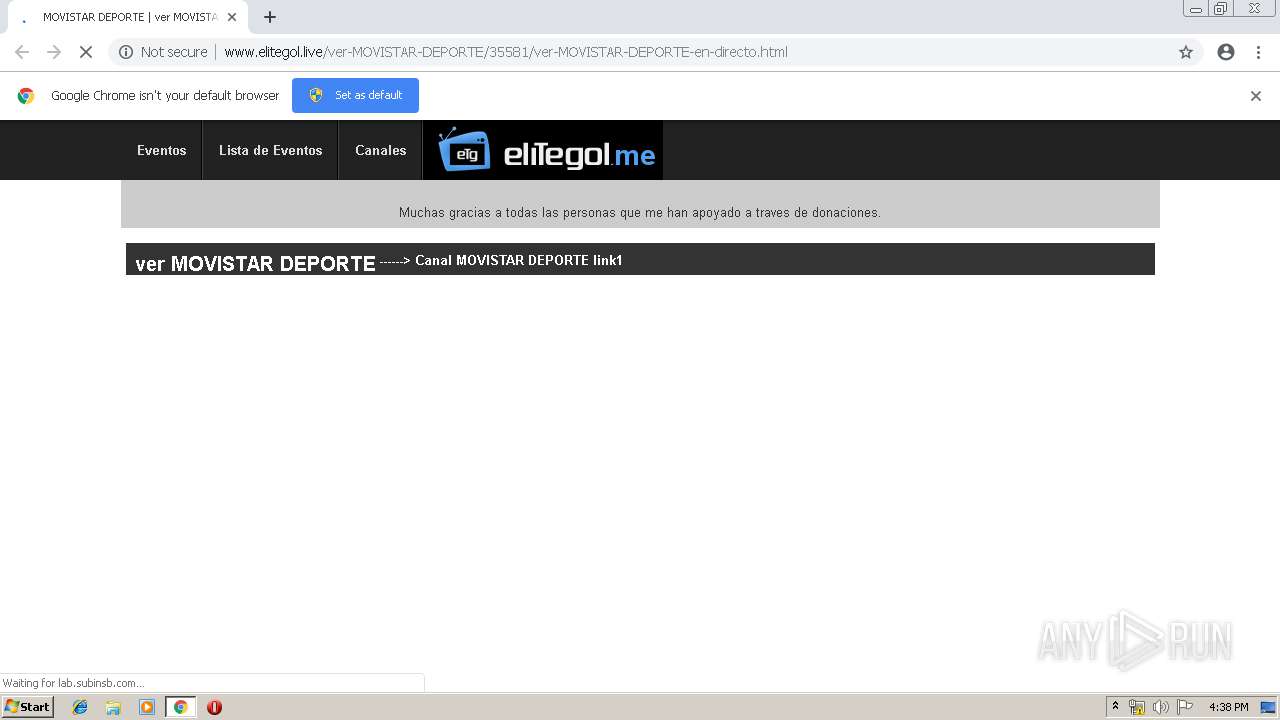
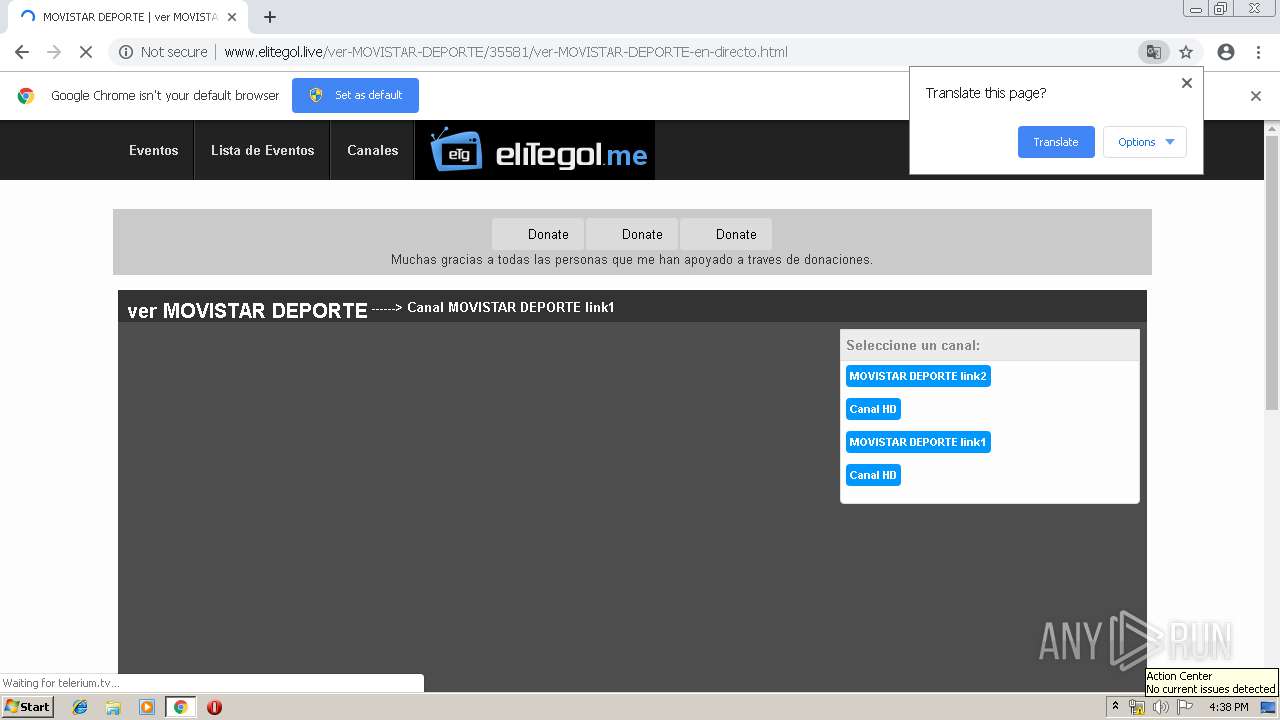
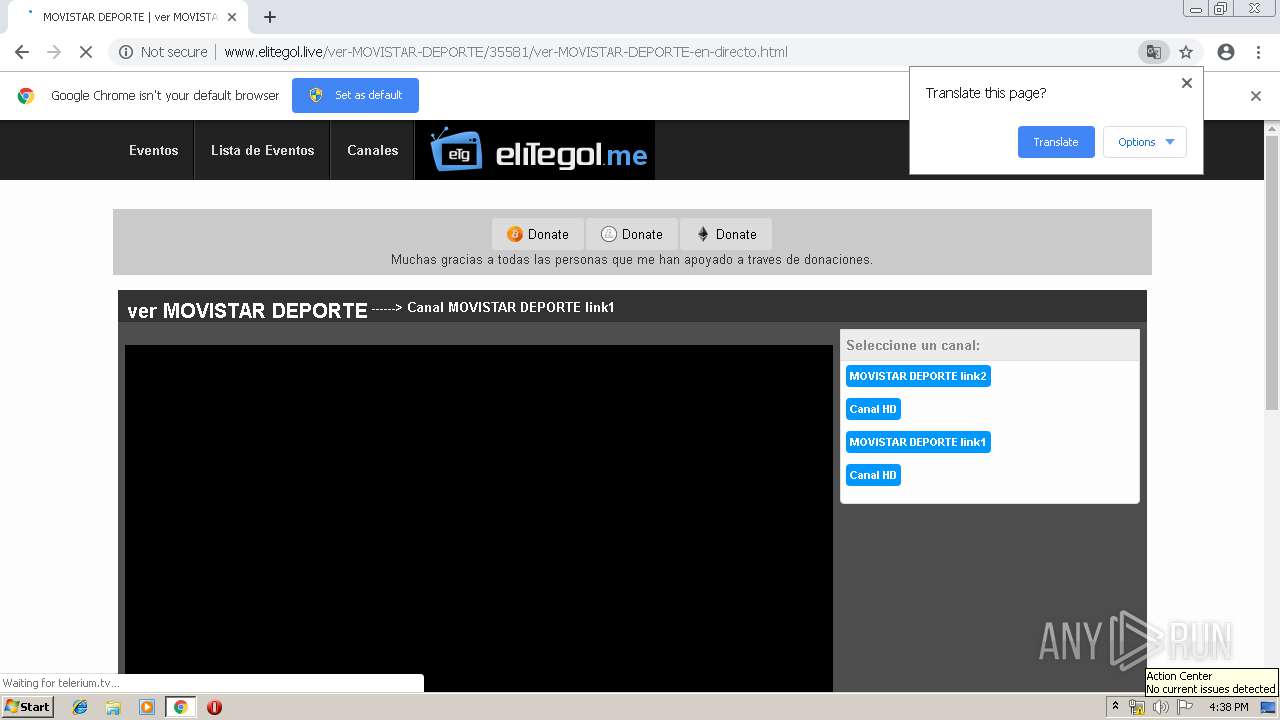
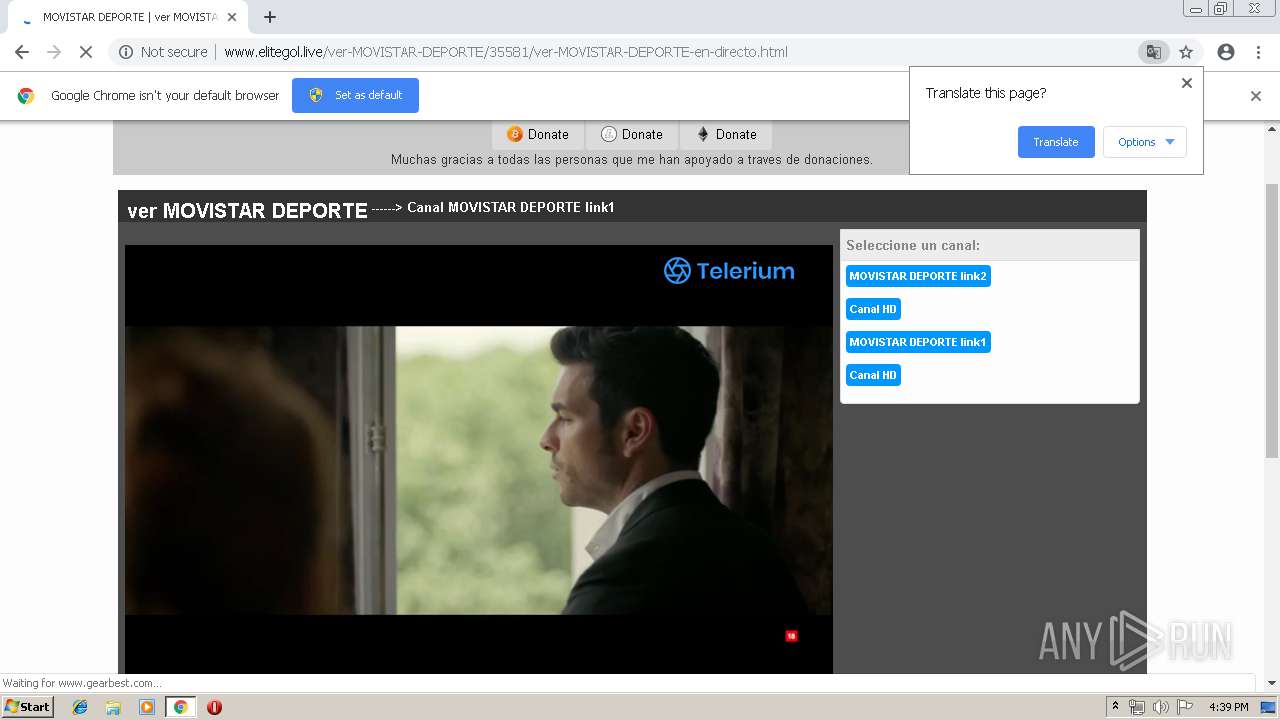
| URL: | http://www.elitegol.live/ver-MOVISTAR-DEPORTE/35581/ver-MOVISTAR-DEPORTE-en-directo.html |
| Full analysis: | https://app.any.run/tasks/3858c39b-f8b0-44fa-98cd-2b3e2ce018cc |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 15:38:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A3303FE9B89BFDA0FE81FC1F2A9613AC |
| SHA1: | 1BC7381F371D55A7D8EFBDEAF1E41EEC73469768 |
| SHA256: | CAF6462C5C577393DF431C8673B31A2C3E3C5616A6F667ABC97223BA2A46A349 |
| SSDEEP: | 3:N1KJS4jAHuyS+cg1MxuQQdTWIt+cg1MxSQWADG:Cc4jAHwg1M0QQdPg1MIQWADG |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3168)
Application launched itself
- chrome.exe (PID: 3168)
Changes settings of System certificates
- chrome.exe (PID: 3168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=ppapi --field-trial-handle=924,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --ppapi-flash-args --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=8531758611692351362 --mojo-platform-channel-handle=4652 --ignored=" --type=renderer " /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10352538850803115930 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10352538850803115930 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15884650511831891205 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15884650511831891205 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3456 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=924,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3951898115158110506 --mojo-platform-channel-handle=948 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9339315913564658235 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9339315913564658235 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4680 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --service-pipe-token=10239757442163782949 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10239757442163782949 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5055691818384694827 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5055691818384694827 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5744 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c680f18,0x6c680f28,0x6c680f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,879739905061943554,18376928256344750665,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3603524518561612874 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3603524518561612874 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
158
Read events
105
Write events
50
Delete events
3
Modification events
| (PID) Process: | (3168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3168-13202840316117625 |
Value: 259 | |||
| (PID) Process: | (3168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3168-13202840316117625 |
Value: 259 | |||
Executable files
0
Suspicious files
87
Text files
36
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\91d1021d-9ba5-4544-aa91-71bd2682b8fd.tmp | — | |
MD5:— | SHA256:— | |||
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
122
DNS requests
91
Threats
45
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3168 | chrome.exe | GET | 307 | 67.202.94.93:80 | http://whos.amung.us/cwidget/vipgoal1/000000ffffff.png | US | — | — | whitelisted |
3168 | chrome.exe | GET | 204 | 52.200.52.74:80 | http://relandssymphoking.info/RUs5NGVqdFpHWBEcAHkELhkBYwx0KlpdDScuTkxdCSwMEVcDDwpmXGM/UFBYcn8AAFJybUldAXh6ARIWMSpNQRZ4eh9dCyMkBBITeHoXBEt1ZQoSETUqXglUYztNQAl4egwBXXZ9DwNXc38PAQ | US | — | — | whitelisted |
3168 | chrome.exe | GET | 200 | 104.28.24.176:80 | http://www.elitegol.live/elitegol/style/mensaje.css | US | text | 215 b | suspicious |
3168 | chrome.exe | GET | 200 | 104.28.24.176:80 | http://www.elitegol.live/elitegol/img/logo.png | US | image | 5.14 Kb | suspicious |
3168 | chrome.exe | GET | 200 | 104.28.24.176:80 | http://www.elitegol.live/ver-MOVISTAR-DEPORTE/35581/ver-MOVISTAR-DEPORTE-en-directo.html | US | html | 3.46 Kb | suspicious |
3168 | chrome.exe | GET | 200 | 104.28.24.176:80 | http://www.elitegol.live/hidden.php | US | html | 305 b | suspicious |
3168 | chrome.exe | GET | 200 | 52.85.188.204:80 | http://d2d8qsxiai9qwj.cloudfront.net/?xsqdd=710958 | US | text | 52.9 Kb | whitelisted |
3168 | chrome.exe | GET | 200 | 198.134.112.244:80 | http://i4rsrcj6.top/8b/65/39/8b653988a0eed89c9a6ba940fb4d4064.js | US | html | 15.4 Kb | suspicious |
3168 | chrome.exe | GET | 200 | 185.225.208.133:80 | http://widgets.amung.us/draw/?w=colored&n=171&c=000000ffffff&p= | unknown | image | 1.21 Kb | whitelisted |
3168 | chrome.exe | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3168 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3168 | chrome.exe | 104.28.24.176:80 | www.elitegol.live | Cloudflare Inc | US | shared |
3168 | chrome.exe | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
3168 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3168 | chrome.exe | 198.134.112.244:80 | i4rsrcj6.top | Webair Internet Development Company Inc. | US | suspicious |
3168 | chrome.exe | 104.28.6.38:80 | lab.subinsb.com | Cloudflare Inc | US | shared |
3168 | chrome.exe | 67.202.94.93:80 | whos.amung.us | Steadfast | US | malicious |
3168 | chrome.exe | 52.85.188.204:80 | d2d8qsxiai9qwj.cloudfront.net | Amazon.com, Inc. | US | unknown |
3168 | chrome.exe | 104.27.141.239:443 | www.elitegol.me | Cloudflare Inc | US | shared |
3168 | chrome.exe | 104.24.107.215:80 | ie8eamus.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.elitegol.live |
| suspicious |
accounts.google.com |
| shared |
bit.ly |
| shared |
i4rsrcj6.top |
| suspicious |
www.elitegol.me |
| unknown |
whos.amung.us |
| whitelisted |
d2d8qsxiai9qwj.cloudfront.net |
| whitelisted |
embed.telerium.tv |
| unknown |
ads.optimizesrv.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3168 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3168 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS WindowBase64.atob Function In Edwards Packed JavaScript - Possible iFrame Injection Detected |
3168 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3168 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3168 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |