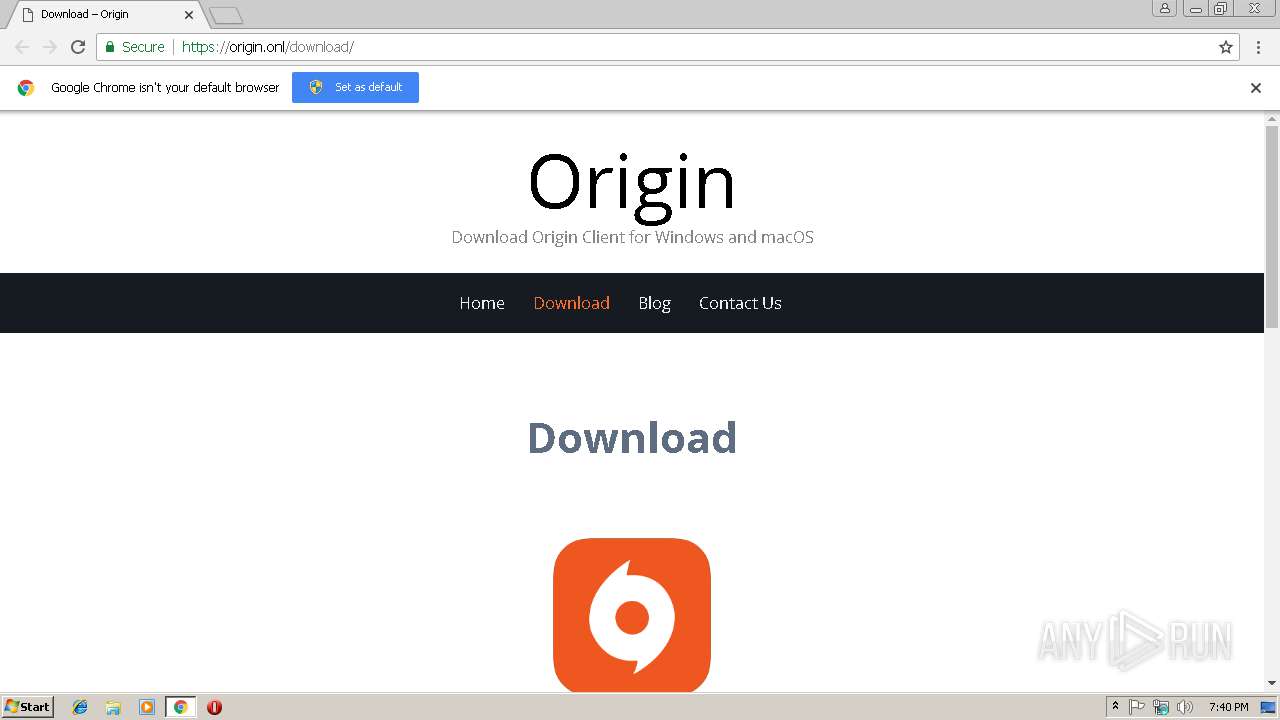
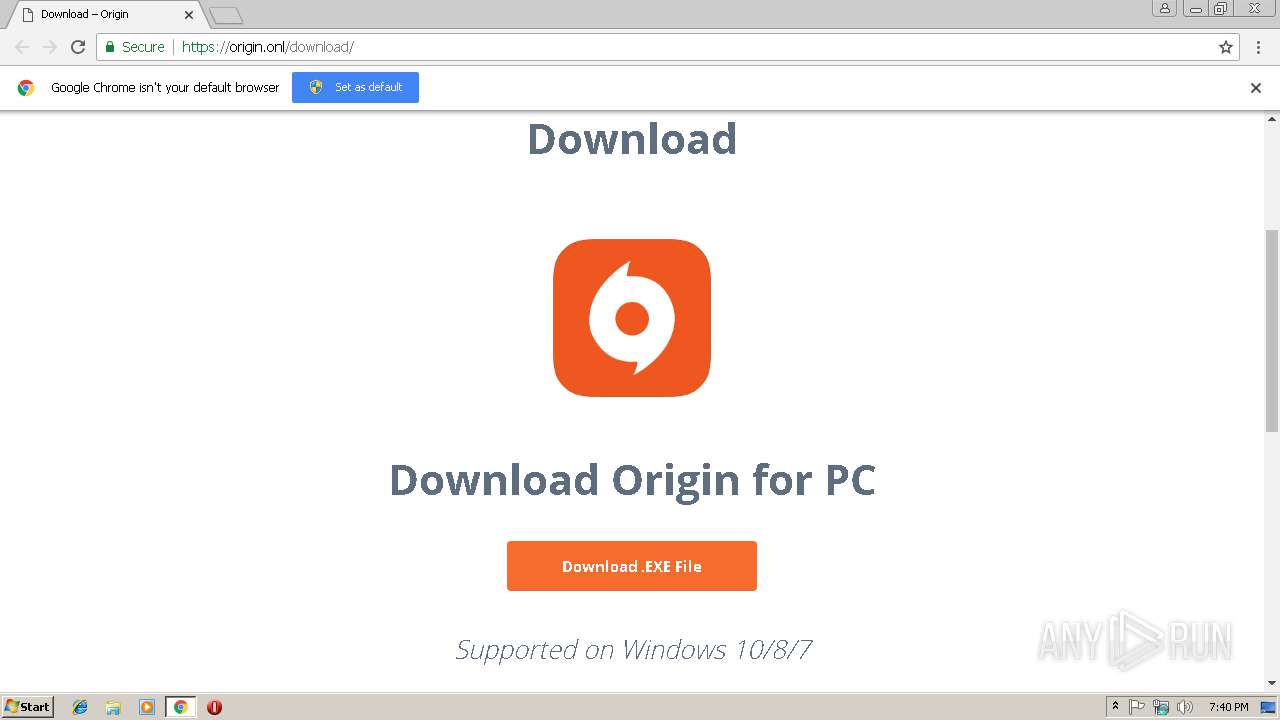
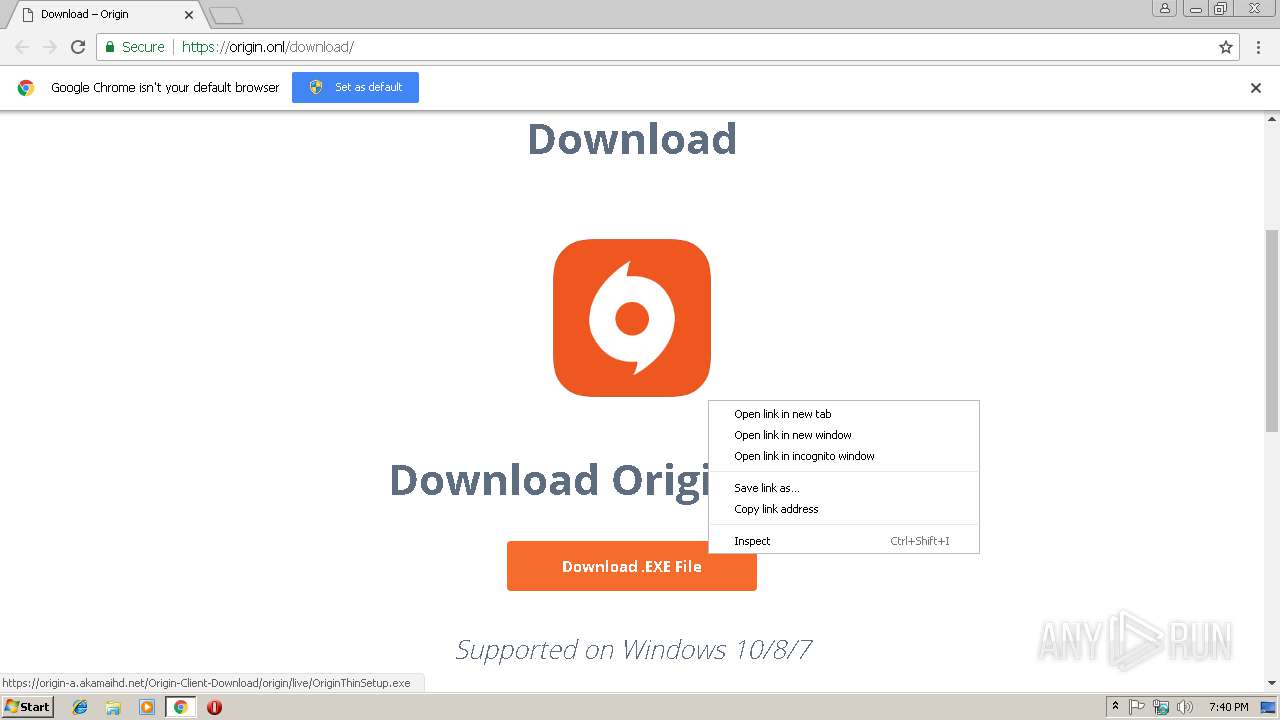
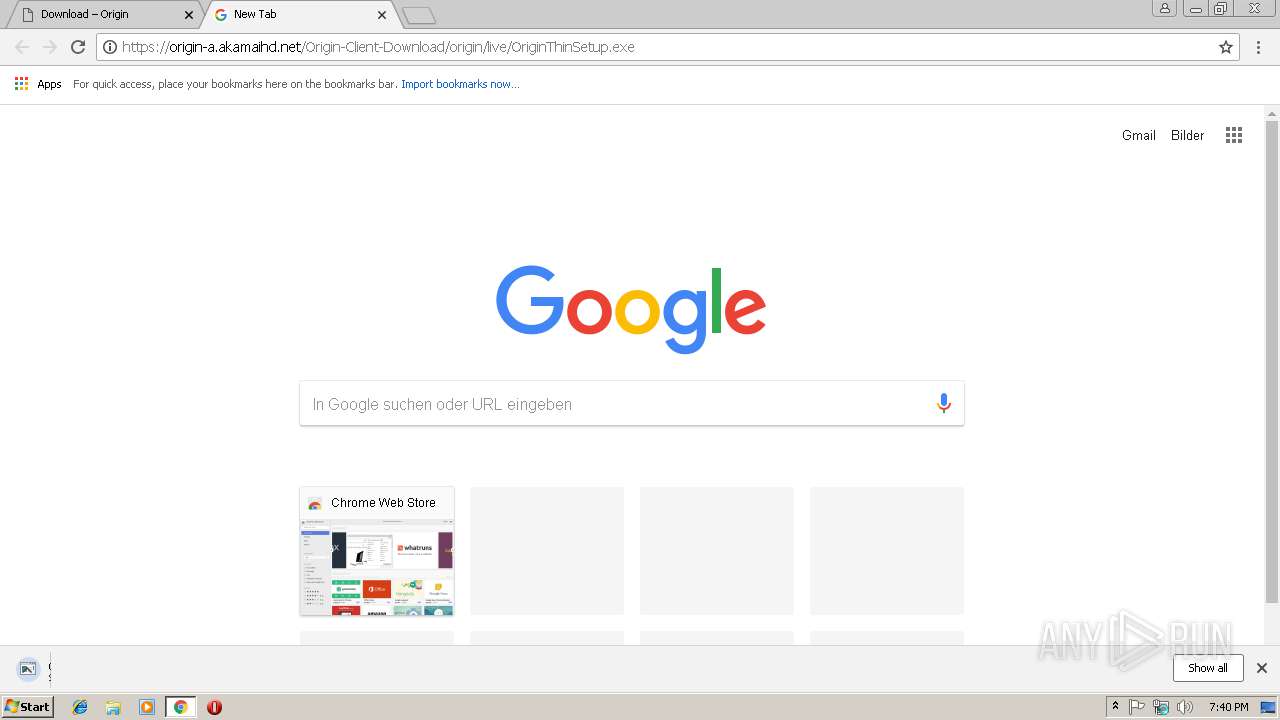
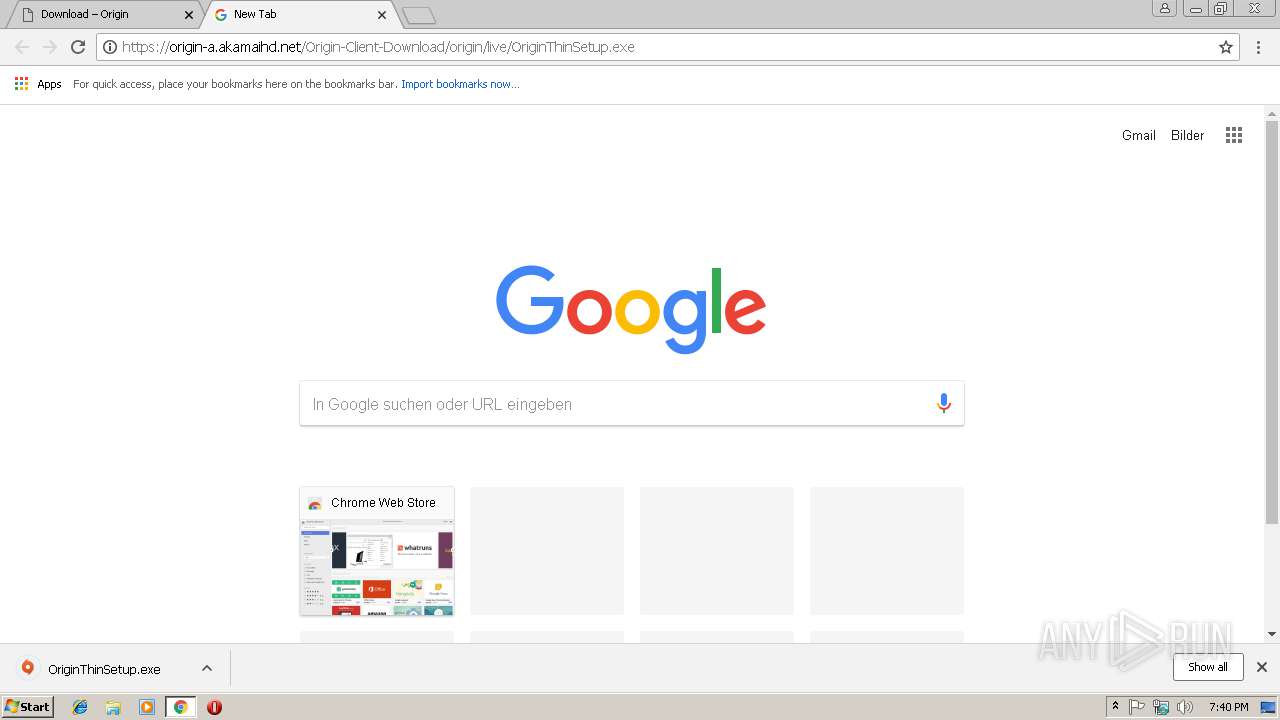
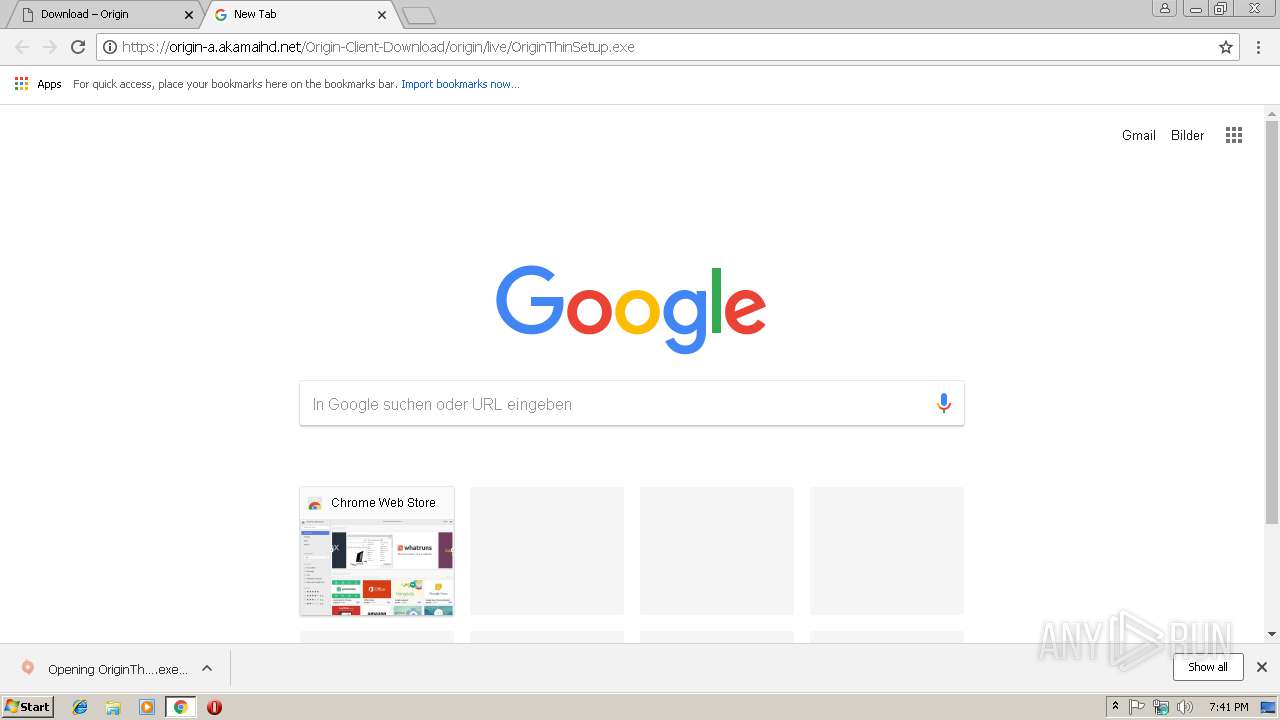
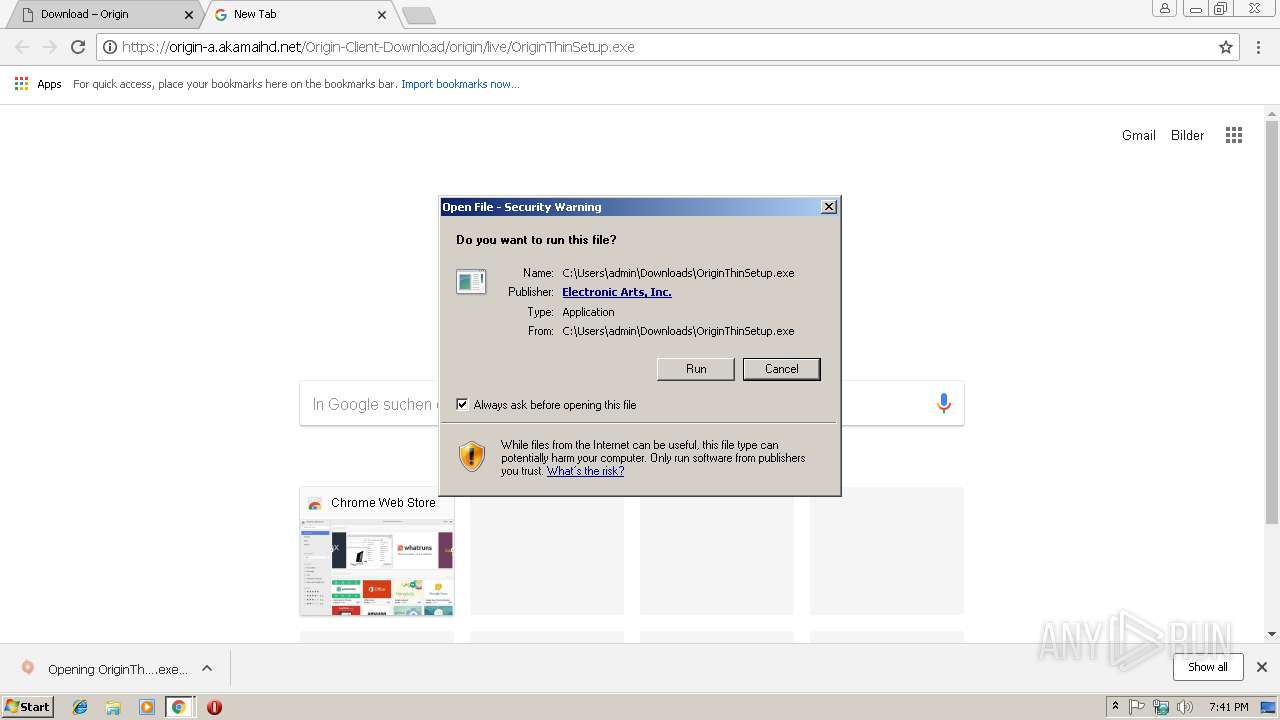
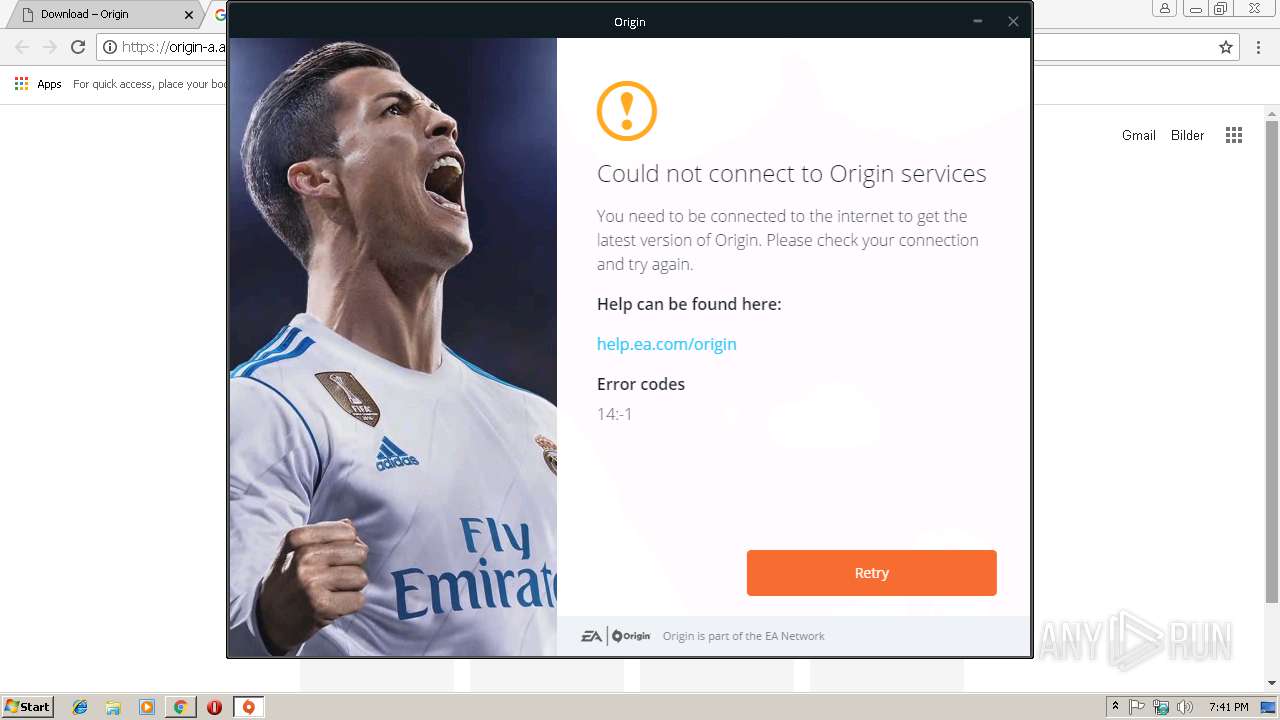
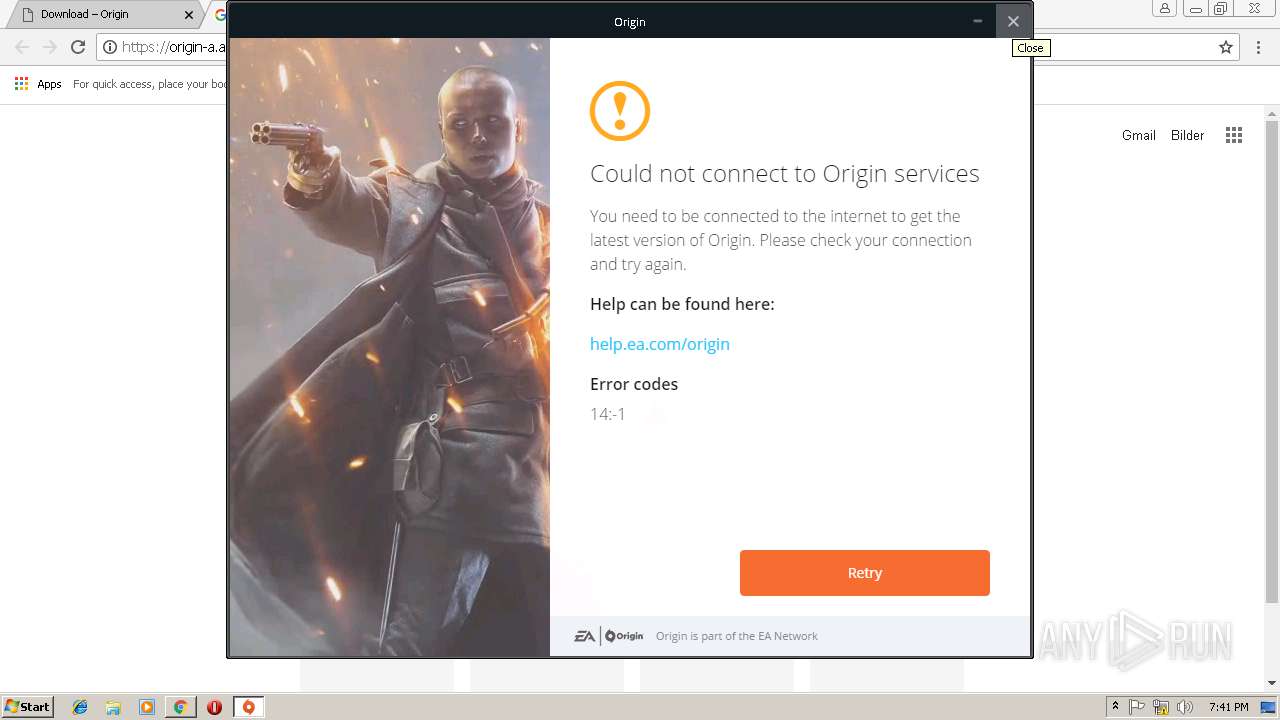
| URL: | https://origin.onl/download |
| Full analysis: | https://app.any.run/tasks/a23e5c92-214c-4e0c-b0ec-2a1f73adbc6b |
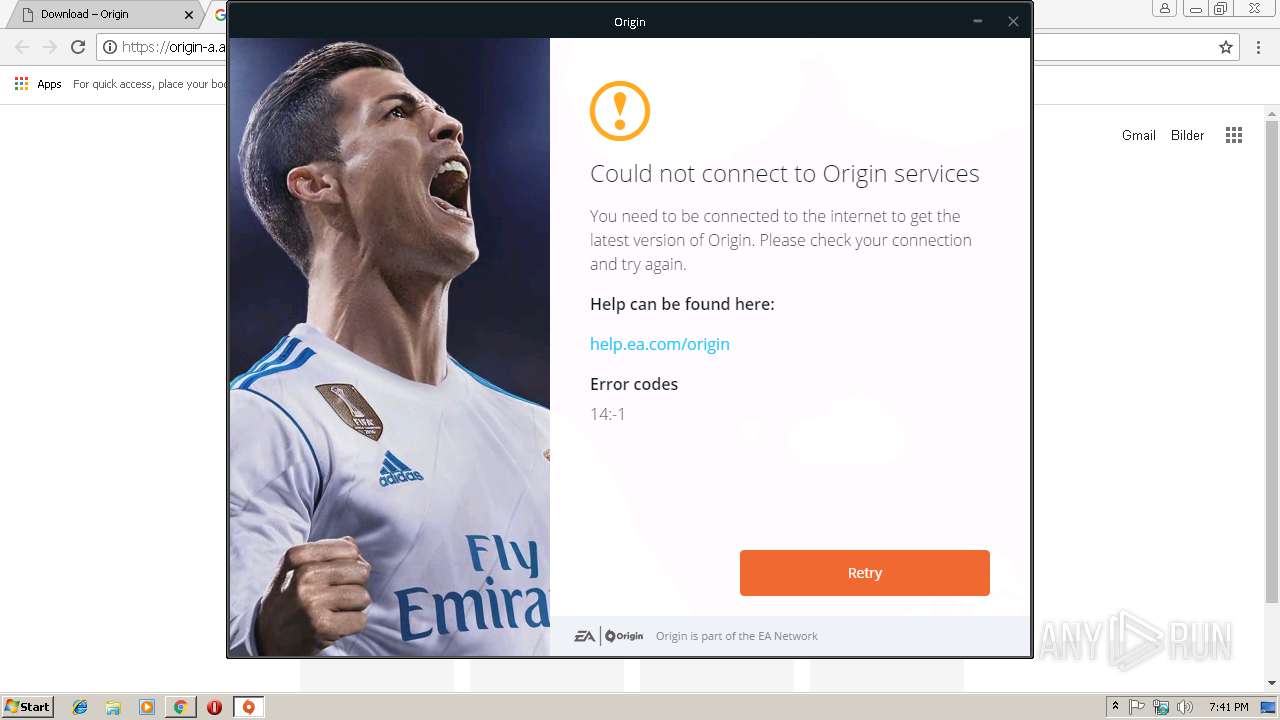
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2019, 19:40:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C85C563841FB3165AA5AC893466423FB |
| SHA1: | 1B3874CB9F374D4DB8958B0AABEBDCE02E7FB2E5 |
| SHA256: | CAA7654582F8C8DCF7C74C907BD3B6994068A58B86058E32B34F4AB37F71B0E4 |
| SSDEEP: | 3:N8eQLwK8S/:2eQLwk/ |
MALICIOUS
Application was dropped or rewritten from another process
- OriginThinSetup.exe (PID: 2844)
- QtWebEngineProcess.exe (PID: 2212)
- QtWebEngineProcess.exe (PID: 2956)
- OriginThinSetupInternal.exe (PID: 4012)
- QtWebEngineProcess.exe (PID: 3452)
Loads dropped or rewritten executable
- OriginThinSetupInternal.exe (PID: 4012)
- QtWebEngineProcess.exe (PID: 2212)
- QtWebEngineProcess.exe (PID: 2956)
- QtWebEngineProcess.exe (PID: 3452)
SUSPICIOUS
Executable content was dropped or overwritten
- OriginThinSetupInternal.exe (PID: 4012)
- chrome.exe (PID: 3012)
- OriginThinSetup.exe (PID: 2844)
Creates files in the program directory
- OriginThinSetupInternal.exe (PID: 4012)
Creates files in the user directory
- OriginThinSetupInternal.exe (PID: 4012)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 3012)
Application launched itself
- chrome.exe (PID: 3012)
Dropped object may contain Bitcoin addresses
- OriginThinSetup.exe (PID: 2844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
15
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=119E810C4395F81FD9BAB99EC352A329 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=119E810C4395F81FD9BAB99EC352A329 --renderer-client-id=6 --mojo-platform-channel-handle=3492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=11BFF5CE3237868FC9DA1CE0606B0AEB --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=234BD23DD865E1DEBFCC268BF09306B7 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=234BD23DD865E1DEBFCC268BF09306B7 --renderer-client-id=7 --mojo-platform-channel-handle=3880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=D4902CA316AEC43B47852333398CC36A --mojo-platform-channel-handle=2756 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2212 | "C:\Users\admin\AppData\Local\Origin\ThinSetup\10.5.34.21025\QtWebEngineProcess.exe" --type=renderer --disable-accelerated-video-decode --disable-gpu-memory-buffer-video-frames --enable-threaded-compositing --no-sandbox --disable-webrtc-hw-encoding --primordial-pipe-token=CF666D643190168BF16203F70BA9740F --lang=en-US --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --disable-gpu-compositing --mojo-channel-token=930C85087A54AC6125C7BD20922A5BC7 --mojo-application-channel-token=CF666D643190168BF16203F70BA9740F --channel="4012.0.662463093\154341535" --mojo-platform-channel-handle=1476 /prefetch:1 | C:\Users\admin\AppData\Local\Origin\ThinSetup\10.5.34.21025\QtWebEngineProcess.exe | OriginThinSetupInternal.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=908,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=06F0BD09BF34A85C3225DBD6B4656207 --mojo-platform-channel-handle=3924 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --renderer-client-id=4 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2844 | "C:\Users\admin\Downloads\OriginThinSetup.exe" | C:\Users\admin\Downloads\OriginThinSetup.exe | chrome.exe | ||||||||||||
User: admin Company: Electronic Arts Integrity Level: MEDIUM Description: OriginThinSetup Exit code: 0 Version: 10,5,34,21025 Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Origin\ThinSetup\10.5.34.21025\QtWebEngineProcess.exe" --type=renderer --disable-accelerated-video-decode --disable-gpu-memory-buffer-video-frames --enable-threaded-compositing --no-sandbox --disable-webrtc-hw-encoding --primordial-pipe-token=57D5137DA93B8384F40D0E508B25556C --lang=en-US --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --content-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --video-image-texture-target=3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553,3553 --disable-gpu-compositing --mojo-channel-token=221E4344A4C8A40C2044C1ECC35F44D9 --mojo-application-channel-token=57D5137DA93B8384F40D0E508B25556C --channel="4012.1.1716333371\1819443383" --mojo-platform-channel-handle=1520 /prefetch:1 | C:\Users\admin\AppData\Local\Origin\ThinSetup\10.5.34.21025\QtWebEngineProcess.exe | OriginThinSetupInternal.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3016 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
875
Read events
821
Write events
51
Delete events
3
Modification events
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3012-13194042038975750 |
Value: 259 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3012-13194042038975750 |
Value: 259 | |||
| (PID) Process: | (3012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
75
Suspicious files
57
Text files
82
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fef9a774-9f4f-4c4d-9da5-b2421317aaf2.tmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\479fdf4c-3758-47f5-950b-0ba7aec0d214.tmp | — | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e860.TMP | text | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF20e87f.TMP | text | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model~RF20eb1f.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
21
DNS requests
14
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3012 | chrome.exe | 75.119.210.224:443 | origin.onl | New Dream Network, LLC | US | unknown |
3012 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 172.217.16.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 172.217.23.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
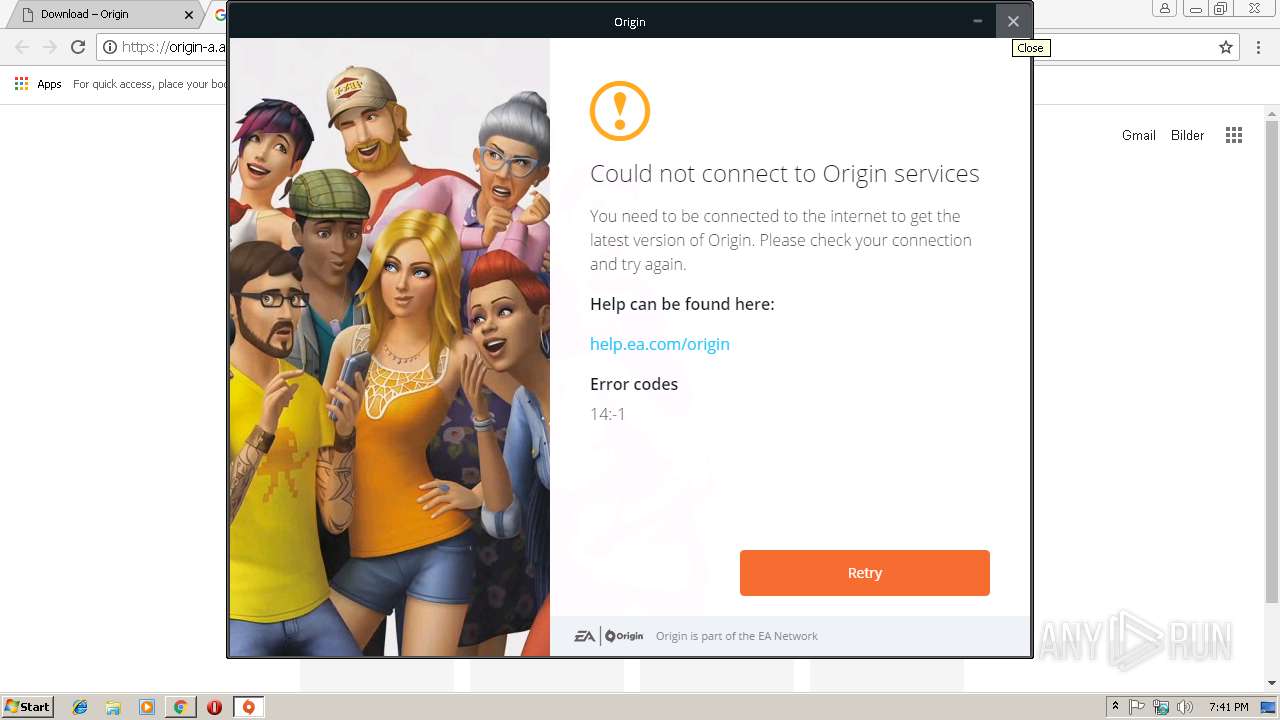
3012 | chrome.exe | 2.16.186.88:443 | origin-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
3012 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
origin.onl |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s.w.org |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
OriginThinSetupInternal.exe | QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
OriginThinSetupInternal.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
OriginThinSetupInternal.exe | QString::arg: 1 argument(s) missing in https://api1.origin.com/autopatch/2/upgradeFrom/%1/%2/%3?platform=%4&osVersion=%5
|
OriginThinSetupInternal.exe | QObject::connect: Cannot connect (null)::userConnectionStateChanged(bool, Origin::Services::Session::SessionRef) to Origin::Services::HttpServiceResponse::onConnectionStateChanged(bool, Origin::Services::Session::SessionRef)
|
OriginThinSetupInternal.exe | QObject::connect: Cannot connect (null)::globalConnectionStateChanged(bool) to Origin::Services::HttpServiceResponse::onGlobalConnectionStateChanged(bool)
|
OriginThinSetupInternal.exe | QIODevice::read (QNetworkReply): device not open
|
OriginThinSetupInternal.exe | QIODevice::read (QNetworkReply): device not open
|
OriginThinSetupInternal.exe | Qt WebEngine ICU data not found at C:/Qt/5.8.0/qtbase/resources. Trying parent directory...
|
OriginThinSetupInternal.exe | Qt WebEngine ICU data not found at C:/Qt/5.8.0/qtbase. Trying application directory...
|
OriginThinSetupInternal.exe | Installed Qt WebEngine locales directory not found at location C:/Qt/5.8.0/qtbase/translations\qtwebengine_locales. Trying application directory...
|