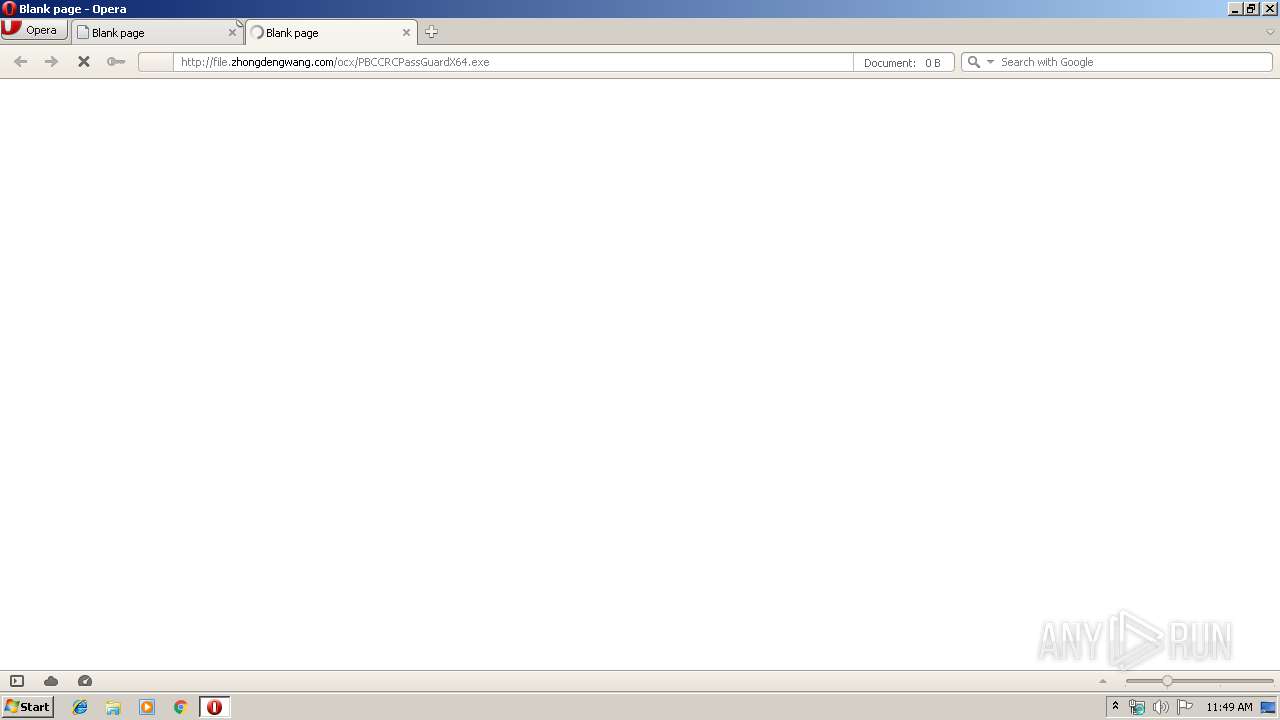
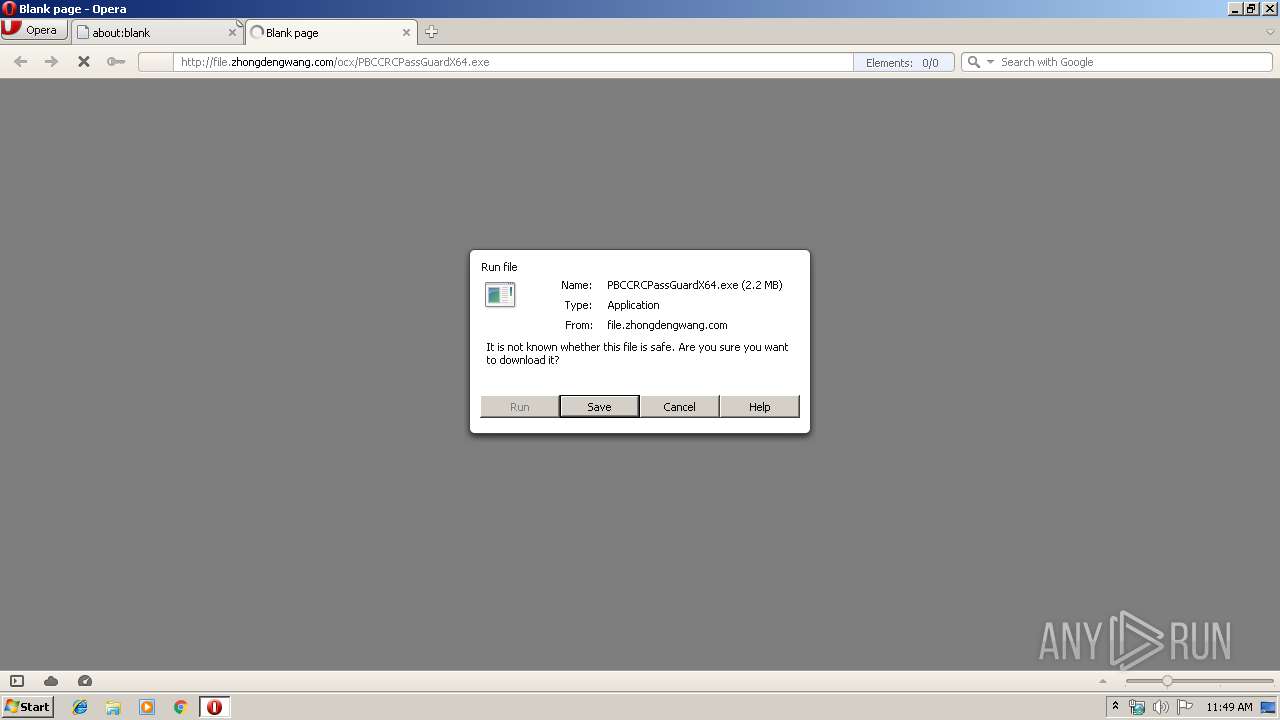
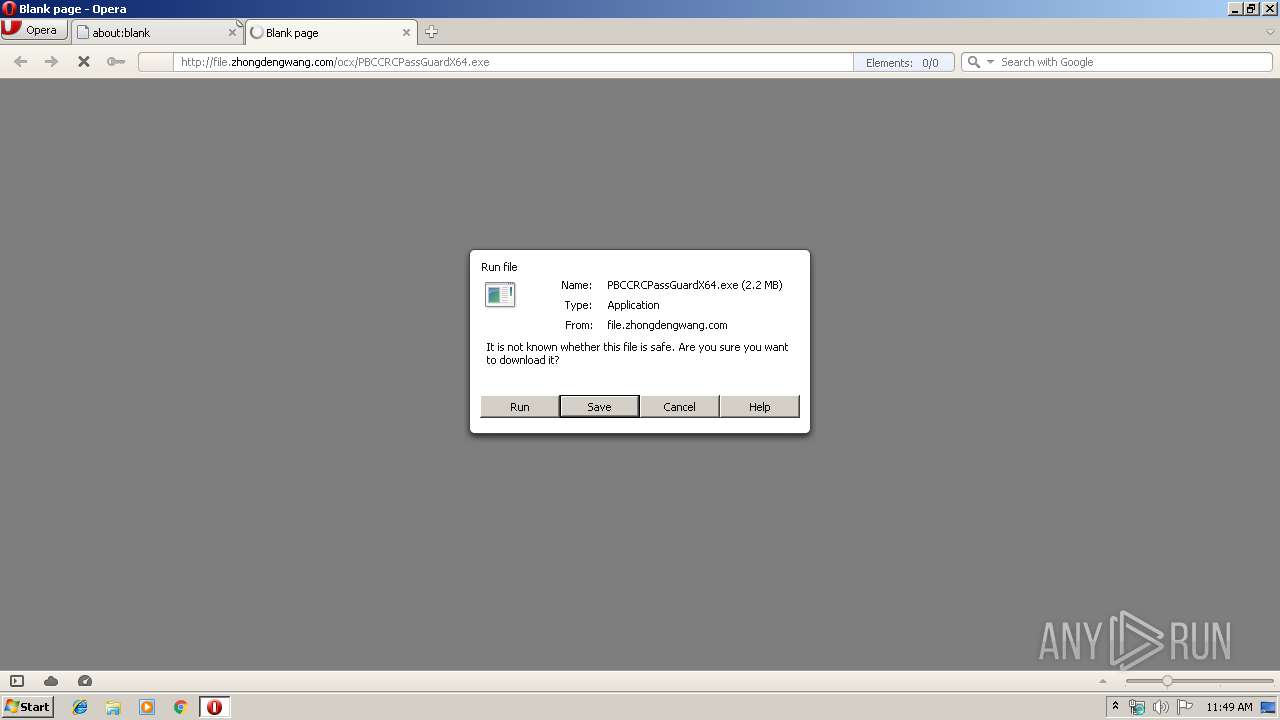
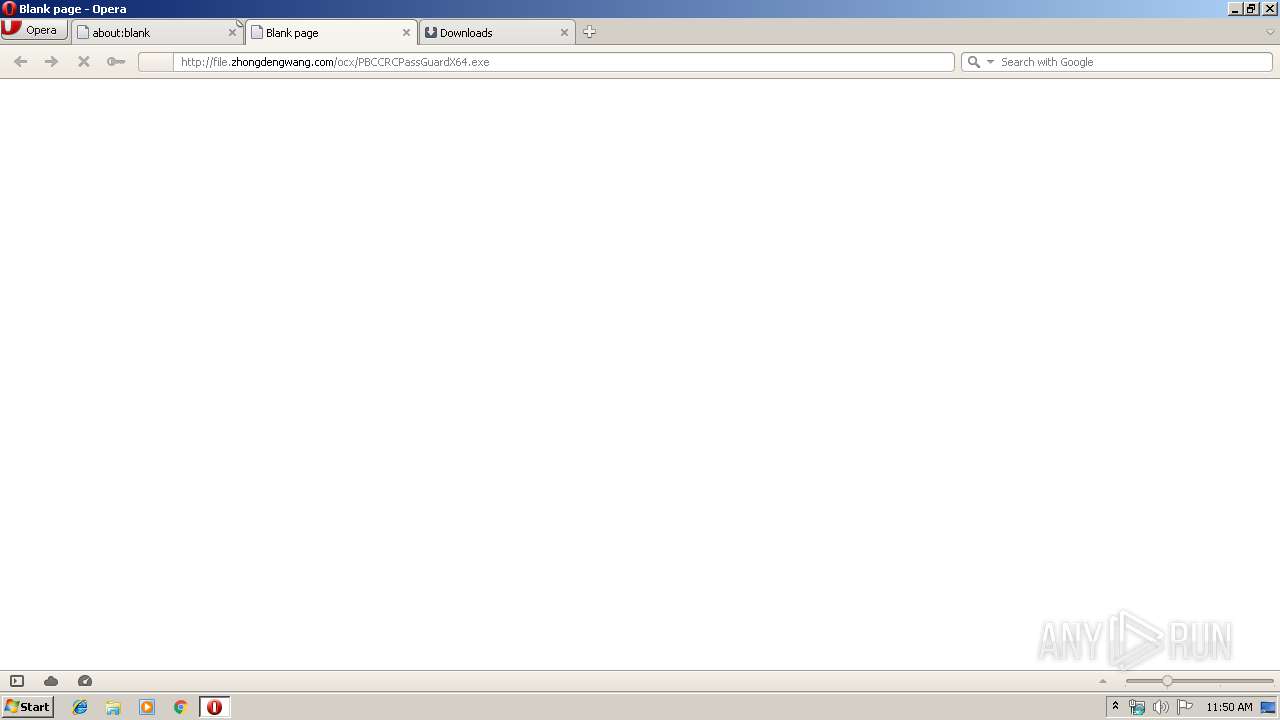
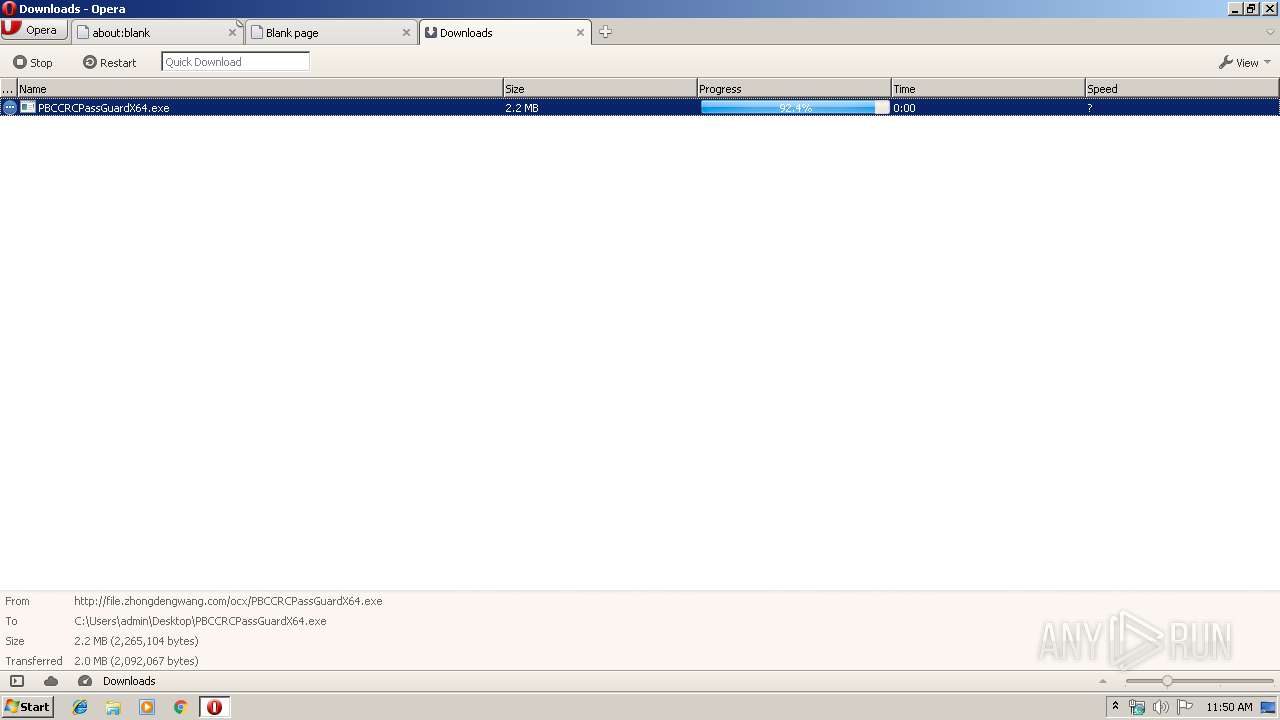
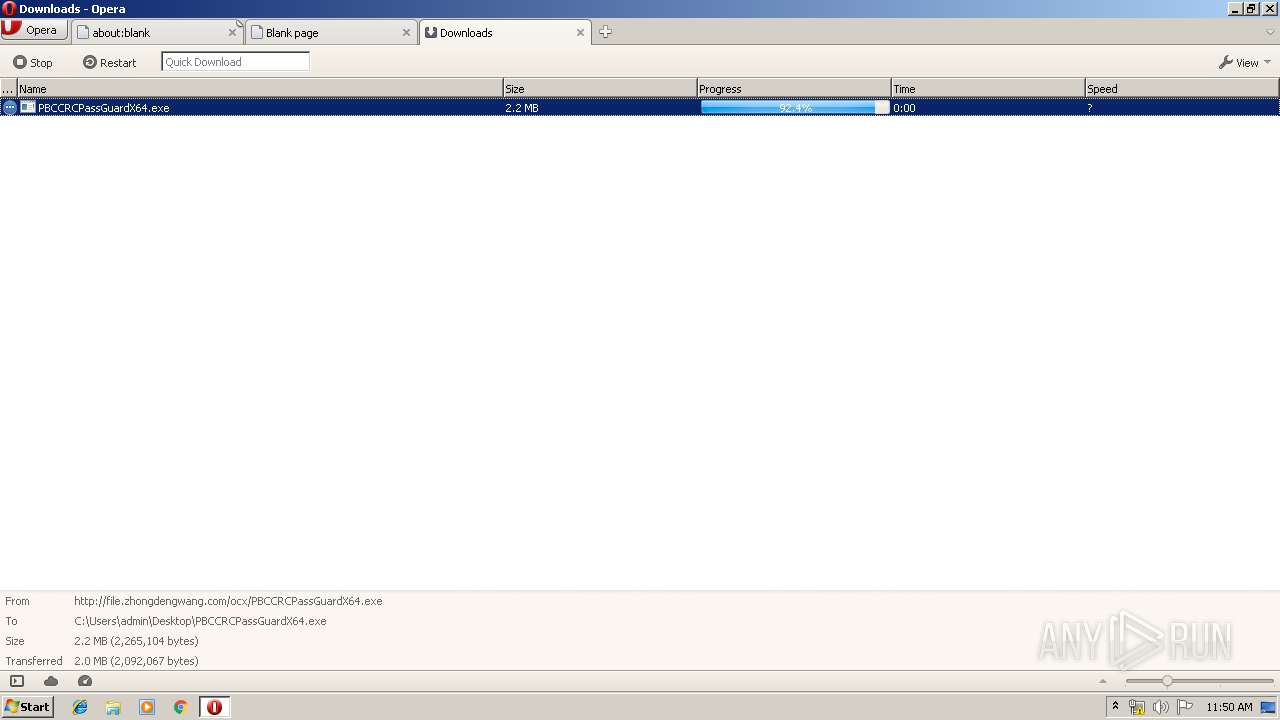
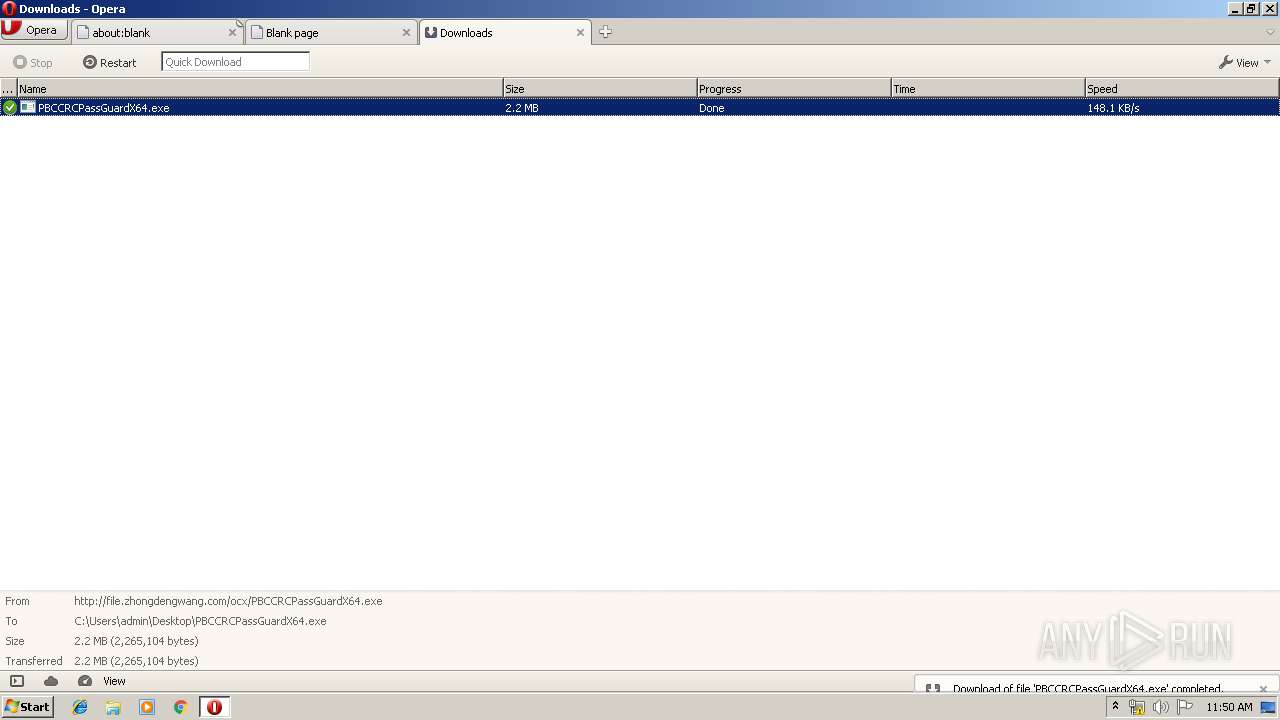
| URL: | http://file.zhongdengwang.com/ocx/PBCCRCPassGuardX64.exe |
| Full analysis: | https://app.any.run/tasks/7ec201a5-2a53-4db1-bfb8-a36c93494819 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 10:49:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F9FE8593843480C76F2217D6CADC0B46 |
| SHA1: | BBE4917D061C67210181B200E333795BC3866648 |
| SHA256: | CA612755296899D557294CA0DD9E417A1911816DBCFBB2E8AB83E06560D3A123 |
| SSDEEP: | 3:N1KYL8RddIRGdKtR32J9TtN:CYgjsKKt4v |
MALICIOUS
Loads dropped or rewritten executable
- PBCCRCPassGuardX64.exe (PID: 2312)
Application was dropped or rewritten from another process
- PBCCRCPassGuardX64.exe (PID: 2312)
- PBCCRCPassGuardX64.exe (PID: 3548)
SUSPICIOUS
Executable content was dropped or overwritten
- PBCCRCPassGuardX64.exe (PID: 2312)
- opera.exe (PID: 3496)
INFO
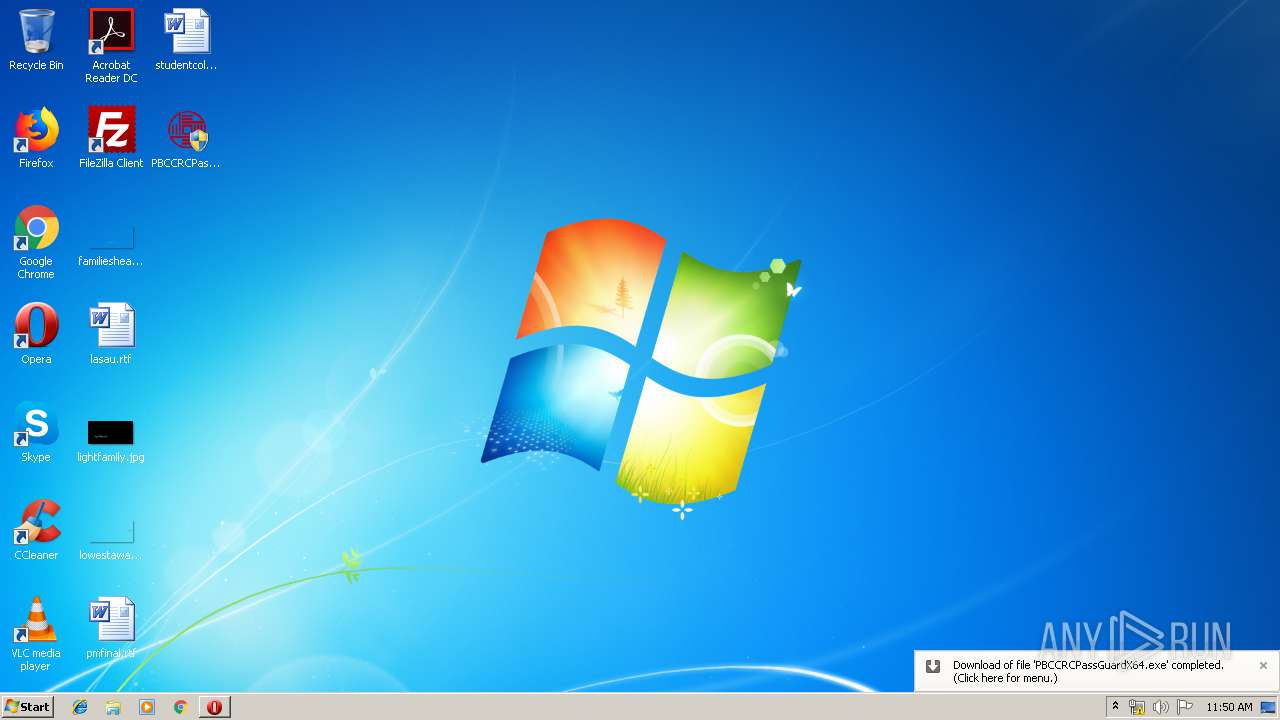
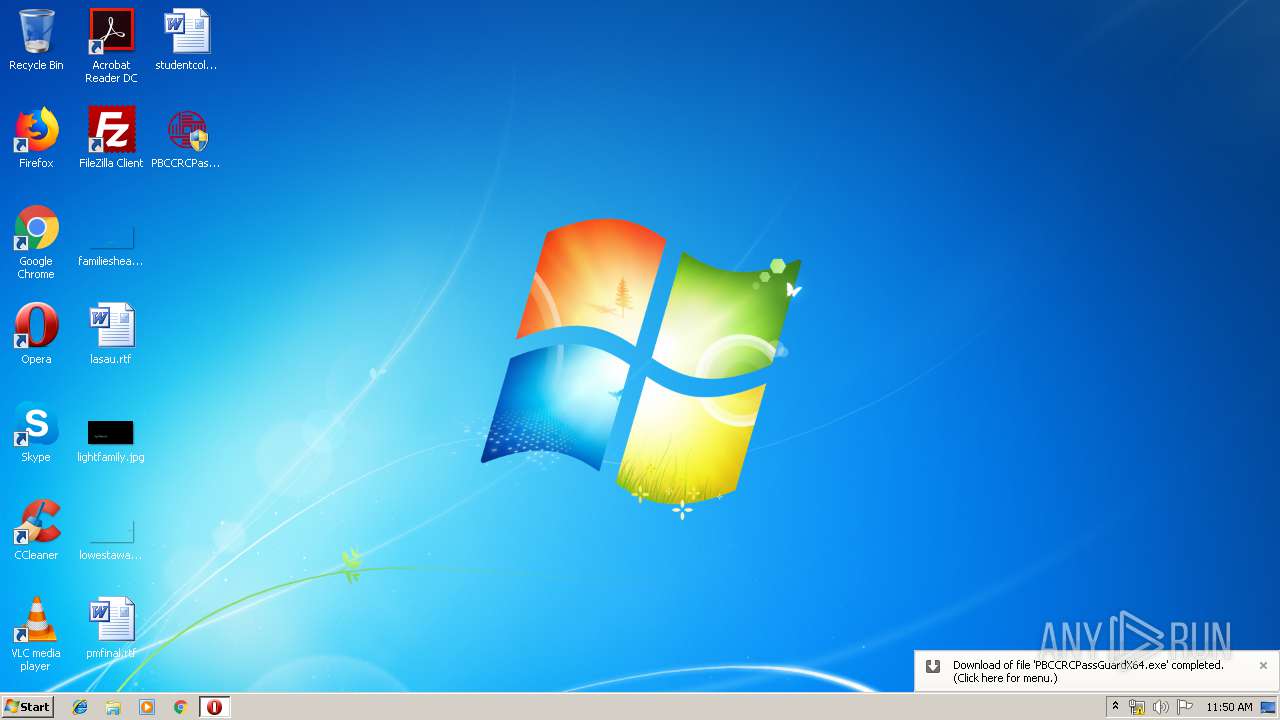
Manual execution by user
- PBCCRCPassGuardX64.exe (PID: 3548)
- PBCCRCPassGuardX64.exe (PID: 2312)
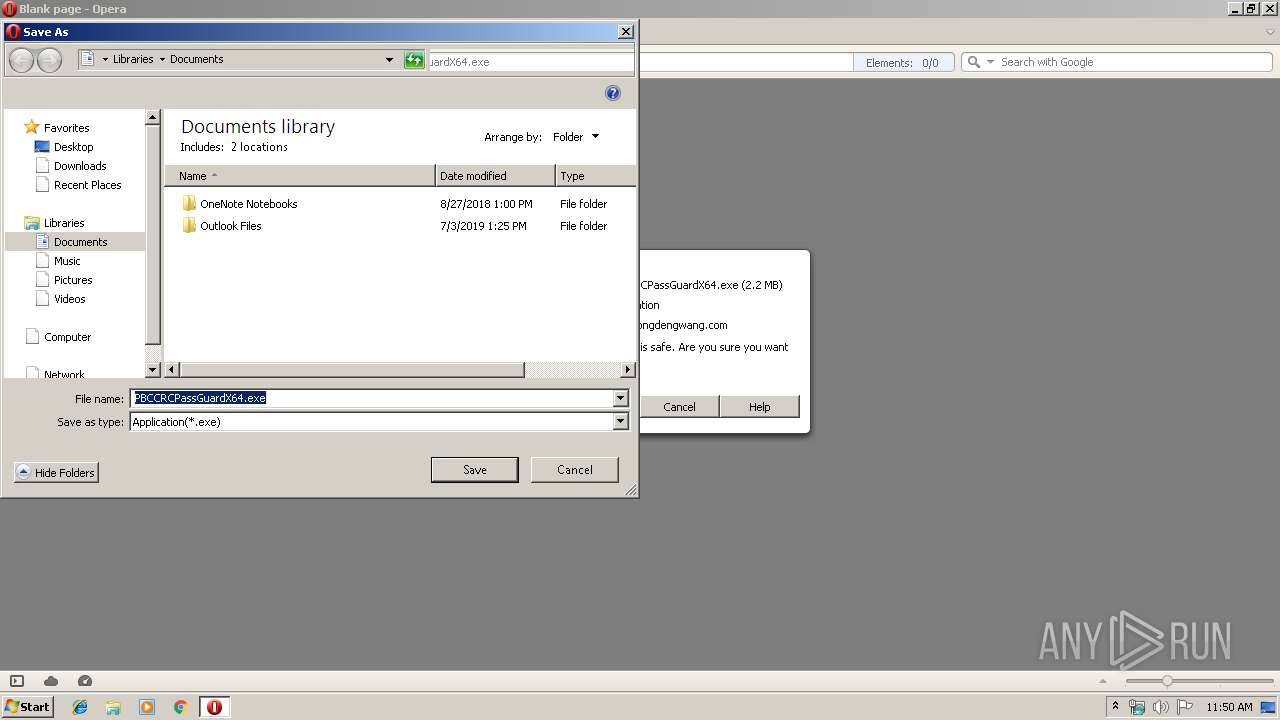
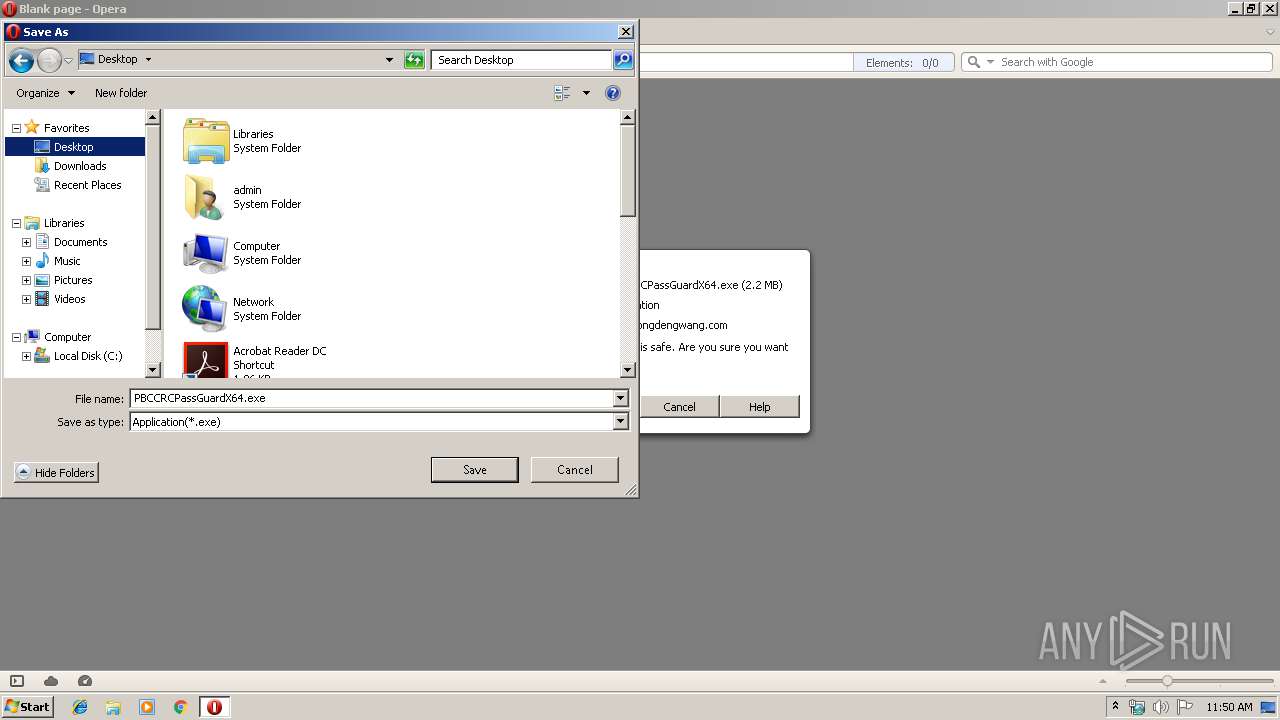
Creates files in the user directory
- opera.exe (PID: 3496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
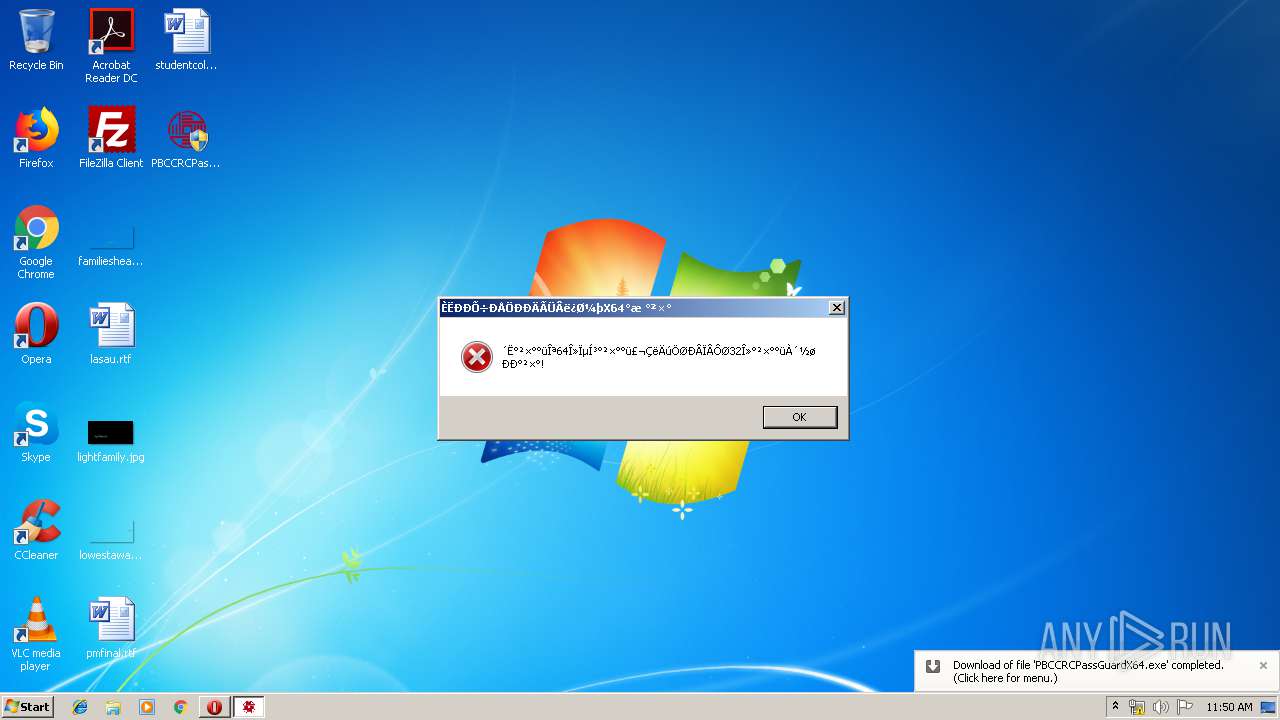
| 2312 | "C:\Users\admin\Desktop\PBCCRCPassGuardX64.exe" | C:\Users\admin\Desktop\PBCCRCPassGuardX64.exe | explorer.exe | ||||||||||||
User: admin Company: 中国人民银行征信中心 Integrity Level: HIGH Description: 人行征信中心密码控件 Exit code: 2 Version: 1.0.0.1 Modules
| |||||||||||||||
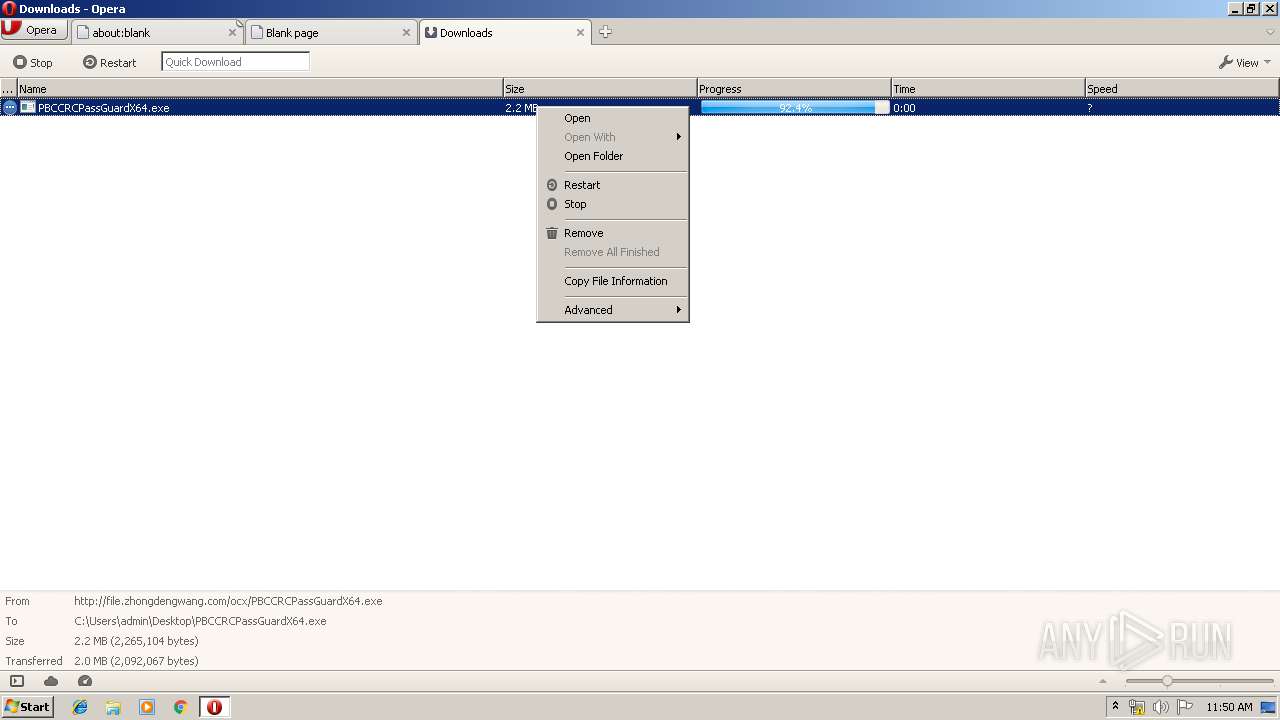
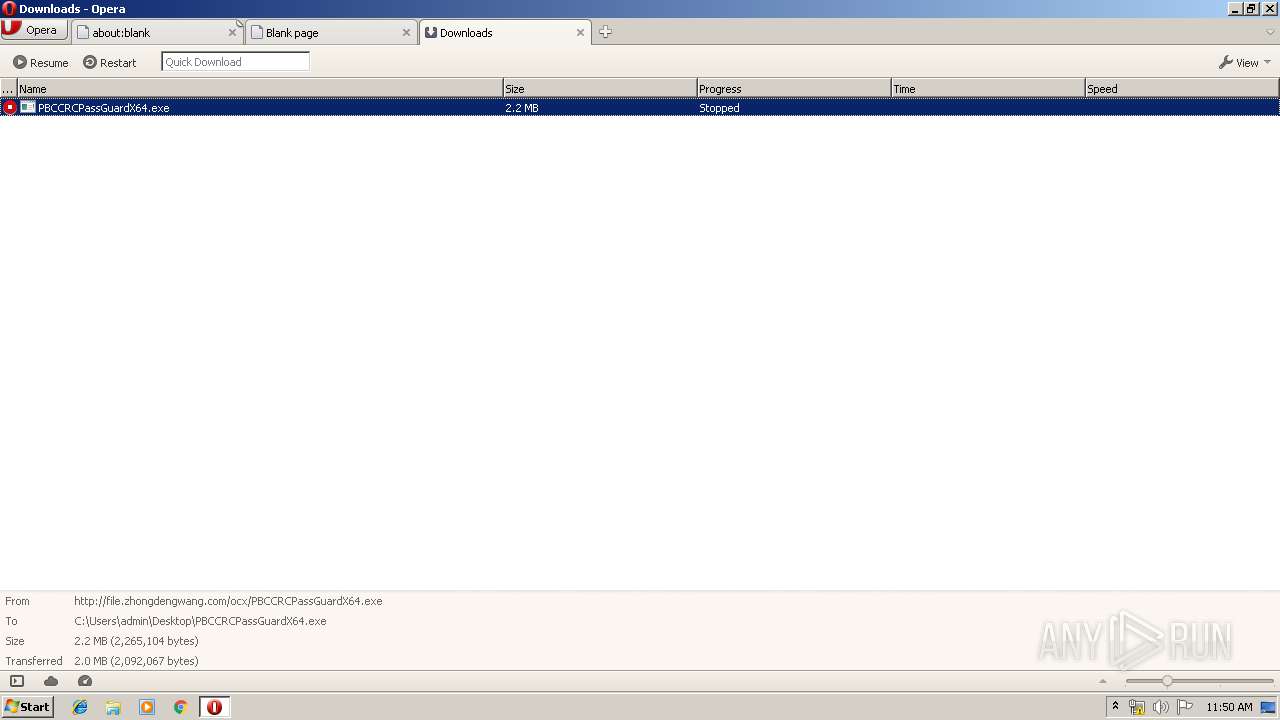
| 3496 | "C:\Program Files\Opera\opera.exe" "http://file.zhongdengwang.com/ocx/PBCCRCPassGuardX64.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3548 | "C:\Users\admin\Desktop\PBCCRCPassGuardX64.exe" | C:\Users\admin\Desktop\PBCCRCPassGuardX64.exe | — | explorer.exe | |||||||||||
User: admin Company: 中国人民银行征信中心 Integrity Level: MEDIUM Description: 人行征信中心密码控件 Exit code: 3221226540 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
701
Read events
578
Write events
121
Delete events
2
Modification events
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe "http://file.zhongdengwang.com/ocx/PBCCRCPassGuardX64.exe" | |||
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000001000000000000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (3496) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: 1092616257 | |||
Executable files
5
Suspicious files
16
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3496 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprEF15.tmp | — | |
MD5:— | SHA256:— | |||
| 3496 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprEF25.tmp | — | |
MD5:— | SHA256:— | |||
| 3496 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprEF55.tmp | — | |
MD5:— | SHA256:— | |||
| 3496 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\55D157NBZA37D1KWXNHJ.temp | — | |
MD5:— | SHA256:— | |||
| 3496 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00002.tmp | — | |
MD5:— | SHA256:— | |||
| 3496 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 3496 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 3496 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RF10fabd.TMP | binary | |
MD5:— | SHA256:— | |||
| 3496 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3496 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3496 | opera.exe | GET | — | 113.142.73.75:80 | http://file.zhongdengwang.com/ocx/PBCCRCPassGuardX64.exe | CN | — | — | suspicious |
3496 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
3496 | opera.exe | GET | 206 | 113.142.73.75:80 | http://file.zhongdengwang.com/ocx/PBCCRCPassGuardX64.exe | CN | binary | 168 Kb | suspicious |
3496 | opera.exe | GET | 400 | 185.26.182.94:80 | http://sitecheck2.opera.com/?host=file.zhongdengwang.com&hdn=bXE2BqWpBn/bQgYf99VCNw== | unknown | html | 150 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3496 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3496 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3496 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3496 | opera.exe | 113.142.73.75:80 | file.zhongdengwang.com | China Telecom (Group) | CN | suspicious |
3496 | opera.exe | 185.26.182.94:80 | certs.opera.com | Opera Software AS | — | whitelisted |
— | — | 113.142.73.75:80 | file.zhongdengwang.com | China Telecom (Group) | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
file.zhongdengwang.com |
| suspicious |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3496 | opera.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |