| File name: | SLskC.7z |
| Full analysis: | https://app.any.run/tasks/dff795f4-4461-4180-abff-6857b2b52fcf |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 08:11:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
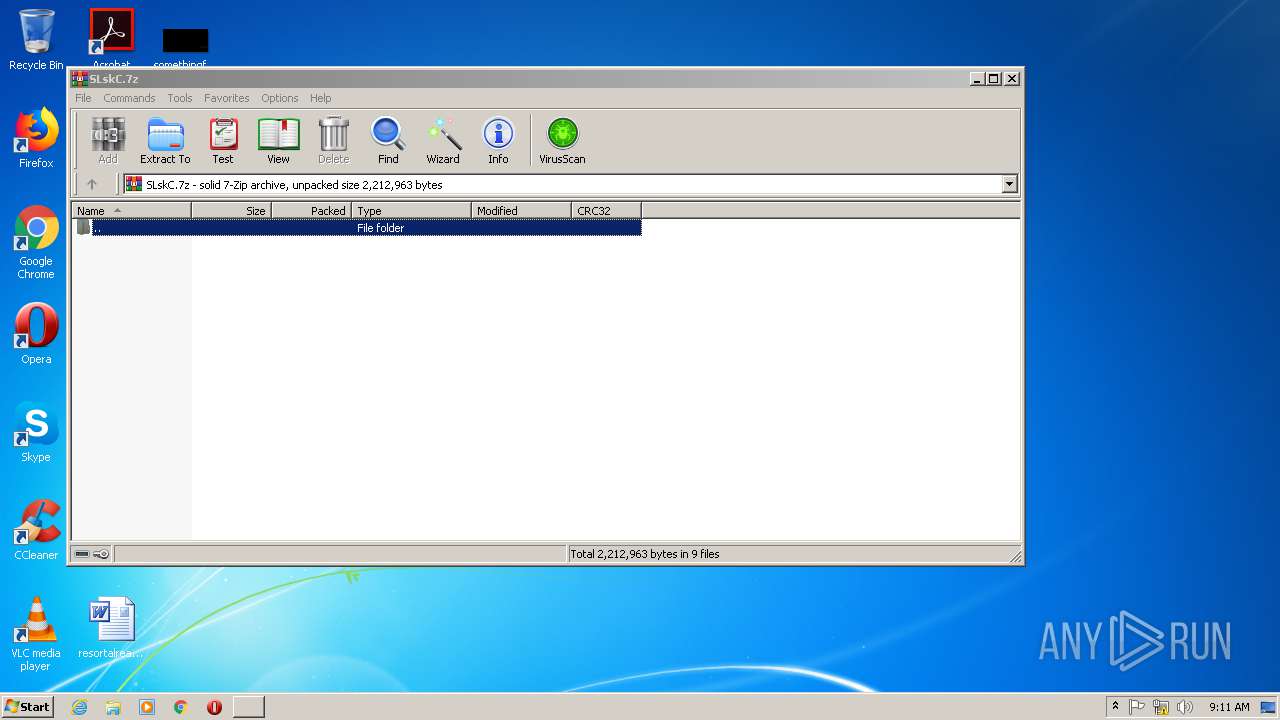
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 9F97BAD35B8084440E655218C923A8B7 |
| SHA1: | AFBA38FB39102652E78D74AC731BF754EEFE38BE |
| SHA256: | CB11DE448907B2AA4D14243E6D36AA07AB1F46418C15F8229B2A0070AEA691AC |
| SSDEEP: | 12288:lY3qg569F389C++ia10x8lI97Goc8JdTfhiUI/cRHmpkzpIKFtPjD:llF3hu26Tq+dThi505lJt/ |
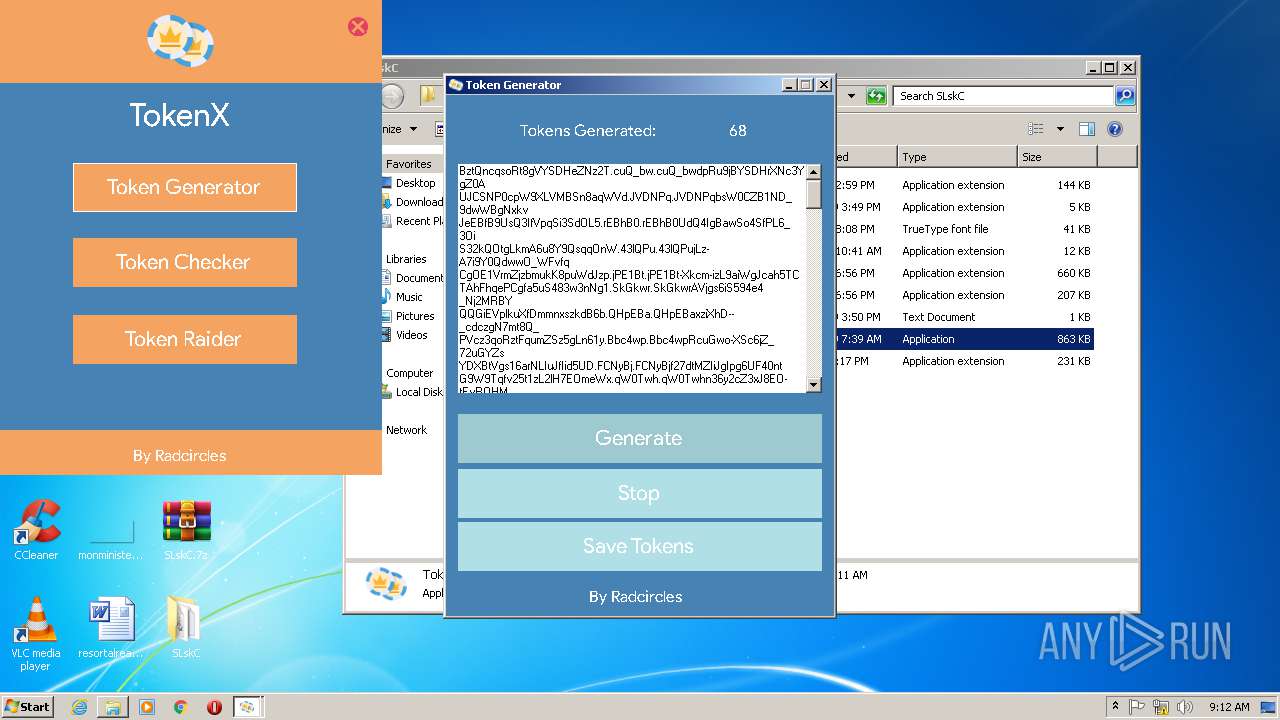
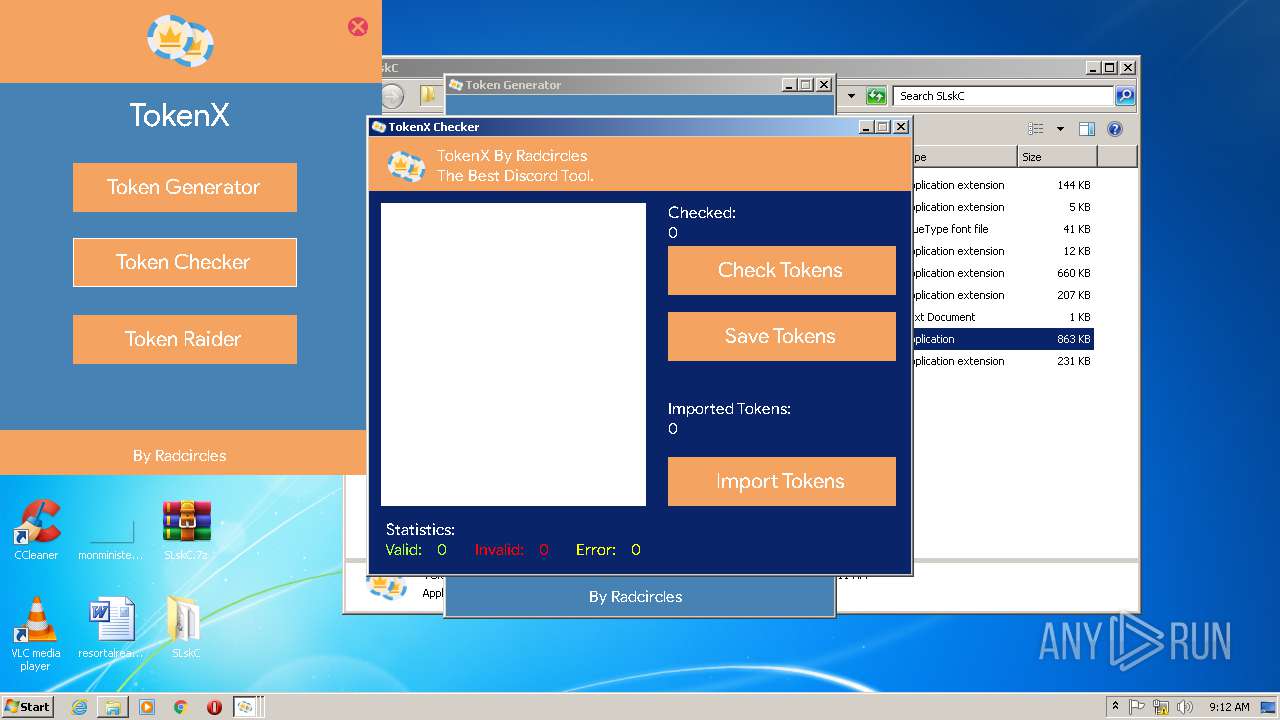
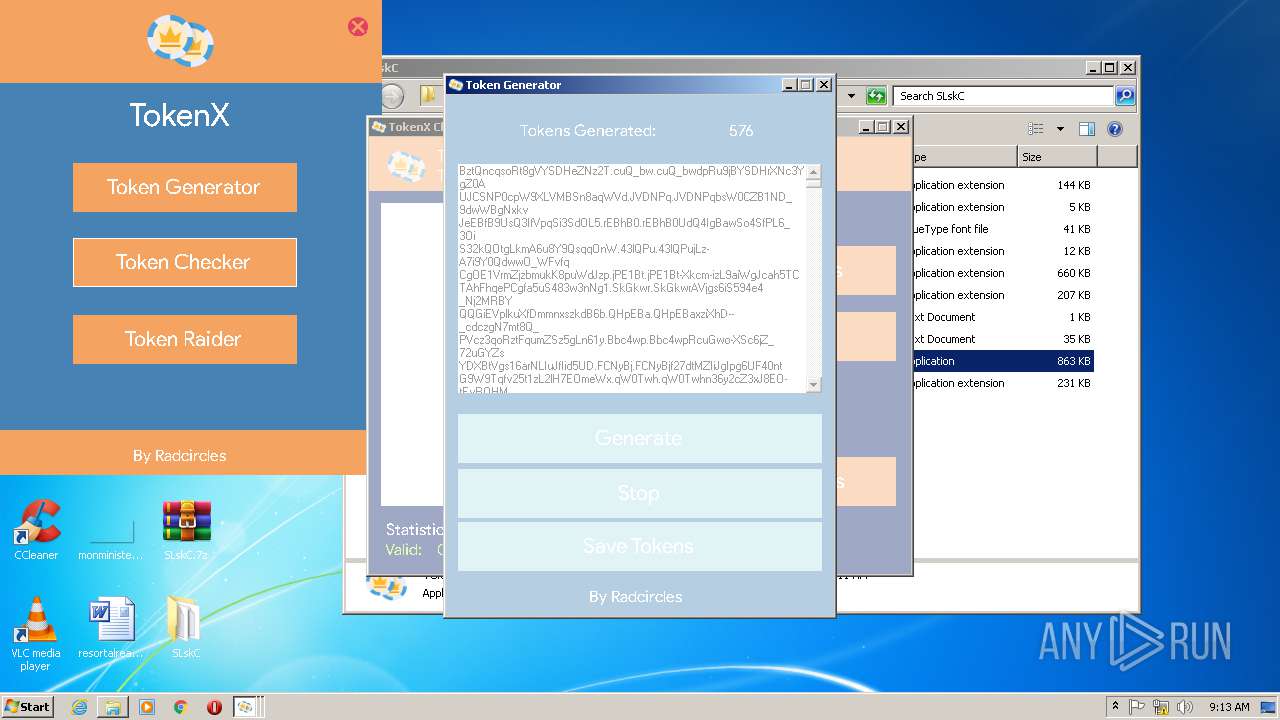
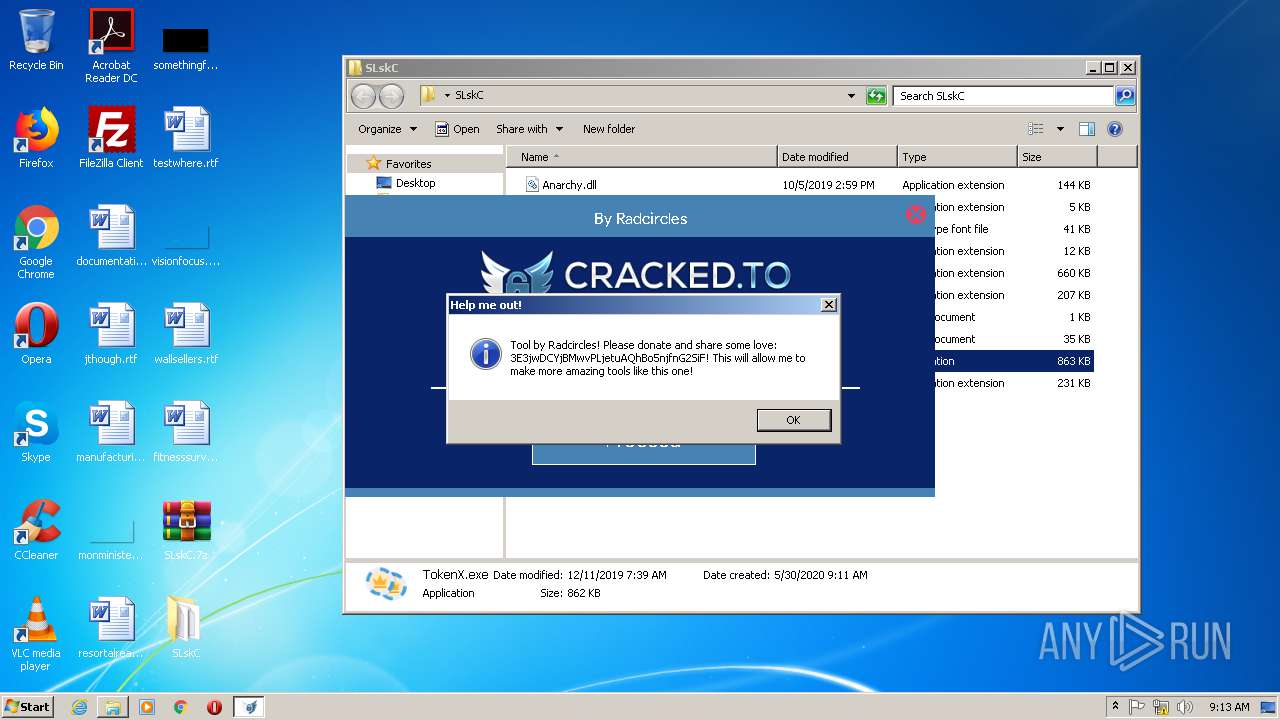
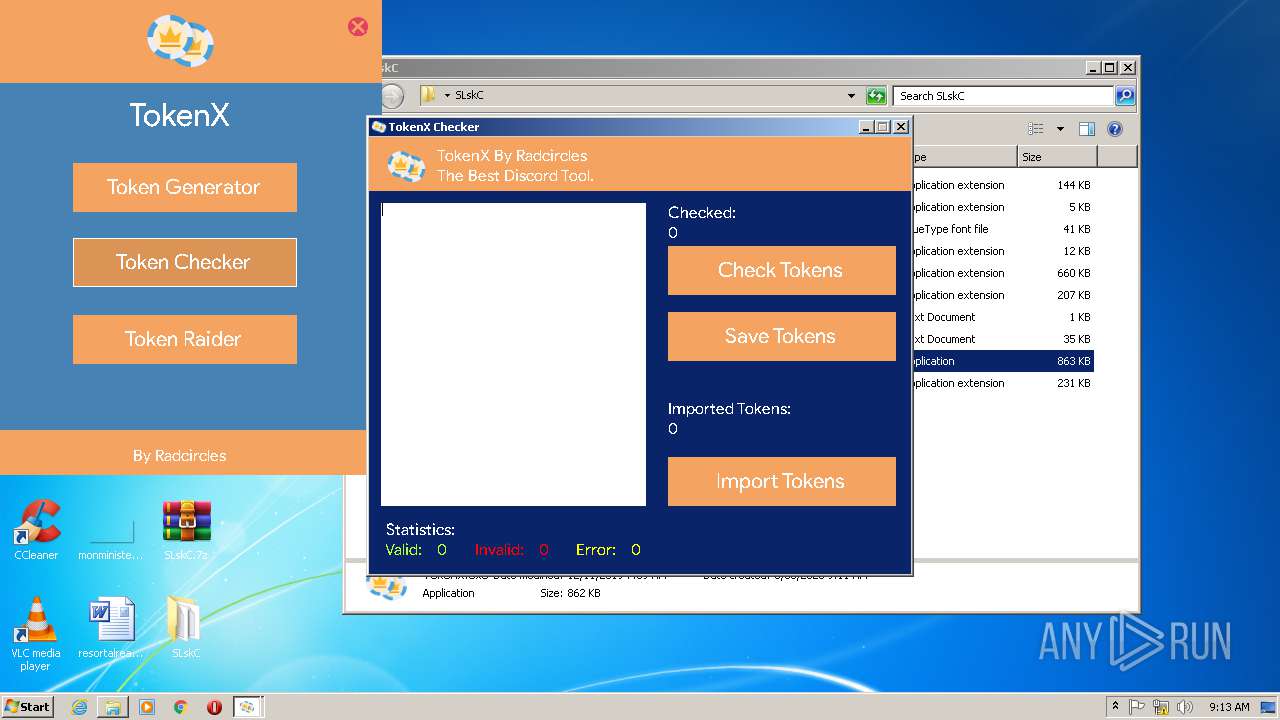
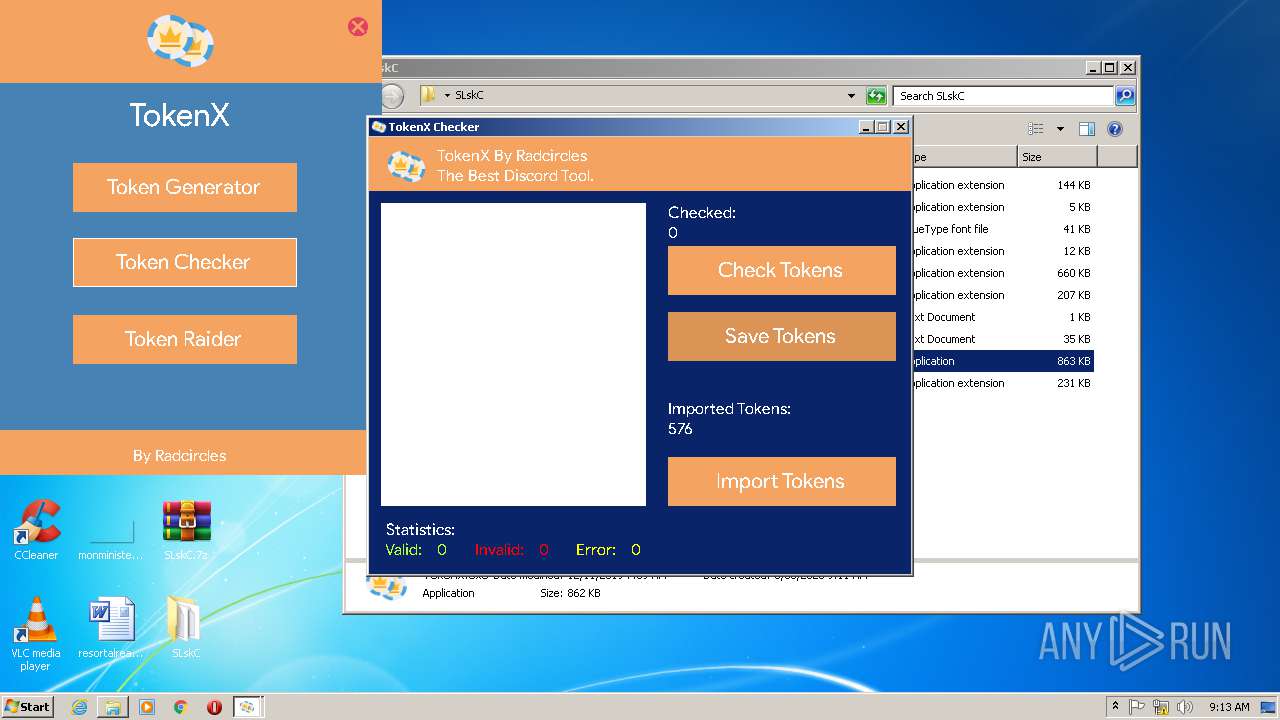
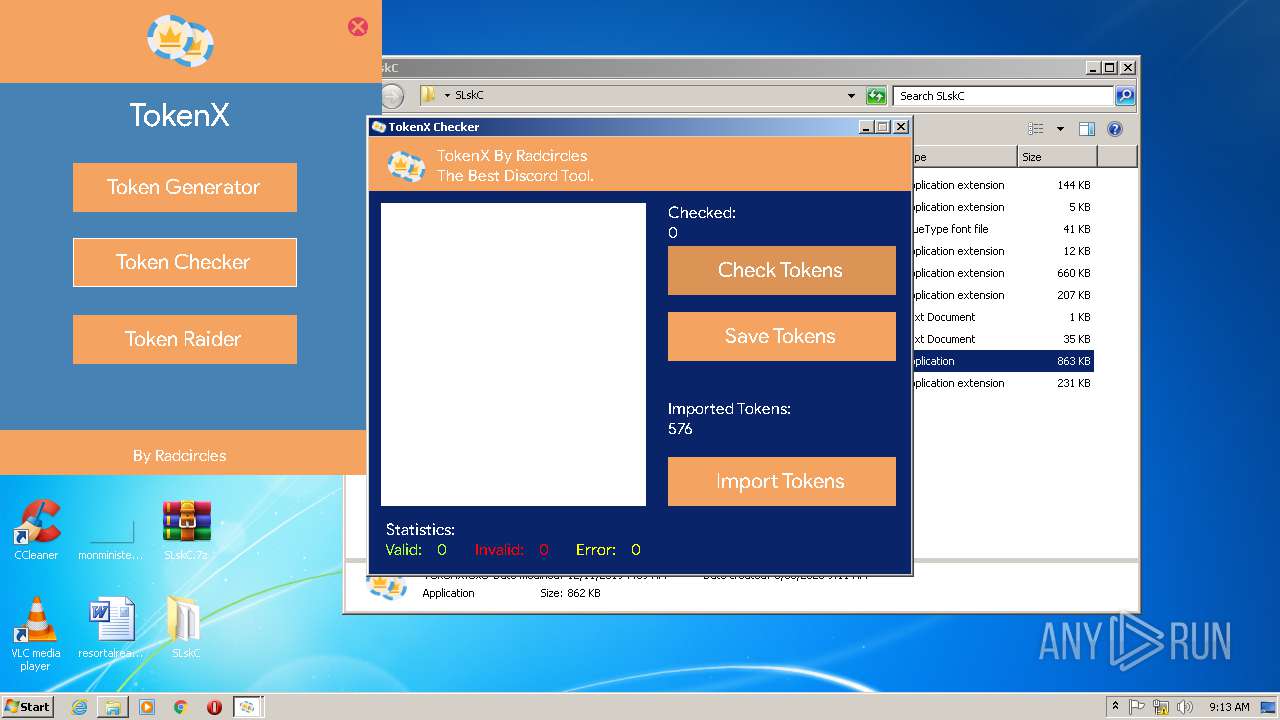
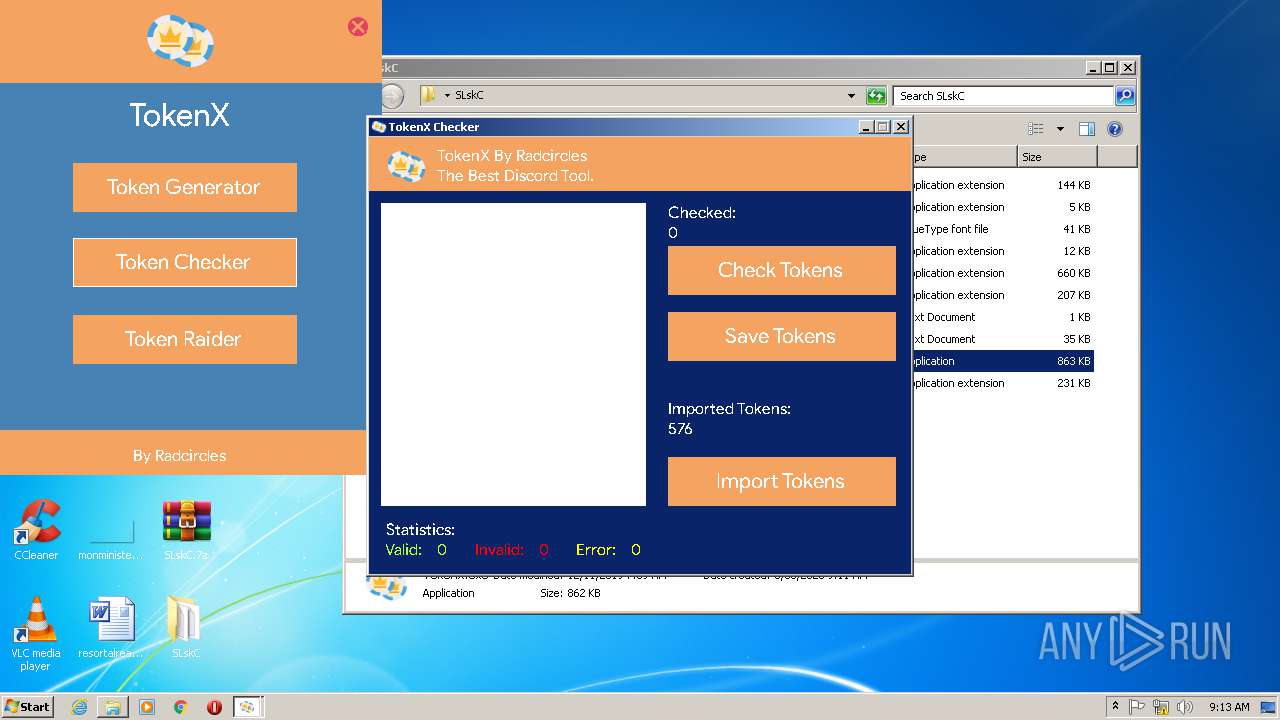
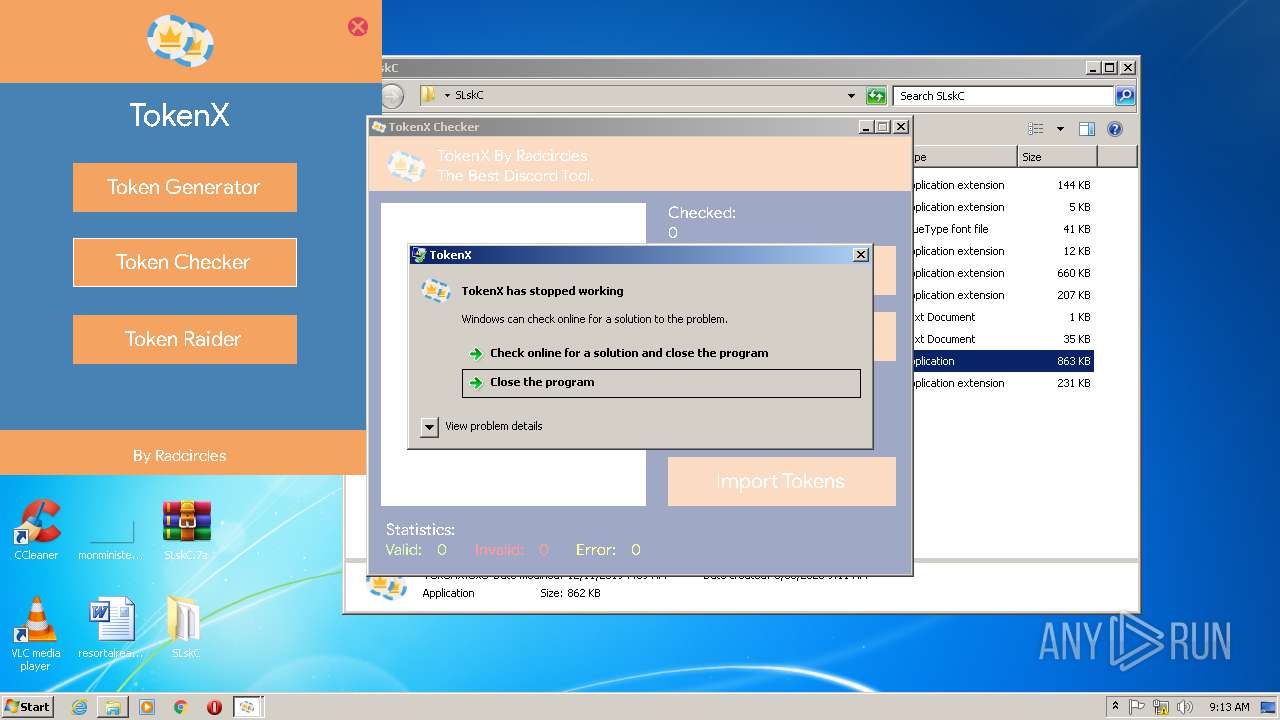
MALICIOUS
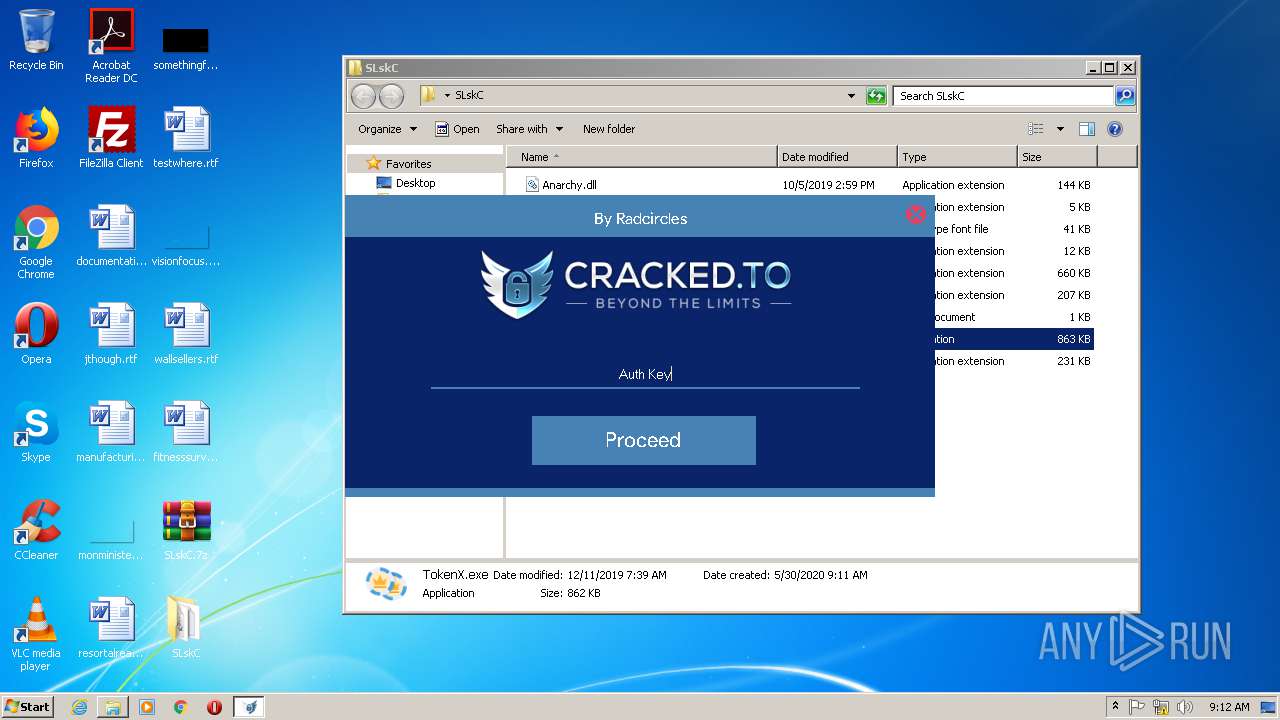
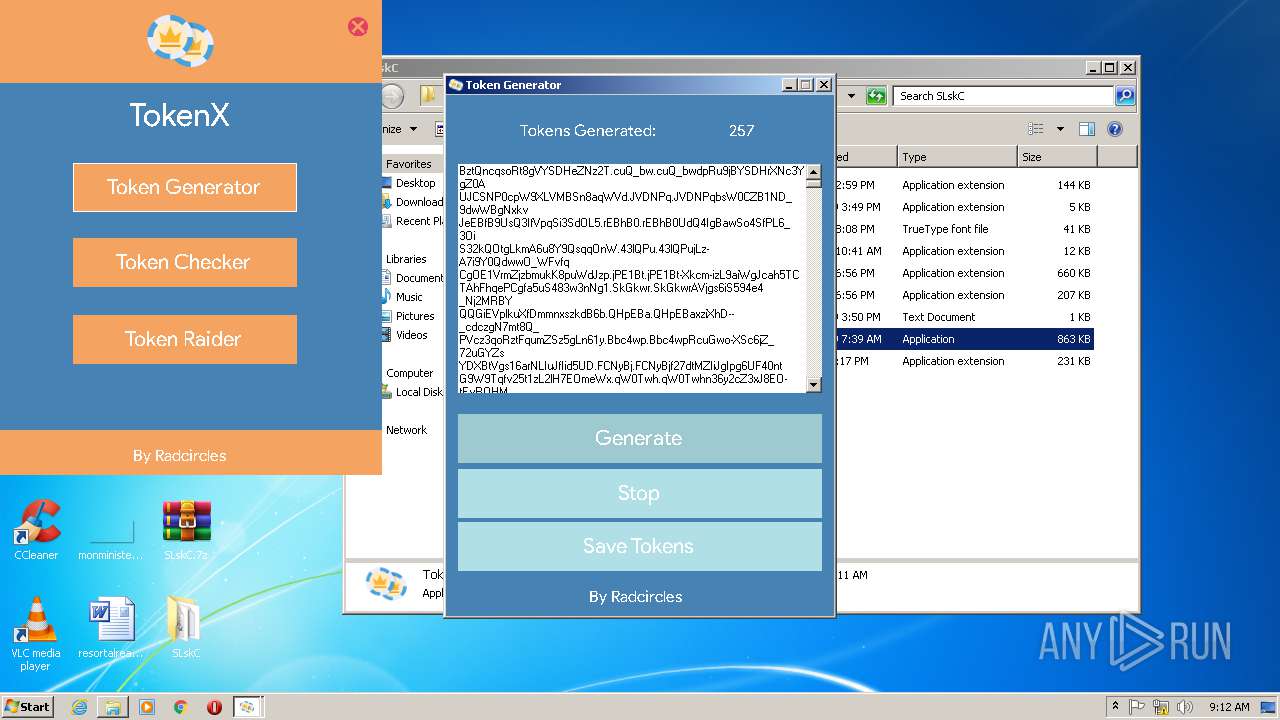
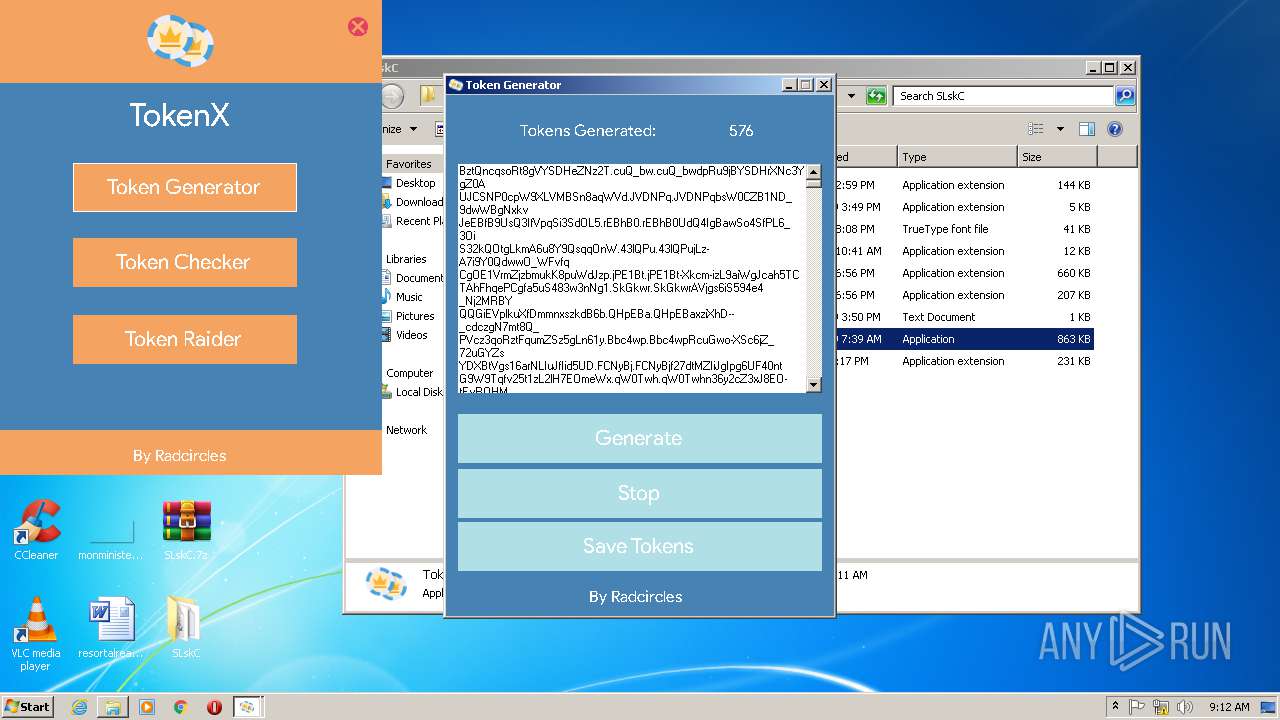
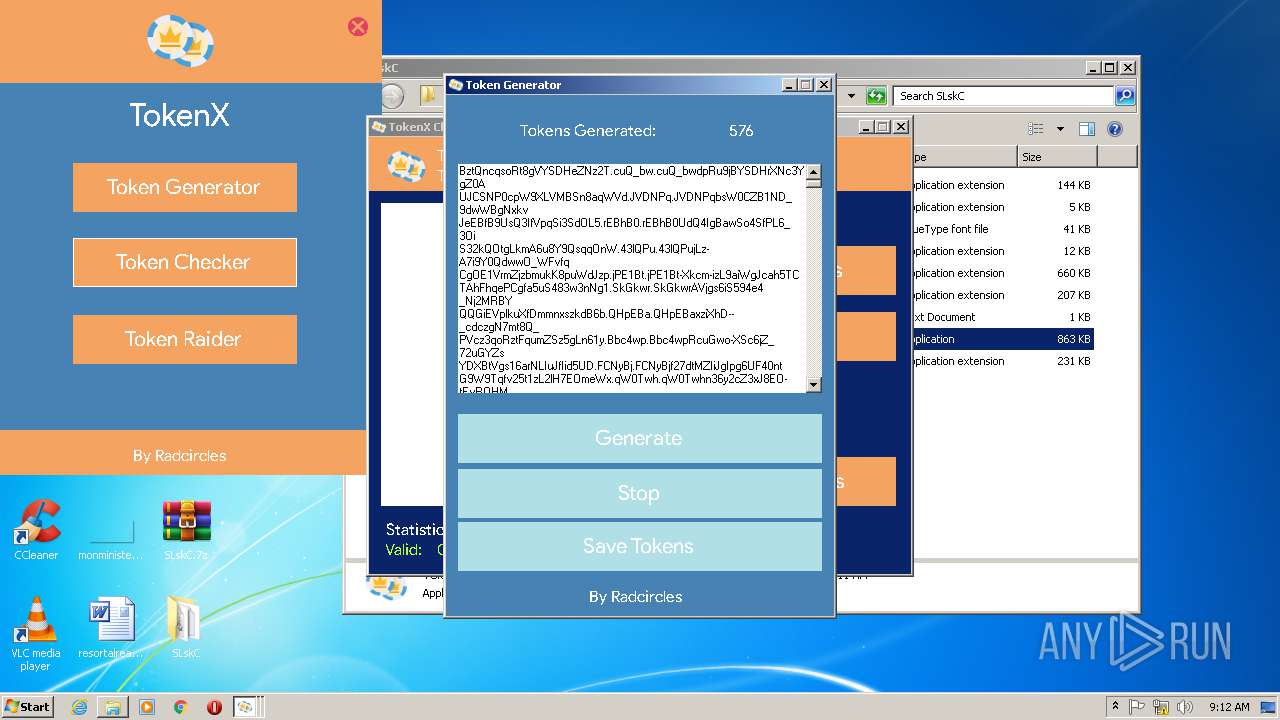
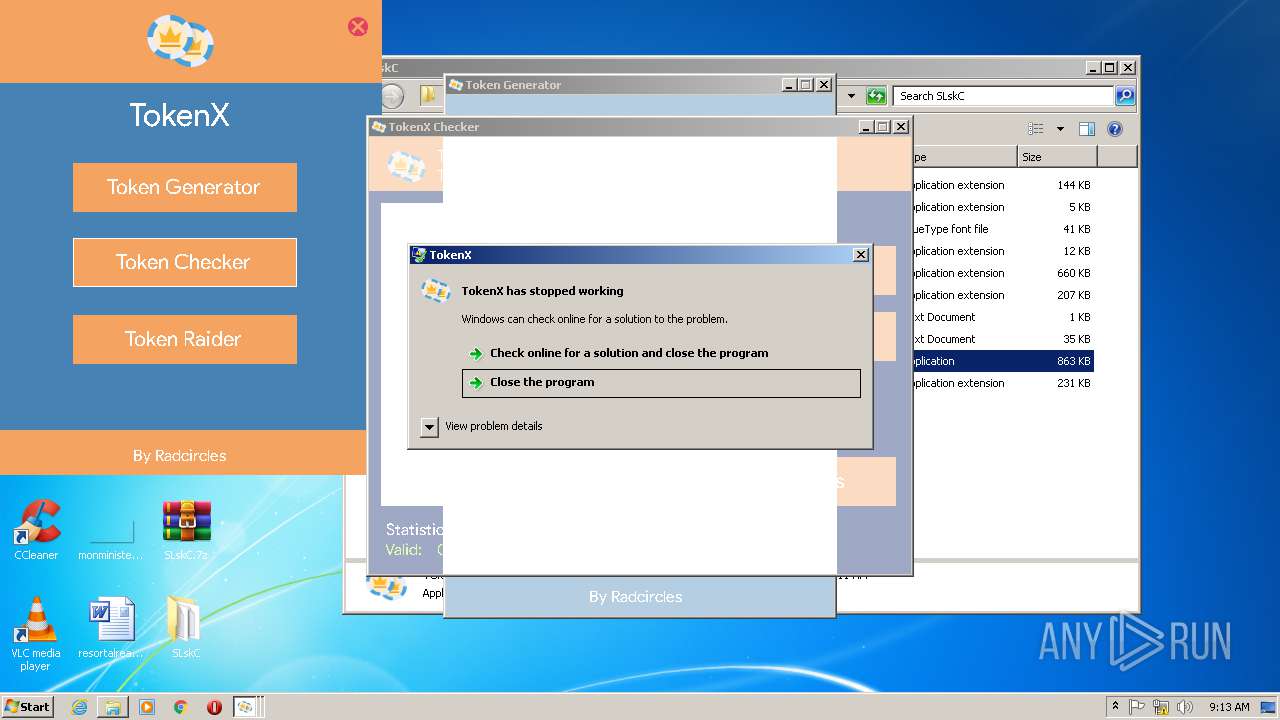
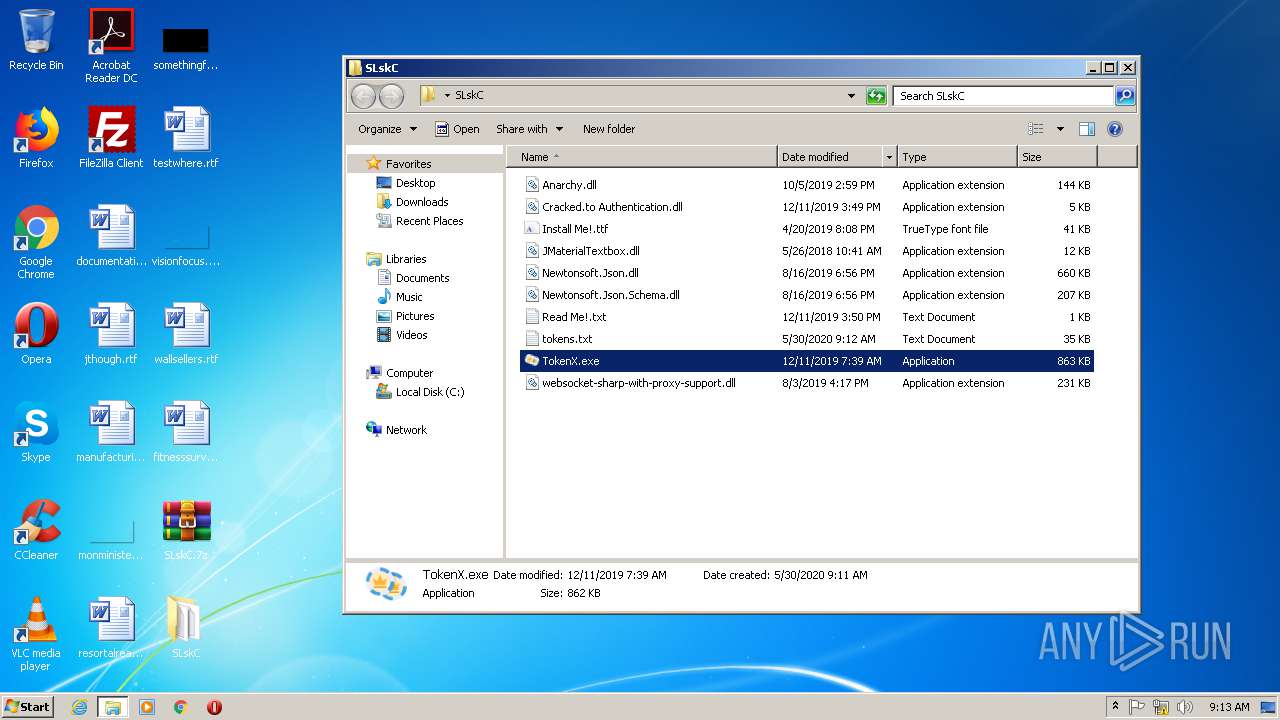
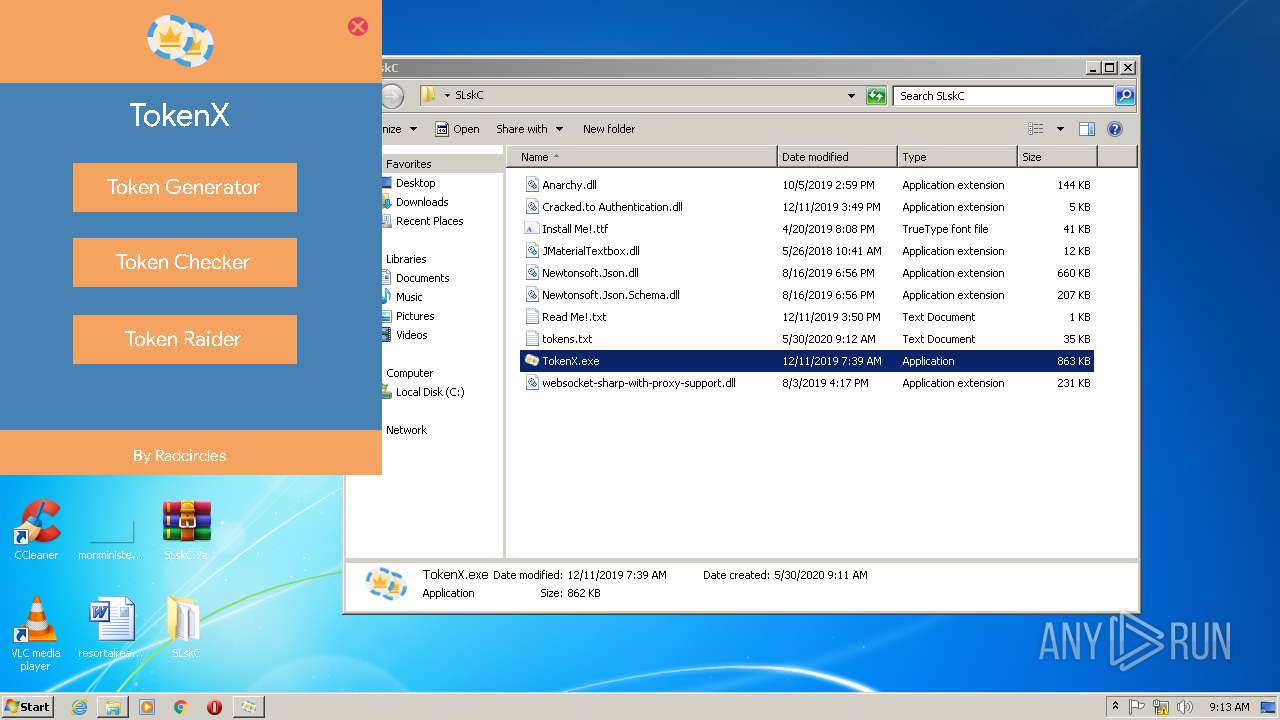
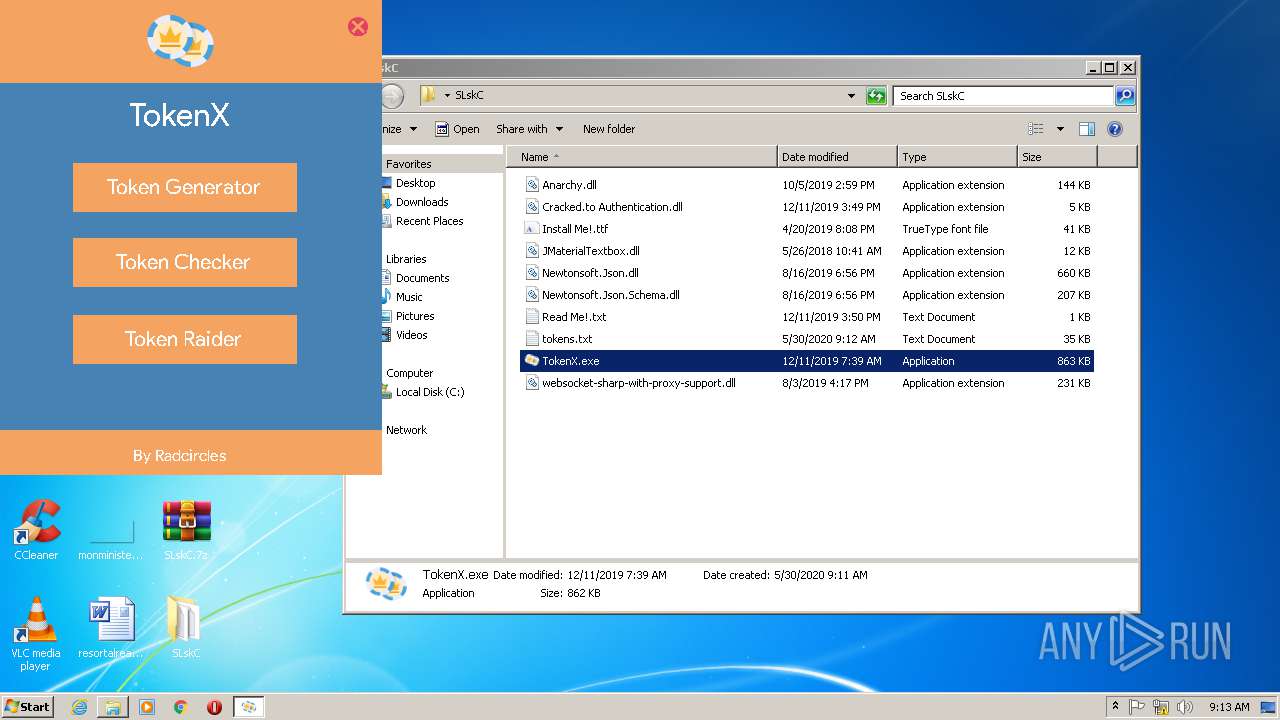
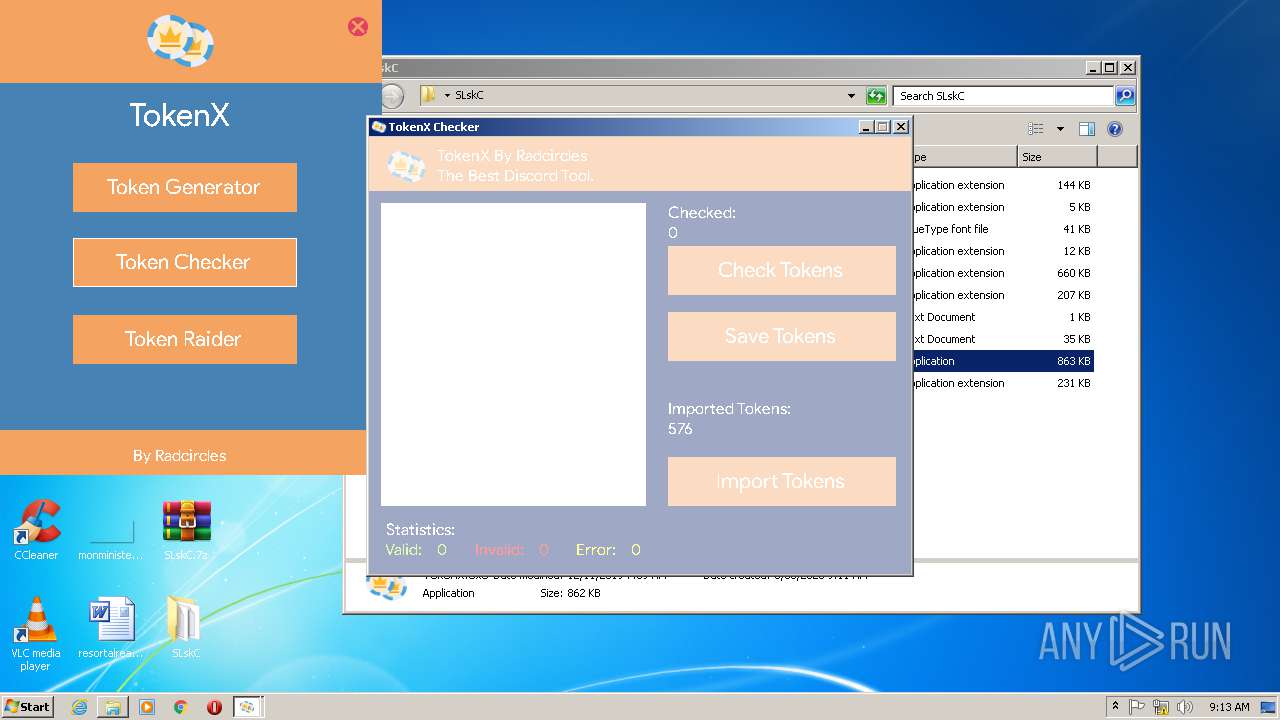
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1132)
- TokenX.exe (PID: 3872)
- TokenX.exe (PID: 340)
Application was dropped or rewritten from another process
- TokenX.exe (PID: 3872)
- TokenX.exe (PID: 340)
SUSPICIOUS
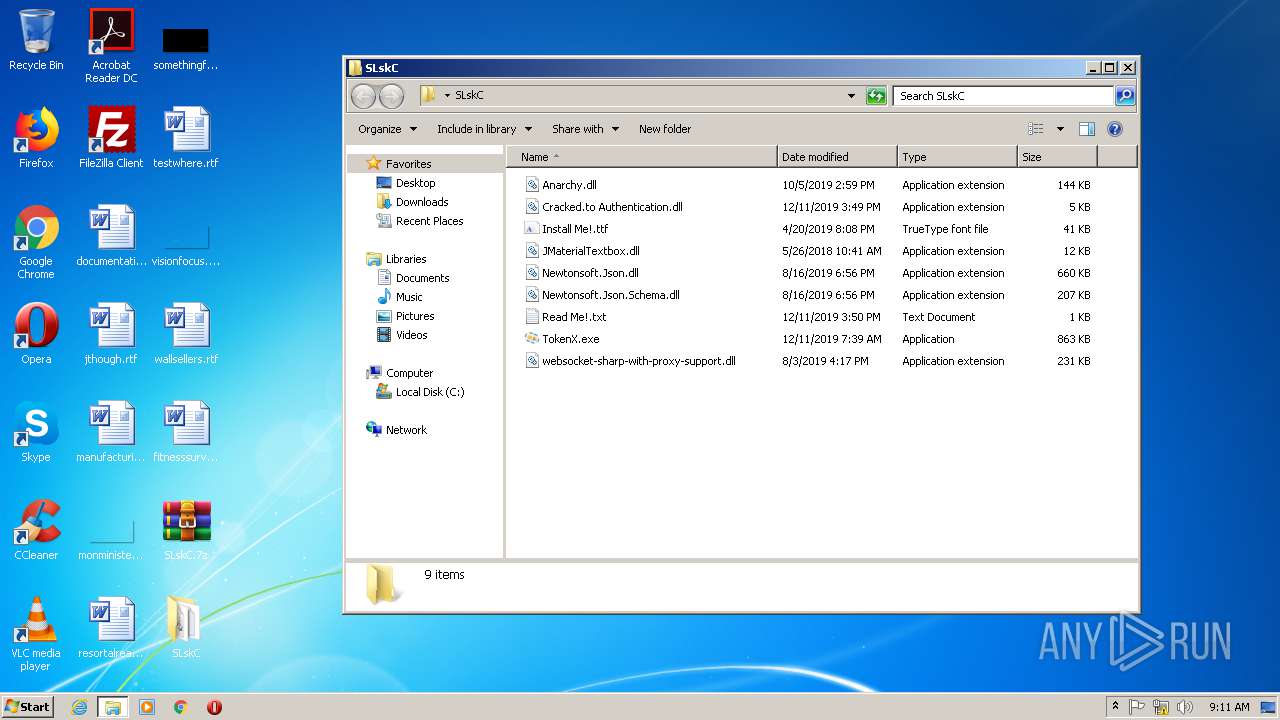
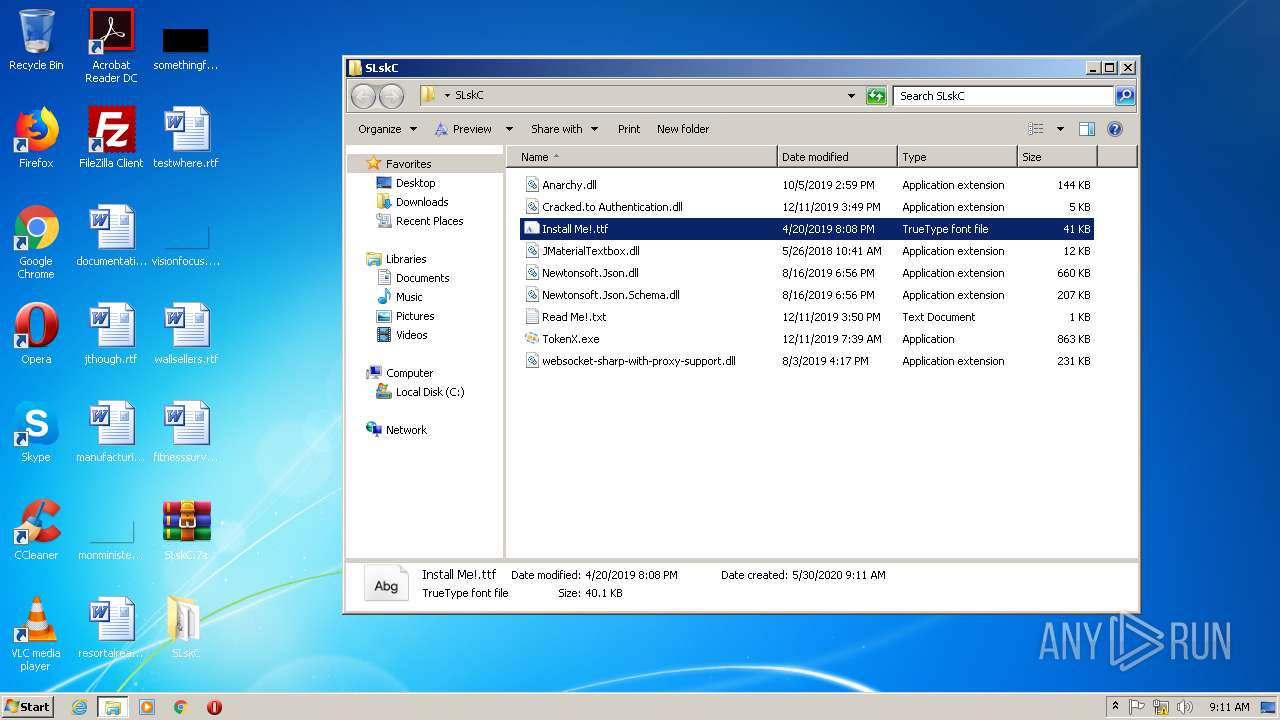
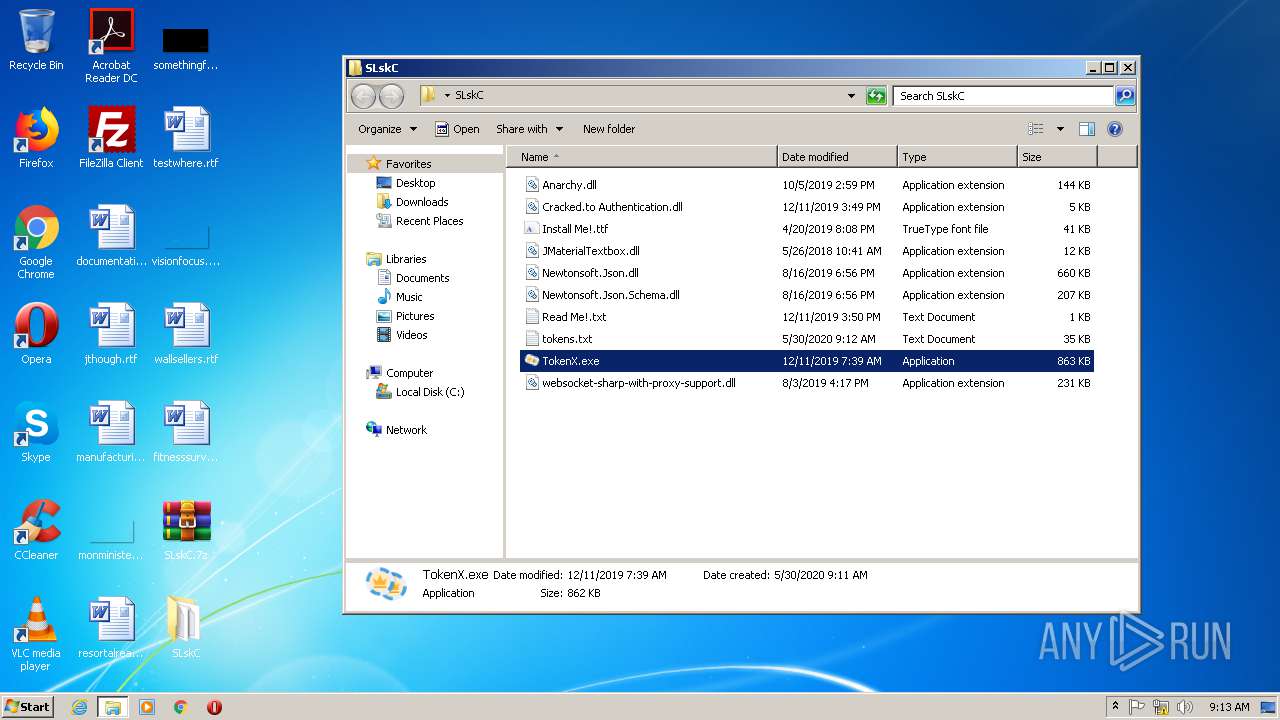
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3716)
Executed via COM
- DllHost.exe (PID: 3580)
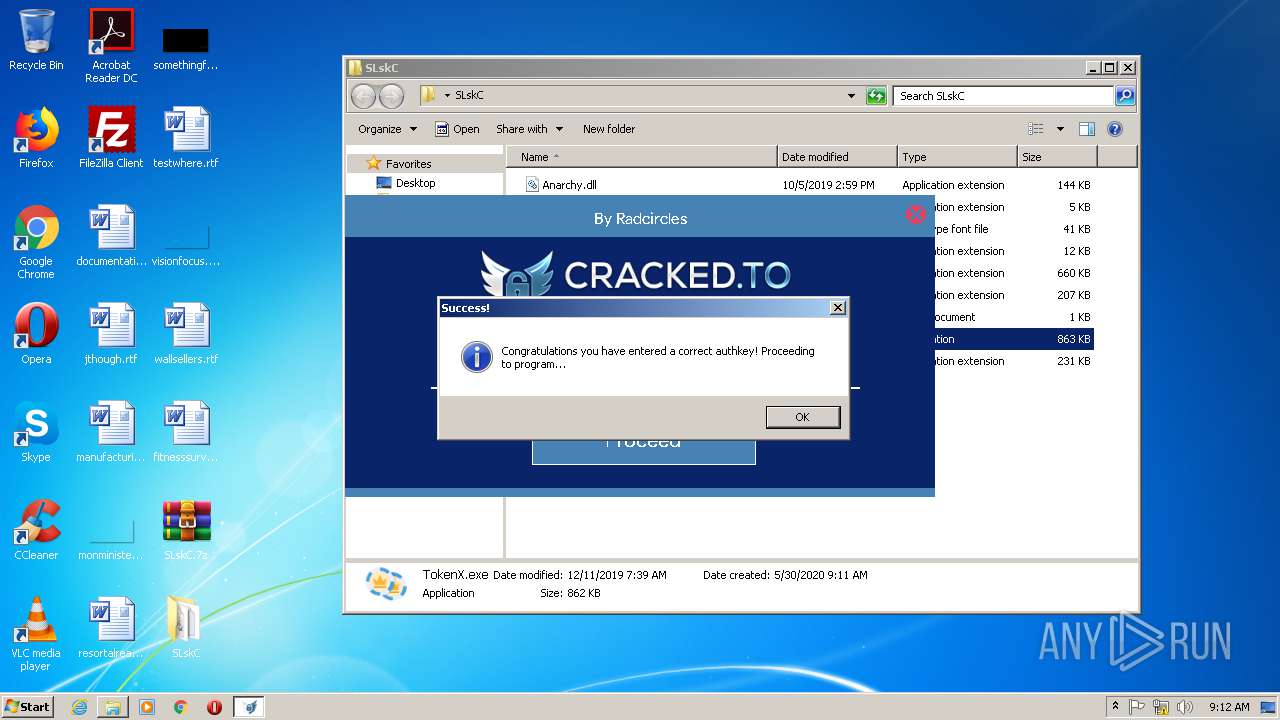
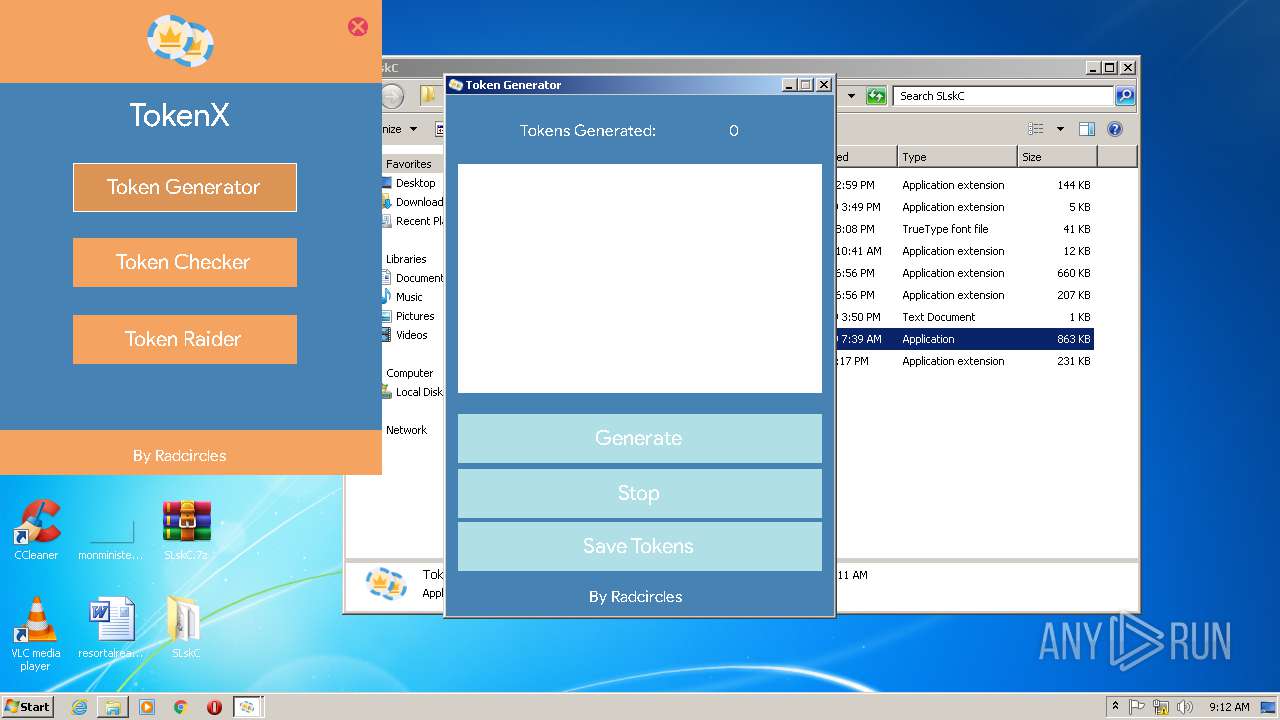
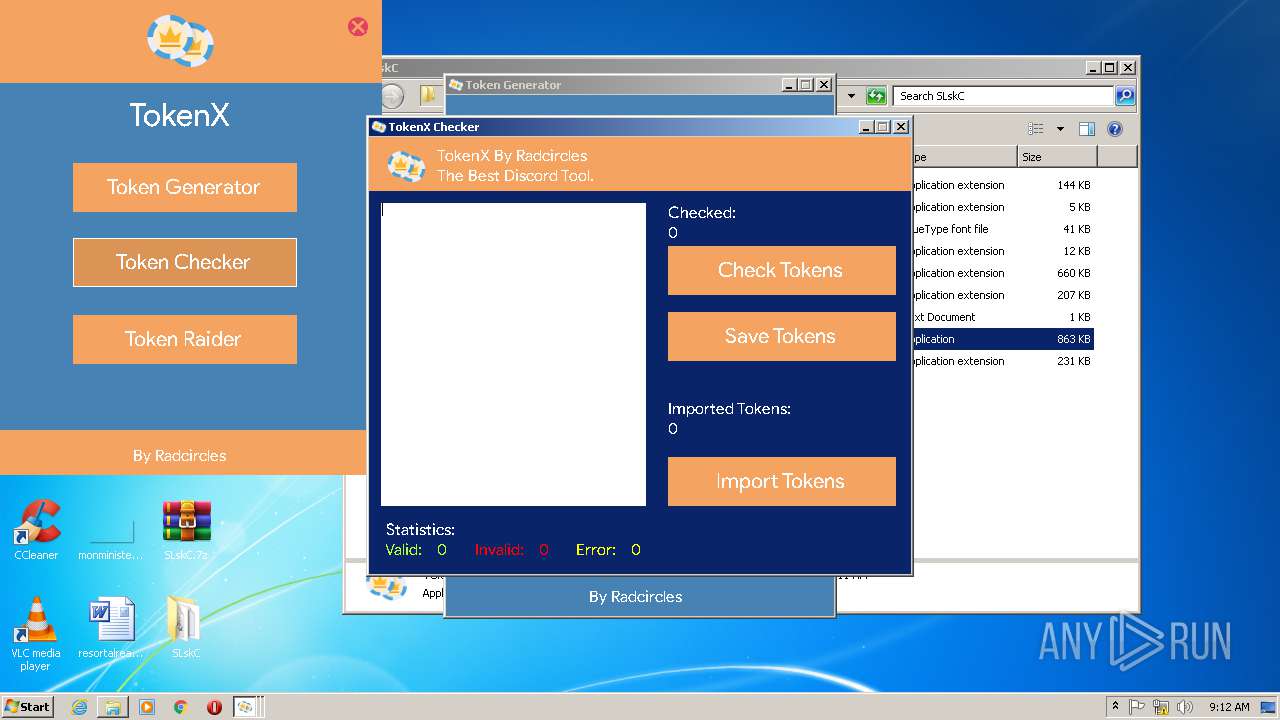
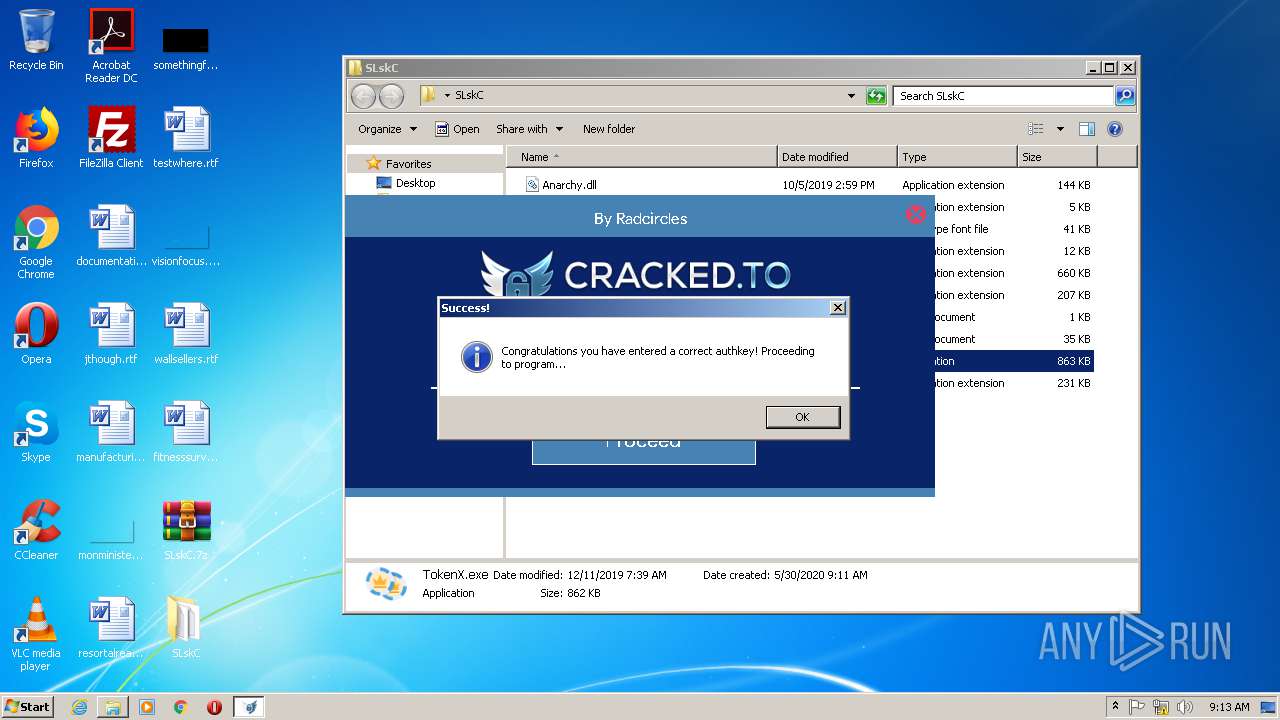
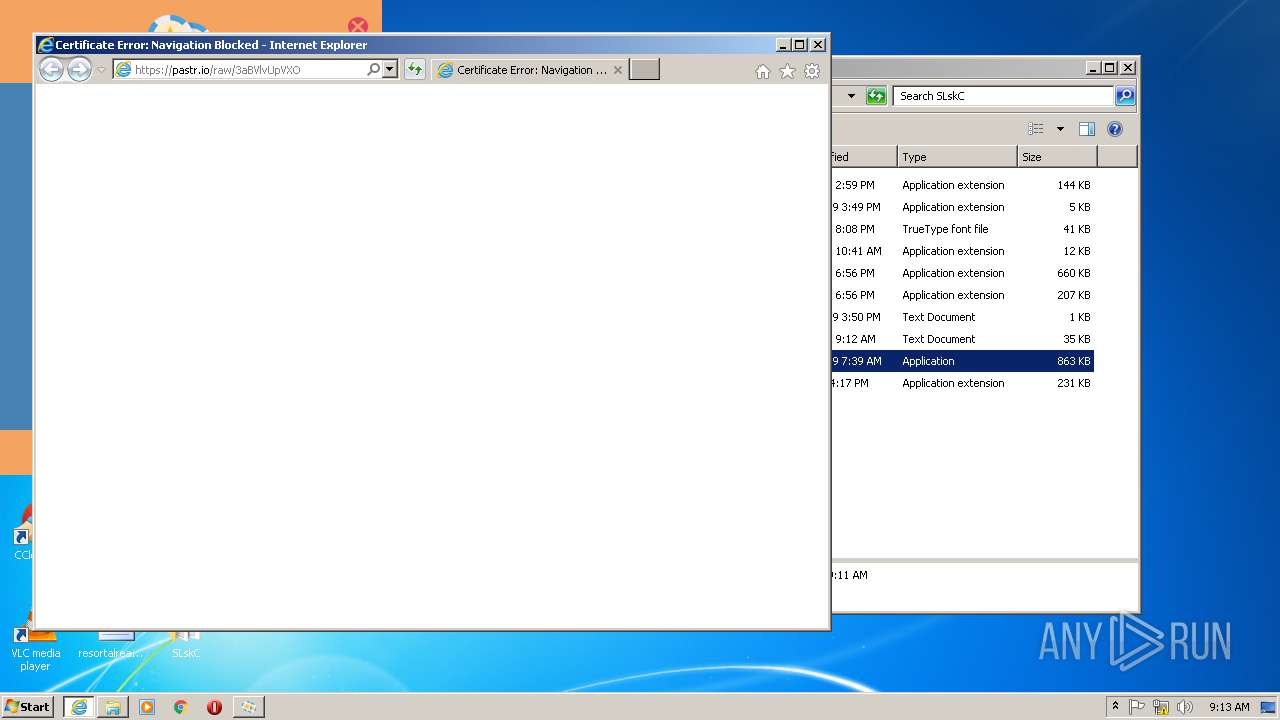
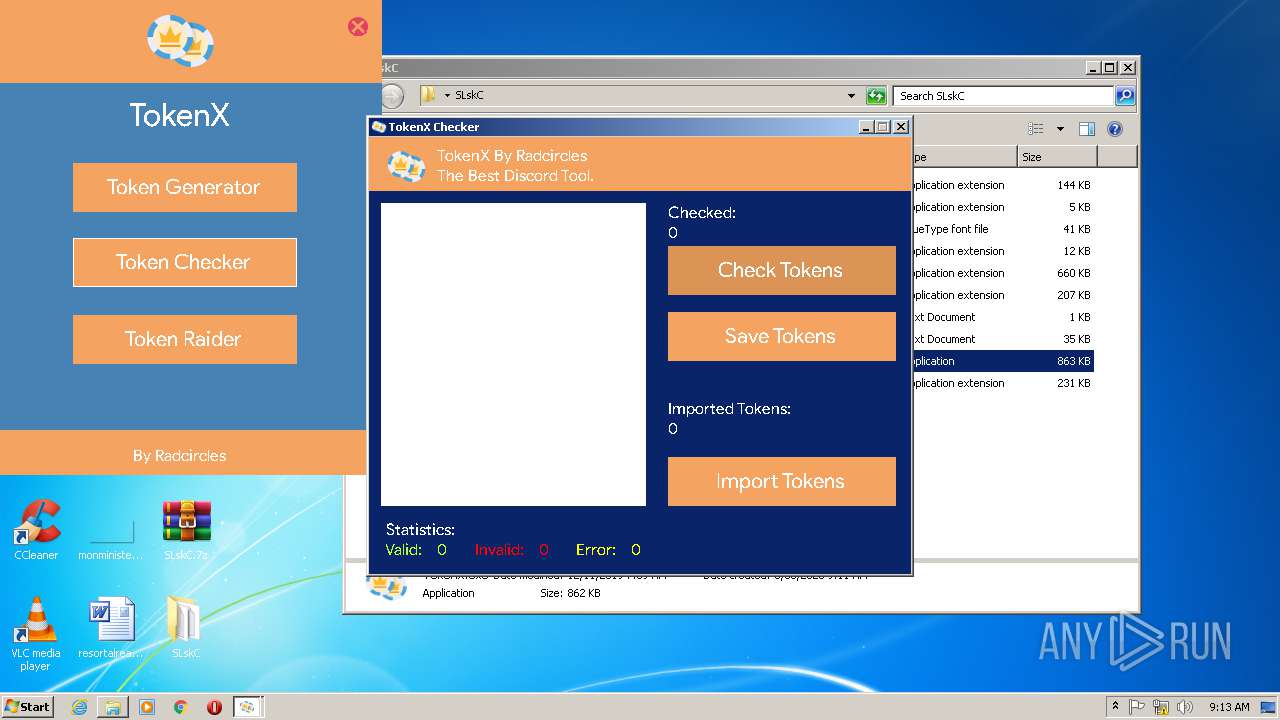
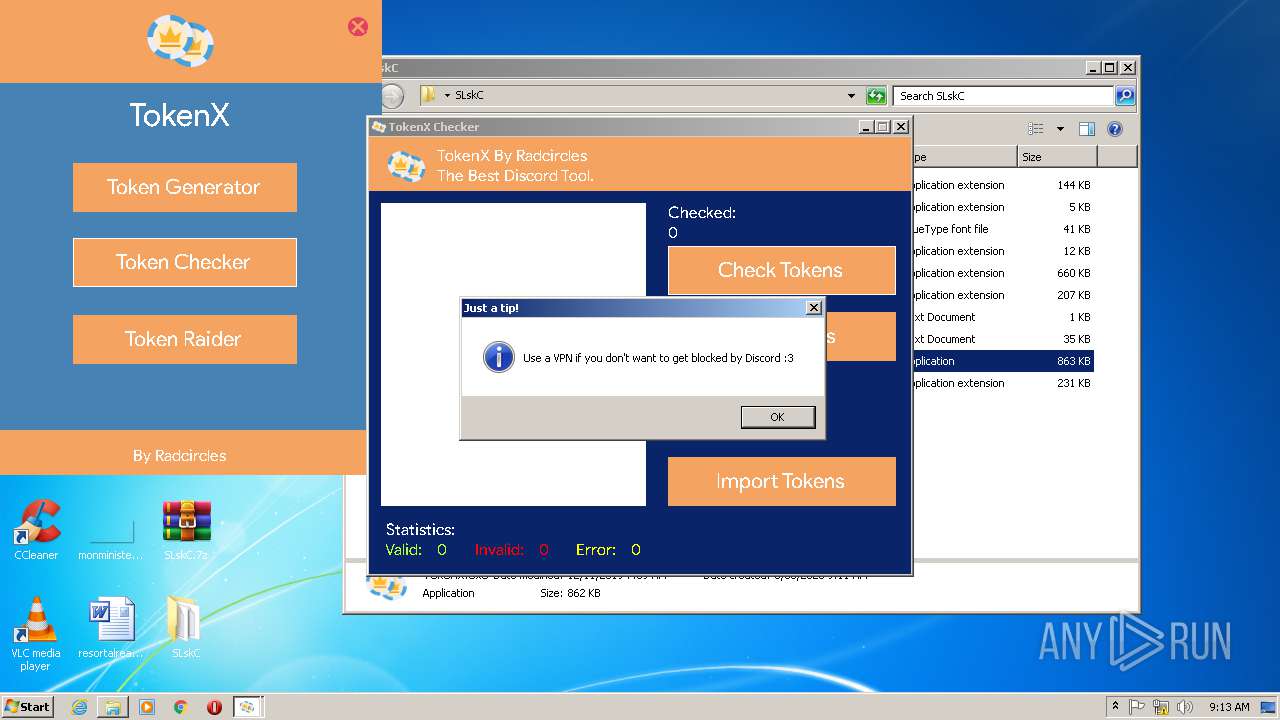
Starts Internet Explorer
- TokenX.exe (PID: 3872)
- TokenX.exe (PID: 340)
Creates files in the Windows directory
- DllHost.exe (PID: 3580)
INFO
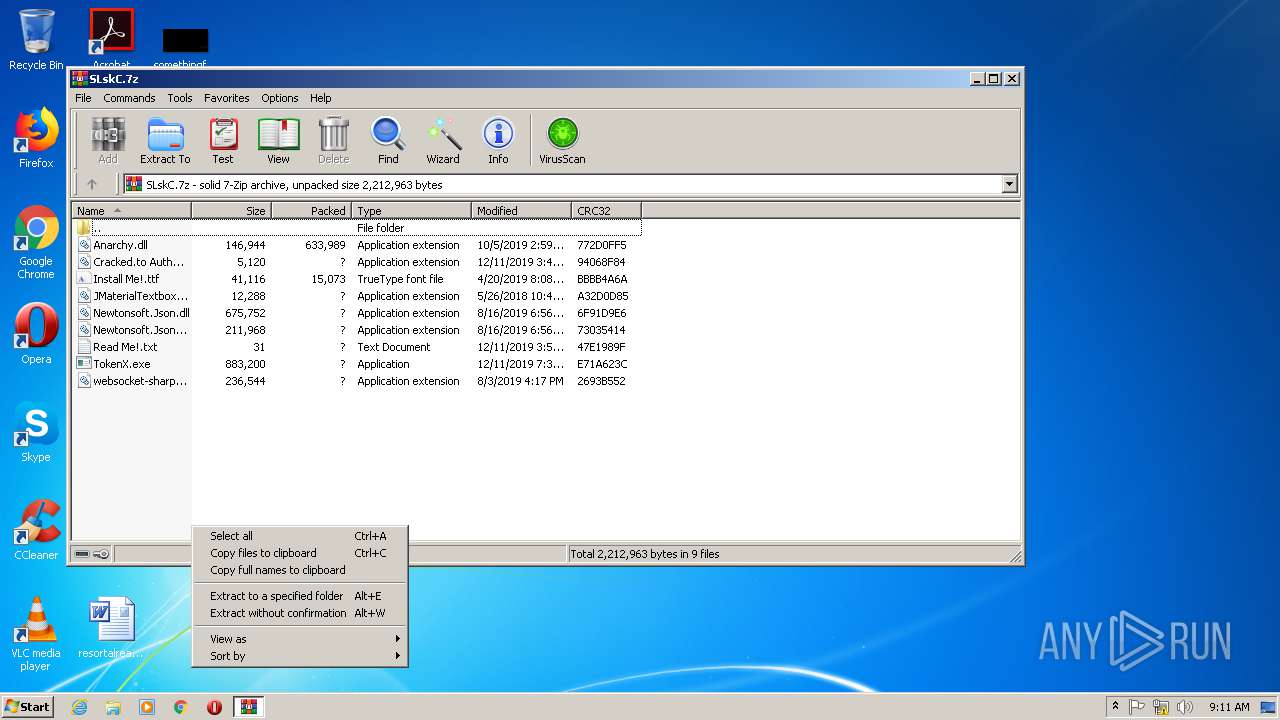
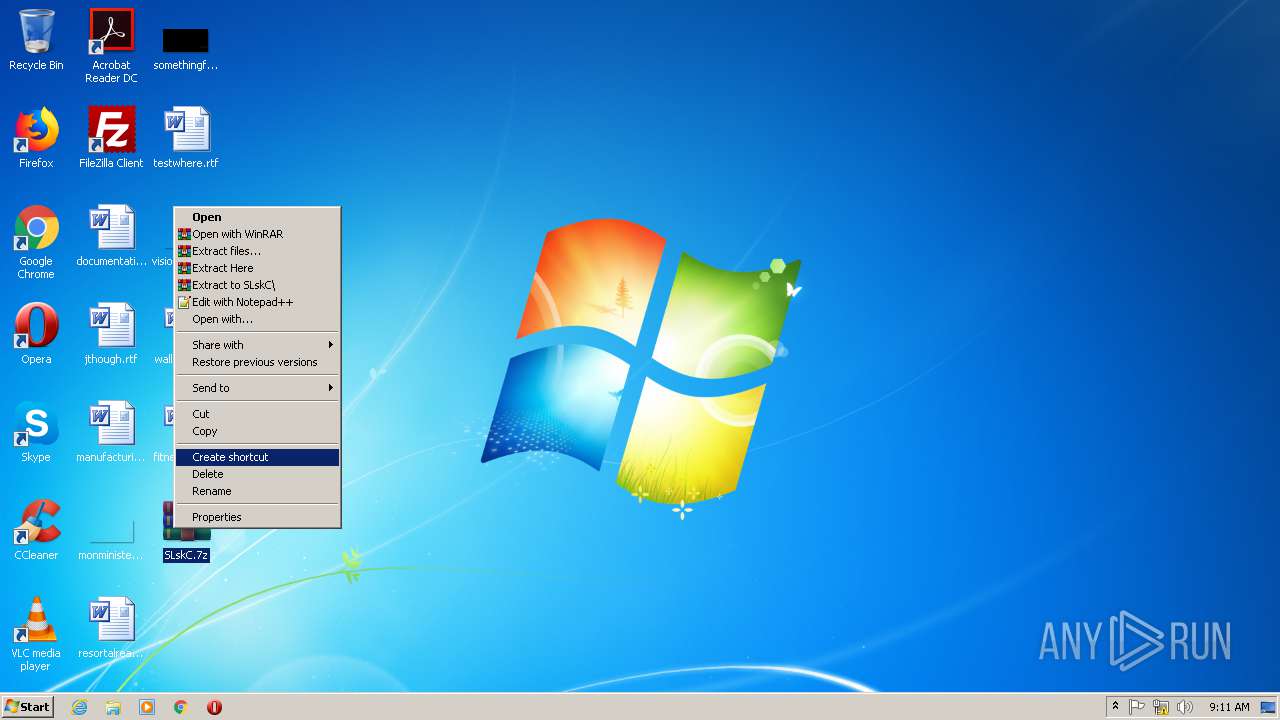
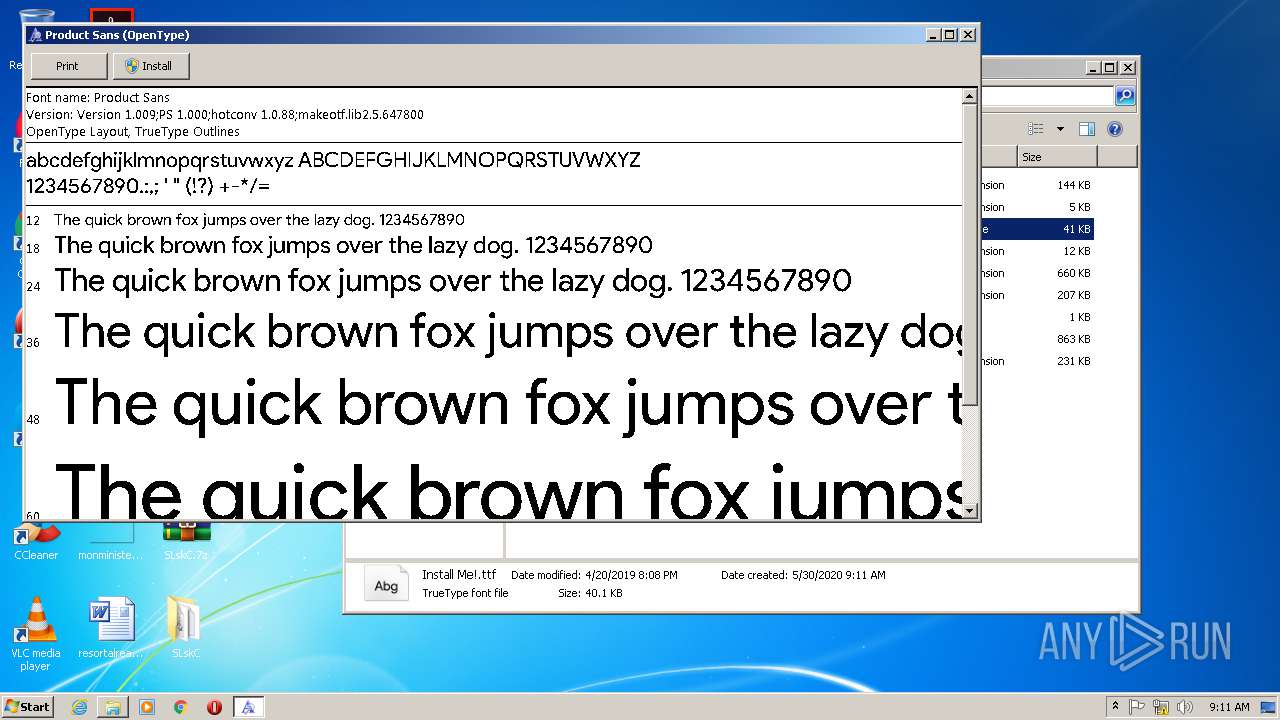
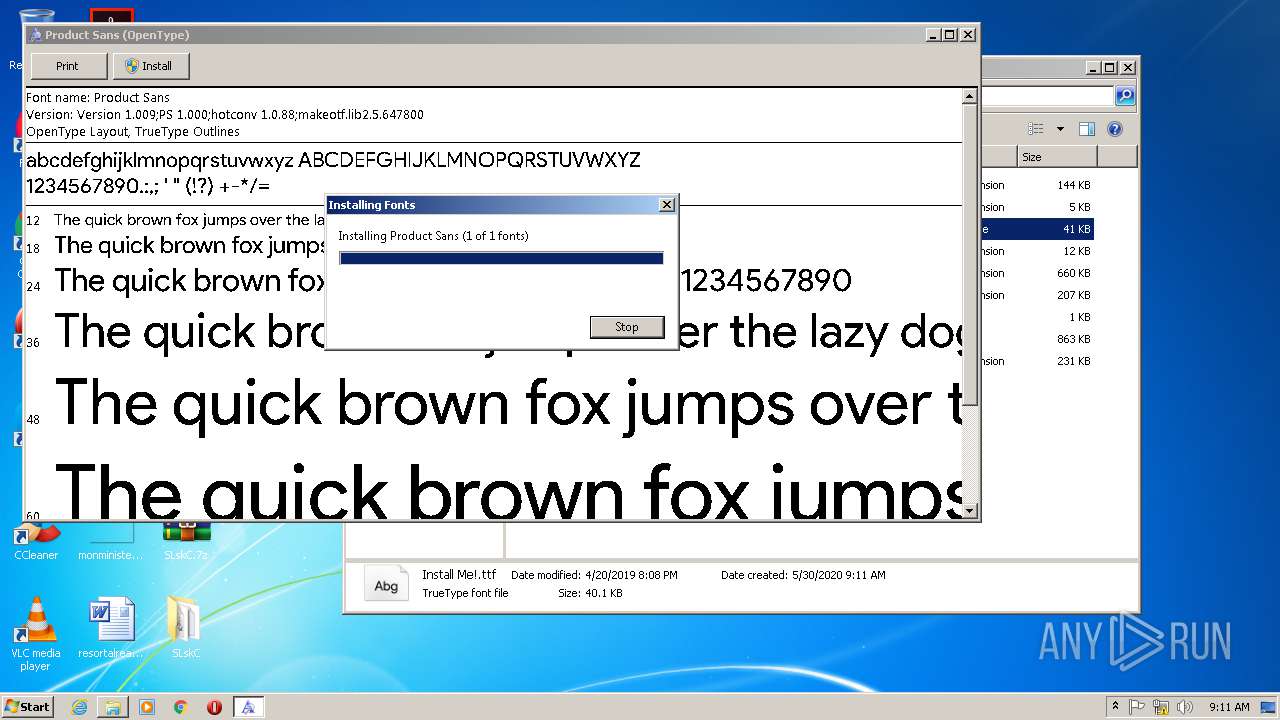
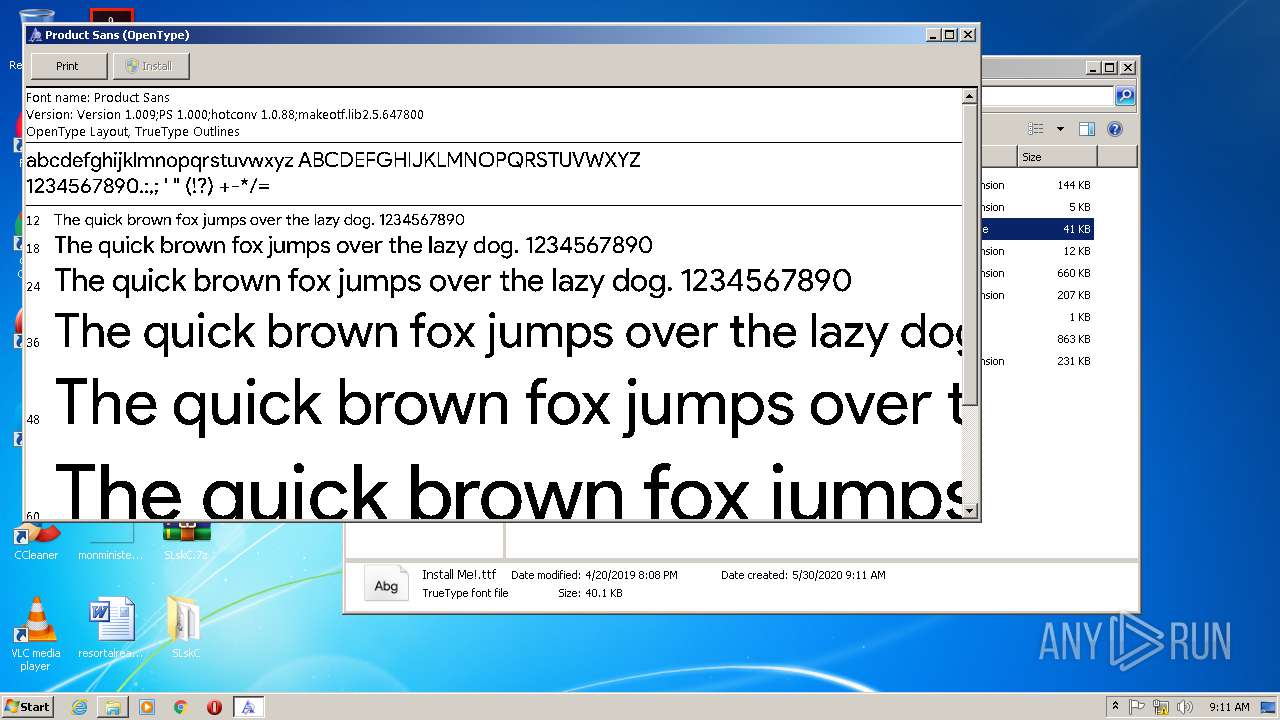
Manual execution by user
- WinRAR.exe (PID: 3716)
- fontview.exe (PID: 2360)
- TokenX.exe (PID: 3872)
- TokenX.exe (PID: 340)
Reads Internet Cache Settings
- iexplore.exe (PID: 1004)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 3416)
- iexplore.exe (PID: 3428)
Changes internet zones settings
- iexplore.exe (PID: 1004)
- iexplore.exe (PID: 3416)
Reads internet explorer settings
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 3428)
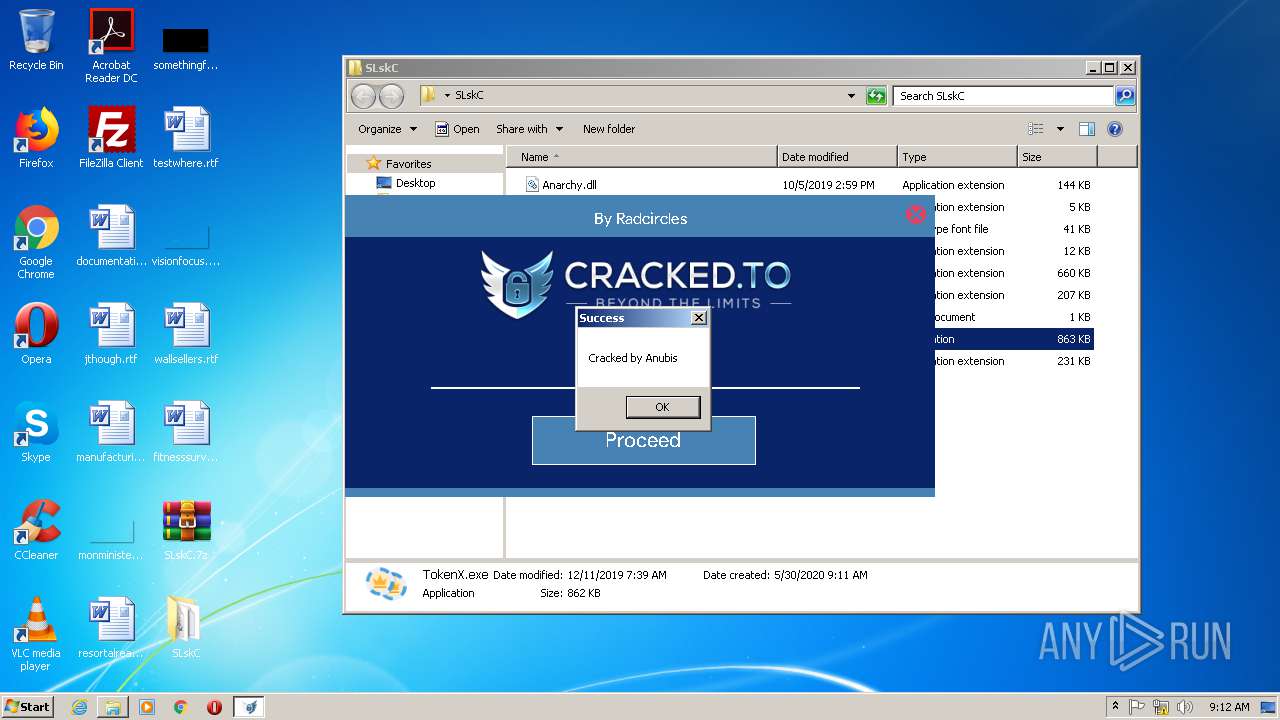
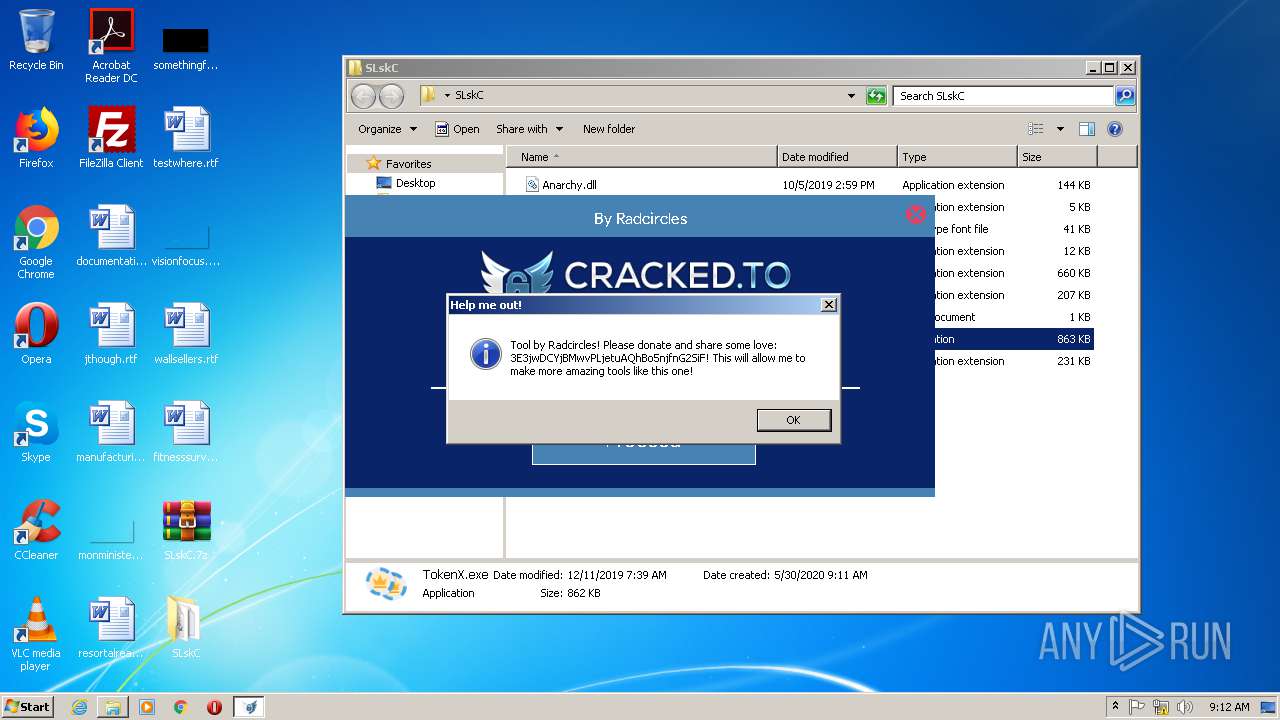
Dropped object may contain Bitcoin addresses
- TokenX.exe (PID: 3872)
Application launched itself
- iexplore.exe (PID: 3416)
Reads settings of System Certificates
- TokenX.exe (PID: 340)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 1004)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1004)
Changes settings of System certificates
- iexplore.exe (PID: 1004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
55
Monitored processes
11
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
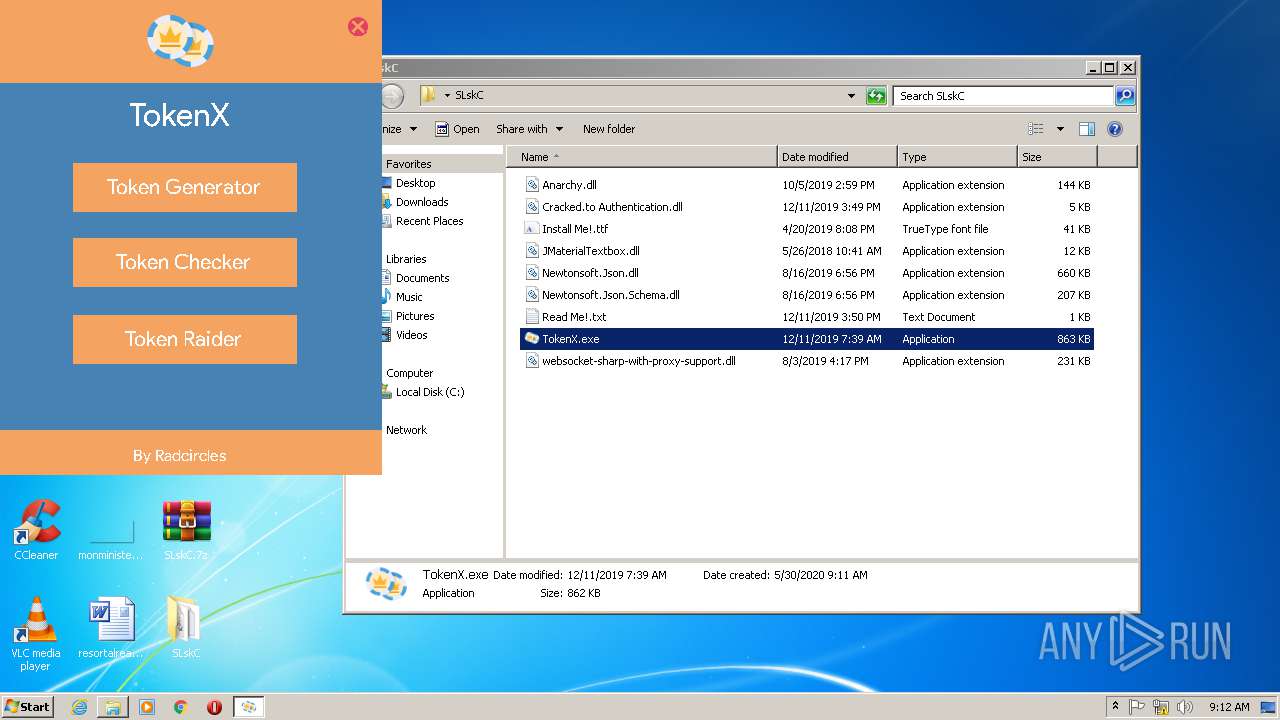
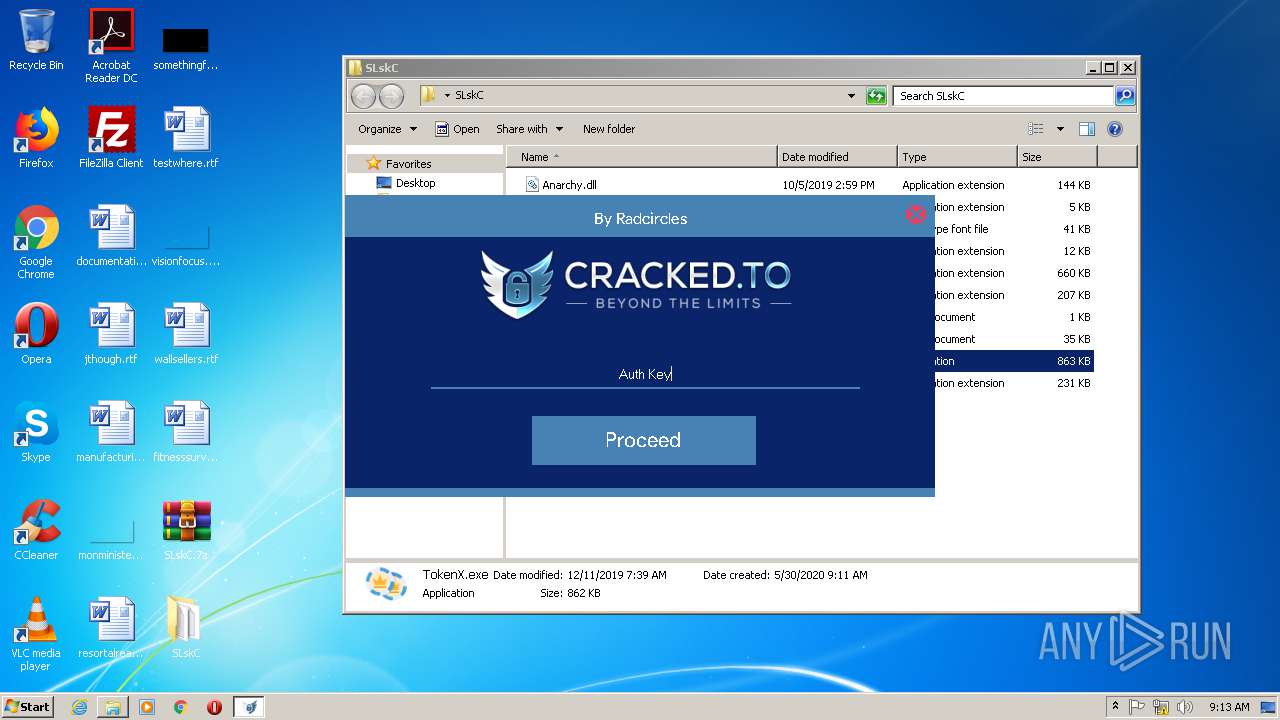
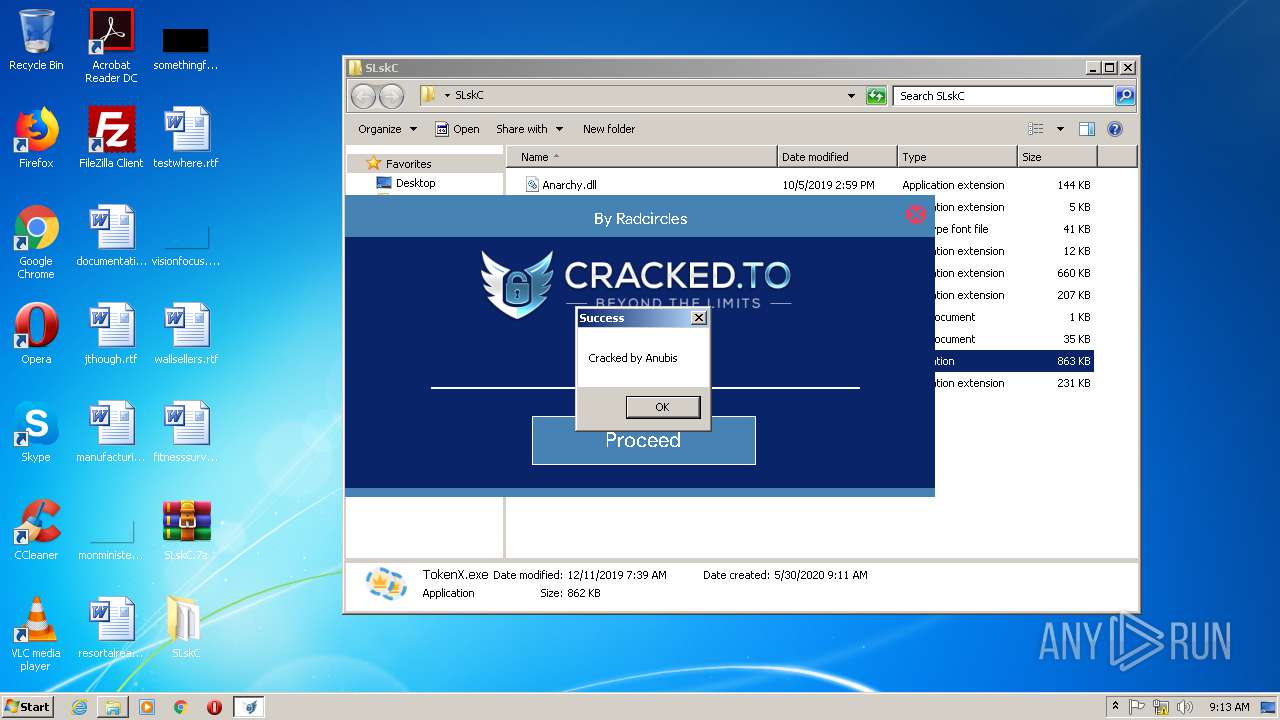
| 340 | "C:\Users\admin\Desktop\SLskC\TokenX.exe" | C:\Users\admin\Desktop\SLskC\TokenX.exe | explorer.exe | ||||||||||||
User: admin Company: HP Inc. Integrity Level: MEDIUM Description: TokenX Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
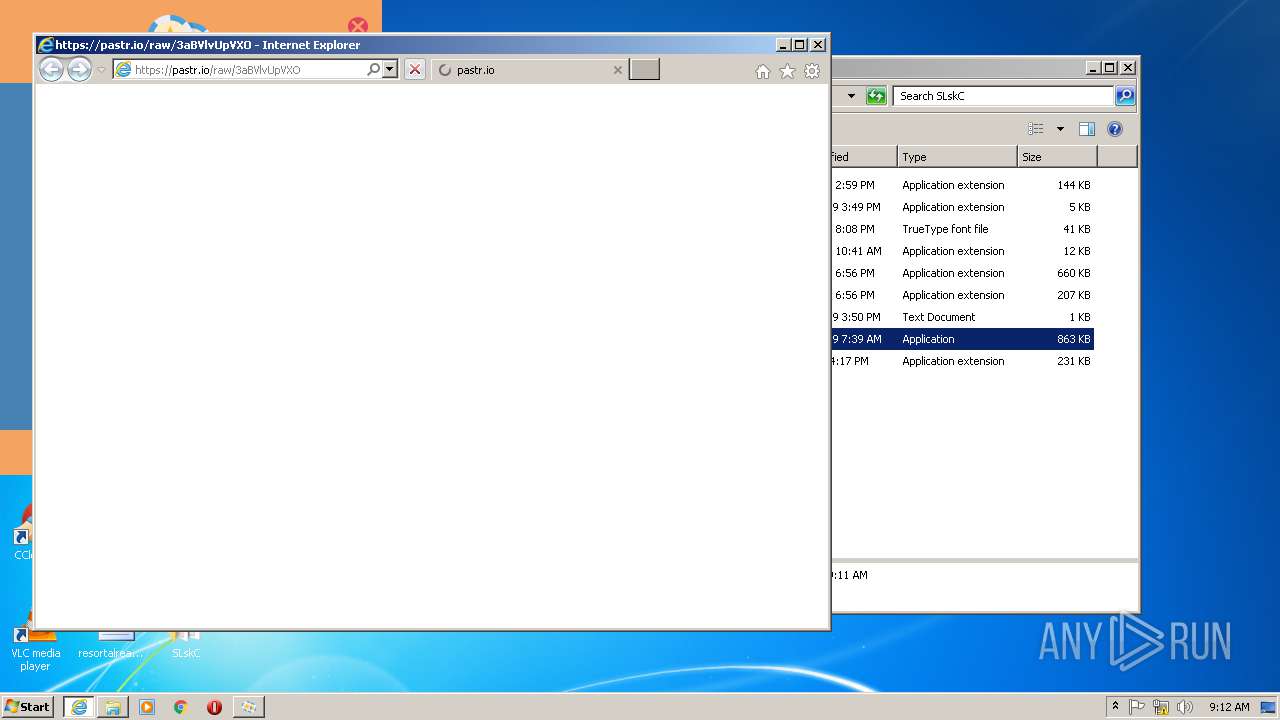
| 1004 | "C:\Program Files\Internet Explorer\iexplore.exe" https://pastr.io/raw/3aBVlvUpVXO | C:\Program Files\Internet Explorer\iexplore.exe | TokenX.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1132 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | "C:\Windows\System32\fontview.exe" C:\Users\admin\Desktop\SLskC\Install Me!.ttf | C:\Windows\System32\fontview.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Font Viewer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\SLskC.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3416 | "C:\Program Files\Internet Explorer\iexplore.exe" https://pastr.io/raw/3aBVlvUpVXO | C:\Program Files\Internet Explorer\iexplore.exe | — | TokenX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3428 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3416 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3580 | C:\Windows\system32\DllHost.exe /Processid:{642EF9D6-48A5-476B-919A-A507CFD02C0F} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3676 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1004 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3716 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\SLskC.7z" C:\Users\admin\Desktop\SLskC\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
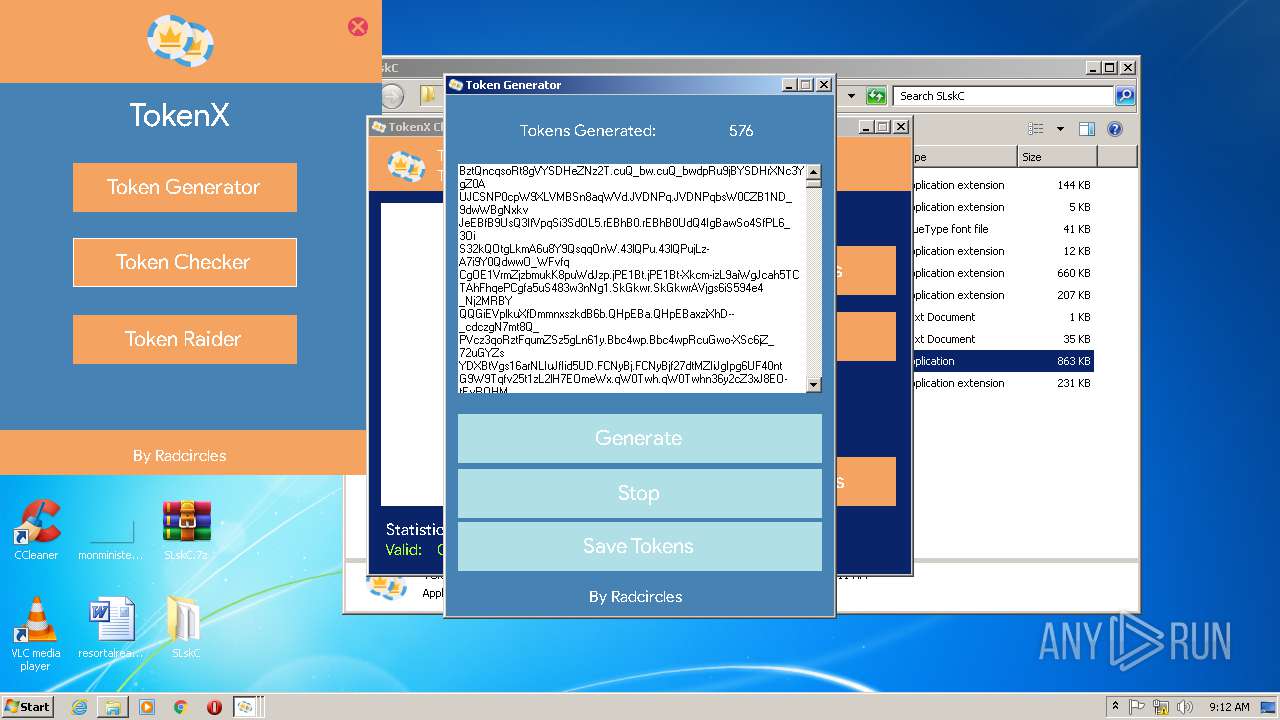
Total events
9 723
Read events
2 836
Write events
4 638
Delete events
2 249
Modification events
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SLskC.7z | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
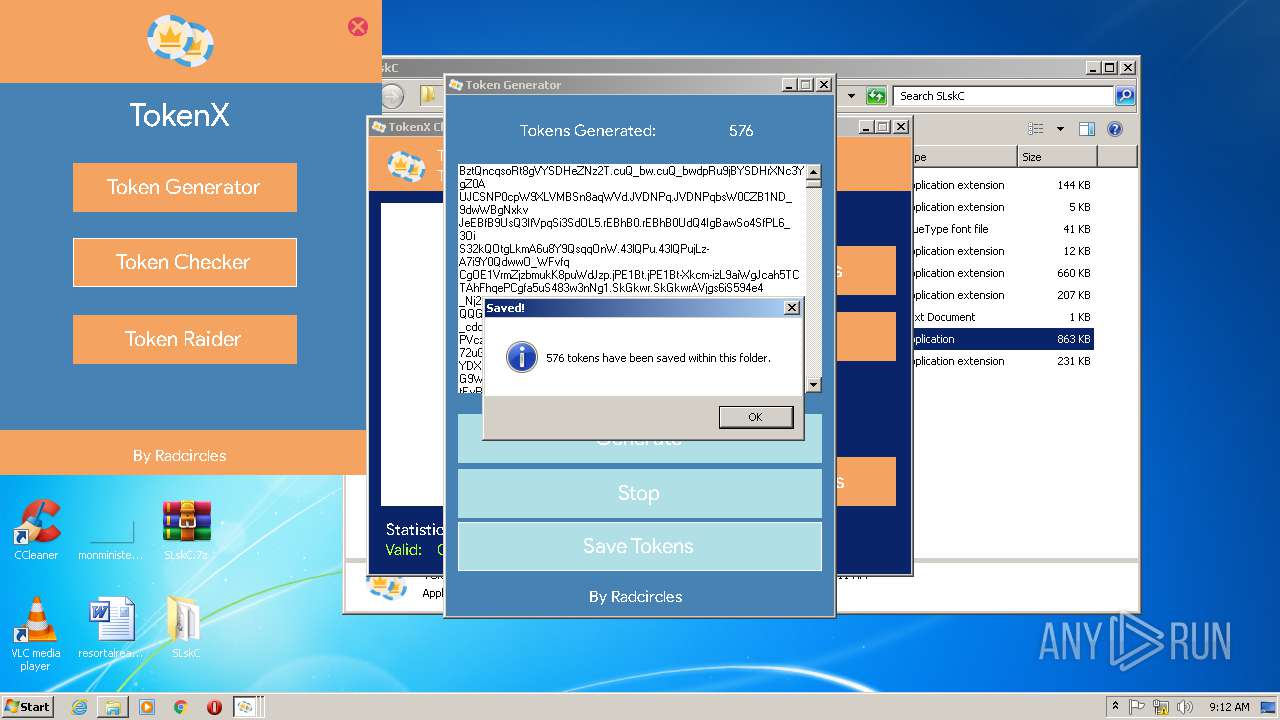
Executable files
7
Suspicious files
7
Text files
22
Unknown types
3
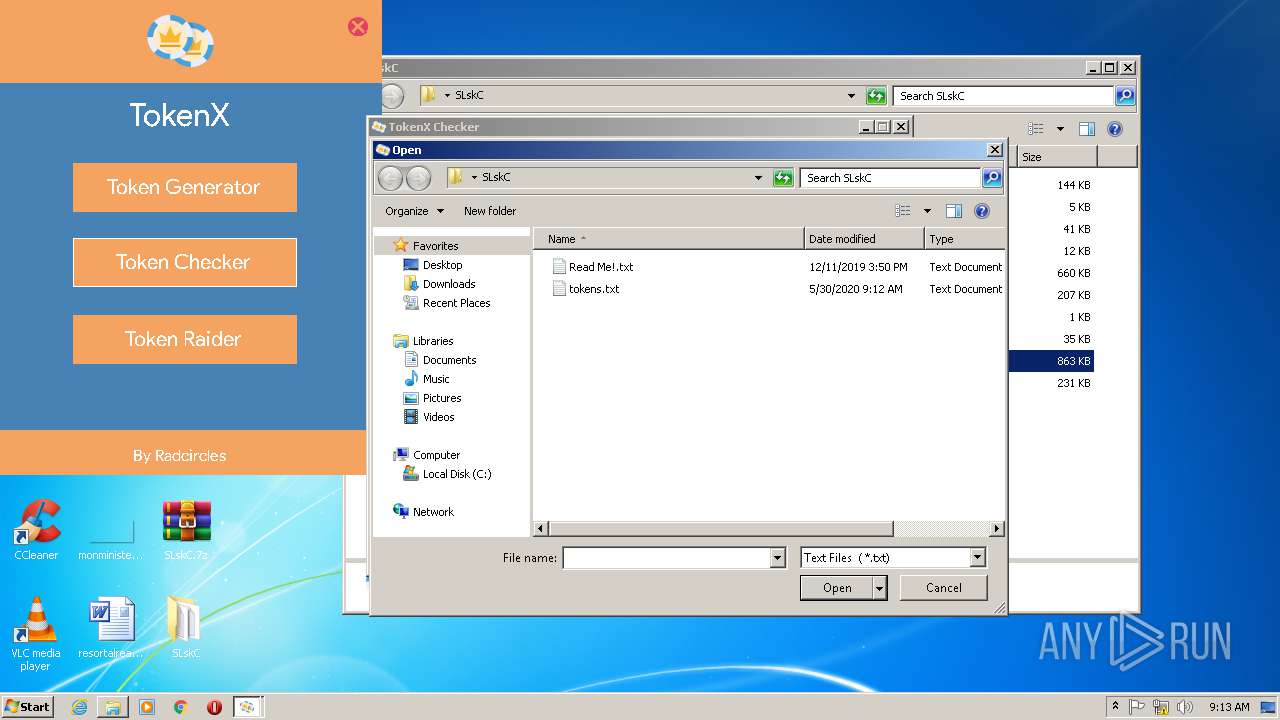
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAC95.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabAC94.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAC96.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarAC97.tmp | — | |
MD5:— | SHA256:— | |||
| 3716 | WinRAR.exe | C:\Users\admin\Desktop\SLskC\JMaterialTextbox.dll | executable | |
MD5:— | SHA256:— | |||
| 3716 | WinRAR.exe | C:\Users\admin\Desktop\SLskC\Cracked.to Authentication.dll | executable | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFD677F035627327E.TMP | — | |
MD5:— | SHA256:— | |||
| 3716 | WinRAR.exe | C:\Users\admin\Desktop\SLskC\TokenX.exe | executable | |
MD5:— | SHA256:— | |||
| 1004 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5BB5D014844C582D.TMP | — | |
MD5:— | SHA256:— | |||
| 3676 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\invalidcert[1] | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
10
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1044 | svchost.exe | GET | 404 | 95.101.72.17:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | xml | 345 b | whitelisted |
1004 | iexplore.exe | GET | 404 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | xml | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.24.111.173:443 | pastr.io | Cloudflare Inc | US | shared |
3676 | iexplore.exe | 104.24.111.173:443 | pastr.io | Cloudflare Inc | US | shared |
1004 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1004 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3428 | iexplore.exe | 104.24.111.173:443 | pastr.io | Cloudflare Inc | US | shared |
1044 | svchost.exe | 95.101.72.17:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
340 | TokenX.exe | 162.159.134.233:443 | discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastr.io |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
discordapp.com |
| whitelisted |