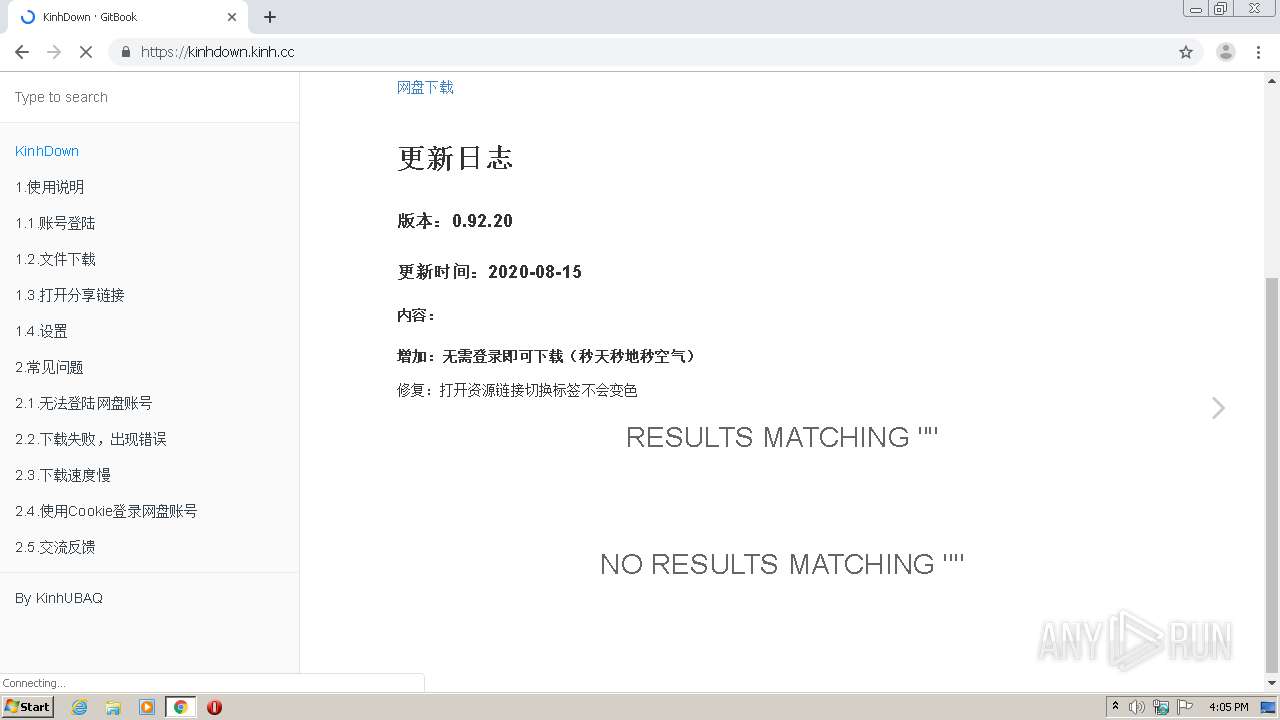
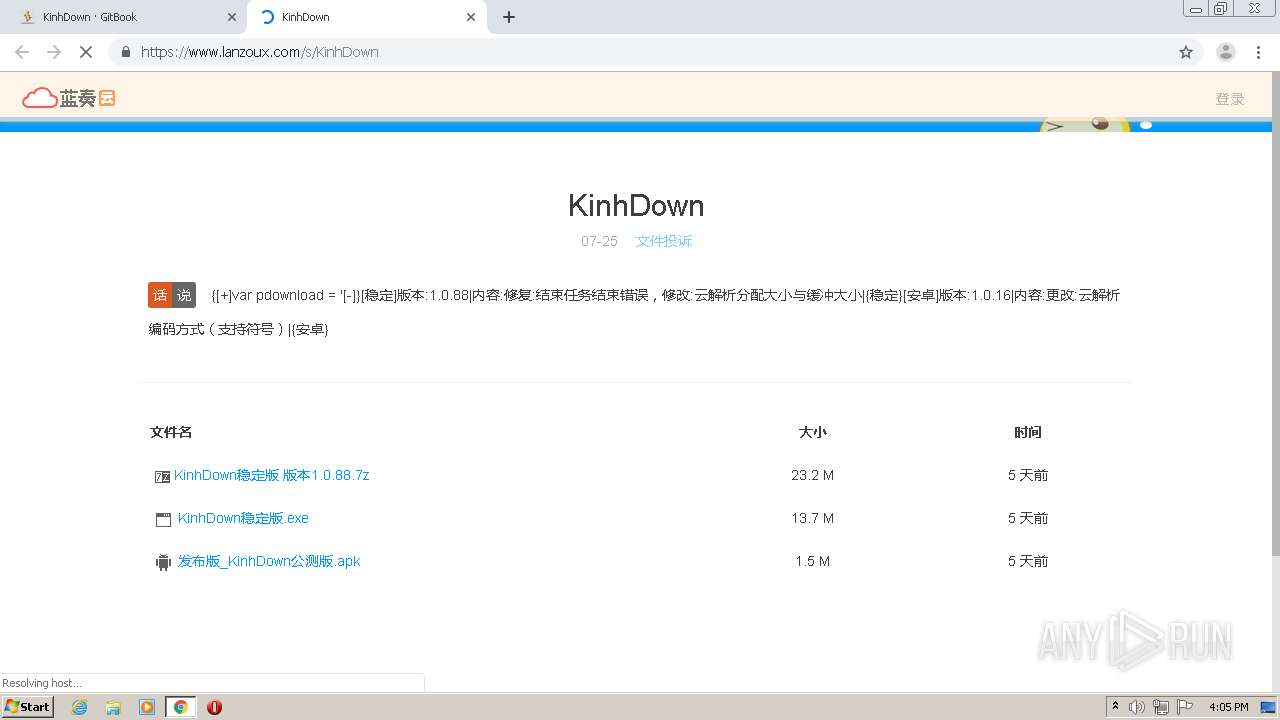
| URL: | https://kinhdown.kinh.cc/&ved=2ahUKEwiD8te4xu_rAhVB3qQKHR7fAg8QFjAAegQIAxAB&cshid=1600323796276294 |
| Full analysis: | https://app.any.run/tasks/a082c543-fe01-4dcd-8f7d-9611686044fd |
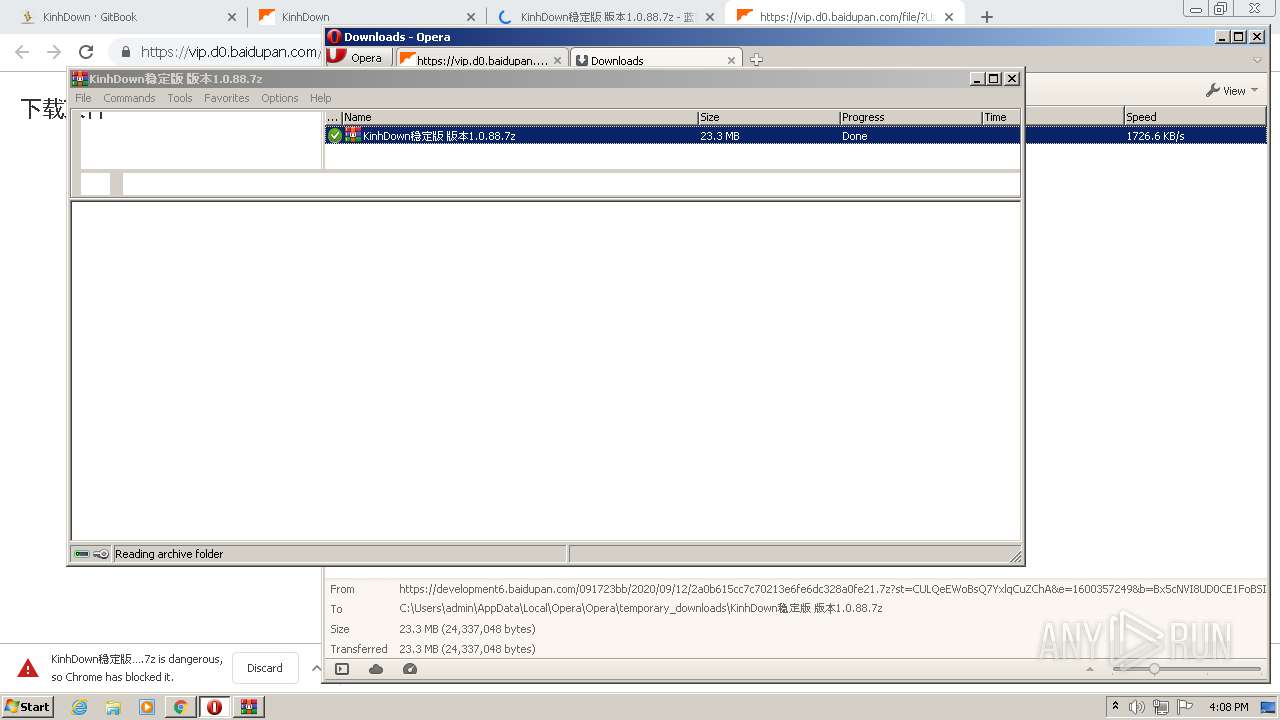
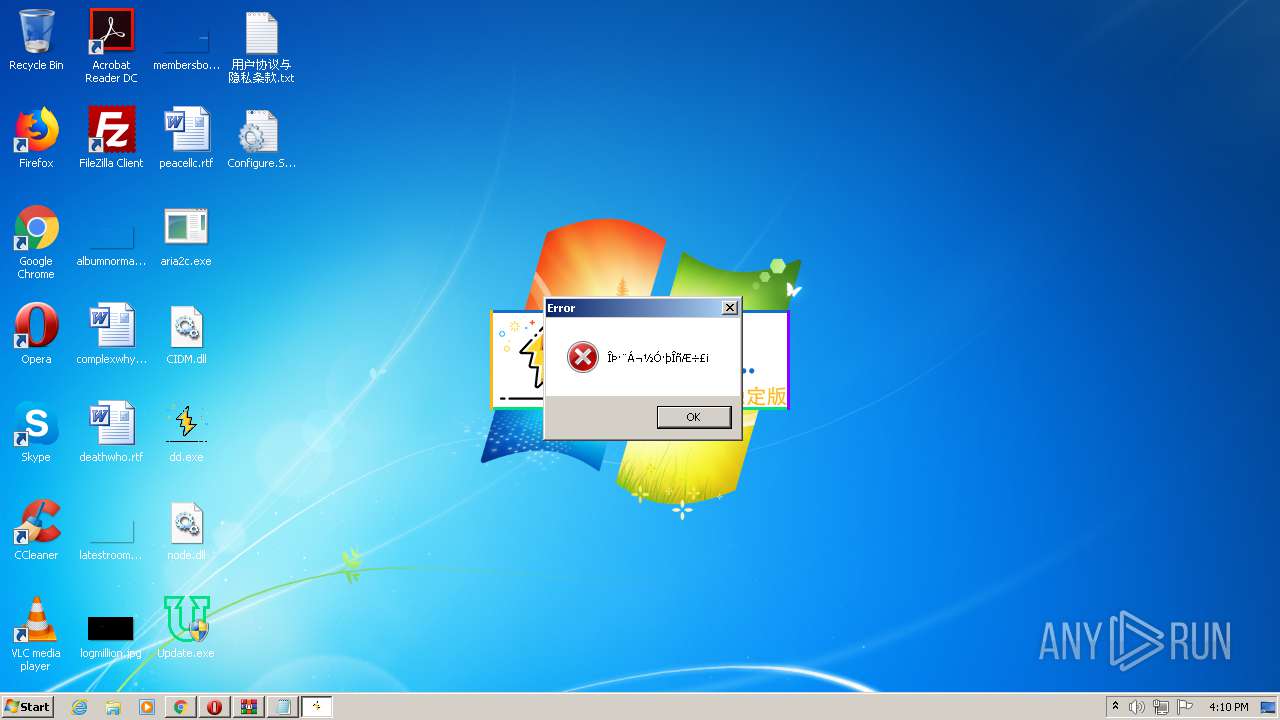
| Verdict: | Malicious activity |
| Analysis date: | September 17, 2020, 15:04:59 |
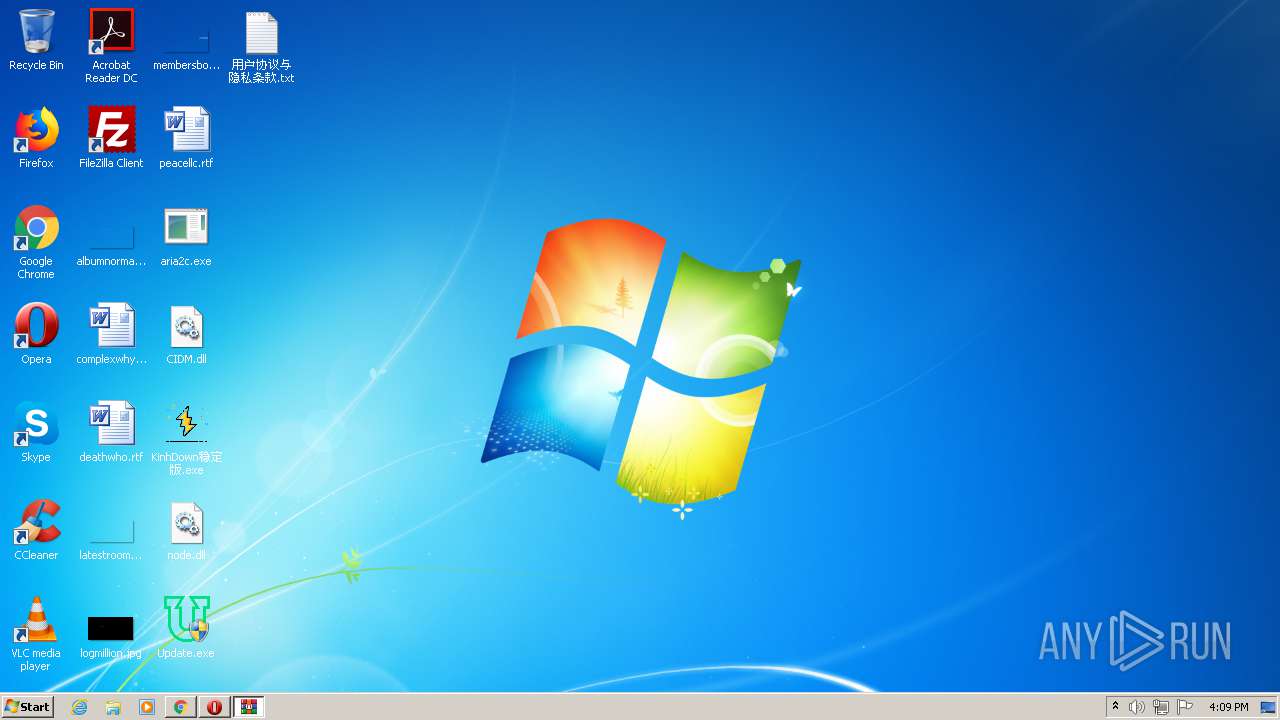
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5A1C1C12828CFF50245D9B32EE25A6B0 |
| SHA1: | 60A7D0F9B60F75FEF7D85EC34F83BC0019E3AE08 |
| SHA256: | CAE844618B127D9E982CE19E55D43A92663D64FAB356B87DCC60D686AA79A373 |
| SSDEEP: | 3:N8JiZML4GRNbHdQ60NznTXt3SDkr+G0PSw:2HnRN4TXou+bSw |
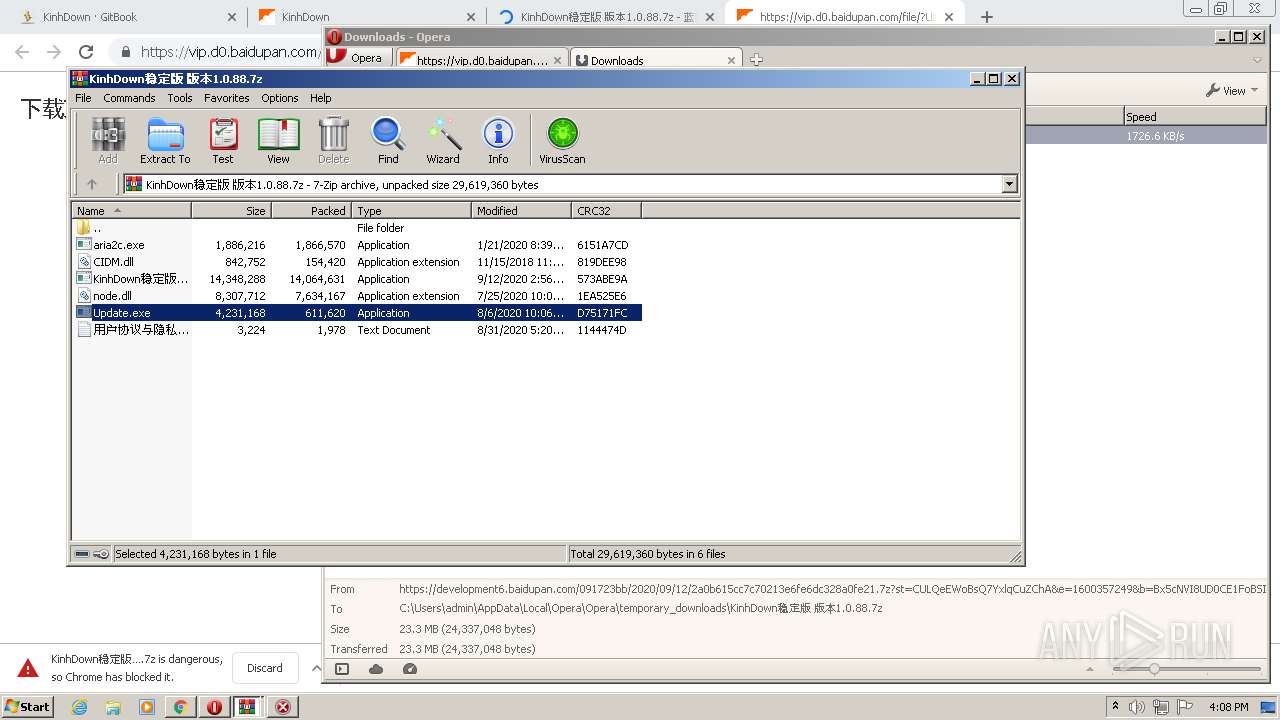
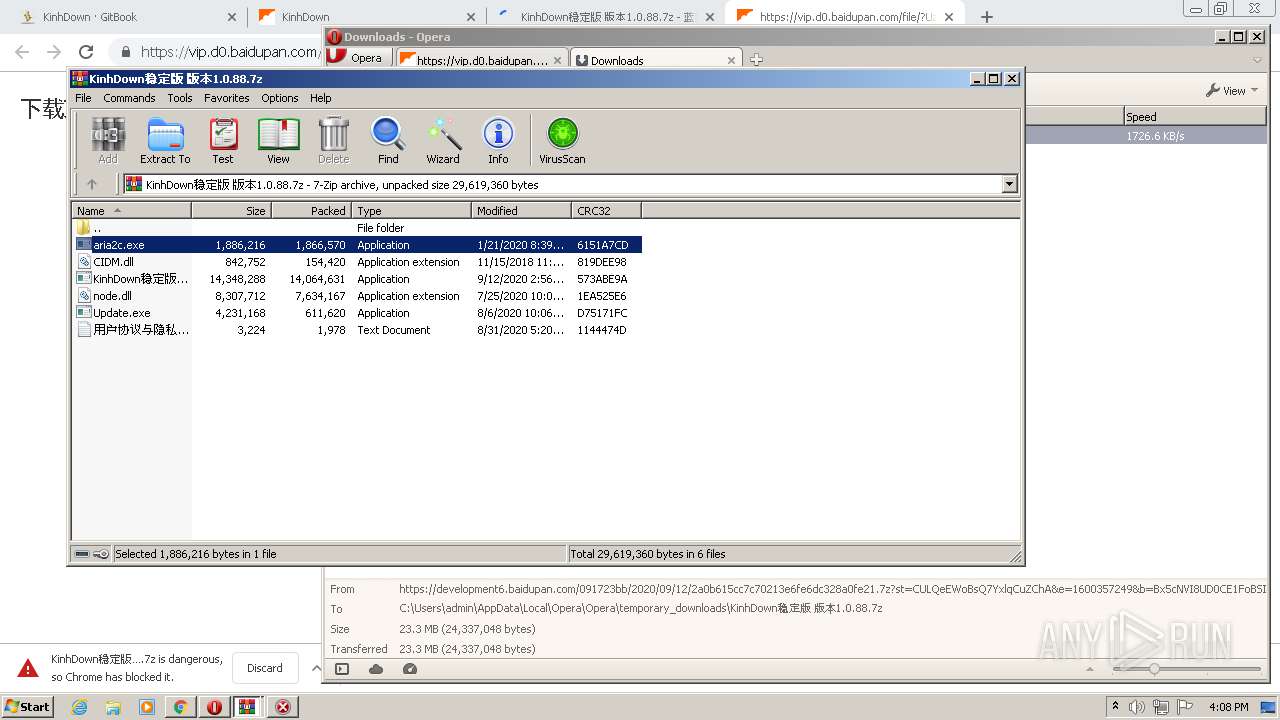
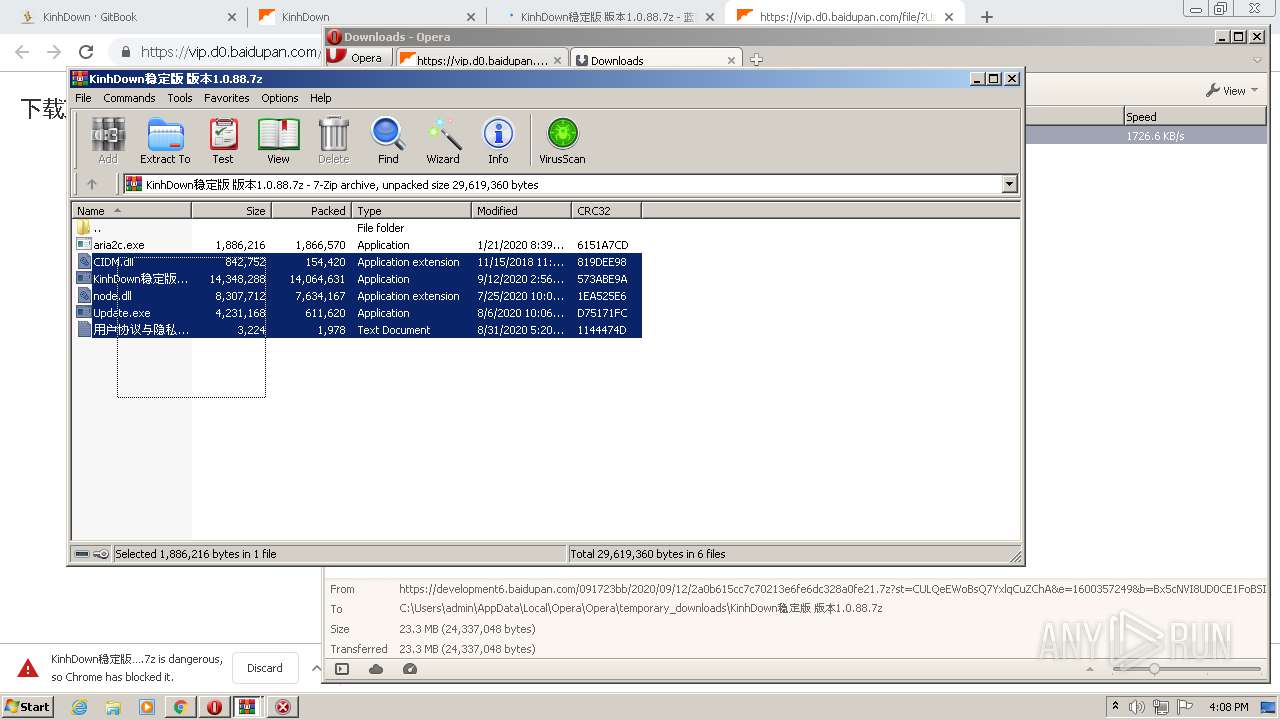
MALICIOUS
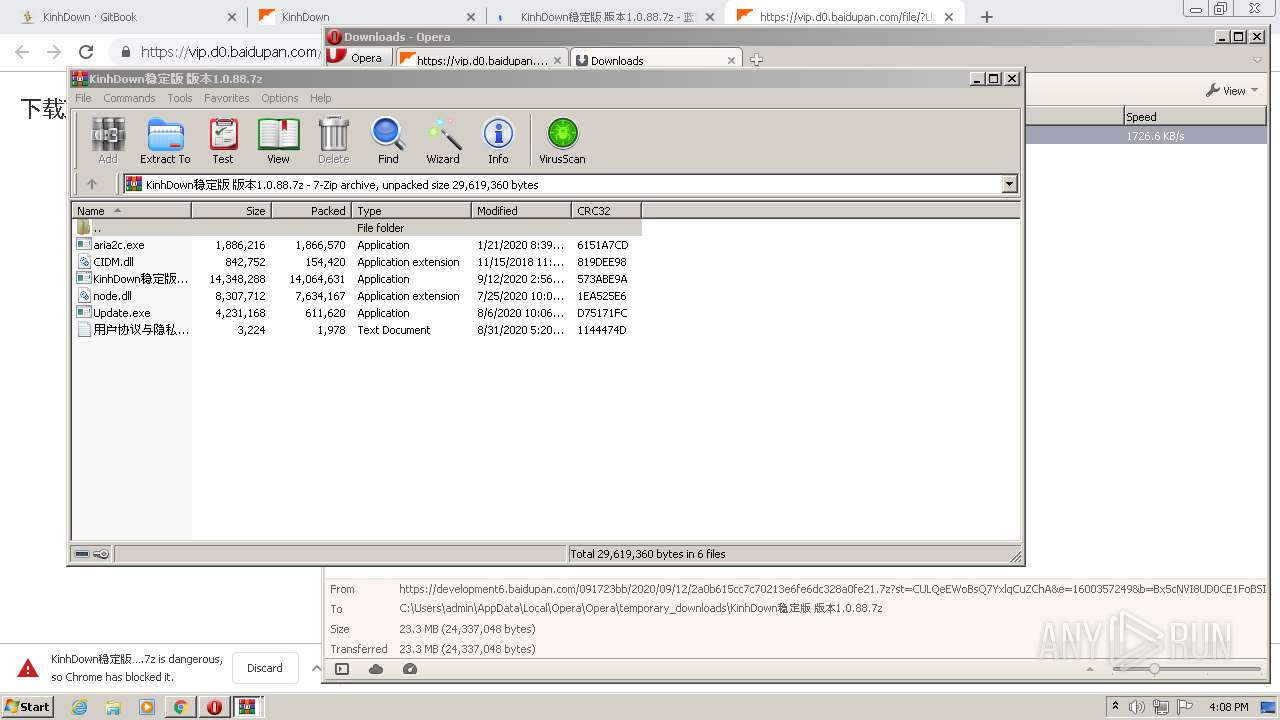
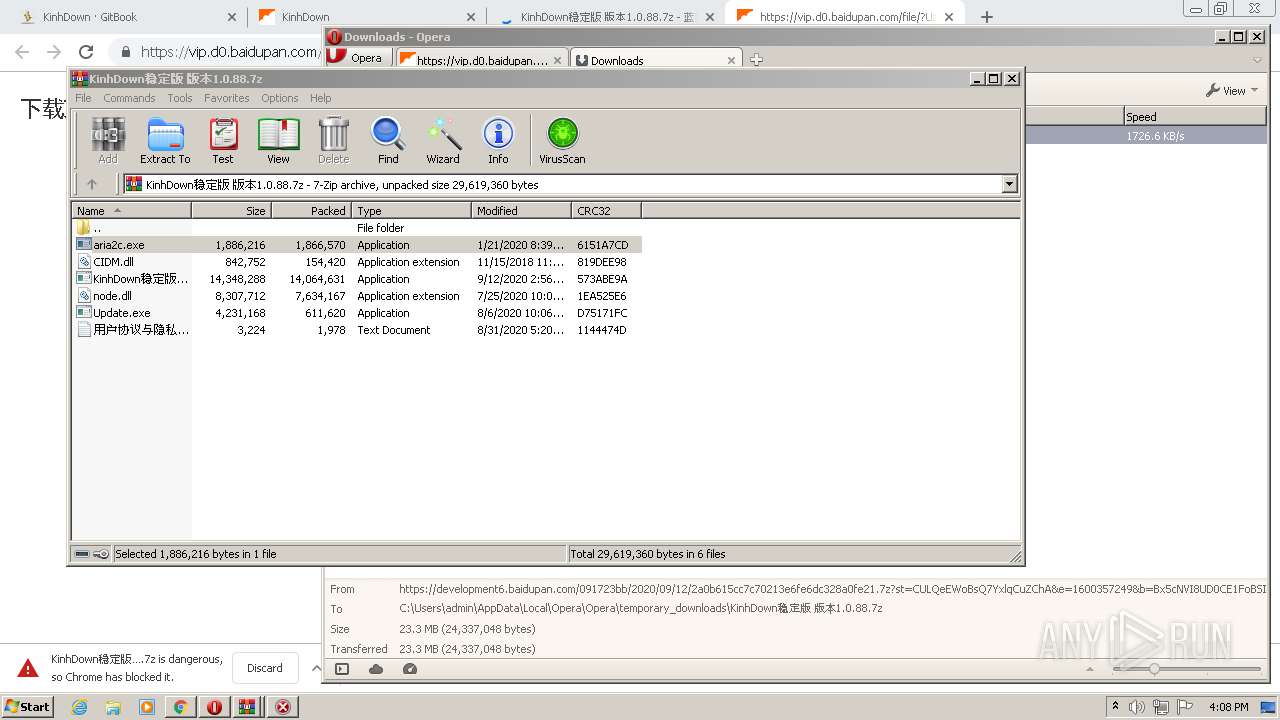
Application was dropped or rewritten from another process
- Update.exe (PID: 3128)
- Update.exe (PID: 3252)
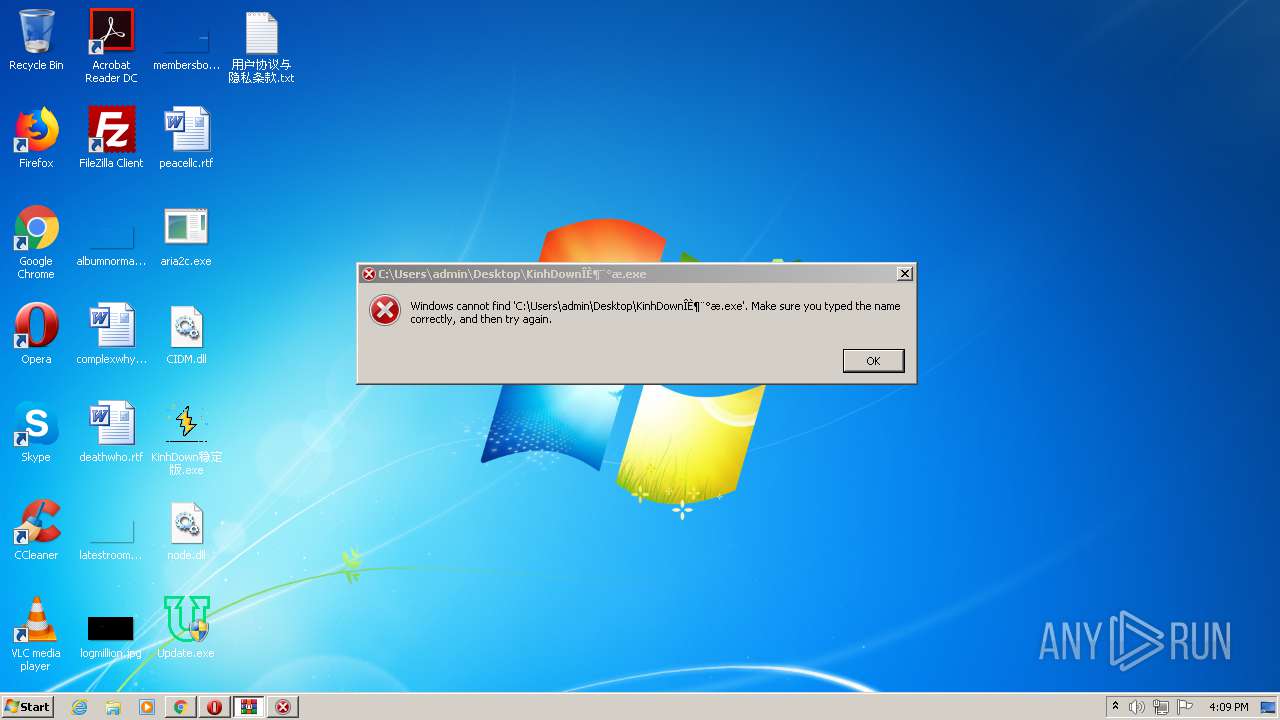
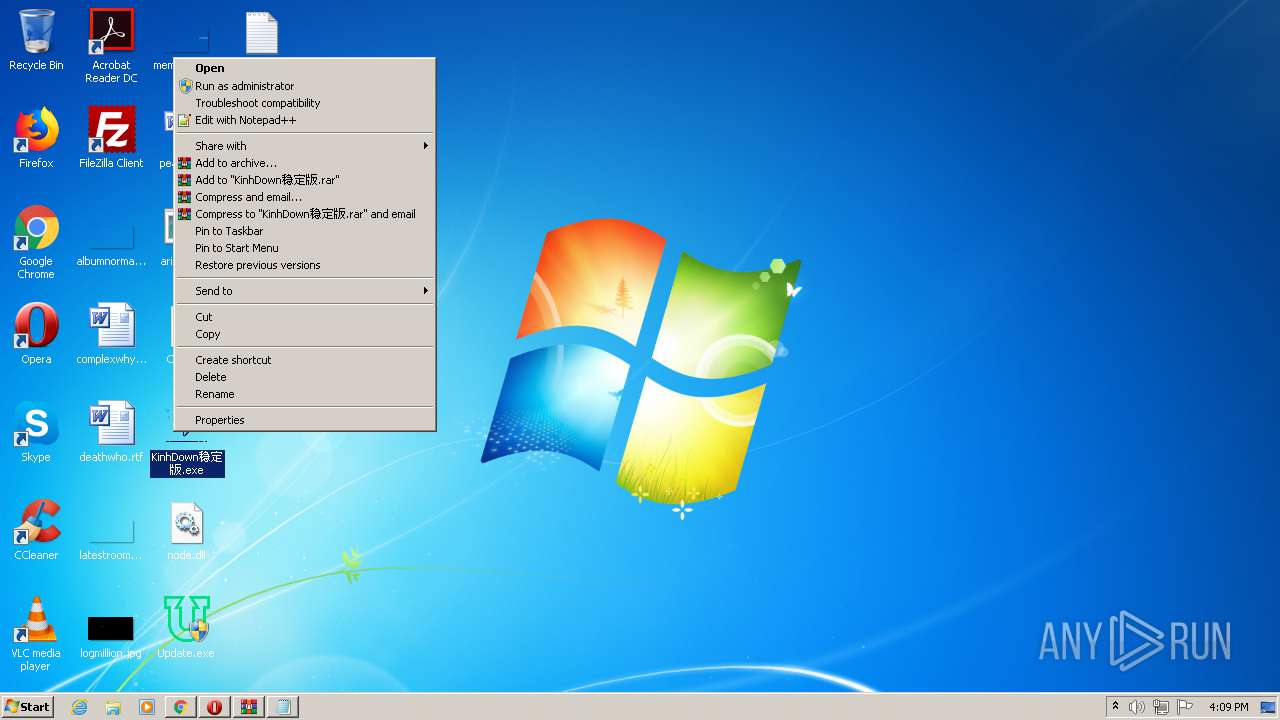
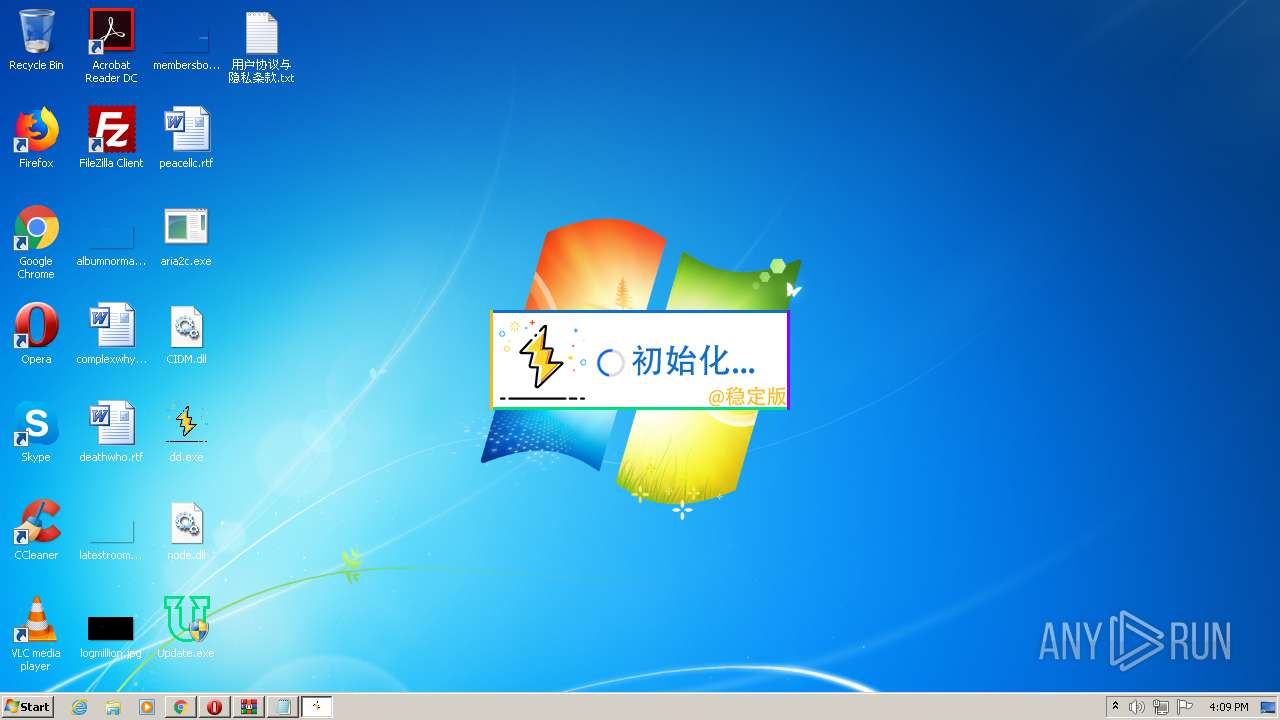
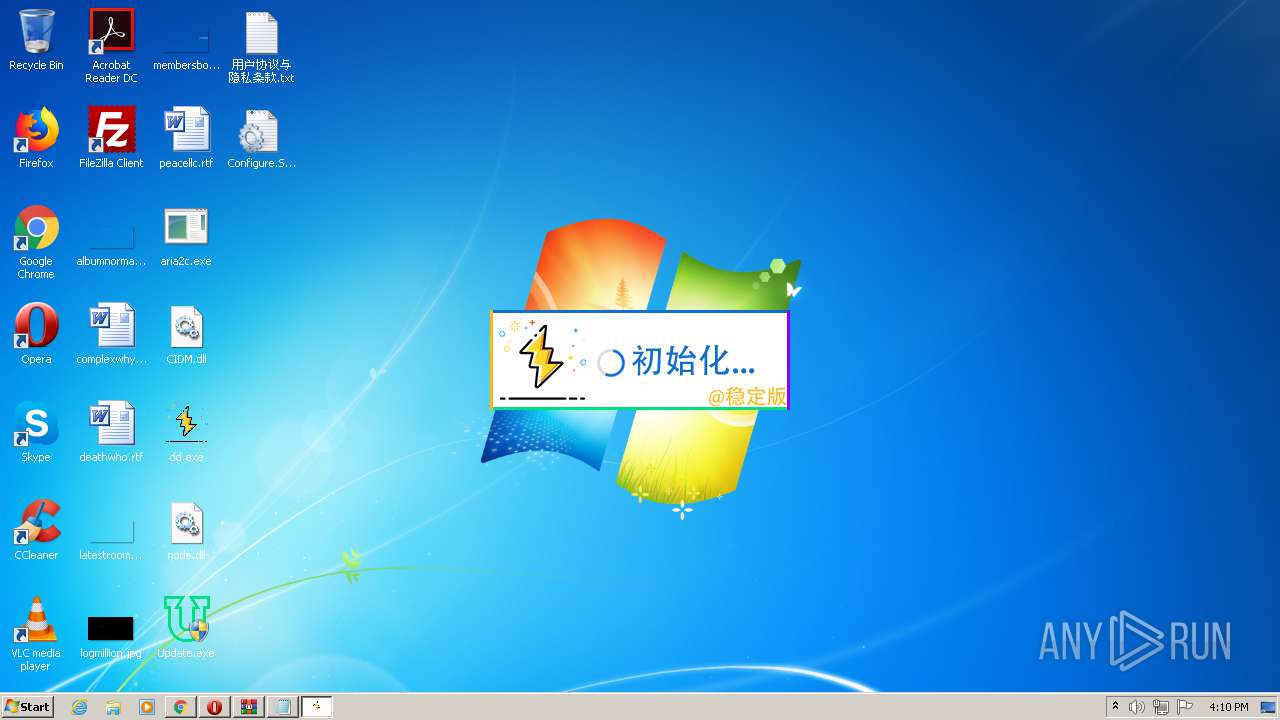
- KinhDown稳定版.exe (PID: 3204)
- aria2c.exe (PID: 2200)
- Update.exe (PID: 1356)
- aria2c.exe (PID: 756)
- KinhDown稳定版.exe (PID: 2308)
- Update.exe (PID: 2700)
- dd.exe (PID: 3404)
- dd.exe (PID: 3824)
- Update.exe (PID: 3844)
- Update.exe (PID: 2572)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3172)
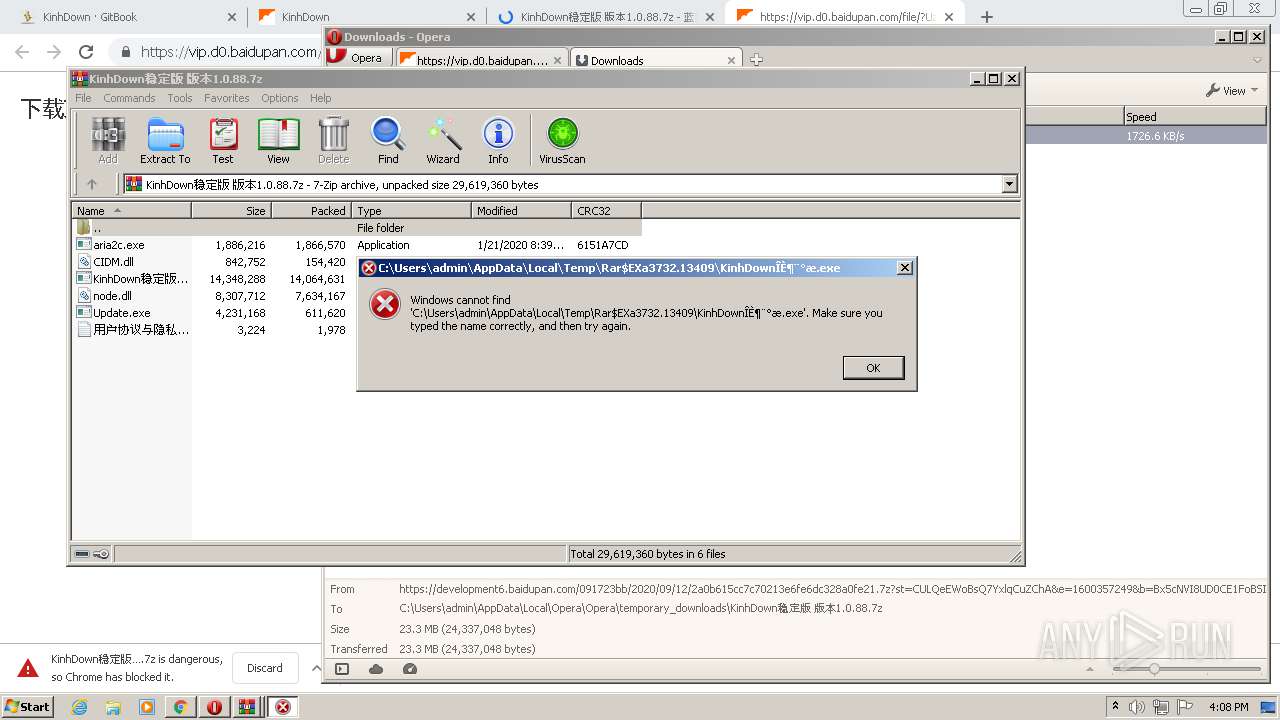
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2528)
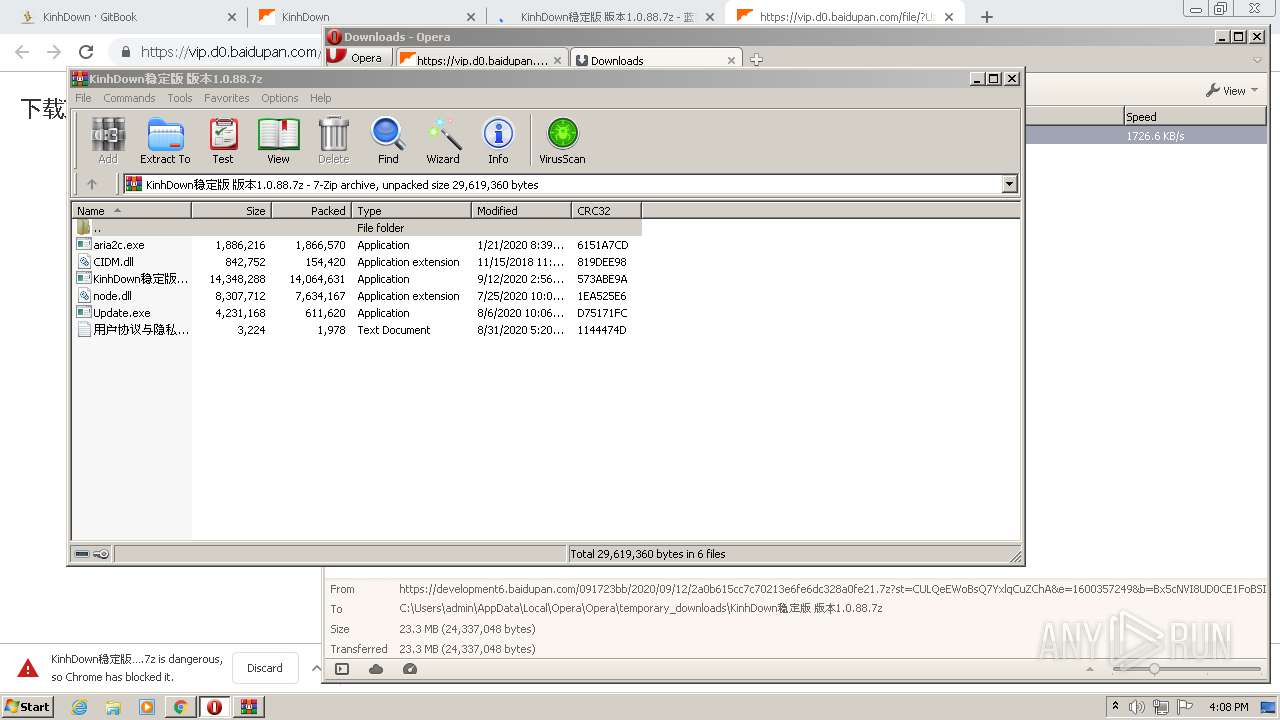
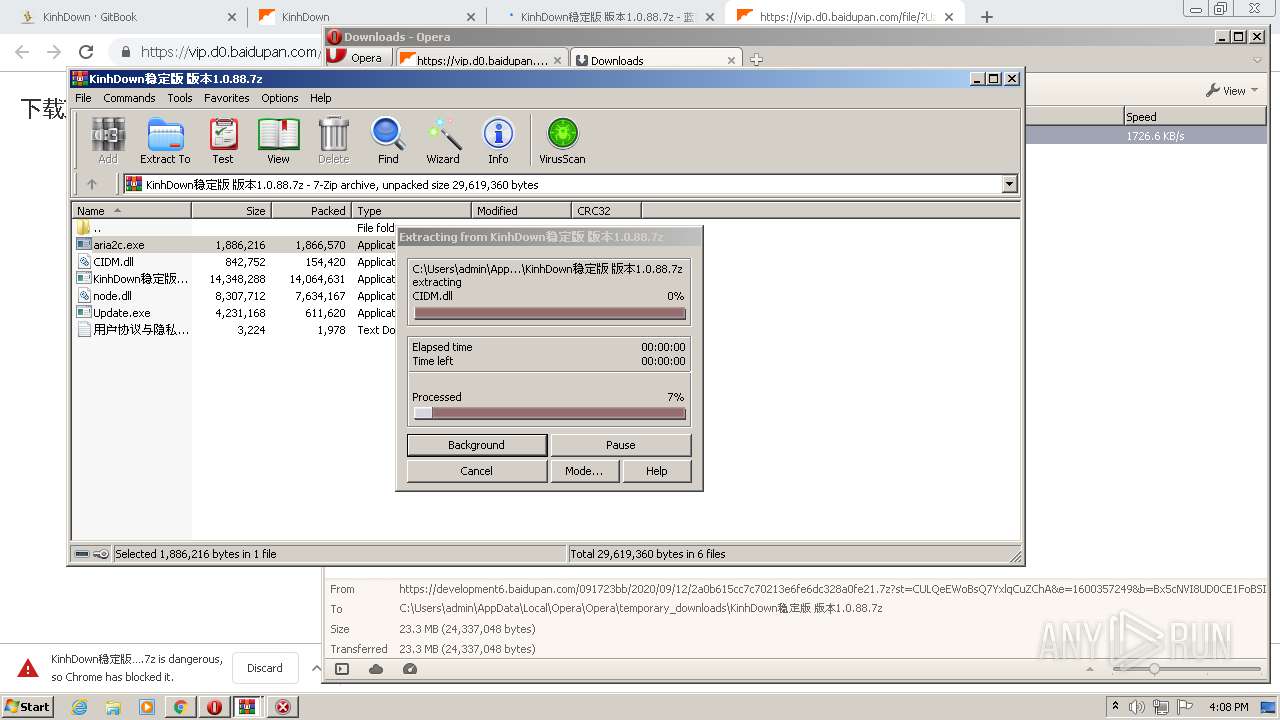
Executable content was dropped or overwritten
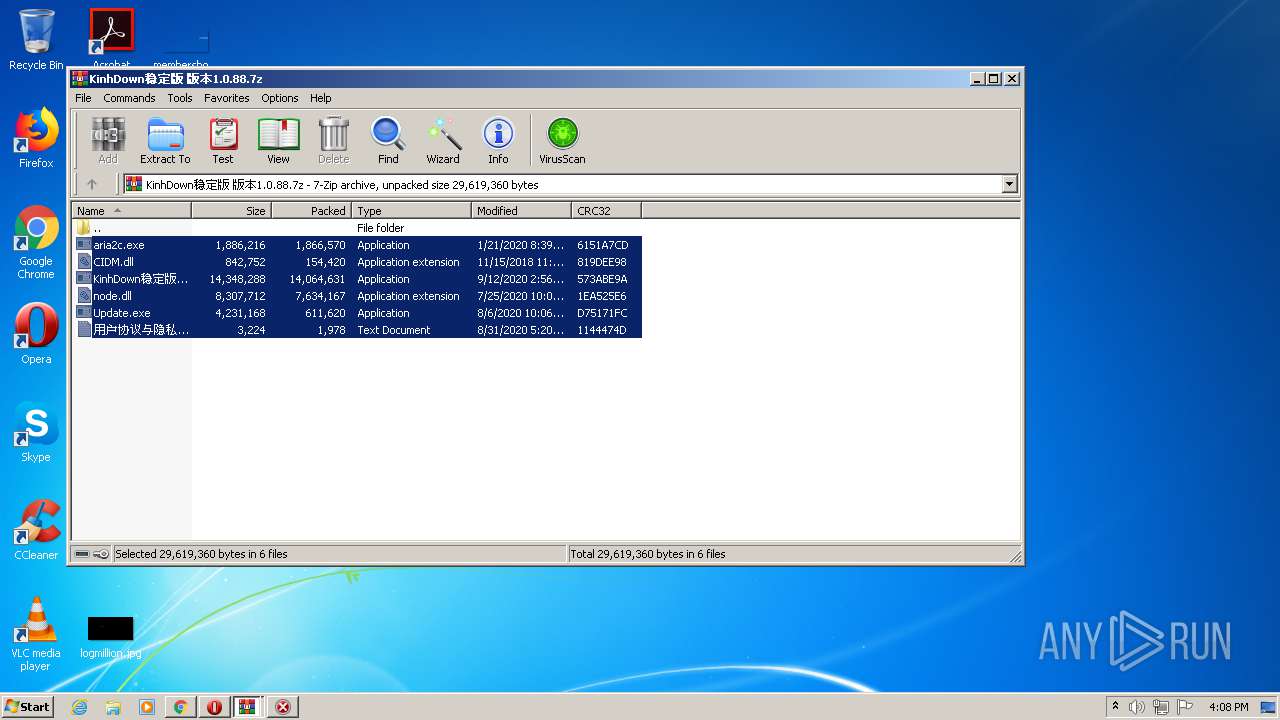
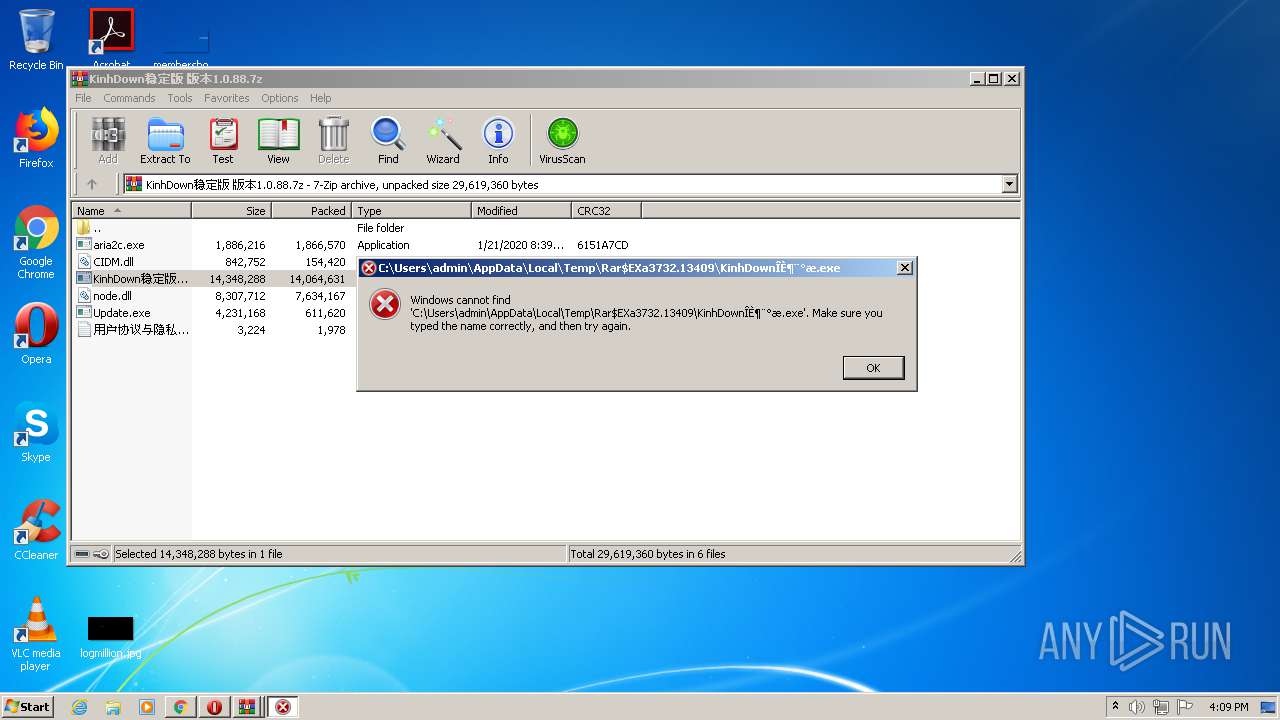
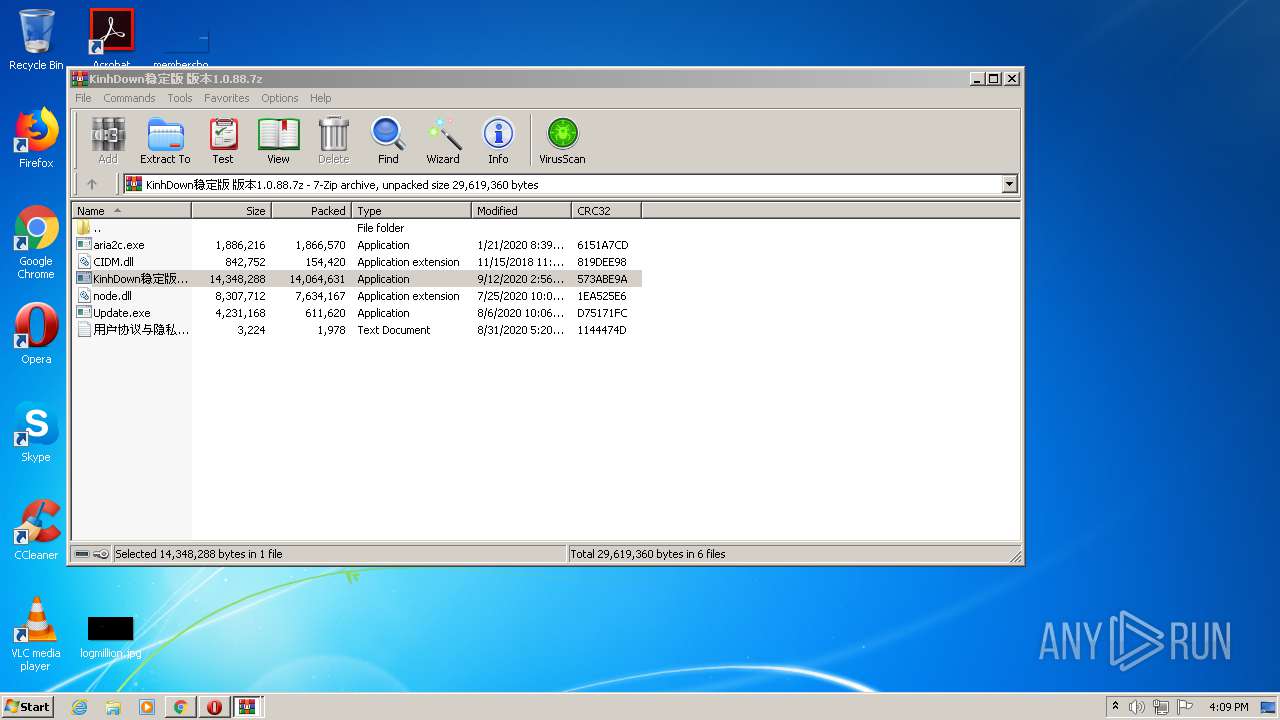
- WinRAR.exe (PID: 3732)
- WinRAR.exe (PID: 2736)
Application launched itself
- Update.exe (PID: 3252)
- Update.exe (PID: 3844)
- dd.exe (PID: 3404)
INFO
Reads the hosts file
- chrome.exe (PID: 1964)
- chrome.exe (PID: 2528)
Application launched itself
- chrome.exe (PID: 2528)
Reads settings of System Certificates
- chrome.exe (PID: 1964)
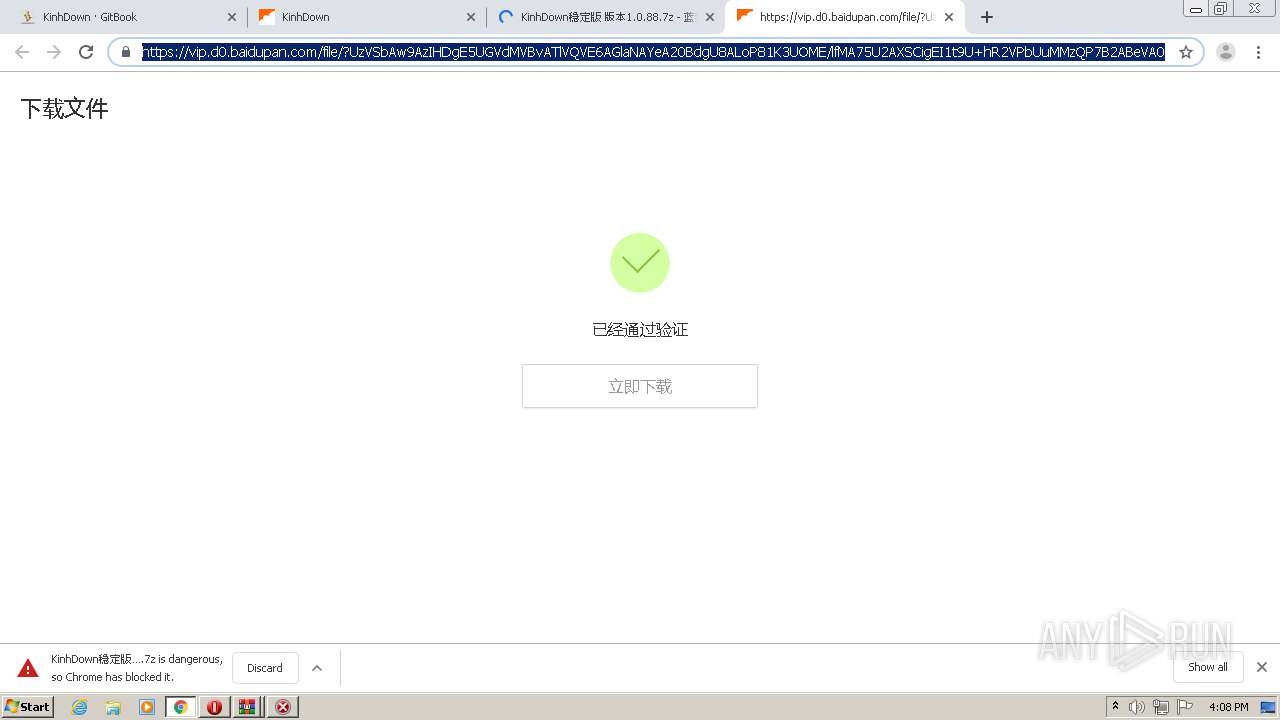
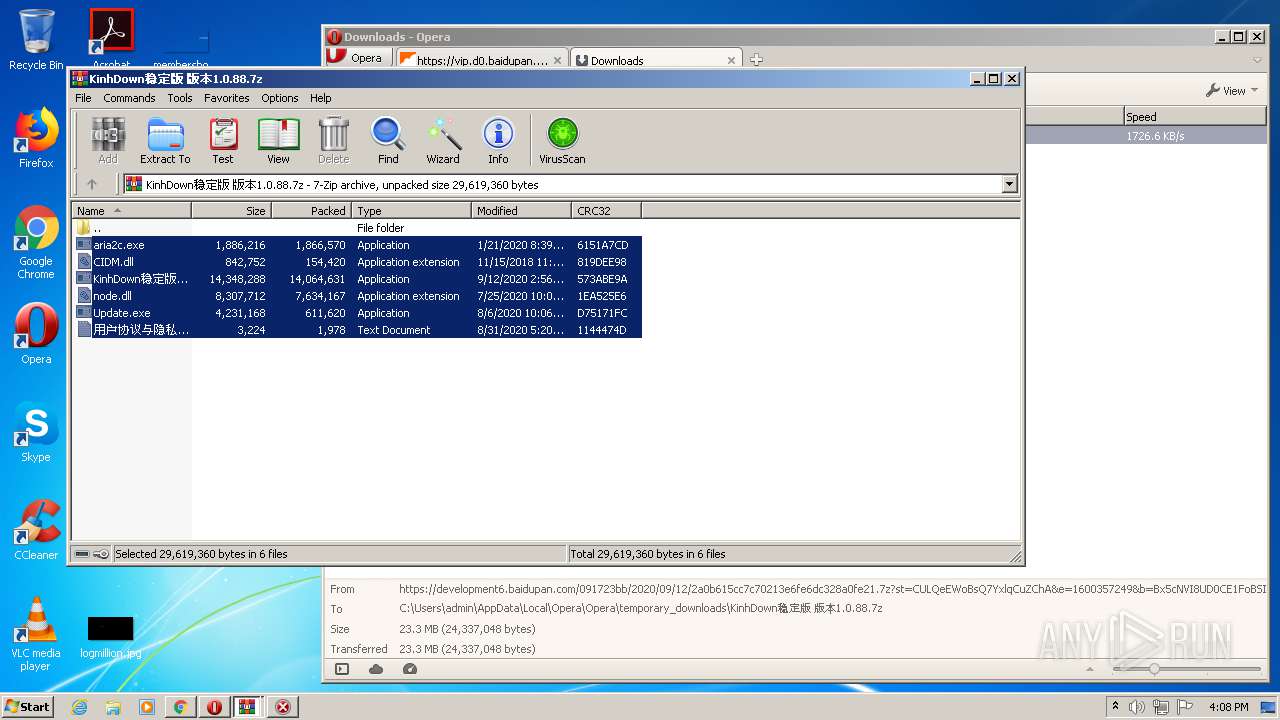
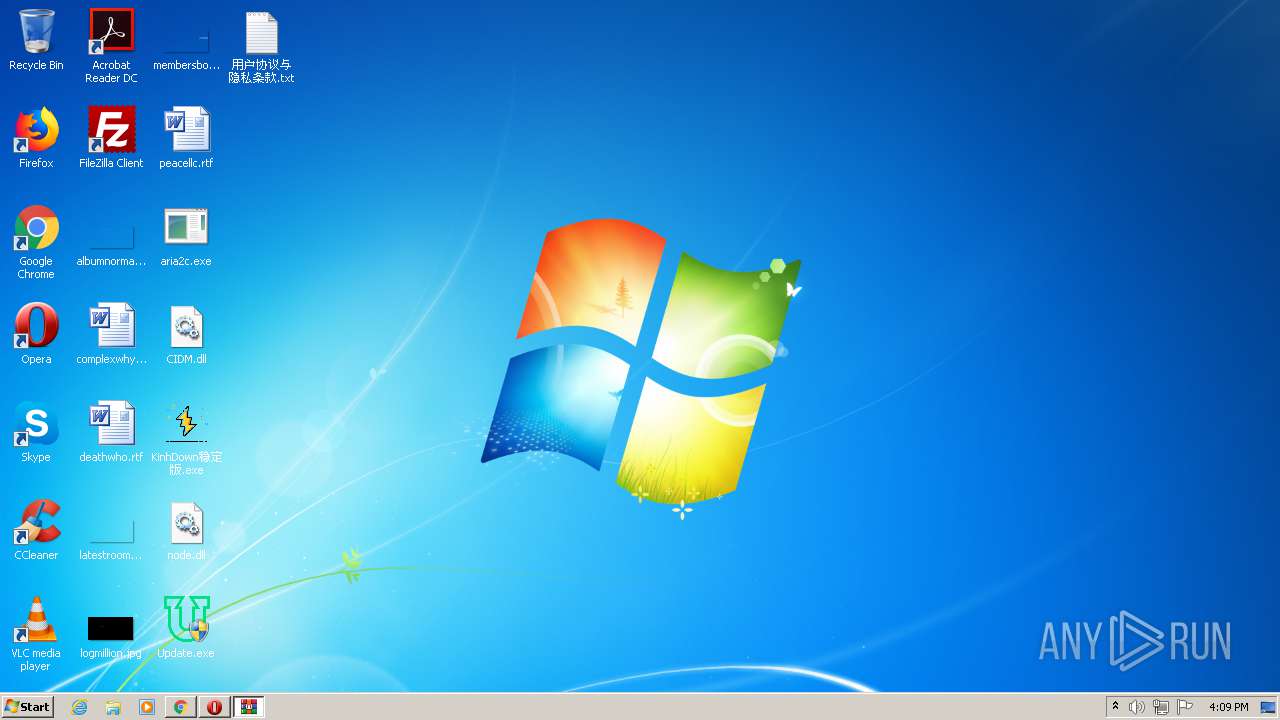
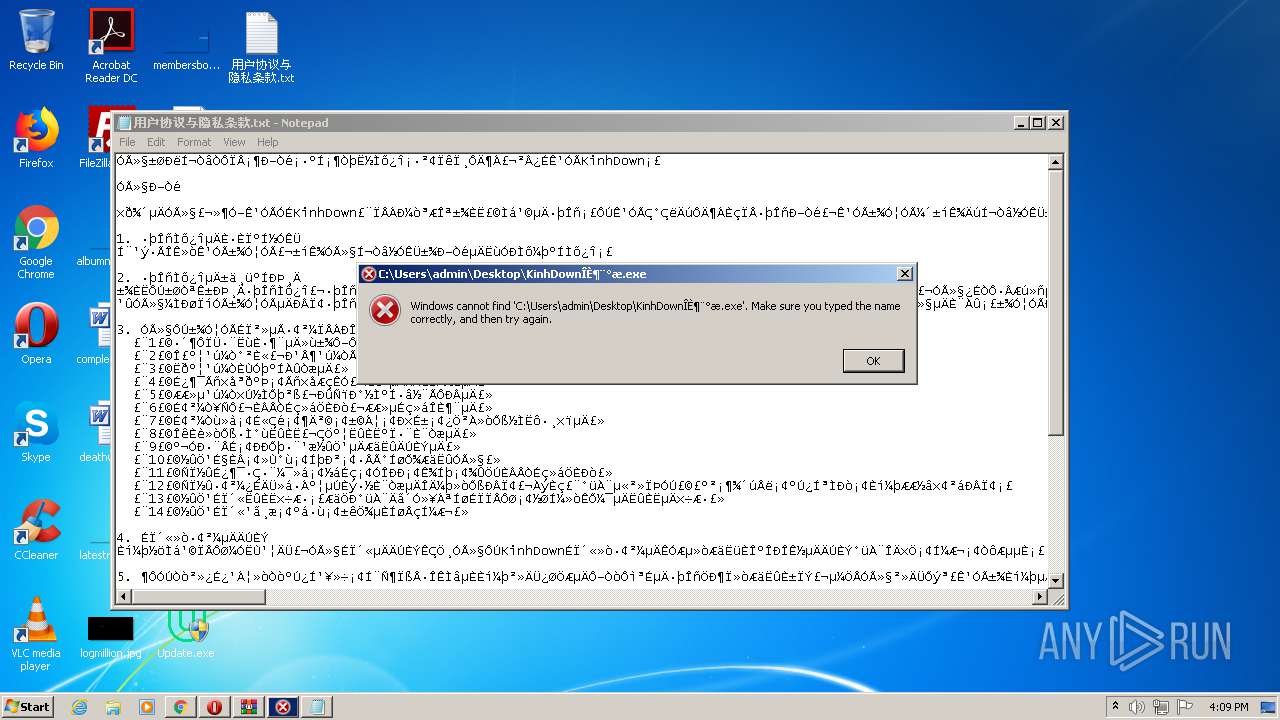
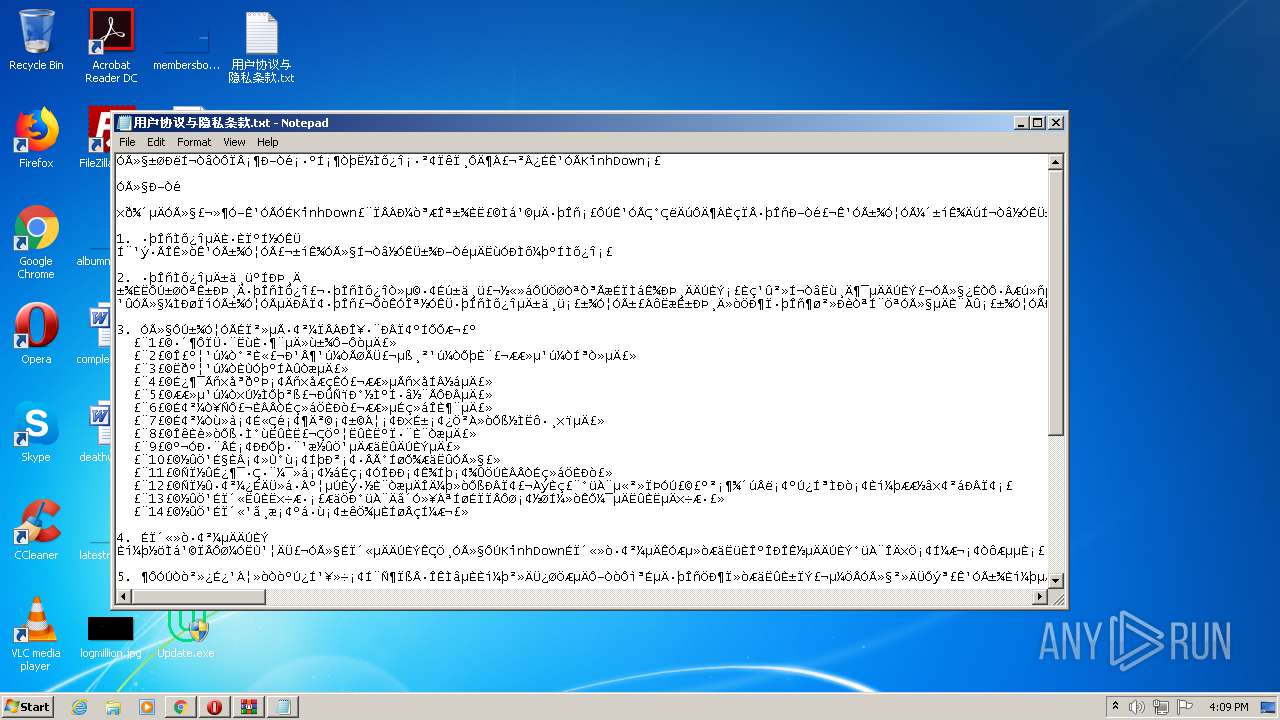
Manual execution by user
- opera.exe (PID: 3068)
- KinhDown稳定版.exe (PID: 2308)
- aria2c.exe (PID: 756)
- Update.exe (PID: 2700)
- NOTEPAD.EXE (PID: 2068)
- Update.exe (PID: 3844)
- dd.exe (PID: 3404)
Creates files in the user directory
- opera.exe (PID: 3068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
98
Monitored processes
39
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13768398650628992298,1824967733886716575,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5378745217037766881 --mojo-platform-channel-handle=3764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 756 | "C:\Users\admin\Desktop\aria2c.exe" | C:\Users\admin\Desktop\aria2c.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13768398650628992298,1824967733886716575,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=760045224144229911 --mojo-platform-channel-handle=3920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13768398650628992298,1824967733886716575,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8948355930796405447 --mojo-platform-channel-handle=3596 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1356 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2736.14156\Update.exe" 796465 | C:\Users\admin\AppData\Local\Temp\Rar$EXa2736.14156\Update.exe | Update.exe | ||||||||||||
User: admin Company: KinhUBAQ_Pro Integrity Level: HIGH Description: Update Exit code: 3221225477 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13768398650628992298,1824967733886716575,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12889554620492192149 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13768398650628992298,1824967733886716575,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10249370563032214366 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13768398650628992298,1824967733886716575,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17343159006243993005 --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13768398650628992298,1824967733886716575,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1896562389973347988 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13768398650628992298,1824967733886716575,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8435344038336983919 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 857
Read events
2 647
Write events
205
Delete events
5
Modification events
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2528-13244828714786875 |
Value: 259 | |||
Executable files
18
Suspicious files
91
Text files
206
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0cbbf07c-bd76-4726-8ef2-0d1be30c56d1.tmp | — | |
MD5:— | SHA256:— | |||
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF207989.TMP | — | |
MD5:— | SHA256:— | |||
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF2079f7.TMP | text | |
MD5:— | SHA256:— | |||
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF207a83.TMP | — | |
MD5:— | SHA256:— | |||
| 2528 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
85
DNS requests
61
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3068 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
3068 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
3068 | opera.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCnHaFEYNiK5tAuCt%2FwnQsC | US | der | 472 b | whitelisted |
1964 | chrome.exe | GET | 200 | 173.194.165.170:80 | http://r4---sn-4g5edney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=45.86.200.17&mm=28&mn=sn-4g5edney&ms=nvh&mt=1600355056&mv=m&mvi=4&pl=25&shardbypass=yes | US | crx | 834 Kb | whitelisted |
3068 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 922 b | whitelisted |
3068 | opera.exe | GET | — | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsalphasha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSE1Wv4CYvTB7dm2OHrrWWWqmtnYQQU9c3VPAhQ%2BWpPOreX2laD5mnSaPcCDAOycd4sx3zmlHk9TQ%3D%3D | US | — | — | whitelisted |
3068 | opera.exe | GET | 200 | 104.18.21.226:80 | http://crl.globalsign.net/root.crl | US | der | 1.22 Kb | whitelisted |
3068 | opera.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDHJYeDZun1boHUGISA%3D%3D | US | der | 1.54 Kb | whitelisted |
1964 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3068 | opera.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDEoqB3LuF7k61ZFD5g%3D%3D | US | der | 1.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1964 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
1964 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1964 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1964 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
1964 | chrome.exe | 216.58.207.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1964 | chrome.exe | 173.194.165.170:80 | r4---sn-4g5edney.gvt1.com | Google Inc. | US | whitelisted |
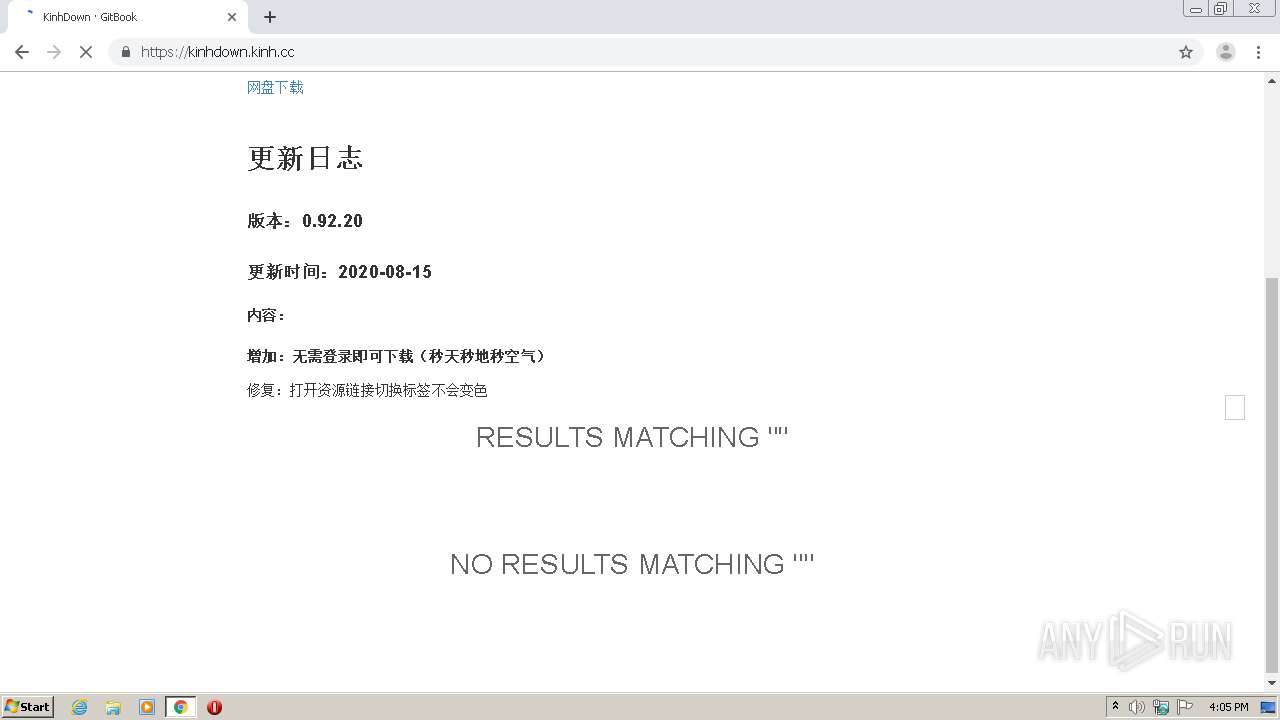
1964 | chrome.exe | 23.225.94.42:35729 | kinhdown.kinh.cc | CloudRadium L.L.C | US | suspicious |
1964 | chrome.exe | 142.250.74.206:443 | translate.google.com | Google Inc. | US | whitelisted |
1964 | chrome.exe | 216.58.207.78:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
kinhdown.kinh.cc |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r4---sn-4g5edney.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |