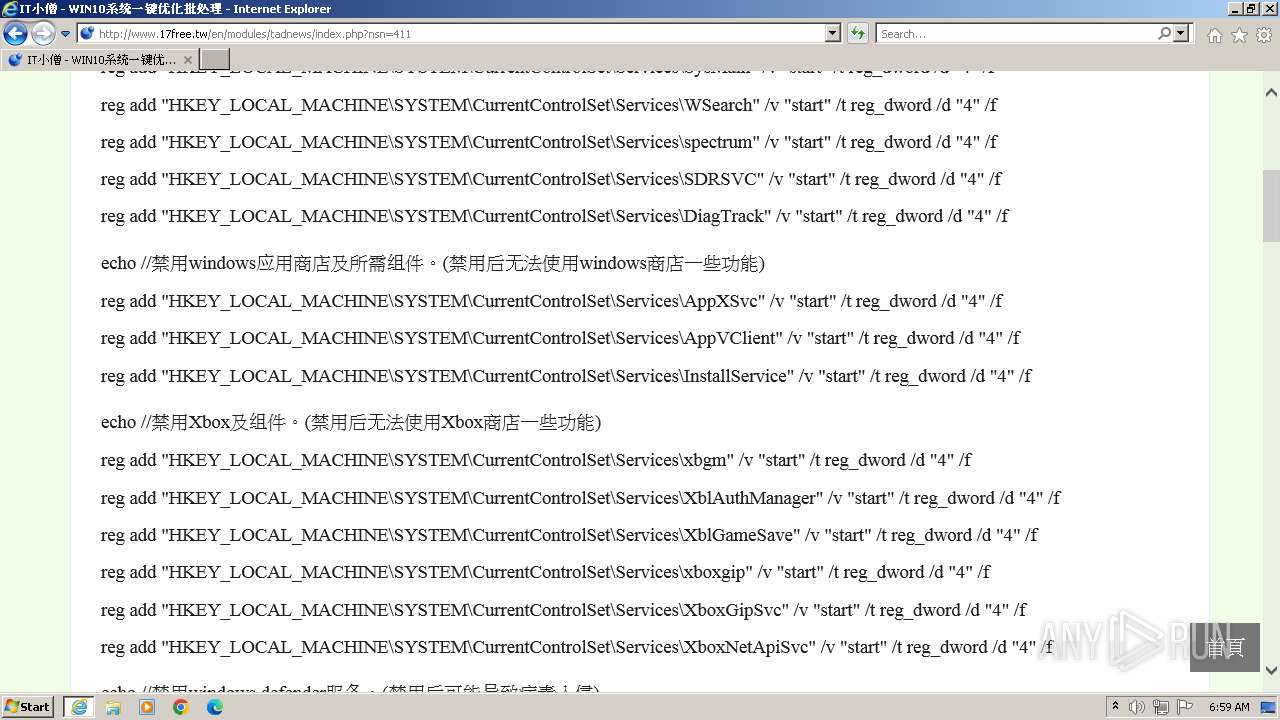
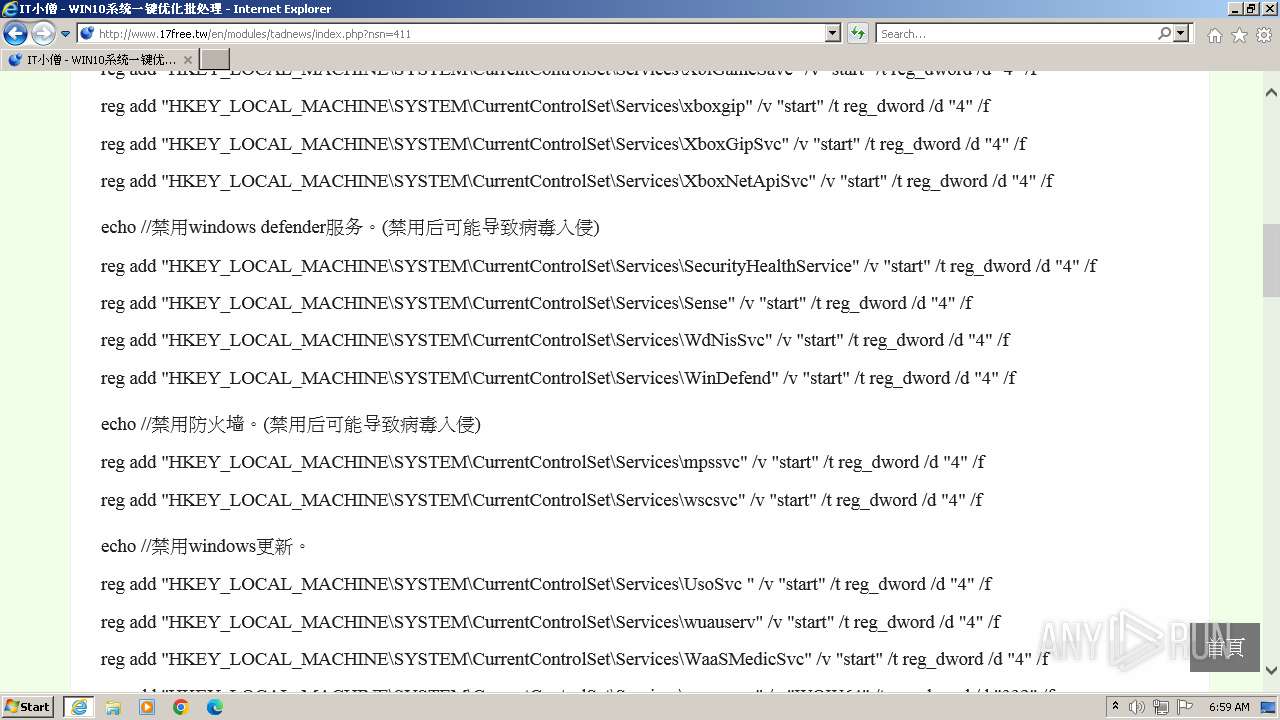
| URL: | www.17free.tw |
| Full analysis: | https://app.any.run/tasks/0f309499-b914-47aa-9ba9-58d308307464 |
| Verdict: | Malicious activity |
| Analysis date: | November 06, 2023, 06:58:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 23B8EBA69DCFC3954776629066AA0EEB |
| SHA1: | 6FAB72BE6D8B86A74ED037A1A491B3350A609AFC |
| SHA256: | CAFAFE7286EE78CD9D80639E873F2FF6C8453D712392F29FEFE69527AF3B9E38 |
| SSDEEP: | 3:EbAu0n:p |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3208)
Manual execution by a user
- wmpnscfg.exe (PID: 3944)
Reads the computer name
- wmpnscfg.exe (PID: 3944)
Checks supported languages
- wmpnscfg.exe (PID: 3944)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3944)
The process uses the downloaded file
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3208 | "C:\Program Files\Internet Explorer\iexplore.exe" "www.17free.tw" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3432 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3208 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3944 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\System32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
24 995
Read events
24 856
Write events
136
Delete events
3
Modification events
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
47
Text files
129
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jquery.smartmenus.bootstrap[1].css | text | |
MD5:14ACD1EE372CA745B0B5D051447C5627 | SHA256:6D22AF88C0F4AEDDF80077218BD5926DB794237CD5CAE221A1F72810BE08DB45 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\shThemeMonokai[1].css | text | |
MD5:5C21E1212DC3A770F1E4D0061547F93B | SHA256:27875AF0F582BB21EAF41CECEB78A74553DB6412CAEB4935C5E1F99A19362BD8 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\xoops[1].css | text | |
MD5:EE0CDC0F25391796CF22432114F38C25 | SHA256:7FA16DCB1441DBC096B79A39E601297E72972328B85AF7C430BEA69B590CB5FC | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\iconize[1].css | text | |
MD5:8544C5991503904EB88B6AE4D1020B9C | SHA256:25E20CC573EAB5EEDC086DC86EAF2FFFD9DE3D4275A00C91F913175D57439B32 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\style[1].css | text | |
MD5:21CDB274BD5129904F17C27C92DE952E | SHA256:90FADE4C740AC3EC7DBD36F68E849ABFE79FD5B6148B205D99CFDF5508A303B2 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:17CD2423C8435E54C9197F57AEB8C04C | SHA256:A9BC5D5A91D4B863A72CDA4A04427FBE0D0526510F81E65D1B26B74D606F7D08 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\shCore[1].css | text | |
MD5:6AA85A0E35A038829E375B36BCA24591 | SHA256:F69339C60718054E326D666EAA7E40862221B021FDA1C09B6284103F6729EF67 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\jquery.fancybox[1].css | text | |
MD5:351C51397AB754DD2670642AECB24237 | SHA256:522C5BCC74F4497FA17A781FF418CC0389600CFA77BAE0766D4E2A1C2EC142D9 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\jquery.fancybox-thumbs[1].css | text | |
MD5:84A2C1E5C79AEAF87C0BA0732BC861B3 | SHA256:8BC312D9AB223A7858654220BE946C125A182A9519B93F4D79ED0E65D9968FC9 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\jquery.fancybox-buttons[1].css | text | |
MD5:741E2DA2561D3B82FB87BE3B6A5520EC | SHA256:87AC81D241C39F34742B8800C81C8669668CA9C9EFAFF743739E0CB29AC0F8AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
112
TCP/UDP connections
94
DNS requests
27
Threats
77
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
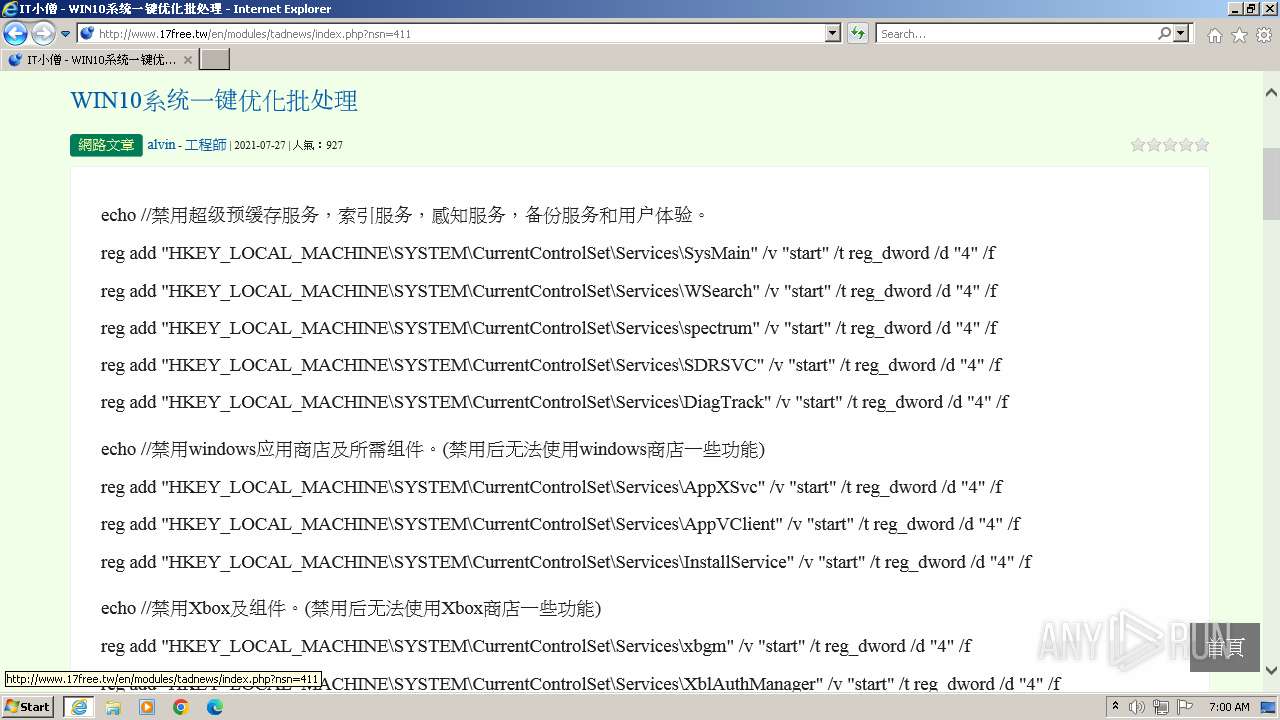
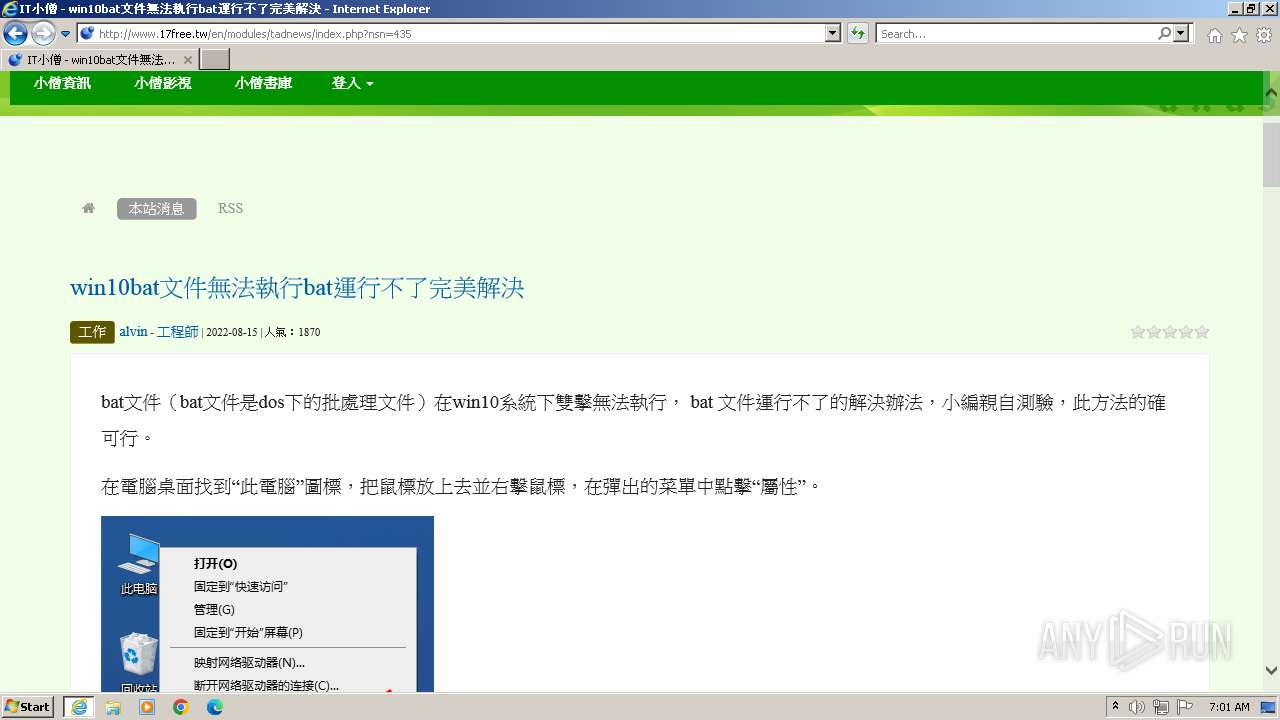
3432 | iexplore.exe | GET | 302 | 108.181.11.196:80 | http://www.17free.tw/ | unknown | — | — | unknown |
3432 | iexplore.exe | GET | 200 | 108.181.11.196:80 | http://www.17free.tw/en/modules/tadtools/syntaxhighlighter/styles/shCore.css | unknown | text | 1.32 Kb | unknown |
3432 | iexplore.exe | GET | 200 | 108.181.11.196:80 | http://www.17free.tw/en/language/tchinese_utf8/style.css | unknown | text | 41 b | unknown |
3432 | iexplore.exe | GET | 200 | 108.181.11.196:80 | http://www.17free.tw/en/modules/tadtools/css/font-awesome/css/font-awesome.css | unknown | text | 6.80 Kb | unknown |
3432 | iexplore.exe | GET | 200 | 108.181.11.196:80 | http://www.17free.tw/en/themes/mkdodos/css/xoops.css | unknown | text | 926 b | unknown |
3432 | iexplore.exe | GET | 200 | 108.181.11.196:80 | http://www.17free.tw/en/ | unknown | html | 7.94 Kb | unknown |
3432 | iexplore.exe | GET | 200 | 108.181.11.196:80 | http://www.17free.tw/en/modules/tadtools/syntaxhighlighter/styles/shThemeMonokai.css | unknown | text | 726 b | unknown |
3432 | iexplore.exe | GET | 200 | 108.181.11.196:80 | http://www.17free.tw/en/modules/tadtools/bootstrap3/css/bootstrap.css | unknown | text | 21.0 Kb | unknown |
3432 | iexplore.exe | GET | 200 | 108.181.11.196:80 | http://www.17free.tw/en/modules/tadtools/fancyBox/source/helpers/jquery.fancybox-thumbs.css?v=1.0.7 | unknown | text | 296 b | unknown |
3432 | iexplore.exe | GET | 200 | 108.181.11.196:80 | http://www.17free.tw/en/themes/mkdodos/language/tchinese_utf8/script.js | unknown | text | 36 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3432 | iexplore.exe | 108.181.11.196:80 | — | TELUS Communications | CA | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3432 | iexplore.exe | 151.101.2.114:80 | ssl.p.jwpcdn.com | FASTLY | US | unknown |
3432 | iexplore.exe | 142.250.74.206:443 | www.youtube.com | GOOGLE | US | whitelisted |
3432 | iexplore.exe | 142.250.186.150:443 | i.ytimg.com | GOOGLE | US | unknown |
3432 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3432 | iexplore.exe | 23.32.238.232:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ssl.p.jwpcdn.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.youtube.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
jwpltx.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |