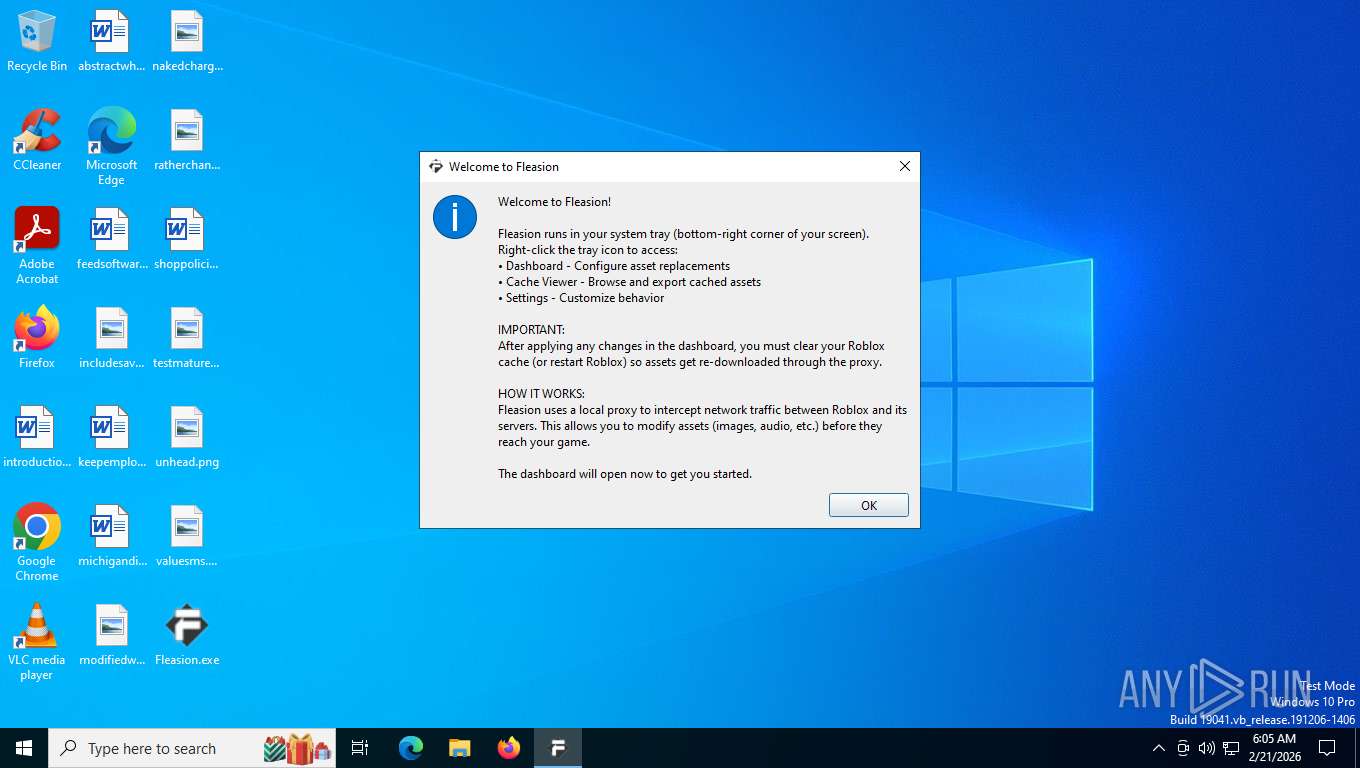
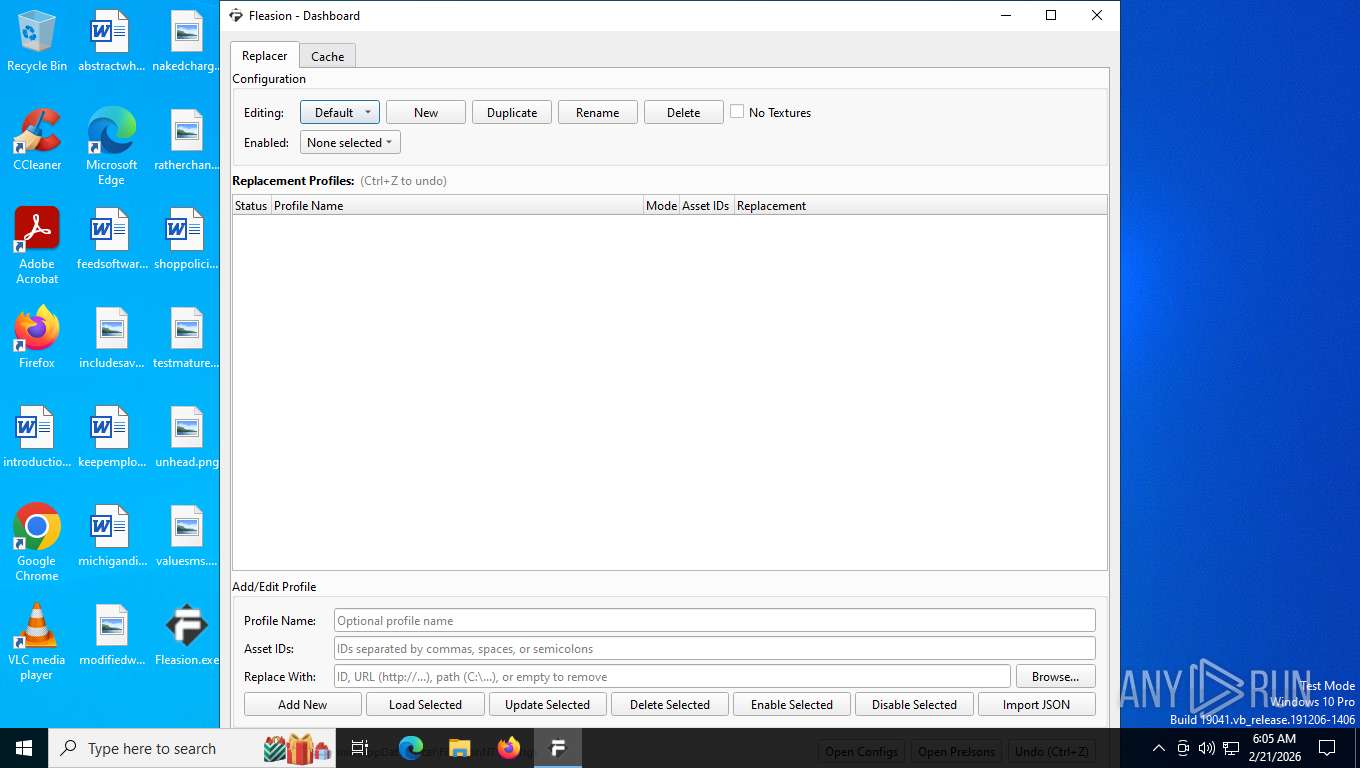
| File name: | Fleasion.exe |
| Full analysis: | https://app.any.run/tasks/6e47640f-28a5-4a39-9183-3c4cbac5a416 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2026, 11:05:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | F2FED5158BFEB27C1F6F64FC5B3781B1 |
| SHA1: | 0EB63A044BE4FA0FE6346541A9BB7CE9558069FD |
| SHA256: | CAE807BDCE5C9A083C2D46B57EE6E523FFDC0B27ECBD5C8A519CA44592ED2B0D |
| SSDEEP: | 786432:6hLygjbUfE6x+EZ6O06dAg7hMlQTagfP9niw+eYtqt2:6hLygjbUvmedX7ClwNFiw+eYtqt |
MALICIOUS
Malicious driver has been detected
- Fleasion.exe (PID: 7360)
- Fleasion.exe (PID: 7360)
GENERIC has been found (auto)
- Fleasion.exe (PID: 7360)
SUSPICIOUS
Application launched itself
- Fleasion.exe (PID: 7360)
Drops a system driver (possible attempt to evade defenses)
- Fleasion.exe (PID: 7360)
Process drops python dynamic module
- Fleasion.exe (PID: 7360)
Executable content was dropped or overwritten
- Fleasion.exe (PID: 7360)
The process drops C-runtime libraries
- Fleasion.exe (PID: 7360)
Get information on the list of running processes
- Fleasion.exe (PID: 132)
Named pipe usage
- windows-redirector.exe (PID: 7472)
Reads the date of Windows installation
- Fleasion.exe (PID: 132)
INFO
Checks proxy server information
- Fleasion.exe (PID: 132)
- slui.exe (PID: 8016)
Reads the computer name
- Fleasion.exe (PID: 132)
- Fleasion.exe (PID: 7360)
- windows-redirector.exe (PID: 7472)
PyInstaller has been detected (YARA)
- Fleasion.exe (PID: 7360)
- Fleasion.exe (PID: 132)
Drops script file
- Fleasion.exe (PID: 132)
- Fleasion.exe (PID: 7360)
Create files in a temporary directory
- Fleasion.exe (PID: 7360)
There is functionality for taking screenshot (YARA)
- Fleasion.exe (PID: 7360)
- Fleasion.exe (PID: 132)
The sample compiled with english language support
- Fleasion.exe (PID: 7360)
Checks supported languages
- Fleasion.exe (PID: 7360)
- Fleasion.exe (PID: 132)
- windows-redirector.exe (PID: 7472)
Creates files or folders in the user directory
- Fleasion.exe (PID: 132)
Reads security settings of Internet Explorer
- Fleasion.exe (PID: 132)
Process checks computer location settings
- Fleasion.exe (PID: 132)
Application based on Rust
- windows-redirector.exe (PID: 7472)
- Fleasion.exe (PID: 132)
Reads the machine GUID from the registry
- Fleasion.exe (PID: 132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2026:01:30 03:48:55+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 181760 |
| InitializedDataSize: | 102912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xdfa0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
275
Monitored processes
141
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Users\admin\Desktop\Fleasion.exe" | C:\Users\admin\Desktop\Fleasion.exe | Fleasion.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 224 | tasklist /FI "IMAGENAME eq RobloxPlayerBeta.exe" | C:\Windows\System32\tasklist.exe | — | Fleasion.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 552 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | tasklist /FI "IMAGENAME eq RobloxPlayerBeta.exe" | C:\Windows\System32\tasklist.exe | — | Fleasion.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 796 | tasklist /FI "IMAGENAME eq RobloxPlayerBeta.exe" | C:\Windows\System32\tasklist.exe | — | Fleasion.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1000 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | tasklist /FI "IMAGENAME eq RobloxPlayerBeta.exe" | C:\Windows\System32\tasklist.exe | — | Fleasion.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 420
Read events
13 418
Write events
2
Delete events
0
Modification events
| (PID) Process: | (7472) windows-redirector.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\WinDivert |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Users\admin\AppData\Local\Temp\_MEI73602\mitmproxy_windows\WinDivert64.sys | |||
| (PID) Process: | (7472) windows-redirector.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\WinDivert |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
Executable files
175
Suspicious files
105
Text files
422
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\OpenGL\DLLS\freeglut64.vc14.dll | executable | |
MD5:1167623310A2868C49C5F990D076C7EA | SHA256:E84436244C0F555151719E22DDB31E4175396F851F124680DE5C776B4DB3C898 | |||
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\OpenGL\DLLS\gle32.vc9.dll | executable | |
MD5:817F42C07D5587E1264697E8F89E6E59 | SHA256:59CAD51526BE5FD00F904A431754C04FBE151471AF571D2F7497635BDE814636 | |||
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\OpenGL\DLLS\freeglut32.vc14.dll | executable | |
MD5:67882F7987F27C8C2E7B4EBAC37BF42C | SHA256:C9C00A4EA9B9FECDCAE81F6FACAF27E349714D56FE7640CE9C37ED38841A0B87 | |||
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\MSVCR100.dll | executable | |
MD5:366FD6F3A451351B5DF2D7C4ECF4C73A | SHA256:AE3CB6C6AFBA9A4AA5C85F66023C35338CA579B30326DD02918F9D55259503D5 | |||
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\DracoPy.cp314-win_amd64.pyd | executable | |
MD5:60498C6B9FC6FD9C4188FE26986F85E7 | SHA256:8AF8C4B70B20EEF873B2E45C958FBF27A8836C5F74154A63A4719B6CAD21CFC9 | |||
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\OpenGL\DLLS\freeglut_COPYING.txt | text | |
MD5:47563886AAB78E25398F067CE2EA1830 | SHA256:D4FF2334437455513889B16F1BA94165E4D32287841E6E1EE856442A155D9E99 | |||
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\OpenGL\DLLS\GLE_WIN32_README.txt | text | |
MD5:C02858F933D989EDB257604159557A23 | SHA256:A7DF9B1FCC74D4DDF51CA0774CC94F00DC55146052FBE08614DBA0E9DA68F887 | |||
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\OpenGL\DLLS\freeglut32.vc9.dll | executable | |
MD5:7663CB1E1AC1F1285E755ED8FB22B19C | SHA256:5BA8C62E293BBDC7064A8607992061C55278596300136785E3C11A8C7BB0723F | |||
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\OpenGL\DLLS\freeglut32.vc10.dll | executable | |
MD5:894D0FF83745E0484F457D600543689E | SHA256:6F9A26D2989E4DF40D948DF565A661F57FE1FA80801C9C3AE5CD3DE4AADC66BE | |||
| 7360 | Fleasion.exe | C:\Users\admin\AppData\Local\Temp\_MEI73602\OpenGL\DLLS\gle32.vc14.dll | executable | |
MD5:88A3205111462AE2ACBBEFB1F1739F99 | SHA256:D14BF244F41FC2ECF2DFABA5A73A389ADED8690282943666EB9880BAB3FFA36D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
51
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8112 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
4 | System | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7544 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
8112 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
— | — | POST | 200 | 40.126.32.140:443 | https://login.live.com/RST2.srf | US | binary | 10.3 Kb | whitelisted |
8112 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 92.123.104.47:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7544 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7544 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |