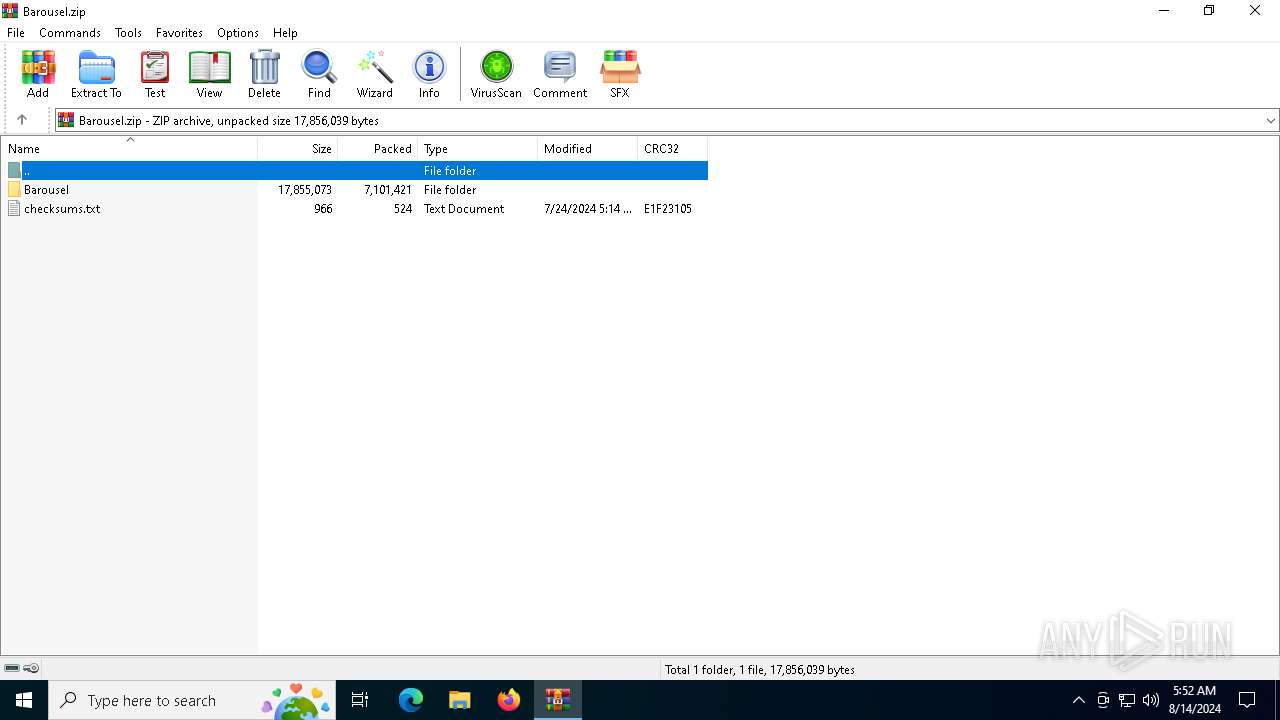
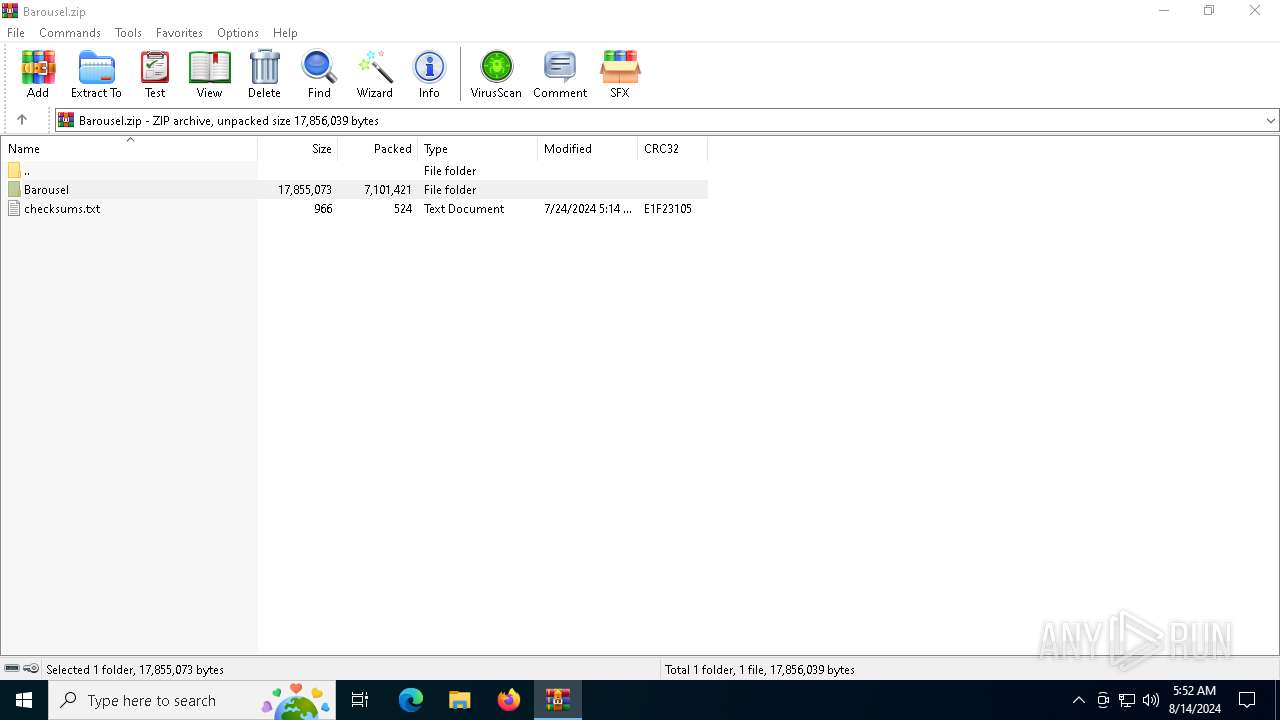
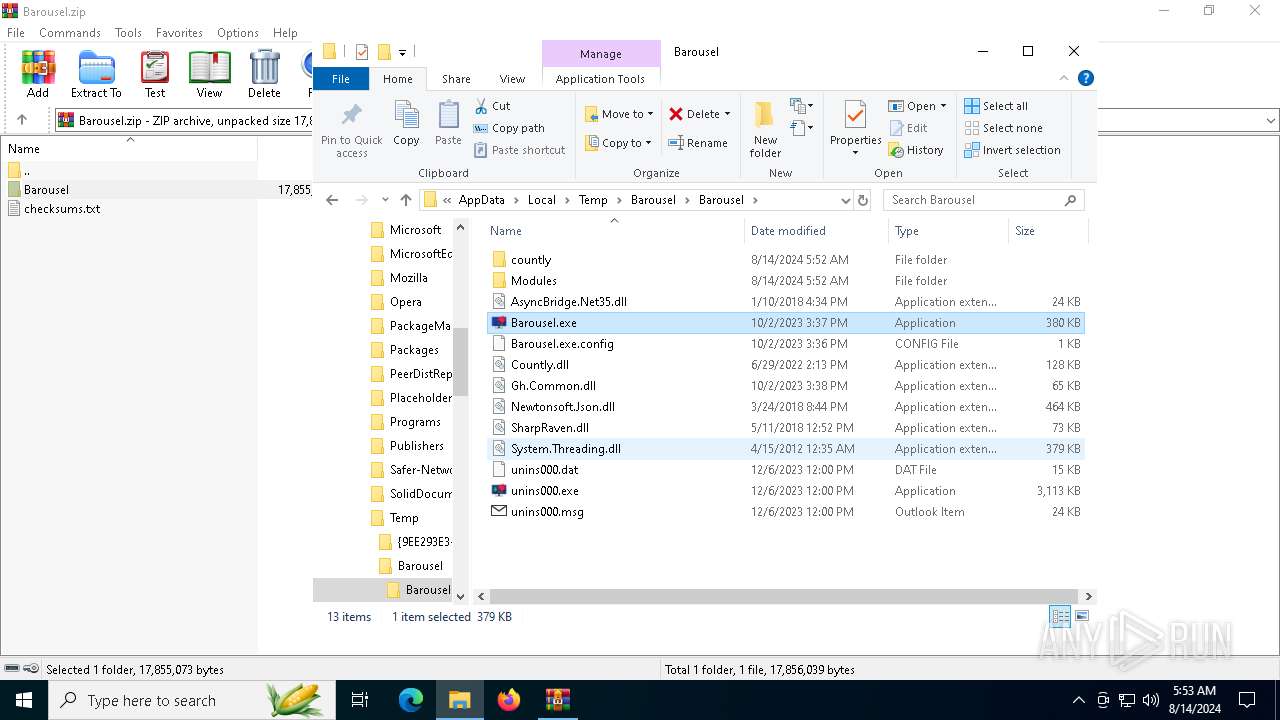
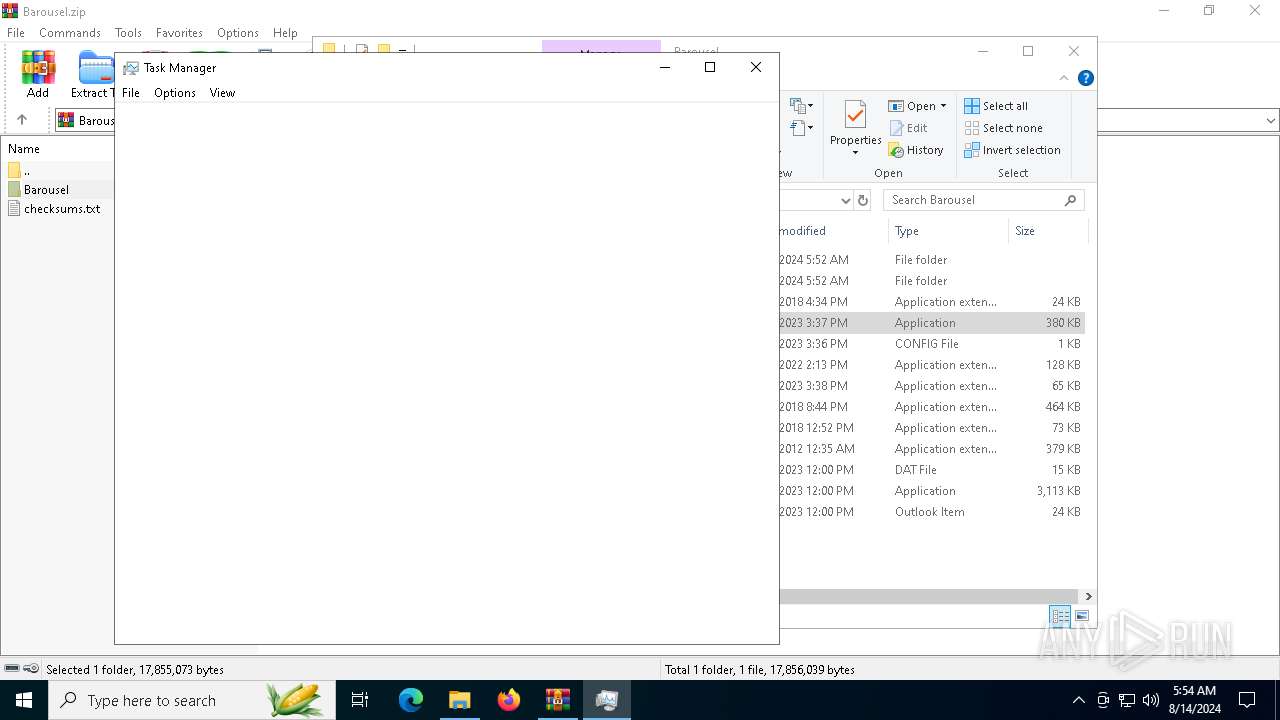
| File name: | Barousel.zip |
| Full analysis: | https://app.any.run/tasks/0eaef2b0-d3ca-47fc-864a-deedff5326f6 |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2024, 05:52:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | B139EB014169AC1BEE240CBDB5296C1B |
| SHA1: | 994D239BC7621628BFD707961A70129E28D0430F |
| SHA256: | CAD9CC4C95233330EF3DA84A9C4D8889CE70D738E9FD211750703A1849487028 |
| SSDEEP: | 98304:V9zCjbesSeNE8nT/GfQc9iU1ombgwSJI3mtl4cDio2/NEqNmYmGrTosBaSpt0dt7:ScAV/Bx8G8E |
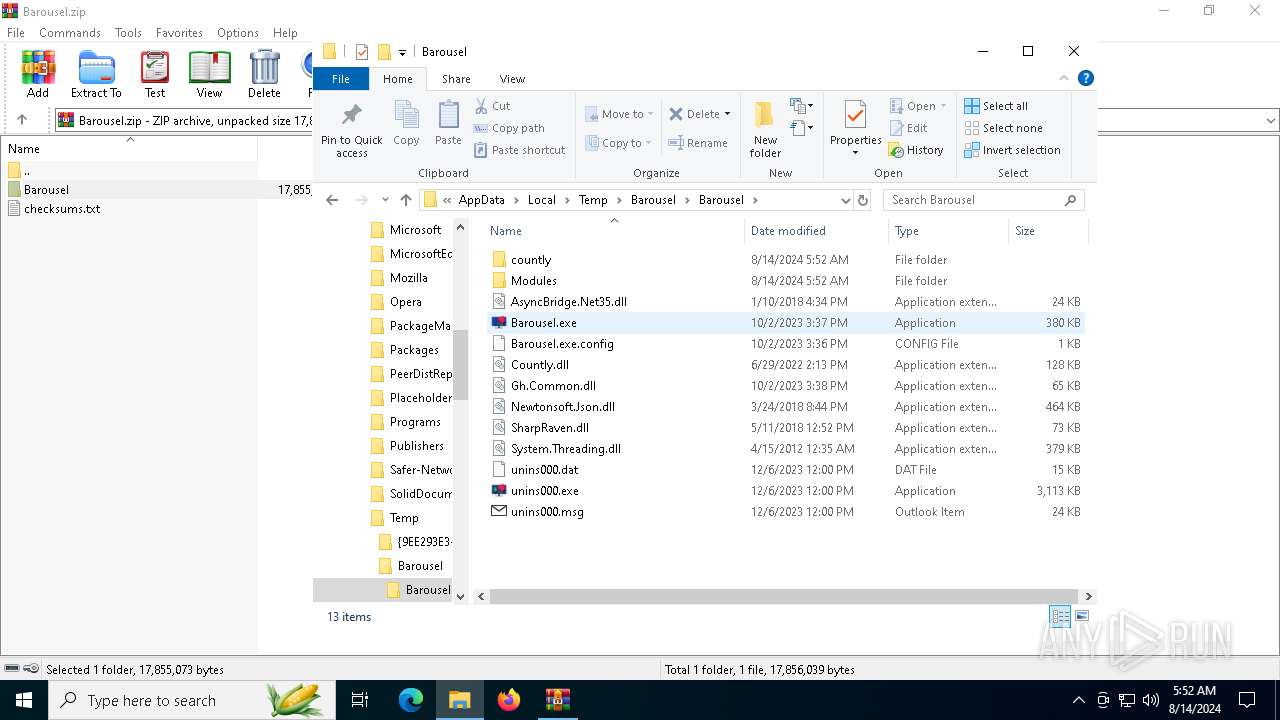
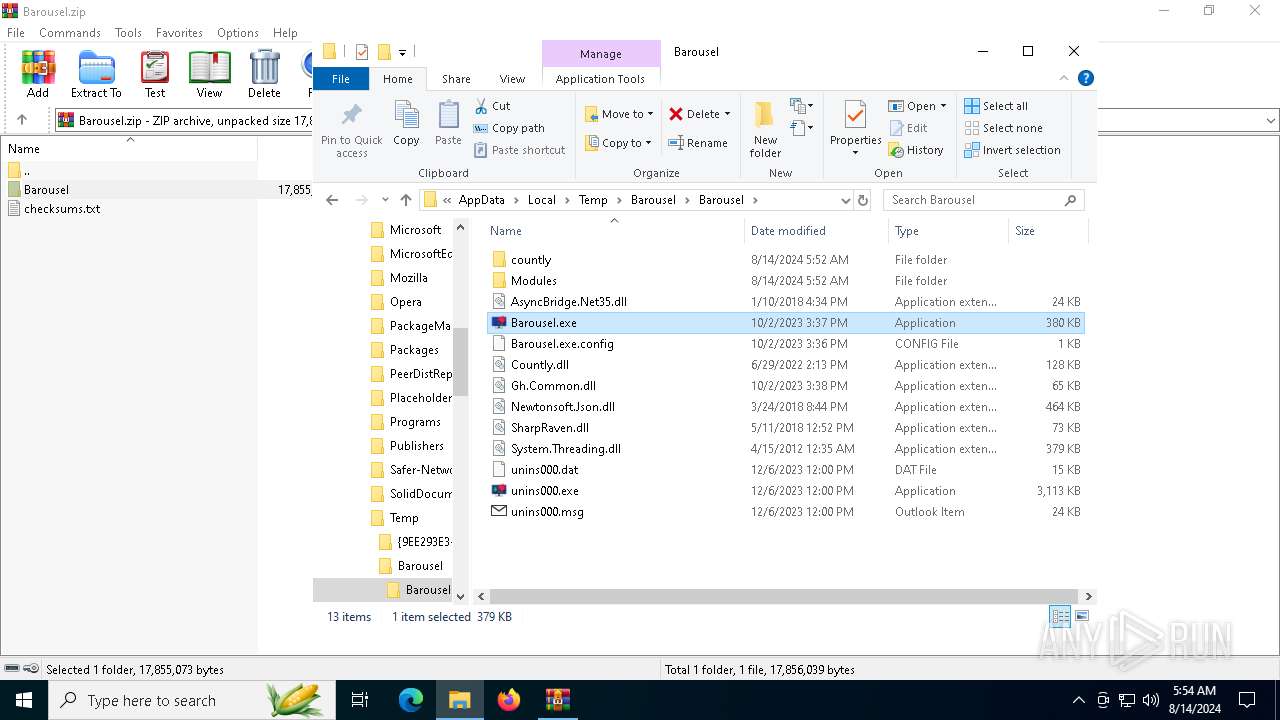
MALICIOUS
Changes the autorun value in the registry
- Barousel.exe (PID: 2384)
SUSPICIOUS
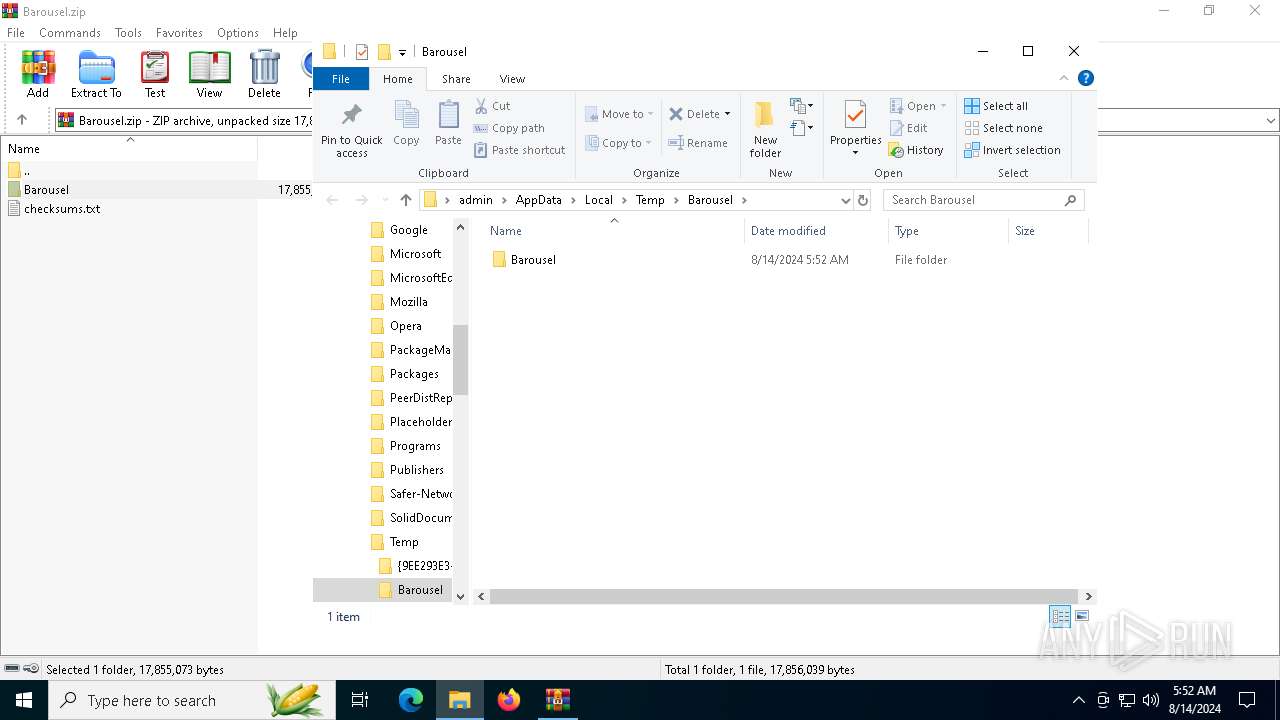
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6432)
- Barousel.exe (PID: 2384)
- ay3jswp4.exe (PID: 7328)
- ay3jswp4.tmp (PID: 7320)
Process drops legitimate windows executable
- WinRAR.exe (PID: 6432)
- ay3jswp4.tmp (PID: 7320)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6432)
- Barousel.exe (PID: 2384)
- Barousel.exe (PID: 7420)
Checks Windows Trust Settings
- Barousel.exe (PID: 2384)
- Barousel.exe (PID: 7420)
Reads Microsoft Outlook installation path
- Barousel.exe (PID: 2384)
Reads Internet Explorer settings
- Barousel.exe (PID: 2384)
MS Edge headless start
- msedge.exe (PID: 7184)
- msedge.exe (PID: 7460)
Checks for external IP
- svchost.exe (PID: 2256)
- Barousel.exe (PID: 2384)
Executable content was dropped or overwritten
- Barousel.exe (PID: 2384)
- ay3jswp4.exe (PID: 7328)
- ay3jswp4.tmp (PID: 7320)
Reads the Windows owner or organization settings
- ay3jswp4.tmp (PID: 7320)
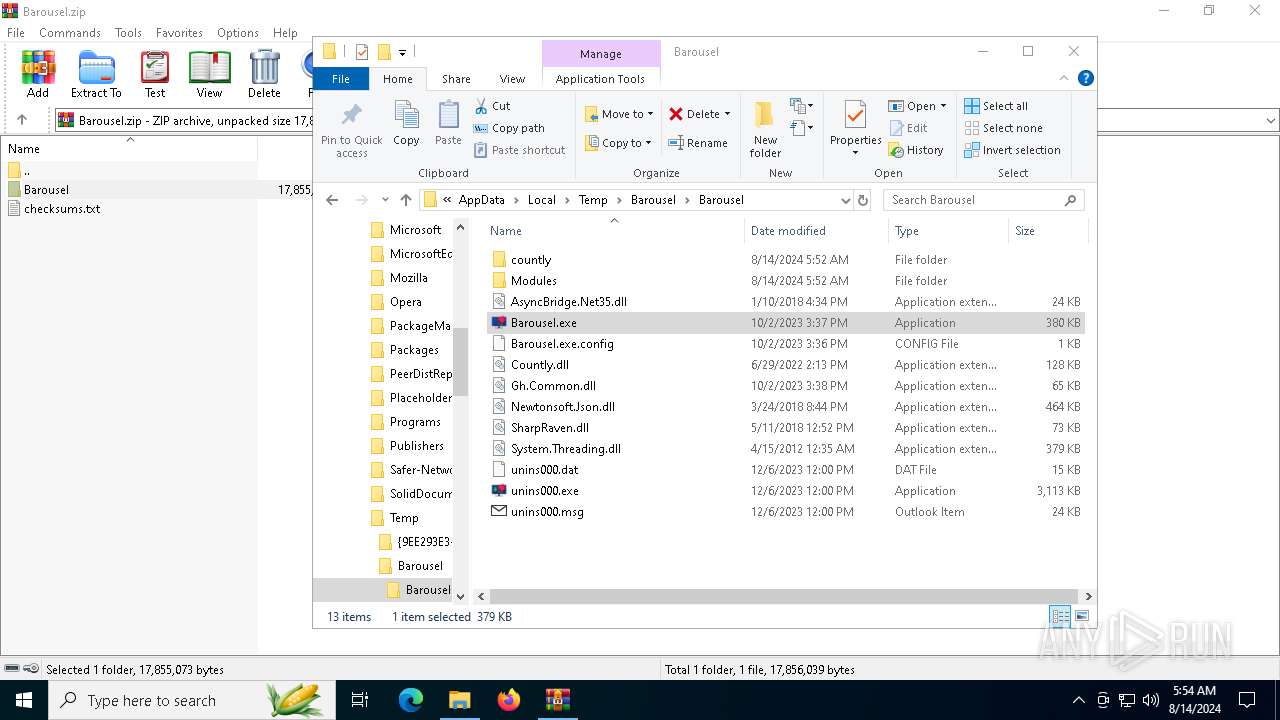
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6432)
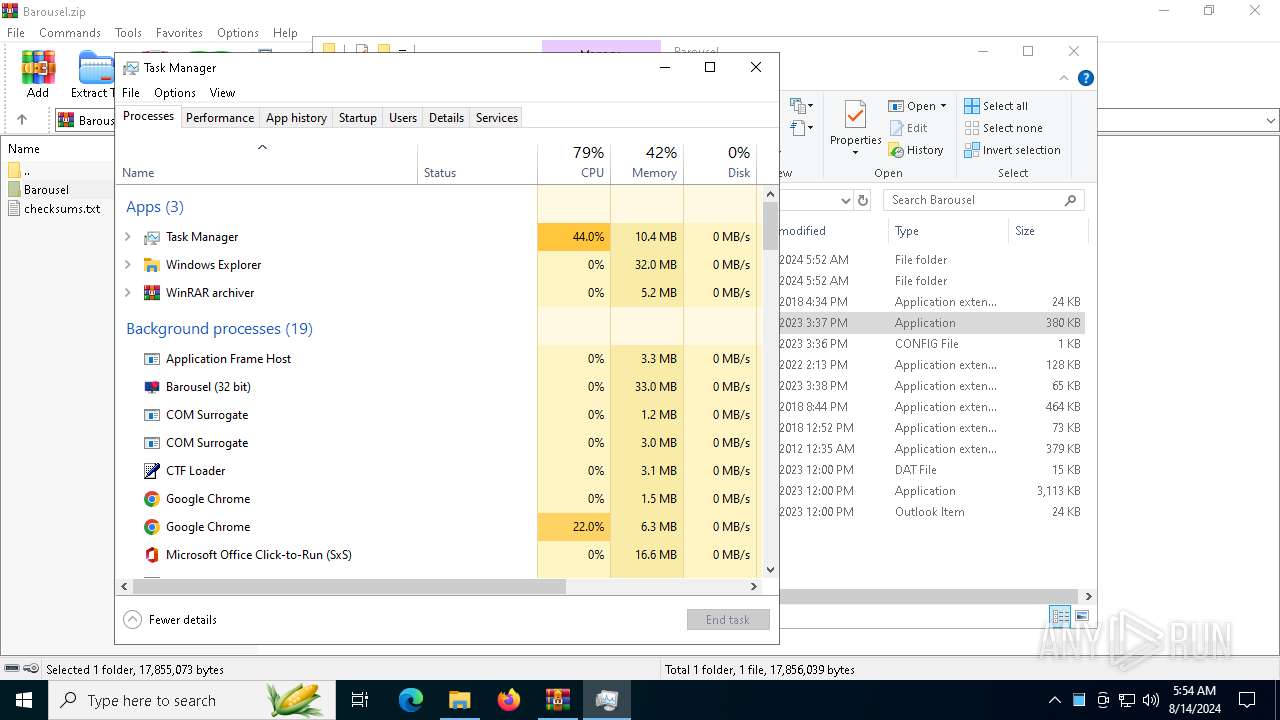
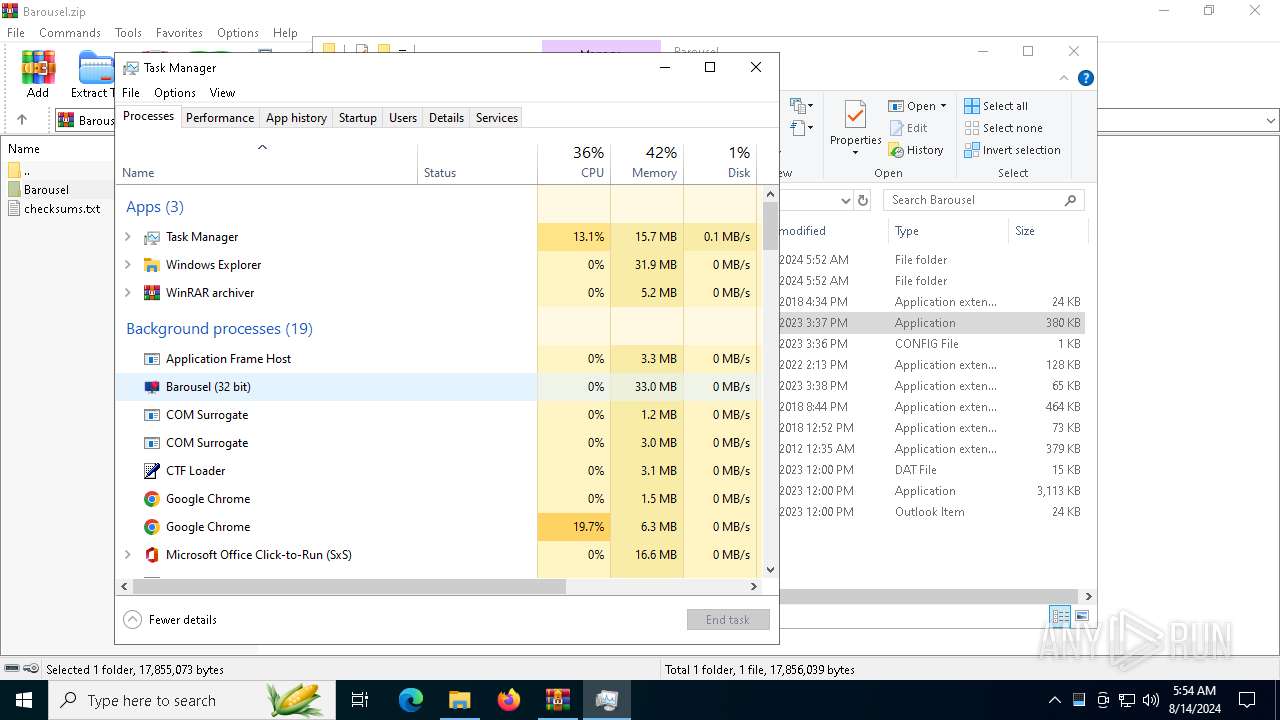
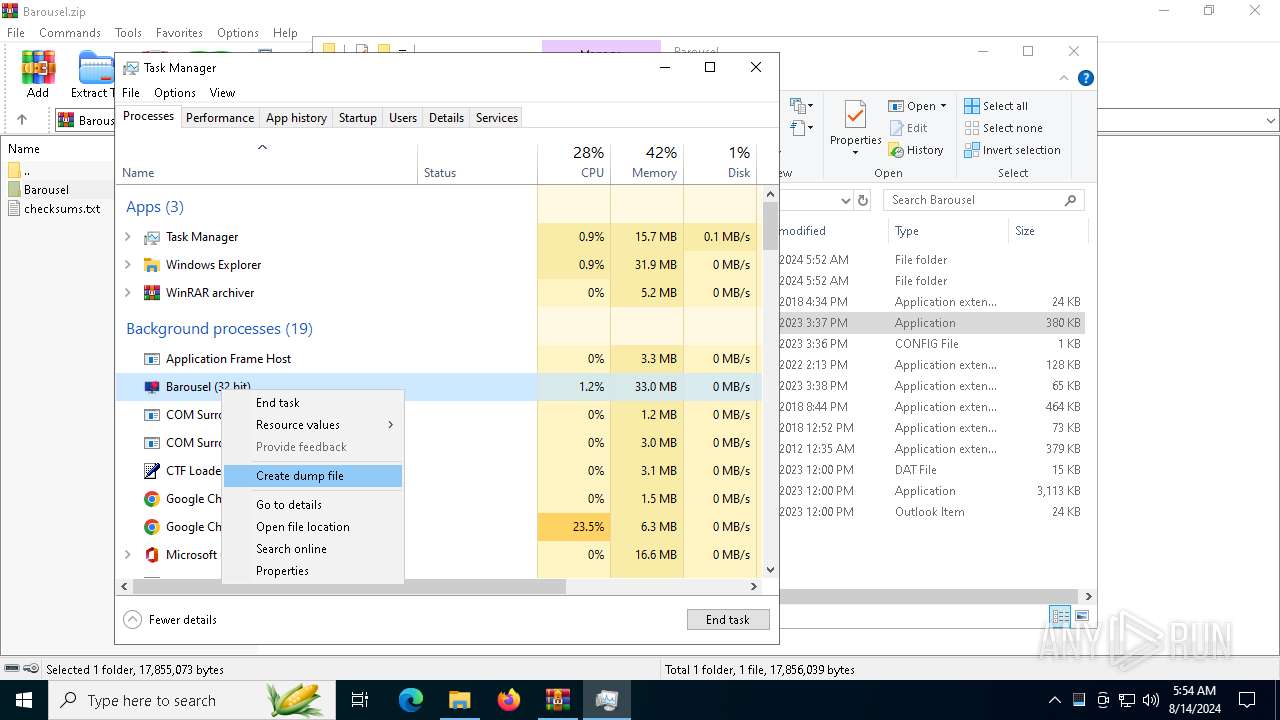
Manual execution by a user
- Barousel.exe (PID: 2384)
- Taskmgr.exe (PID: 7888)
- Taskmgr.exe (PID: 4168)
Checks supported languages
- Barousel.exe (PID: 2384)
- ay3jswp4.exe (PID: 7328)
- ay3jswp4.tmp (PID: 7320)
- Barousel.exe (PID: 7420)
Reads the machine GUID from the registry
- Barousel.exe (PID: 2384)
- ay3jswp4.tmp (PID: 7320)
- Barousel.exe (PID: 7420)
Reads the software policy settings
- Barousel.exe (PID: 2384)
- ay3jswp4.tmp (PID: 7320)
- Barousel.exe (PID: 7420)
Reads the computer name
- Barousel.exe (PID: 2384)
- ay3jswp4.tmp (PID: 7320)
- Barousel.exe (PID: 7420)
Checks proxy server information
- Barousel.exe (PID: 2384)
Creates files or folders in the user directory
- Barousel.exe (PID: 2384)
- ay3jswp4.tmp (PID: 7320)
Reads Environment values
- Barousel.exe (PID: 2384)
- ay3jswp4.exe (PID: 7328)
- ay3jswp4.tmp (PID: 7320)
- Barousel.exe (PID: 7420)
Reads the time zone
- Barousel.exe (PID: 2384)
Disables trace logs
- Barousel.exe (PID: 2384)
Create files in a temporary directory
- Barousel.exe (PID: 2384)
- ay3jswp4.exe (PID: 7328)
- ay3jswp4.tmp (PID: 7320)
Application launched itself
- chrome.exe (PID: 4592)
- msedge.exe (PID: 7184)
Process checks Internet Explorer phishing filters
- Barousel.exe (PID: 2384)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7888)
Creates a software uninstall entry
- ay3jswp4.tmp (PID: 7320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:01:10 16:34:50 |
| ZipCRC: | 0x6643d01c |
| ZipCompressedSize: | 11090 |
| ZipUncompressedSize: | 24064 |
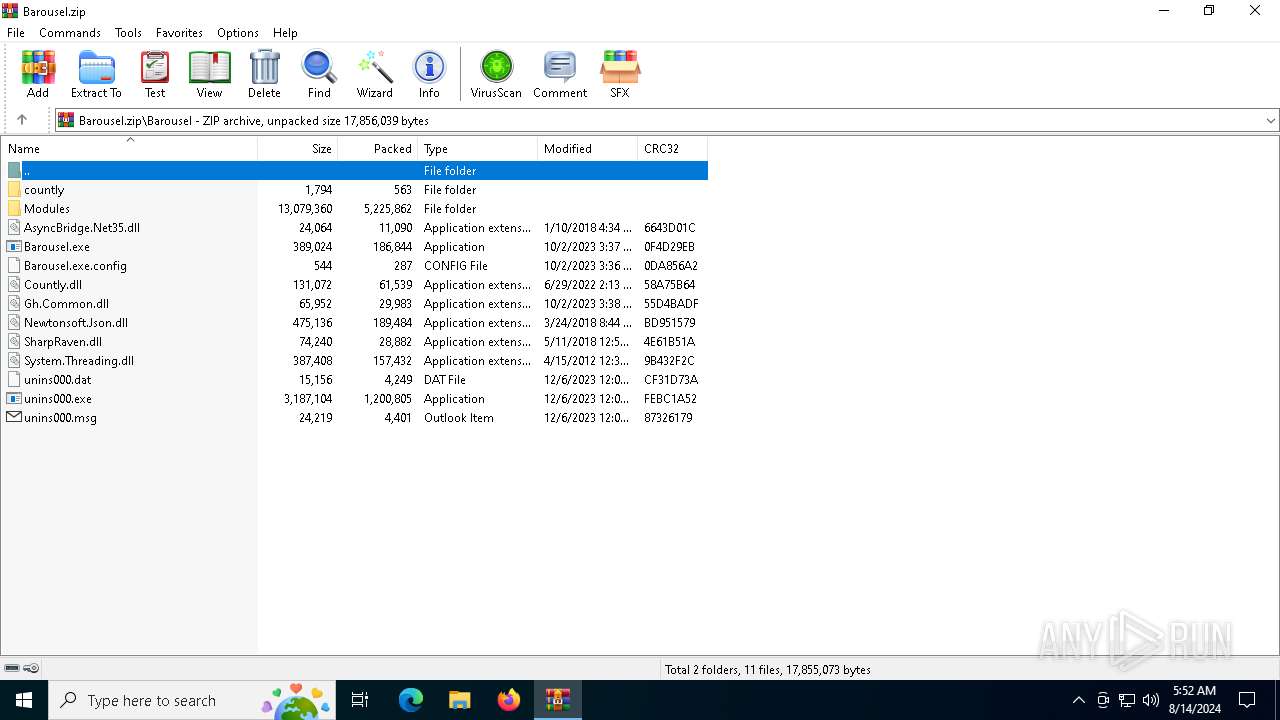
| ZipFileName: | Barousel/AsyncBridge.Net35.dll |
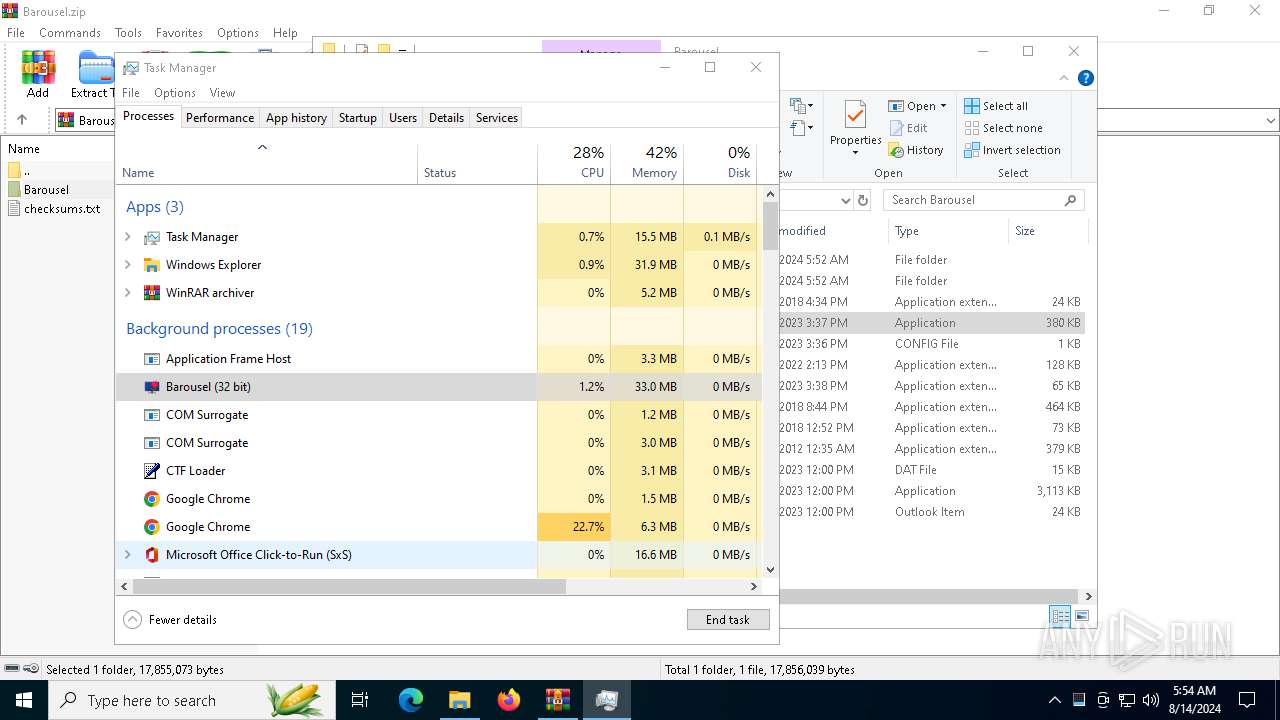
Total processes
162
Monitored processes
24
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-sandbox --ignore-certificate-errors --mute-audio --ignore-certificate-errors --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\chrome-runner3834444515" --no-appcompat-clear --mojo-platform-channel-handle=2192 --field-trial-handle=1832,i,16306591803918962453,15946314633620893135,262144 --enable-features=NetworkService,NetworkServiceInProcess --disable-features=AutofillServerCommunication,InterestFeedContentSuggestions,MediaRouter,PaintHolding,Translate --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
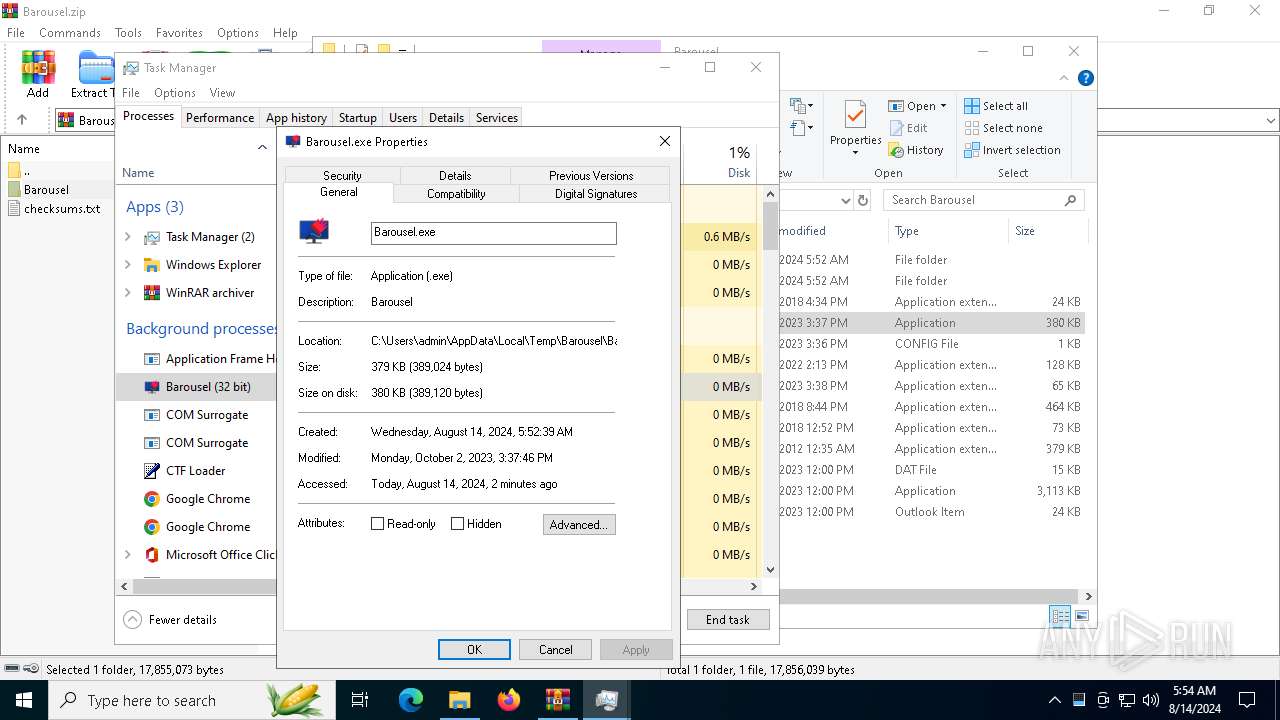
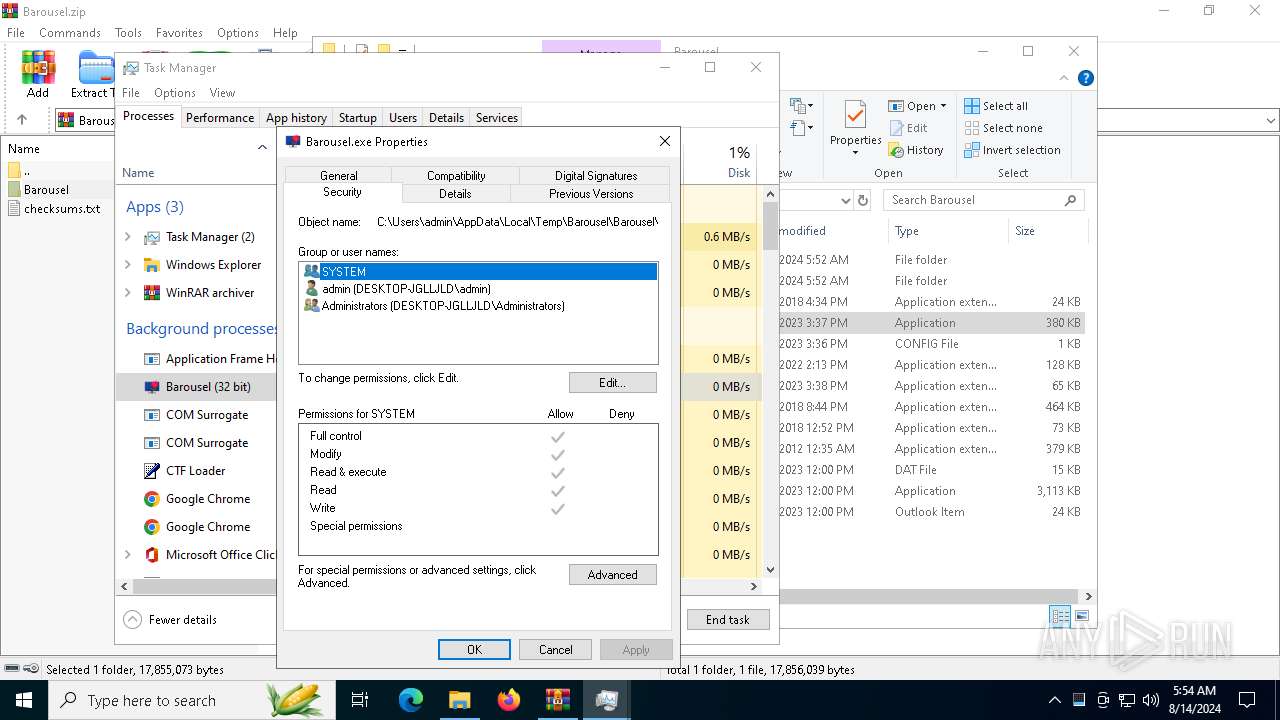
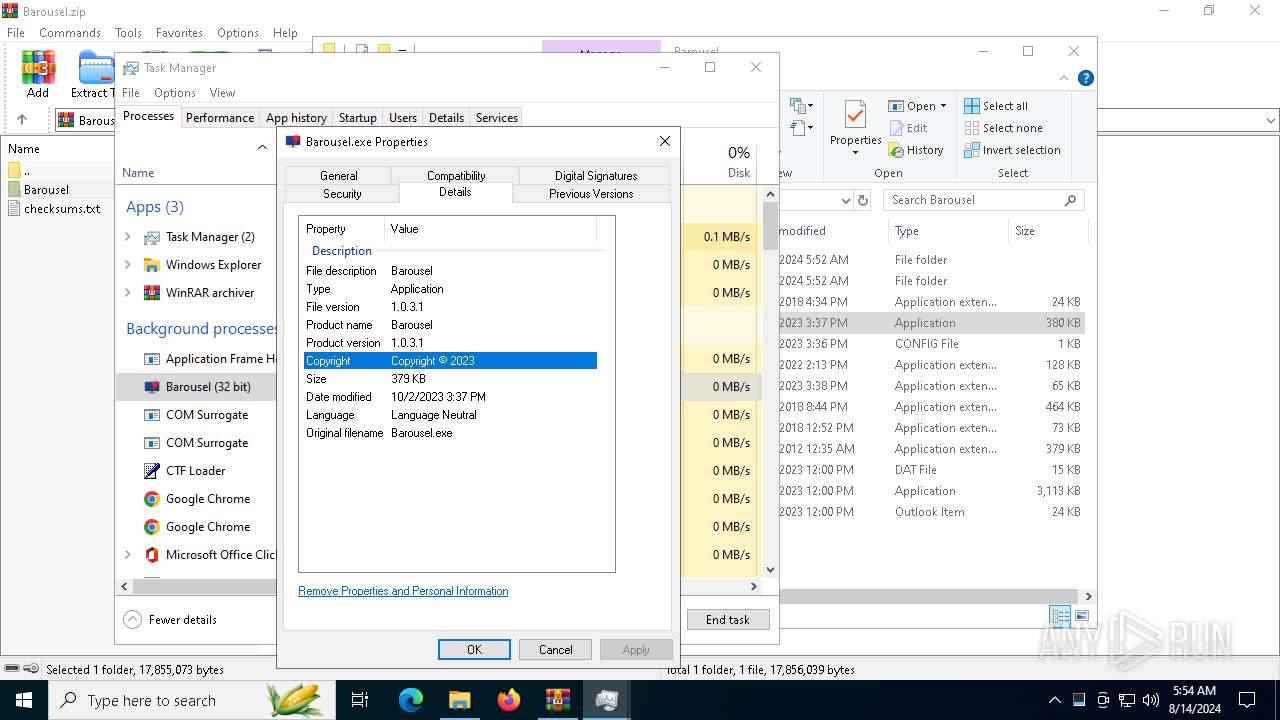
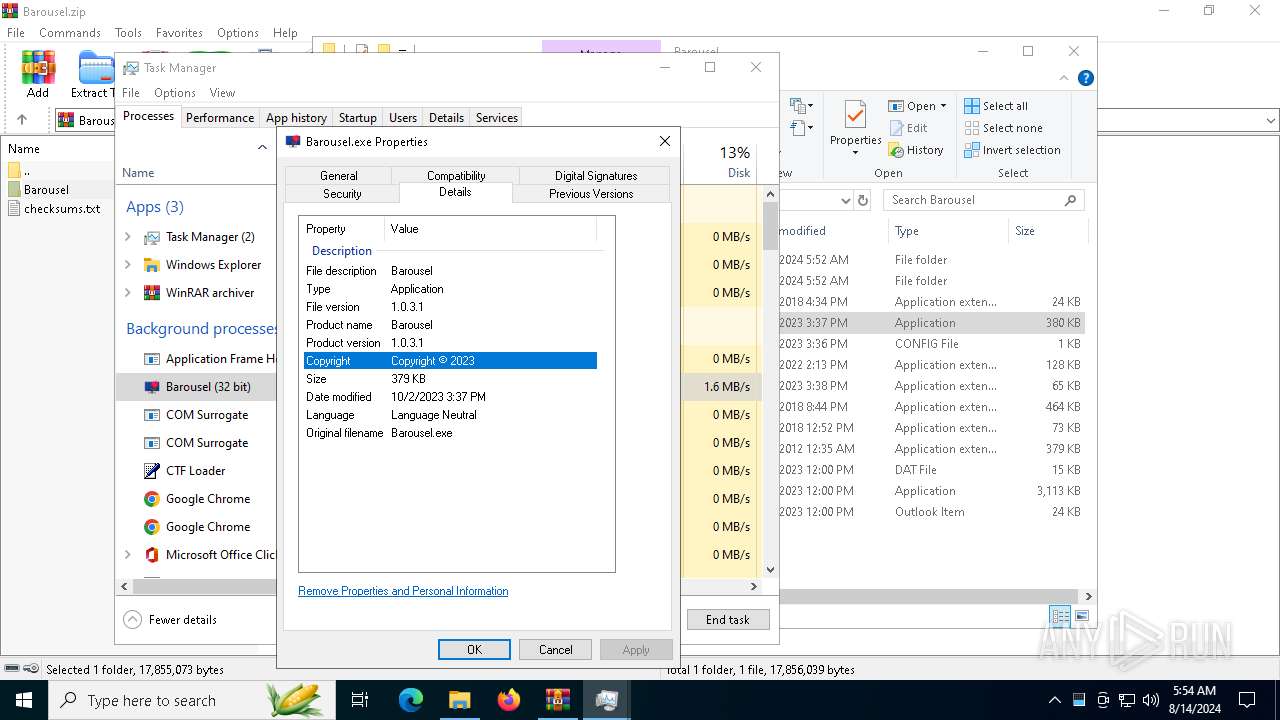
| 2384 | "C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\Barousel.exe" | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\Barousel.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Barousel Version: 1.0.3.1 Modules
| |||||||||||||||
| 4168 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disable-component-extensions-with-background-pages= --no-first-run= --disable-backgrounding-occluded-windows= --remote-debugging-host=127.0.0.1 --disable-extensions= --disable-component-update= --headless=new --disable-hang-monitor= --disable-domain-reliability= --no-pings= --disable-setuid-sandbox= --disable-background-timer-throttling= --metrics-recording-only= --enable-features=NetworkService,NetworkServiceInProcess --ignore-certificate-errors= --temp-profile= --window-size=1280,800 --disable-features=MediaRouter,Translate,InterestFeedContentSuggestions,AutofillServerCommunication --disable-infobars= --no-sandbox= --disable-dev-shm-usage= --disable-renderer-backgrounding= --mute-audio= --disable-fre= --disable-breakpad= --no-default-browser-check= --disable-background-networking= --no-zygote= --disable-sync= --no-service-autorun= --user-data-dir=C:\Users\admin\AppData\Local\Temp\chrome-runner3834444515 --ignore-certificate-errors-skip-list= --noerrdialogs= --remote-debugging-port=0 | C:\Program Files\Google\Chrome\Application\chrome.exe | Barousel.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\chrome-runner3834444515 /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\chrome-runner3834444515\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x224,0x228,0x22c,0x200,0x230,0x7fffd418dc40,0x7fffd418dc4c,0x7fffd418dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-sandbox --ignore-certificate-errors --mute-audio --ignore-certificate-errors --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\chrome-runner3834444515" --no-appcompat-clear --mojo-platform-channel-handle=1968 --field-trial-handle=1832,i,16306591803918962453,15946314633620893135,262144 --enable-features=NetworkService,NetworkServiceInProcess --disable-features=AutofillServerCommunication,InterestFeedContentSuggestions,MediaRouter,PaintHolding,Translate --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 6264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-sandbox --disable-breakpad --headless=new --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\chrome-runner3834444515" --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1800 --field-trial-handle=1832,i,16306591803918962453,15946314633620893135,262144 --enable-features=NetworkService,NetworkServiceInProcess --disable-features=AutofillServerCommunication,InterestFeedContentSuggestions,MediaRouter,PaintHolding,Translate --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
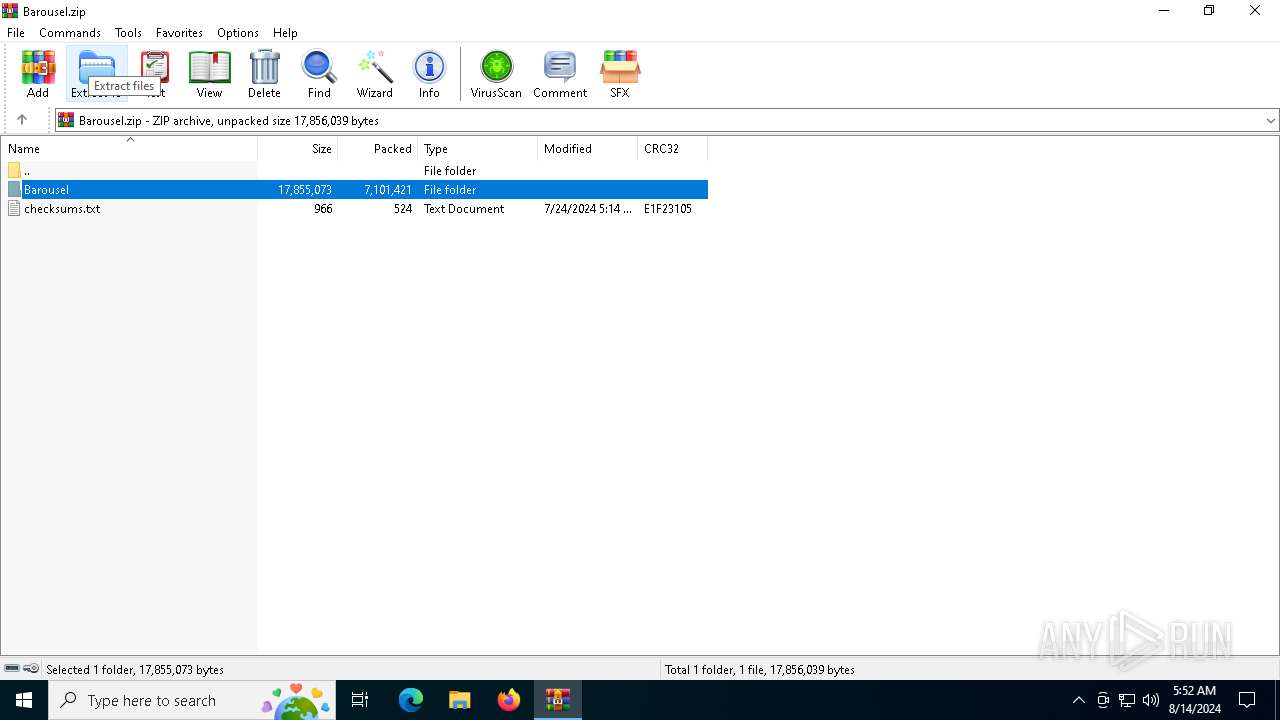
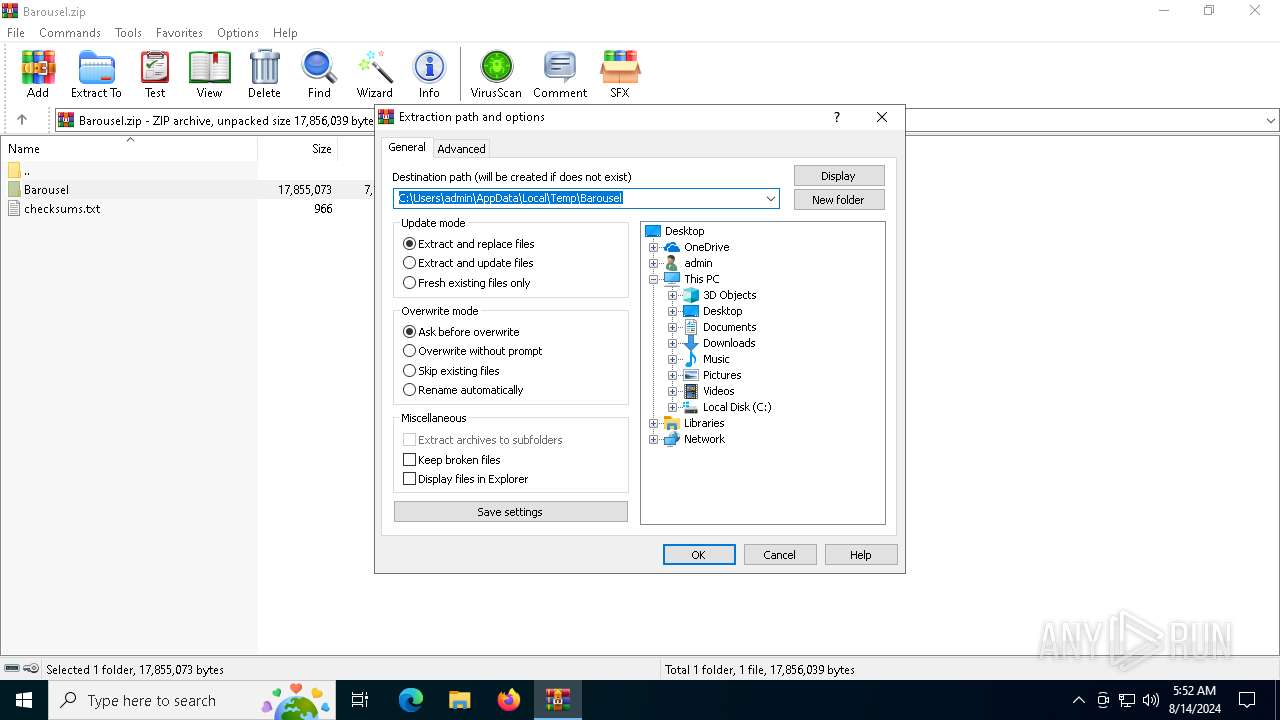
| 6432 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Barousel.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\chrome-runner3834444515" --no-appcompat-clear --no-sandbox --disable-background-timer-throttling --disable-breakpad --no-zygote --remote-debugging-port=0 --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2820 --field-trial-handle=1832,i,16306591803918962453,15946314633620893135,262144 --enable-features=NetworkService,NetworkServiceInProcess --disable-features=AutofillServerCommunication,InterestFeedContentSuggestions,MediaRouter,PaintHolding,Translate --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
29 507
Read events
29 399
Write events
96
Delete events
12
Modification events
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\Root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-150 |
Value: Outlook Item | |||
| (PID) Process: | (6432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Barousel | |||
| (PID) Process: | (2384) Barousel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2384) Barousel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Barousel_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2384) Barousel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Barousel_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2384) Barousel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Barousel_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2384) Barousel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Barousel_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2384) Barousel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Barousel_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
31
Suspicious files
128
Text files
69
Unknown types
35
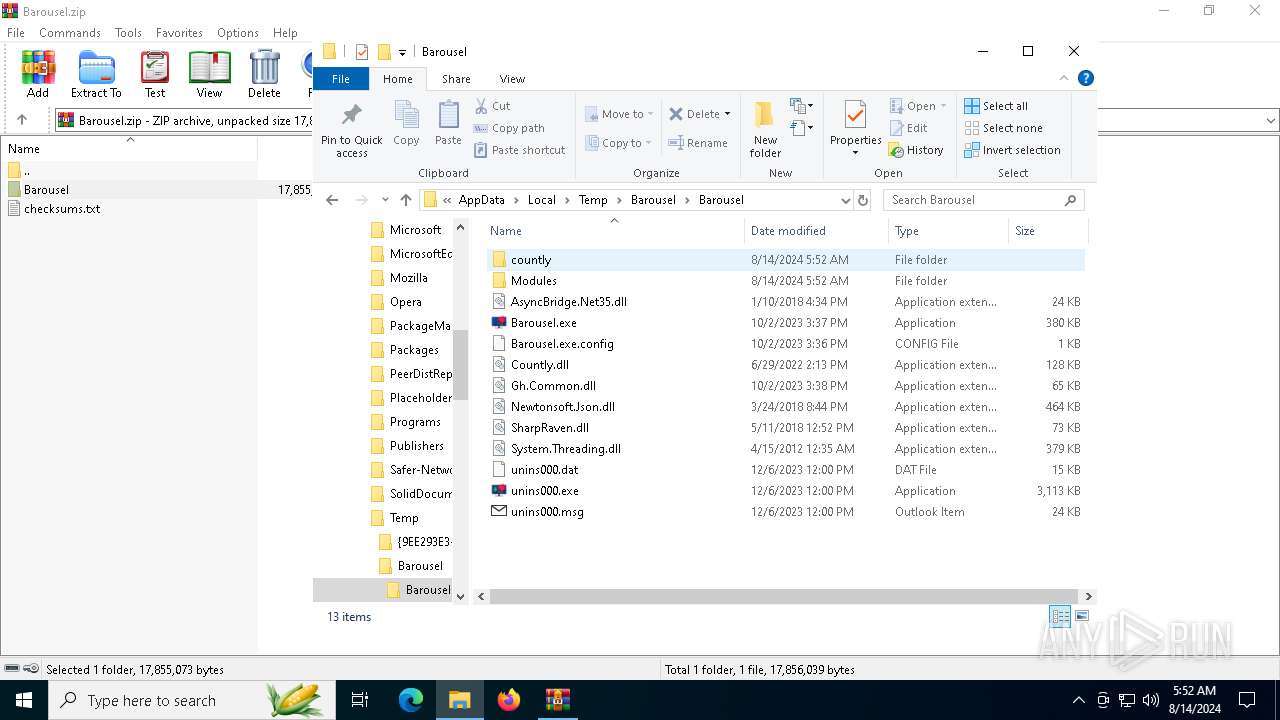
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\Barousel.exe.config | xml | |
MD5:3E8F51C2B6FD8149C32819EADEC0CA72 | SHA256:0E7ACBB755E5161D596D65BC357EC09EE0F82017D15F65504E4EEC47DAC927BD | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\AsyncBridge.Net35.dll | executable | |
MD5:35CBDBE6987B9951D3467DDA2F318F3C | SHA256:E4915F18FD6713EE84F27A06ED1F6F555CDBEBE1522792CF4B4961664550CF83 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\System.Threading.dll | executable | |
MD5:F5EE17938D7C545BF62AD955803661C7 | SHA256:8A791AF9E3861E231662B657098A823B21A084CBB6A4901D6CCF363405849A78 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\Countly.dll | executable | |
MD5:304E0F414C764D7A5C2647D721646E13 | SHA256:86CB999EF8B3D20CB81B69FF03580CC6F3D2CA6CC699AB0810FAB8CAC0E7397E | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\unins000.dat | dat | |
MD5:C919A2A33EAAFB2784D19BBCBF185D2B | SHA256:E232C4A3D9A4FBDA992E07ECADD0B4D0723BBCFD720F1FCB83CDE1EEF7DA4704 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\Barousel.exe | executable | |
MD5:73759A293FE38620F47D099B625FFFB3 | SHA256:101A9E7F2C376896344DE6A91D1E3DB244EB5A41869F2C19ACDBB0350A941756 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\countly\userdetails.xml | text | |
MD5:14921DEC3E0FAB83B3EC874FE02FC63F | SHA256:FA538BF6C7ED503B921C021892093D52765AC90C037D230A78A93FCBCA471519 | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\Modules\classic.dll | executable | |
MD5:8852CC35102956EB429279F768125172 | SHA256:0978CBACD1245E8FE85D829A2BA0C8923612EA03B377F65857A33BBDB794E9E4 | |||
| 2384 | Barousel.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\18E6B4A57A6BC7EC9B861CDF2D6D0D02_EF52C1EC85F21F31CC0157A5C8803013 | der | |
MD5:FDDD84F970A702C68342E323CF0AD1EA | SHA256:EA9F593BFD0386F8DDA3DF0203FD8A33BF6AD00F7D397BBED0CFF9B792F6C88E | |||
| 6432 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Barousel\Barousel\Modules\novel.dll | executable | |
MD5:A857780E29051BFBDCD69CE82ED99150 | SHA256:D2744E244B510E16CCFB29976885B3AAA91B045368C8638165F1D95C5AE3AD0D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
141
DNS requests
90
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6772 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6812 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2384 | Barousel.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
2384 | Barousel.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
2384 | Barousel.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEQC67%2BPv6JBMH8tNHthn3EeN | unknown | — | — | whitelisted |
2384 | Barousel.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
2384 | Barousel.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/CodeSigPCA.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4788 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5116 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4788 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 184.86.251.9:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1372 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2384 | Barousel.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrome-runner3834444515 directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrome-runner1540823388 directory exists )
|