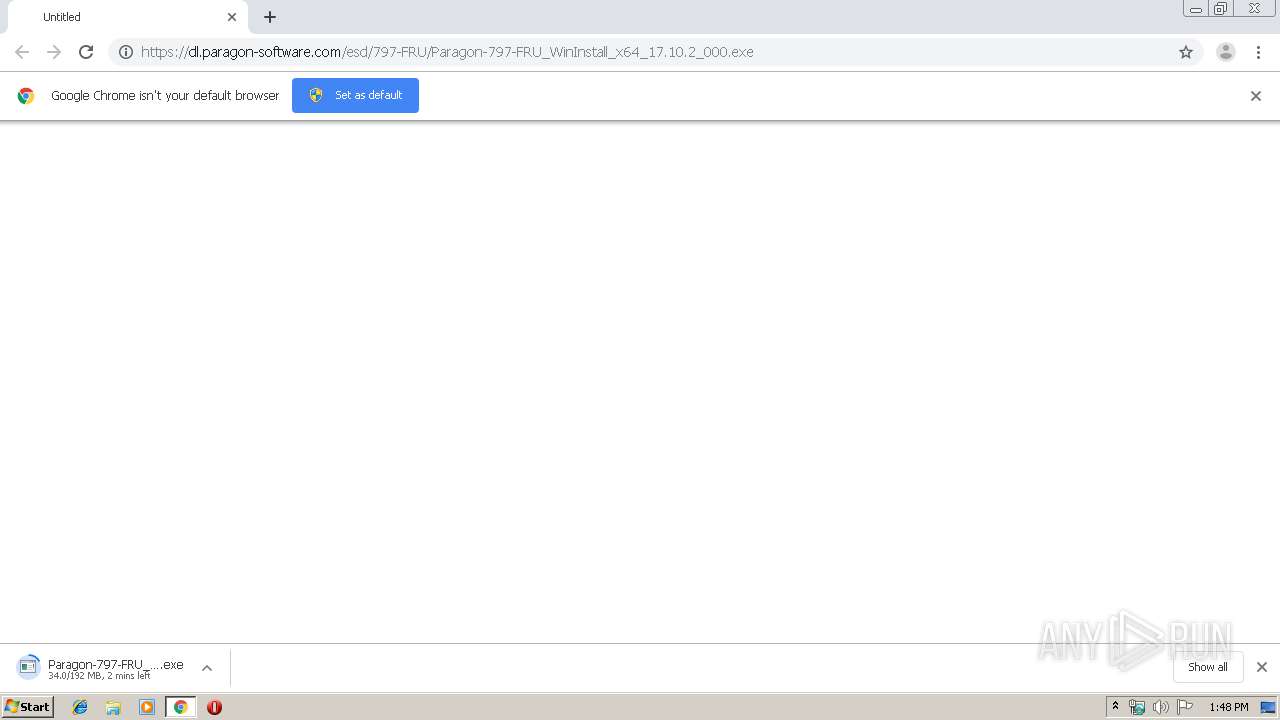
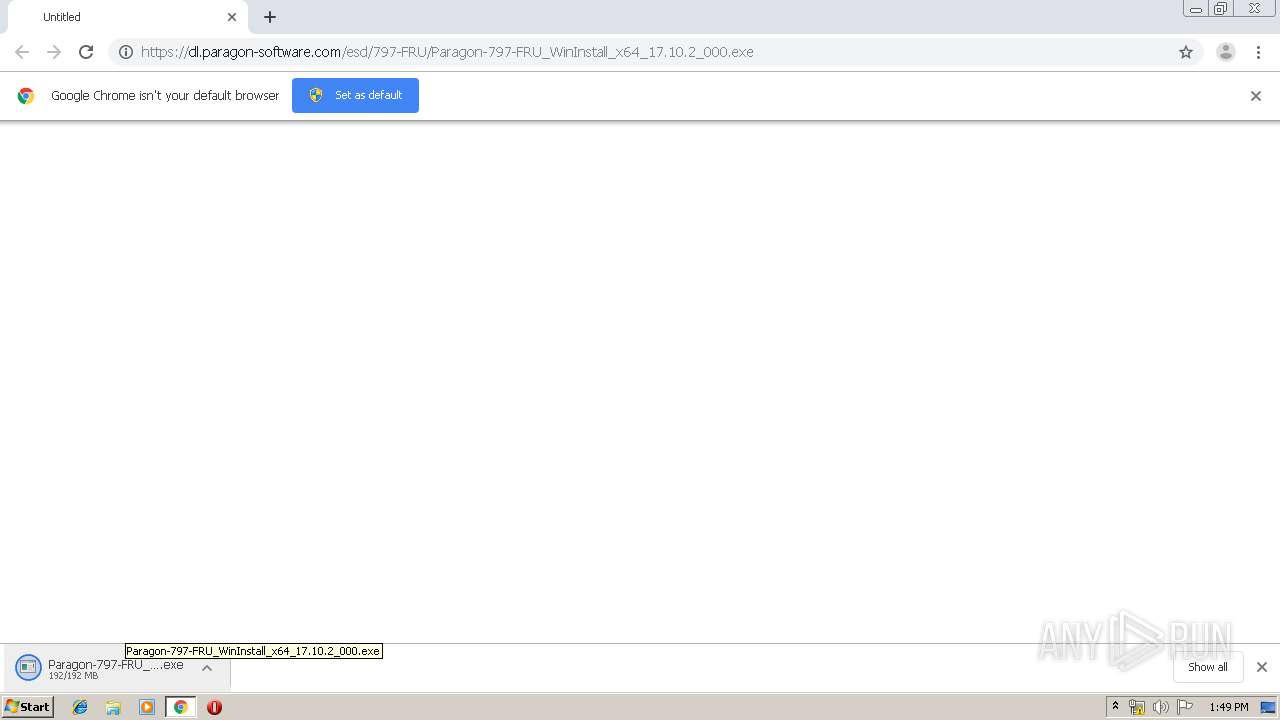
| URL: | https://dl.paragon-software.com/esd/797-FRU/Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe |
| Full analysis: | https://app.any.run/tasks/16a830ae-ed9a-4363-8a09-5cfd7114595a |
| Verdict: | Malicious activity |
| Analysis date: | December 22, 2019, 13:47:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D329D6549D4810ACB0247D47F4FA4261 |
| SHA1: | DC53B0216FD2CEE2F8496FFCF6BECB38E07B2407 |
| SHA256: | CAA201C248025BCDE6EFFF5D23AC1A37D67F07E2D680BBDEBD3E4489C206B180 |
| SSDEEP: | 3:N8RSXeHFwGJ80Qvc7LPynJ0hV4Nn:2+PG4E7TynJ0D4n |
MALICIOUS
Application was dropped or rewritten from another process
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 2508)
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 3100)
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 1416)
Loads dropped or rewritten executable
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 1416)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2108)
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 3100)
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 1416)
Creates files in the Windows directory
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 3100)
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 1416)
Removes files from Windows directory
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 3100)
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 1416)
INFO
Reads the hosts file
- chrome.exe (PID: 2108)
- chrome.exe (PID: 3976)
Reads settings of System Certificates
- chrome.exe (PID: 3976)
Application launched itself
- chrome.exe (PID: 2108)
Reads Internet Cache Settings
- chrome.exe (PID: 2108)
Dropped object may contain Bitcoin addresses
- Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe (PID: 1416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,3207724735020144132,8011526629135158438,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11644165681902398760 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
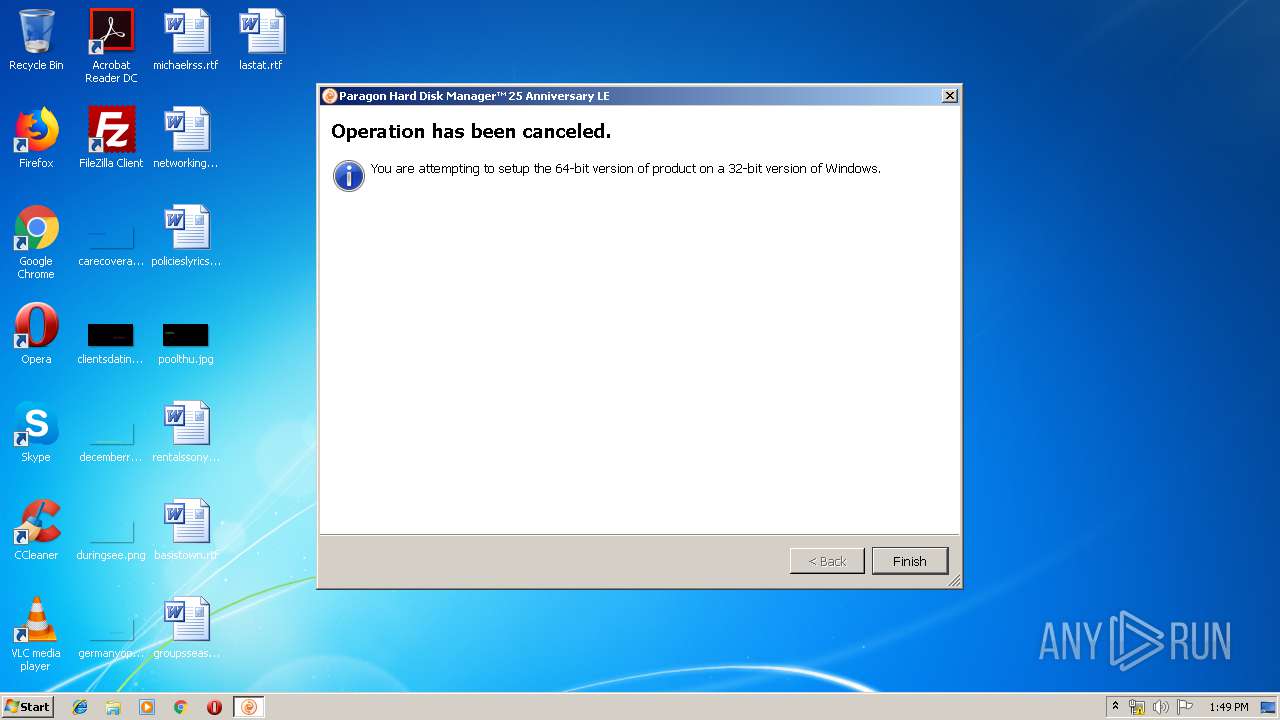
| 1416 | "C:\Windows\Temp\{A011A33A-B097-47A5-ADD1-14365AEF1A57}\.cr\Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe" -burn.clean.room="C:\Users\admin\Downloads\Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Windows\Temp\{A011A33A-B097-47A5-ADD1-14365AEF1A57}\.cr\Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe | Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe | ||||||||||||
User: admin Company: Paragon Software GmbH Integrity Level: HIGH Description: Paragon Hard Disk Manager™ 25 Anniversary LE Exit code: 1 Version: 17.10.2.5049 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,3207724735020144132,8011526629135158438,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10675799182476559391 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3180 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,3207724735020144132,8011526629135158438,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16920272561717183026 --mojo-platform-channel-handle=1160 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://dl.paragon-software.com/esd/797-FRU/Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,3207724735020144132,8011526629135158438,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5091287728970815359 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ed2a9d0,0x6ed2a9e0,0x6ed2a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\Downloads\Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe" | C:\Users\admin\Downloads\Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe | — | chrome.exe | |||||||||||
User: admin Company: Paragon Software GmbH Integrity Level: MEDIUM Description: Paragon Hard Disk Manager™ 25 Anniversary LE Exit code: 3221226540 Version: 17.10.2.5049 Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\Downloads\Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe" | C:\Users\admin\Downloads\Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe | chrome.exe | ||||||||||||
User: admin Company: Paragon Software GmbH Integrity Level: HIGH Description: Paragon Hard Disk Manager™ 25 Anniversary LE Exit code: 1 Version: 17.10.2.5049 Modules
| |||||||||||||||
Total events
949
Read events
868
Write events
78
Delete events
3
Modification events
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2108-13221496068287875 |
Value: 259 | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2108) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
17
Suspicious files
22
Text files
101
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\52aa218c-ef17-4a03-ae2c-909b4154e1f3.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a8be.TMP | text | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a8cd.TMP | text | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a8dd.TMP | text | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3976 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 216.58.207.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 172.217.22.99:443 | — | Google Inc. | US | whitelisted |
3976 | chrome.exe | 13.35.253.21:443 | dl.paragon-software.com | — | US | suspicious |
3976 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3976 | chrome.exe | 172.217.16.142:443 | — | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
dl.paragon-software.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Paragon-797-FRU_WinInstall_x64_17.10.2_000.exe | QObject::~QObject: Timers cannot be stopped from another thread
|