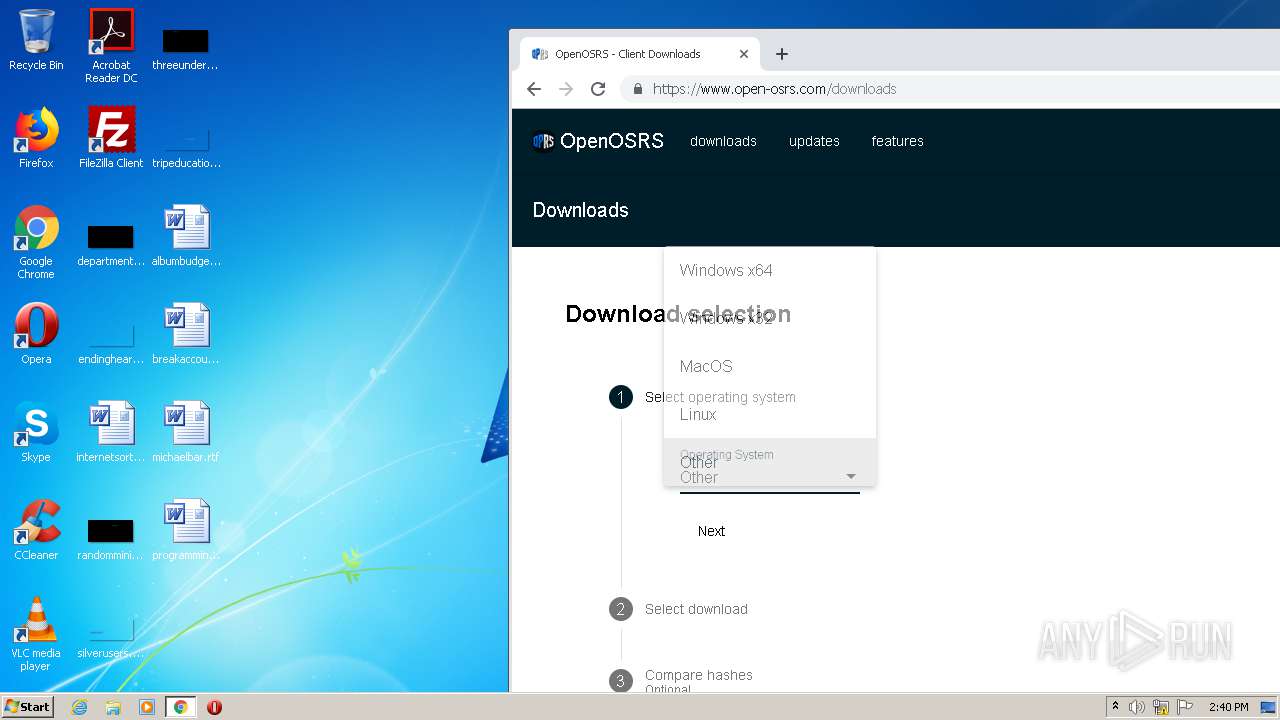
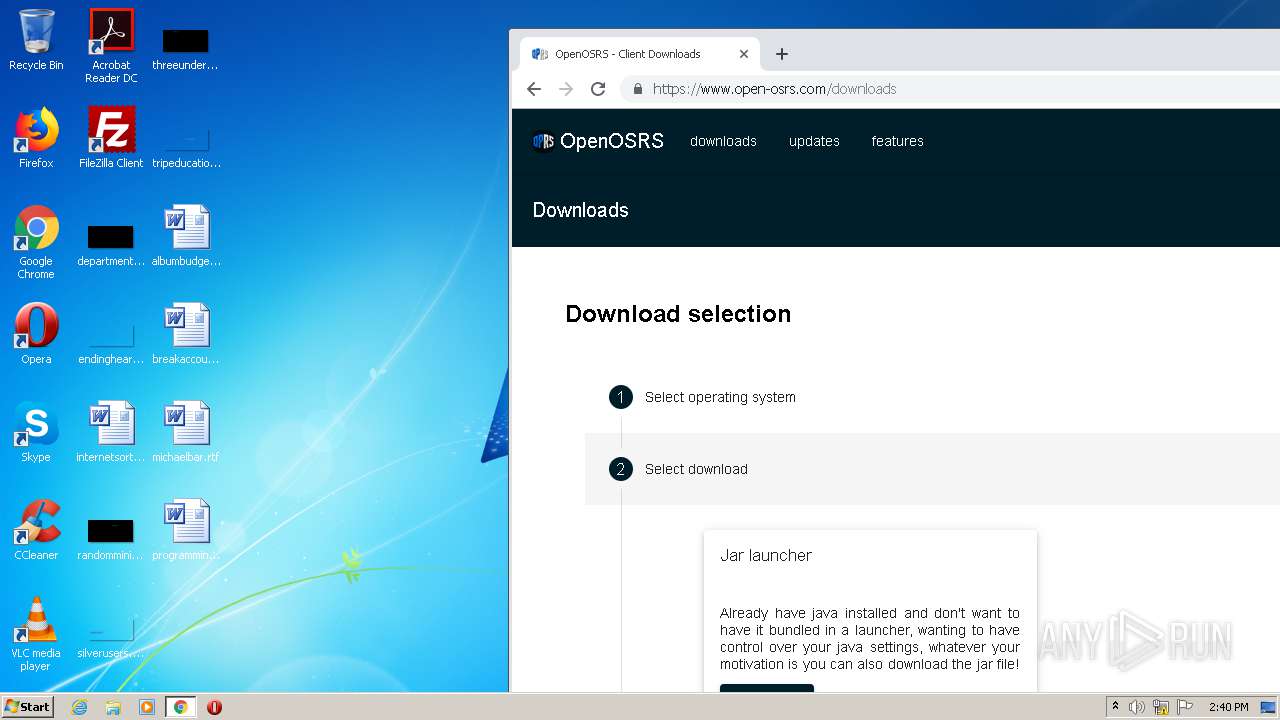
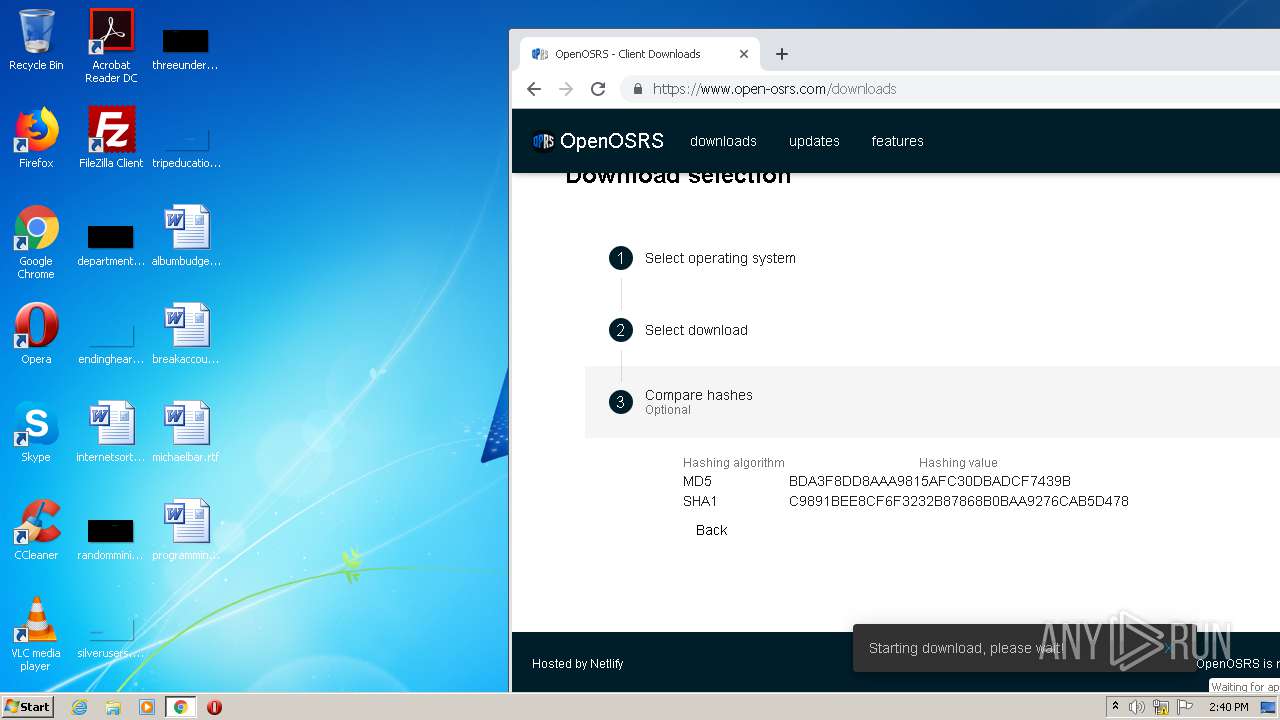
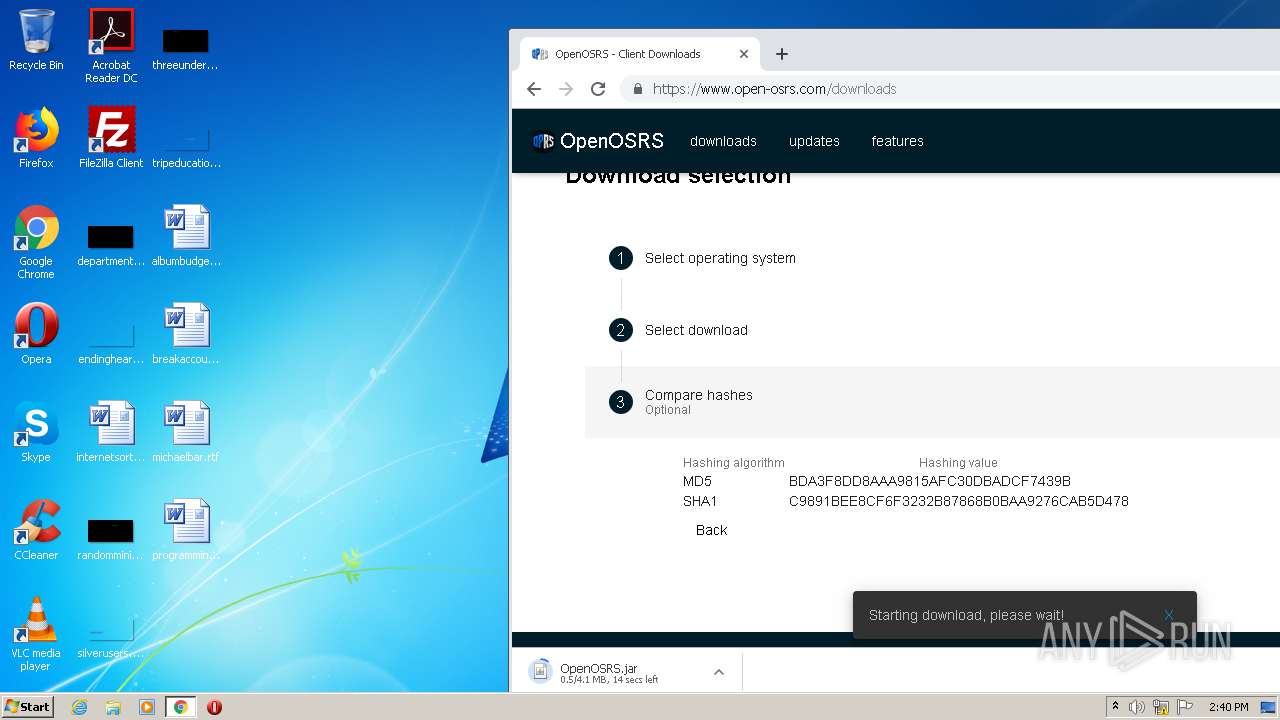
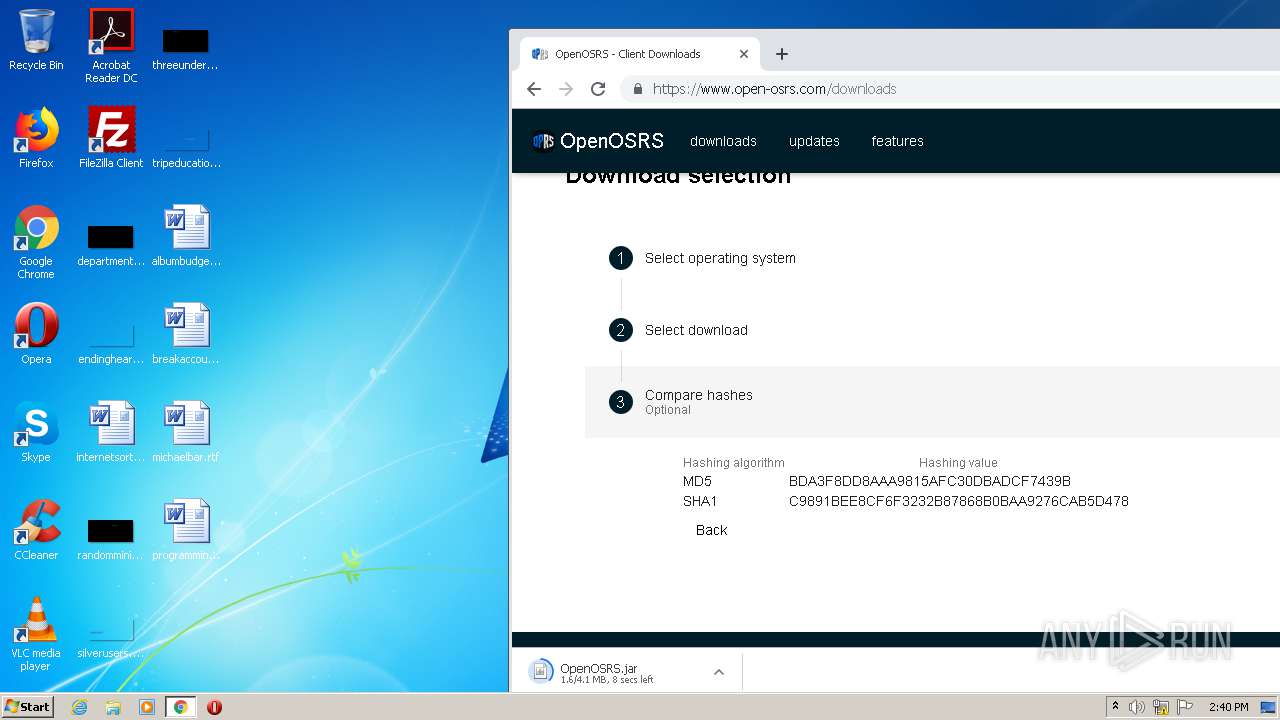
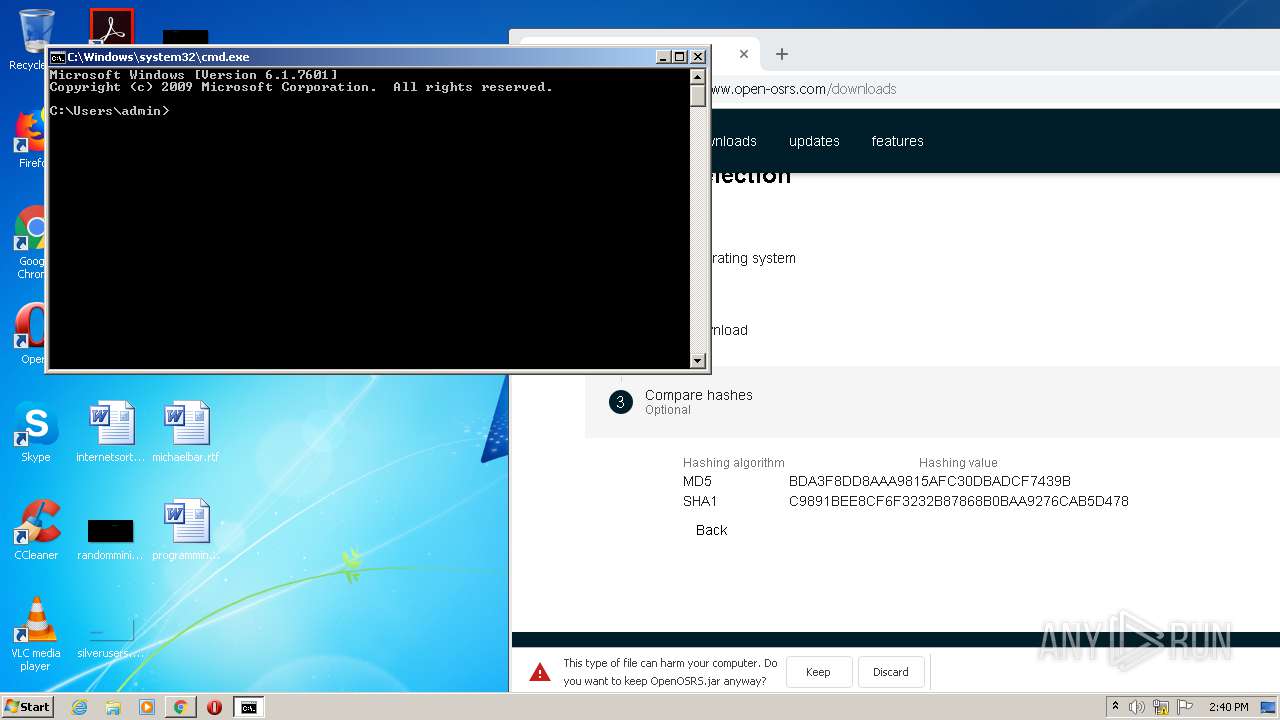
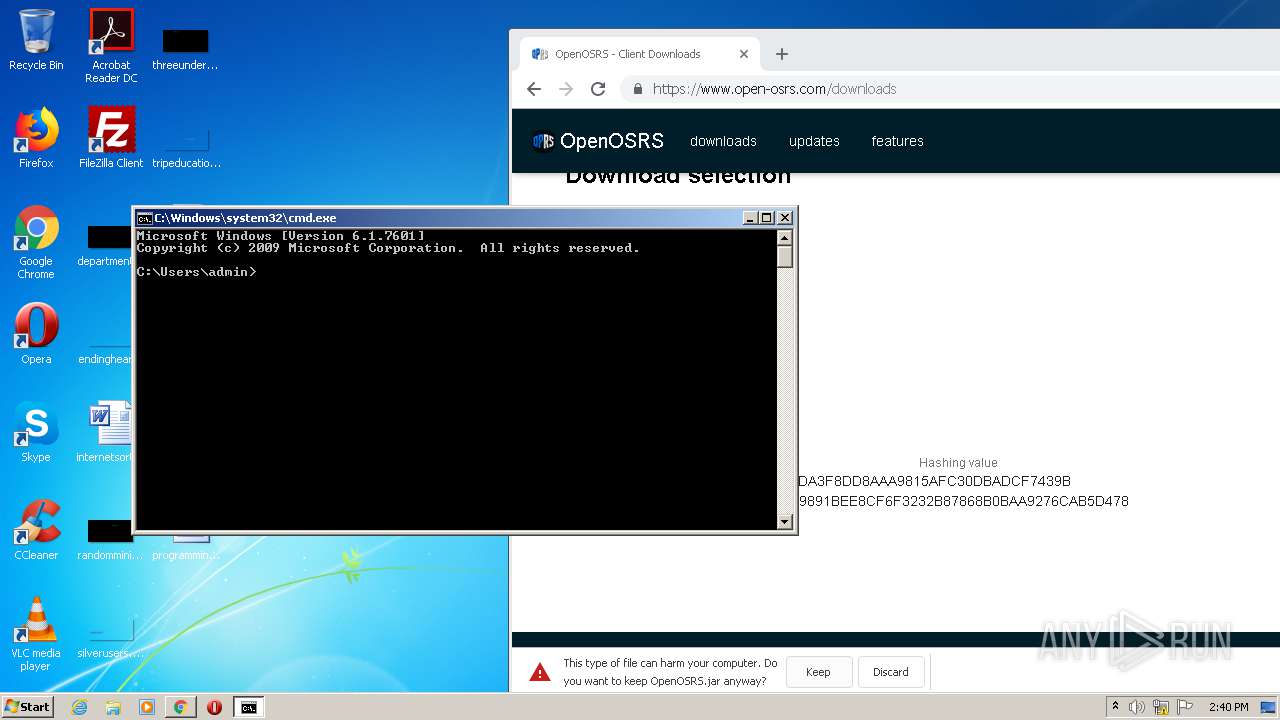
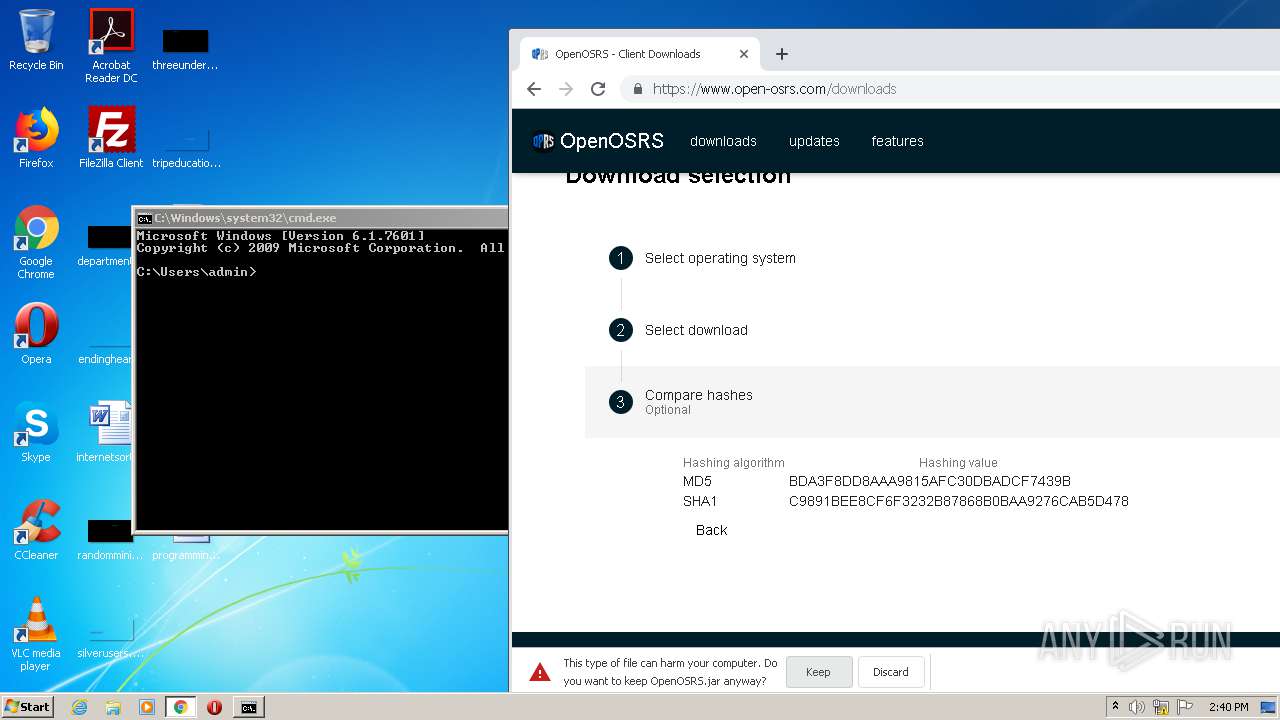
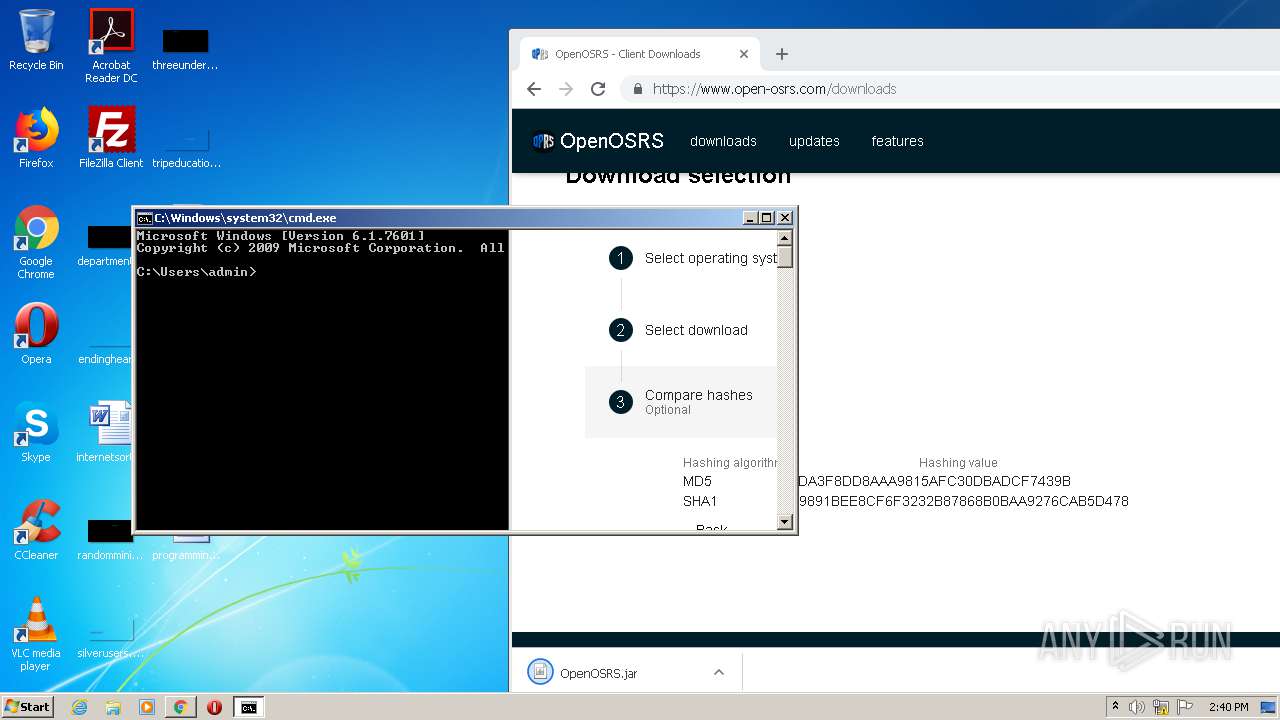
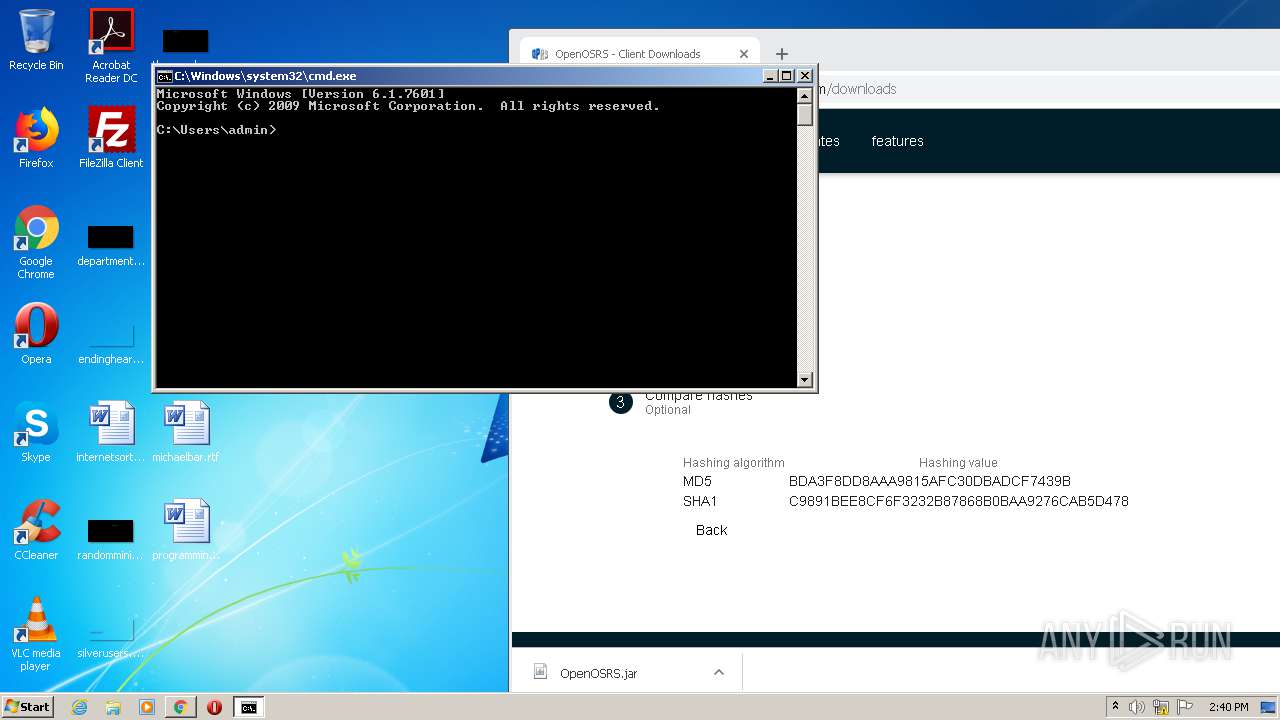
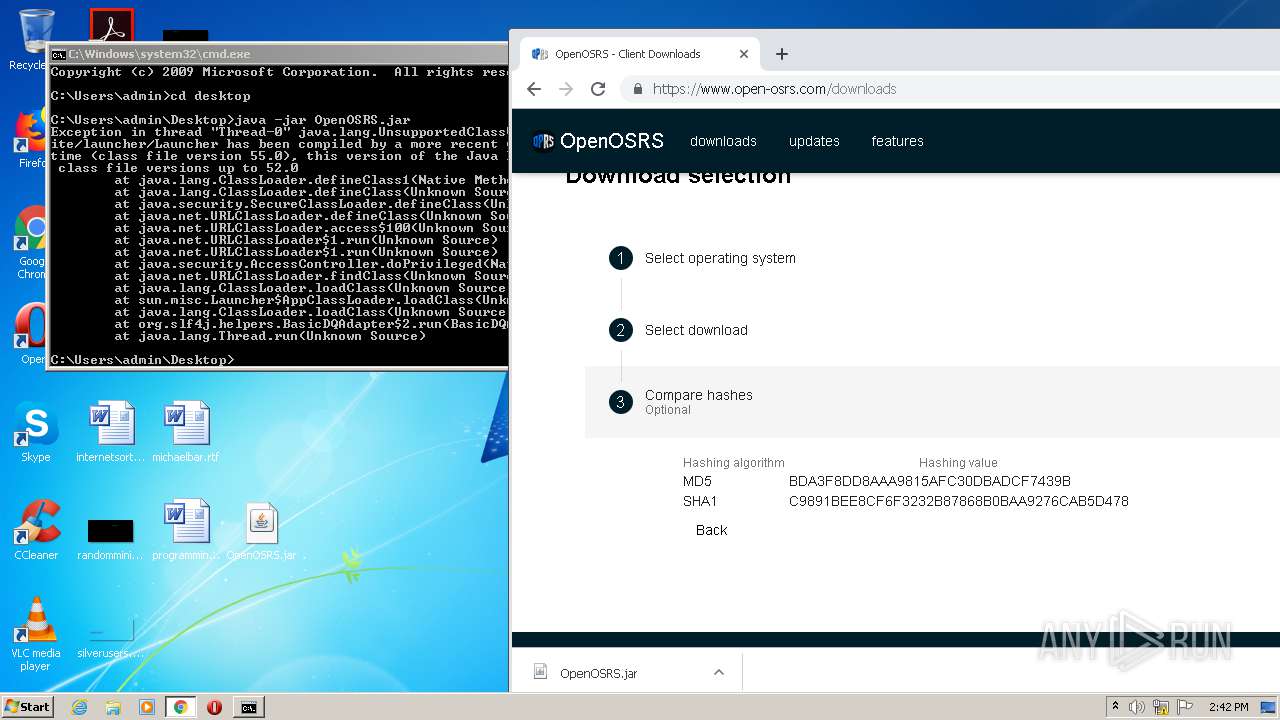
| download: | OpenOSRS.jar |
| Full analysis: | https://app.any.run/tasks/92be2260-9809-4828-b749-741b591d239b |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 13:38:20 |
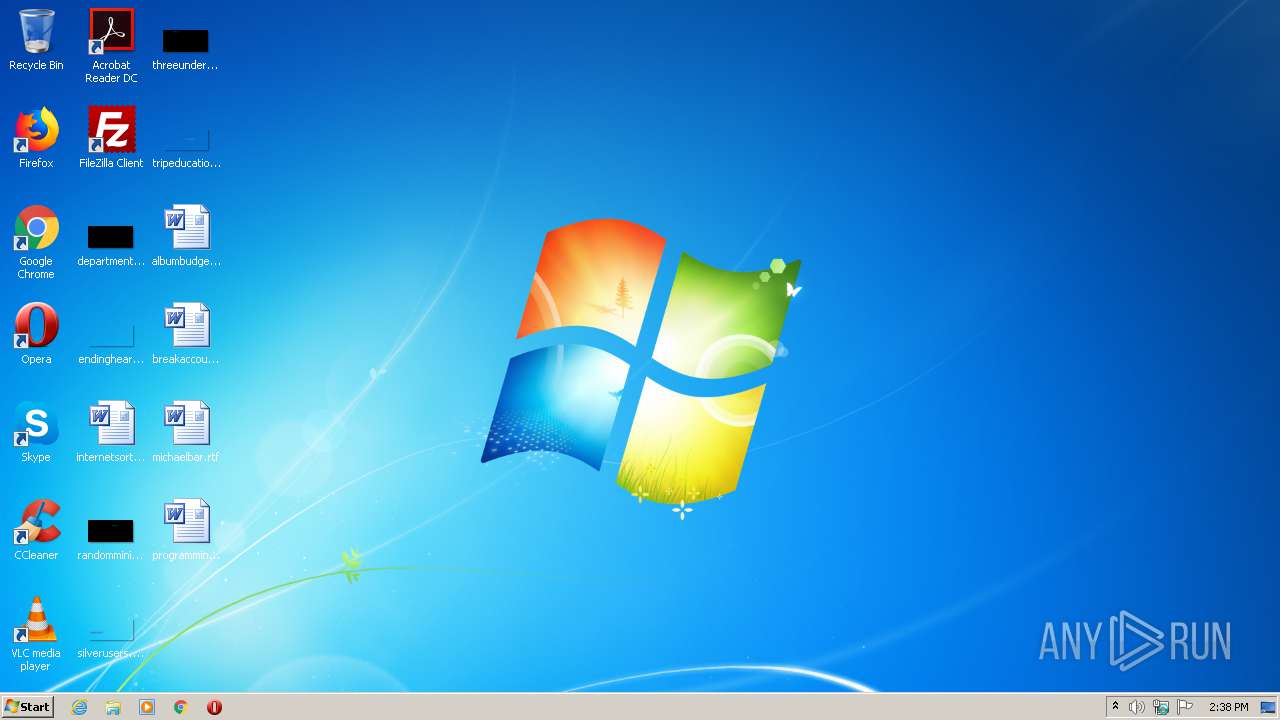
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | 4068A28747EC907086E6CACCC2AD6DE1 |
| SHA1: | 634BDC2653FA37D87759A32BE65E71CD5C851441 |
| SHA256: | CA76D6B9CC43FDA59A4450D501DA2FFD191B6B1A007D9F446C2A501FF7CB1631 |
| SSDEEP: | 49152:7pRrlMH6GNLi7KkPfAXUPspp6ZJGamX2tzts4tszvmNCpWXZtRkj8gju/59R71az:1HMaGN+PK/D6dEfdiQS/gj0N7u6vBXpy |
MALICIOUS
Loads dropped or rewritten executable
- java.exe (PID: 4068)
- java.exe (PID: 1516)
Changes the autorun value in the registry
- REG.exe (PID: 2296)
SUSPICIOUS
Executes JAVA applets
- javaw.exe (PID: 2760)
Executable content was dropped or overwritten
- java.exe (PID: 4068)
- java.exe (PID: 1516)
Creates files in the user directory
- javaw.exe (PID: 2760)
- java.exe (PID: 4068)
- java.exe (PID: 1452)
Uses REG.EXE to modify Windows registry
- java.exe (PID: 4068)
Application launched itself
- java.exe (PID: 1452)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3608)
Reads the hosts file
- chrome.exe (PID: 3608)
- chrome.exe (PID: 3428)
Reads Internet Cache Settings
- chrome.exe (PID: 3428)
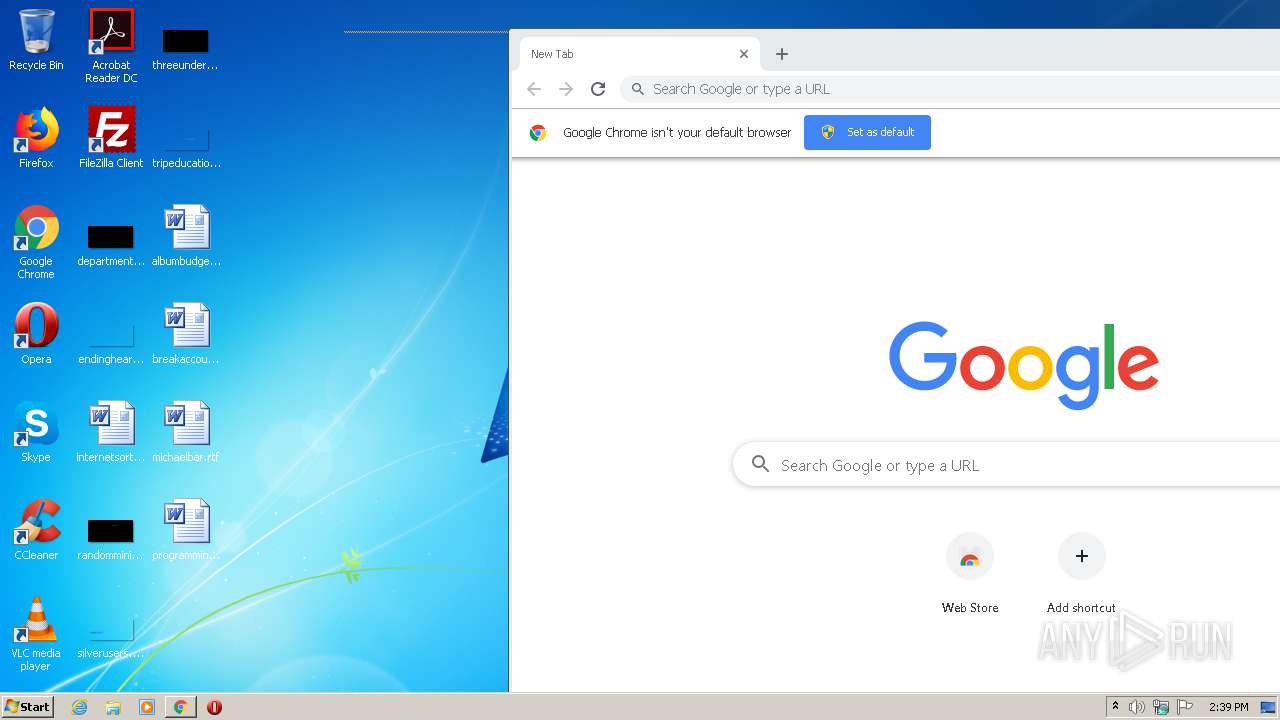
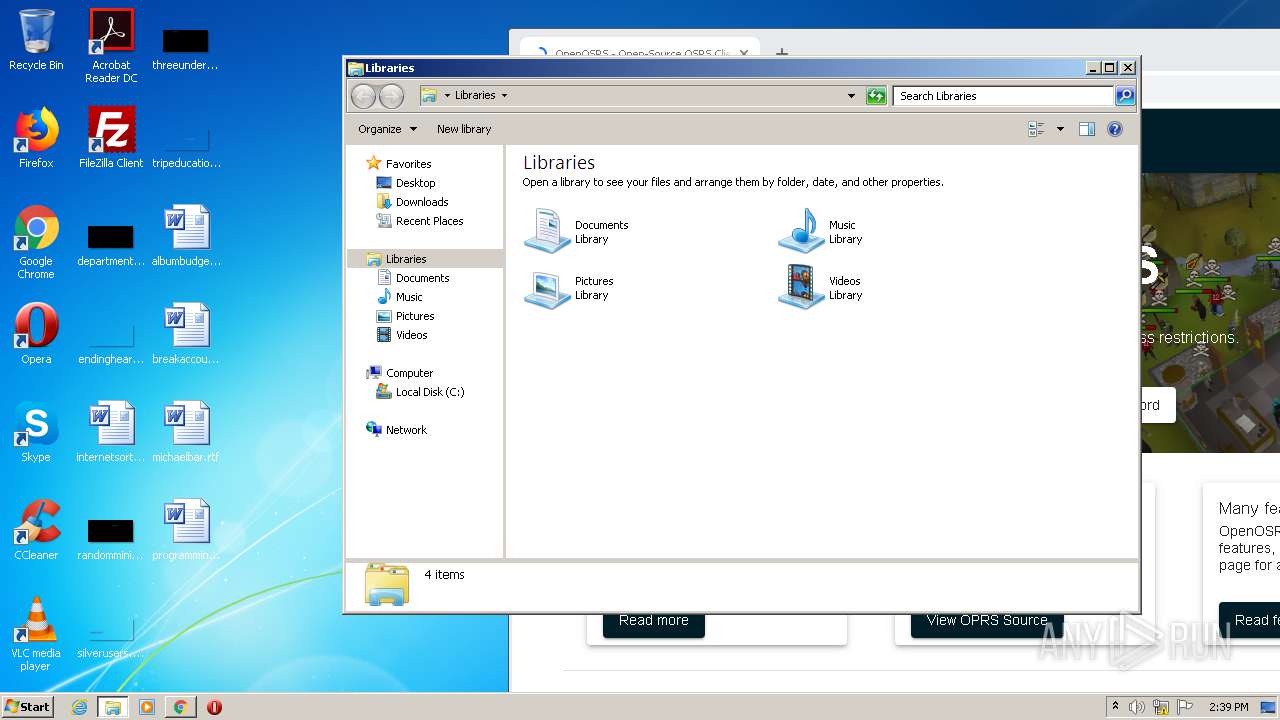
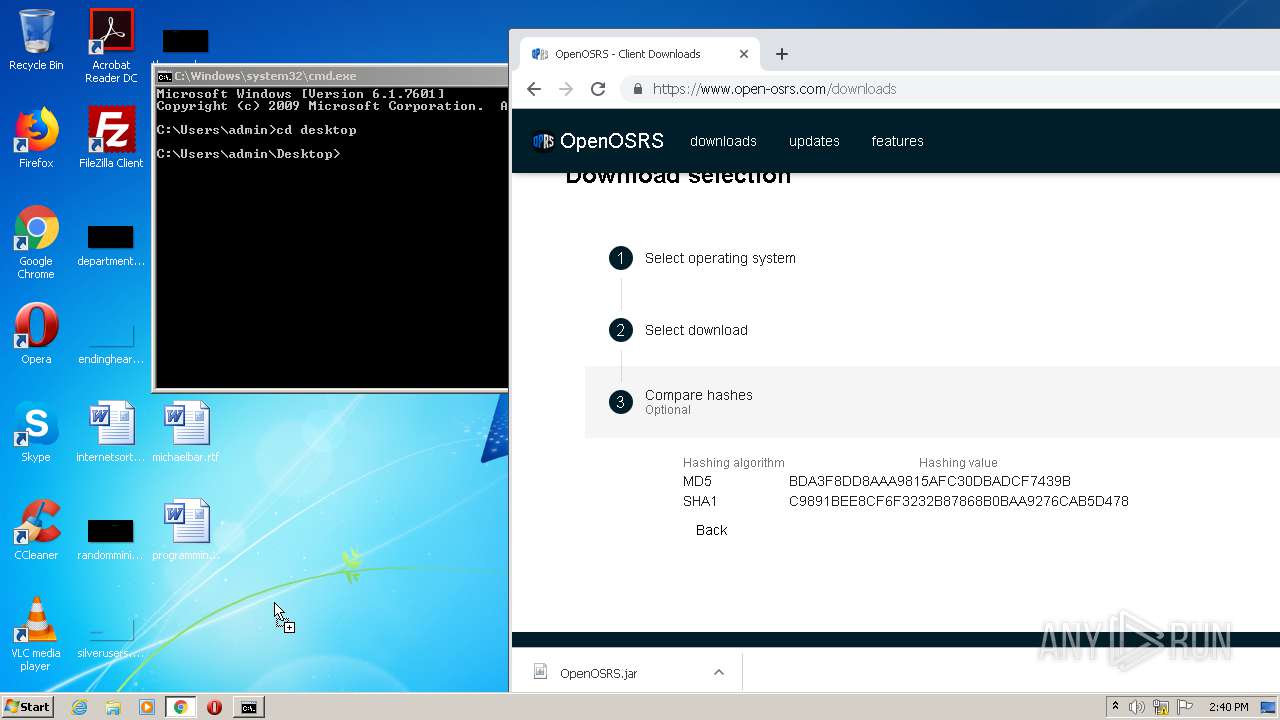
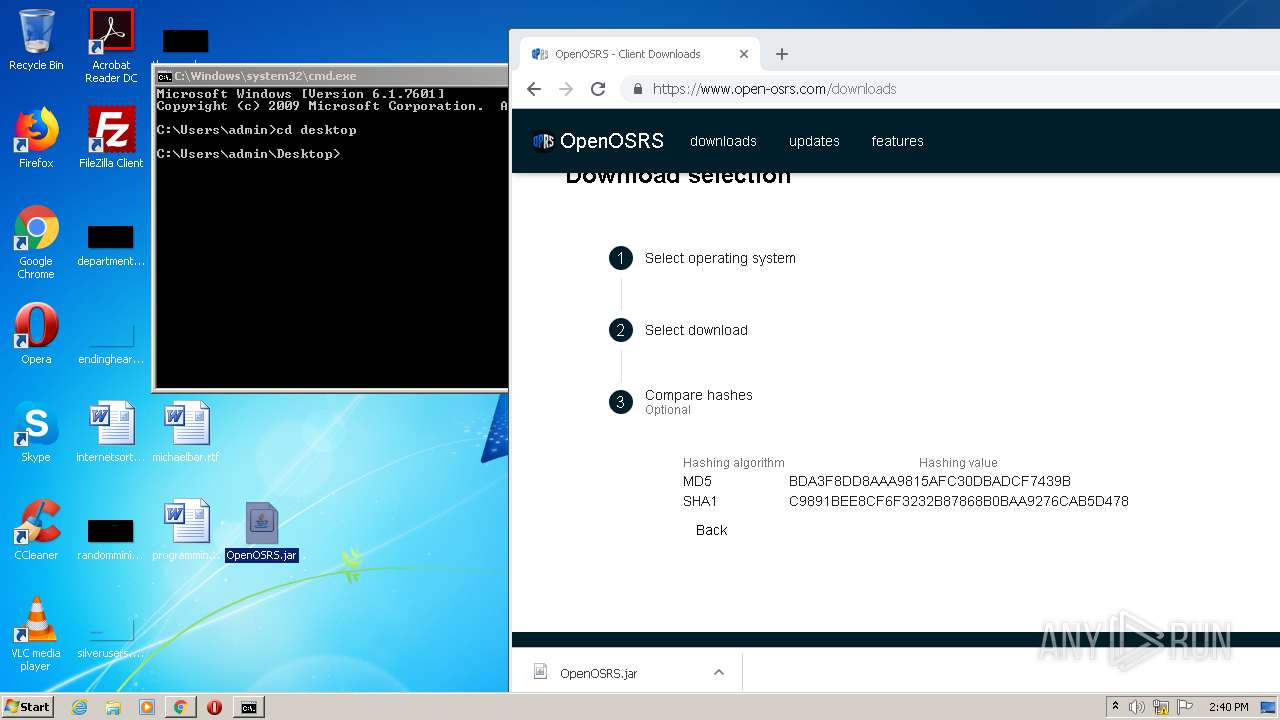
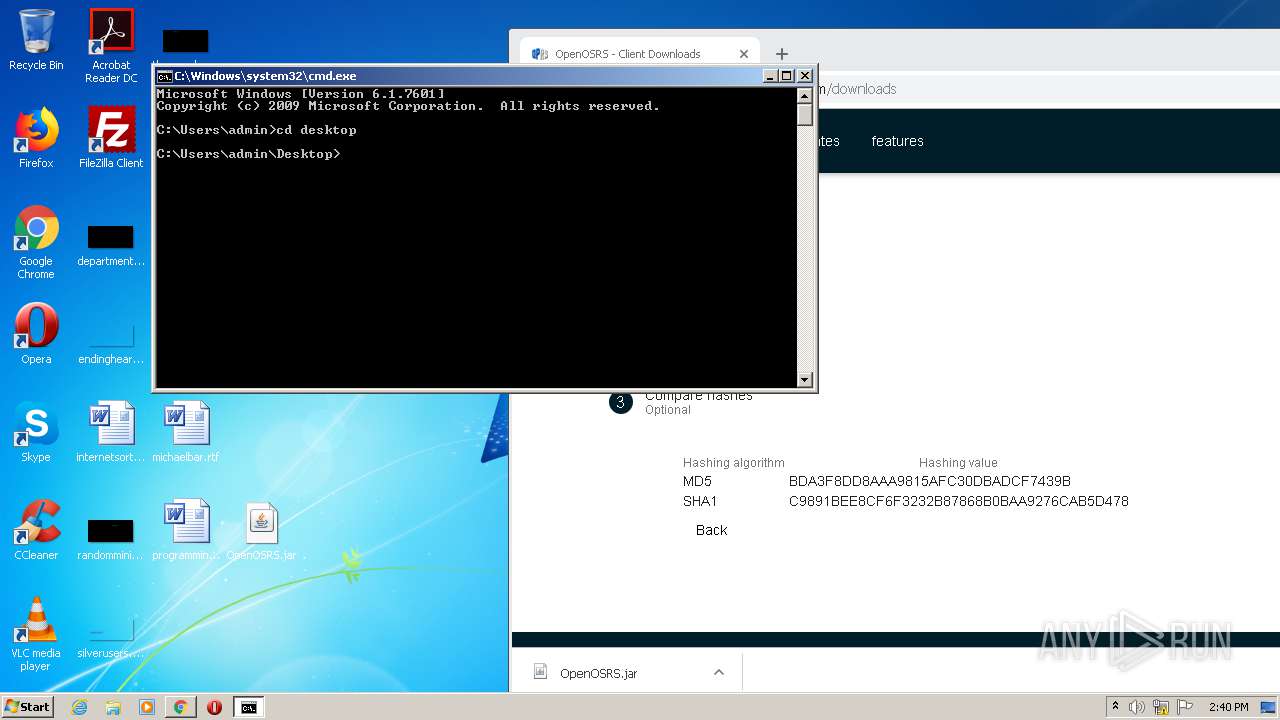
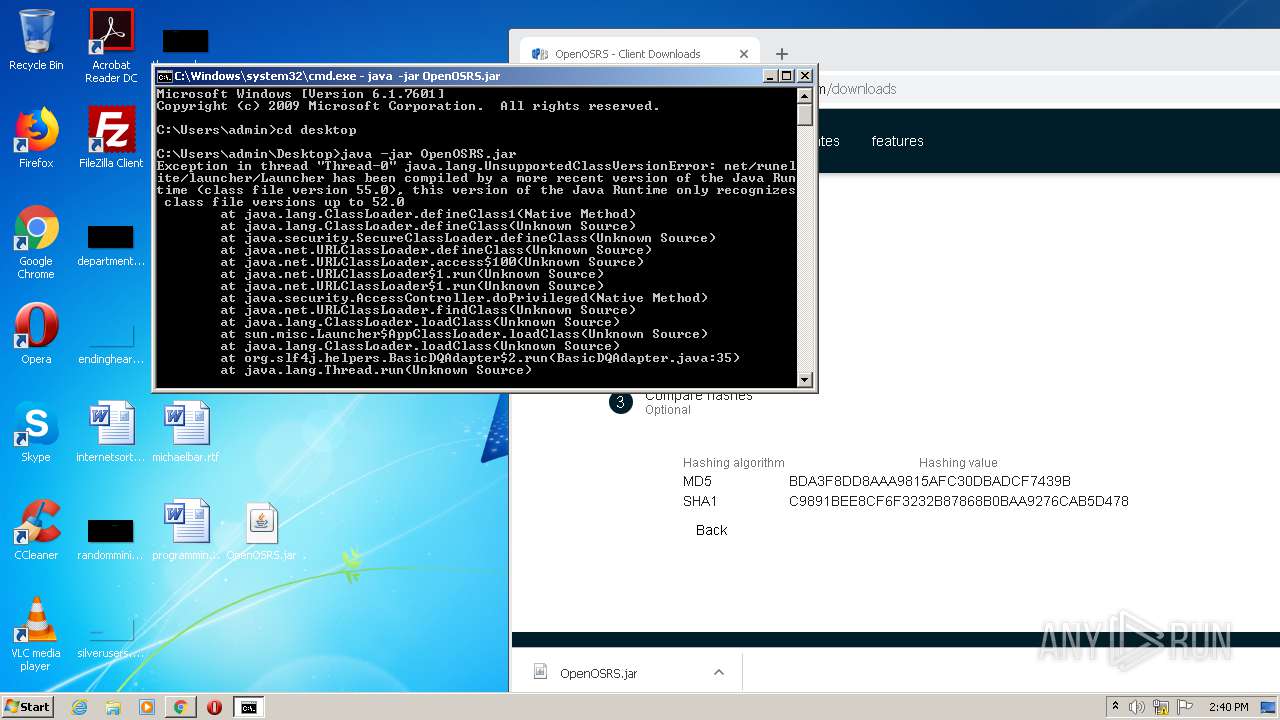
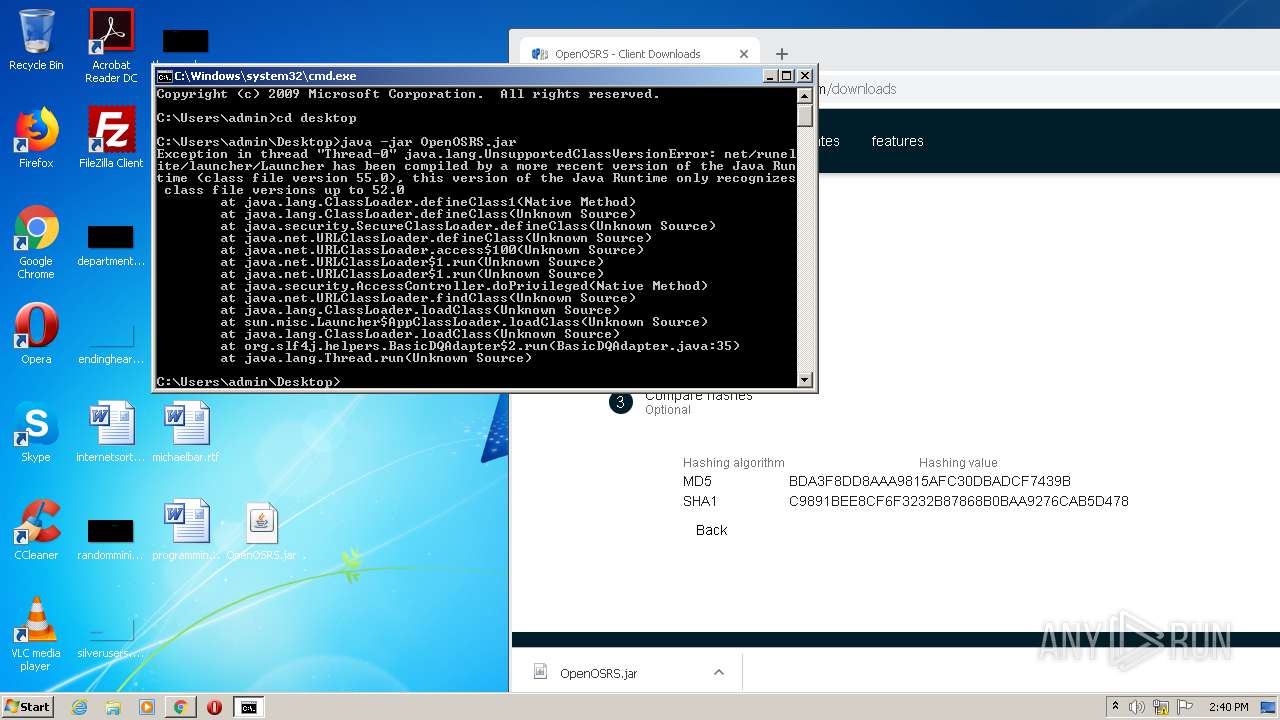
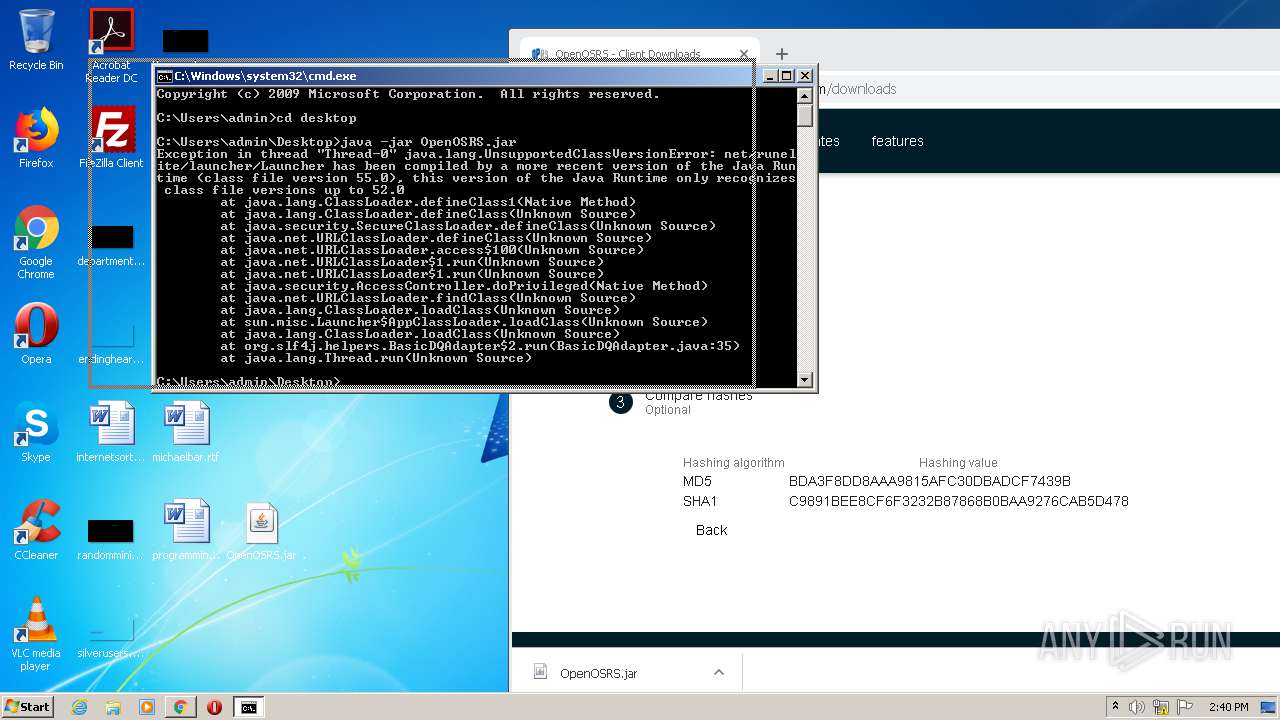
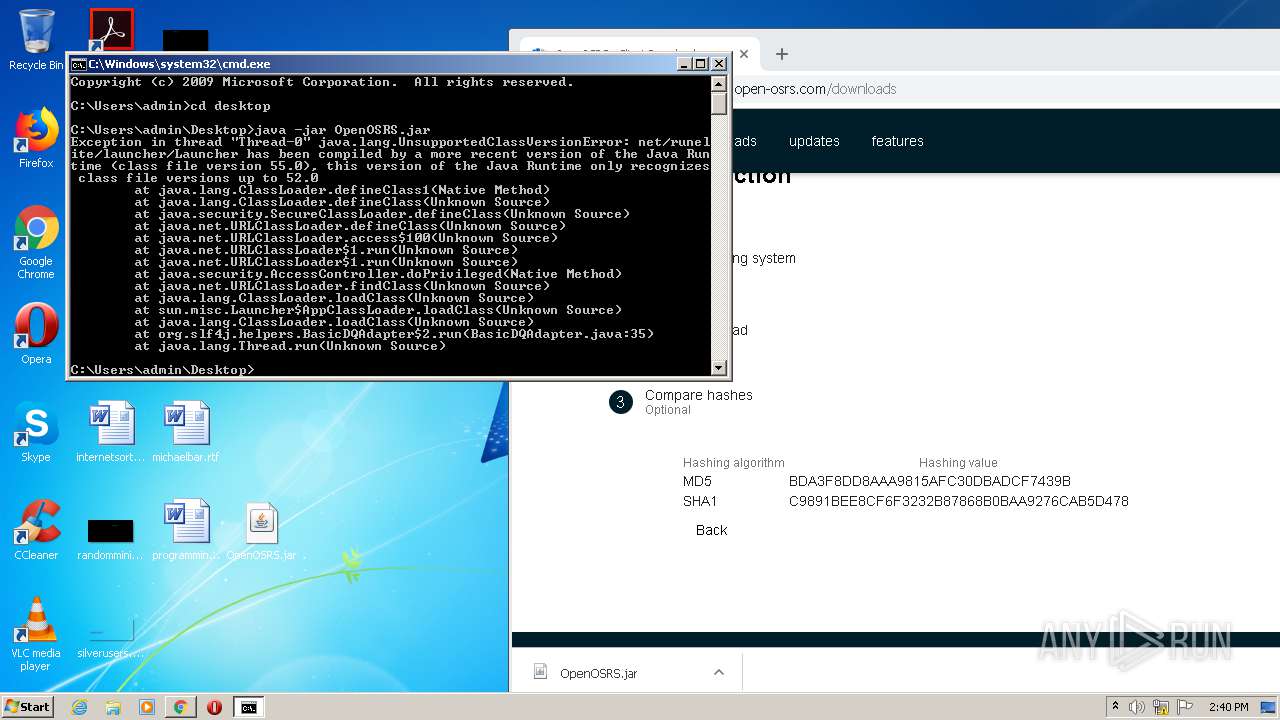
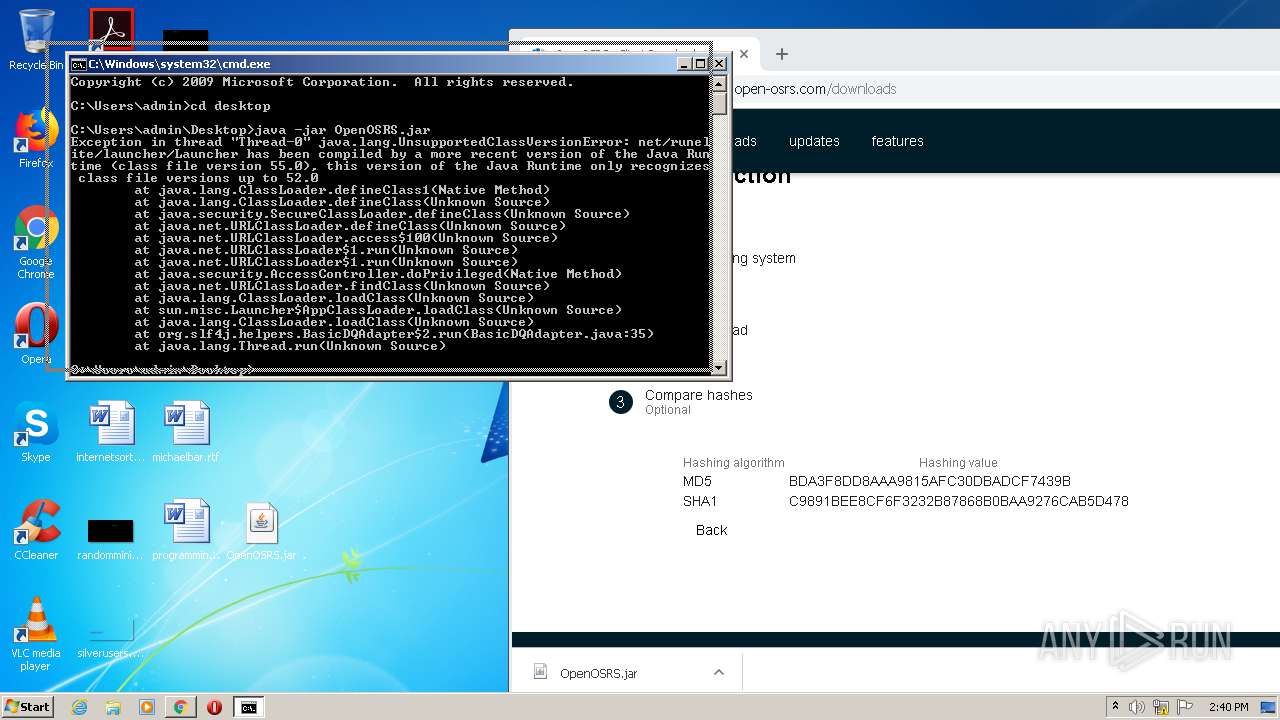
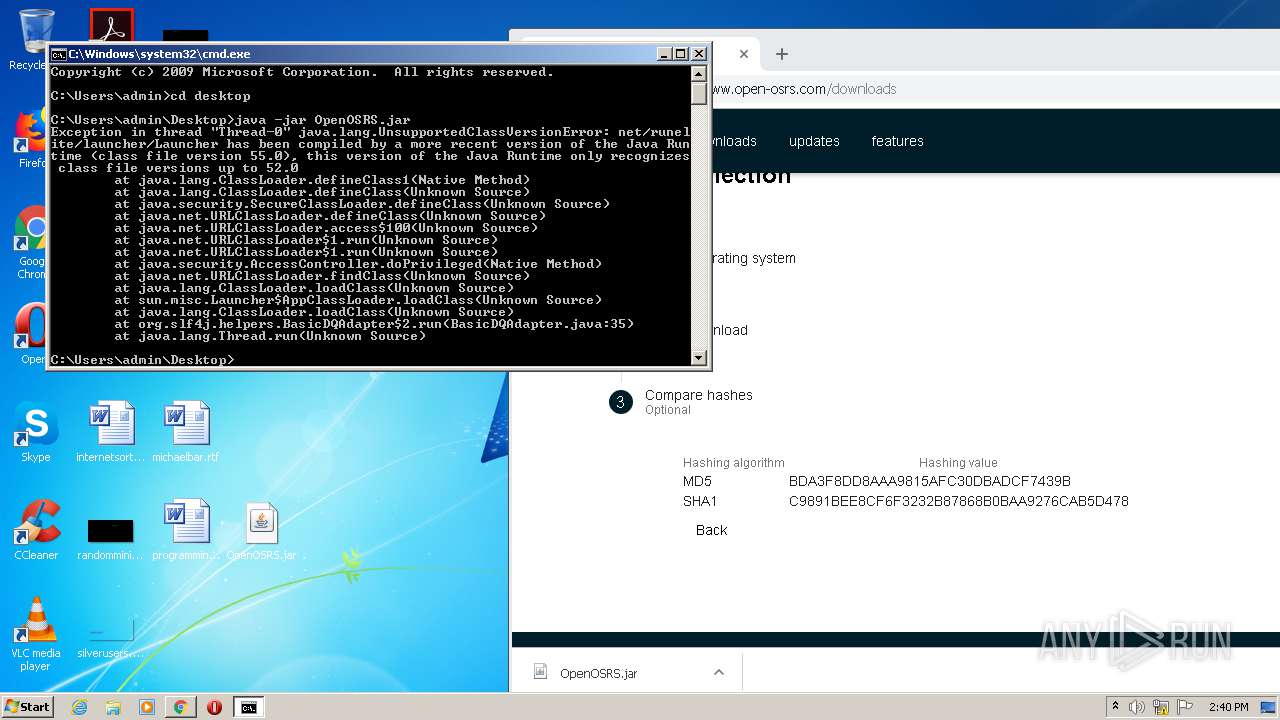
Manual execution by user
- cmd.exe (PID: 3004)
- chrome.exe (PID: 3428)
- explorer.exe (PID: 1272)
Application launched itself
- chrome.exe (PID: 3428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:05:20 15:03:22 |
| ZipCRC: | 0x1d5a56c9 |
| ZipCompressedSize: | 84 |
| ZipUncompressedSize: | 86 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
74
Monitored processes
27
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,12186656279458529056,3771201382003576198,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13652942303236533253 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,12186656279458529056,3771201382003576198,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2450024950003047459 --mojo-platform-channel-handle=3604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1272 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1452 | java -jar OpenOSRS.jar | C:\ProgramData\Oracle\Java\javapath\java.exe | cmd.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1516 | java -jar C:\Users\admin\AppData\Roaming\Opera\java.jar | C:\ProgramData\Oracle\Java\javapath\java.exe | java.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,12186656279458529056,3771201382003576198,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11934199311837590812 --mojo-platform-channel-handle=2788 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6e3da9d0,0x6e3da9e0,0x6e3da9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2296 | REG ADD HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run /V java /t REG_SZ /F /D C:\Users\admin\AppData\Roaming\WinRAR\java.jar | C:\Windows\system32\REG.exe | java.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,12186656279458529056,3771201382003576198,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8388745935434101942 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,12186656279458529056,3771201382003576198,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5232154566753578427 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 221
Read events
1 100
Write events
116
Delete events
5
Modification events
| (PID) Process: | (2296) REG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | java |
Value: C:\Users\admin\AppData\Roaming\WinRAR\java.jar | |||
| (PID) Process: | (4068) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
| (PID) Process: | (3644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3428-13241367546375000 |
Value: 259 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3428) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
9
Suspicious files
50
Text files
99
Unknown types
5
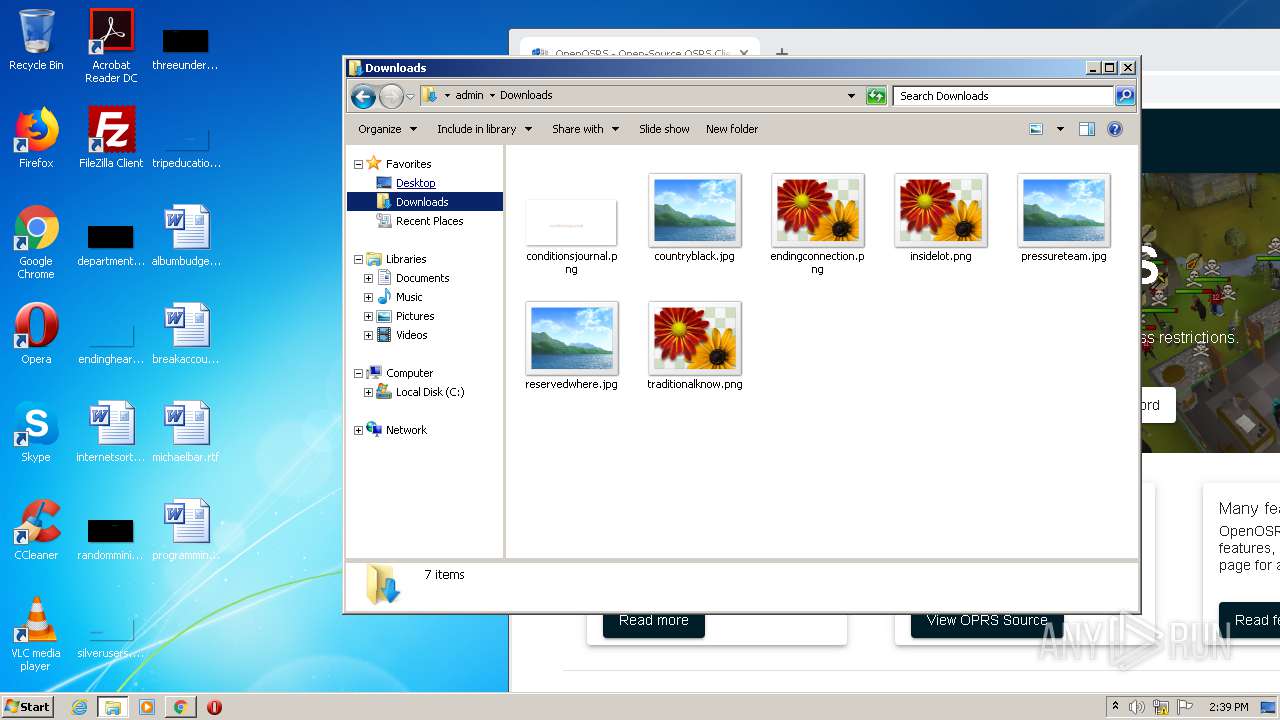
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b2855bbc-8a45-49fc-ba3a-01e3c0884837.tmp | — | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2760 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4068 | java.exe | C:\Users\admin\AppData\Local\Temp\jna-92668751\jna5892372797433873915.dll | executable | |
MD5:9268651539D1ECBEC9E6ED81AECED380 | SHA256:67059E9D04131CF85B41B881D214FC745D8E165859DADB7634114E7E96EB6E42 | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe179a.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
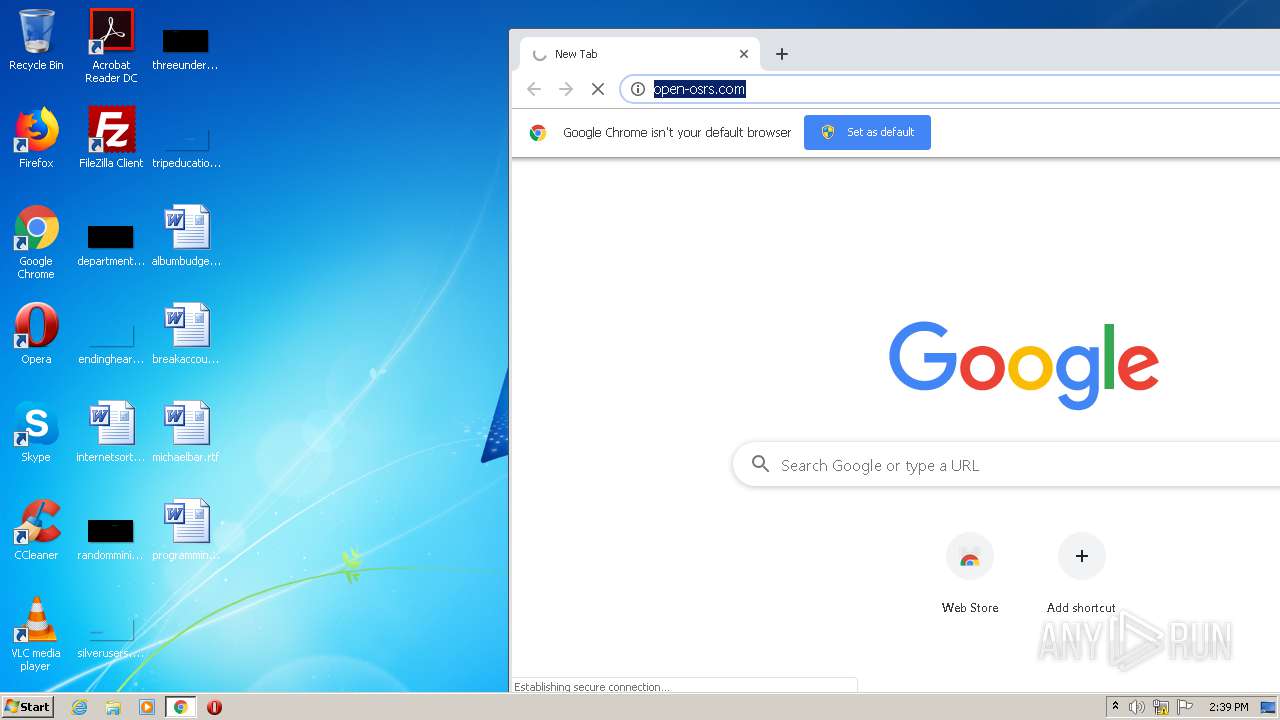
HTTP(S) requests
1
TCP/UDP connections
65
DNS requests
22
Threats
1
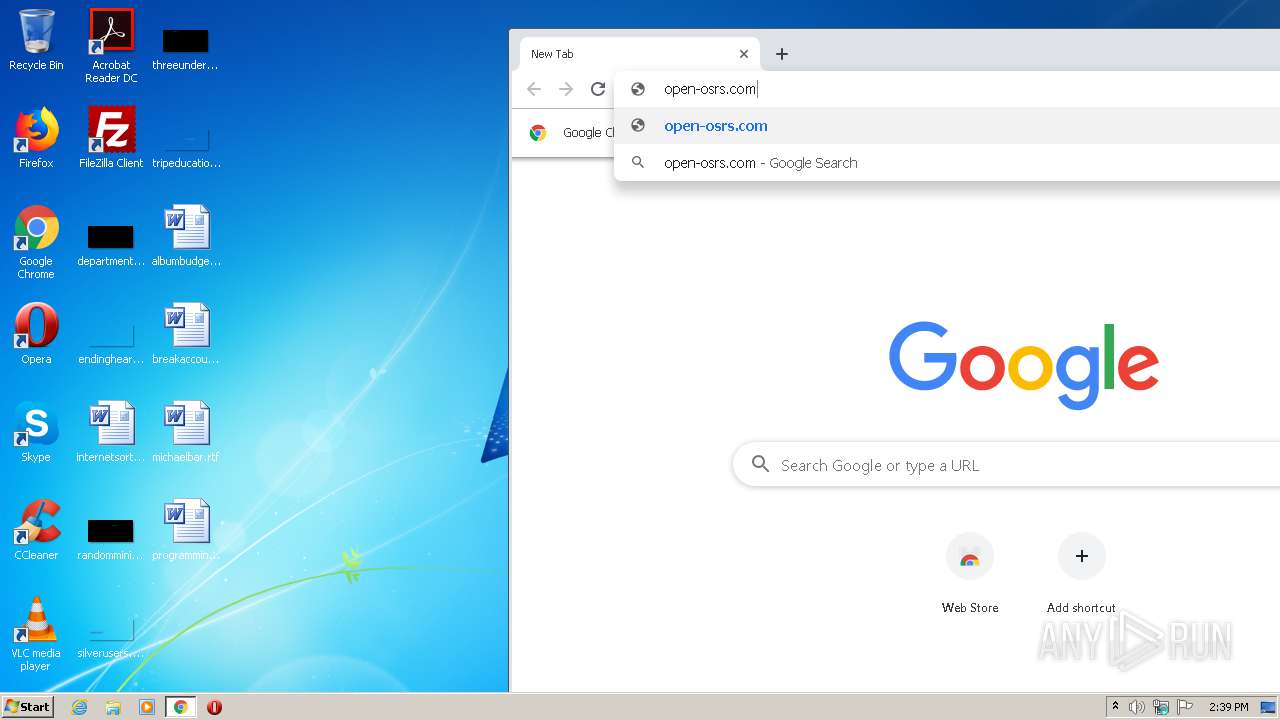
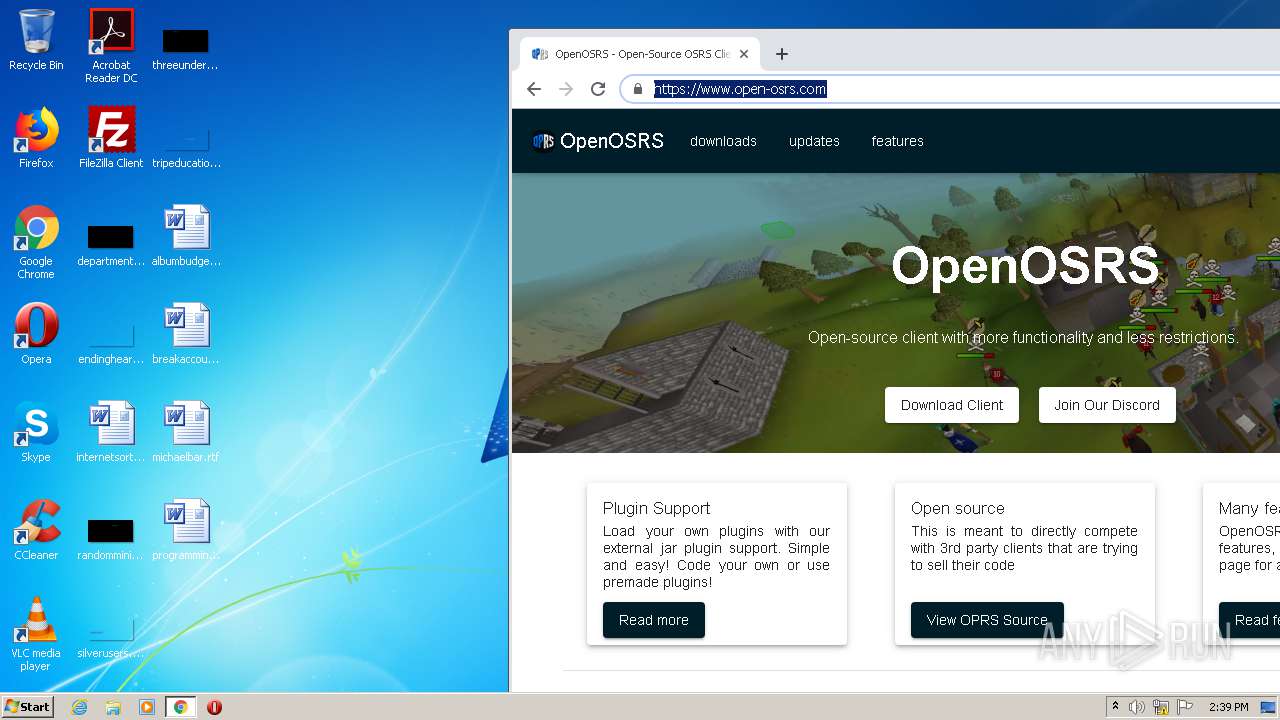
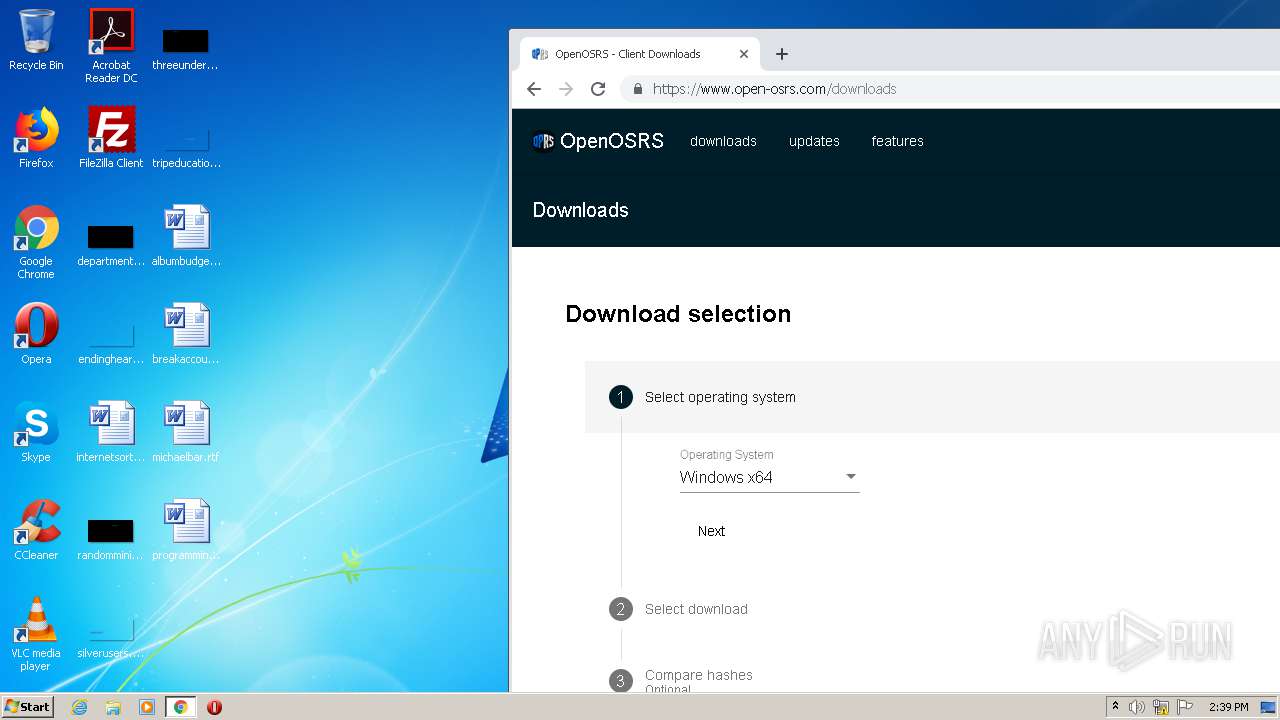
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
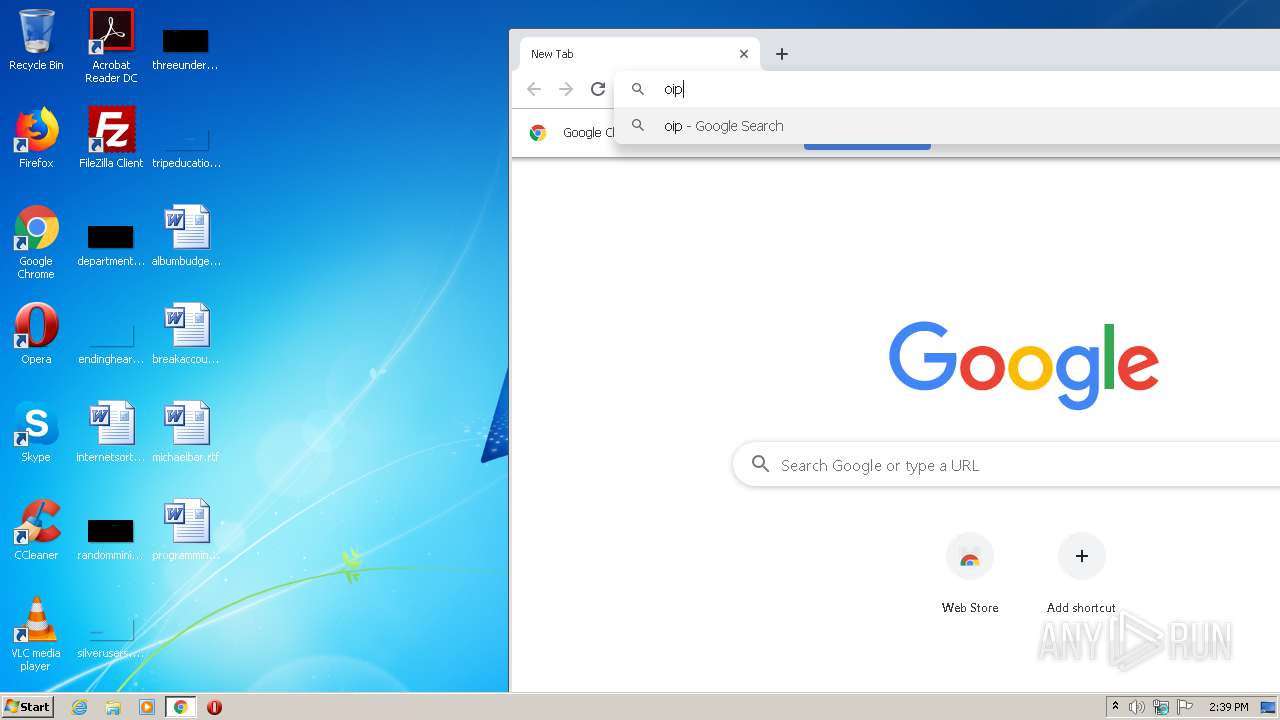
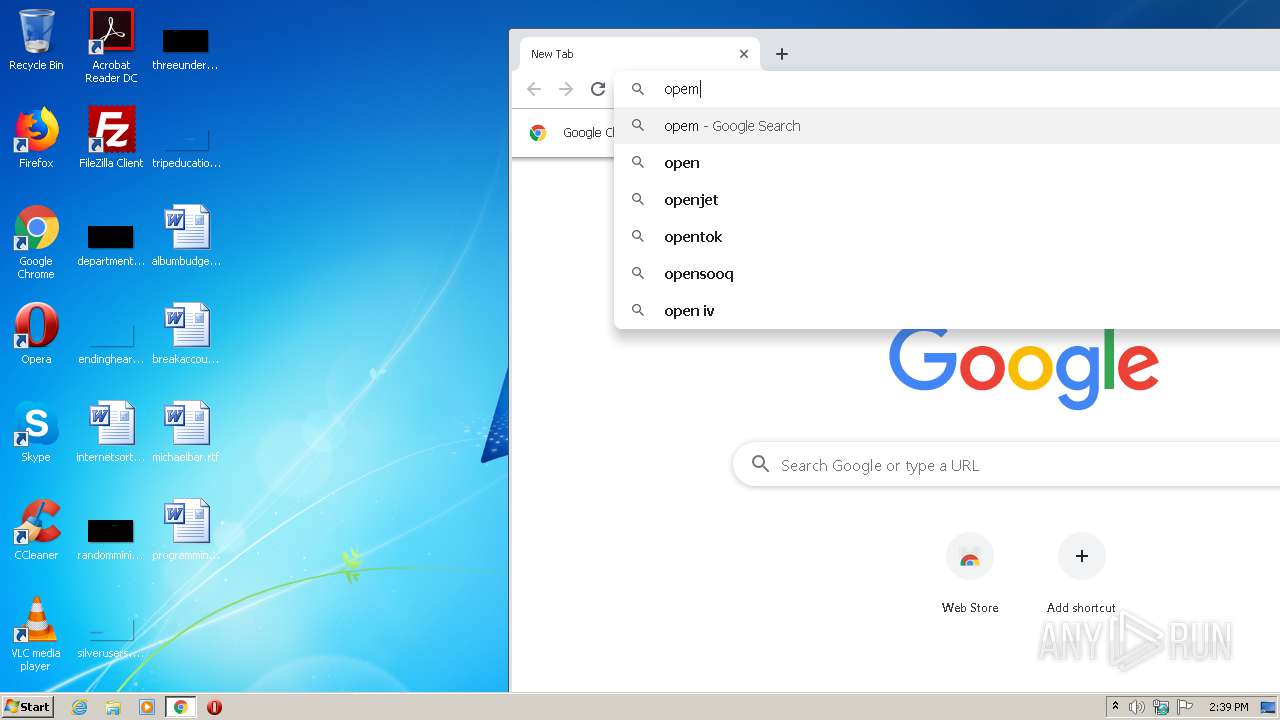
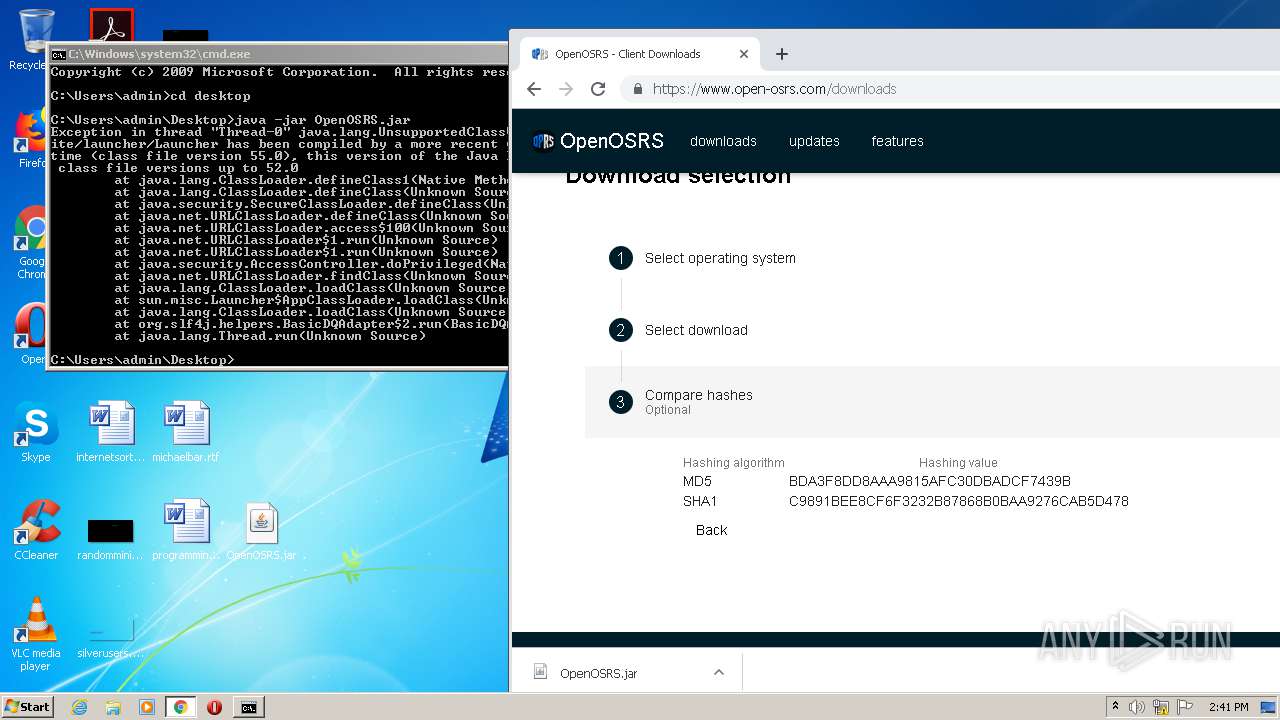
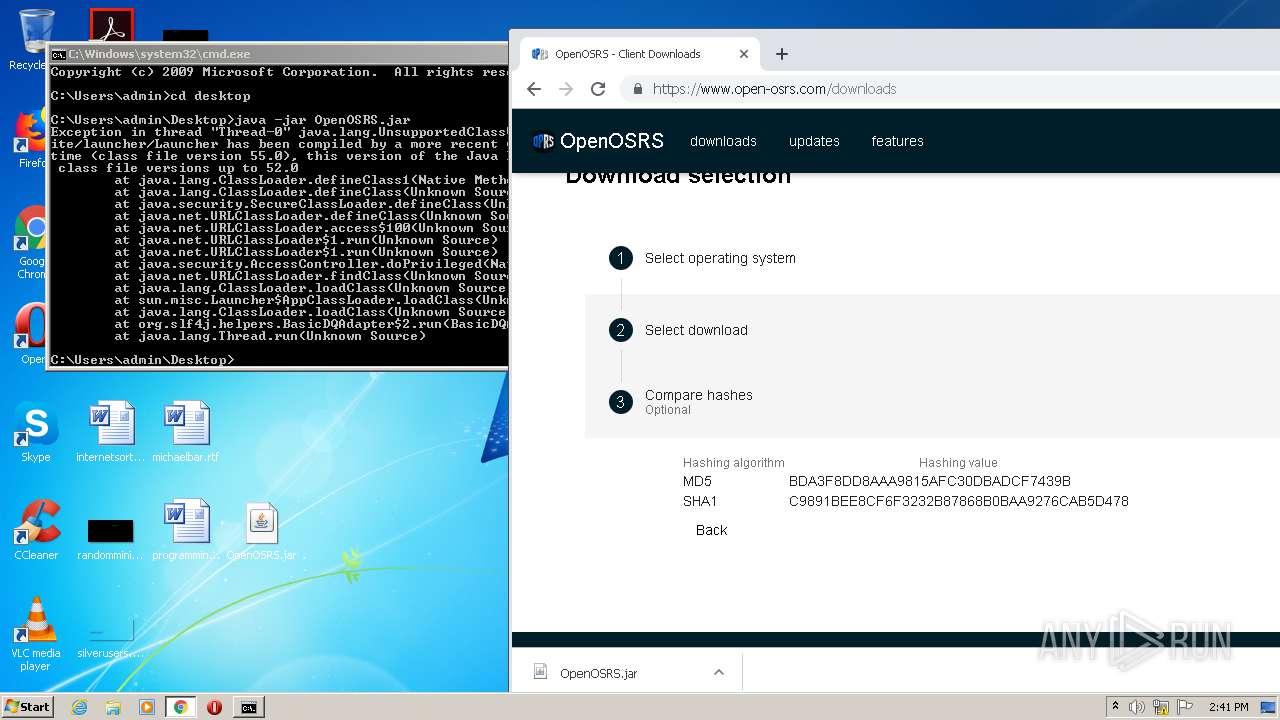
3608 | chrome.exe | GET | 302 | 198.187.31.49:80 | http://open-osrs.com/ | US | html | 210 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
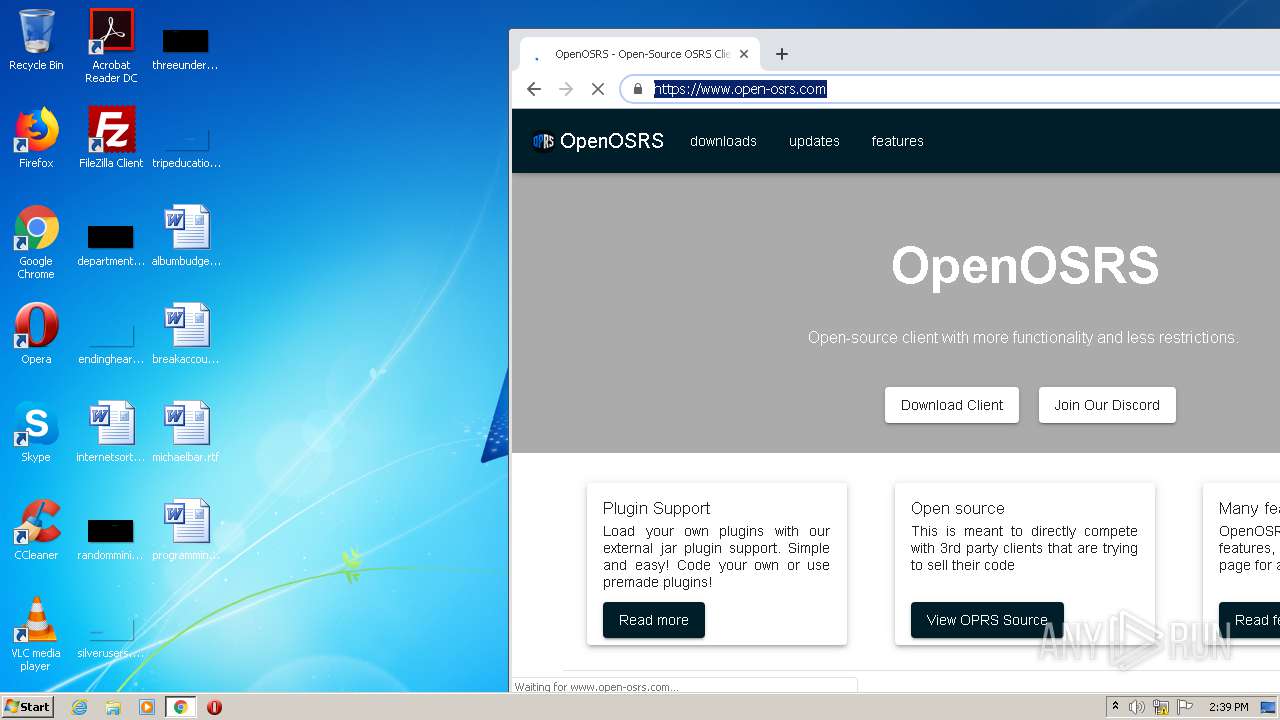
2760 | javaw.exe | 198.187.31.49:443 | open-osrs.com | Namecheap, Inc. | US | suspicious |
3608 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 198.187.31.49:80 | open-osrs.com | Namecheap, Inc. | US | suspicious |
3608 | chrome.exe | 216.58.212.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3608 | chrome.exe | 198.187.31.49:80 | open-osrs.com | Namecheap, Inc. | US | suspicious |
3608 | chrome.exe | 198.187.31.49:443 | open-osrs.com | Namecheap, Inc. | US | suspicious |
4068 | java.exe | 185.224.137.108:443 | rspshosting.site | — | — | malicious |
— | — | 185.224.137.108:443 | rspshosting.site | — | — | malicious |
3608 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3608 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
open-osrs.com |
| suspicious |
rspshosting.site |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3608 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |