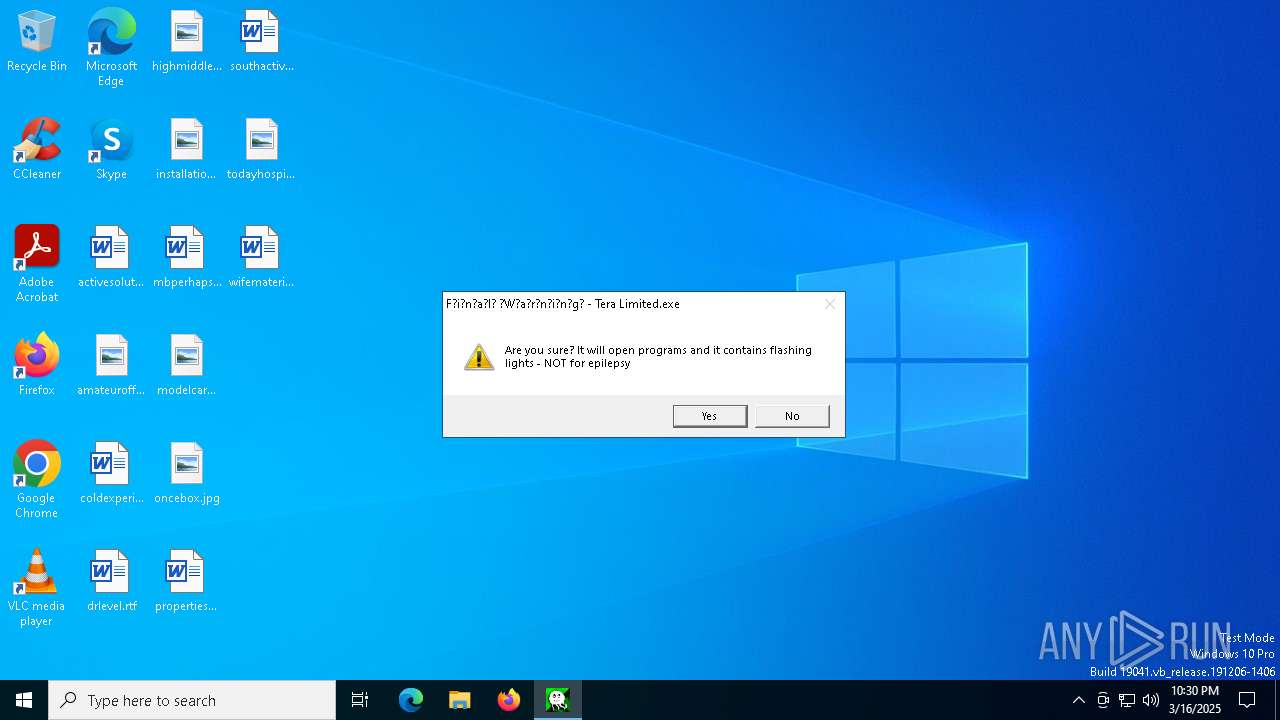
| File name: | Tera Limited.exe |
| Full analysis: | https://app.any.run/tasks/11200dd5-b973-4437-87e2-8773e81cd058 |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2025, 22:30:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 18 sections |
| MD5: | 9D275F4F577FEDB4C501B1C4E30E8411 |
| SHA1: | 20DAFB854AC3F3EB2CDA2EA850AE91F8C72D0335 |
| SHA256: | CABDDDEEAF37F5A656C57422C64C2271C2BEA2F8EAC5684F5ABCD8D91CEDB041 |
| SSDEEP: | 49152:ZZi/9MdOHJTe066x66cqc5GwBQUQd0MNBsFvF:aHaqc5GwBQd0MNBsFvF |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- Tera Limited.exe (PID: 6724)
There is functionality for taking screenshot (YARA)
- Tera Limited.exe (PID: 6724)
Reads security settings of Internet Explorer
- Tera Limited.exe (PID: 6724)
Working with threads in the GNU C Compiler (GCC) libraries related mutex has been found
- Tera Limited.exe (PID: 6724)
INFO
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8024)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7276)
- BackgroundTransferHost.exe (PID: 7788)
- BackgroundTransferHost.exe (PID: 6108)
- BackgroundTransferHost.exe (PID: 8144)
- BackgroundTransferHost.exe (PID: 680)
- BackgroundTransferHost.exe (PID: 8024)
Reads the computer name
- Tera Limited.exe (PID: 6724)
Process checks computer location settings
- Tera Limited.exe (PID: 6724)
Checks supported languages
- Tera Limited.exe (PID: 6724)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8024)
- slui.exe (PID: 5324)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:01 20:38:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.24 |
| CodeSize: | 468480 |
| InitializedDataSize: | 791040 |
| UninitializedDataSize: | 6144 |
| EntryPoint: | 0x14d0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
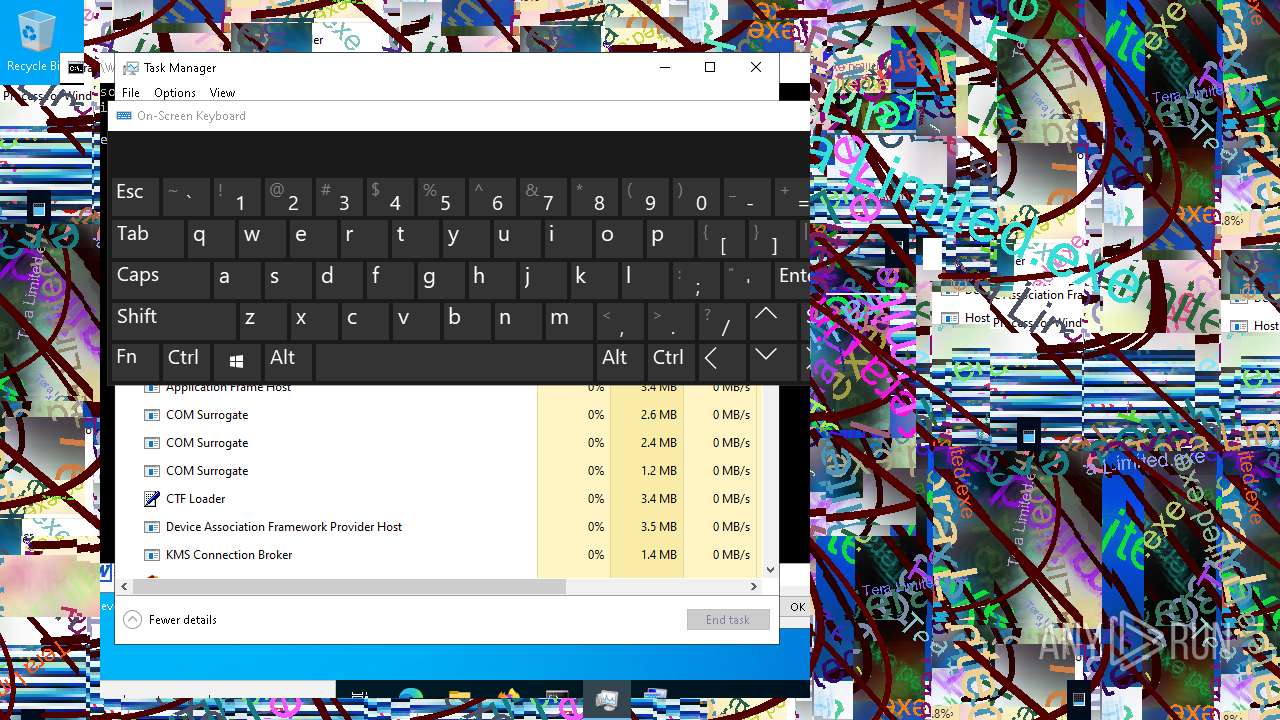
Total processes
150
Monitored processes
15
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4776 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Tera Limited.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
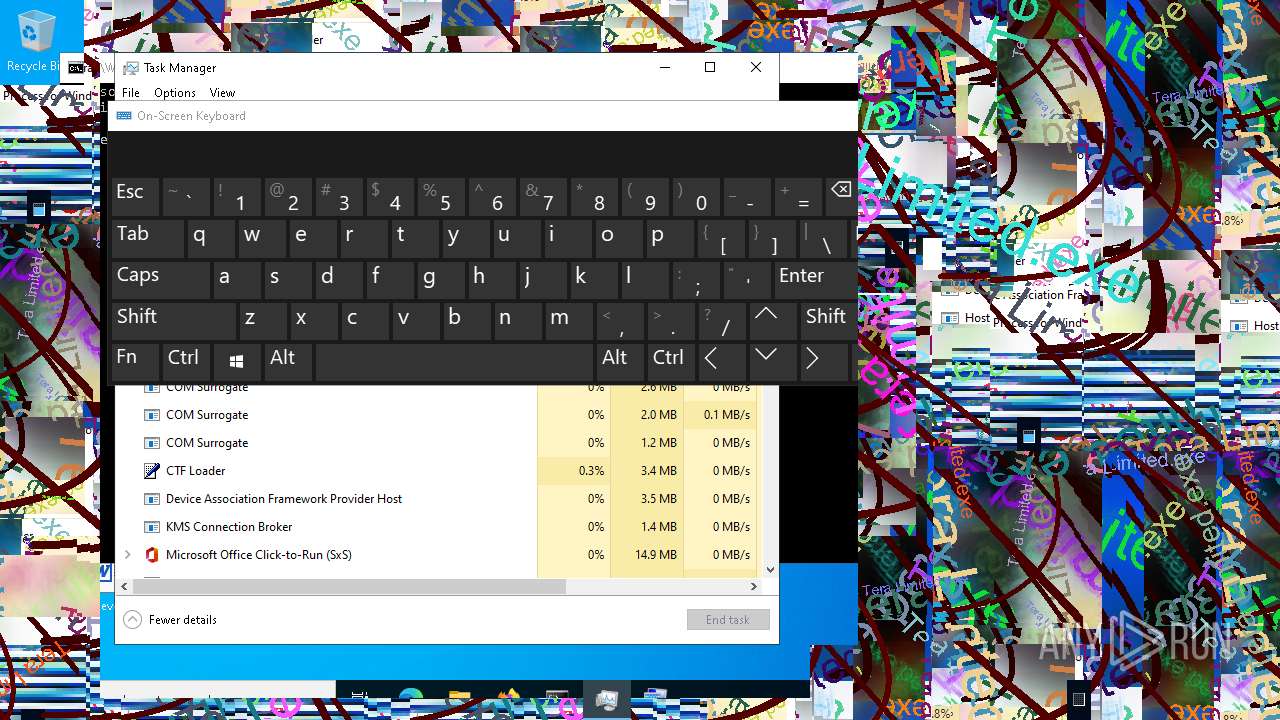
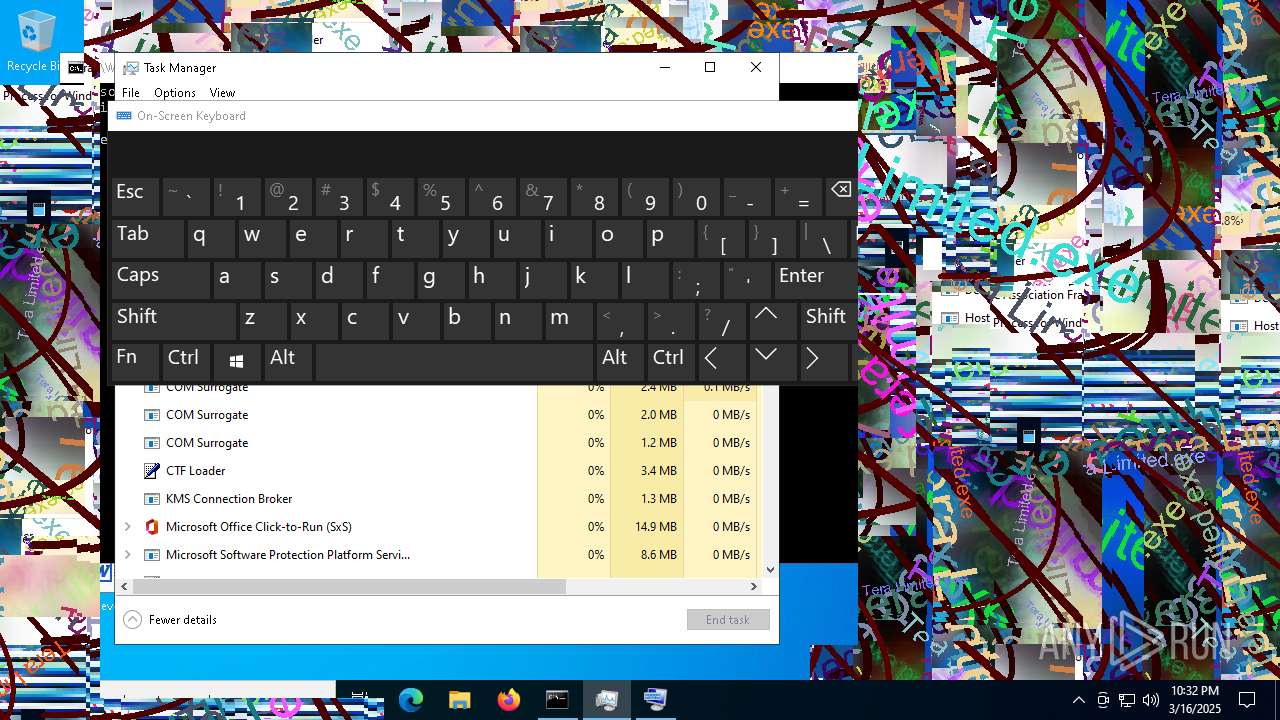
| 5124 | "C:\Windows\System32\osk.exe" | C:\Windows\System32\osk.exe | Tera Limited.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Accessibility On-Screen Keyboard Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5256 | "C:\Windows\System32\Taskmgr.exe" | C:\Windows\System32\Taskmgr.exe | — | Tera Limited.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5260 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5324 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
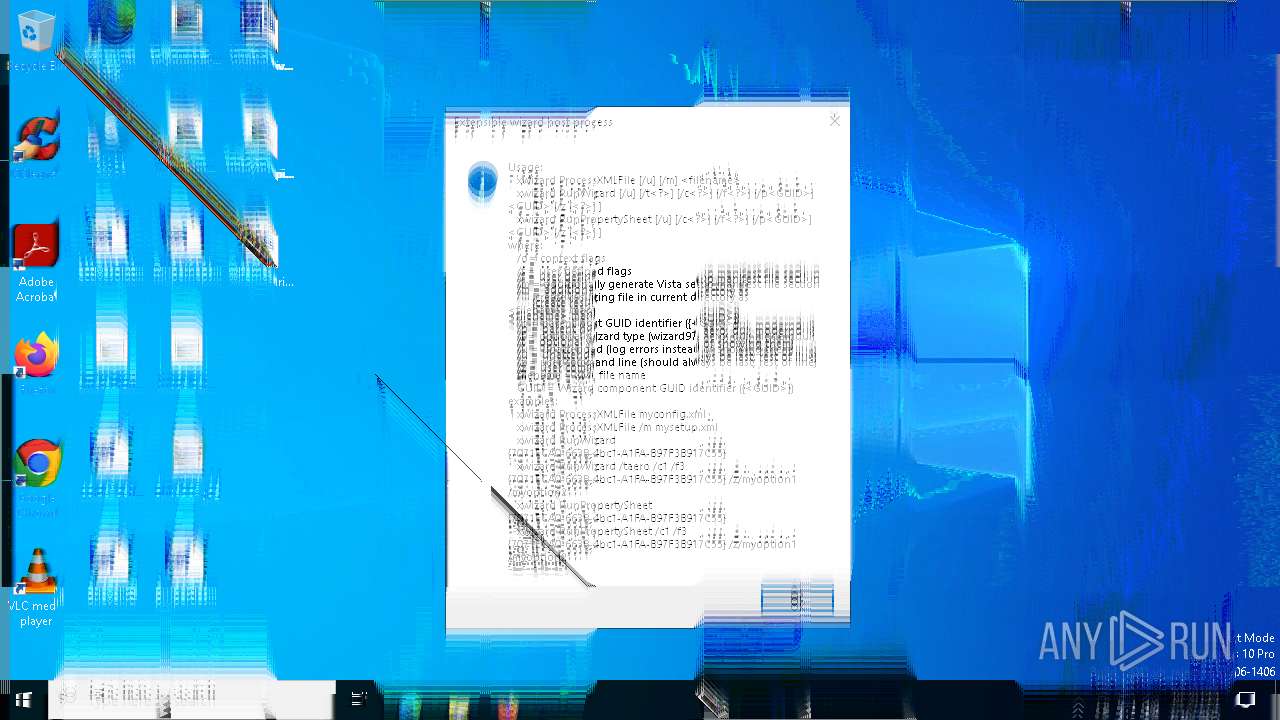
| 5504 | "C:\Windows\System32\xwizard.exe" | C:\Windows\System32\xwizard.exe | — | Tera Limited.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extensible Wizards Host Process Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6108 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 541
Read events
5 456
Write events
84
Delete events
1
Modification events
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Osk |
| Operation: | write | Name: | ScanKey |
Value: 32 | |||
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Accessibility\ATConfig\osk |
| Operation: | write | Name: | ScanKey |
Value: 32 | |||
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Osk |
| Operation: | write | Name: | UseTextPrediction |
Value: 1 | |||
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Accessibility\ATConfig\osk |
| Operation: | write | Name: | UseTextPrediction |
Value: 1 | |||
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Osk |
| Operation: | write | Name: | InsertSpace |
Value: 1 | |||
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Accessibility\ATConfig\osk |
| Operation: | write | Name: | InsertSpace |
Value: 1 | |||
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Osk |
| Operation: | write | Name: | ShowNumPad |
Value: 0 | |||
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Accessibility\ATConfig\osk |
| Operation: | write | Name: | ShowNumPad |
Value: 0 | |||
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Osk |
| Operation: | write | Name: | NavigationMode |
Value: 0 | |||
| (PID) Process: | (5124) osk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Accessibility\ATConfig\osk |
| Operation: | write | Name: | NavigationMode |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8024 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\f6e637d5-8421-410c-be65-febe16c1cd98.down_data | — | |
MD5:— | SHA256:— | |||
| 8024 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\b25ee717-4f4b-4e16-acac-14e907b2034d.up_meta_secure | binary | |
MD5:8D5ABB8C873EFCD09625C49205E202C4 | SHA256:749DFF6D7AA596671C967B33209693E774F749495CF9B8B708EB28EB60E61B22 | |||
| 8024 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:6BD7B4AA25CACD54B2749276B125F047 | SHA256:442E94289F66150FE741005A8C1B76824BD0EA818840A55DECADE7318044591C | |||
| 7276 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\ecbf0d5a3a180bb\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 8024 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\f6e637d5-8421-410c-be65-febe16c1cd98.08d7e27a-a300-49fb-8b4c-2426d3b1e5be.down_meta | binary | |
MD5:2AF2FFBF87B752D0E1D9D14092A5E4FE | SHA256:336F8096AA4A00A5FA6F11920F4AD77A5340A5D0DE6E65A7D0DD253FE3EC25A1 | |||
| 8024 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:90A9729DDF5977B7E2836006B33D032F | SHA256:6ADC5B1C38F4C79D0CB232ABF8915F3B059041B0B5FB44AB99194975F723A5C5 | |||
| 8024 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\b25ee717-4f4b-4e16-acac-14e907b2034d.08d7e27a-a300-49fb-8b4c-2426d3b1e5be.down_meta | binary | |
MD5:2AF2FFBF87B752D0E1D9D14092A5E4FE | SHA256:336F8096AA4A00A5FA6F11920F4AD77A5340A5D0DE6E65A7D0DD253FE3EC25A1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.110.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5968 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8108 | SIHClient.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8108 | SIHClient.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8024 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 88.221.110.114:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5968 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5968 | backgroundTaskHost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |