| download: | BvebCryptoSetup.exe |
| Full analysis: | https://app.any.run/tasks/d7225339-3824-4255-a887-59258ccb1608 |
| Verdict: | Malicious activity |
| Analysis date: | September 29, 2019, 10:05:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EB5A9DF903B6E41F7F20E63D679A8514 |
| SHA1: | CDE8AC0751D032C0AC3FE4DB36C6BCC7BBE306D2 |
| SHA256: | CAE789212A334910521D8A10E11637AF5A0DBCD15D071082BC800D0A681DA5EF |
| SSDEEP: | 393216:Dk+2F5fhc1e6QRi22Yj2mwSivuAeO97/cHpUbyFdL8I6c4FB5rPoGzERiUCwof:DWXKXQRi20mFAeO9TcHpU+FdL8dhg9of |
MALICIOUS
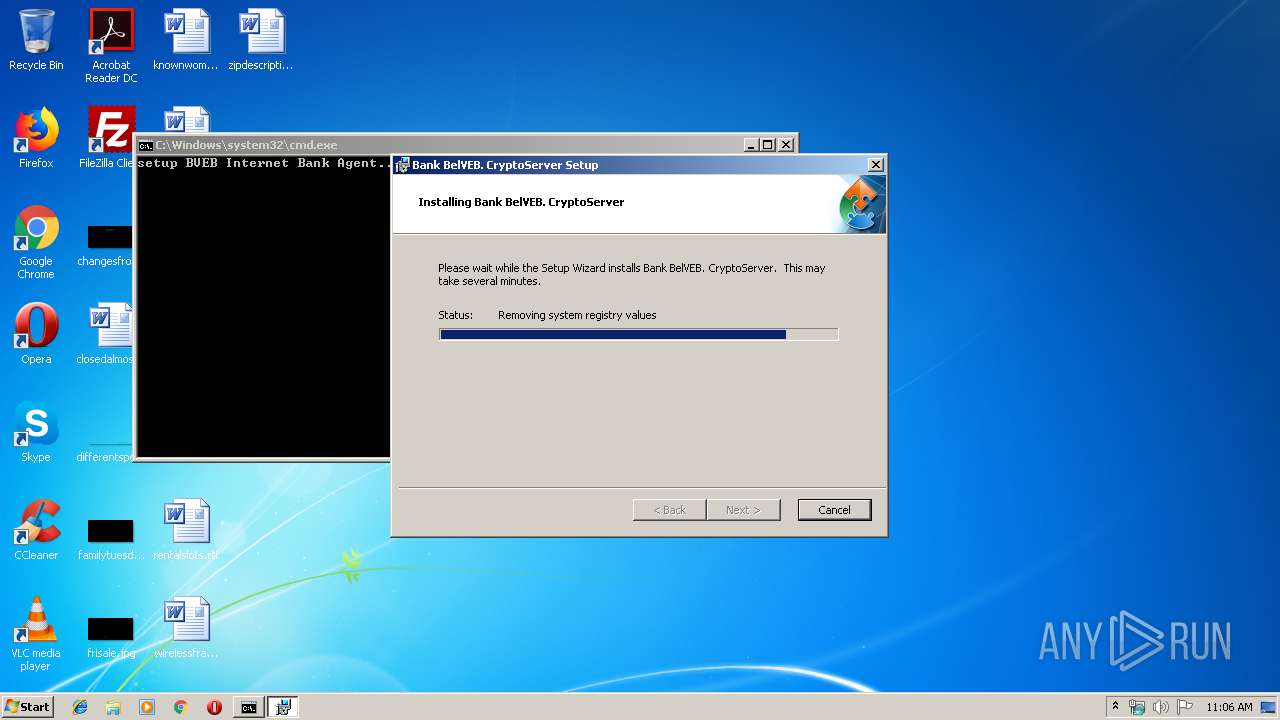
Application was dropped or rewritten from another process
- BvebInternetBankAgent2.4.0.36.exe (PID: 3936)
- BvebInternetBankAgent2.4.0.36.exe (PID: 3156)
- BvebInternetBankAgent2.4.0.36.exe (PID: 2524)
- openssl.exe (PID: 552)
- openssl.exe (PID: 3888)
- openssl.exe (PID: 2192)
- openssl.exe (PID: 3252)
- certmgr.exe (PID: 2984)
- certmgr.exe (PID: 2480)
- certutil.exe (PID: 3332)
- certutil.exe (PID: 3208)
- certmgr.exe (PID: 4020)
- certutil.exe (PID: 3464)
- OBCryptoApp.exe (PID: 1448)
- AddFfProxyException.exe (PID: 3540)
- AvPCMEx_setup.exe (PID: 2232)
- AvPCMEx_setup.exe (PID: 2808)
Loads dropped or rewritten executable
- BvebInternetBankAgent2.4.0.36.exe (PID: 3936)
- openssl.exe (PID: 552)
- openssl.exe (PID: 2192)
- openssl.exe (PID: 3888)
- openssl.exe (PID: 3252)
- certutil.exe (PID: 3332)
- certutil.exe (PID: 3208)
- certutil.exe (PID: 3464)
- OBCryptoApp.exe (PID: 1448)
Changes settings of System certificates
- certmgr.exe (PID: 2480)
Loads the Task Scheduler DLL interface
- BvebInternetBankAgent2.4.0.36.exe (PID: 3936)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 3056)
- BvebInternetBankAgent2.4.0.36.exe (PID: 3936)
- BvebCryptoSetup.exe (PID: 3380)
- AvPCMEx_setup.exe (PID: 2232)
- msiexec.exe (PID: 2408)
Creates files in the user directory
- BvebInternetBankAgent2.4.0.36.exe (PID: 3936)
- xcopy.exe (PID: 1388)
- xcopy.exe (PID: 2856)
- xcopy.exe (PID: 2340)
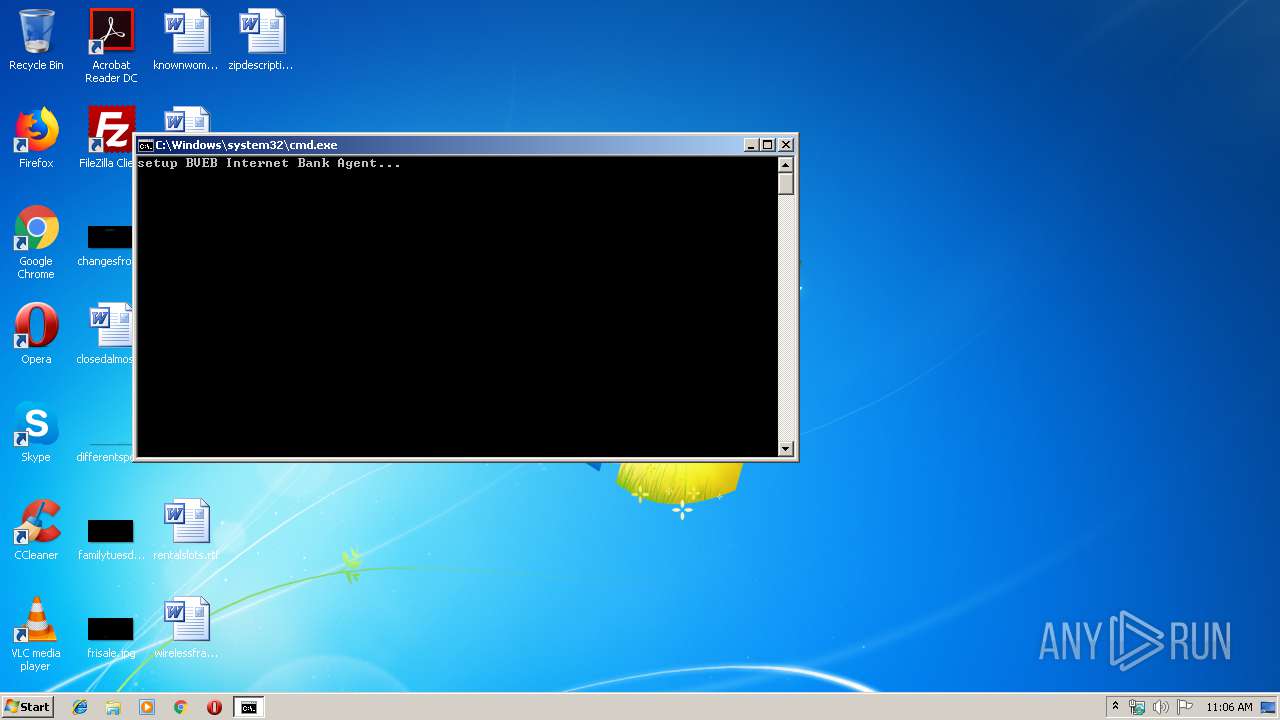
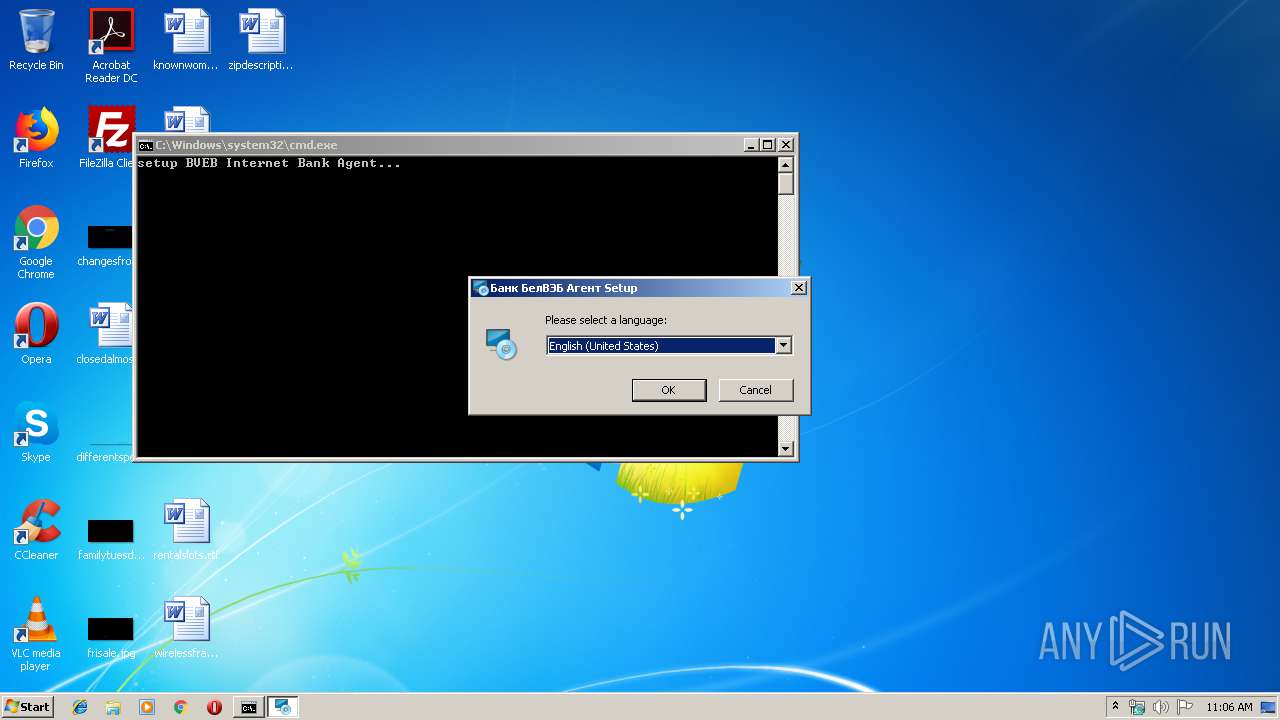
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3192)
- BvebCryptoSetup.exe (PID: 3380)
- MsiExec.exe (PID: 3812)
- cmd.exe (PID: 3752)
- MSIF7CB.tmp (PID: 3696)
- cmd.exe (PID: 2796)
- MSI3B22.tmp (PID: 2660)
- cmd.exe (PID: 3440)
- MSI3EEC.tmp (PID: 2644)
- MSI4035.tmp (PID: 1816)
Executed as Windows Service
- vssvc.exe (PID: 920)
Changes the autorun value in the registry
- msiexec.exe (PID: 2408)
Creates files in the program directory
- cmd.exe (PID: 2796)
- openssl.exe (PID: 552)
- openssl.exe (PID: 2192)
- openssl.exe (PID: 3888)
- openssl.exe (PID: 3252)
- xcopy.exe (PID: 1084)
- certutil.exe (PID: 3332)
- xcopy.exe (PID: 3604)
- xcopy.exe (PID: 3400)
Application launched itself
- cmd.exe (PID: 2796)
- cmd.exe (PID: 3192)
Uses NETSH.EXE for network configuration
- MSI38C0.tmp (PID: 3780)
- MSI3583.tmp (PID: 2532)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 3392)
Executed via COM
- DrvInst.exe (PID: 3188)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2188)
- MsiExec.exe (PID: 3812)
- MsiExec.exe (PID: 3436)
Searches for installed software
- msiexec.exe (PID: 2408)
Creates files in the program directory
- msiexec.exe (PID: 2408)
Creates a software uninstall entry
- msiexec.exe (PID: 2408)
Application was dropped or rewritten from another process
- MSIF7CB.tmp (PID: 3696)
- MSI32A2.tmp (PID: 592)
- MSI33FB.tmp (PID: 1412)
- MSI3583.tmp (PID: 2532)
- MSI38C0.tmp (PID: 3780)
- MSI3EEC.tmp (PID: 2644)
- MSI3B22.tmp (PID: 2660)
- MSI4035.tmp (PID: 1816)
- AvPCMEx_setup.tmp (PID: 3704)
- AvPCMEx_setup.tmp (PID: 2132)
Low-level read access rights to disk partition
- vssvc.exe (PID: 920)
Starts application with an unusual extension
- msiexec.exe (PID: 2408)
Application launched itself
- msiexec.exe (PID: 2408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:30 20:01:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 109568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d549 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Sep-2018 18:01:44 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 30-Sep-2018 18:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E924 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69845 |
.rdata | 0x00030000 | 0x00009A8C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13014 |
.data | 0x0003A000 | 0x000203A0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23545 |
.gfids | 0x0005B000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.09308 |
.rsrc | 0x0005C000 | 0x0000E060 | 0x0000E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.80069 |
.reloc | 0x0006B000 | 0x00001FDC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67876 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.10026 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.25868 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.02609 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.18109 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.04307 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.66634 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
8 | 3.71728 | 582 | Latin 1 / Western European | UNKNOWN | RT_STRING |
9 | 3.74776 | 476 | Latin 1 / Western European | UNKNOWN | RT_STRING |
10 | 3.55807 | 220 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
175
Monitored processes
123
Malicious processes
10
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\Windows\system32\cmd.exe /S /D /c" echo Default " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 312 | "C:\Windows\System32\netsh.exe" http add urlacl url=http://127.0.0.1:42339/bveb user=EVERYONE listen=yes delegate=no sddl= | C:\Windows\System32\netsh.exe | — | MSI38C0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | .\OpenSSL\openssl req -sha512 -x509 -new -days 10000 -nodes -out .\cert\OBCryptoCA.crt -keyout .\cert\OBCryptoCA.key -subj "/C=BY/ST=/L=/O=System Technologies/OU=/CN=OBCrypto Local Only CA (crypto.ibank.bveb.by)" | C:\Program Files\Bank BelVEB\BVEB Internet Bank Agent\ReinstallSslCert\OpenSSL\openssl.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 592 | "C:\Windows\Installer\MSI32A2.tmp" /HideWindow "C:\Windows\system32\\xcopy.exe" "C:\Program Files\Bank BelVEB\BVEB Internet Bank Agent\ReinstallSslCert\cert\OBCrypto.crt" "C:\Program Files\Bank BelVEB\BVEB Internet Bank Agent\" /y | C:\Windows\Installer\MSI32A2.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: HIGH Description: File that launches another file Exit code: 0 Version: 10.9.1.0 Modules
| |||||||||||||||
| 920 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 972 | findstr /b "[" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | xcopy "C:\Users\admin\AppData\Roaming\mozilla\firefox\Profiles/qldyz51w.default\*.db" .\ff_add_cert\tmp /y | C:\Windows\system32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1388 | xcopy "C:\Users\admin\AppData\Roaming\mozilla\firefox\Profiles/qldyz51w.default\*.db" "C:\Users\admin\AppData\Roaming\mozilla\firefox\Profiles/qldyz51w.default\backup\" /-y | C:\Windows\system32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1412 | "C:\Windows\Installer\MSI33FB.tmp" /HideWindow "C:\Windows\system32\\xcopy.exe" "C:\Program Files\Bank BelVEB\BVEB Internet Bank Agent\ReinstallSslCert\cert\OBCrypto.key" "C:\Program Files\Bank BelVEB\BVEB Internet Bank Agent\" /y | C:\Windows\Installer\MSI33FB.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: HIGH Description: File that launches another file Exit code: 0 Version: 10.9.1.0 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Bank BelVEB\BVEB Internet Bank Agent\OBCryptoApp.exe" | C:\Program Files\Bank BelVEB\BVEB Internet Bank Agent\OBCryptoApp.exe | — | msiexec.exe | |||||||||||
User: admin Company: System Technologies Integrity Level: HIGH Description: ST Crypto Agent Exit code: 0 Version: DEBUG Modules
| |||||||||||||||
Total events
3 456
Read events
2 957
Write events
485
Delete events
14
Modification events
| (PID) Process: | (3380) BvebCryptoSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3380) BvebCryptoSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3192) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3192) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000007A46C790AD76D50168090000EC0B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000007A46C790AD76D50168090000EC0B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (920) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E4062991AD76D50198030000580F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (920) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E4062991AD76D501980300006C0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (920) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E4062991AD76D50198030000980B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (920) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E4062991AD76D50198030000800B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
48
Suspicious files
25
Text files
102
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | BvebInternetBankAgent2.4.0.36.exe | C:\Users\admin\AppData\Roaming\Bank BelVEB\BVEB Internet Bank Agent 2.4.0.36\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 3056 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI801B.tmp | — | |
MD5:— | SHA256:— | |||
| 3056 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8089.tmp | — | |
MD5:— | SHA256:— | |||
| 3056 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI80B9.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2408 | msiexec.exe | C:\Windows\Installer\MSID251.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | msiexec.exe | C:\Windows\Installer\MSID541.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF59647A409B5D7294.TMP | — | |
MD5:— | SHA256:— | |||
| 2408 | msiexec.exe | C:\Windows\Installer\MSID68B.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | msiexec.exe | C:\Windows\Installer\MSID6EA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2216] | OnAiRemoveRegsImmediate start.
|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2216] | MsiTableReader: Getting the active MSI database for this installation session...
|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2216] | Build JOINed tables CustomActionData string...
|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2216] | SELECT Join Query: [SELECT * FROM `RemoveRegistry`, `AI_RemoveRegistry` WHERE `RemoveRegistry`.`RemoveRegistry` = `AI_RemoveRegistry`.`RemoveReg`].
|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2216] | MsiTableReader::ExecuteQuery [SELECT * FROM `RemoveRegistry`, `AI_RemoveRegistry` WHERE `RemoveRegistry`.`RemoveRegistry` = `AI_RemoveRegistry`.`RemoveReg`]...
|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2216] | MsiTableReader::ExecuteQuery [DELETE FROM `RemoveRegistry` WHERE `RemoveRegistry`.`RemoveRegistry`='ProductName']...
|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2216] | Commit scheduled.
|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2216] | OnAiRemoveRegsImmediate end.
|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2488] | OnAiRemoveFileImmediate start.
|
MsiExec.exe | # 2019-09-29 @11:06:45 [PID=3436|Thread=2488] | MsiTableReader: Getting the active MSI database for this installation session...
|