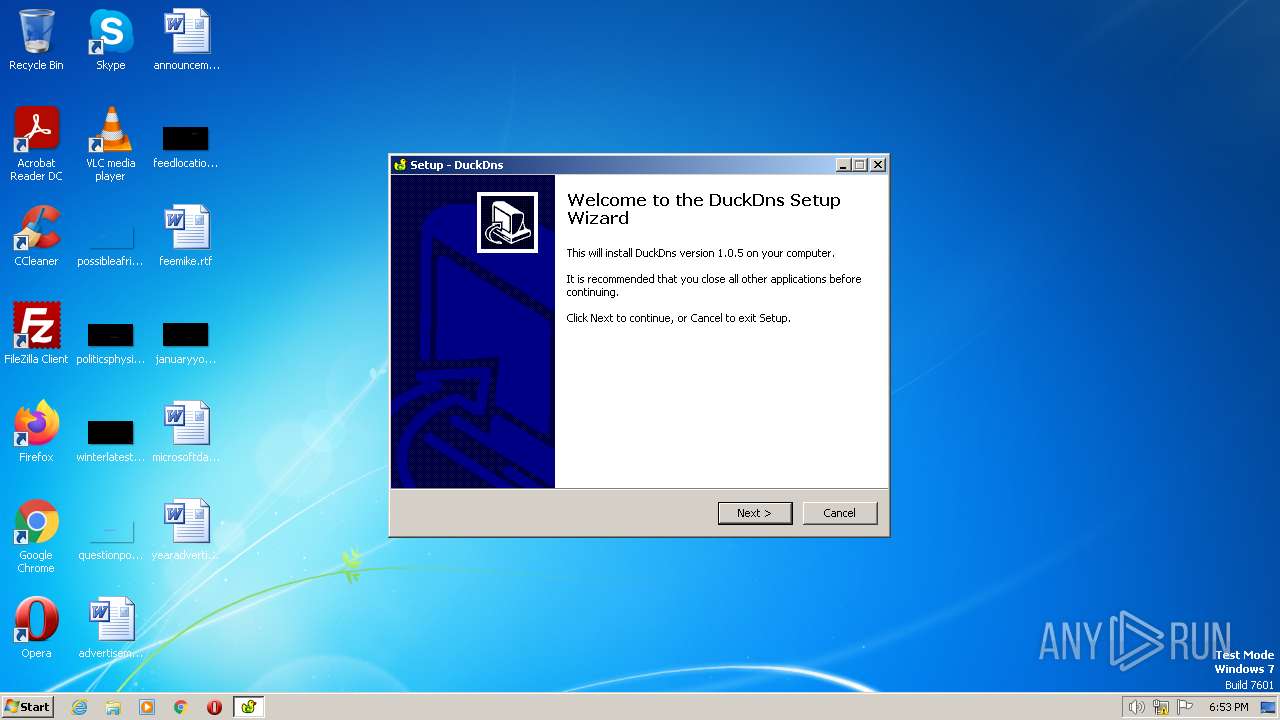
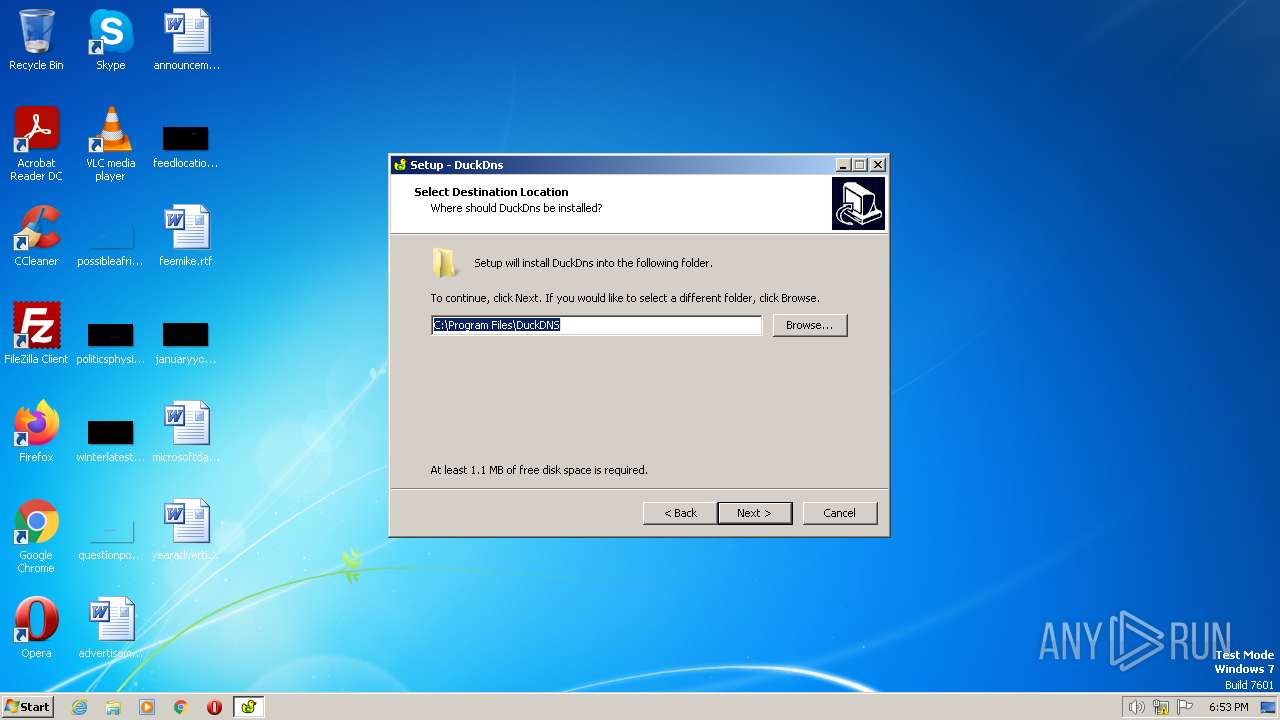
| ProductVersion: | 1.0.5 |
|---|---|
| ProductName: | DuckDns |
| LegalCopyright: | |
| FileVersion: | |
| FileDescription: | DuckDns Setup |
| CompanyName: | ETX Software Inc. |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 1 |
| EntryPoint: | 0xa5f8 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 43008 |
| CodeSize: | 40448 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | ETX Software Inc. |
| FileDescription: | DuckDns Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | DuckDns |
| ProductVersion: | 1.0.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009D30 | 0x00009E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6316 |
DATA | 0x0000B000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75472 |
BSS | 0x0000C000 | 0x00000E90 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x0000965C | 0x00009800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.92986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.57827 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.41434 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.22429 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
45
Monitored processes
7
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\Temp\is-M6V5V.tmp\DuckDnsInst.tmp" /SL5="$6010A,402740,84480,C:\Users\admin\AppData\Local\Temp\DuckDnsInst.exe" | C:\Users\admin\AppData\Local\Temp\is-M6V5V.tmp\DuckDnsInst.tmp | — | DuckDnsInst.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\is-H87KP.tmp\DuckDnsInst.tmp" /SL5="$D0152,402740,84480,C:\Users\admin\AppData\Local\Temp\DuckDnsInst.exe" /SPAWNWND=$90190 /NOTIFYWND=$6010A | C:\Users\admin\AppData\Local\Temp\is-H87KP.tmp\DuckDnsInst.tmp | DuckDnsInst.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\Temp\DuckDnsInst.exe" /SPAWNWND=$90190 /NOTIFYWND=$6010A | C:\Users\admin\AppData\Local\Temp\DuckDnsInst.exe | DuckDnsInst.tmp | ||||||||||||
User: admin Company: ETX Software Inc. Integrity Level: HIGH Description: DuckDns Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3916 | "C:\Program Files\DuckDNS\DuckDns.exe" | C:\Program Files\DuckDNS\DuckDns.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3956 | "C:\Users\admin\AppData\Local\Temp\DuckDnsInst.exe" | C:\Users\admin\AppData\Local\Temp\DuckDnsInst.exe | explorer.exe | ||||||||||||
User: admin Company: ETX Software Inc. Integrity Level: MEDIUM Description: DuckDns Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 4028 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Program Files\DuckDNS\DuckDns.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | DuckDns.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
Total events
2 990
Read events
2 976
Write events
2
Delete events
12
Modification events
| (PID) Process: | (2384) DuckDnsInst.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: FBD5A26E41333C7AFC20C7C24817546DA40E99A8BD5B32D64CC7276258191255 | |||
| (PID) Process: | (2384) DuckDnsInst.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Program Files\DuckDNS\DuckDns.exe | |||
| (PID) Process: | (2384) DuckDnsInst.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2384) DuckDnsInst.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 1F65B73573CC88A9DDB08B48B42DD01DFEF1CD26E7F284BCAD6A1B2608A1769B | |||
| (PID) Process: | (2384) DuckDnsInst.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 50090000F42A5D2F5687D901 | |||
| (PID) Process: | (2384) DuckDnsInst.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4028) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Explorer.EXE | |||
Executable files
14
Suspicious files
18
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3956 | DuckDnsInst.exe | C:\Users\admin\AppData\Local\Temp\is-M6V5V.tmp\DuckDnsInst.tmp | executable | |
MD5:8FF731D01F86D5FF9A326E82823CC30C | SHA256:3228932BA90230EC52DAC304FB9F155BA2DF33DD6775093FB7F3D0AE83546A28 | |||
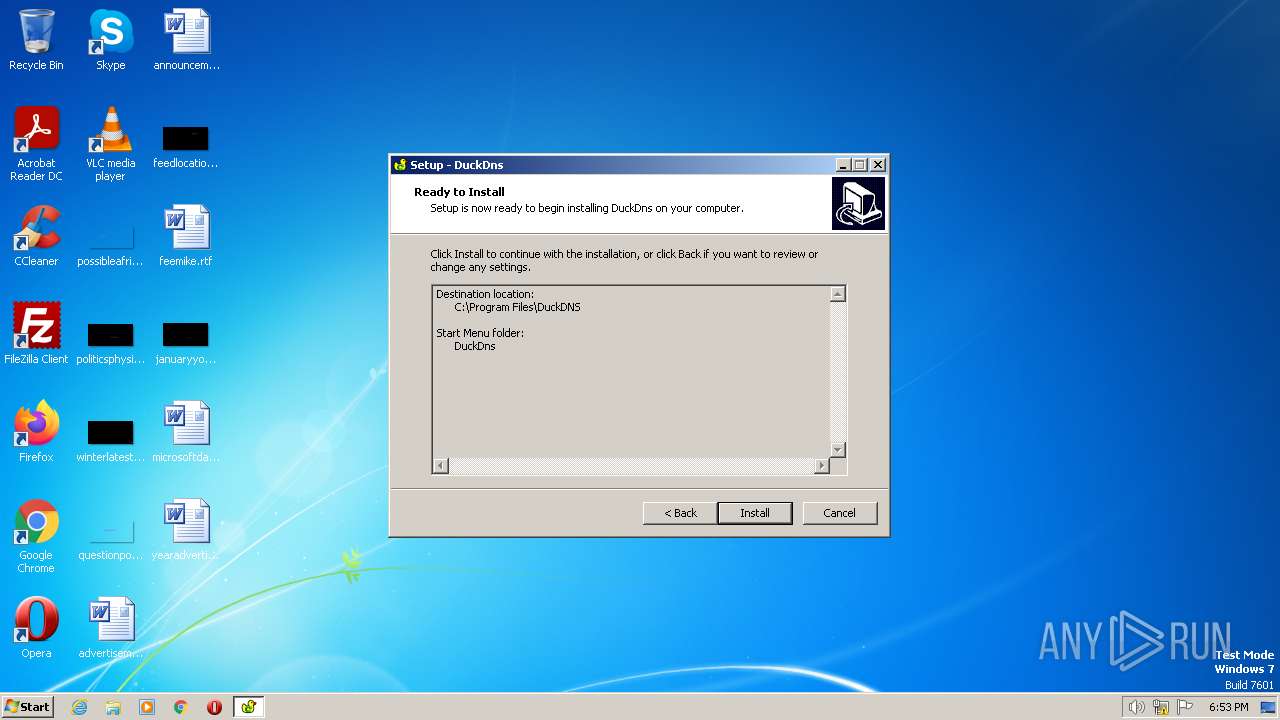
| 2384 | DuckDnsInst.tmp | C:\Program Files\DuckDNS\is-GB1VH.tmp | executable | |
MD5:96E657F29C85D52E65C26325B4EBB41A | SHA256:FF97FA590D1407BC09C24B4F14D8CD5C12FA89F9A87D5DFD8056CE9CD2B848E1 | |||
| 2384 | DuckDnsInst.tmp | C:\Program Files\DuckDNS\DuckDns.exe | executable | |
MD5:96E657F29C85D52E65C26325B4EBB41A | SHA256:FF97FA590D1407BC09C24B4F14D8CD5C12FA89F9A87D5DFD8056CE9CD2B848E1 | |||
| 2700 | DuckDnsInst.exe | C:\Users\admin\AppData\Local\Temp\is-H87KP.tmp\DuckDnsInst.tmp | executable | |
MD5:8FF731D01F86D5FF9A326E82823CC30C | SHA256:3228932BA90230EC52DAC304FB9F155BA2DF33DD6775093FB7F3D0AE83546A28 | |||
| 2384 | DuckDnsInst.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DuckDns\DuckDns.lnk | binary | |
MD5:E53FB20815ED475C3B9019A766CF91A5 | SHA256:C9D2D09D978399D3B5713024606AE6DD53F2038E27CF012E95D3AB78855DBED1 | |||
| 2384 | DuckDnsInst.tmp | C:\Program Files\DuckDNS\is-MS2BH.tmp | executable | |
MD5:5EE2008AE3EB35DC855F147F3DDA5F56 | SHA256:50F4D4C5533BFFD18D56B6B33DCCC705ED6B9E955939D144C53368B964B8ABAF | |||
| 2384 | DuckDnsInst.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DuckDns\Uninstall DuckDns.lnk | binary | |
MD5:6360A250ED3542C296D3250FF5B50DCC | SHA256:A72F9379499192D93EA1E9F1579B77BAA66425EF3B207D08B0823D473B0930FD | |||
| 2384 | DuckDnsInst.tmp | C:\Program Files\DuckDNS\unins000.dat | dat | |
MD5:4DA071C34E70D5B8789B792A4020FB02 | SHA256:C48E0A60D21F82D64DFF78263A2333628EED99CC9E05376DA873C4B514D9B170 | |||
| 4028 | javaw.exe | C:\Users\admin\AppData\Local\Temp\jar_cache7708078849368233225.tmp | compressed | |
MD5:AFE75B4855C7AEDEA21C0101151599CA | SHA256:AB3642F43D603D2C7156F14B99E2EA8C928D966FB69710A1871748E9B930DF15 | |||
| 2384 | DuckDnsInst.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\DuckDns.lnk | binary | |
MD5:E53FB20815ED475C3B9019A766CF91A5 | SHA256:C9D2D09D978399D3B5713024606AE6DD53F2038E27CF012E95D3AB78855DBED1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3372 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |