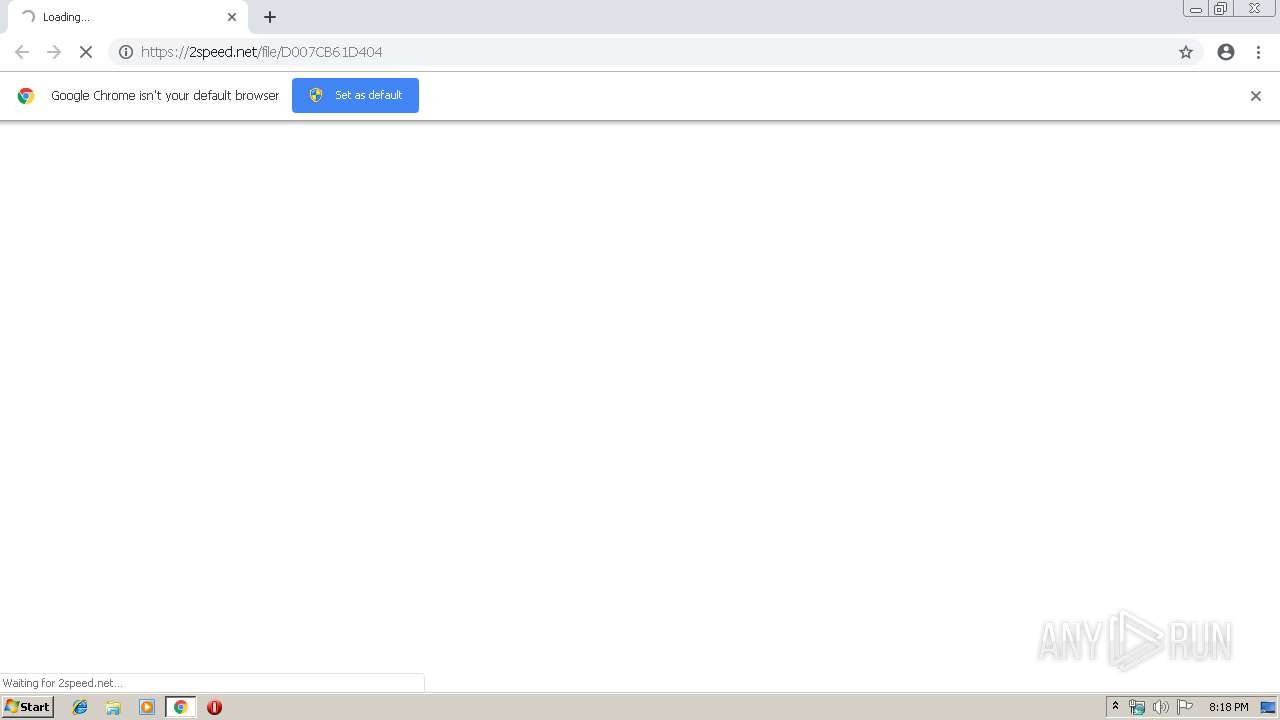
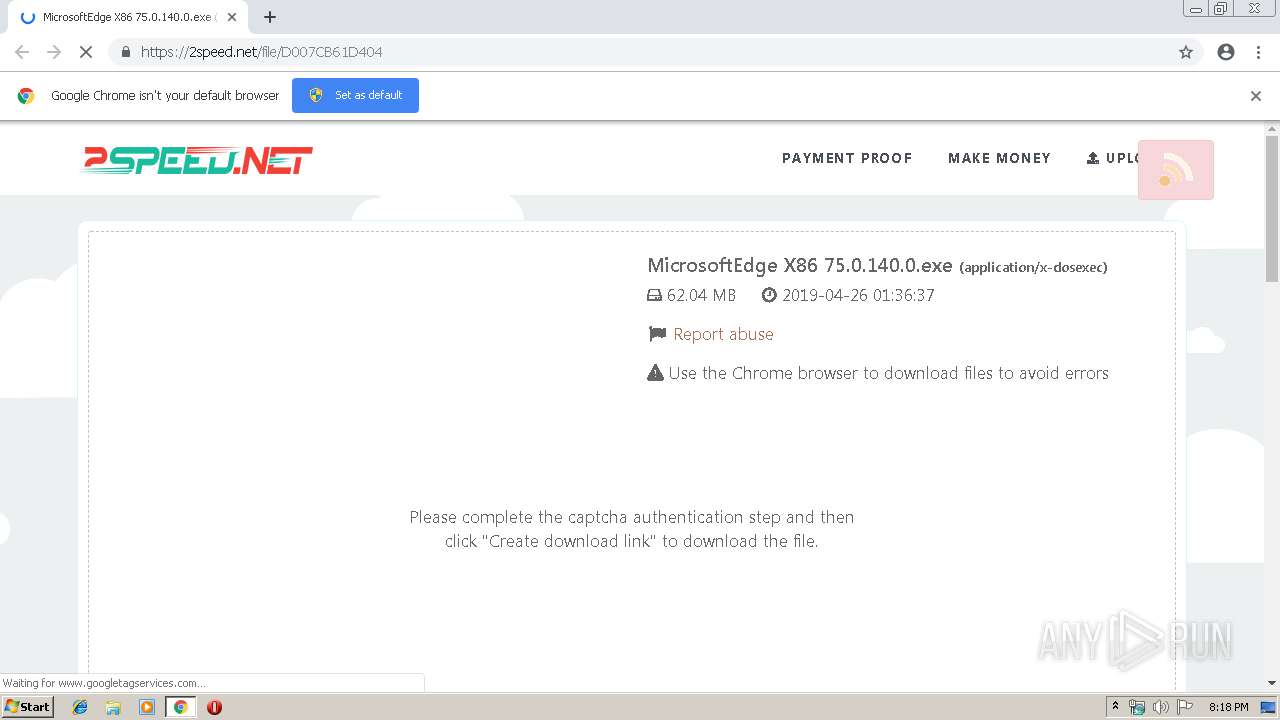
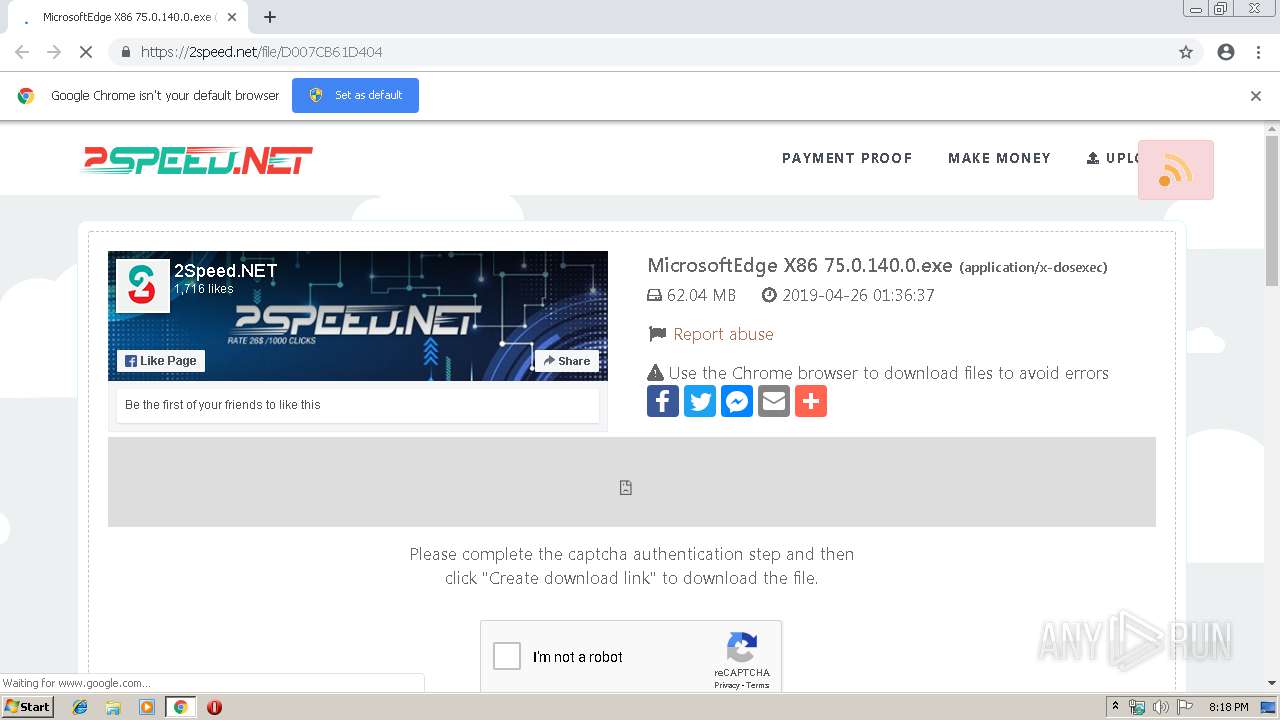
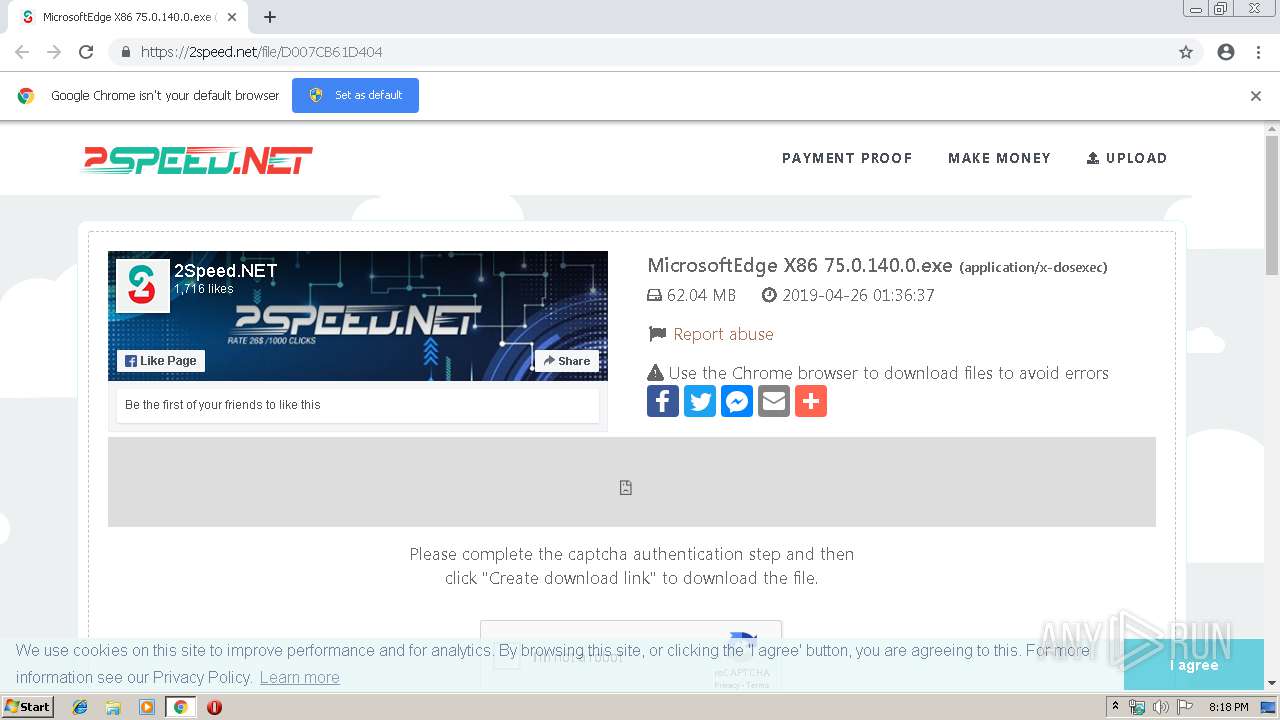
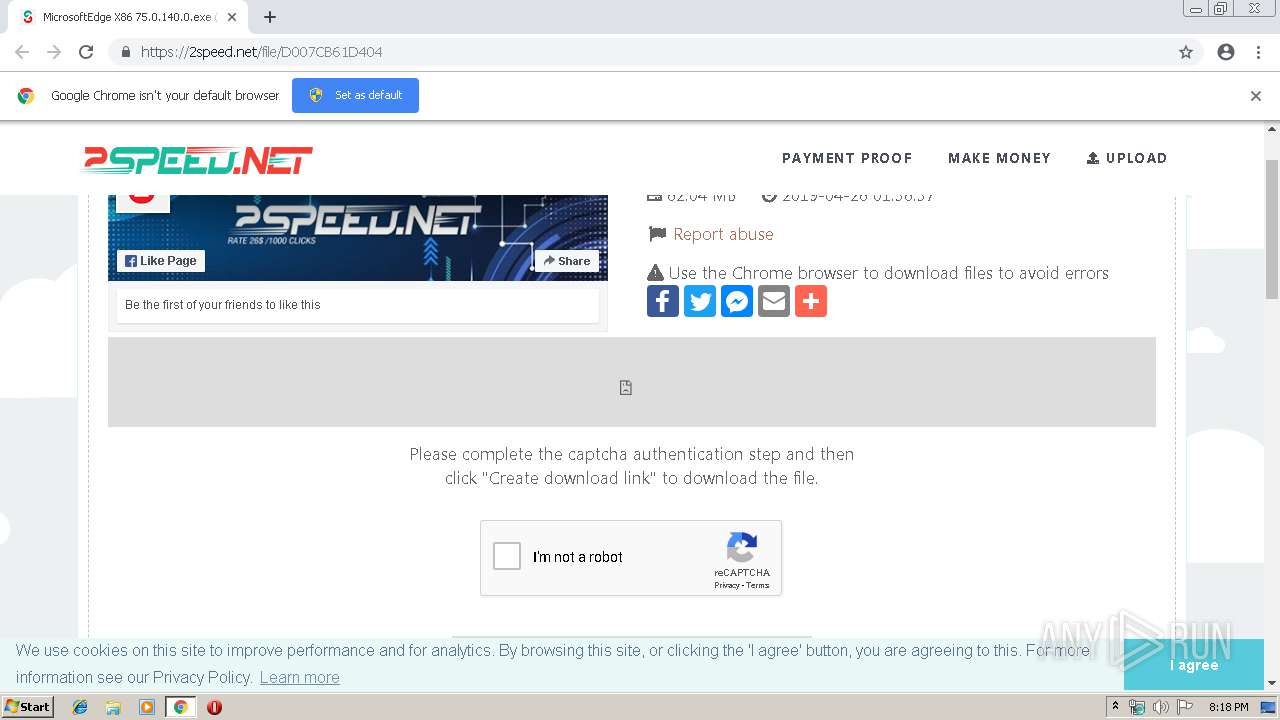
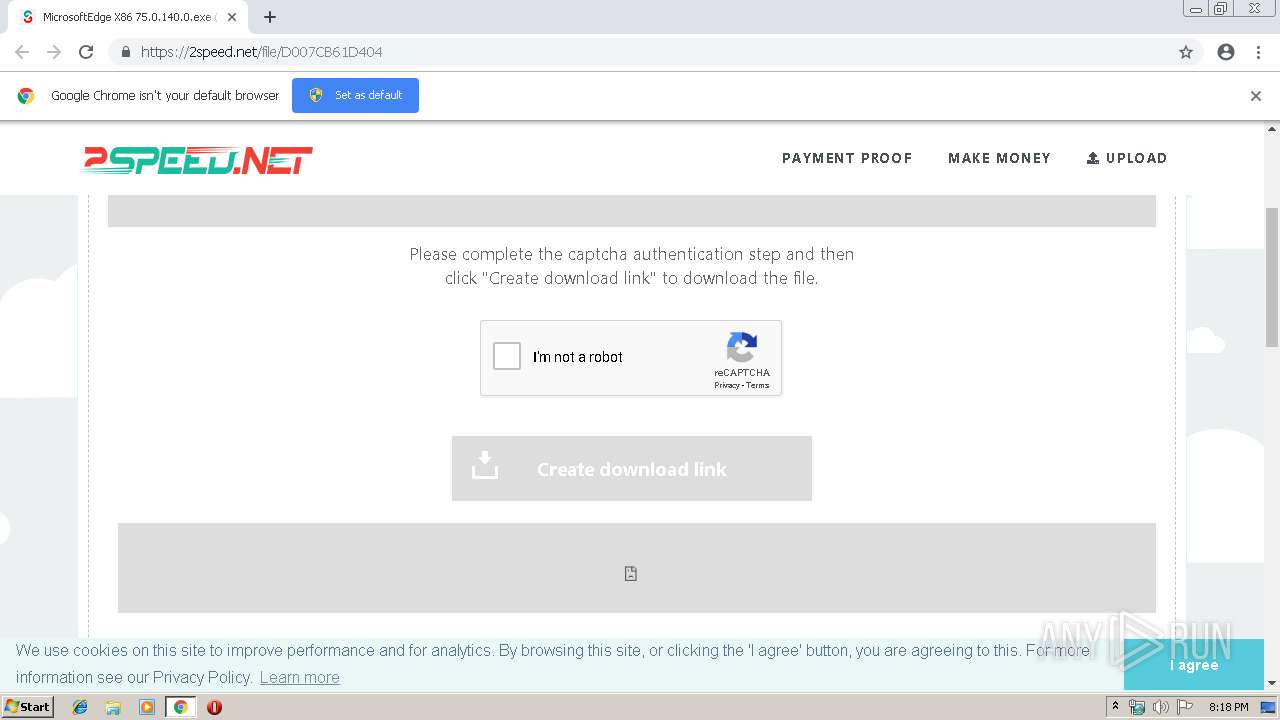
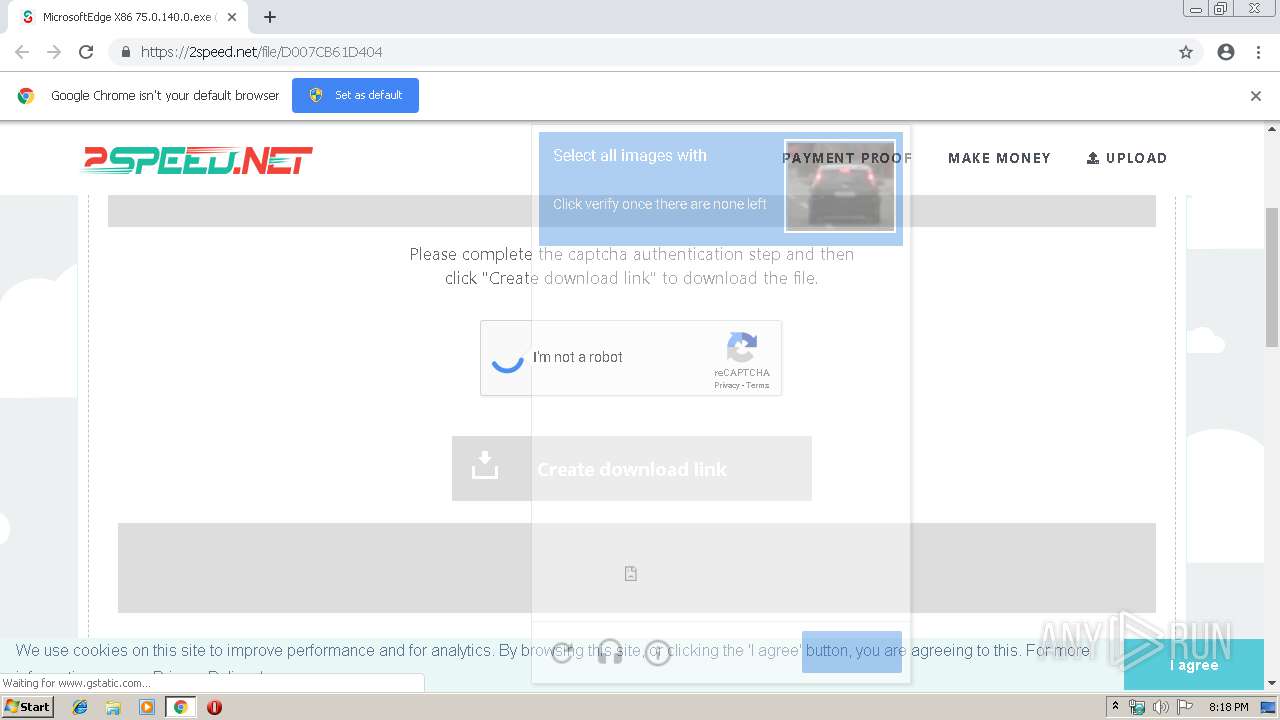
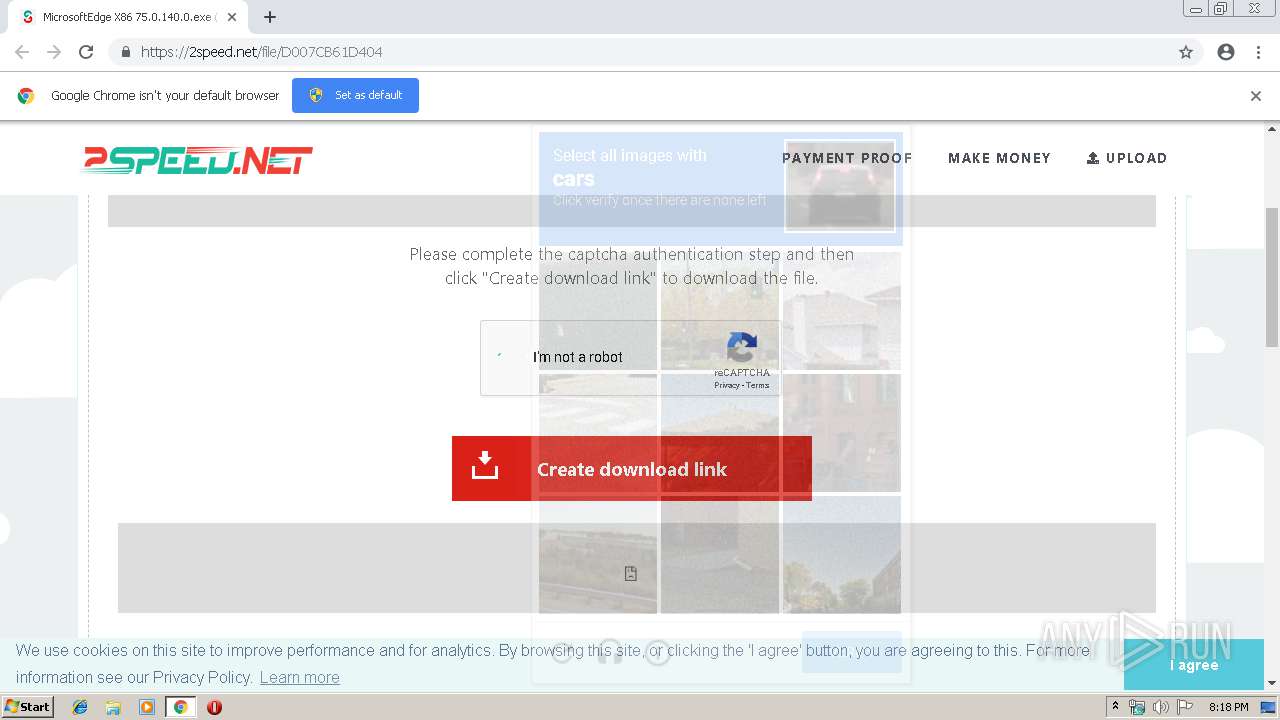
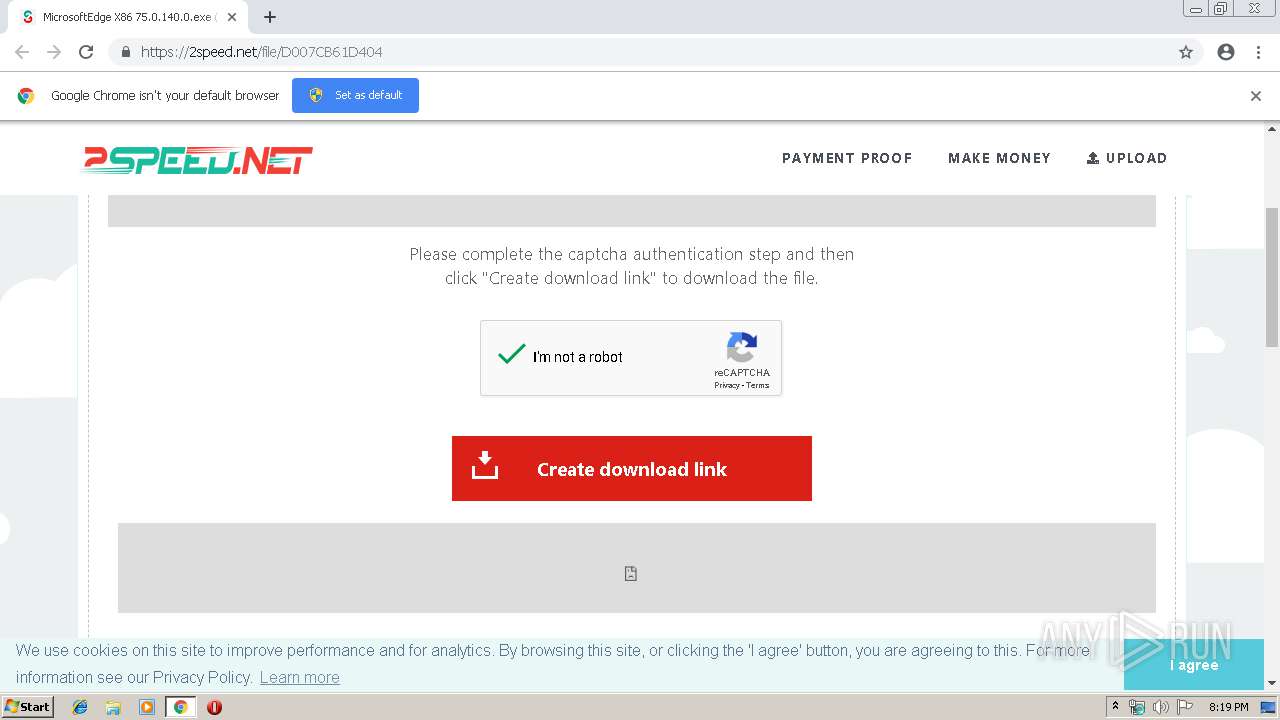
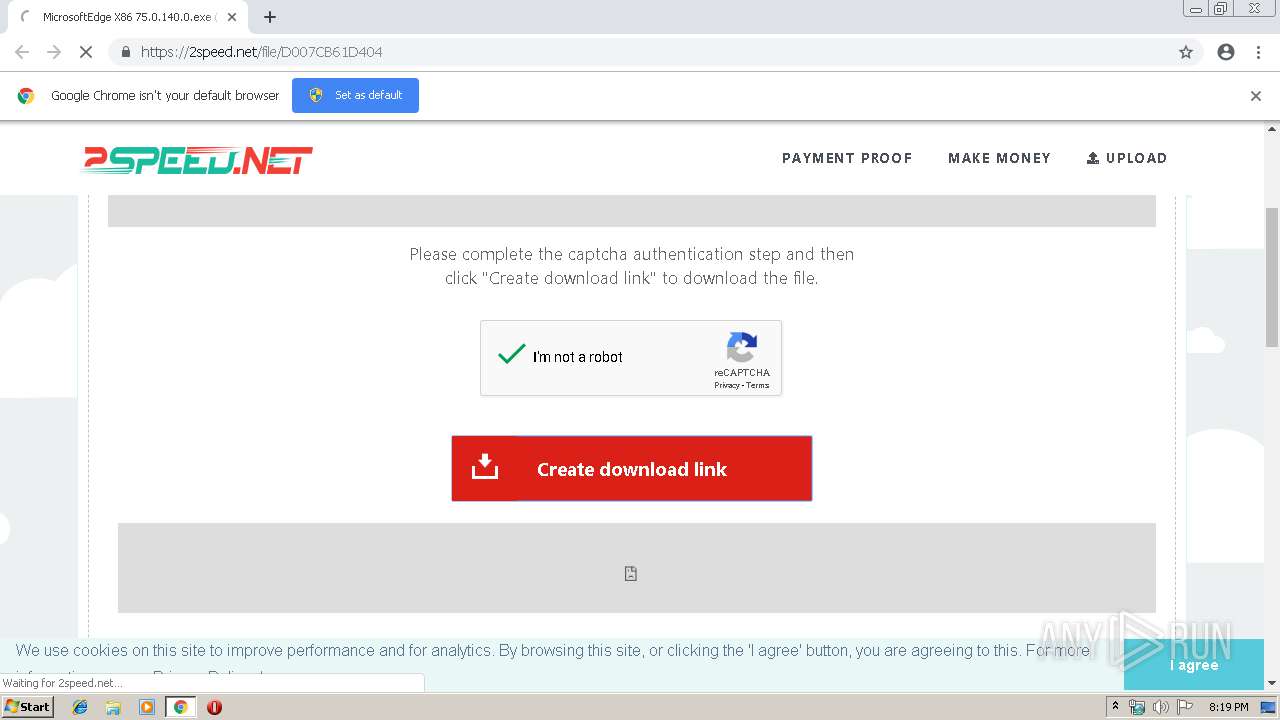
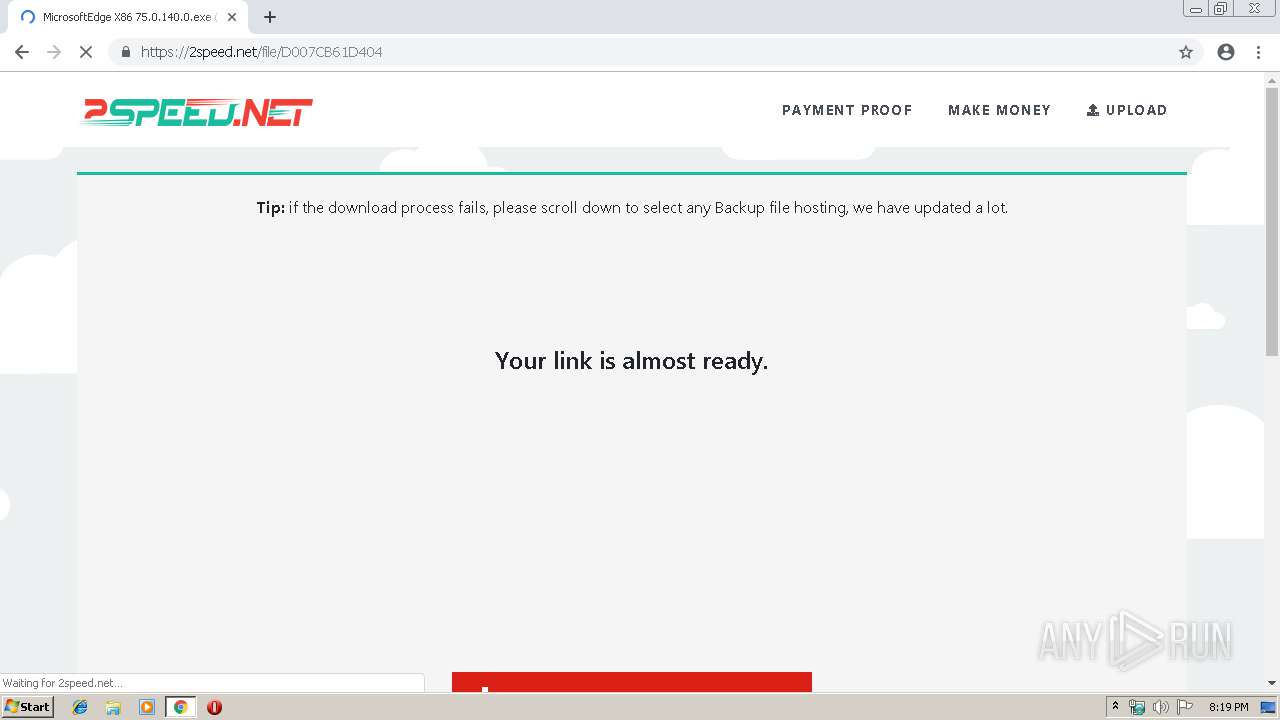
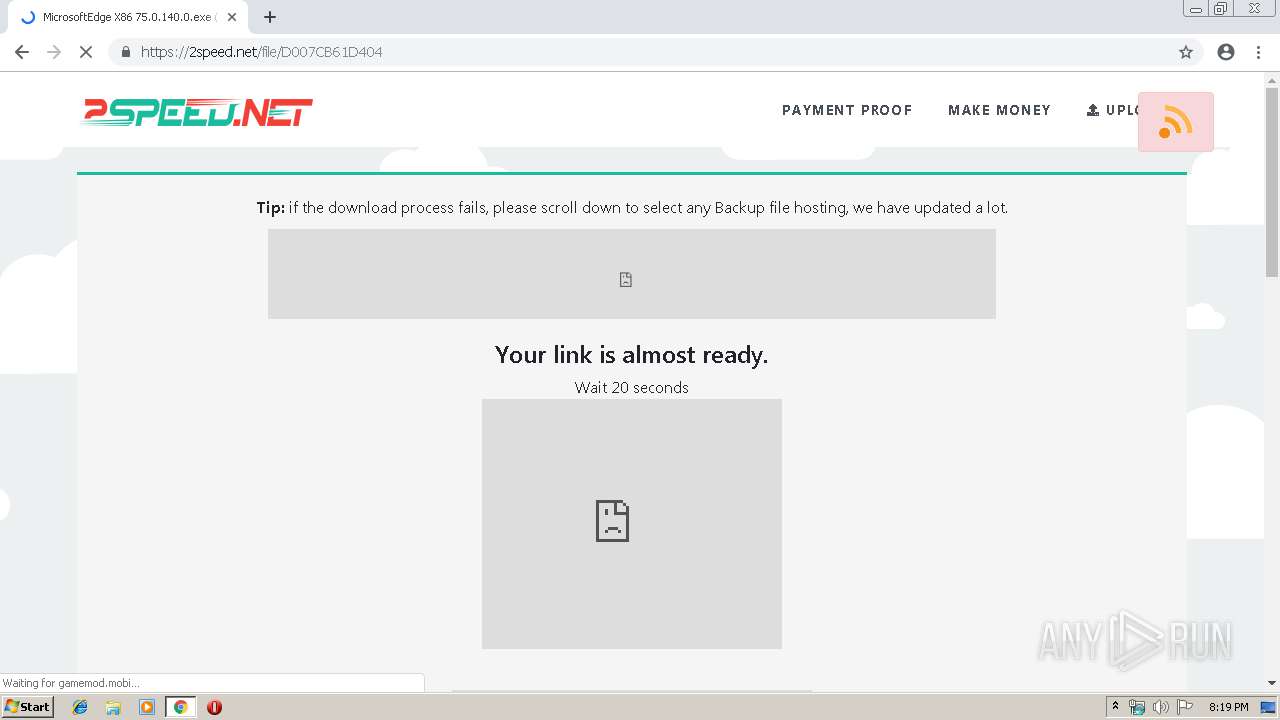
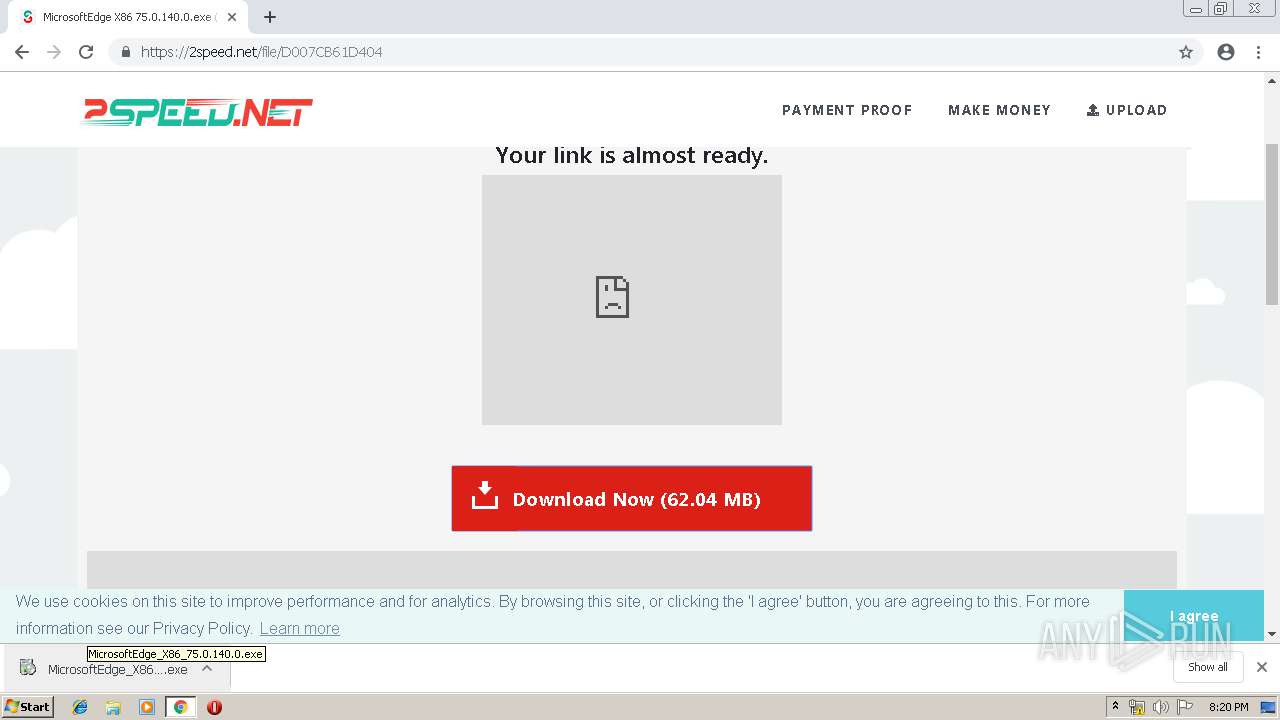
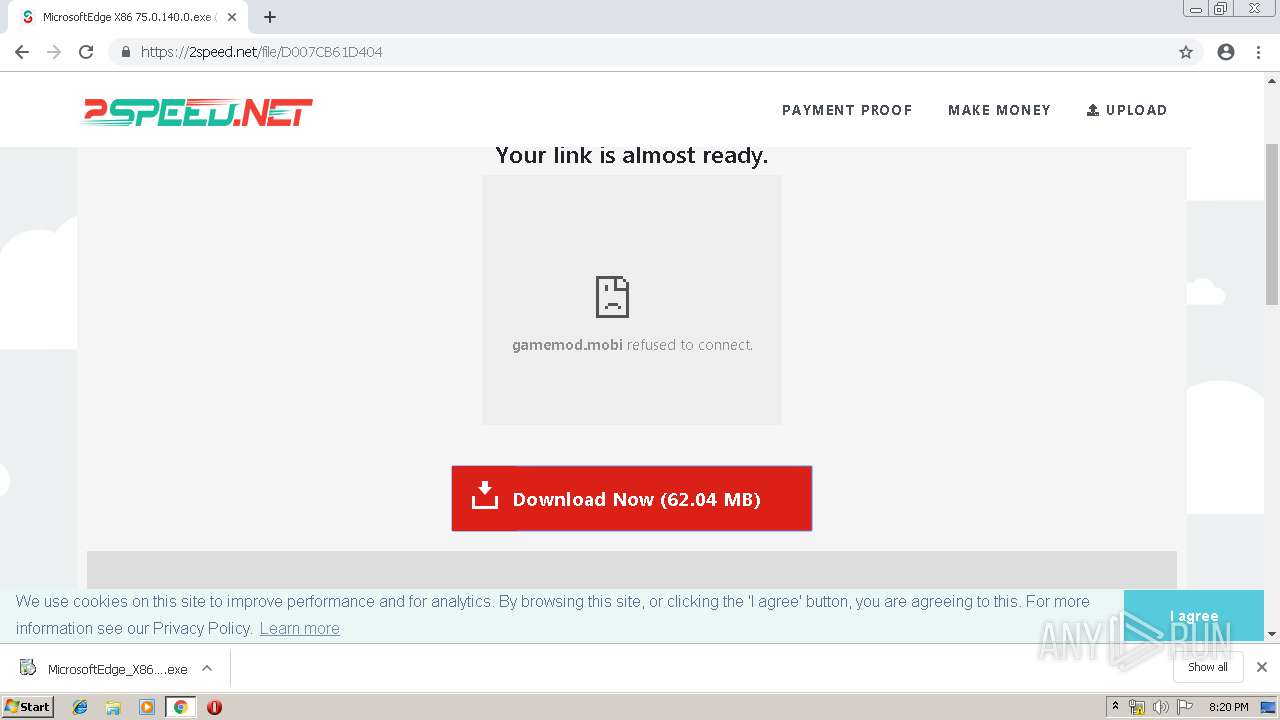
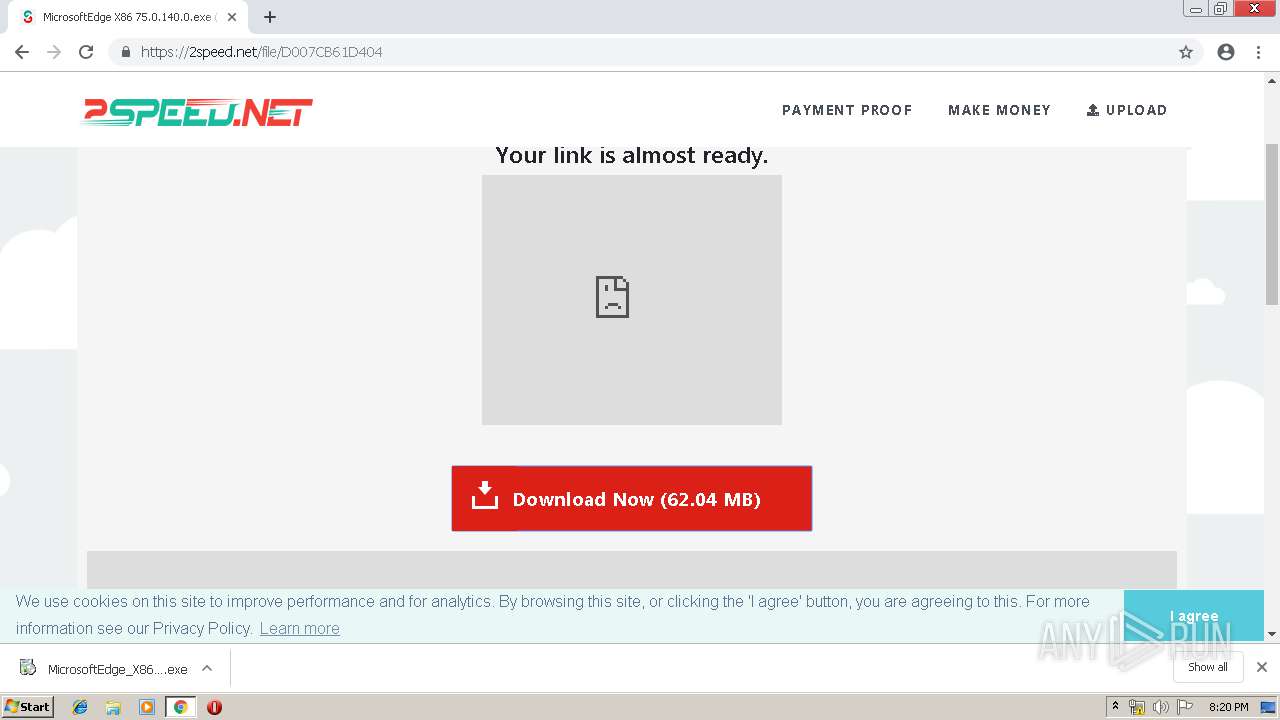
| URL: | https://2speed.net/file/D007CB61D404 |
| Full analysis: | https://app.any.run/tasks/12214f94-d0db-4c35-9c74-8f71d6ce3bd0 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 19:18:23 |
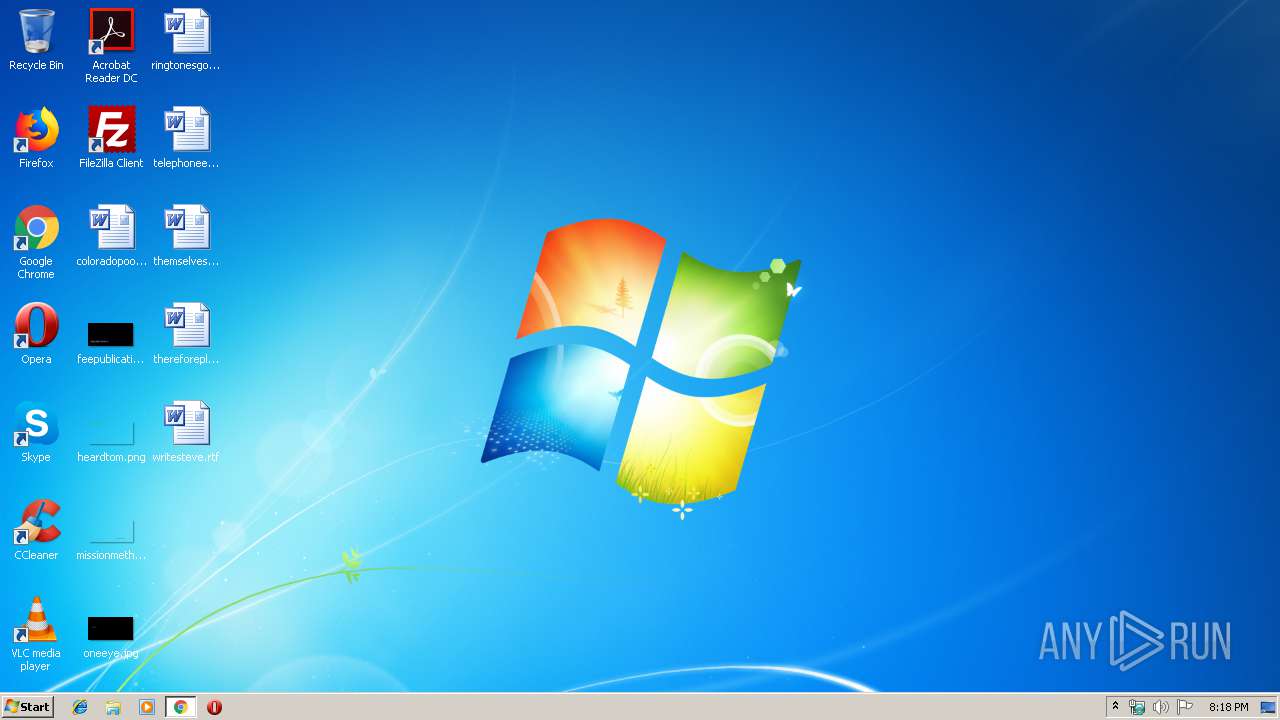
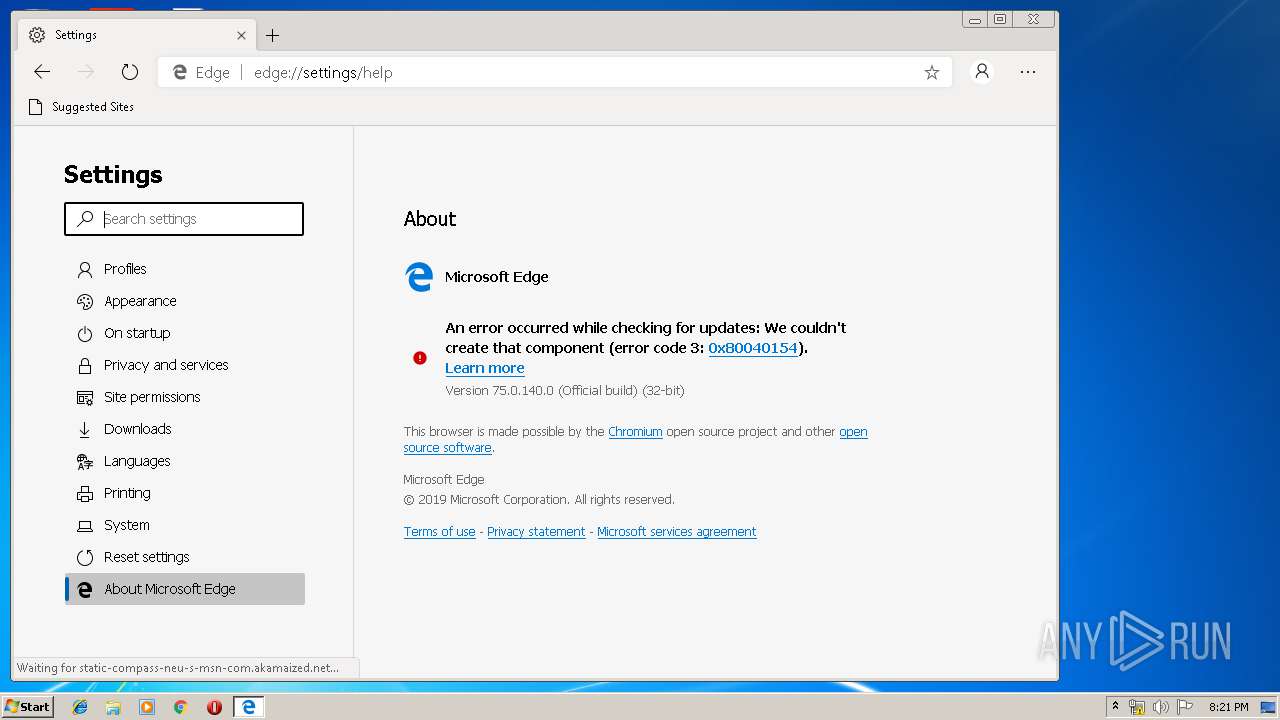
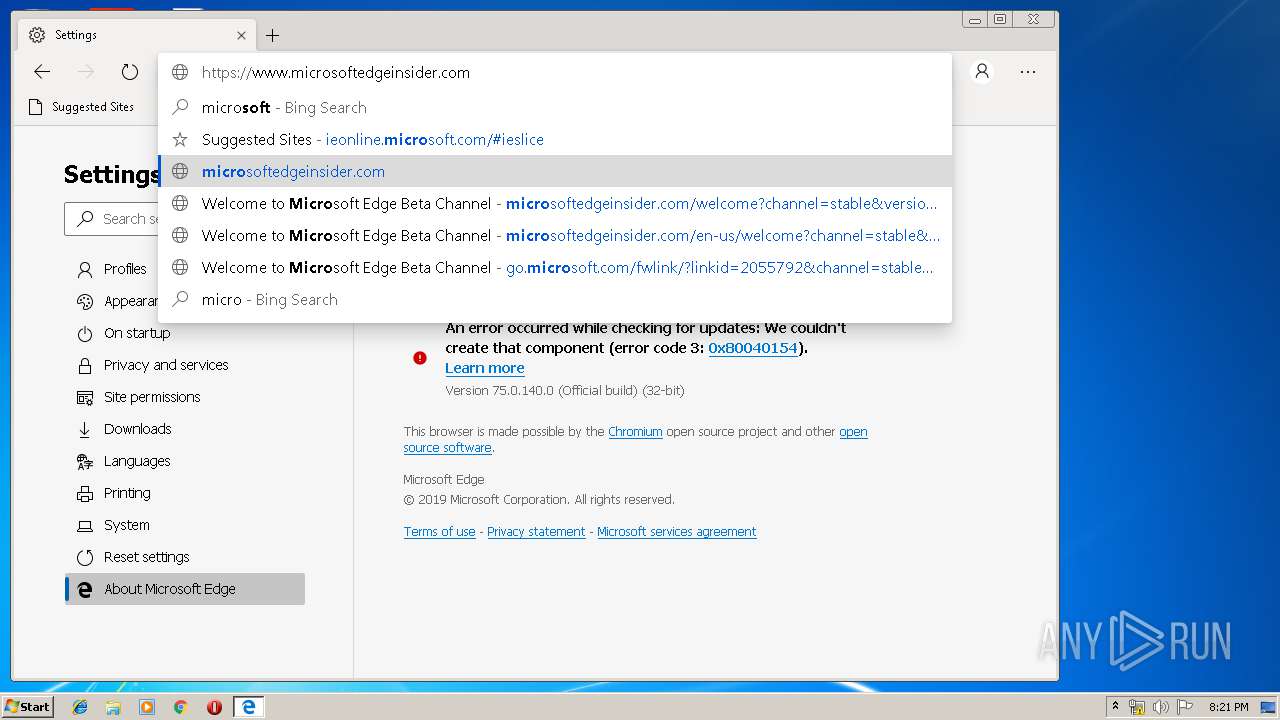
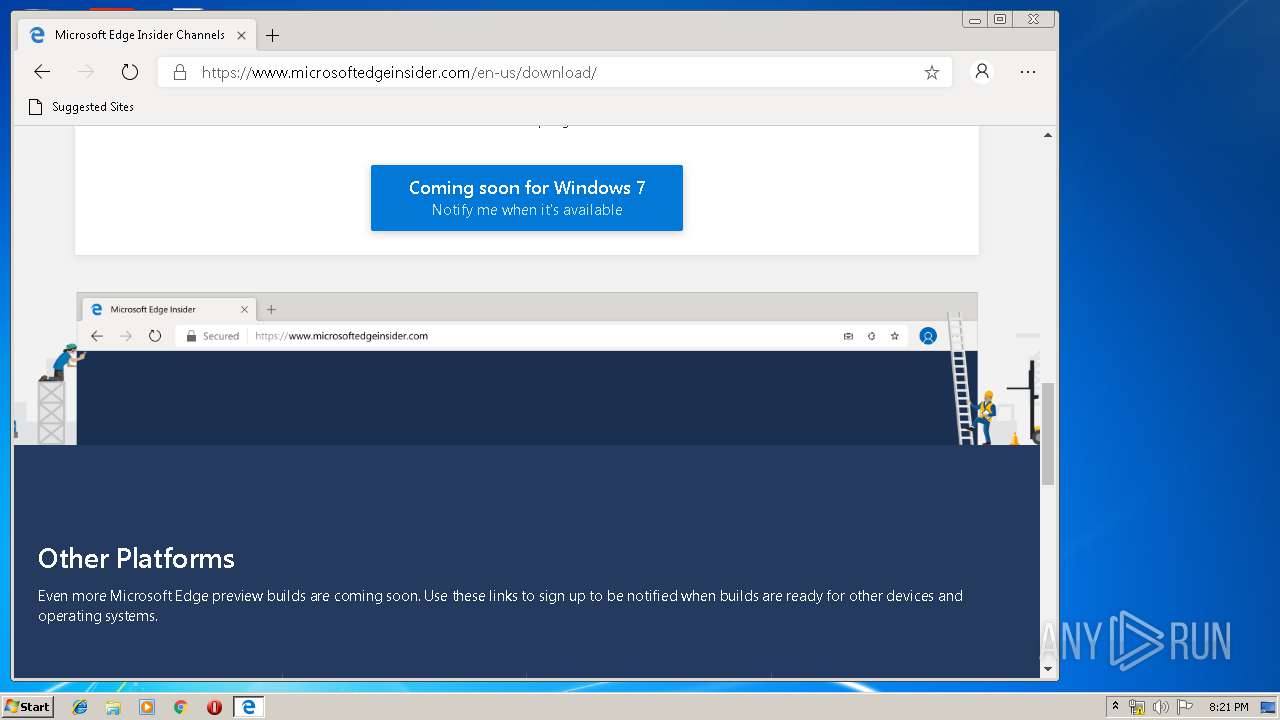
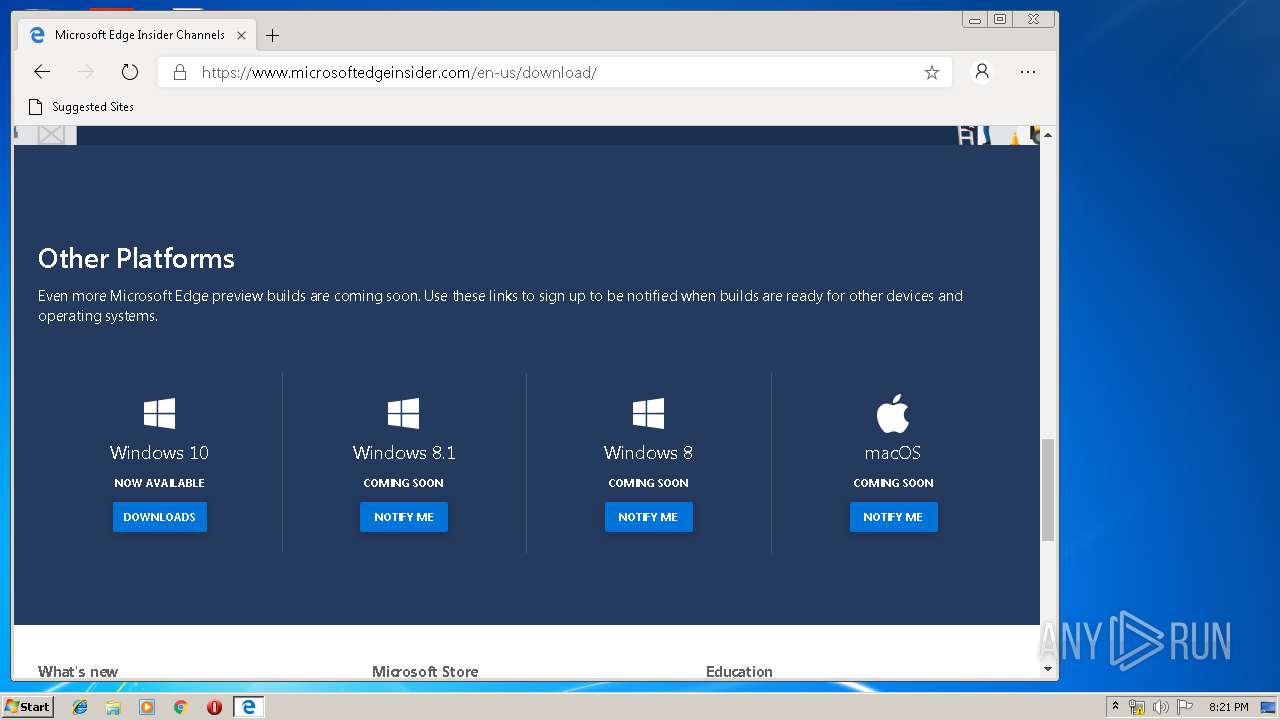
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1A3AB4AB5FDC060763726CED07EA8F3C |
| SHA1: | CB75151C678340B2CB38461EEE1B1CBBA55430DF |
| SHA256: | CAC10E7BD6B171AD516A14CBD480724ADBF2F943DA8EA431F035A4ED0998FE4E |
| SSDEEP: | 3:N8ioD4QQ7:2RQ7 |
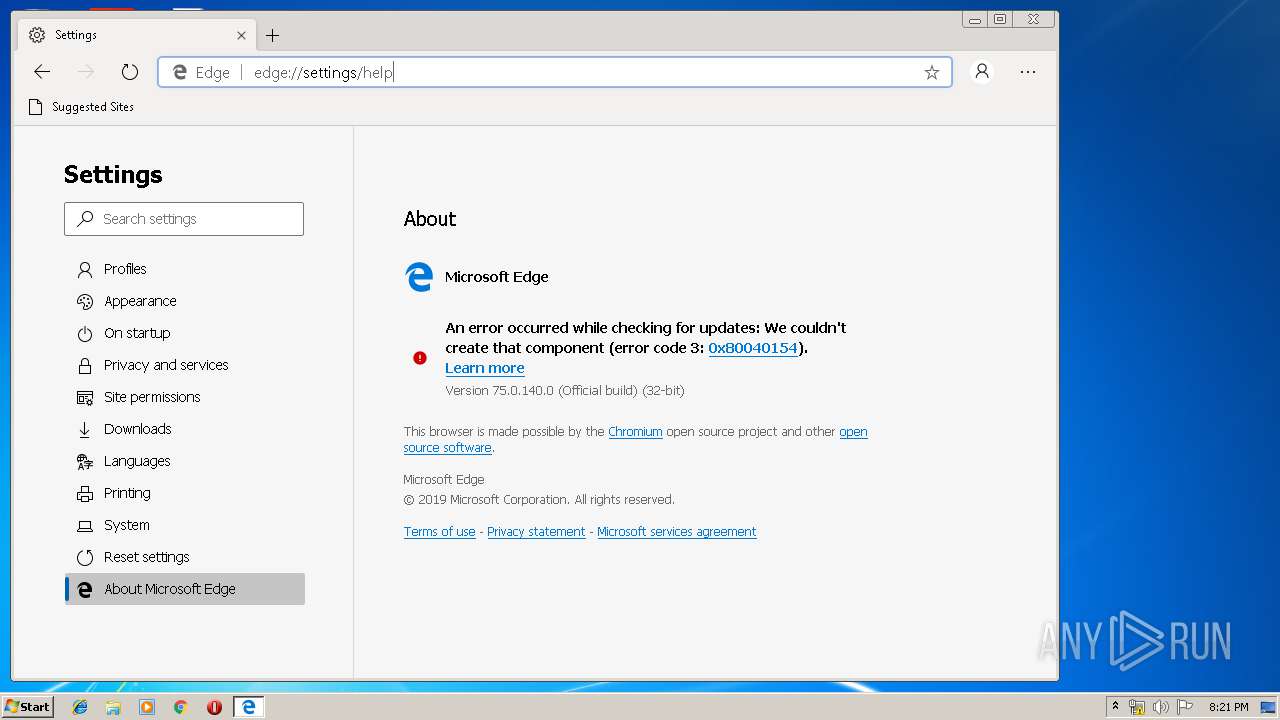
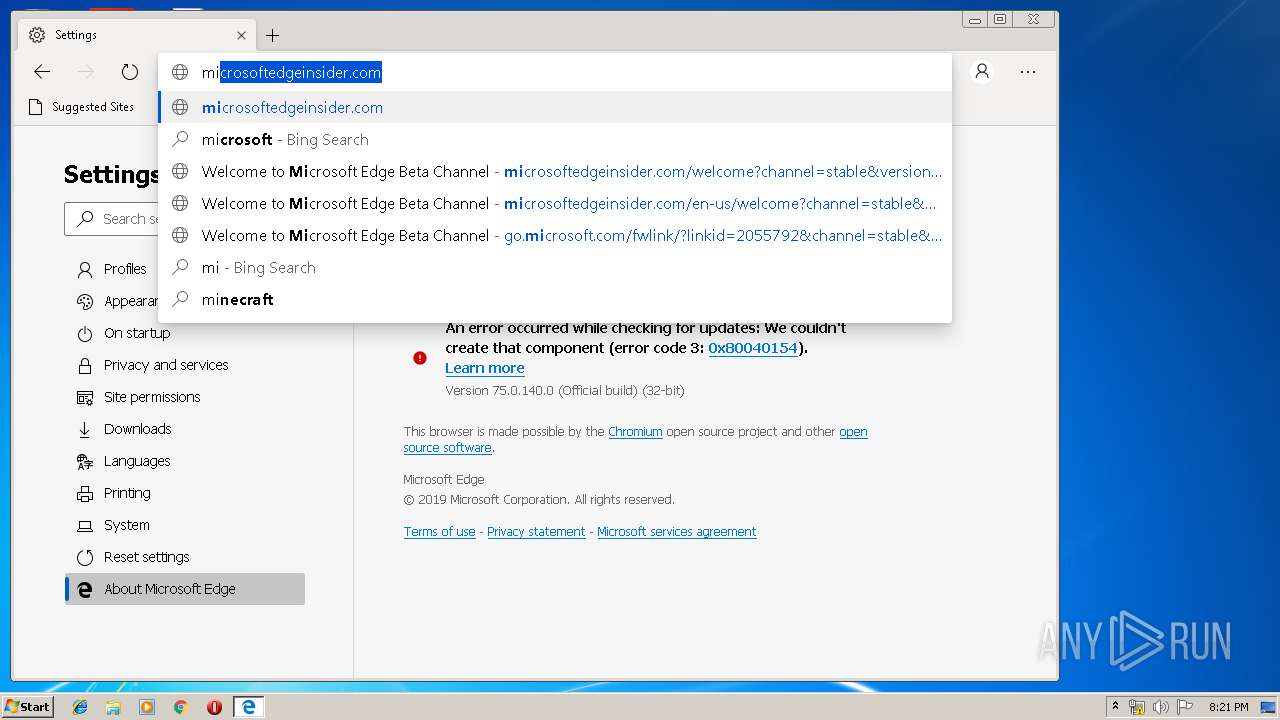
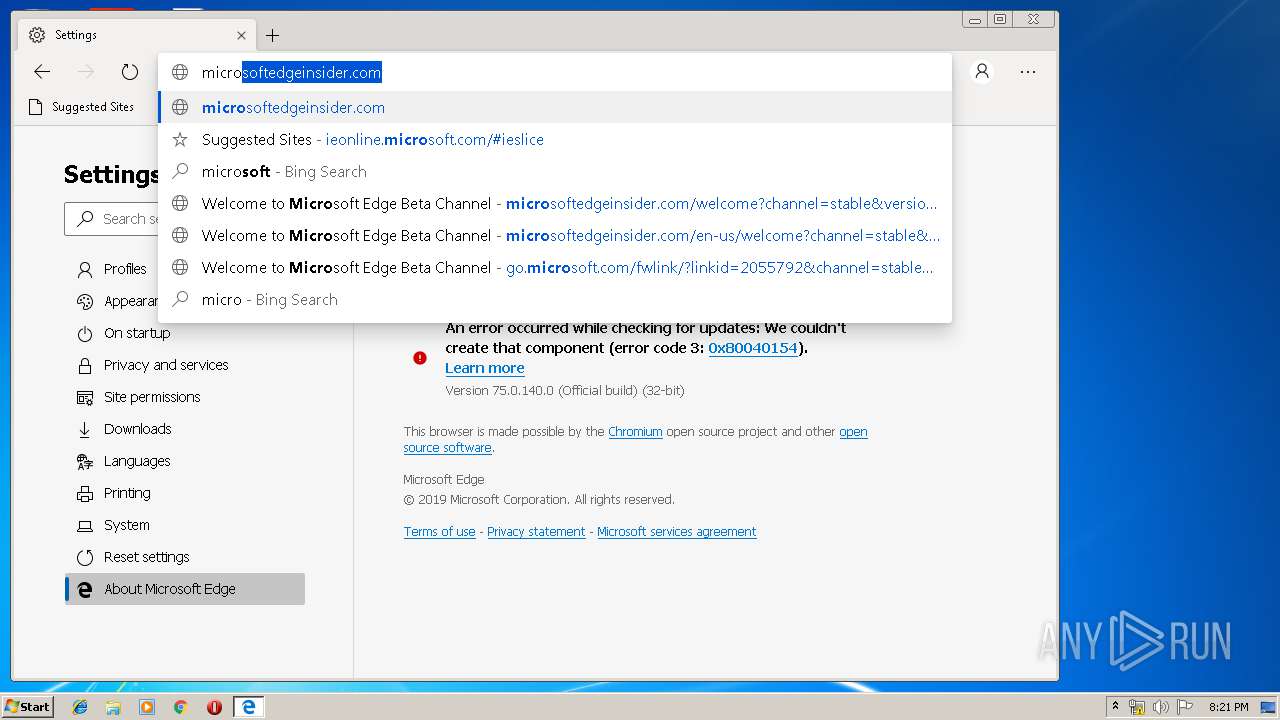
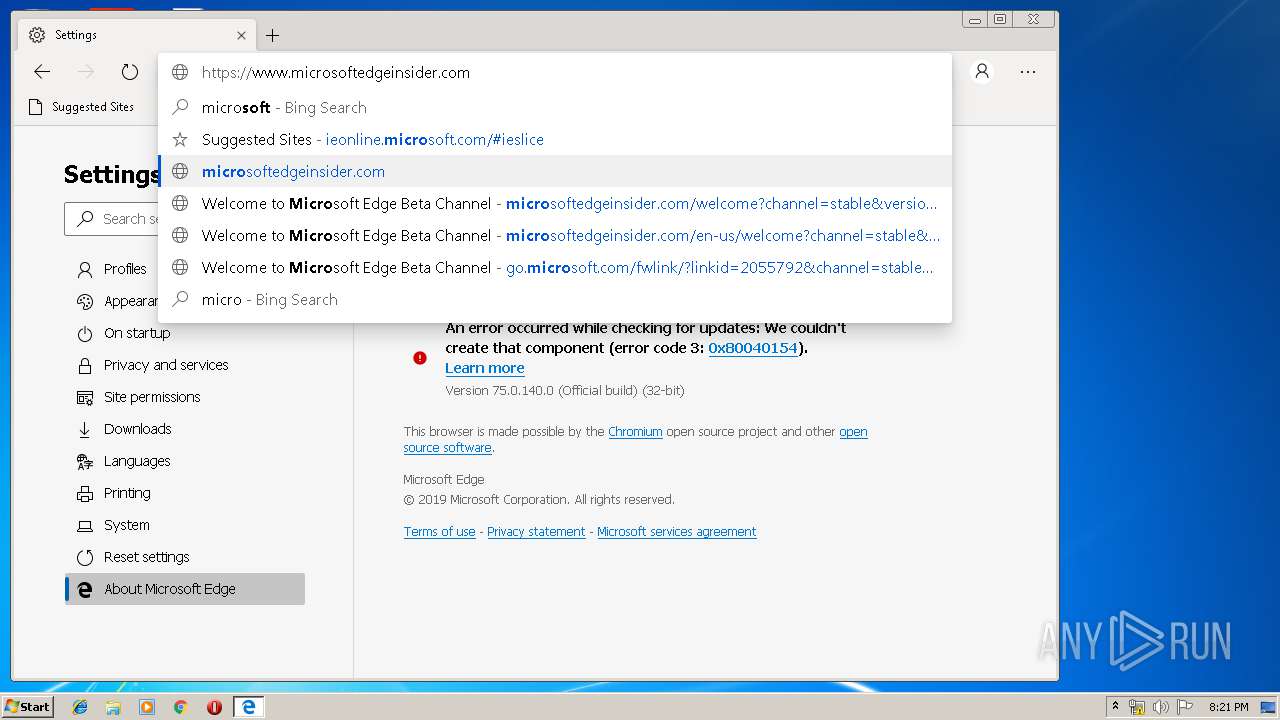
MALICIOUS
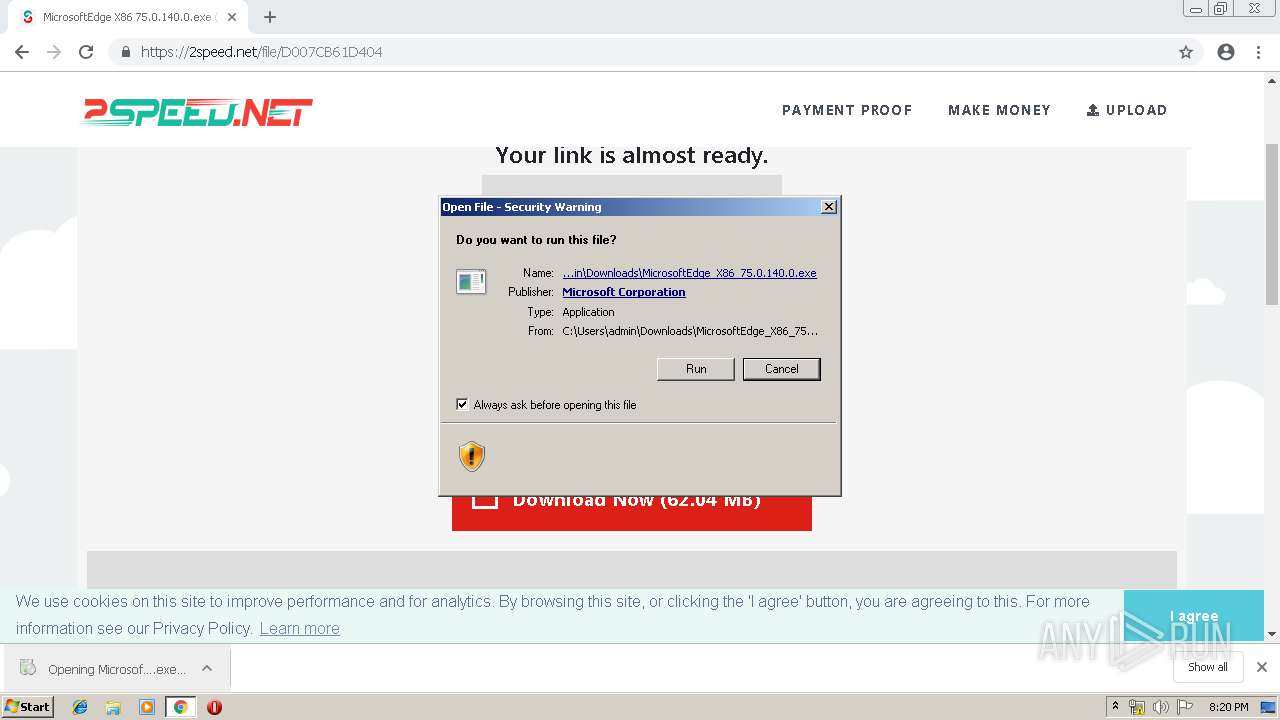
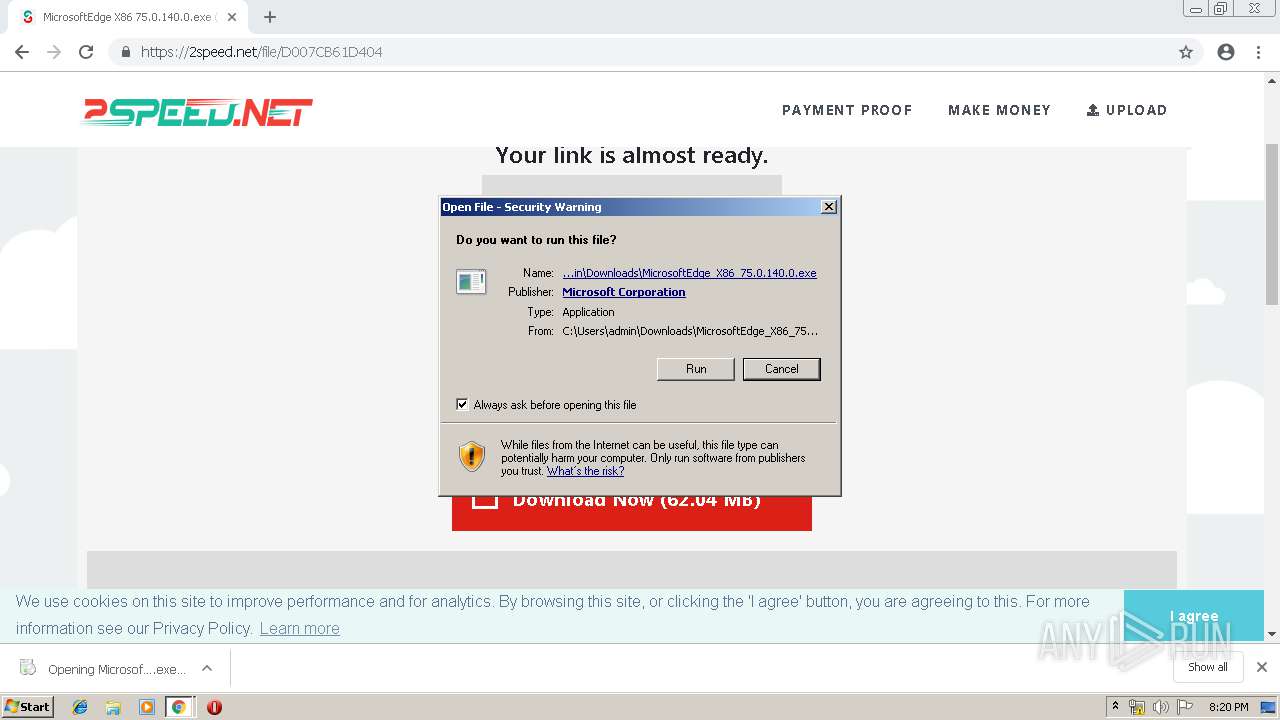
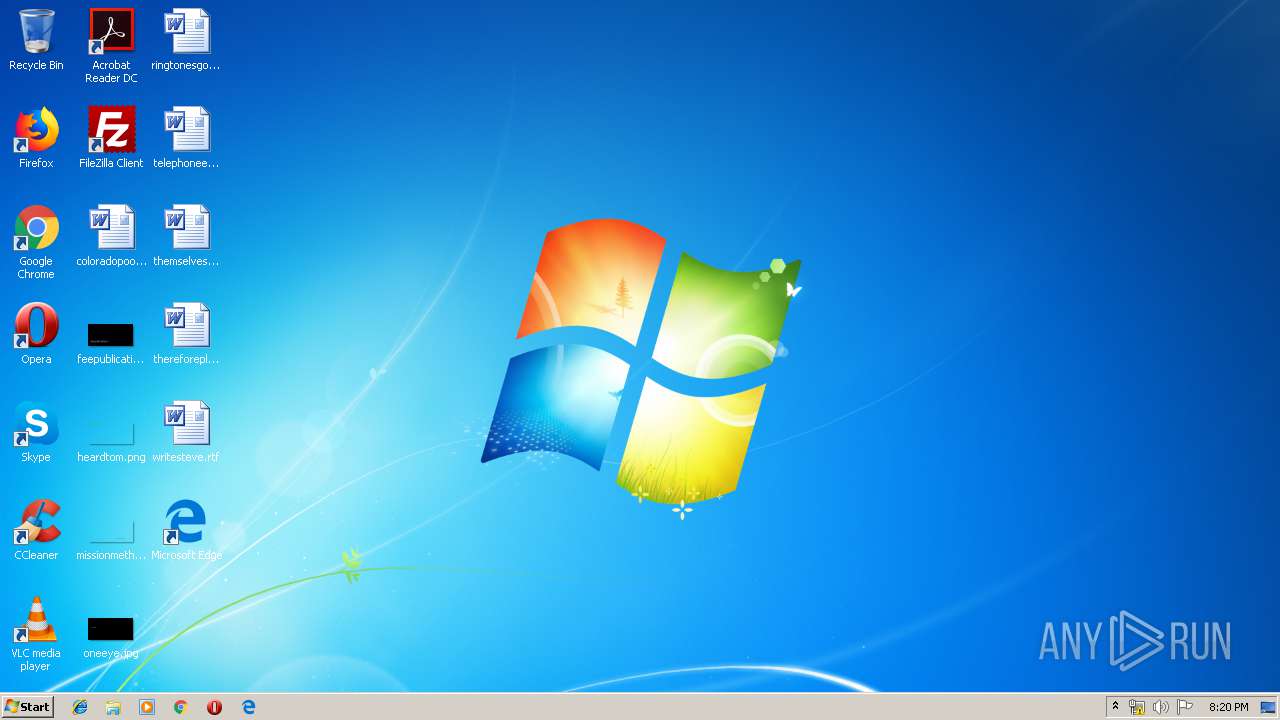
Application was dropped or rewritten from another process
- MicrosoftEdge_X86_75.0.140.0.exe (PID: 352)
- setup.exe (PID: 3764)
- setup.exe (PID: 2260)
- msedge.exe (PID: 3156)
- msedge.exe (PID: 2932)
- msedge.exe (PID: 2648)
- msedge.exe (PID: 600)
- msedge.exe (PID: 2972)
- msedge.exe (PID: 3568)
- msedge.exe (PID: 4008)
- msedge.exe (PID: 2568)
- msedge.exe (PID: 3940)
- msedge.exe (PID: 2908)
- msedge.exe (PID: 932)
- msedge.exe (PID: 3364)
- msedge.exe (PID: 3512)
- msedge.exe (PID: 284)
- msedge.exe (PID: 3552)
- msedge.exe (PID: 2776)
- msedge.exe (PID: 3208)
- msedge.exe (PID: 2324)
- msedge.exe (PID: 2280)
- msedge.exe (PID: 3880)
- msedge.exe (PID: 1168)
- msedge.exe (PID: 1340)
- msedge.exe (PID: 4032)
- msedge.exe (PID: 2276)
- msedge.exe (PID: 3632)
- msedge.exe (PID: 3184)
- msedge.exe (PID: 916)
- msedge.exe (PID: 3020)
- msedge.exe (PID: 2532)
Loads dropped or rewritten executable
- msedge.exe (PID: 2932)
- msedge.exe (PID: 600)
- msedge.exe (PID: 3156)
- msedge.exe (PID: 2648)
- msedge.exe (PID: 2972)
- msedge.exe (PID: 3940)
- msedge.exe (PID: 2776)
- msedge.exe (PID: 2568)
- msedge.exe (PID: 284)
- msedge.exe (PID: 2908)
- msedge.exe (PID: 932)
- msedge.exe (PID: 3364)
- msedge.exe (PID: 3552)
- msedge.exe (PID: 3512)
- msedge.exe (PID: 3208)
- msedge.exe (PID: 2280)
- msedge.exe (PID: 2276)
- msedge.exe (PID: 2324)
- msedge.exe (PID: 3880)
- msedge.exe (PID: 1168)
- msedge.exe (PID: 4032)
- msedge.exe (PID: 1340)
- msedge.exe (PID: 4008)
- msedge.exe (PID: 3568)
- msedge.exe (PID: 916)
- msedge.exe (PID: 3184)
- msedge.exe (PID: 3020)
- msedge.exe (PID: 3632)
- msedge.exe (PID: 2532)
SUSPICIOUS
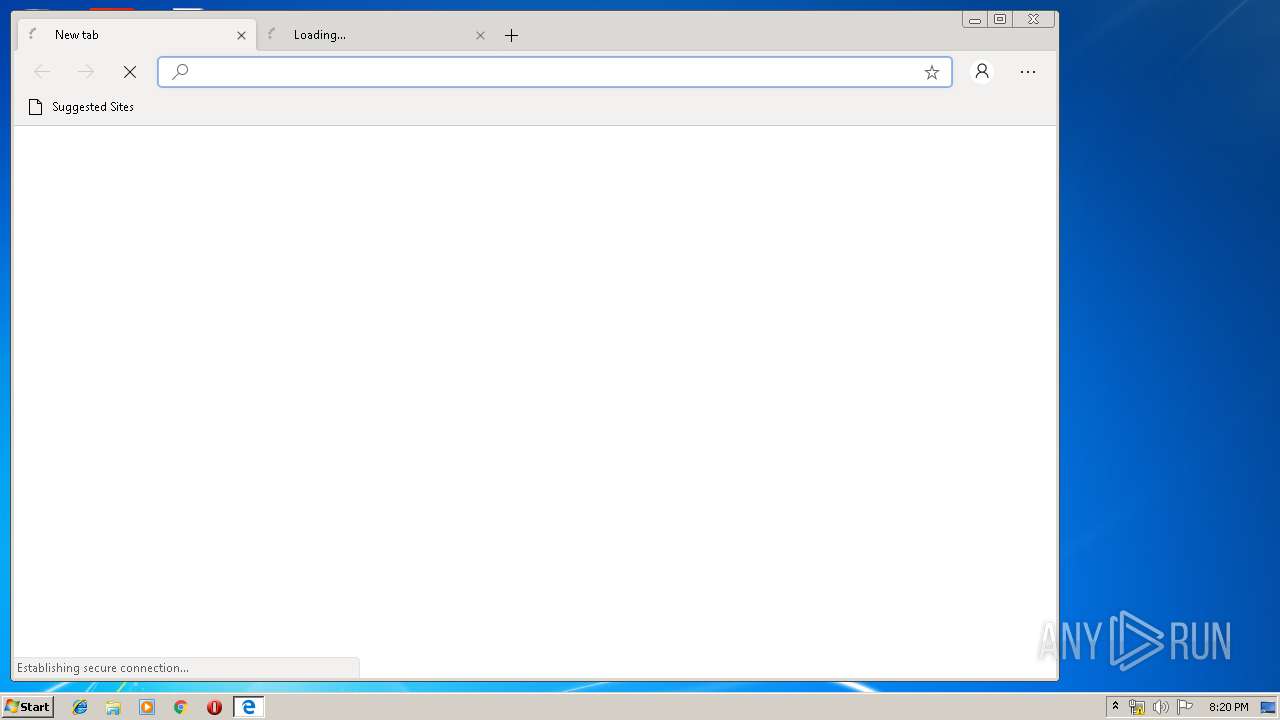
Application launched itself
- setup.exe (PID: 2260)
- msedge.exe (PID: 3156)
Modifies the open verb of a shell class
- setup.exe (PID: 2260)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2964)
Executable content was dropped or overwritten
- chrome.exe (PID: 2964)
- MicrosoftEdge_X86_75.0.140.0.exe (PID: 352)
- setup.exe (PID: 2260)
- msedge.exe (PID: 3156)
Creates files in the user directory
- setup.exe (PID: 2260)
Creates a software uninstall entry
- setup.exe (PID: 2260)
INFO
Dropped object may contain TOR URL's
- chrome.exe (PID: 2964)
Application launched itself
- chrome.exe (PID: 2964)
Reads settings of System Certificates
- msedge.exe (PID: 600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
58
Malicious processes
17
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=renderer --field-trial-handle=956,4118996972591211504,17156398626161327344,131072 --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-refresh --enable-offline-auto-refresh-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1298901218231532826 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3416 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 75.0.140.0 Modules
| |||||||||||||||
| 352 | "C:\Users\admin\Downloads\MicrosoftEdge_X86_75.0.140.0.exe" | C:\Users\admin\Downloads\MicrosoftEdge_X86_75.0.140.0.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 75.0.140.0 Modules
| |||||||||||||||
| 600 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=utility --field-trial-handle=956,4118996972591211504,17156398626161327344,131072 --lang=en-US --service-sandbox-type=network --service-request-channel-token=5684060759082871668 --mojo-platform-channel-handle=1712 /prefetch:8 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 75.0.140.0 Modules
| |||||||||||||||
| 916 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=ppapi-broker --field-trial-handle=956,4118996972591211504,17156398626161327344,131072 --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --service-request-channel-token=9624067953075049317 --mojo-platform-channel-handle=5204 /prefetch:4 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 75.0.140.0 Modules
| |||||||||||||||
| 932 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=renderer --field-trial-handle=956,4118996972591211504,17156398626161327344,131072 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-refresh --enable-offline-auto-refresh-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9405659984595511152 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3556 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 75.0.140.0 Modules
| |||||||||||||||
| 1168 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=utility --field-trial-handle=956,4118996972591211504,17156398626161327344,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4256162008038982169 --mojo-platform-channel-handle=4672 --ignored=" --type=renderer " /prefetch:8 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 75.0.140.0 Modules
| |||||||||||||||
| 1340 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=renderer --field-trial-handle=956,4118996972591211504,17156398626161327344,131072 --disable-gpu-compositing --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-refresh --enable-offline-auto-refresh-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10141070316604792450 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1540 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 75.0.140.0 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,2043283896163928293,11372168043744989382,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12427265531939511974 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12427265531939511974 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,2043283896163928293,11372168043744989382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3566799382498959022 --mojo-platform-channel-handle=5196 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 349
Read events
2 068
Write events
275
Delete events
6
Modification events
| (PID) Process: | (2696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2964-13200693518749000 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
52
Suspicious files
215
Text files
359
Unknown types
50
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f40932b3-6c2b-438c-b96f-4ab2bf8795df.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
98
DNS requests
78
Threats
2
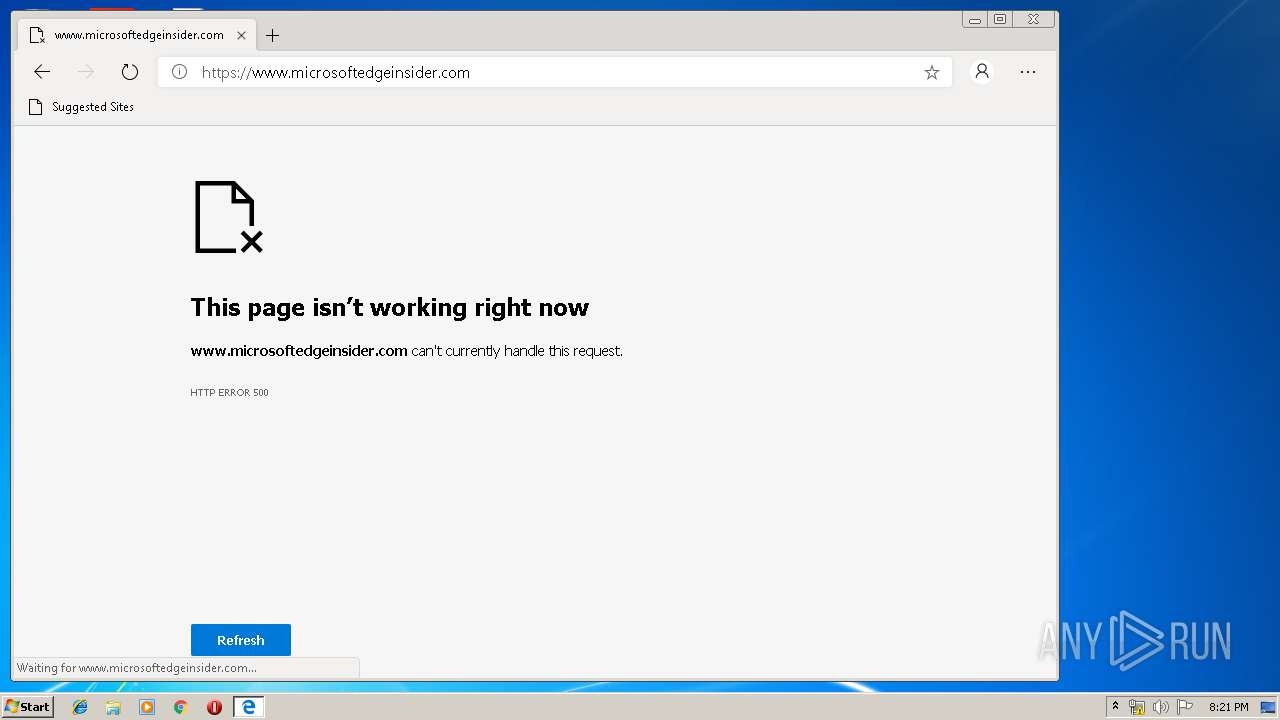
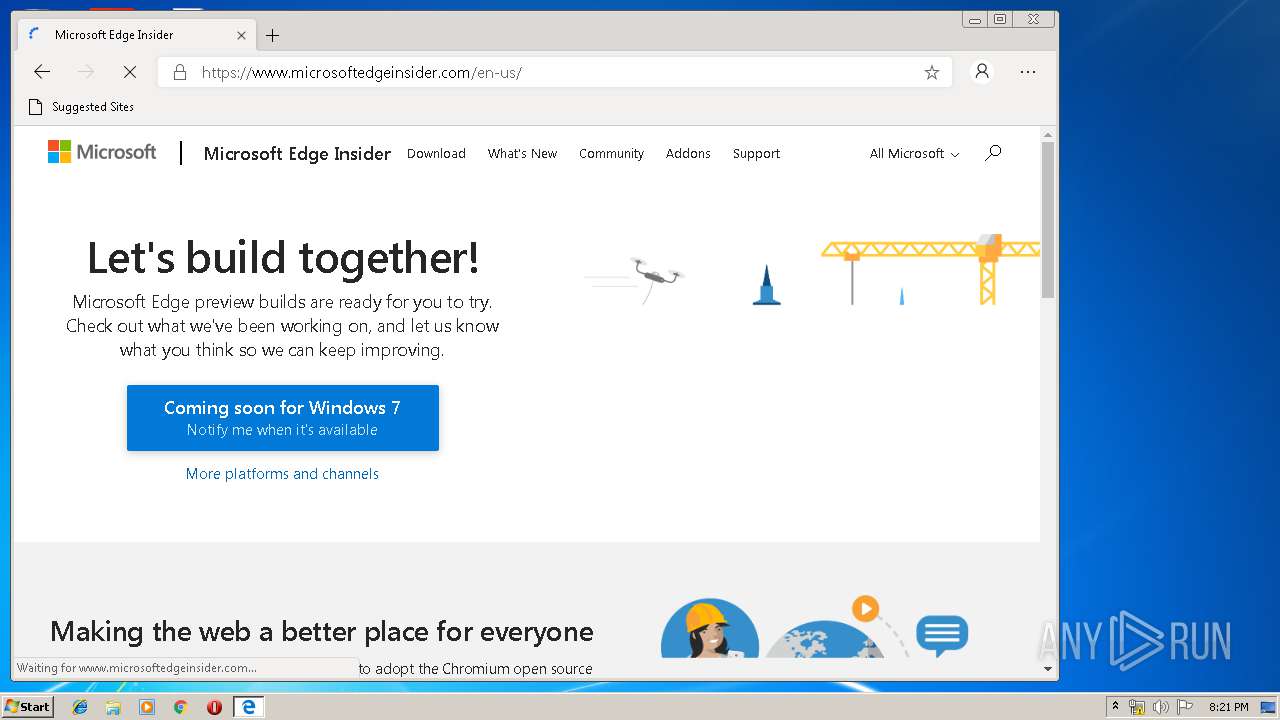
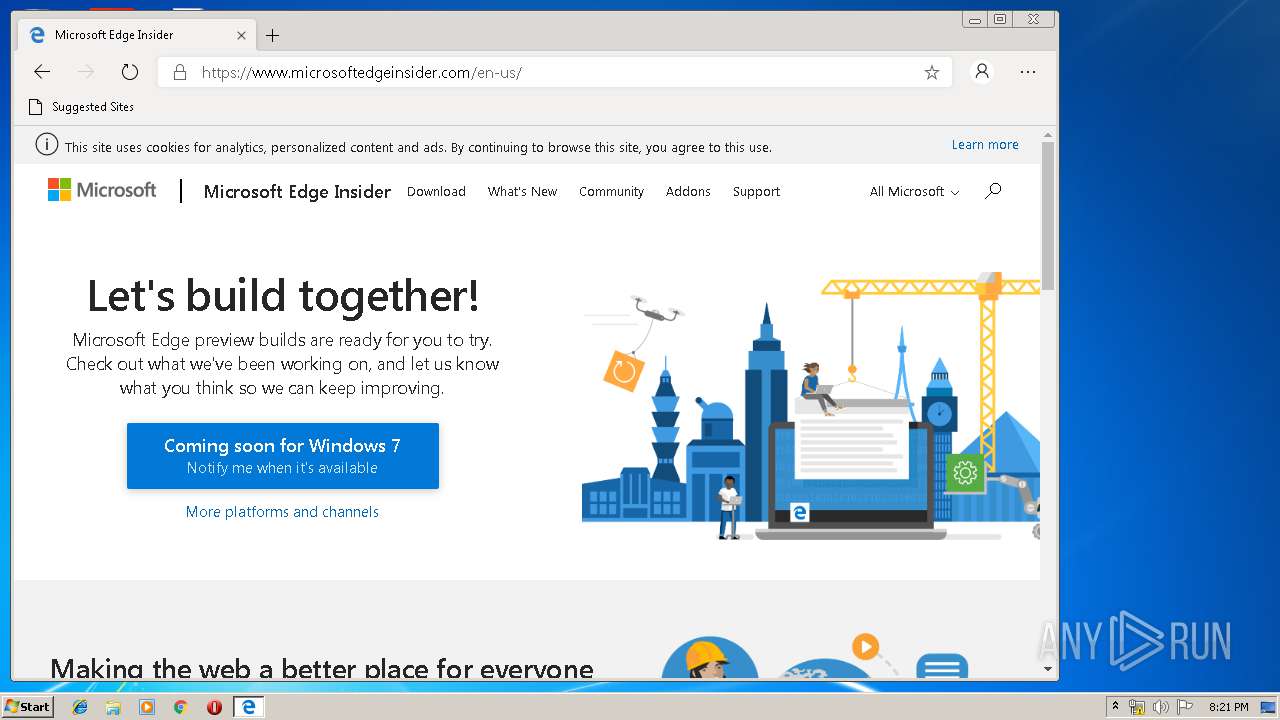
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2964 | chrome.exe | GET | 200 | 87.245.198.16:80 | http://r5---sn-gxuog0-axqe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.117.118.92&mm=28&mn=sn-gxuog0-axqe&ms=nvh&mt=1556219747&mv=u&pl=25&shardbypass=yes | RU | crx | 842 Kb | whitelisted |
3156 | msedge.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.43 Kb | whitelisted |
3156 | msedge.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCEyAAA7VE2alhoJR2mHYAAAADtUQ%3D | US | der | 1.79 Kb | whitelisted |
3156 | msedge.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCEyAAA7VE2alhoJR2mHYAAAADtUQ%3D | US | der | 1.79 Kb | whitelisted |
600 | msedge.exe | GET | 200 | 87.245.198.12:80 | http://r1---sn-gxuog0-axqe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWRiQUFXRzBmNy0xYlVRZ0JEM3hyZ3NxUQ/7519.415.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.117.118.92&mm=28&mn=sn-gxuog0-axqe&ms=nvh&mt=1556219747&mv=u&pl=25&shardbypass=yes | RU | crx | 853 Kb | whitelisted |
3156 | msedge.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.43 Kb | whitelisted |
600 | msedge.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWRiQUFXRzBmNy0xYlVRZ0JEM3hyZ3NxUQ/7519.415.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 511 b | whitelisted |
2964 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 511 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 104.25.9.107:443 | 2speed.net | Cloudflare Inc | US | shared |
2964 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 172.217.22.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2964 | chrome.exe | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2964 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 172.217.18.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 151.101.120.134:443 | 2speed-net.disqus.com | Fastly | US | unknown |
2964 | chrome.exe | 216.58.208.34:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
2speed.net |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
apis.google.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.google.com |
| malicious |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2964 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2964 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |