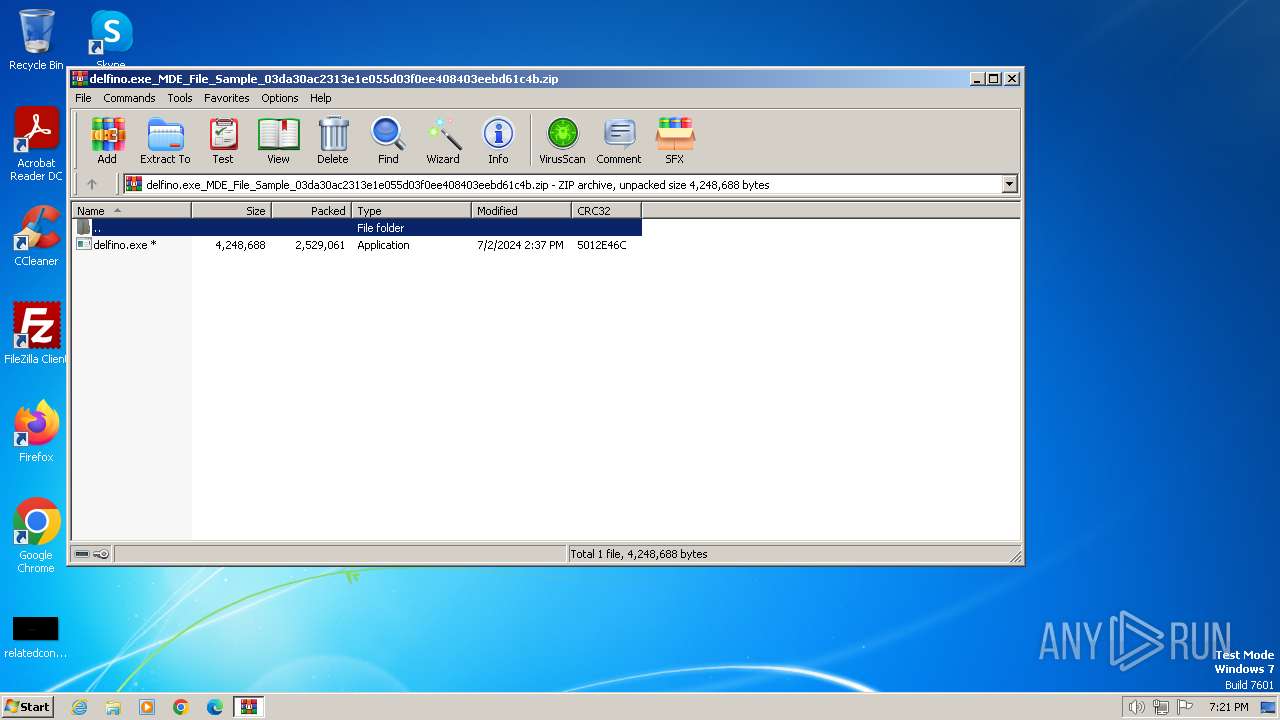
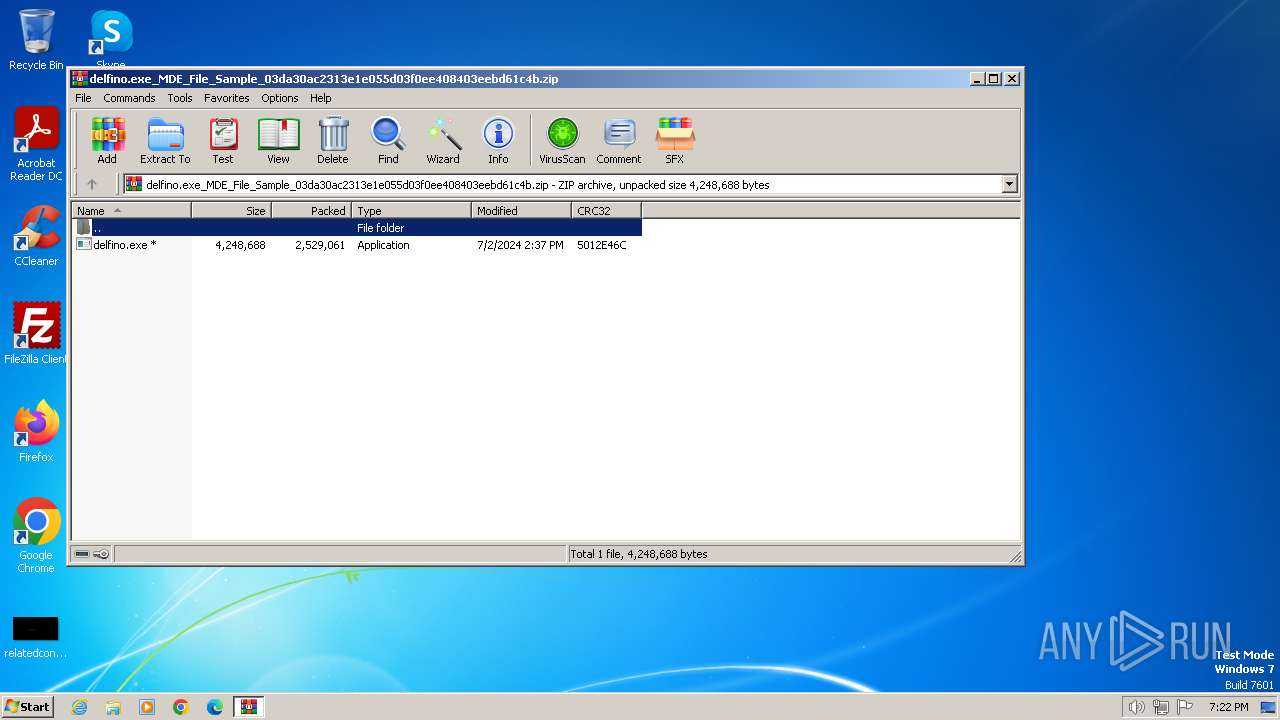
| File name: | delfino.exe_MDE_File_Sample_03da30ac2313e1e055d03f0ee408403eebd61c4b.zip |
| Full analysis: | https://app.any.run/tasks/e97e68a7-15f4-4c9f-8e90-0ee5df8006b6 |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2024, 18:21:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 9E7395D3E18A570C885C0D309D3DDD83 |
| SHA1: | EBFA7B71AE31D5E019C25F04FAFA32A1B73705E9 |
| SHA256: | CB085F4FBC984306BCD689263B3EB149BD45465460496BC07E111AADBBE35CC7 |
| SSDEEP: | 98304:tBKwC0bMQYZoTbz6fi9ivhYMPMh8rbLxdPw9Kea/YQhjw8QWY70DEOKy9e+5Y3P2:DTez |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3344)
SUSPICIOUS
Reads the BIOS version
- delfino.exe (PID: 2900)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3344)
Checks supported languages
- delfino.exe (PID: 2900)
Manual execution by a user
- delfino.exe (PID: 2900)
- explorer.exe (PID: 3568)
Create files in a temporary directory
- delfino.exe (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:07:02 13:37:26 |
| ZipCRC: | 0x5012e46c |
| ZipCompressedSize: | 2529061 |
| ZipUncompressedSize: | 4248688 |
| ZipFileName: | delfino.exe |
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
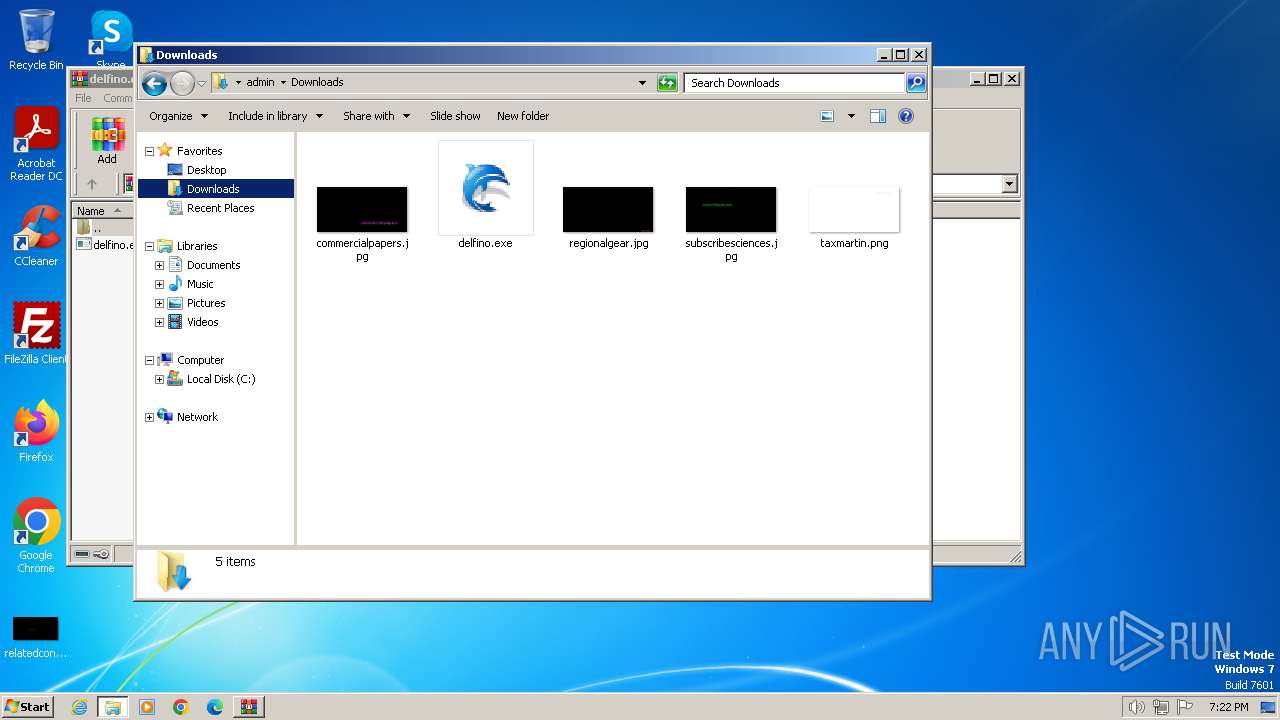
| 2900 | "C:\Users\admin\Downloads\delfino.exe" | C:\Users\admin\Downloads\delfino.exe | — | explorer.exe | |||||||||||
User: admin Company: Wizvera Integrity Level: MEDIUM Description: WIZVERA Delfino Handler 3.7.0.0 Exit code: 4294967295 Version: 3.7.0.0 Modules
| |||||||||||||||
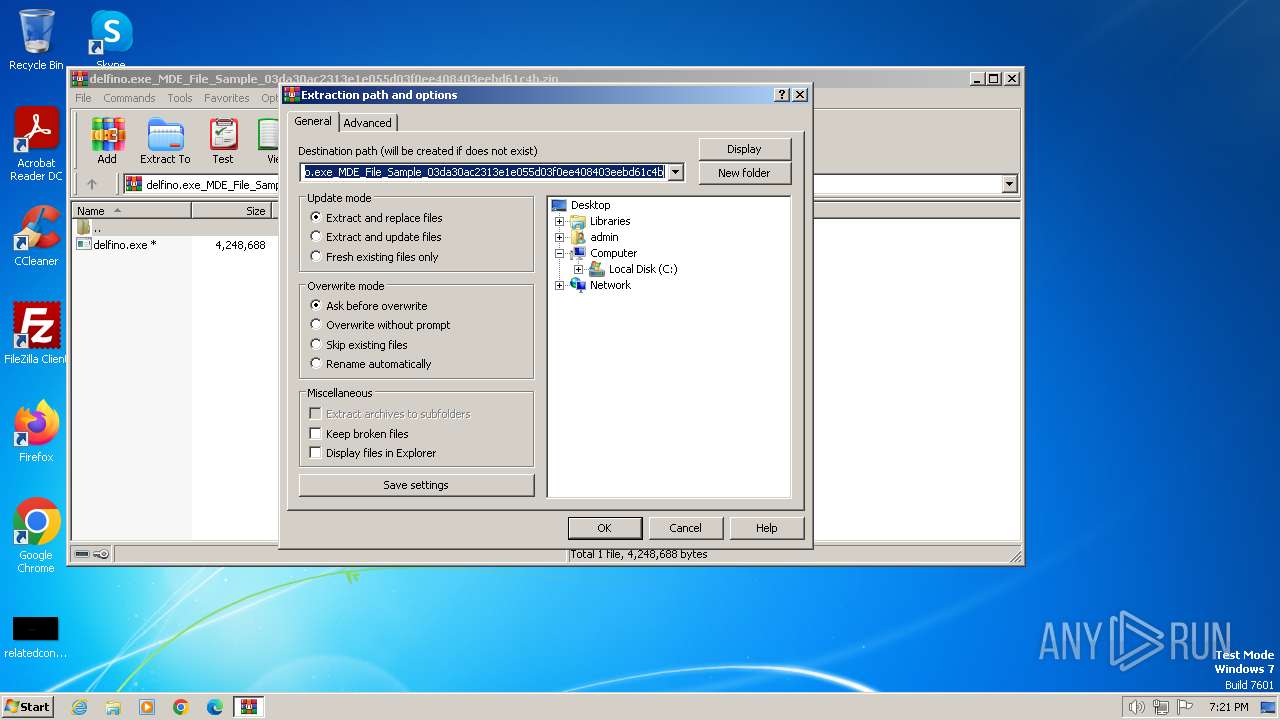
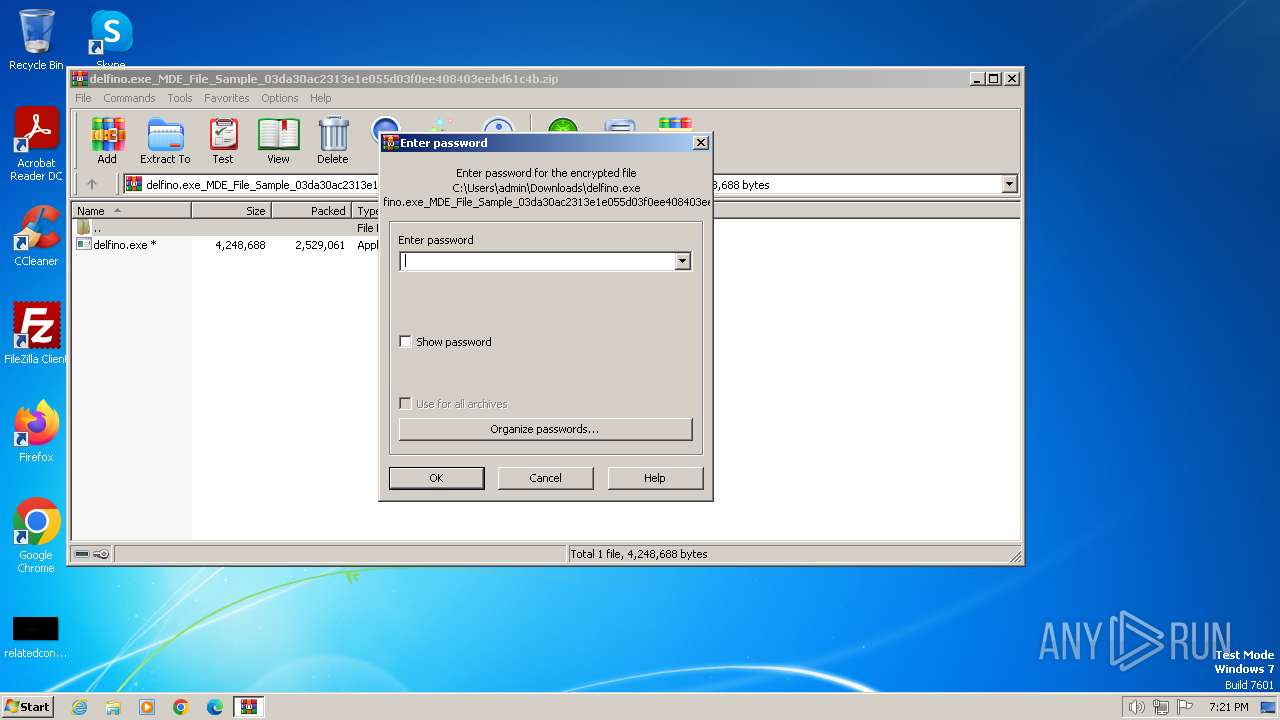
| 3344 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\delfino.exe_MDE_File_Sample_03da30ac2313e1e055d03f0ee408403eebd61c4b.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3568 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 753
Read events
3 733
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\delfino.exe_MDE_File_Sample_03da30ac2313e1e055d03f0ee408403eebd61c4b.zip | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3344) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | WinRAR.exe | C:\Users\admin\Downloads\delfino.exe | executable | |
MD5:21CF0E23172FAC8BCAA1F2AA8A47A6C5 | SHA256:F0F548BB8C4D480040B7AD8D4EB1F000F8D29BDBA0E6D5C49089C6FE89A5905C | |||
| 2900 | delfino.exe | C:\Users\admin\AppData\Local\Temp\delfino_exit_cause.log | text | |
MD5:DD044F7BE388571FE156A5265D0B4319 | SHA256:D48FE9211579CDB939713F824EFDA73FF4DBD2602D9855E38C78C7272FF3E587 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.50.131.205:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.21.20.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 23.50.131.206:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 23.50.131.205:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 2.21.20.133:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 23.50.131.206:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |