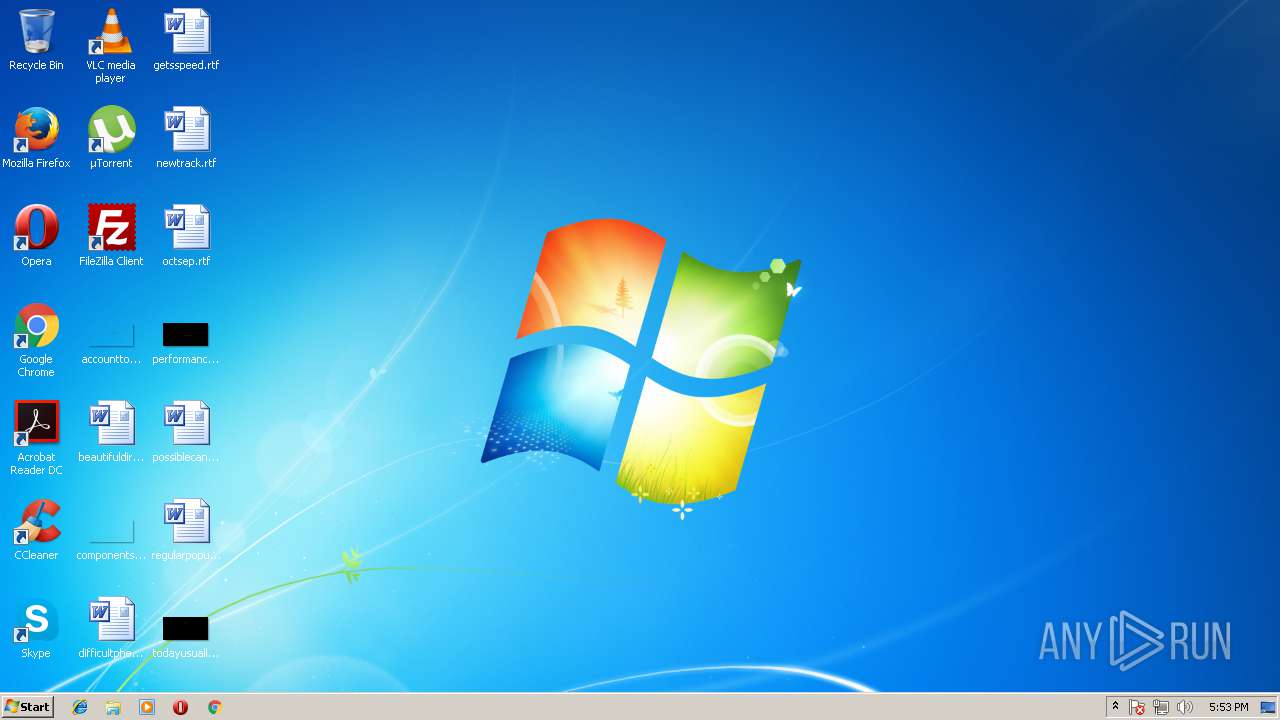
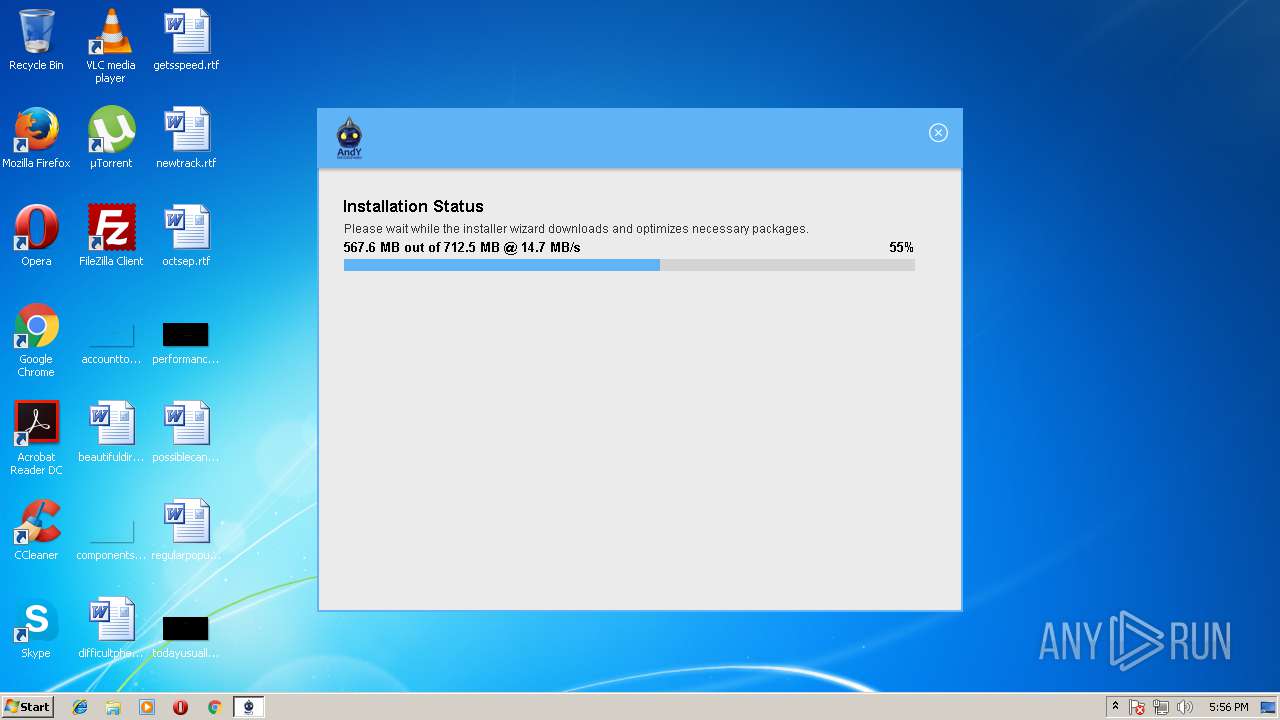
| File name: | Andy_46.16_66.exe |
| Full analysis: | https://app.any.run/tasks/89a0b502-f009-4064-86c6-9bbdf61bcede |
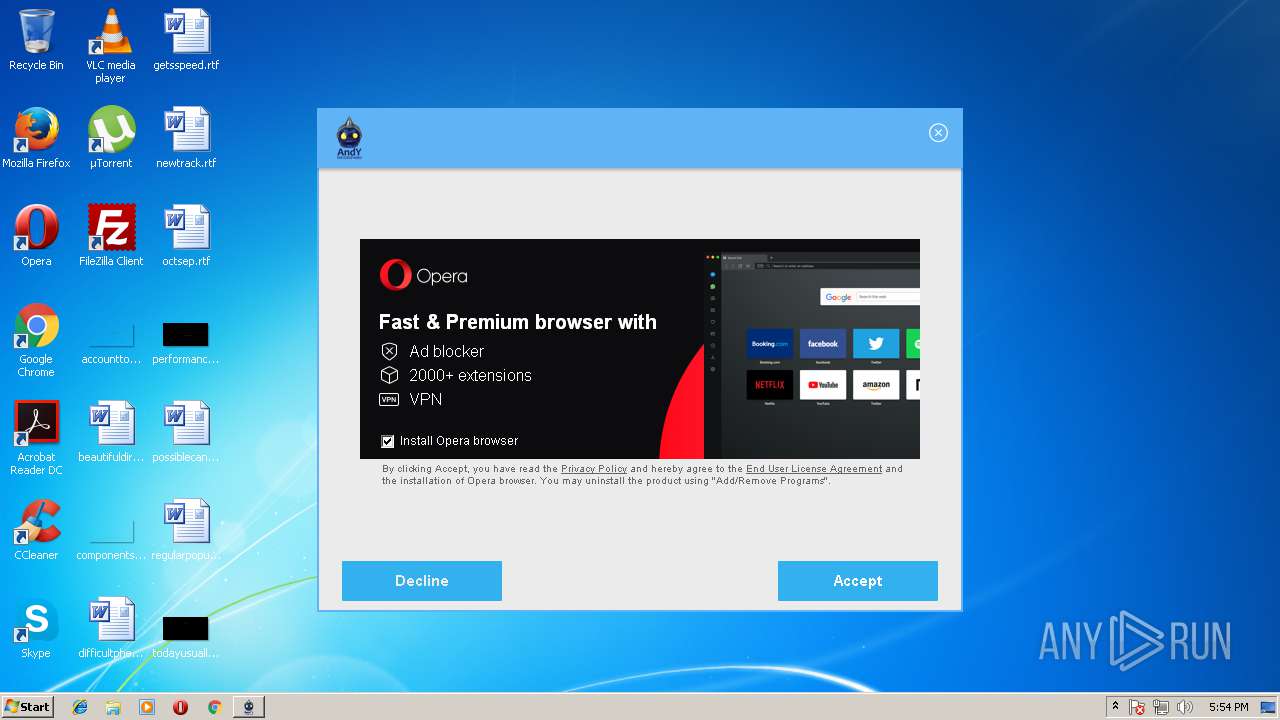
| Verdict: | Suspicious activity |
| Analysis date: | June 28, 2018, 16:53:33 |
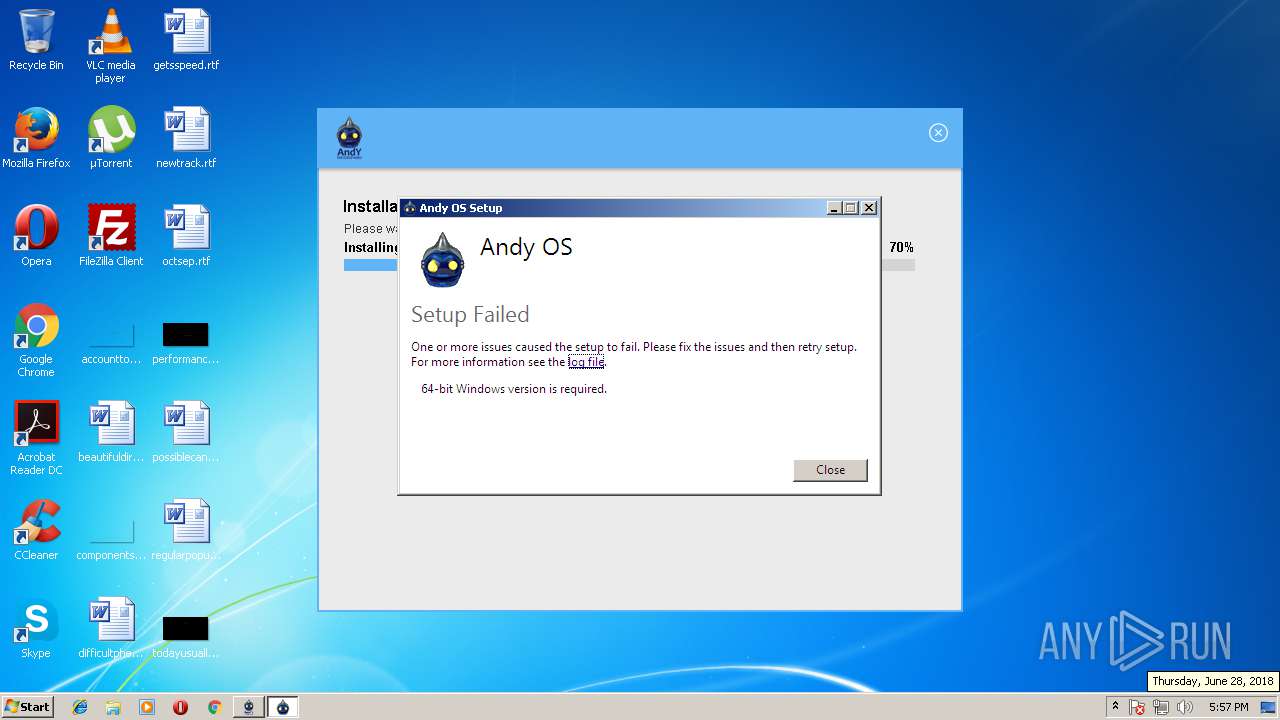
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8A687D6C281F478FD925B97545CACAB0 |
| SHA1: | F70DF24CD5F9E93B141DD9F65602231E69C3548C |
| SHA256: | CAAC75EF9B1580AA4E94A3E4AB55E3721A2C418685244B4DB95F87640516133B |
| SSDEEP: | 49152:X2ujLcmSHGtznPu+ggkZq9qsidGaGpfUR:mujLcmSHGtzPujgkZqHidAUR |
MALICIOUS
Application was dropped or rewritten from another process
- 553D37DD_stp.exe (PID: 648)
Loads dropped or rewritten executable
- 553D37DD_stp.exe (PID: 648)
SUSPICIOUS
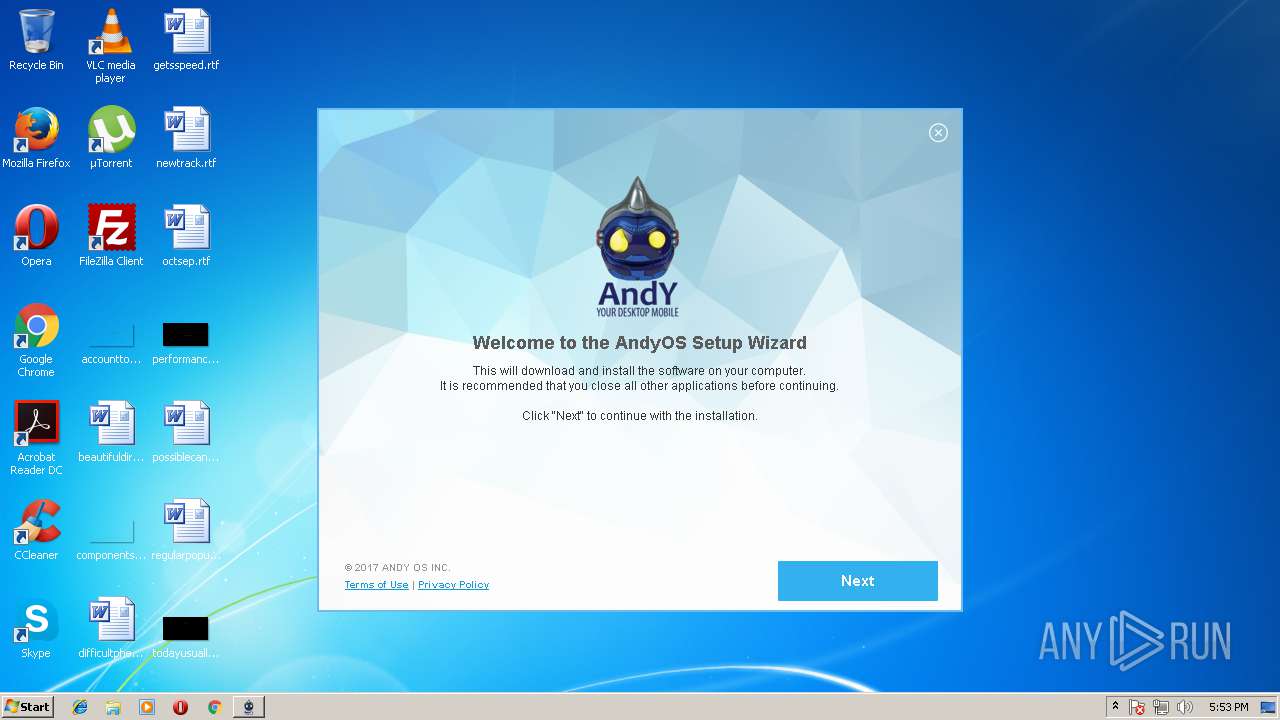
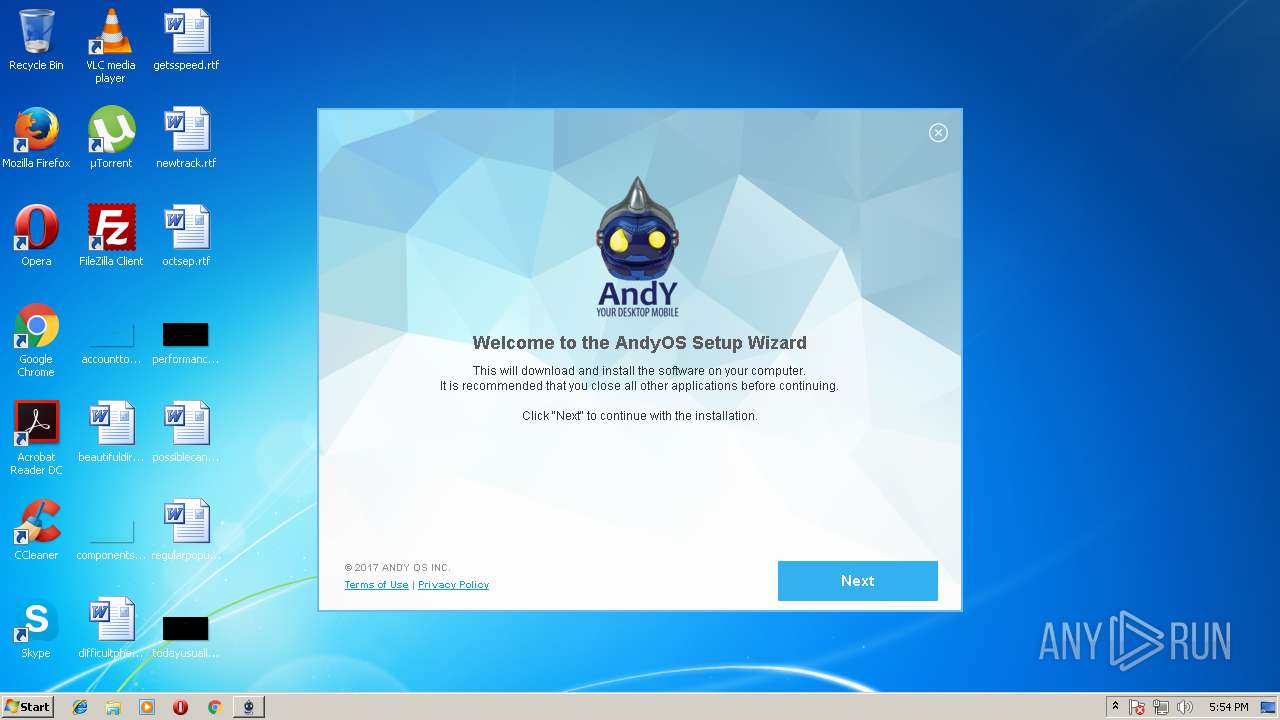
Application launched itself
- Andy_46.16_66.exe (PID: 3628)
Reads internet explorer settings
- Andy_46.16_66.exe (PID: 3196)
Reads the date of Windows installation
- Andy_46.16_66.exe (PID: 3196)
Reads productID from registry
- Andy_46.16_66.exe (PID: 3196)
Executable content was dropped or overwritten
- 553D37DD_stp.exe (PID: 4036)
- 553D37DD_stp.exe (PID: 648)
Reads the machine GUID from the registry
- Andy_46.16_66.exe (PID: 3196)
Reads CPU info
- Andy_46.16_66.exe (PID: 3196)
Creates files in the program directory
- Andy_46.16_66.exe (PID: 3196)
INFO
Dropped object may contain URL's
- Andy_46.16_66.exe (PID: 3628)
- Andy_46.16_66.exe (PID: 3196)
- 553D37DD_stp.exe (PID: 648)
- 553D37DD_stp.exe (PID: 4036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Pebede Setup |
| FileVersion: | |
| LegalCopyright: | Program Installer |
| ProductName: | Pebede |
| ProductVersion: | 1.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Pebede Setup |
| FileVersion: | - |
| LegalCopyright: | Program Installer |
| ProductName: | Pebede |
| ProductVersion: | 1.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009D30 | 0x00009E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62042 |
DATA | 0x0000B000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75182 |
BSS | 0x0000C000 | 0x00000E8C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00009FDC | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.26983 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11919 | 1512 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.19427 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.16143 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.38796 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.32225 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
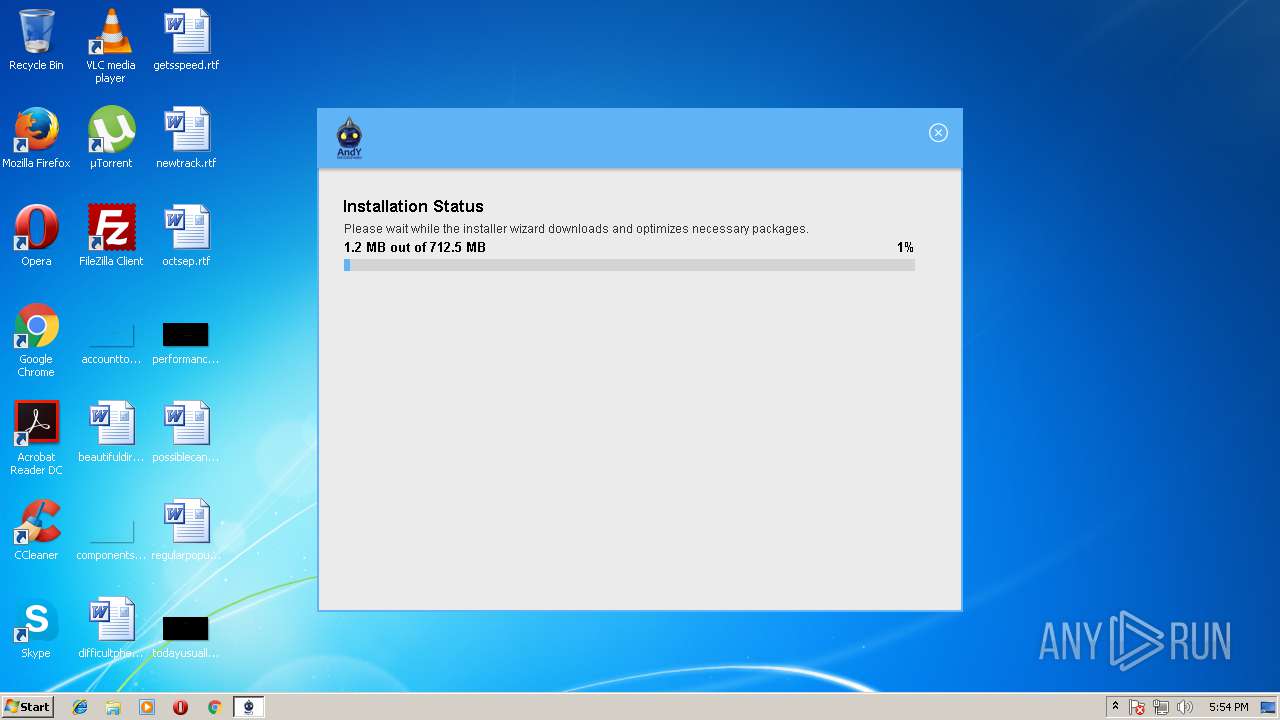
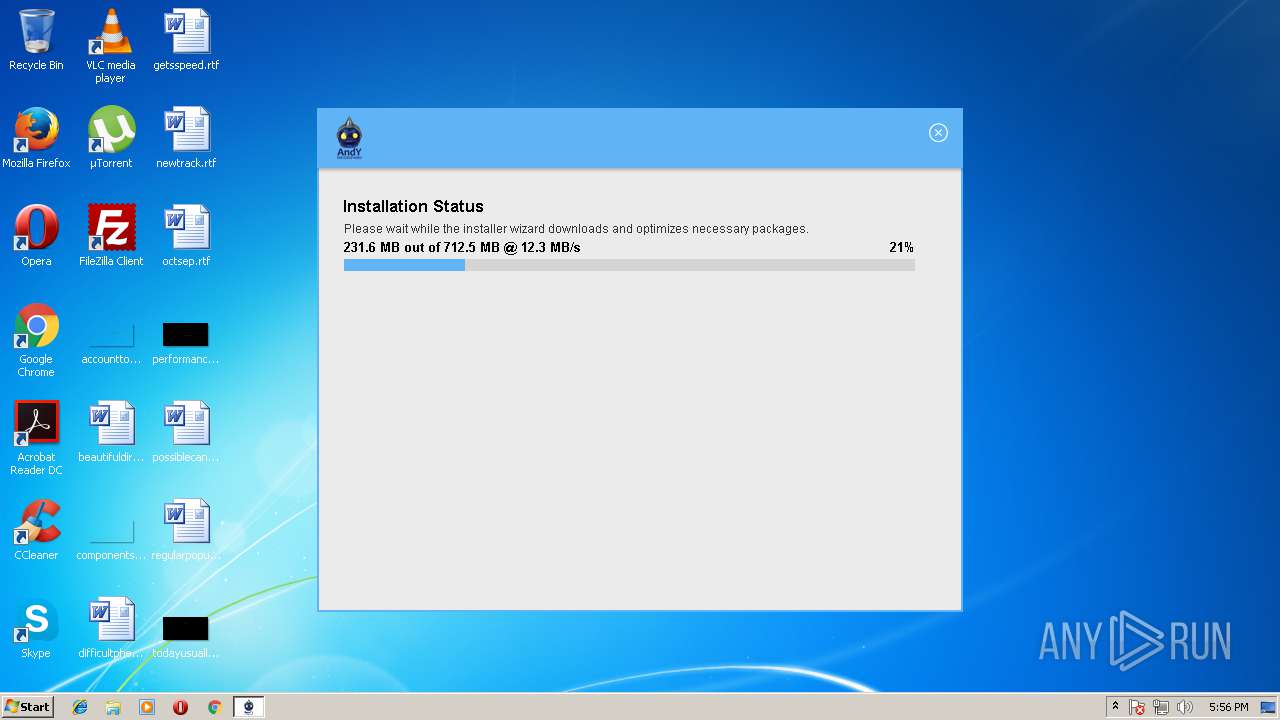
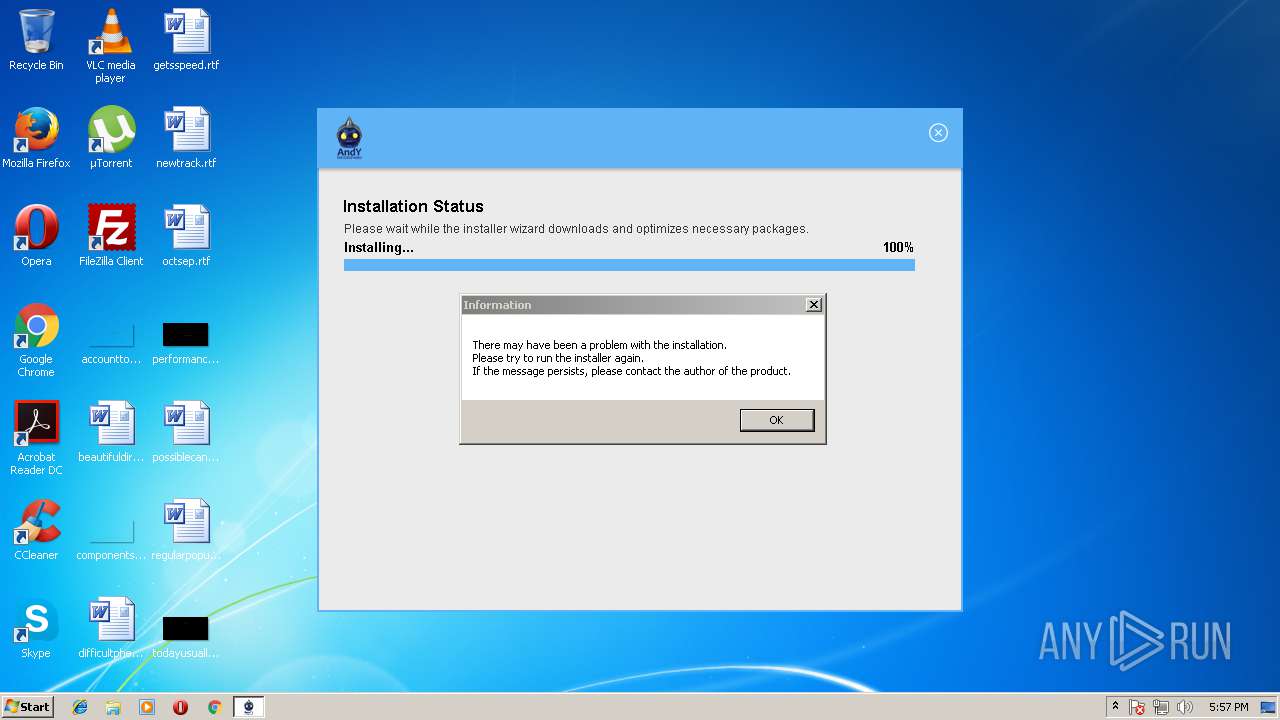
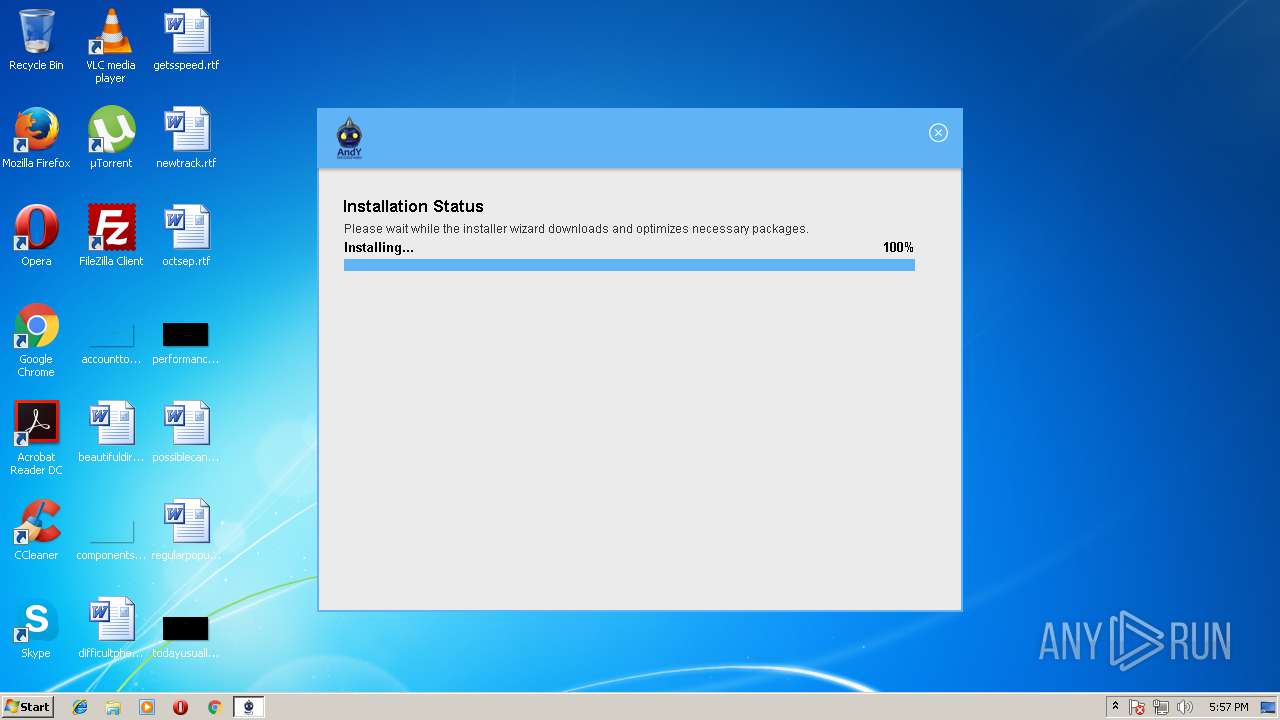
| 648 | "C:\Users\admin\AppData\Local\Temp\{B2B32214-B26B-4493-9E7B-426006B666D5}\.cr\553D37DD_stp.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\in68BAA86E\553D37DD_stp.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 -sp--silent | C:\Users\admin\AppData\Local\Temp\{B2B32214-B26B-4493-9E7B-426006B666D5}\.cr\553D37DD_stp.exe | 553D37DD_stp.exe | ||||||||||||
User: admin Company: Andy OS Inc. Integrity Level: HIGH Description: Andy OS Exit code: 1 Version: 47.0.146 Modules
| |||||||||||||||
| 2688 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Local\Temp\Andy_46.16_66.exe" /RSF /ppn:YyhwYgxaFRAiP211FM5W /mnl | C:\Users\admin\AppData\Local\Temp\Andy_46.16_66.exe | Andy_46.16_66.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Pebede Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3628 | "C:\Users\admin\AppData\Local\Temp\Andy_46.16_66.exe" | C:\Users\admin\AppData\Local\Temp\Andy_46.16_66.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Pebede Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 4036 | "C:\Users\admin\AppData\Local\Temp\in68BAA86E\553D37DD_stp.exe" -sp--silent | C:\Users\admin\AppData\Local\Temp\in68BAA86E\553D37DD_stp.exe | Andy_46.16_66.exe | ||||||||||||
User: admin Company: Andy OS Inc. Integrity Level: HIGH Description: Andy OS Exit code: 1 Version: 47.0.146 Modules
| |||||||||||||||
Total events
988
Read events
948
Write events
40
Delete events
0
Modification events
| (PID) Process: | (3628) Andy_46.16_66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3628) Andy_46.16_66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3196) Andy_46.16_66.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3196) Andy_46.16_66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3196) Andy_46.16_66.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3196) Andy_46.16_66.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Andy_46_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3196) Andy_46.16_66.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Andy_46_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3196) Andy_46.16_66.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Andy_46_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3196) Andy_46.16_66.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Andy_46_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3196) Andy_46.16_66.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Andy_46_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
2
Suspicious files
1
Text files
96
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\001A8DDA.log | — | |
MD5:— | SHA256:— | |||
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\inH174025056766\installer.ico | image | |
MD5:— | SHA256:— | |||
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\inH174025056766\csshover3.htc | html | |
MD5:52FA0DA50BF4B27EE625C80D36C67941 | SHA256:E37E99DDFC73AC7BA774E23736B2EF429D9A0CB8C906453C75B14C029BDD5493 | |||
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\inH174025056766\css\sdk-ui\images\progress-bg.png | image | |
MD5:E9F12F92A9EEB8EBE911080721446687 | SHA256:C1CF449536BC2778E27348E45F0F53D04C284109199FB7A9AF7A61016B91F8BC | |||
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\inH174025056766\css\main.css | text | |
MD5:988507C4A7ED2E9DDE3974ED8F2AD453 | SHA256:AEB39FE1F27A17FE4A3CE0F6D7242C3EFF9ACC43CC849D2879C95B2AF6414111 | |||
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\inH174025056766\css\sdk-ui\browse.css | text | |
MD5:6009D6E864F60AEA980A9DF94C1F7E1C | SHA256:5EF48A8C8C3771B4F233314D50DD3B5AFDCD99DD4B74A9745C8FE7B22207056D | |||
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\inH174025056766\css\sdk-ui\images\button-bg.png | image | |
MD5:98B1DE48DFA64DC2AA1E52FACFBEE3B0 | SHA256:2693930C474FE640E2FE8D6EF98ABE2ECD303D2392C3D8B2E006E8942BA8F534 | |||
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\inH174025056766\css\sdk-ui\button.css | text | |
MD5:37E1FF96E084EC201F0D95FEEF4D5E94 | SHA256:8E806F5B94FC294E918503C8053EF1284E4F4B1E02C7DA4F4635E33EC33E0534 | |||
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\inH174025056766\css\ie6_main.css | text | |
MD5:FB95941D7AA47EAC4BE4AAAC0C0AF6A1 | SHA256:C228A33296F74C300E3095475849DF44ECFE6957487136D77D6C516D3A8FCC67 | |||
| 3628 | Andy_46.16_66.exe | C:\Users\admin\AppData\Local\Temp\inH174025056766\images\Loader.gif | image | |
MD5:AFC685139A108E33BD945D5A3FF64122 | SHA256:4D70F45A9C69D8CE2E630214C1B2871454D631CCF9D88976470170D0E106ACBC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
12
DNS requests
5
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
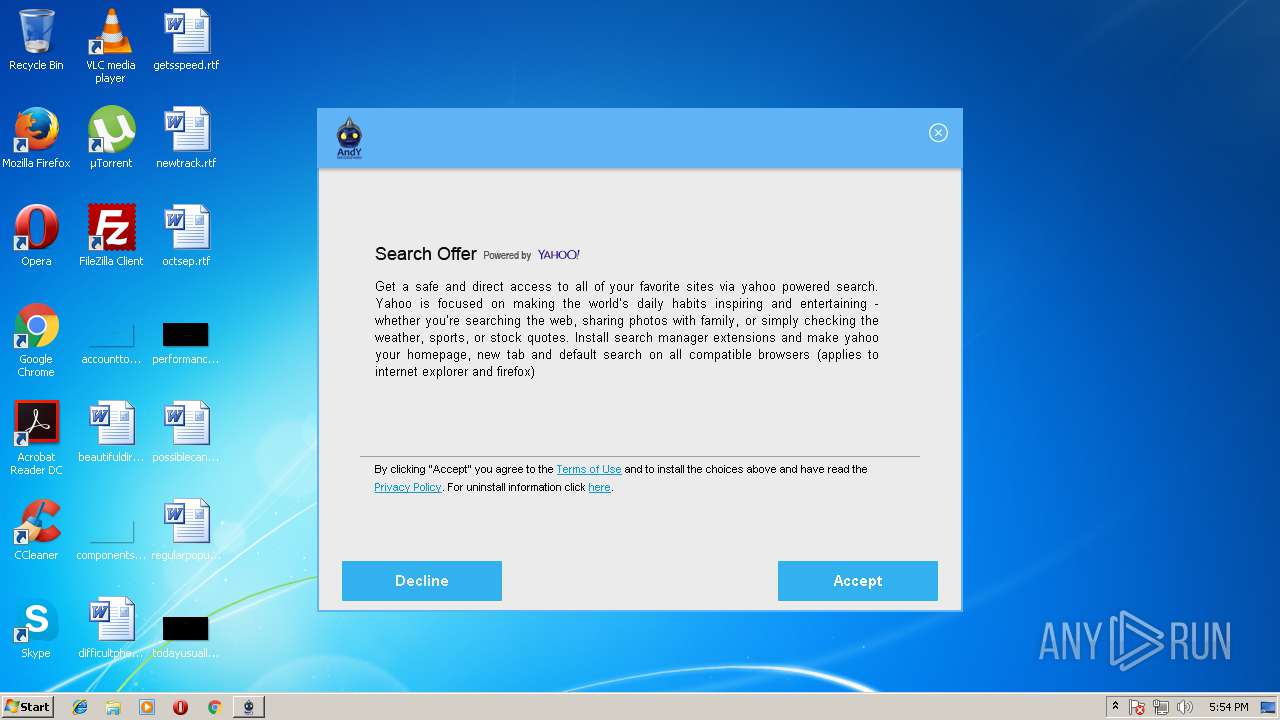
3196 | Andy_46.16_66.exe | POST | 200 | 54.72.212.121:80 | http://rp.nadosoyo.com/ | IE | — | — | malicious |
3196 | Andy_46.16_66.exe | POST | 200 | 54.72.212.121:80 | http://rp.nadosoyo.com/ | IE | — | — | malicious |
3196 | Andy_46.16_66.exe | POST | 200 | 34.251.155.7:80 | http://info.nadosoyo.com/?boyel=0 | IE | text | 896 b | malicious |
3196 | Andy_46.16_66.exe | POST | 200 | 54.72.212.121:80 | http://rp.nadosoyo.com/ | IE | — | — | malicious |
3196 | Andy_46.16_66.exe | POST | 200 | 54.72.212.121:80 | http://rp.nadosoyo.com/ | IE | — | — | malicious |
3196 | Andy_46.16_66.exe | GET | 200 | 209.95.37.242:80 | http://img.nadosoyo.com/img/Rowabobeso/icon1.png | US | image | 481 b | malicious |
3196 | Andy_46.16_66.exe | POST | 200 | 54.72.212.121:80 | http://rp.nadosoyo.com/ | IE | — | — | malicious |
3196 | Andy_46.16_66.exe | POST | 200 | 54.72.212.121:80 | http://rp.nadosoyo.com/ | IE | — | — | malicious |
3196 | Andy_46.16_66.exe | GET | 200 | 209.95.37.242:80 | http://img.nadosoyo.com/img/Rowabobeso/icon2.png | US | image | 422 b | malicious |
3196 | Andy_46.16_66.exe | GET | 200 | 209.95.37.242:80 | http://img.nadosoyo.com/img/Rowabobeso/b2_win_clean.png | US | image | 42.9 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3196 | Andy_46.16_66.exe | 54.72.212.121:80 | rp.nadosoyo.com | Amazon.com, Inc. | IE | unknown |
3196 | Andy_46.16_66.exe | 34.251.155.7:80 | info.nadosoyo.com | Amazon.com, Inc. | IE | whitelisted |
3196 | Andy_46.16_66.exe | 52.48.96.210:80 | os.nadosoyo.com | Amazon.com, Inc. | IE | whitelisted |
3196 | Andy_46.16_66.exe | 209.95.37.242:80 | img.nadosoyo.com | WestHost, Inc. | US | suspicious |
3196 | Andy_46.16_66.exe | 13.32.121.167:80 | downloads.andyroid.net | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rp.nadosoyo.com |
| unknown |
info.nadosoyo.com |
| malicious |
os.nadosoyo.com |
| malicious |
img.nadosoyo.com |
| malicious |
downloads.andyroid.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3196 | Andy_46.16_66.exe | Misc activity | [PT ADWARE] PUP.Optional.InstallCore Artifact M2 |
3196 | Andy_46.16_66.exe | Misc activity | [PT ADWARE] PUP.Optional.InstallCore Artifact M1 |
3196 | Andy_46.16_66.exe | Misc activity | [PT ADWARE] PUP.Optional.InstallCore Artifact M3 |
3196 | Andy_46.16_66.exe | Misc activity | [PT ADWARE] PUP.Optional.InstallCore Artifact M4 |
3196 | Andy_46.16_66.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
3196 | Andy_46.16_66.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |