| File name: | Bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/24c69807-0e52-4cea-94cc-74a5ddc920ee |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2024, 21:57:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 71F9ACC8A05119570909A439AB55DAD7 |
| SHA1: | C84A8F6554207AE3604E7D8CE7AE6890A67ED28B |
| SHA256: | CA854ACB38A73997E862F7693D0E60ADF75B22D7B6626AE66260713079FBD3F4 |
| SSDEEP: | 98304:VqN8ppo+JprMqI4vJaX6j+MuUJwxexfjKAQQVc6bW/g84zg7WJFKoX0pSBEXBZ4V:O6i/gps7MtXUDXBZtiuoqPao |
MALICIOUS
Adds extension to the Windows Defender exclusion list
- setup.exe (PID: 1612)
SUSPICIOUS
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 1020)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 7160)
- Bootstrapper.exe (PID: 6488)
- Bootstrapper.exe (PID: 6728)
- Bootstrapper.exe (PID: 6444)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 4820)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 2328)
- Bootstrapper.exe (PID: 6332)
- Bootstrapper.exe (PID: 6236)
- Bootstrapper.exe (PID: 3648)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 7116)
- Bootstrapper.exe (PID: 4824)
- Bootstrapper.exe (PID: 3708)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 5060)
- Bootstrapper.exe (PID: 2144)
- Bootstrapper.exe (PID: 4680)
- Bootstrapper.exe (PID: 3076)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7560)
- Bootstrapper.exe (PID: 7696)
- Bootstrapper.exe (PID: 8092)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 7464)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7568)
Base64-obfuscated command line is found
- Bootstrapper.exe (PID: 1020)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 7160)
- Bootstrapper.exe (PID: 6488)
- Bootstrapper.exe (PID: 6444)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 6728)
- Bootstrapper.exe (PID: 4820)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 2328)
- Bootstrapper.exe (PID: 6332)
- Bootstrapper.exe (PID: 6236)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 3648)
- Bootstrapper.exe (PID: 7116)
- Bootstrapper.exe (PID: 4824)
- Bootstrapper.exe (PID: 3708)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 2144)
- Bootstrapper.exe (PID: 4680)
- Bootstrapper.exe (PID: 5060)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 3076)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7696)
- Bootstrapper.exe (PID: 7560)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 8092)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 7464)
- Bootstrapper.exe (PID: 9208)
- Bootstrapper.exe (PID: 9428)
- Bootstrapper.exe (PID: 9780)
- Bootstrapper.exe (PID: 8484)
- Bootstrapper.exe (PID: 10088)
- Bootstrapper.exe (PID: 9676)
- Bootstrapper.exe (PID: 10016)
- Bootstrapper.exe (PID: 10404)
- Bootstrapper.exe (PID: 10660)
- Bootstrapper.exe (PID: 3508)
- Bootstrapper.exe (PID: 9592)
- Bootstrapper.exe (PID: 11696)
- Bootstrapper.exe (PID: 11492)
- Bootstrapper.exe (PID: 11948)
- Bootstrapper.exe (PID: 4076)
- Bootstrapper.exe (PID: 4520)
- Bootstrapper.exe (PID: 12412)
- Bootstrapper.exe (PID: 13012)
- Bootstrapper.exe (PID: 13244)
- Bootstrapper.exe (PID: 1636)
- Bootstrapper.exe (PID: 8840)
- Bootstrapper.exe (PID: 1148)
- Bootstrapper.exe (PID: 11952)
- Bootstrapper.exe (PID: 6288)
- Bootstrapper.exe (PID: 5248)
- Bootstrapper.exe (PID: 9484)
- Bootstrapper.exe (PID: 4540)
- Bootstrapper.exe (PID: 7540)
- Bootstrapper.exe (PID: 9336)
- Bootstrapper.exe (PID: 8508)
- Bootstrapper.exe (PID: 2900)
- Bootstrapper.exe (PID: 7000)
- Bootstrapper.exe (PID: 4604)
- Bootstrapper.exe (PID: 6404)
- Bootstrapper.exe (PID: 9092)
Starts POWERSHELL.EXE for commands execution
- Bootstrapper.exe (PID: 1020)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 7160)
- Bootstrapper.exe (PID: 6488)
- Bootstrapper.exe (PID: 6444)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 6728)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 4820)
- Bootstrapper.exe (PID: 2328)
- Bootstrapper.exe (PID: 6332)
- Bootstrapper.exe (PID: 6236)
- Bootstrapper.exe (PID: 3648)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 7116)
- Bootstrapper.exe (PID: 4824)
- Bootstrapper.exe (PID: 3708)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 2144)
- Bootstrapper.exe (PID: 4680)
- Bootstrapper.exe (PID: 5060)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 3076)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7696)
- Bootstrapper.exe (PID: 7560)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 8092)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 7464)
- Bootstrapper.exe (PID: 8484)
- Bootstrapper.exe (PID: 9208)
- Bootstrapper.exe (PID: 9780)
- Bootstrapper.exe (PID: 9428)
- Bootstrapper.exe (PID: 10088)
- Bootstrapper.exe (PID: 10016)
- Bootstrapper.exe (PID: 9676)
- setup.exe (PID: 1612)
- Bootstrapper.exe (PID: 10404)
- Bootstrapper.exe (PID: 10660)
- Bootstrapper.exe (PID: 3508)
- Bootstrapper.exe (PID: 9592)
- Bootstrapper.exe (PID: 11492)
- Bootstrapper.exe (PID: 11696)
- Bootstrapper.exe (PID: 11948)
- Bootstrapper.exe (PID: 4076)
- Bootstrapper.exe (PID: 4520)
- Bootstrapper.exe (PID: 12412)
- Bootstrapper.exe (PID: 13012)
- Bootstrapper.exe (PID: 13244)
- Bootstrapper.exe (PID: 8840)
- Bootstrapper.exe (PID: 11952)
- Bootstrapper.exe (PID: 6288)
- Bootstrapper.exe (PID: 1636)
- Bootstrapper.exe (PID: 1148)
- Bootstrapper.exe (PID: 5248)
- Bootstrapper.exe (PID: 9484)
- Bootstrapper.exe (PID: 4540)
- Bootstrapper.exe (PID: 9336)
- Bootstrapper.exe (PID: 8508)
- Bootstrapper.exe (PID: 7540)
- Bootstrapper.exe (PID: 7000)
- Bootstrapper.exe (PID: 2900)
- Bootstrapper.exe (PID: 6404)
- Bootstrapper.exe (PID: 9092)
- Bootstrapper.exe (PID: 4604)
BASE64 encoded PowerShell command has been detected
- Bootstrapper.exe (PID: 1020)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 6488)
- Bootstrapper.exe (PID: 7160)
- Bootstrapper.exe (PID: 6444)
- Bootstrapper.exe (PID: 6728)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 4820)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 2328)
- Bootstrapper.exe (PID: 6332)
- Bootstrapper.exe (PID: 6236)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 3648)
- Bootstrapper.exe (PID: 7116)
- Bootstrapper.exe (PID: 4824)
- Bootstrapper.exe (PID: 3708)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 2144)
- Bootstrapper.exe (PID: 5060)
- Bootstrapper.exe (PID: 4680)
- Bootstrapper.exe (PID: 3076)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7696)
- Bootstrapper.exe (PID: 7560)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 8092)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 7464)
- Bootstrapper.exe (PID: 9208)
- Bootstrapper.exe (PID: 9428)
- Bootstrapper.exe (PID: 9780)
- Bootstrapper.exe (PID: 8484)
- Bootstrapper.exe (PID: 10088)
- Bootstrapper.exe (PID: 9676)
- Bootstrapper.exe (PID: 10016)
- Bootstrapper.exe (PID: 10404)
- Bootstrapper.exe (PID: 10660)
- Bootstrapper.exe (PID: 3508)
- Bootstrapper.exe (PID: 9592)
- Bootstrapper.exe (PID: 11492)
- Bootstrapper.exe (PID: 11696)
- Bootstrapper.exe (PID: 11948)
- Bootstrapper.exe (PID: 4076)
- Bootstrapper.exe (PID: 4520)
- Bootstrapper.exe (PID: 12412)
- Bootstrapper.exe (PID: 13012)
- Bootstrapper.exe (PID: 1636)
- Bootstrapper.exe (PID: 13244)
- Bootstrapper.exe (PID: 1148)
- Bootstrapper.exe (PID: 6288)
- Bootstrapper.exe (PID: 11952)
- Bootstrapper.exe (PID: 8840)
- Bootstrapper.exe (PID: 9484)
- Bootstrapper.exe (PID: 4540)
- Bootstrapper.exe (PID: 7540)
- Bootstrapper.exe (PID: 5248)
- Bootstrapper.exe (PID: 7000)
- Bootstrapper.exe (PID: 9336)
- Bootstrapper.exe (PID: 8508)
- Bootstrapper.exe (PID: 2900)
- Bootstrapper.exe (PID: 4604)
- Bootstrapper.exe (PID: 6404)
- Bootstrapper.exe (PID: 9092)
Application launched itself
- Bootstrapper.exe (PID: 1020)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 7160)
- Bootstrapper.exe (PID: 6488)
- Bootstrapper.exe (PID: 6444)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 6728)
- Bootstrapper.exe (PID: 4820)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 2328)
- Bootstrapper.exe (PID: 6332)
- Bootstrapper.exe (PID: 6236)
- Bootstrapper.exe (PID: 3648)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 7116)
- Bootstrapper.exe (PID: 4824)
- Bootstrapper.exe (PID: 3708)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 2144)
- Bootstrapper.exe (PID: 4680)
- Bootstrapper.exe (PID: 5060)
- Bootstrapper.exe (PID: 3076)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7696)
- Bootstrapper.exe (PID: 7560)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 8092)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7464)
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 8484)
- Bootstrapper.exe (PID: 9208)
- Bootstrapper.exe (PID: 9428)
- Bootstrapper.exe (PID: 10088)
- Bootstrapper.exe (PID: 9676)
- Bootstrapper.exe (PID: 10016)
- Bootstrapper.exe (PID: 9780)
- Bootstrapper.exe (PID: 9592)
- Bootstrapper.exe (PID: 10404)
- Bootstrapper.exe (PID: 10660)
- Bootstrapper.exe (PID: 11492)
- Bootstrapper.exe (PID: 11696)
- Bootstrapper.exe (PID: 11948)
- Bootstrapper.exe (PID: 3508)
- Bootstrapper.exe (PID: 4520)
- Bootstrapper.exe (PID: 12412)
- Bootstrapper.exe (PID: 13012)
- Bootstrapper.exe (PID: 13244)
- Bootstrapper.exe (PID: 4076)
- Bootstrapper.exe (PID: 1148)
- Bootstrapper.exe (PID: 8840)
- Bootstrapper.exe (PID: 11952)
- Bootstrapper.exe (PID: 1636)
- Bootstrapper.exe (PID: 5248)
- Bootstrapper.exe (PID: 4540)
- Bootstrapper.exe (PID: 9484)
- Bootstrapper.exe (PID: 6288)
- Bootstrapper.exe (PID: 9336)
- Bootstrapper.exe (PID: 7000)
- Bootstrapper.exe (PID: 2900)
- Bootstrapper.exe (PID: 8508)
- Bootstrapper.exe (PID: 7540)
- Bootstrapper.exe (PID: 9092)
- Bootstrapper.exe (PID: 4604)
Executable content was dropped or overwritten
- Bootstrapper.exe (PID: 1020)
- setup.exe (PID: 1612)
Script adds exclusion extension to Windows Defender
- setup.exe (PID: 1612)
Script adds exclusion path to Windows Defender
- setup.exe (PID: 1612)
Starts SC.EXE for service management
- setup.exe (PID: 1612)
Starts CMD.EXE for commands execution
- setup.exe (PID: 1612)
Uses powercfg.exe to modify the power settings
- setup.exe (PID: 1612)
Process uninstalls Windows update
- wusa.exe (PID: 9060)
Executes as Windows Service
- updater.exe (PID: 11044)
INFO
Checks supported languages
- Bootstrapper.exe (PID: 1020)
- setup.exe (PID: 1612)
- Bootstrapper.exe (PID: 7160)
- setup.exe (PID: 5908)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 6488)
- setup.exe (PID: 1384)
- Bootstrapper.exe (PID: 6444)
- setup.exe (PID: 5292)
- Bootstrapper.exe (PID: 6728)
- setup.exe (PID: 2576)
- Bootstrapper.exe (PID: 6272)
- setup.exe (PID: 4540)
- Bootstrapper.exe (PID: 4820)
- setup.exe (PID: 4780)
- setup.exe (PID: 4784)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 2328)
- setup.exe (PID: 6536)
- Bootstrapper.exe (PID: 6332)
- setup.exe (PID: 6232)
- Bootstrapper.exe (PID: 6236)
- setup.exe (PID: 7076)
- Bootstrapper.exe (PID: 3648)
- setup.exe (PID: 6396)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 7116)
- setup.exe (PID: 2464)
- setup.exe (PID: 5244)
- Bootstrapper.exe (PID: 4824)
- setup.exe (PID: 5736)
- setup.exe (PID: 1808)
- Bootstrapper.exe (PID: 3708)
- setup.exe (PID: 1072)
- Bootstrapper.exe (PID: 6272)
- setup.exe (PID: 2580)
- Bootstrapper.exe (PID: 2144)
- setup.exe (PID: 1640)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 5060)
- setup.exe (PID: 6840)
- setup.exe (PID: 2268)
- Bootstrapper.exe (PID: 3076)
- setup.exe (PID: 7188)
- Bootstrapper.exe (PID: 4680)
- setup.exe (PID: 7312)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 7560)
- setup.exe (PID: 7580)
- setup.exe (PID: 7464)
- Bootstrapper.exe (PID: 7696)
- setup.exe (PID: 7728)
- setup.exe (PID: 7976)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 8092)
- setup.exe (PID: 8124)
- setup.exe (PID: 7208)
- setup.exe (PID: 3352)
- Bootstrapper.exe (PID: 7464)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7568)
- setup.exe (PID: 7872)
- Bootstrapper.exe (PID: 8484)
- setup.exe (PID: 8520)
The process uses the downloaded file
- Bootstrapper.exe (PID: 1020)
- Bootstrapper.exe (PID: 7160)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 6488)
- Bootstrapper.exe (PID: 6444)
- Bootstrapper.exe (PID: 6728)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 4820)
- Bootstrapper.exe (PID: 2328)
- Bootstrapper.exe (PID: 6332)
- Bootstrapper.exe (PID: 6236)
- Bootstrapper.exe (PID: 3648)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 4824)
- Bootstrapper.exe (PID: 7116)
- Bootstrapper.exe (PID: 3708)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 5060)
- Bootstrapper.exe (PID: 2144)
- Bootstrapper.exe (PID: 4680)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 3076)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7560)
- Bootstrapper.exe (PID: 7696)
- Bootstrapper.exe (PID: 8092)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7464)
- Bootstrapper.exe (PID: 7568)
Reads the computer name
- Bootstrapper.exe (PID: 1020)
- Bootstrapper.exe (PID: 7160)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 6488)
- Bootstrapper.exe (PID: 6444)
- Bootstrapper.exe (PID: 6728)
- Bootstrapper.exe (PID: 4820)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 2328)
- Bootstrapper.exe (PID: 6332)
- Bootstrapper.exe (PID: 6236)
- Bootstrapper.exe (PID: 3648)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 7116)
- Bootstrapper.exe (PID: 4824)
- Bootstrapper.exe (PID: 3708)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 5060)
- Bootstrapper.exe (PID: 2144)
- Bootstrapper.exe (PID: 4680)
- Bootstrapper.exe (PID: 3076)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 7560)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7696)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 8092)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7464)
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 8484)
Process checks computer location settings
- Bootstrapper.exe (PID: 1020)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 6488)
- Bootstrapper.exe (PID: 7160)
- Bootstrapper.exe (PID: 6728)
- Bootstrapper.exe (PID: 6444)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 4820)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 2328)
- Bootstrapper.exe (PID: 6332)
- Bootstrapper.exe (PID: 6236)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 3648)
- Bootstrapper.exe (PID: 4824)
- Bootstrapper.exe (PID: 7116)
- Bootstrapper.exe (PID: 3708)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 2144)
- Bootstrapper.exe (PID: 5060)
- Bootstrapper.exe (PID: 4680)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 3076)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7560)
- Bootstrapper.exe (PID: 7696)
- Bootstrapper.exe (PID: 8092)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7464)
- Bootstrapper.exe (PID: 7568)
Sends debugging messages
- Bootstrapper.exe (PID: 1020)
- Bootstrapper.exe (PID: 6364)
- Bootstrapper.exe (PID: 6488)
- Bootstrapper.exe (PID: 7160)
- Bootstrapper.exe (PID: 6444)
- Bootstrapper.exe (PID: 6728)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 6440)
- Bootstrapper.exe (PID: 4820)
- Bootstrapper.exe (PID: 2328)
- Bootstrapper.exe (PID: 6332)
- Bootstrapper.exe (PID: 6236)
- Bootstrapper.exe (PID: 2268)
- Bootstrapper.exe (PID: 3648)
- Bootstrapper.exe (PID: 7116)
- Bootstrapper.exe (PID: 4824)
- Bootstrapper.exe (PID: 3708)
- Bootstrapper.exe (PID: 6272)
- Bootstrapper.exe (PID: 2424)
- Bootstrapper.exe (PID: 2144)
- Bootstrapper.exe (PID: 5060)
- Bootstrapper.exe (PID: 4680)
- Bootstrapper.exe (PID: 3076)
- Bootstrapper.exe (PID: 7264)
- Bootstrapper.exe (PID: 7432)
- Bootstrapper.exe (PID: 7560)
- Bootstrapper.exe (PID: 7696)
- Bootstrapper.exe (PID: 7908)
- Bootstrapper.exe (PID: 8092)
- Bootstrapper.exe (PID: 1176)
- Bootstrapper.exe (PID: 7568)
- Bootstrapper.exe (PID: 7464)
Create files in a temporary directory
- Bootstrapper.exe (PID: 1020)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- powershell.exe (PID: 6448)
- powershell.exe (PID: 6496)
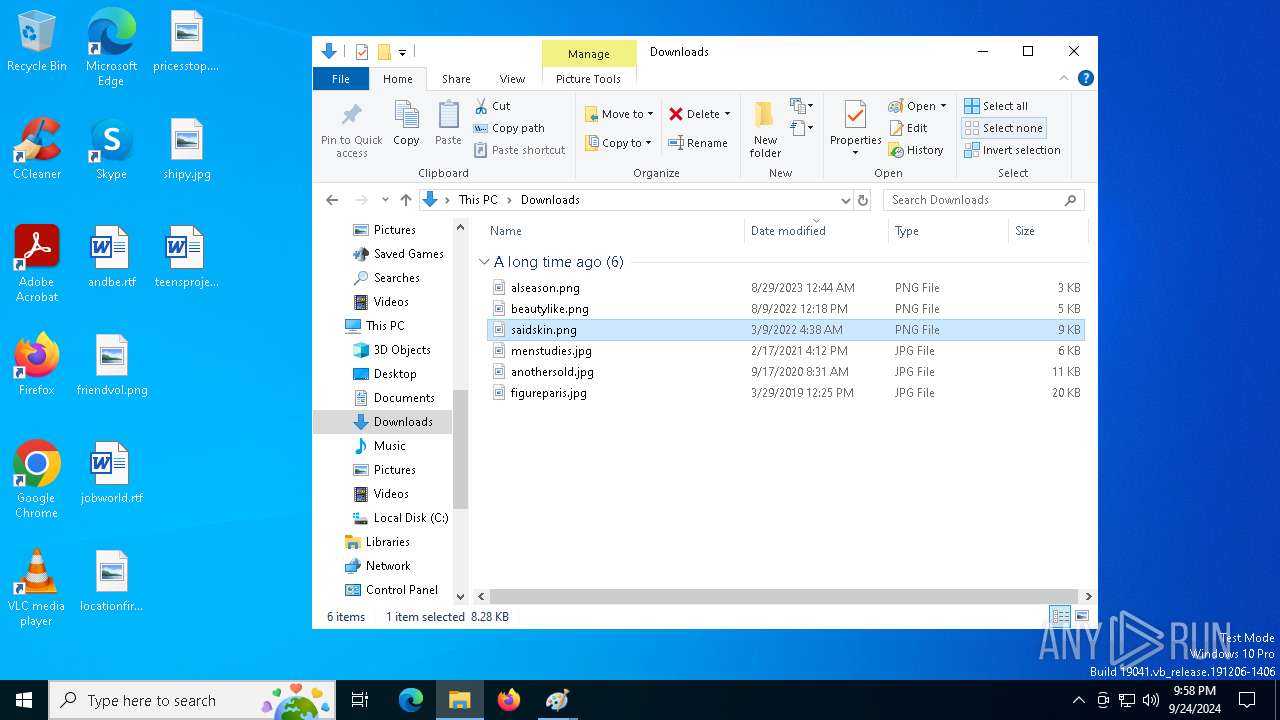
Manual execution by a user
- mspaint.exe (PID: 10568)
- mspaint.exe (PID: 7460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 2048 |
| InitializedDataSize: | 6135808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14d1 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
427
Monitored processes
303
Malicious processes
55
Suspicious processes
14
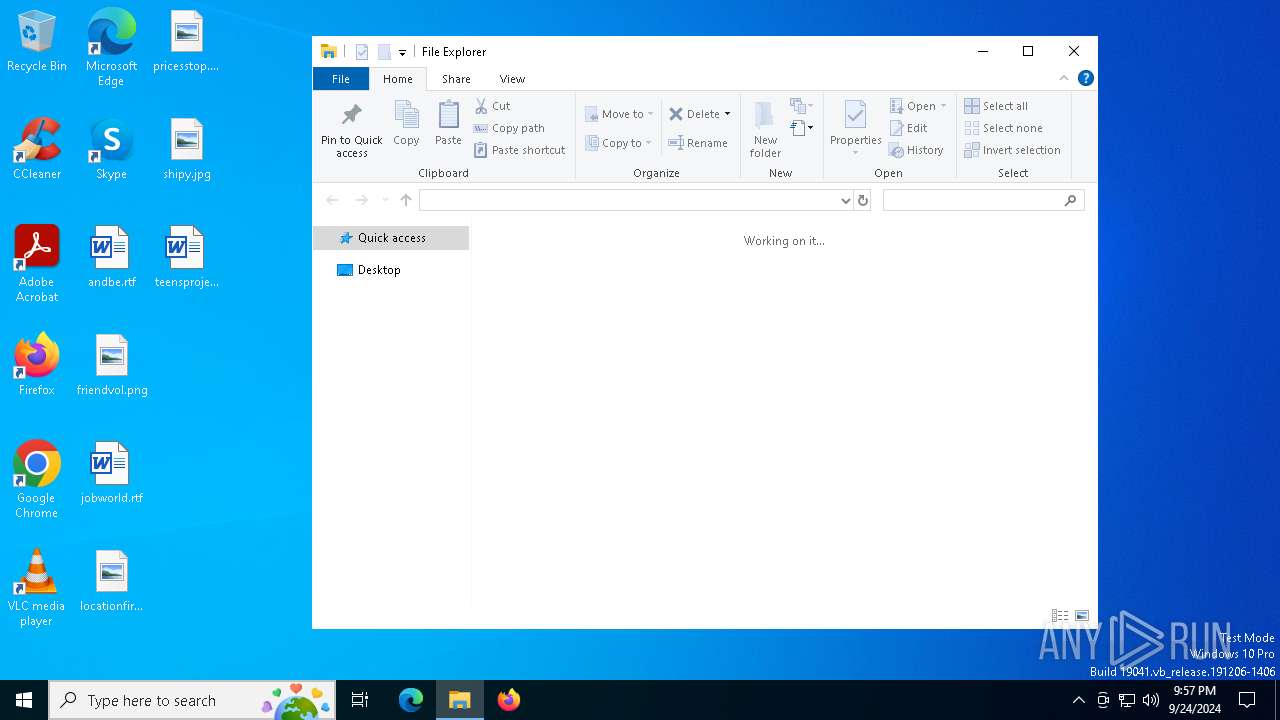
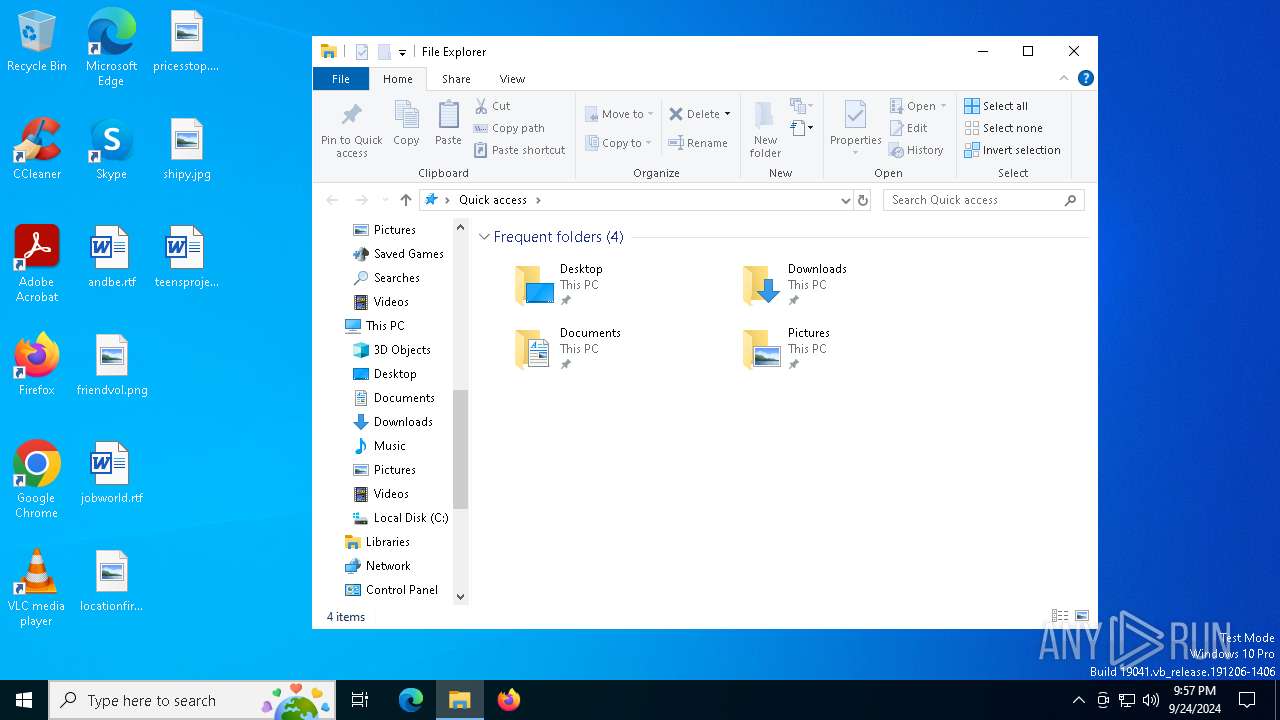
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1048 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | Bootstrapper.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1092 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1148 | "C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe | — | Bootstrapper.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 | |||||||||||||||
| 1176 | "C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe | Bootstrapper.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
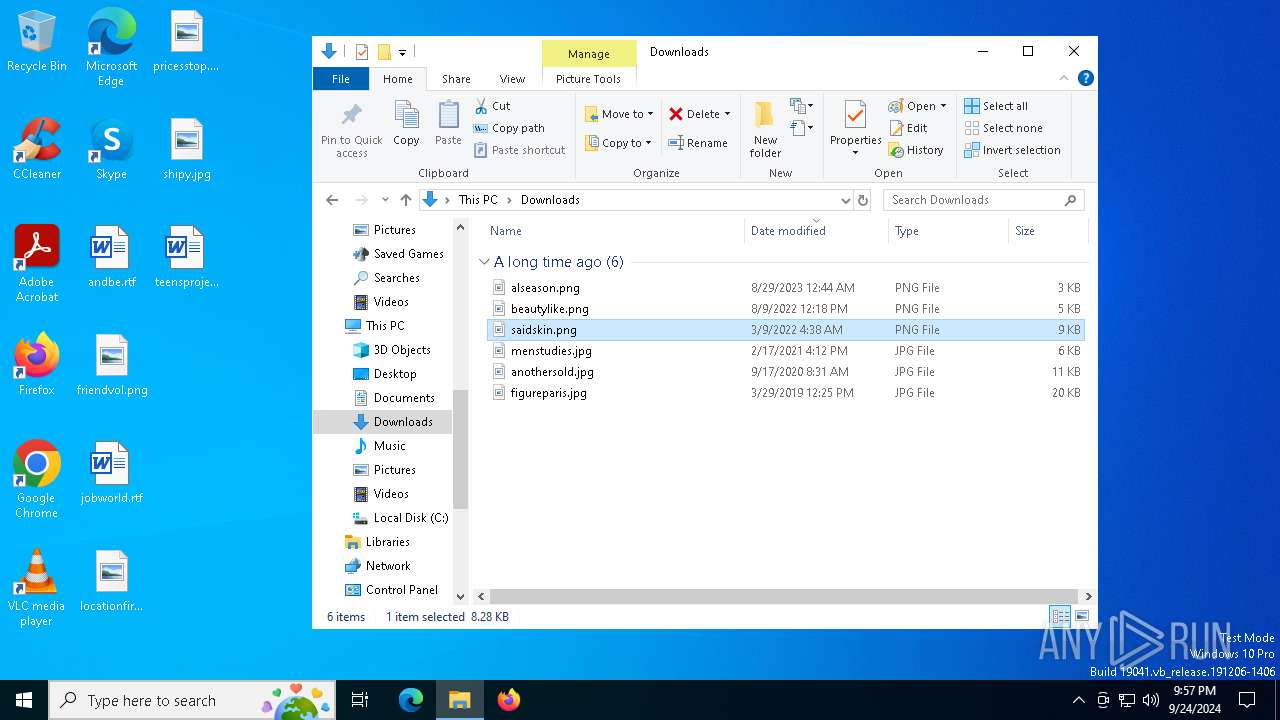
Total events
123 613
Read events
123 613
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
2
Text files
205
Unknown types
0
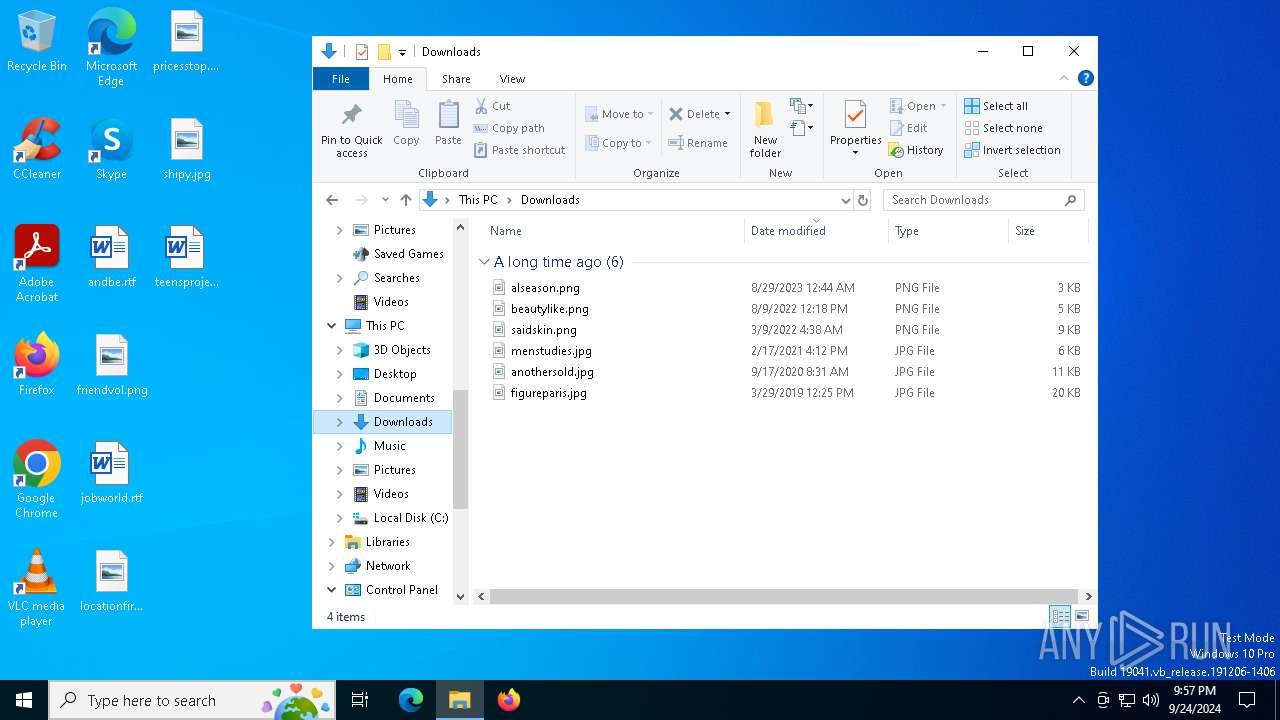
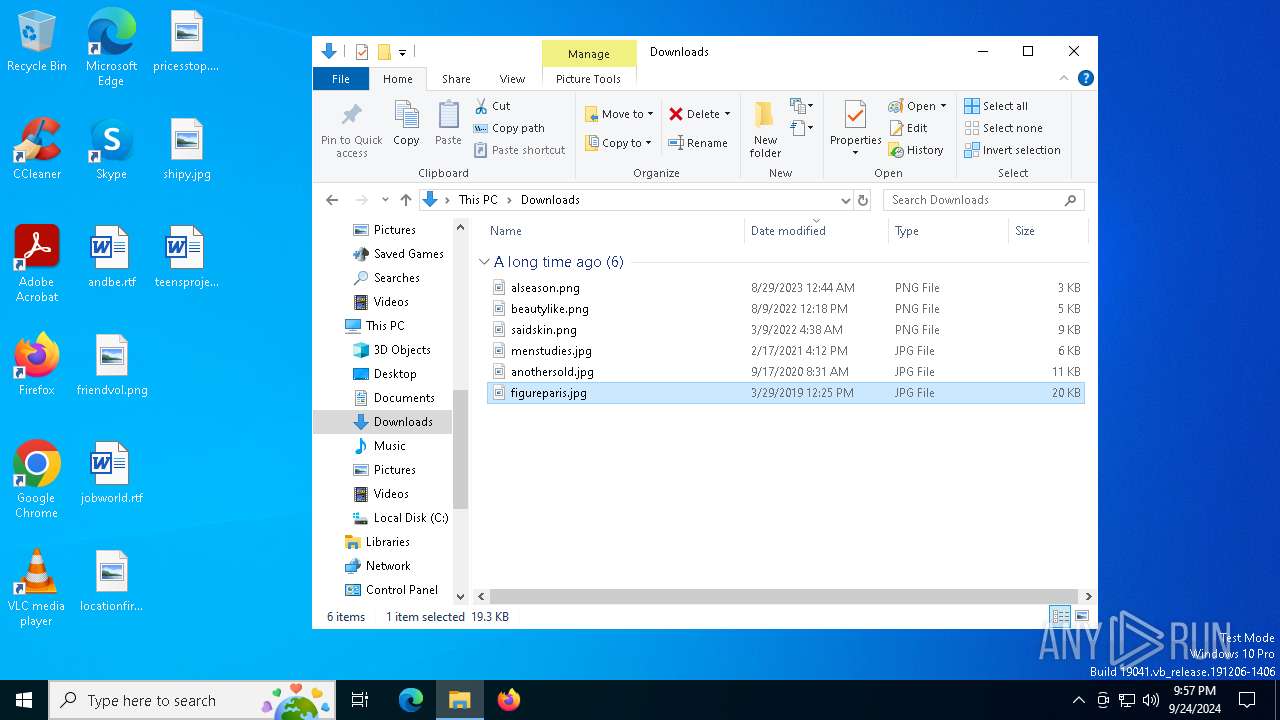
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sg5qz1vb.j3f.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wz54e23i.22r.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4644 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eau50w44.4pe.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6020 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_x3preltc.z5x.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2qobioab.0xq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5000 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vpftxg3r.wbl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8028 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xyvy5wyz.jgj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8160 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_evoiv3i2.ran.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4644 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mr4g244y.oox.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qdt3w4es.ttb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
15
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
32 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|
Bootstrapper.exe | Invalid parameter passed to C runtime function.
|