| File name: | Virus.bat |
| Full analysis: | https://app.any.run/tasks/da53727e-99b5-4043-985f-4447da3f3562 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2024, 15:46:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 2F932E1CC918A531D2568F7842B1A70D |
| SHA1: | BD7B024526B2E1C098D117674DB3B3B535E84304 |
| SHA256: | CA76EF30CB34B0B8D55F11A58F53863C7808BDF695726EAEF29AD76F1FDDF6AC |
| SSDEEP: | 3:8FyEL89NRn:88p9D |
MALICIOUS
No malicious indicators.SUSPICIOUS
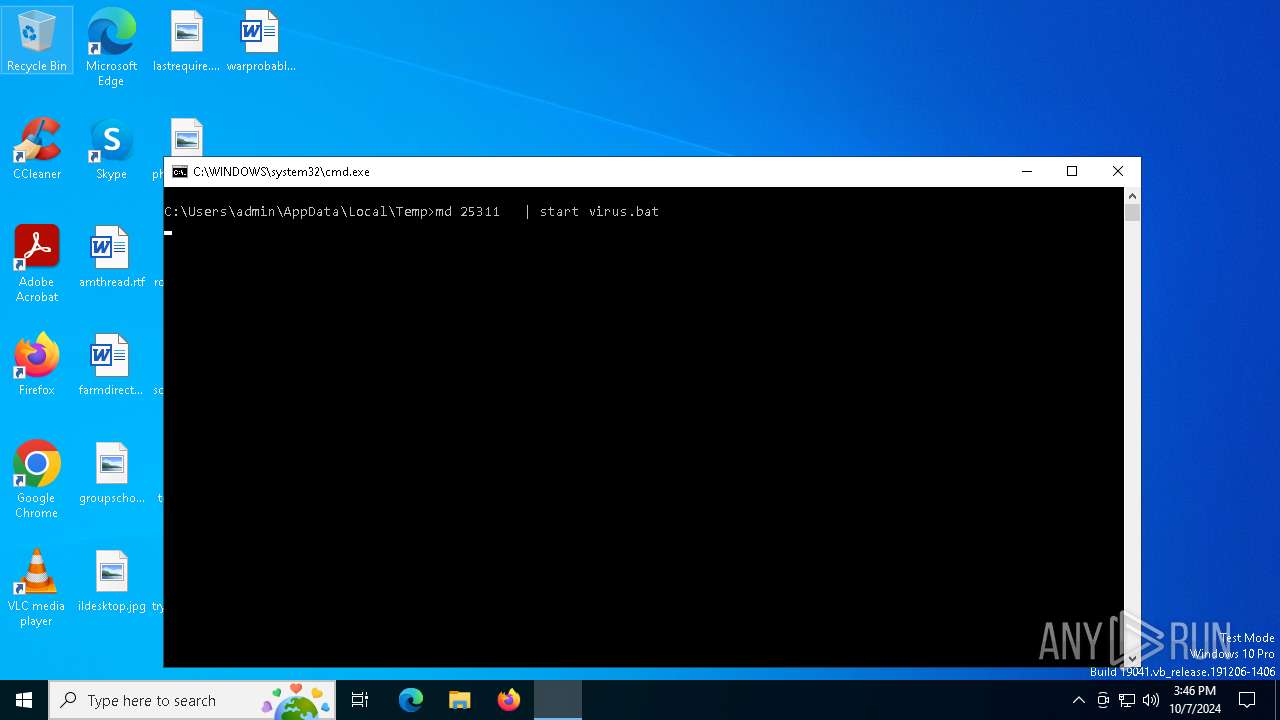
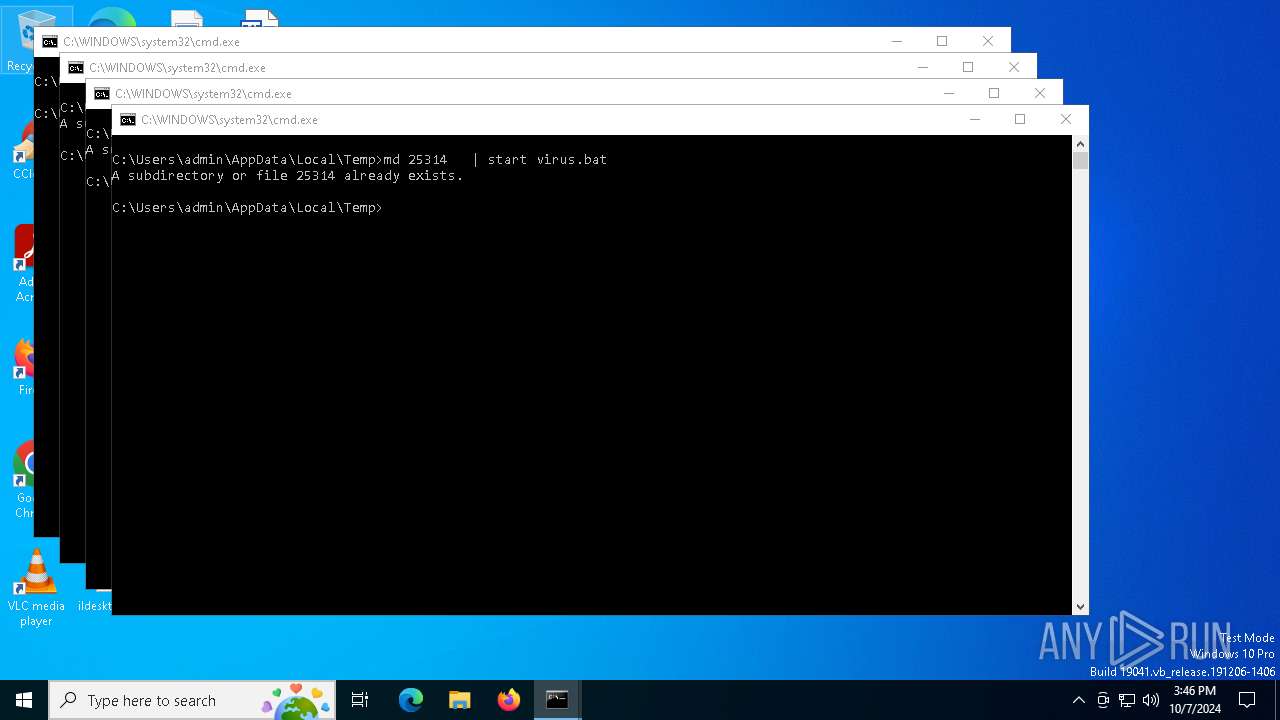
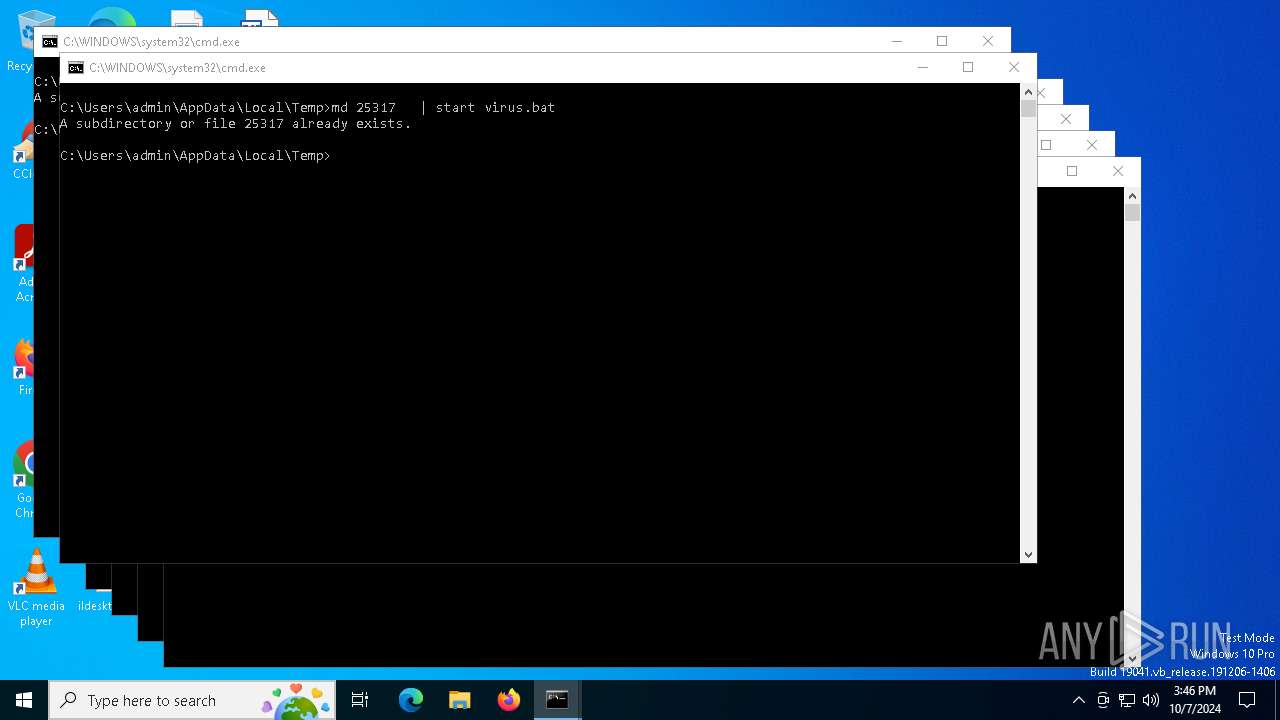
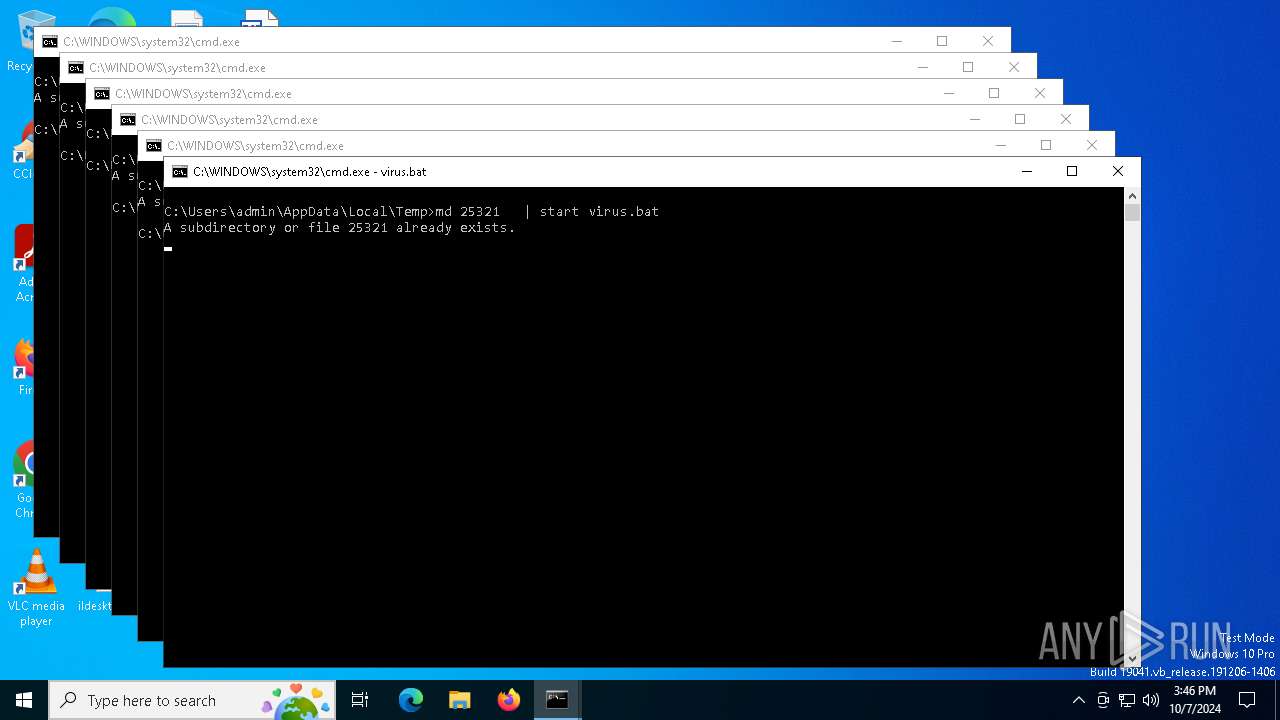
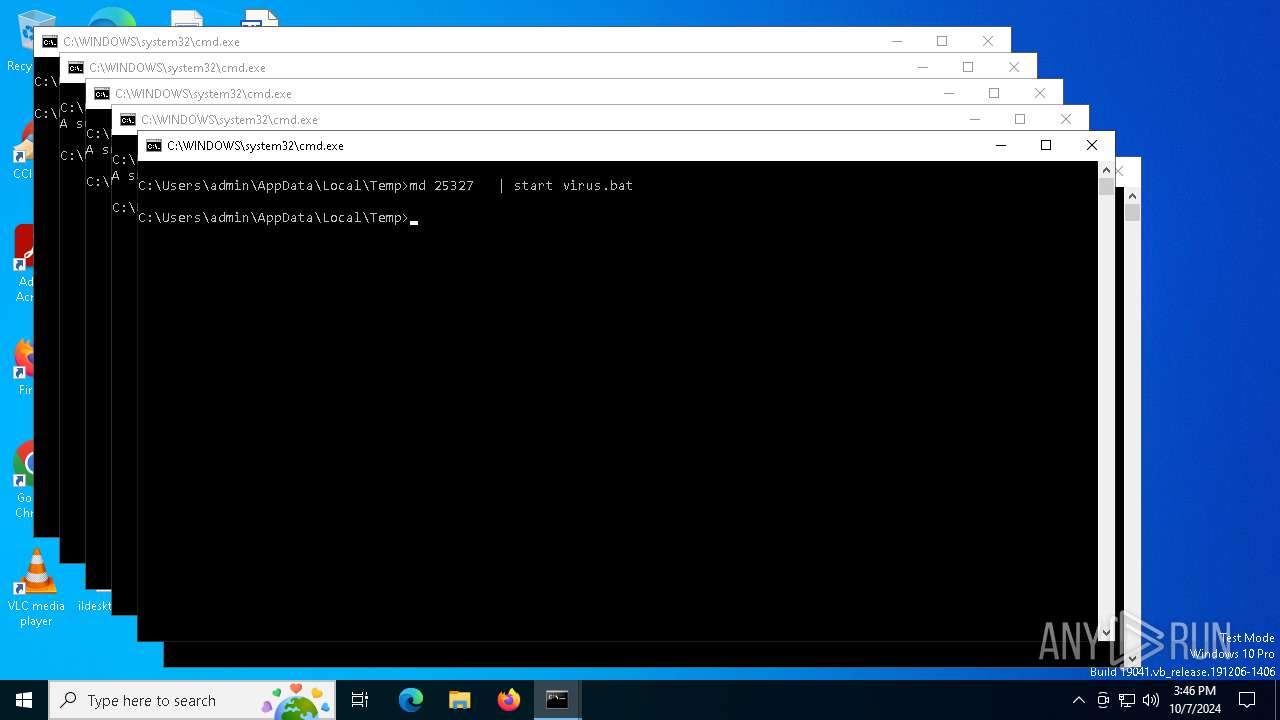
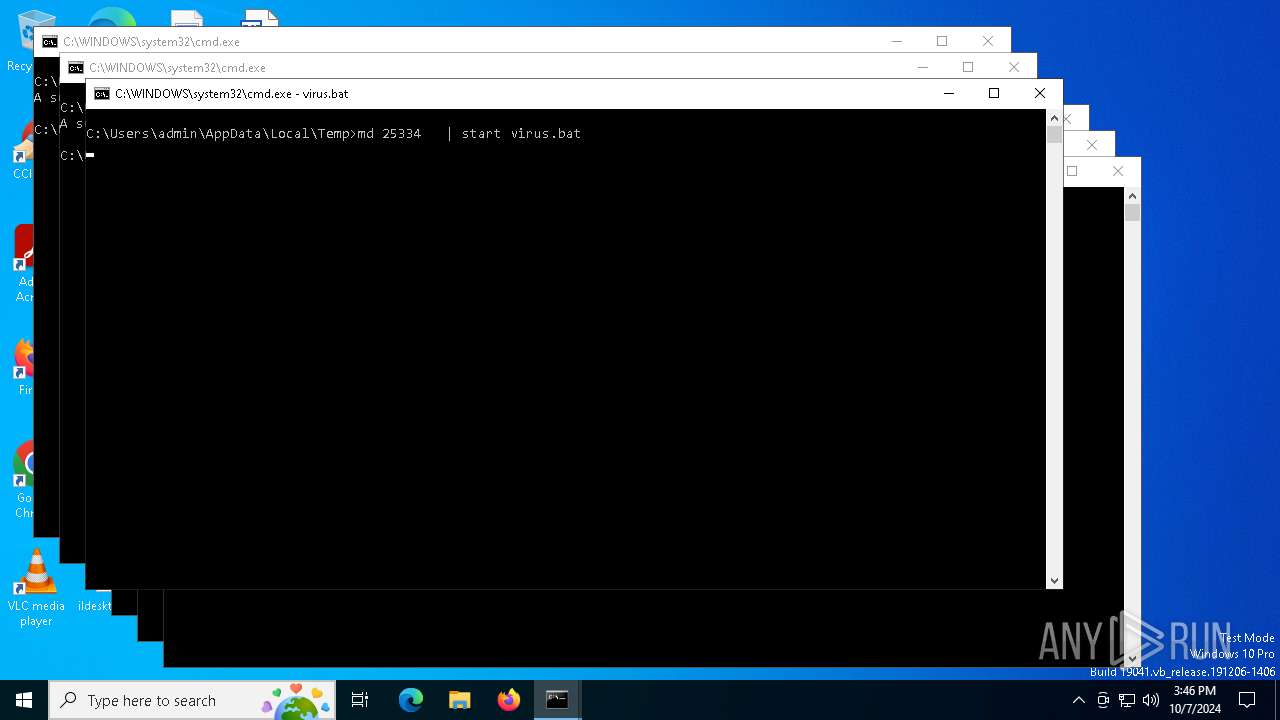
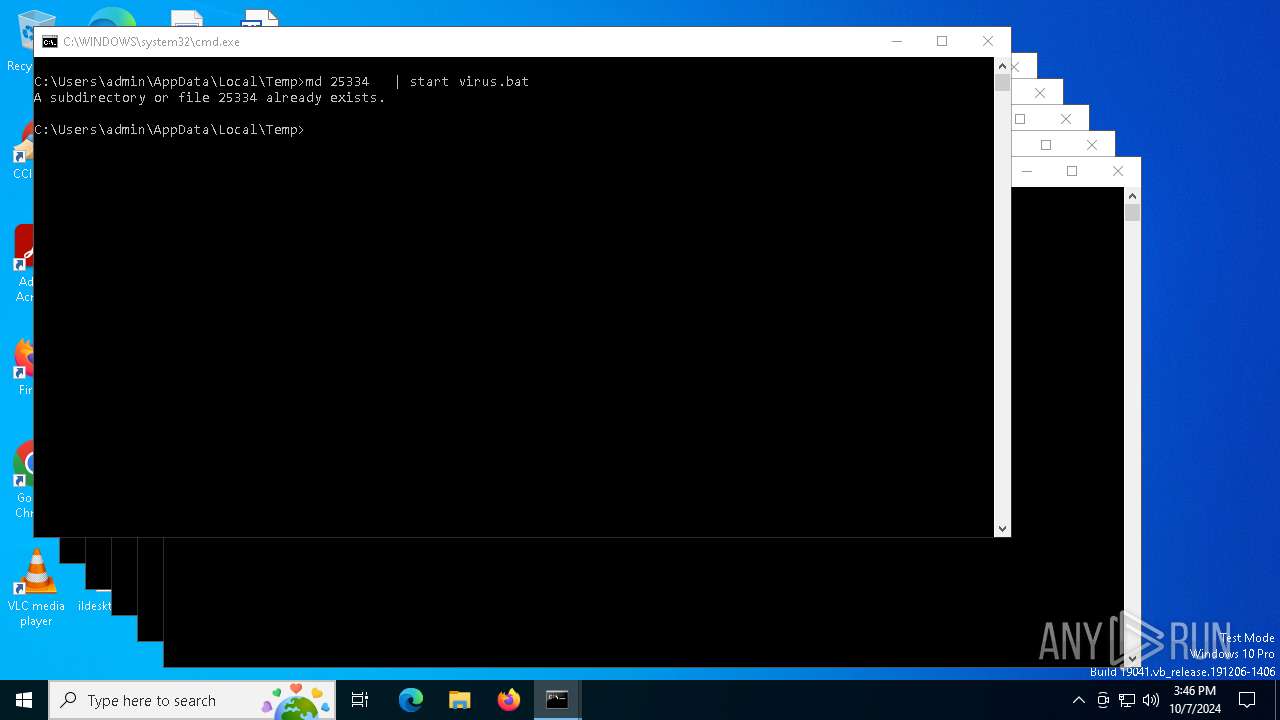
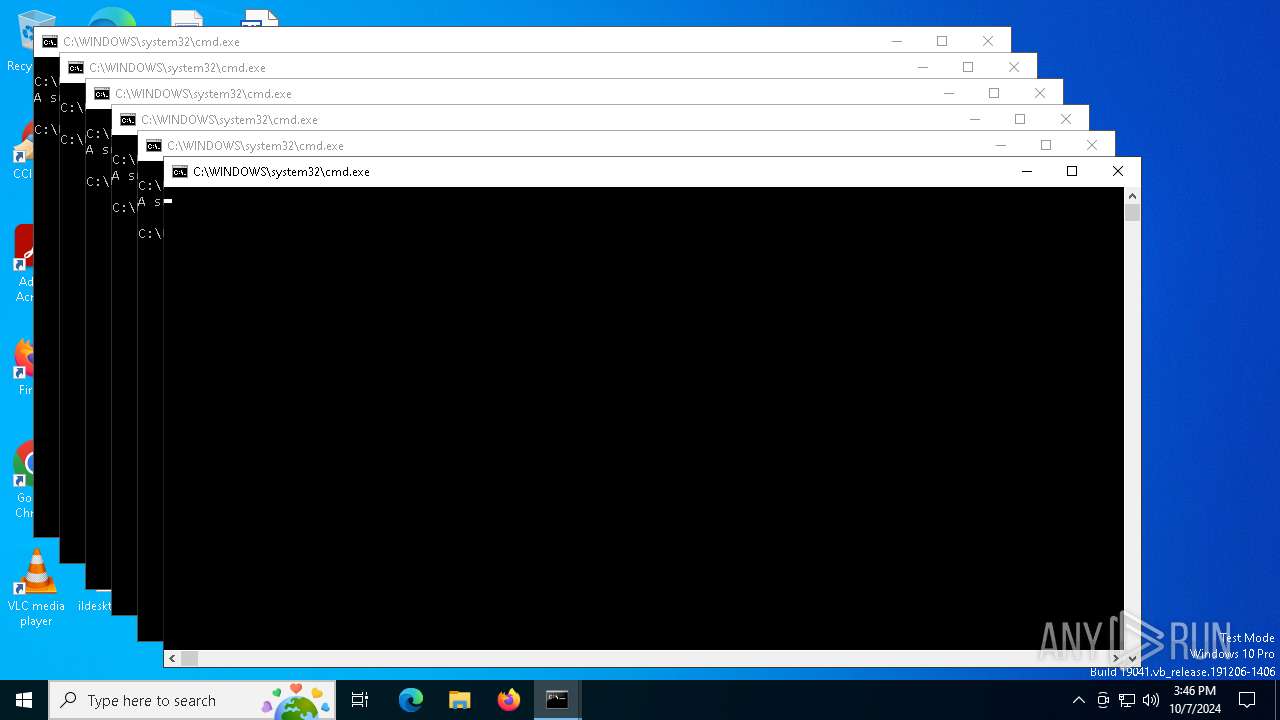
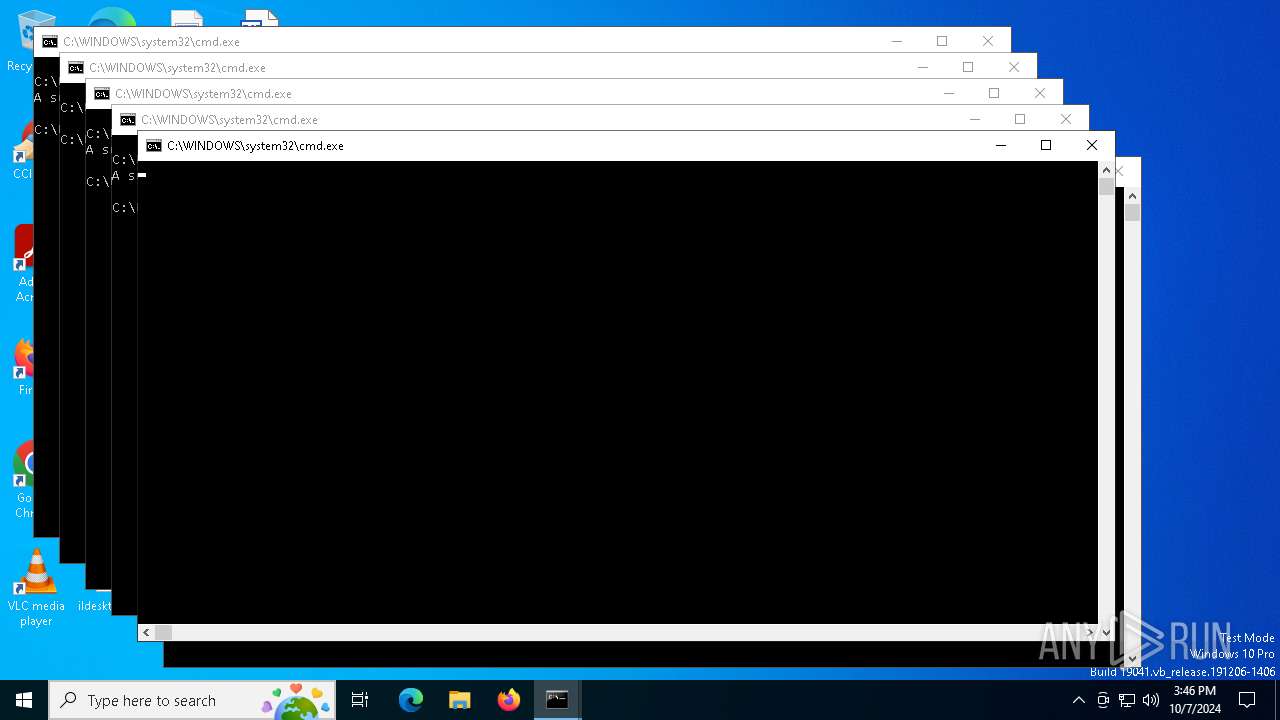
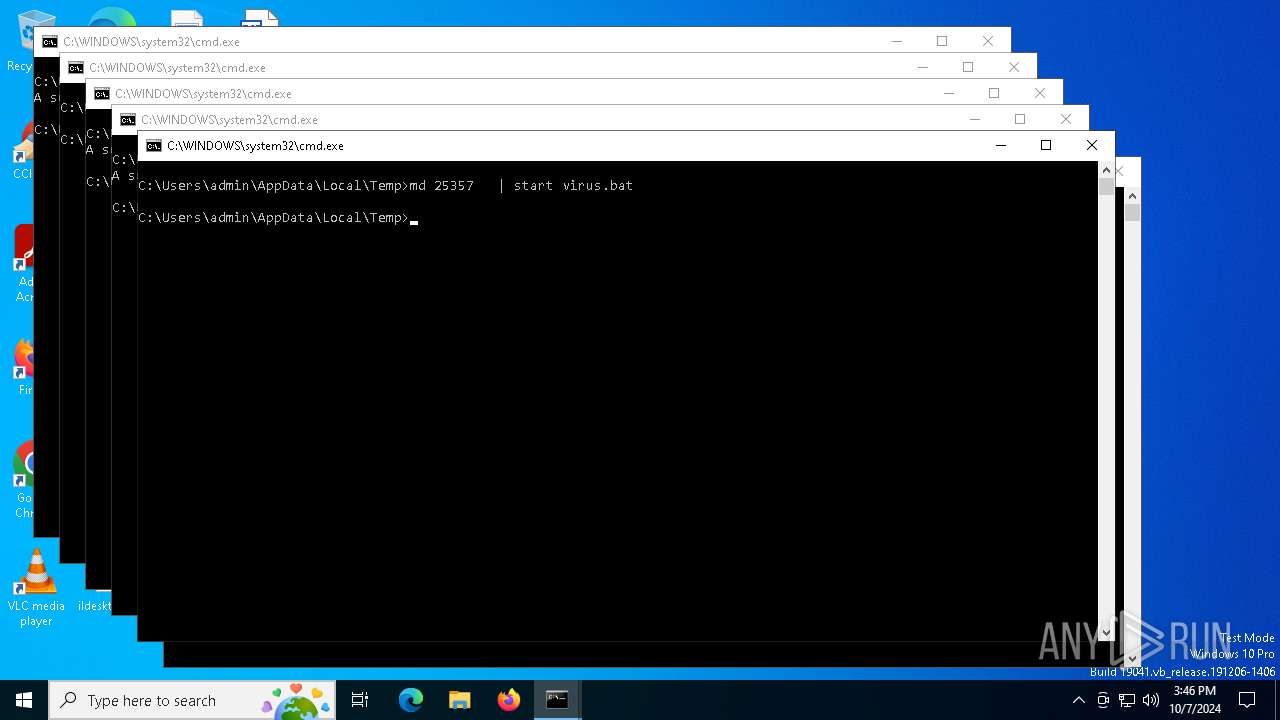
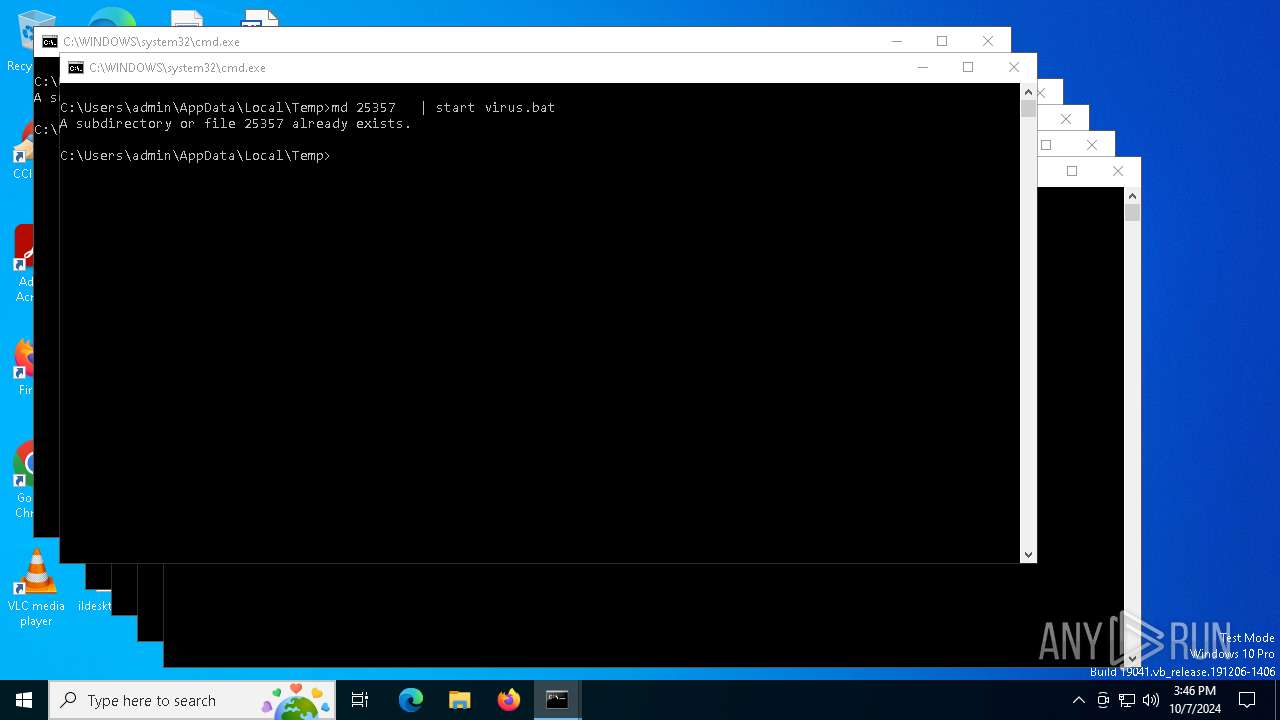
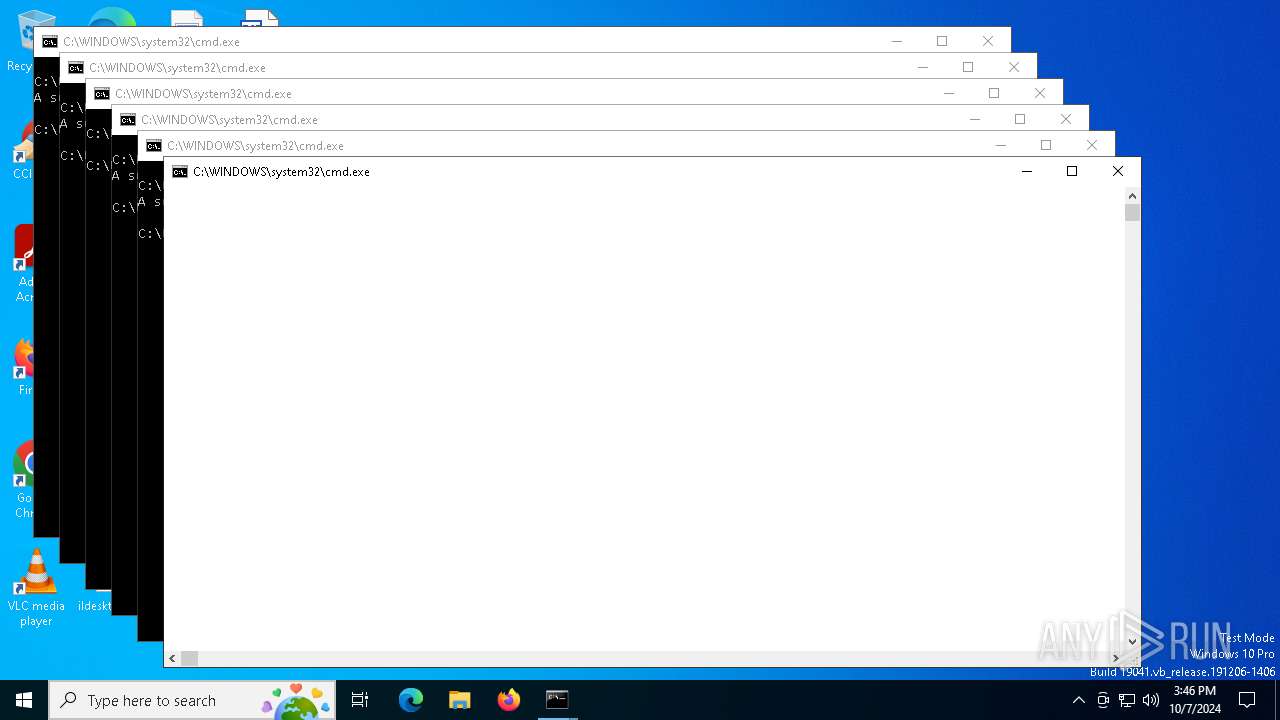
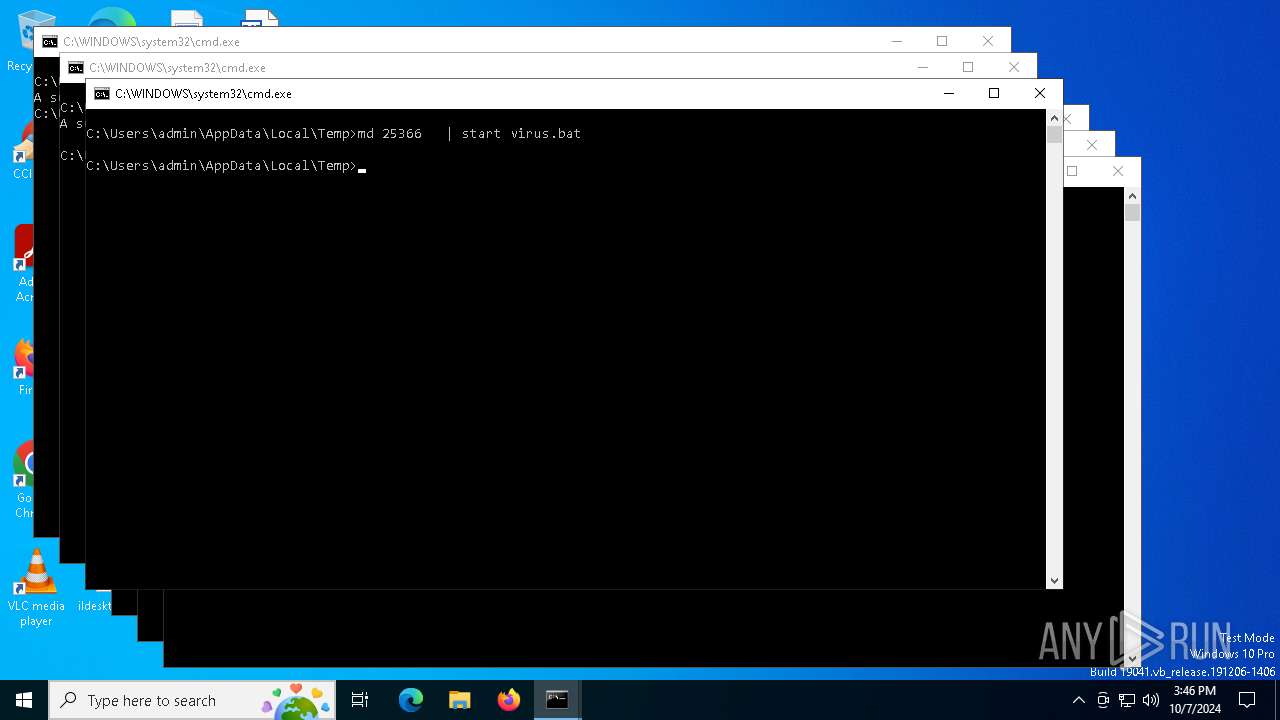
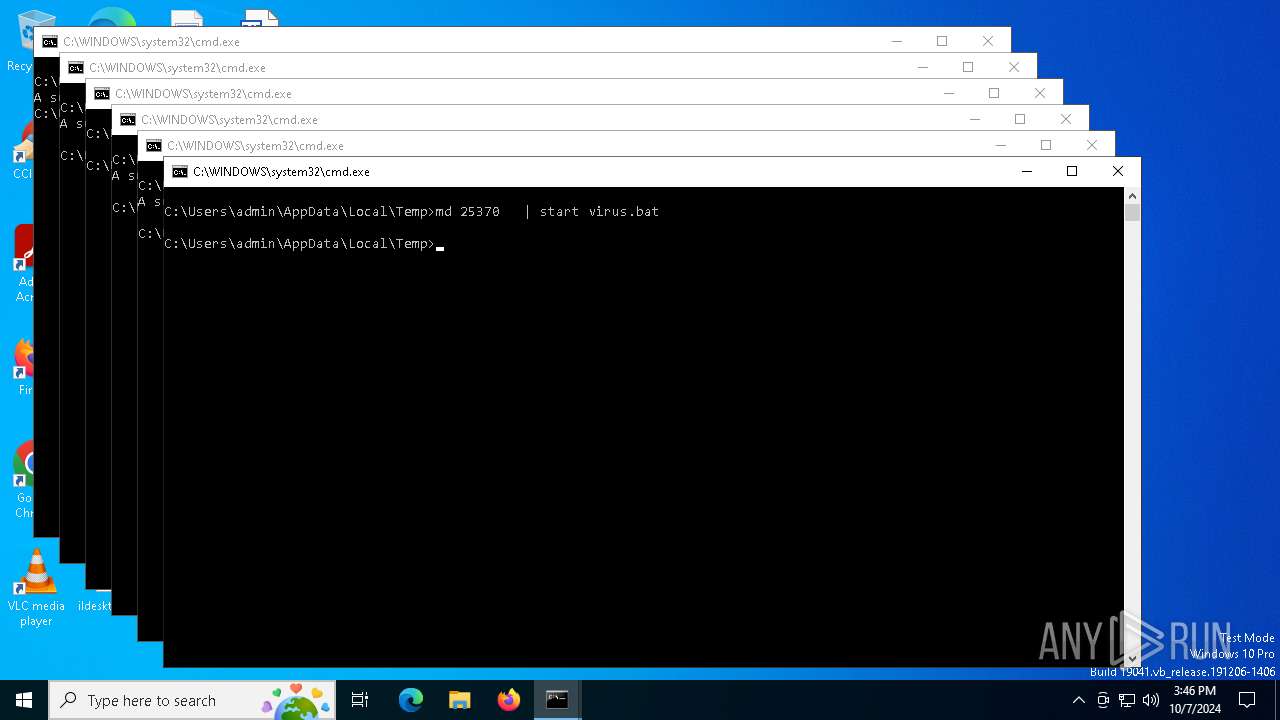
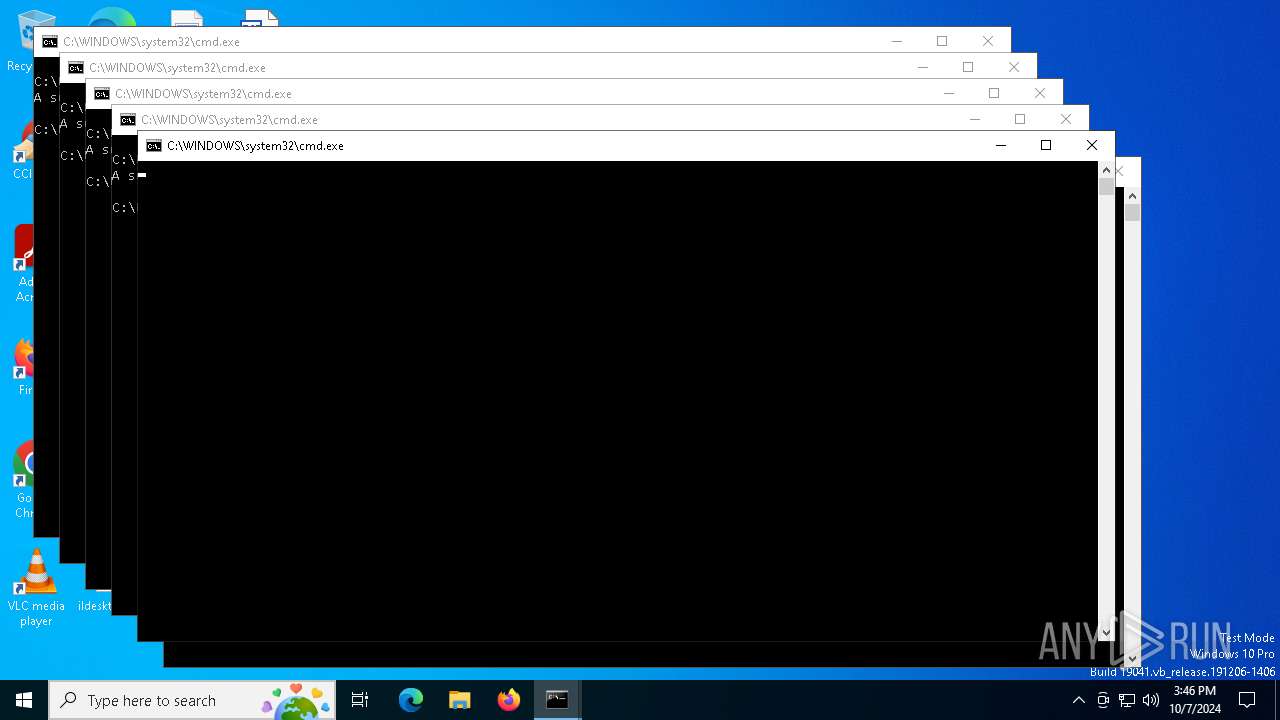
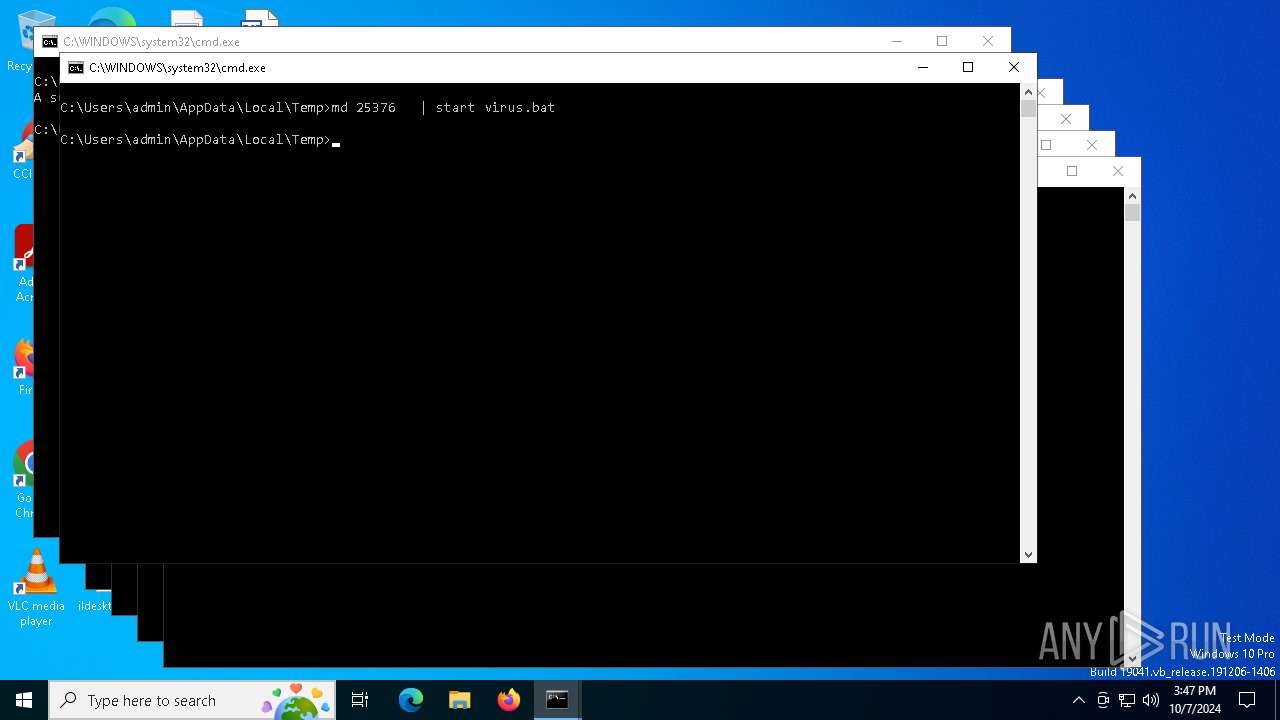
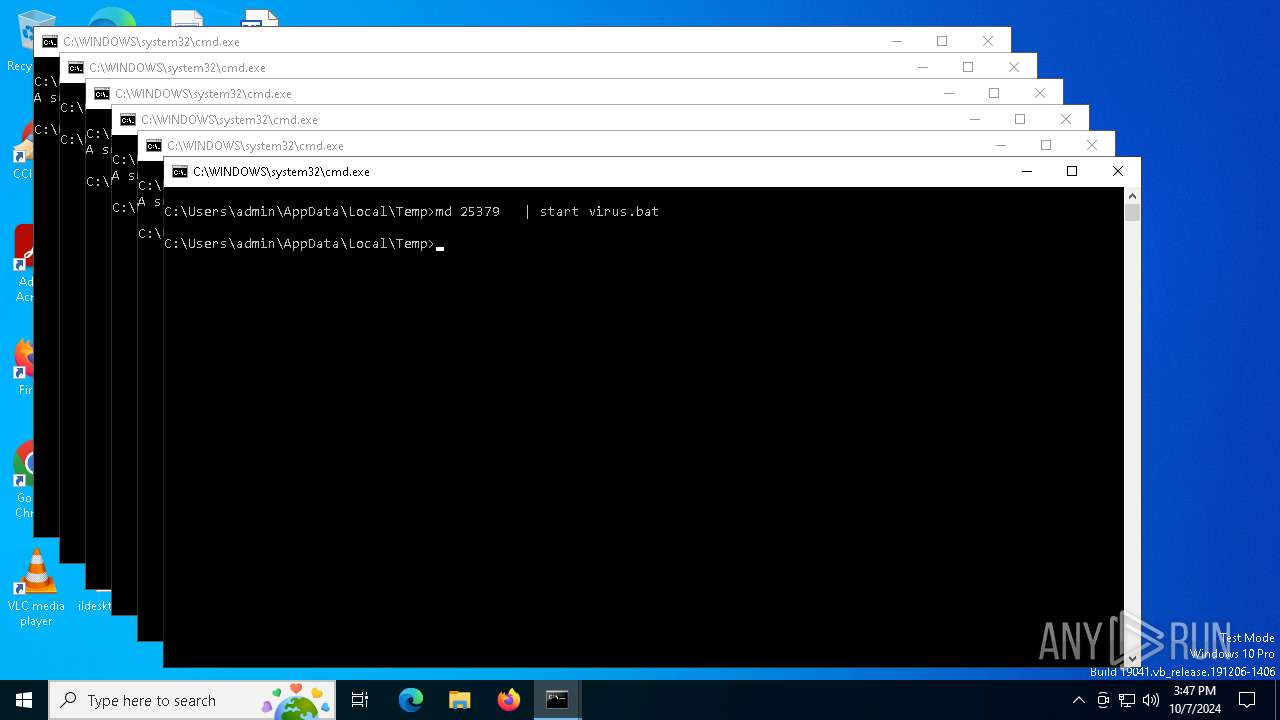
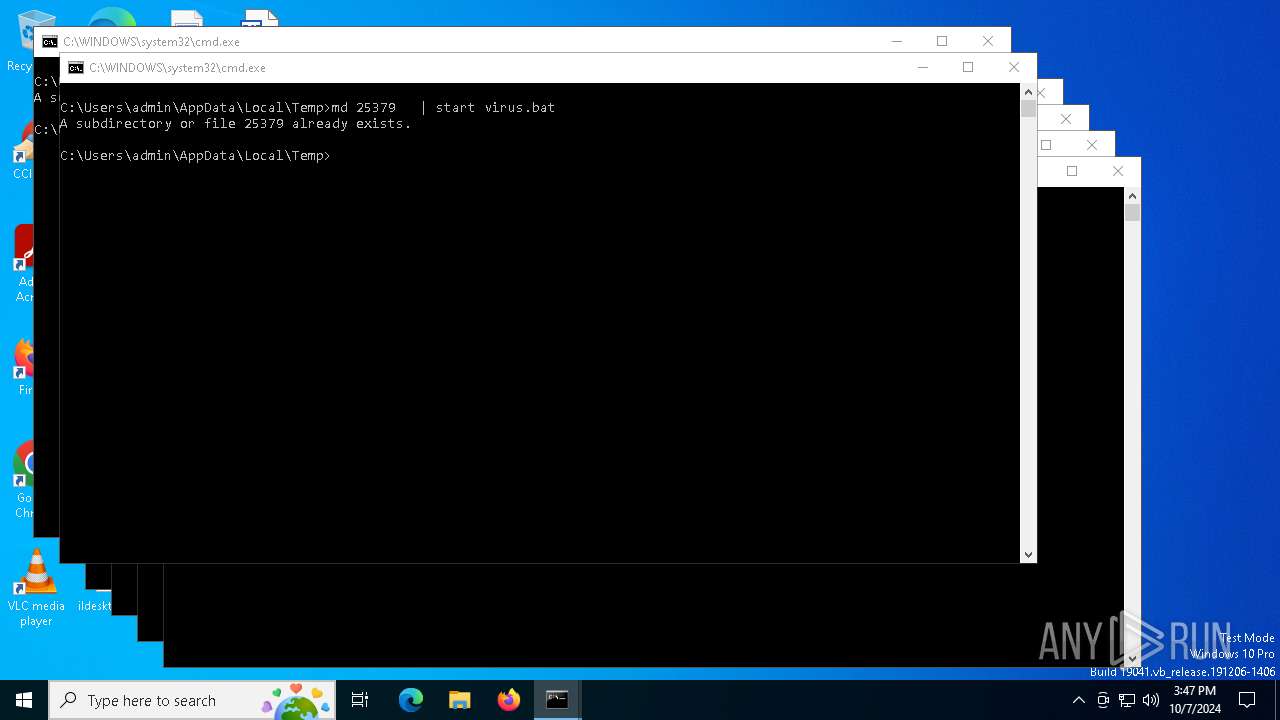
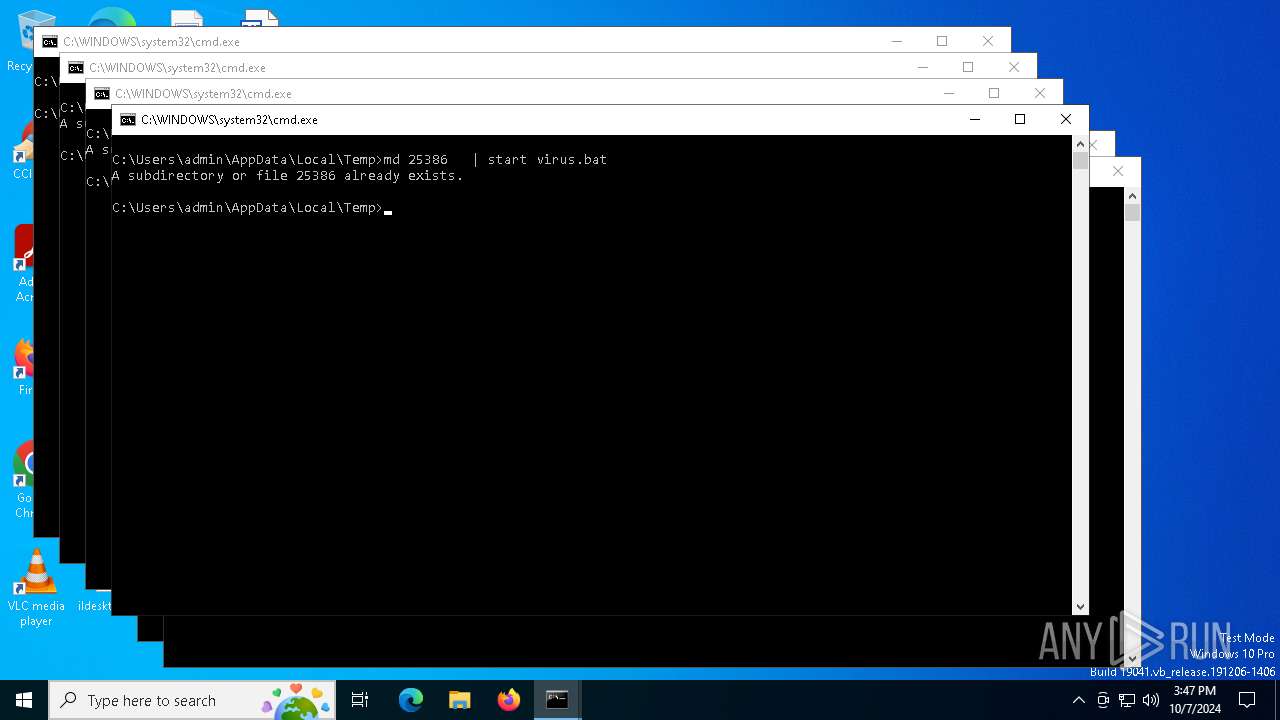
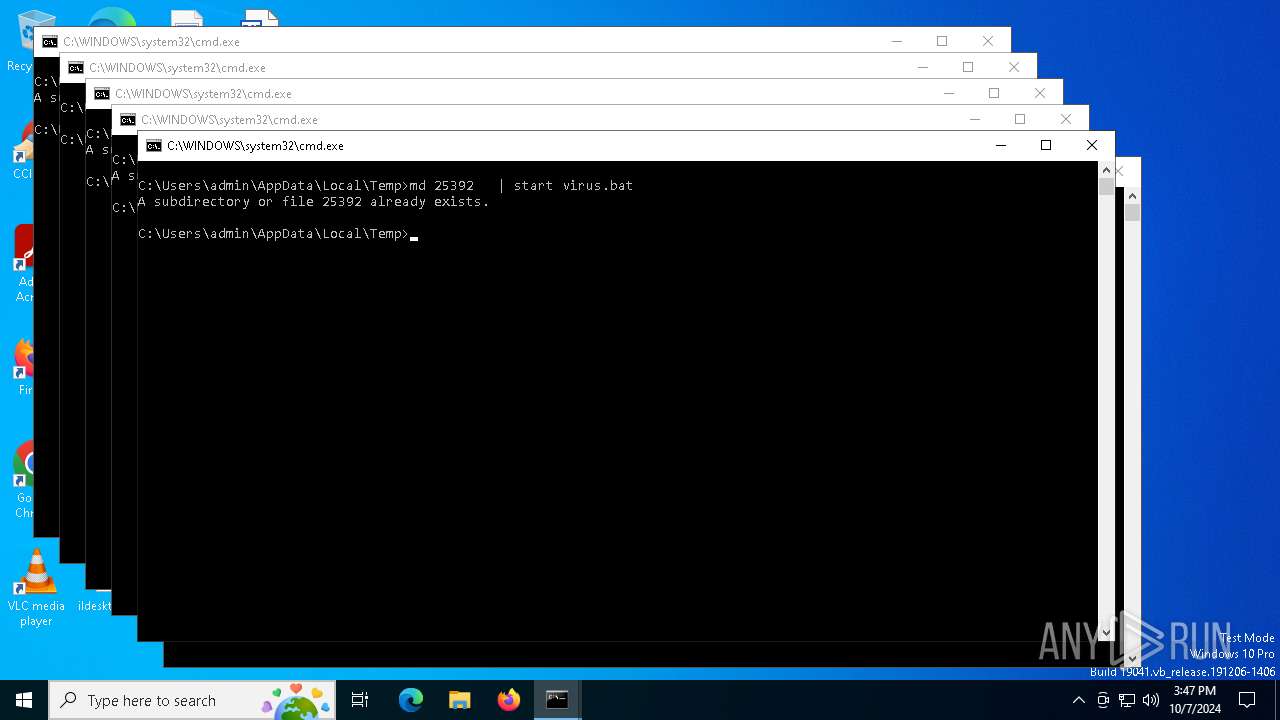
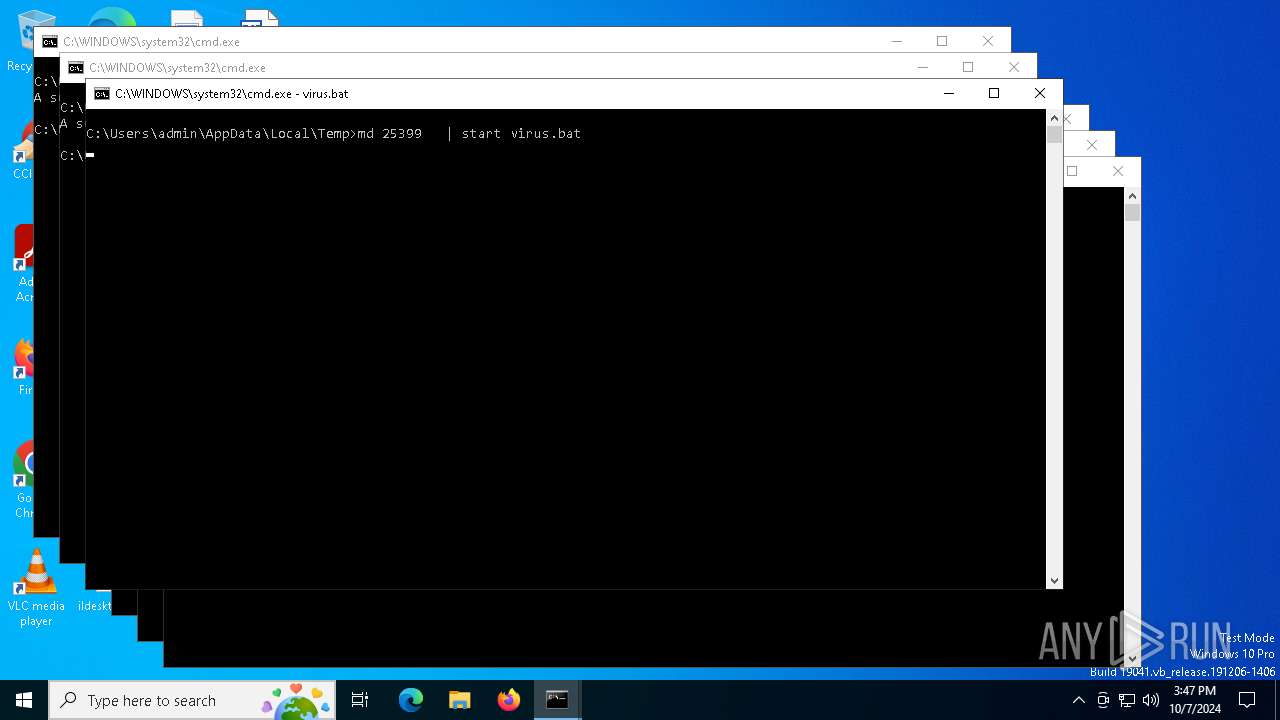
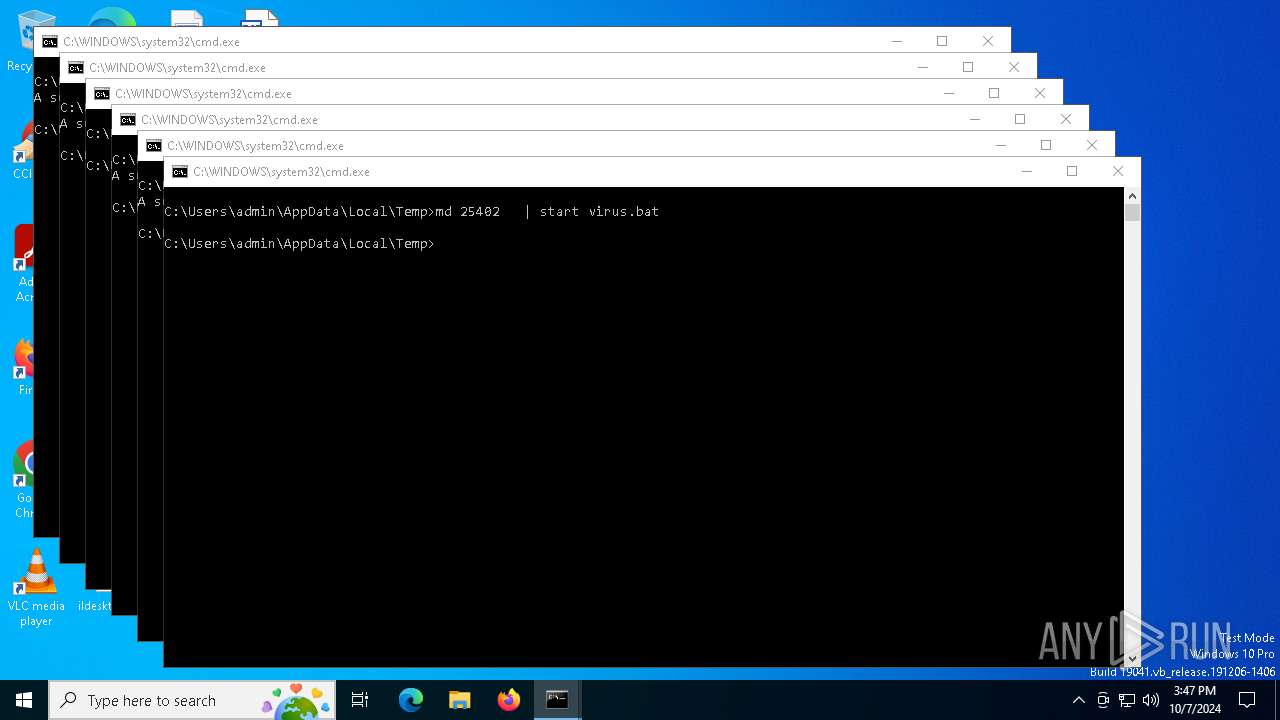
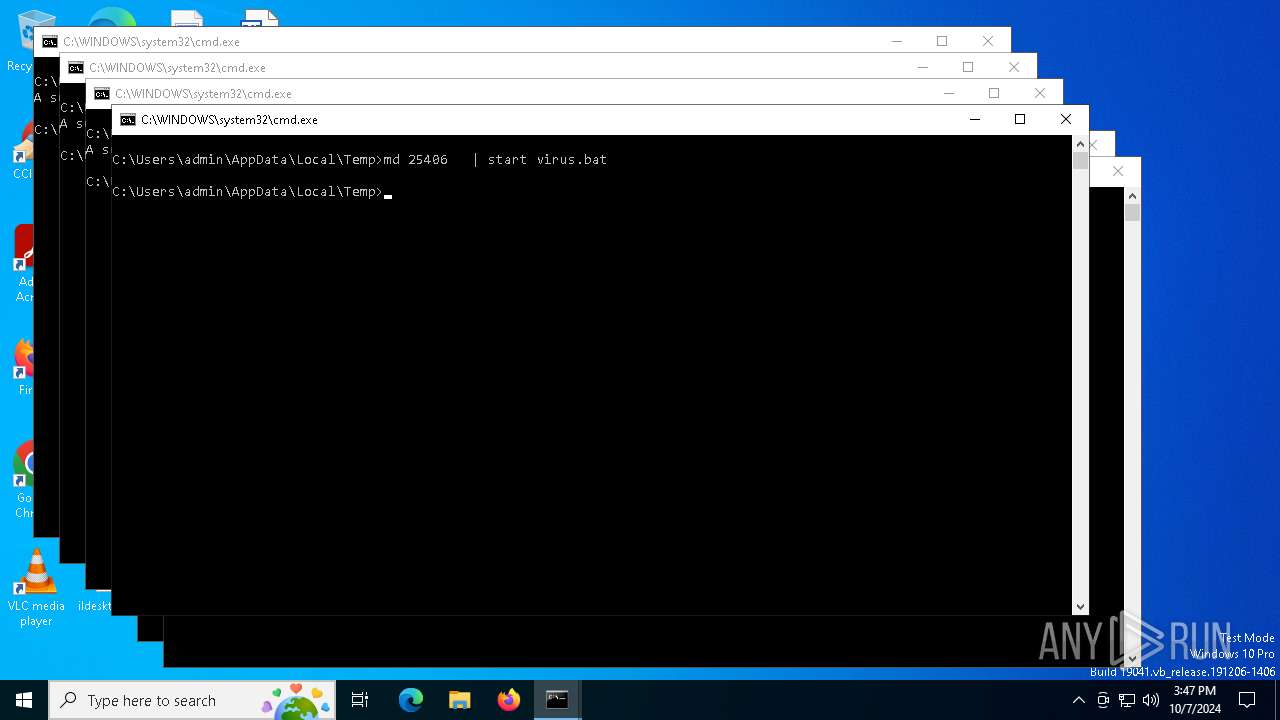
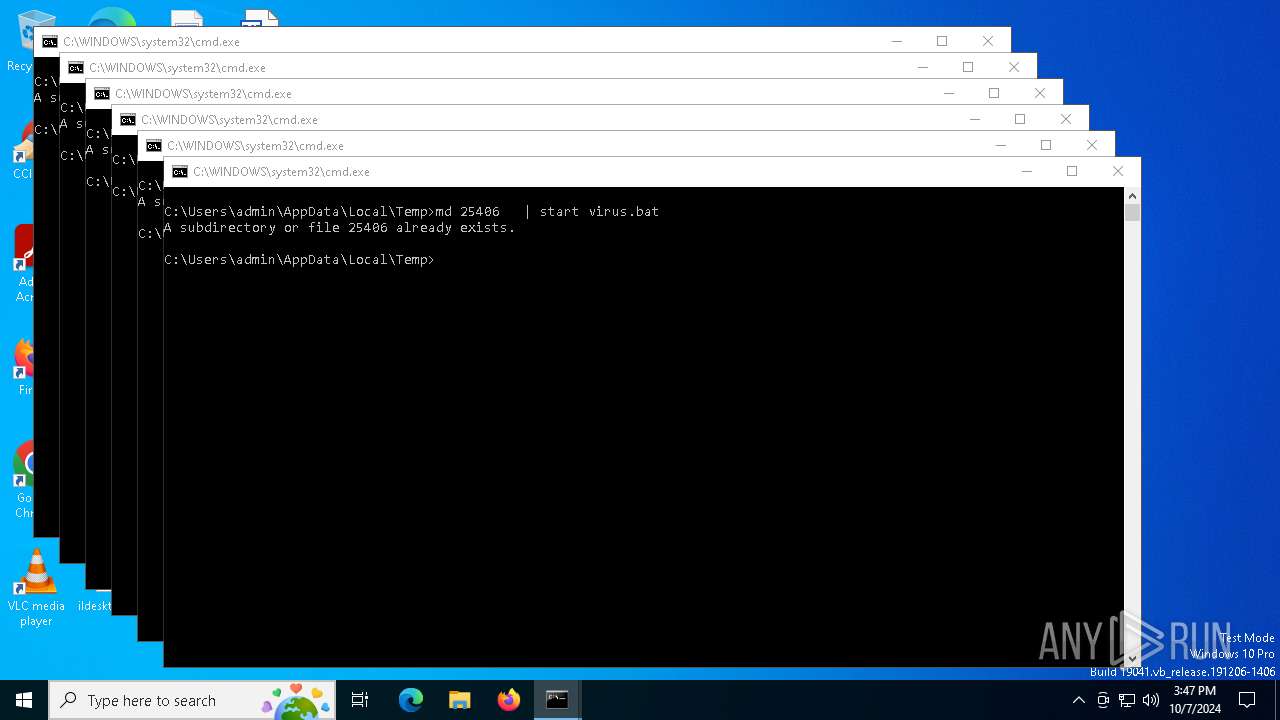
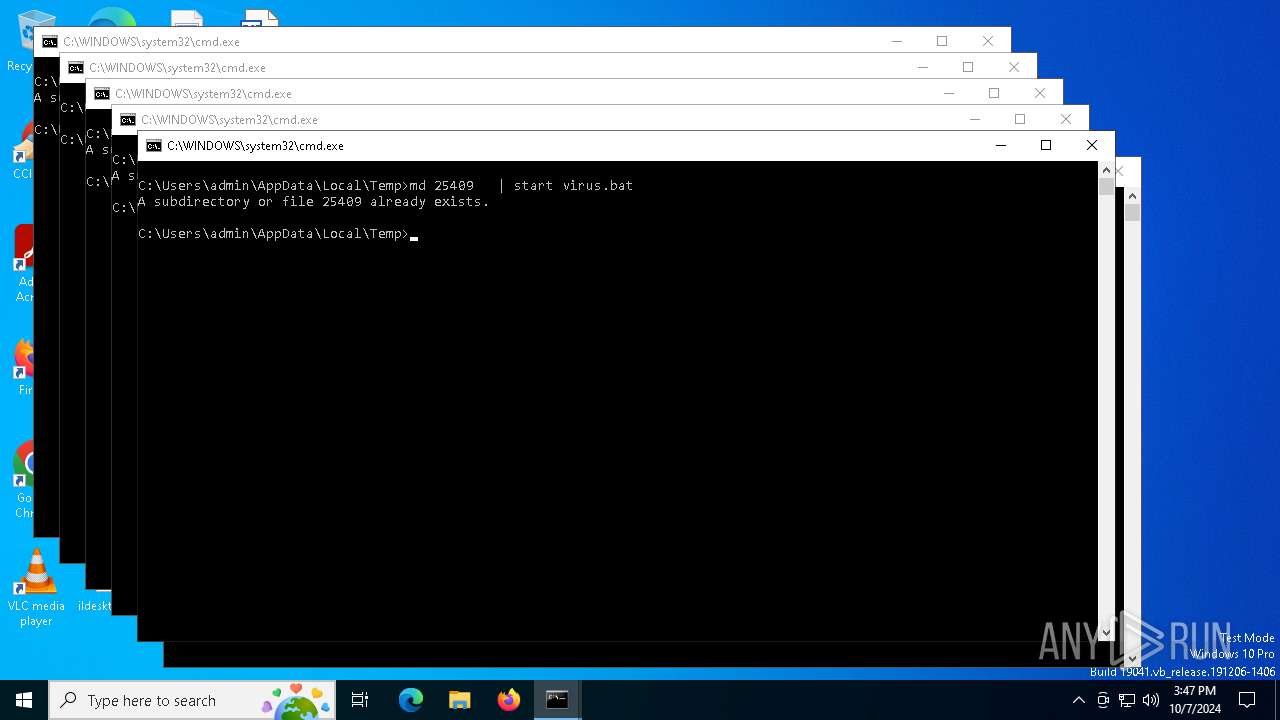
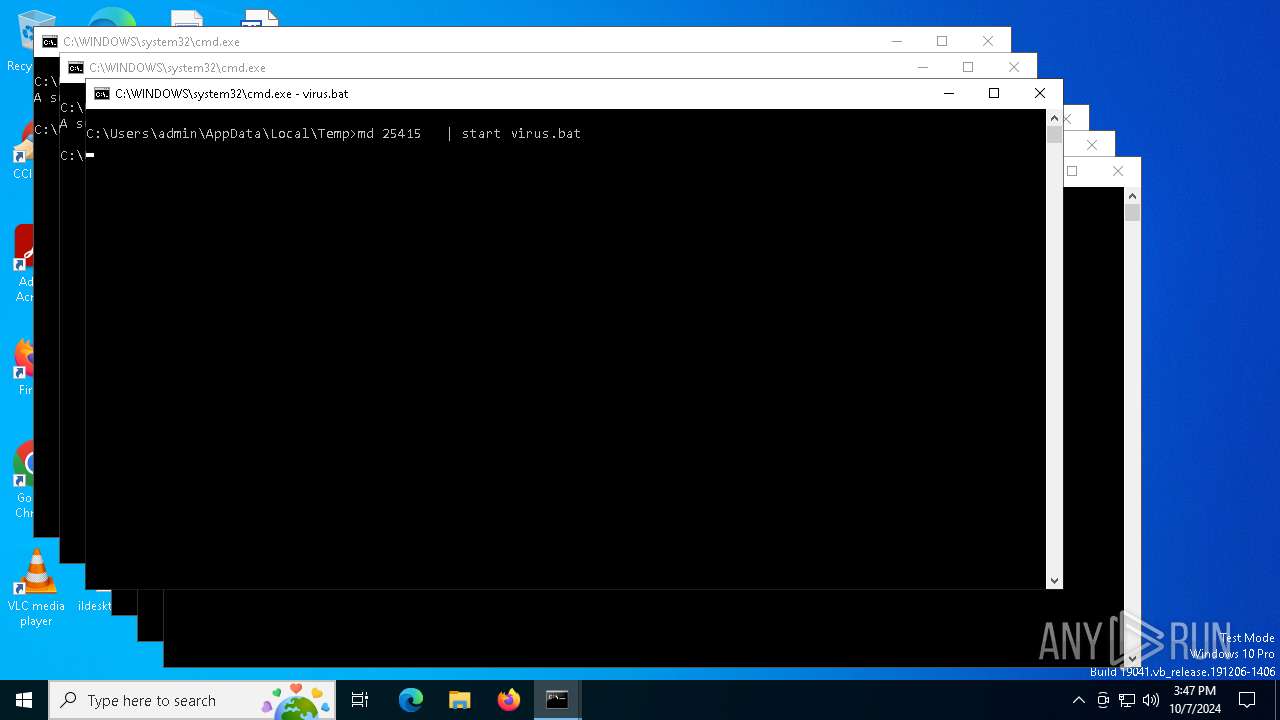
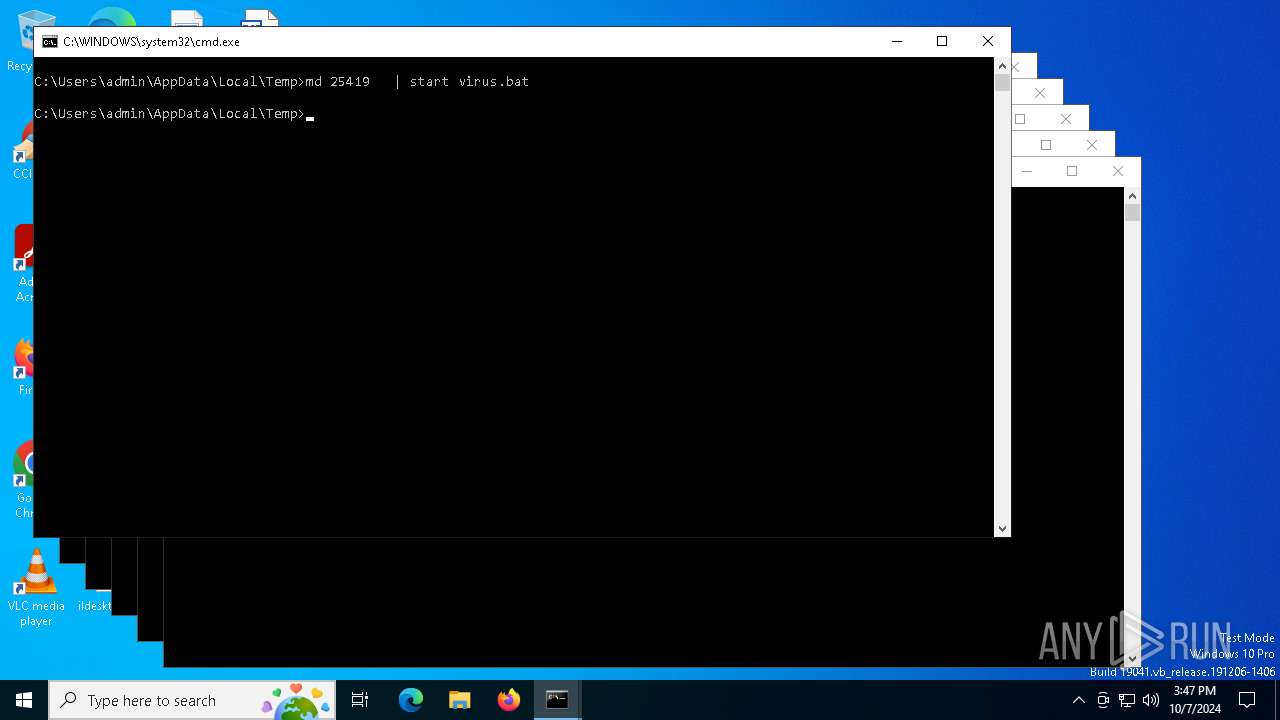
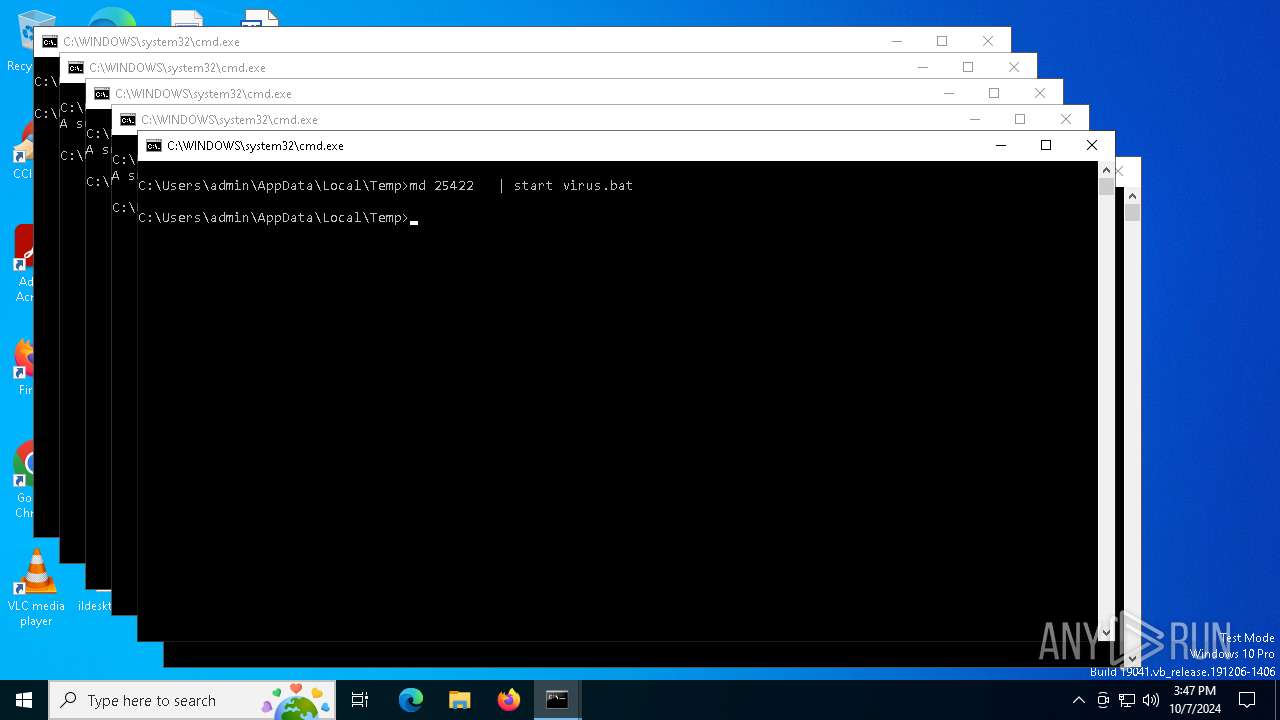
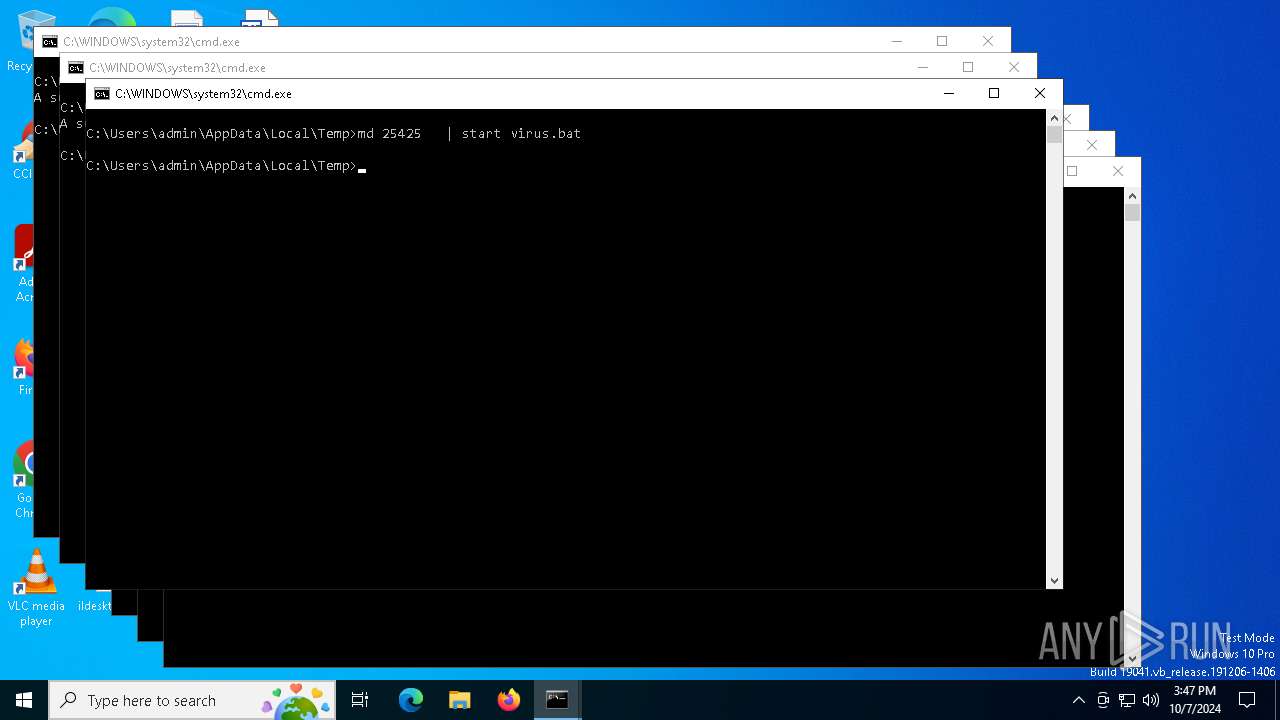
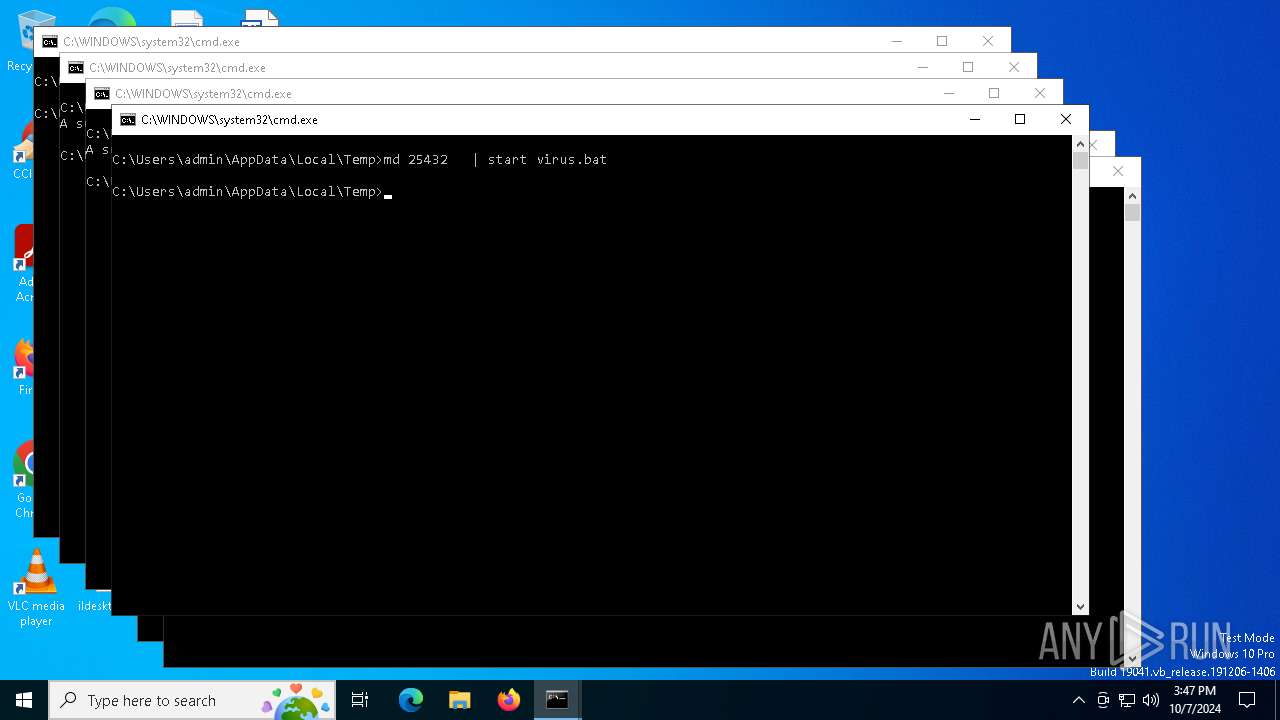
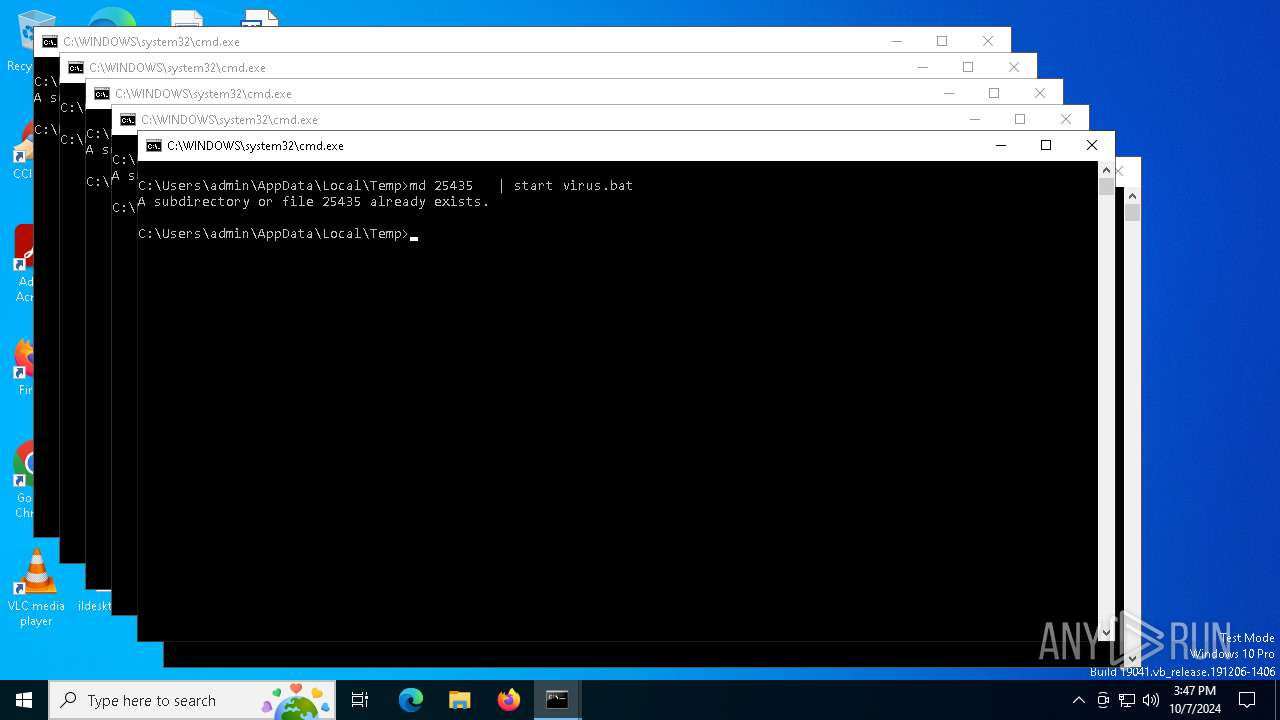
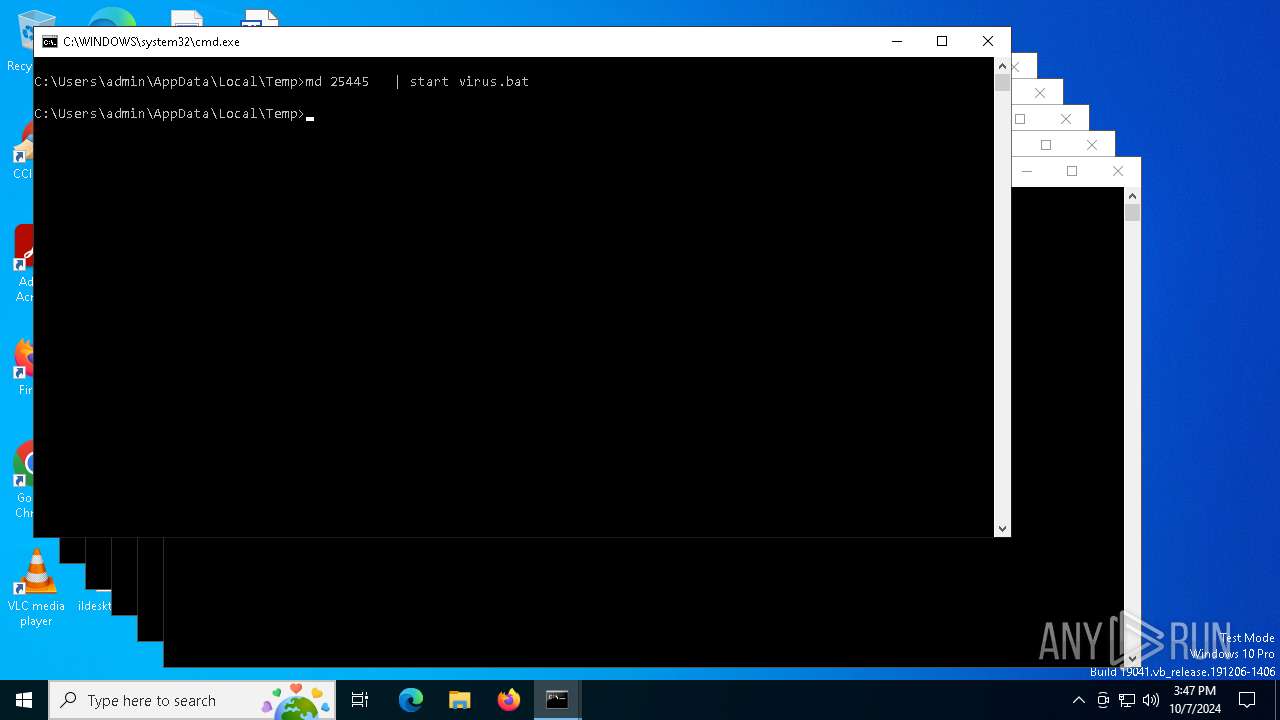
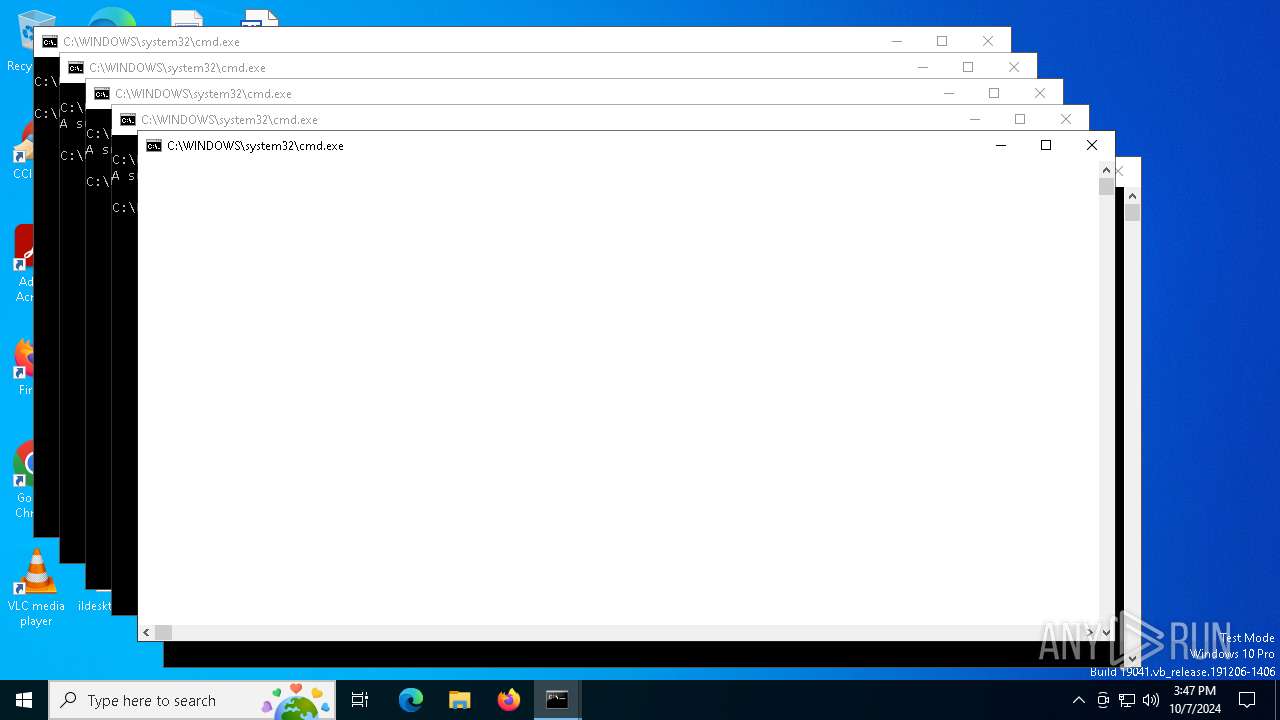
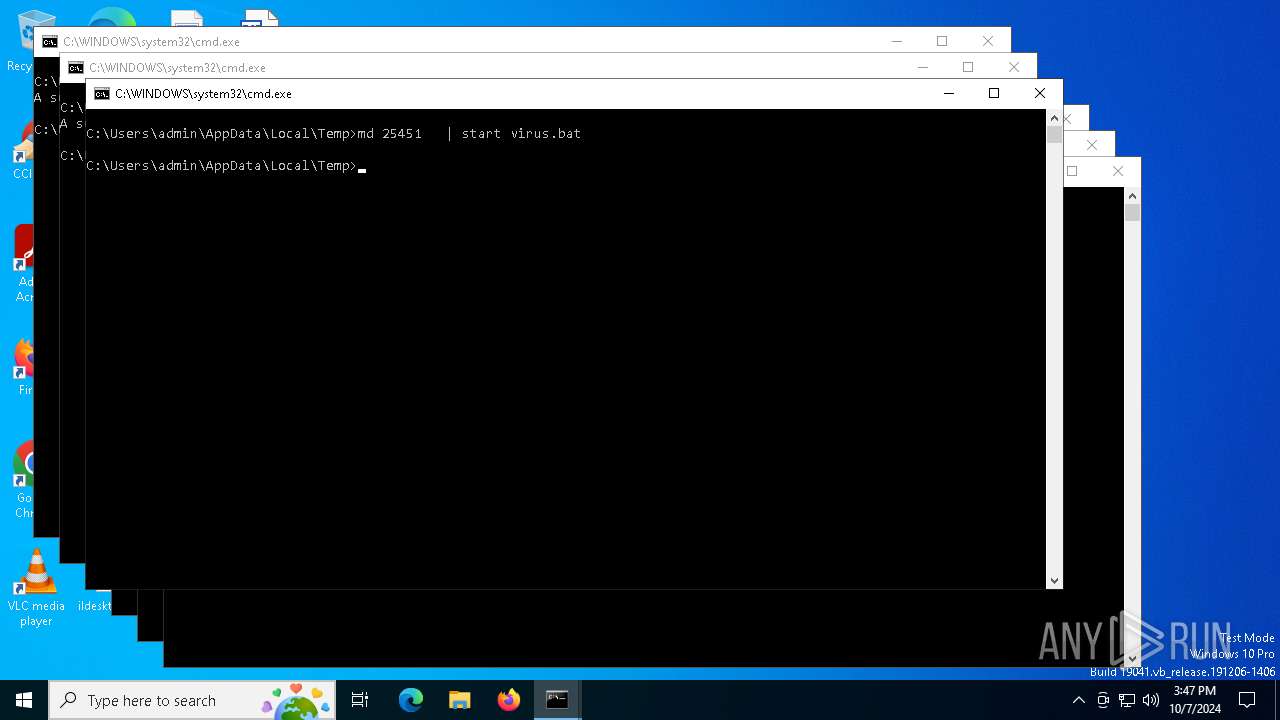
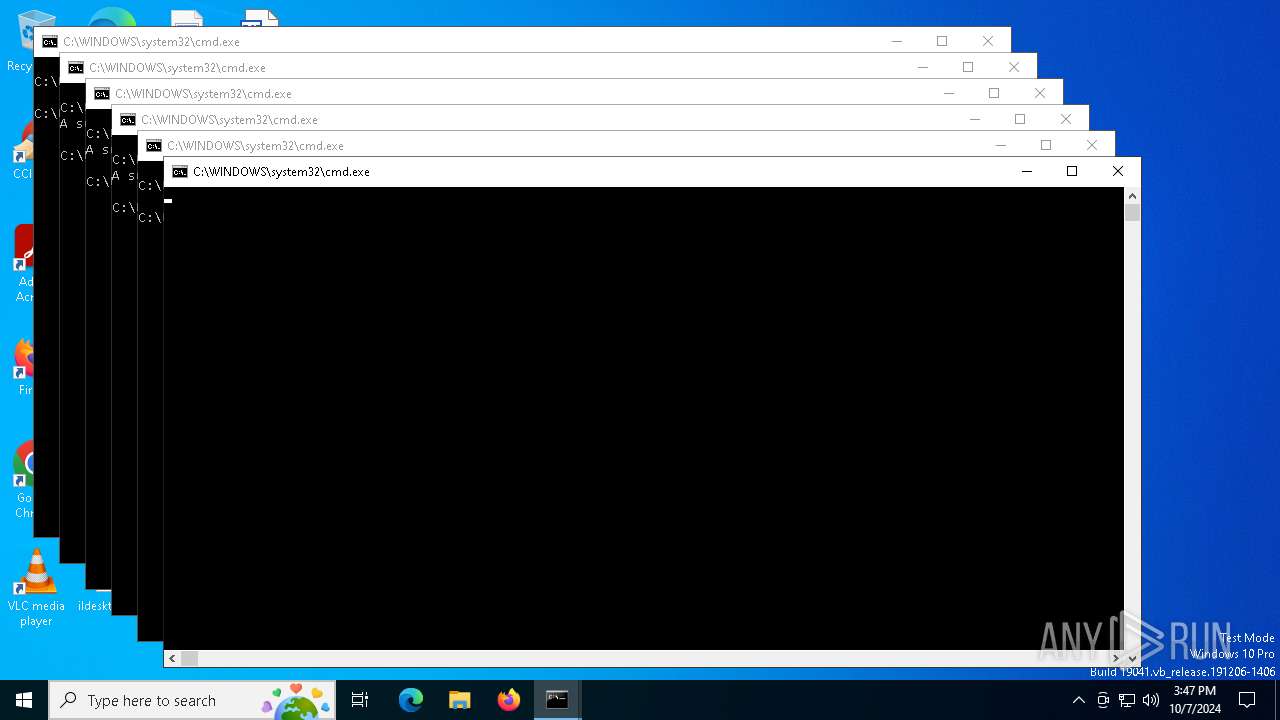
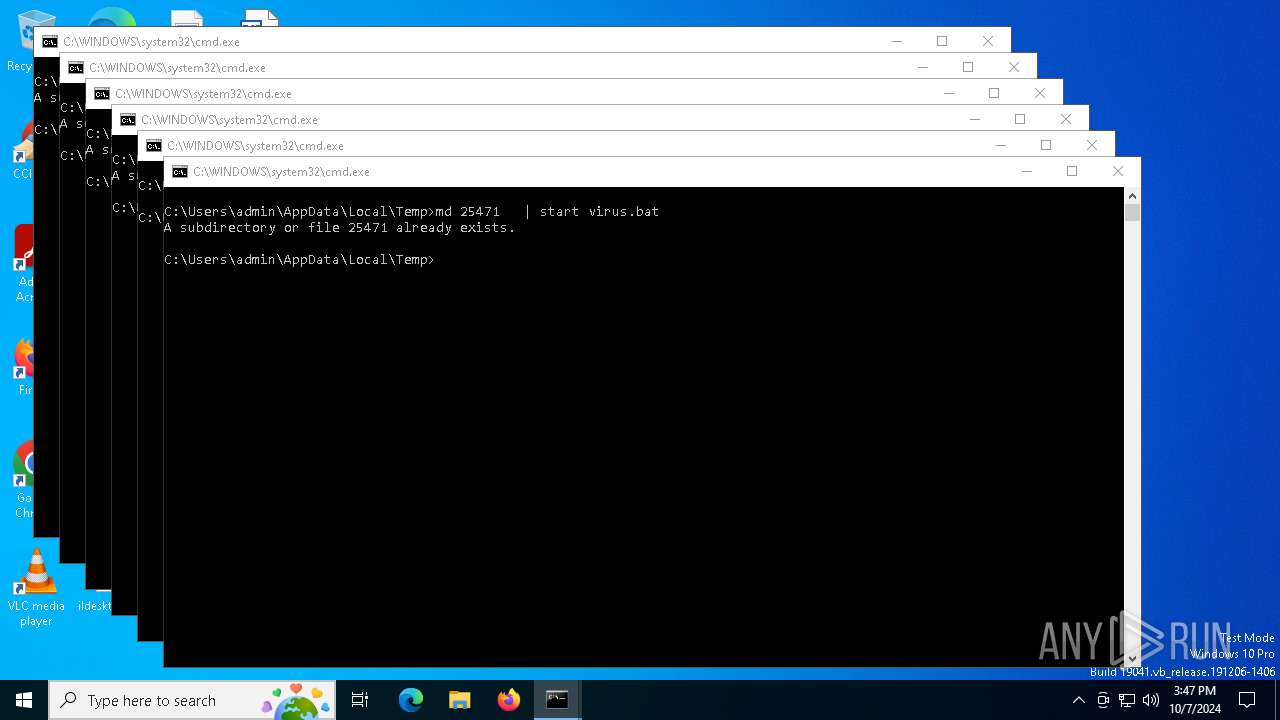
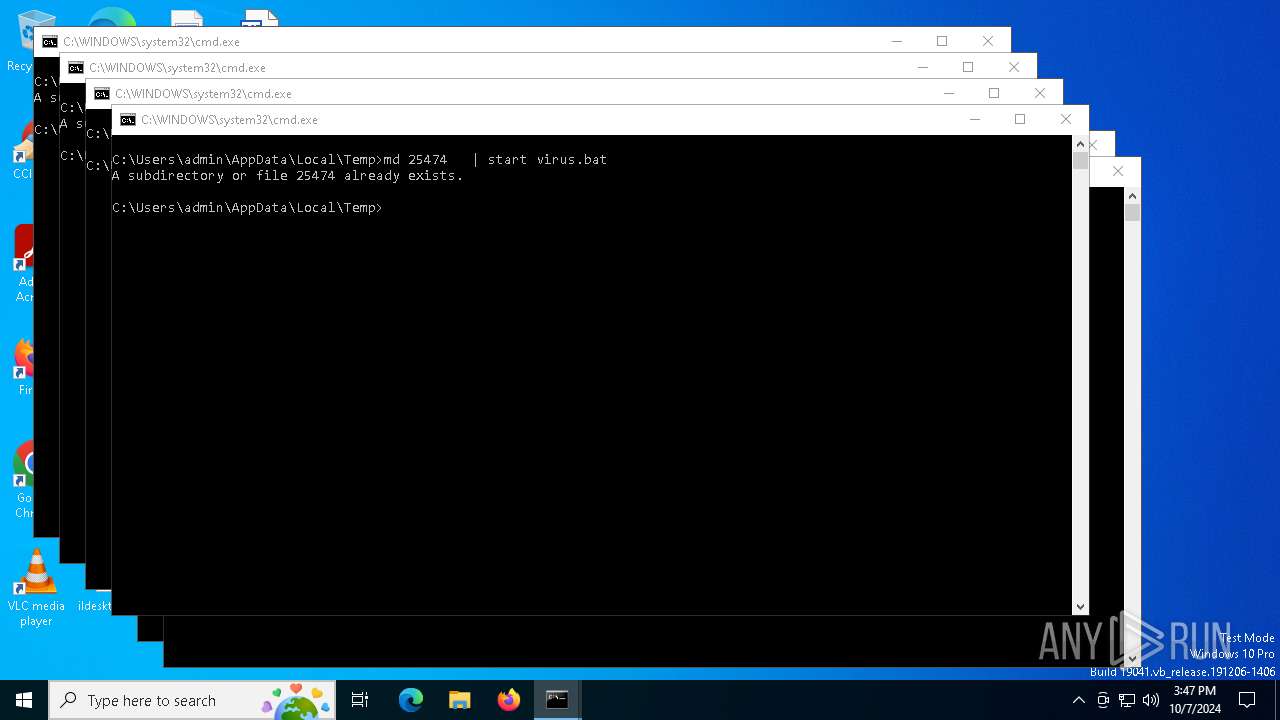
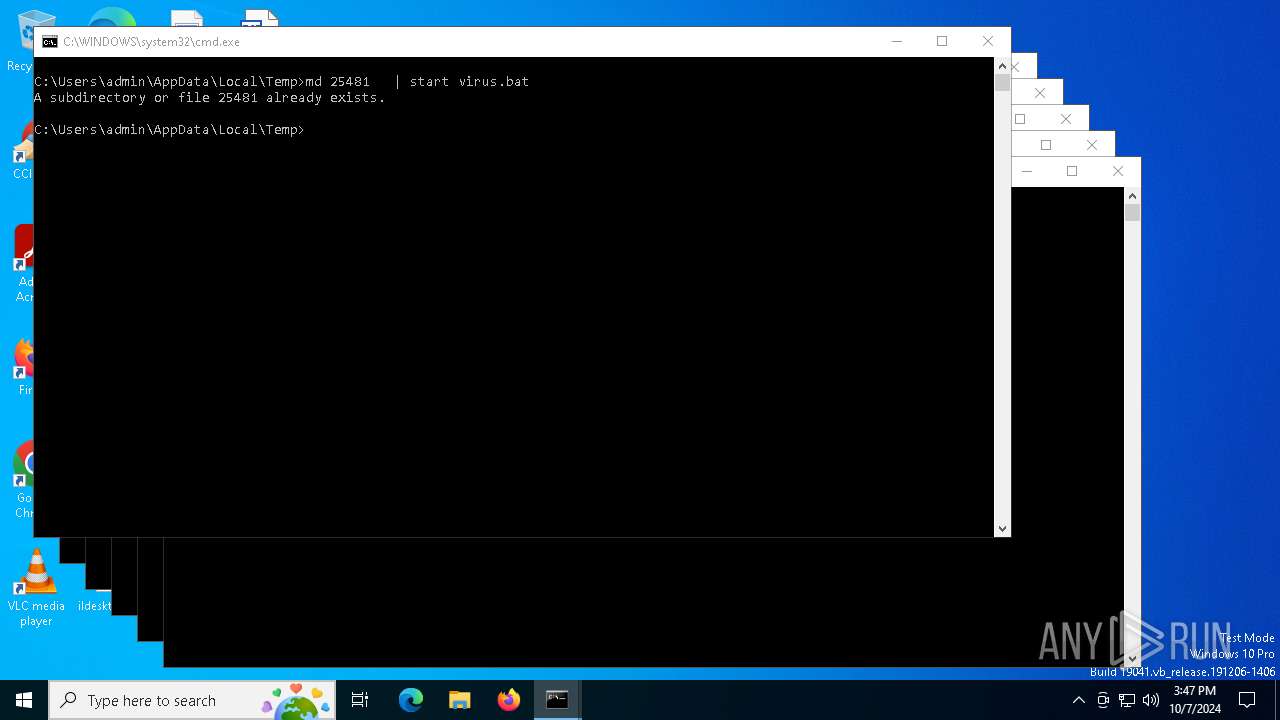
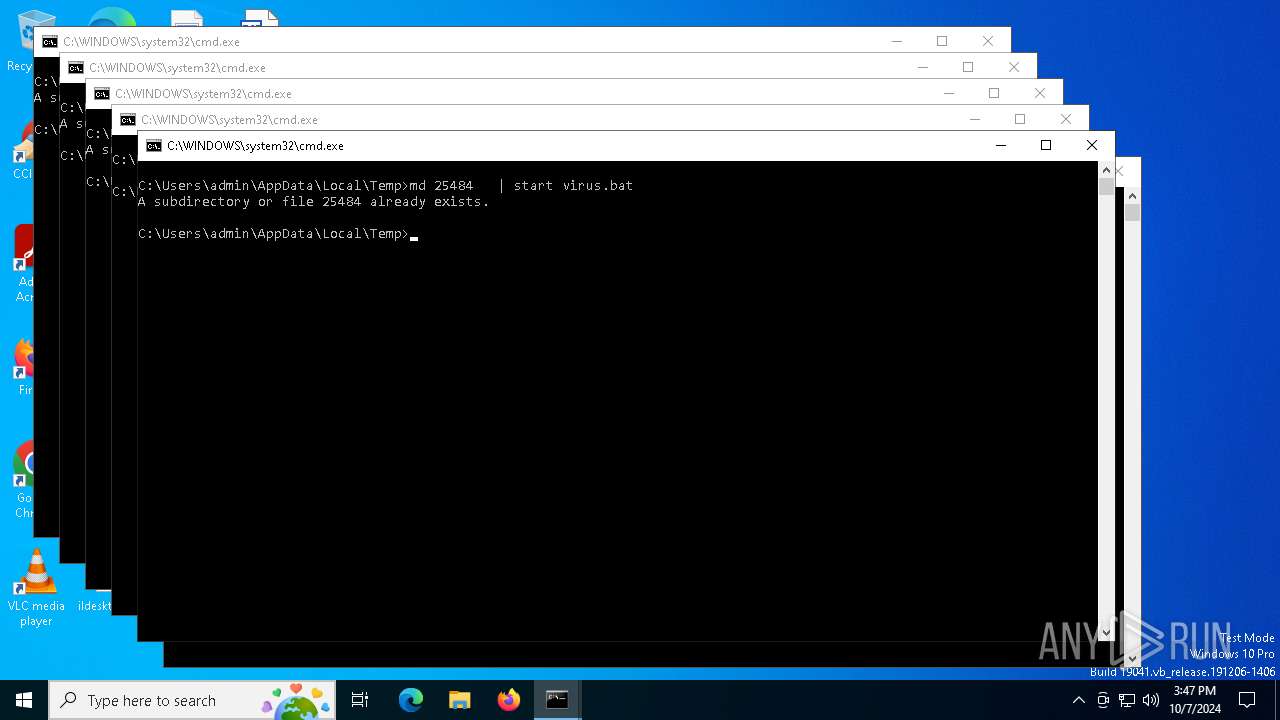
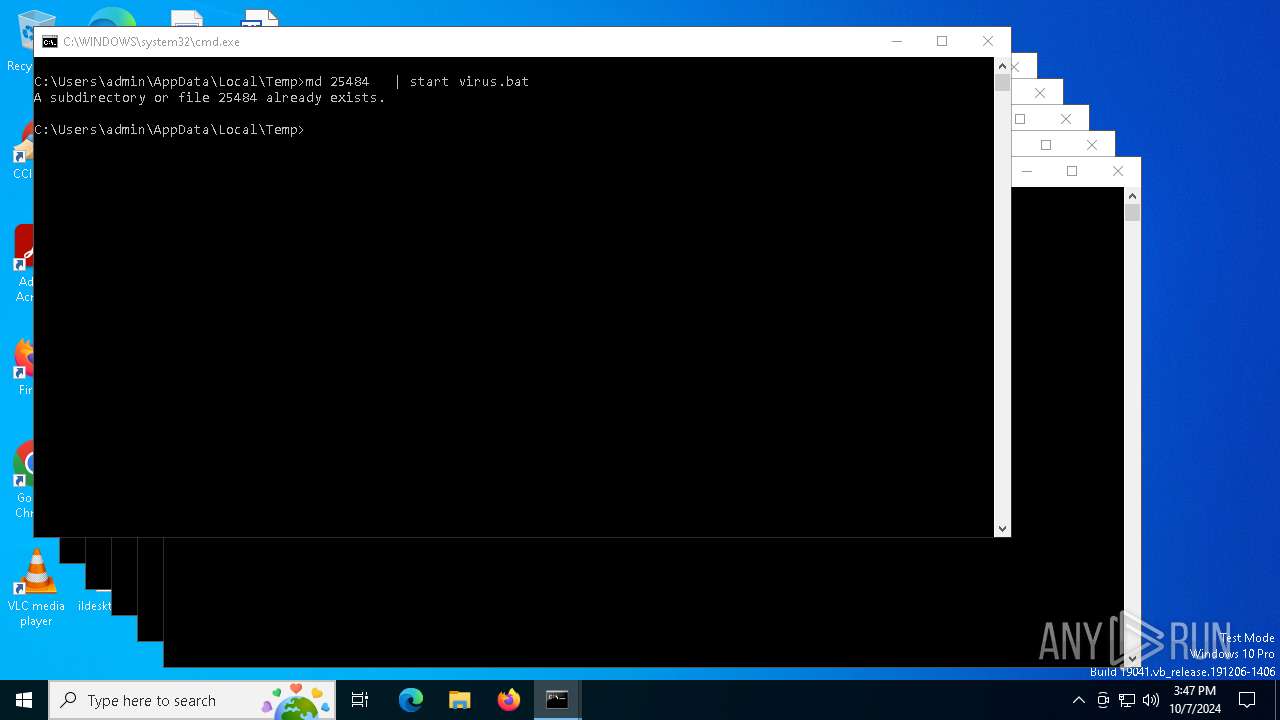
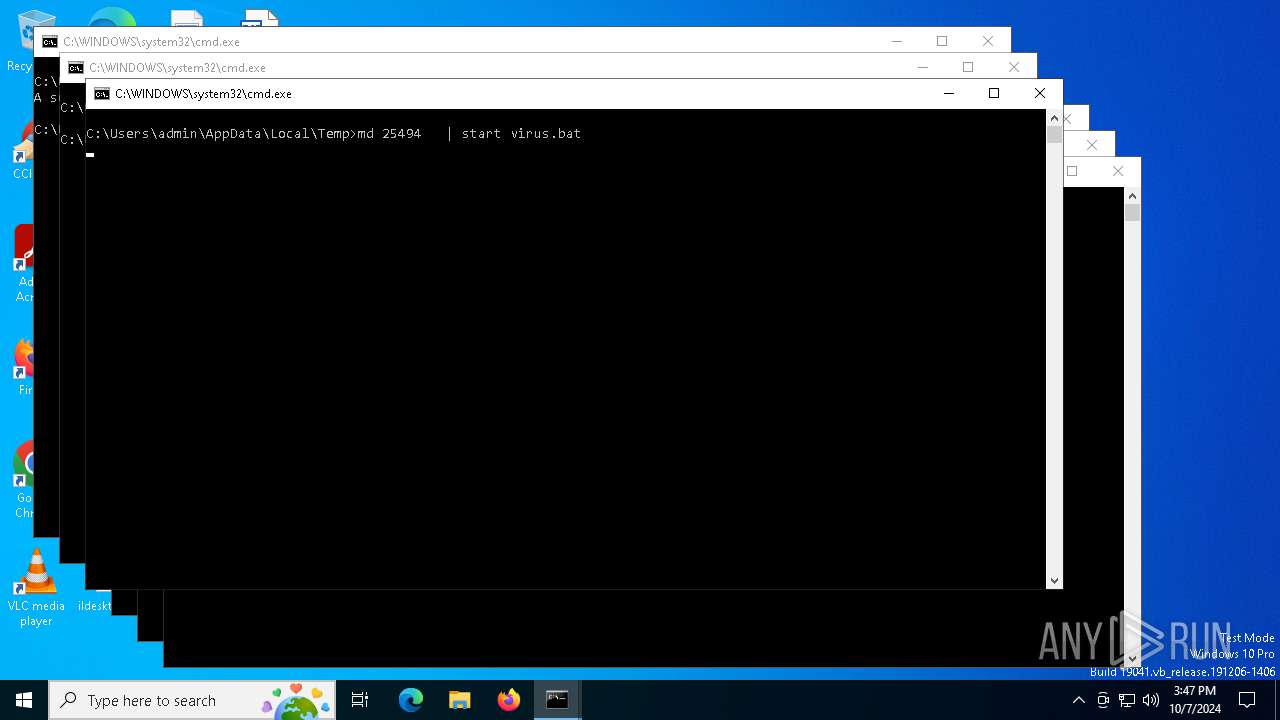
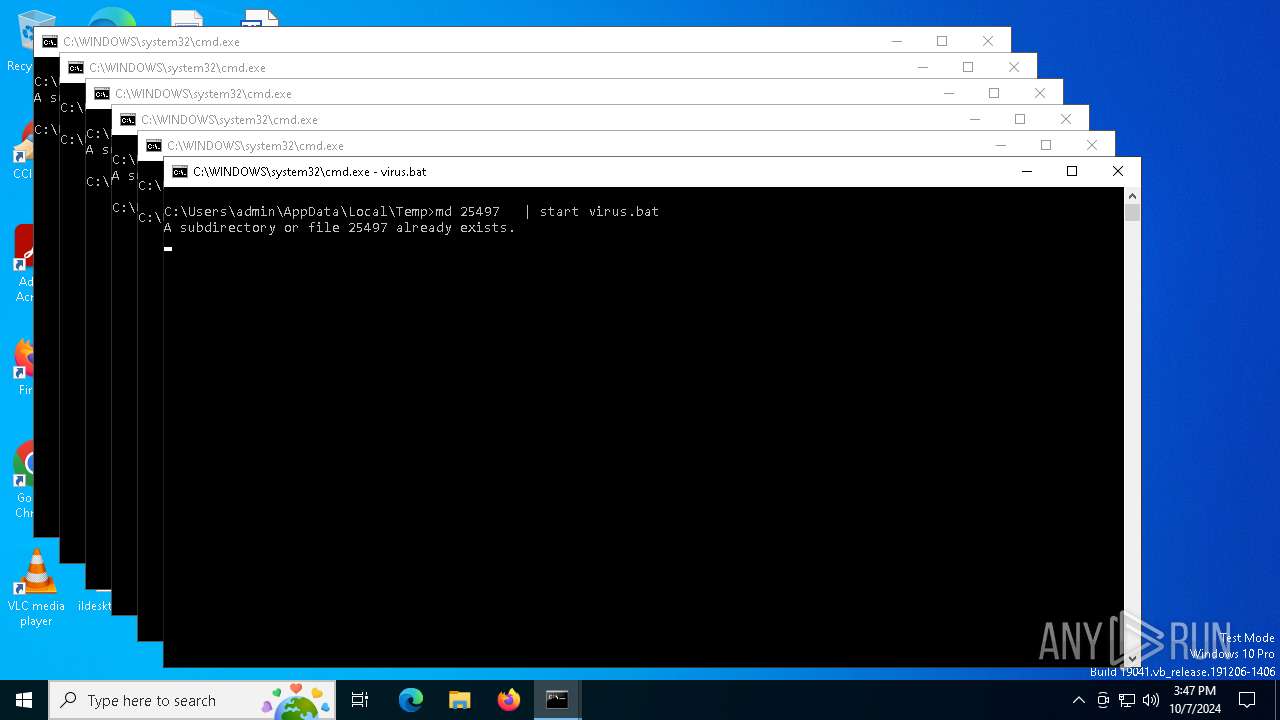
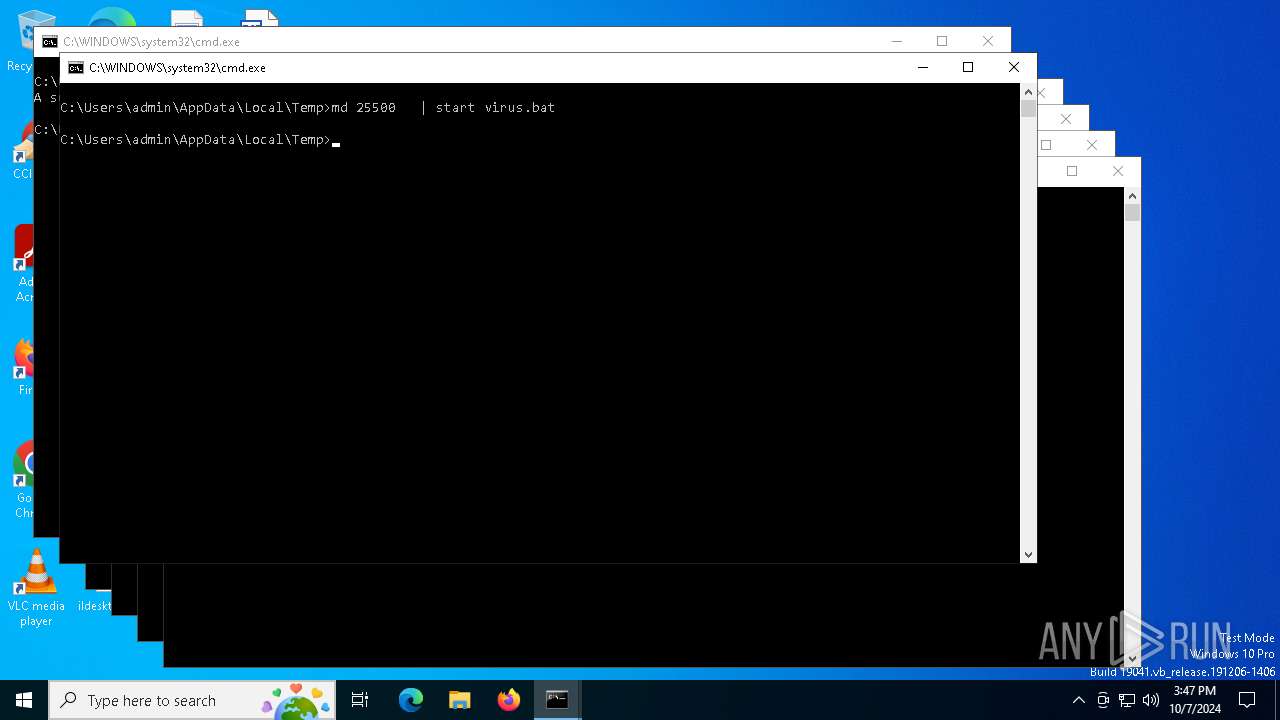
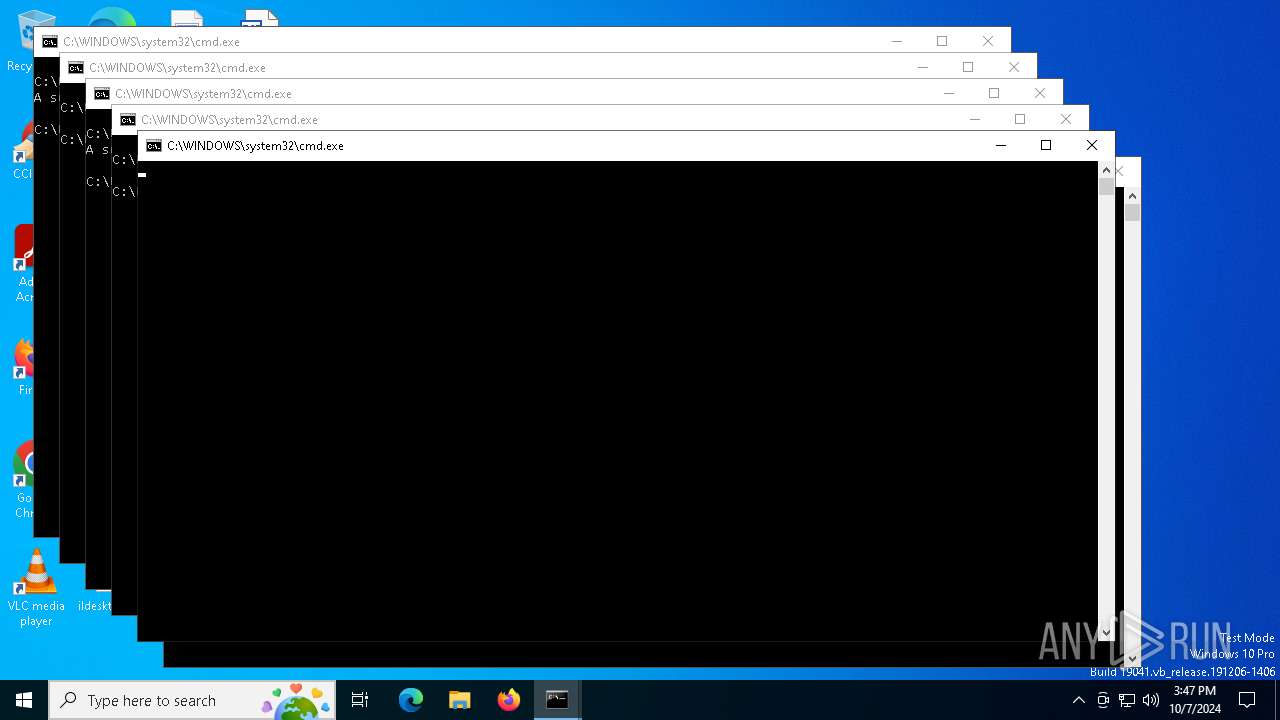
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1236)
- cmd.exe (PID: 608)
- cmd.exe (PID: 5240)
- cmd.exe (PID: 4524)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 4368)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 5484)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 6868)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 5476)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 6564)
- cmd.exe (PID: 68)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 2208)
- cmd.exe (PID: 5088)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 3396)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 876)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 5128)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 3160)
- cmd.exe (PID: 5092)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 1372)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 5500)
- cmd.exe (PID: 7080)
- cmd.exe (PID: 5500)
- cmd.exe (PID: 6772)
Application launched itself
- cmd.exe (PID: 1236)
- cmd.exe (PID: 5240)
- cmd.exe (PID: 608)
- cmd.exe (PID: 4524)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 4368)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 5484)
- cmd.exe (PID: 6868)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 5476)
- cmd.exe (PID: 68)
- cmd.exe (PID: 6564)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 5088)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 2208)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 3396)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 876)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 5128)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 3160)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 5092)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 7080)
- cmd.exe (PID: 1372)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 5500)
- cmd.exe (PID: 6772)
- cmd.exe (PID: 5500)
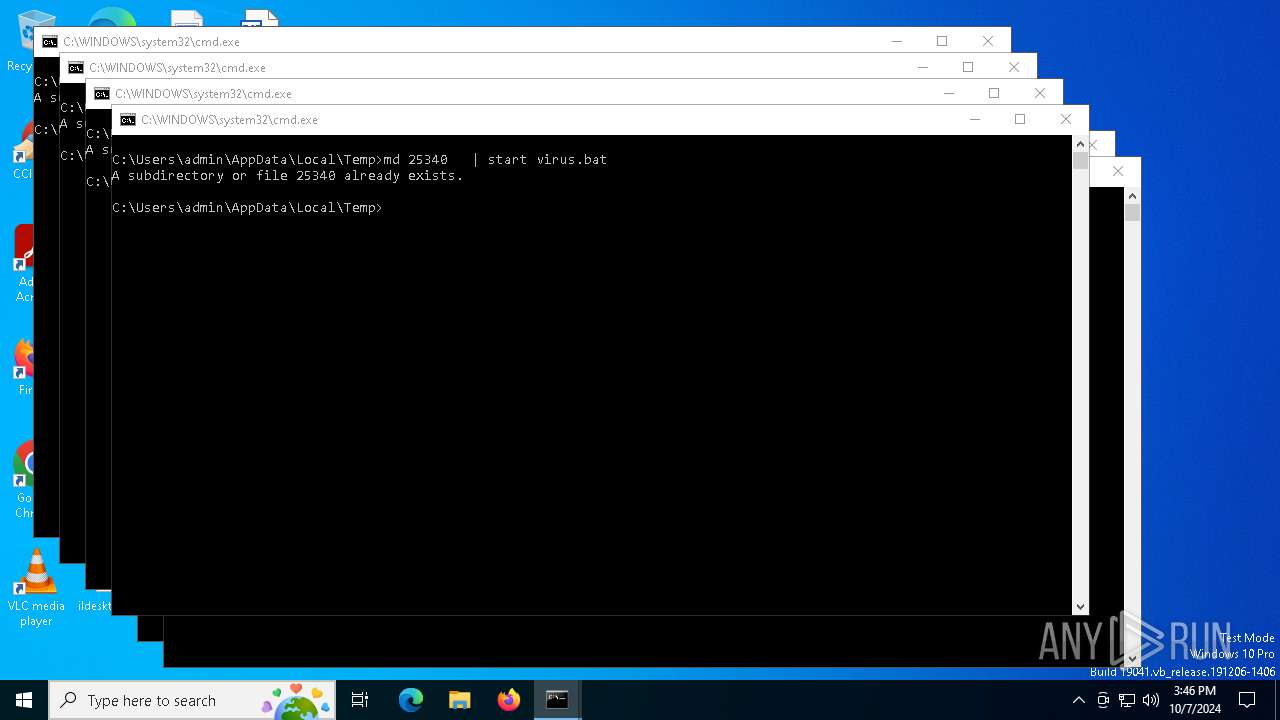
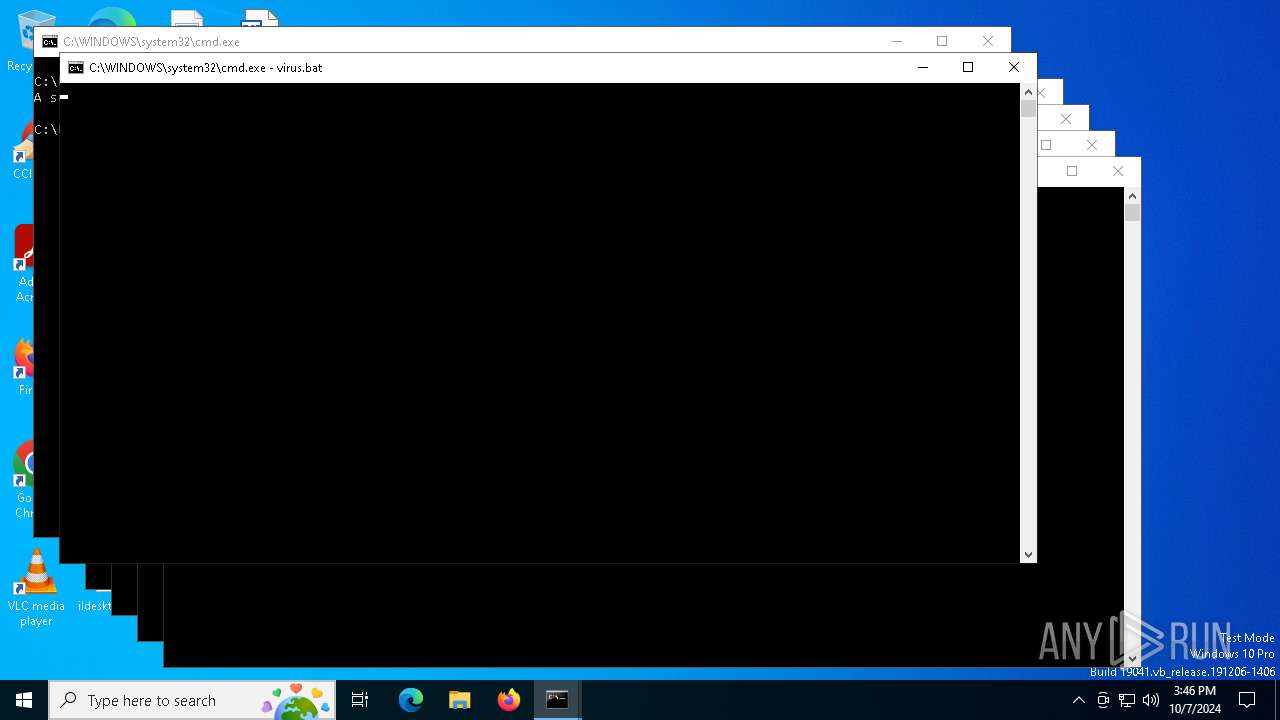
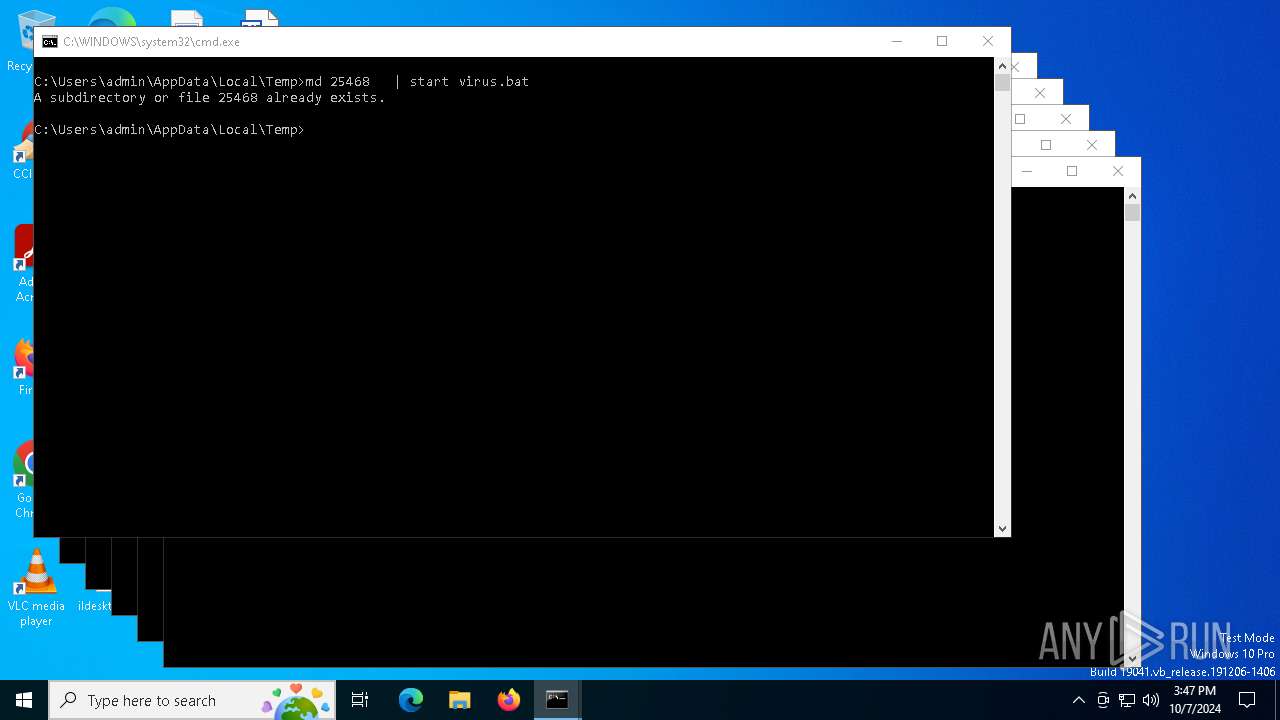
Executing commands from a ".bat" file
- cmd.exe (PID: 5240)
- cmd.exe (PID: 1236)
- cmd.exe (PID: 608)
- cmd.exe (PID: 4524)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 5180)
- cmd.exe (PID: 4368)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 5484)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 6868)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 5476)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 6564)
- cmd.exe (PID: 68)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 2208)
- cmd.exe (PID: 5088)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 3396)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 876)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 5092)
- cmd.exe (PID: 3256)
- cmd.exe (PID: 3160)
- cmd.exe (PID: 5500)
- cmd.exe (PID: 7080)
- cmd.exe (PID: 1372)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 5128)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 6844)
- cmd.exe (PID: 5500)
- cmd.exe (PID: 6772)
INFO
Creates a new folder
- cmd.exe (PID: 6836)
- cmd.exe (PID: 7016)
- cmd.exe (PID: 4472)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 1308)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 1848)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 6504)
- cmd.exe (PID: 6176)
- cmd.exe (PID: 5584)
- cmd.exe (PID: 4080)
- cmd.exe (PID: 6664)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 5136)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 5280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
962
Monitored processes
89
Malicious processes
9
Suspicious processes
27
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | C:\WINDOWS\system32\cmd.exe /K virus.bat | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | C:\WINDOWS\system32\cmd.exe /S /D /c" start virus.bat" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | C:\WINDOWS\system32\cmd.exe /K virus.bat | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | C:\WINDOWS\system32\cmd.exe /S /D /c" md 25317 " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1236 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Virus.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1308 | C:\WINDOWS\system32\cmd.exe /S /D /c" md 25317 " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1308 | C:\WINDOWS\system32\cmd.exe /S /D /c" start virus.bat" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 446
Read events
1 446
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
42
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8264 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
10288 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
10288 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5244 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6776 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6776 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |