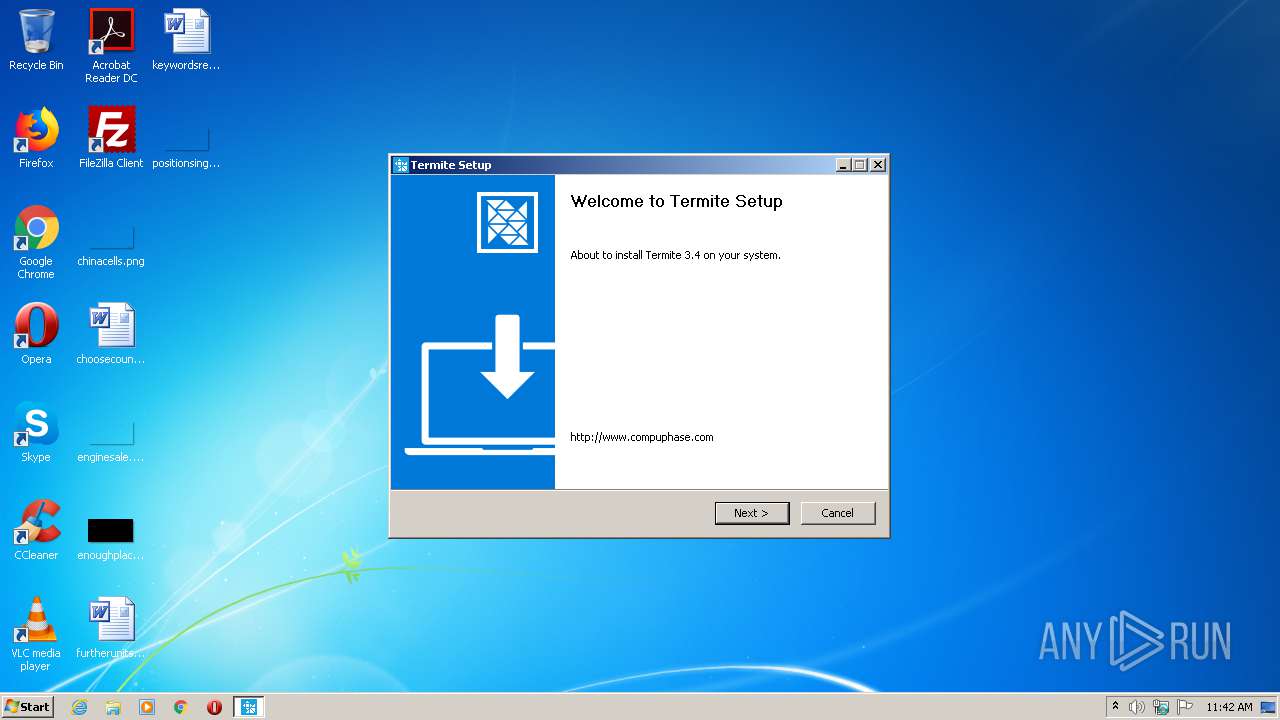
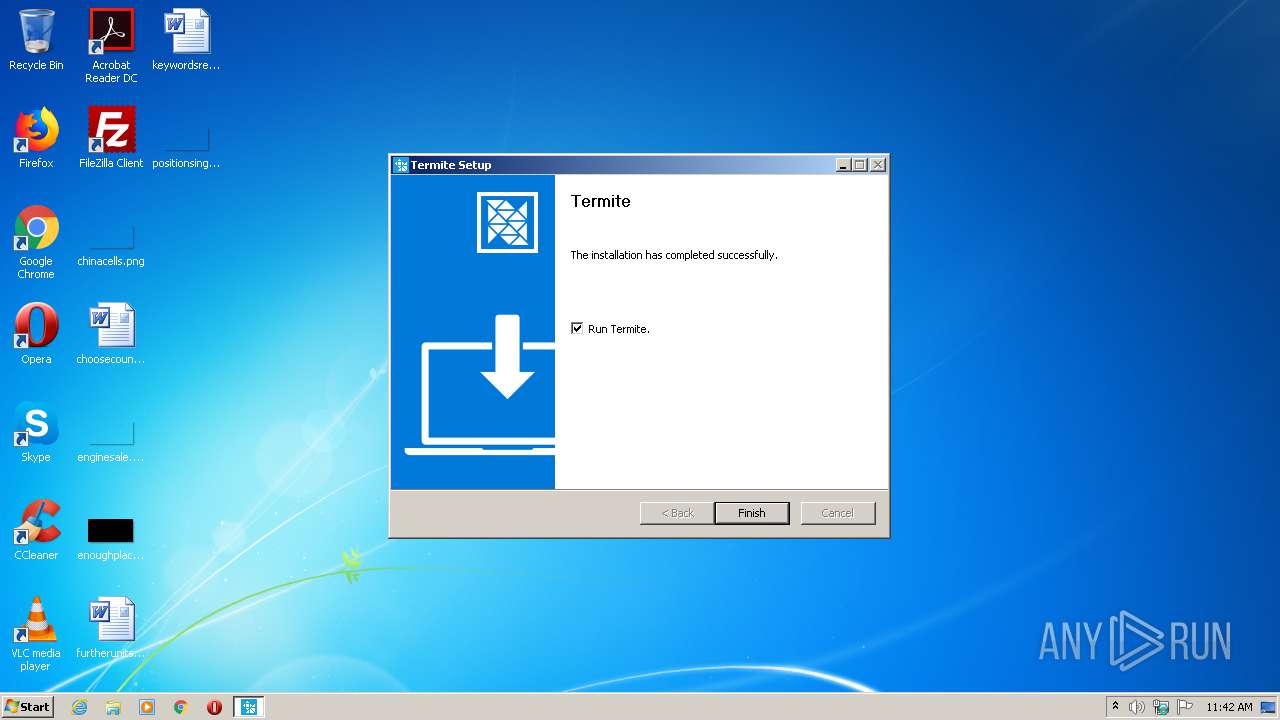
| File name: | termite-3.4.exe |
| Full analysis: | https://app.any.run/tasks/cce96568-c536-4d0e-af02-fc593d84a70e |
| Verdict: | Malicious activity |
| Analysis date: | July 20, 2020, 10:42:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 86F615A0D2D14733BF1463CBDB5E2E2E |
| SHA1: | 374F6E57E767C60ECB1F9FCA70C5344154332293 |
| SHA256: | CA440B6C7F6EAA812BA5F8BF42AED86E02022CA50A1C72585168C9B671D0FE19 |
| SSDEEP: | 6144:C1onZAbB4M77eDozYO00B2P/Jq7bWkS65N4V8KHuaZ5VqksOE:uoZAt7iozYjbXk7bTSIw8KO2VqksOE |
MALICIOUS
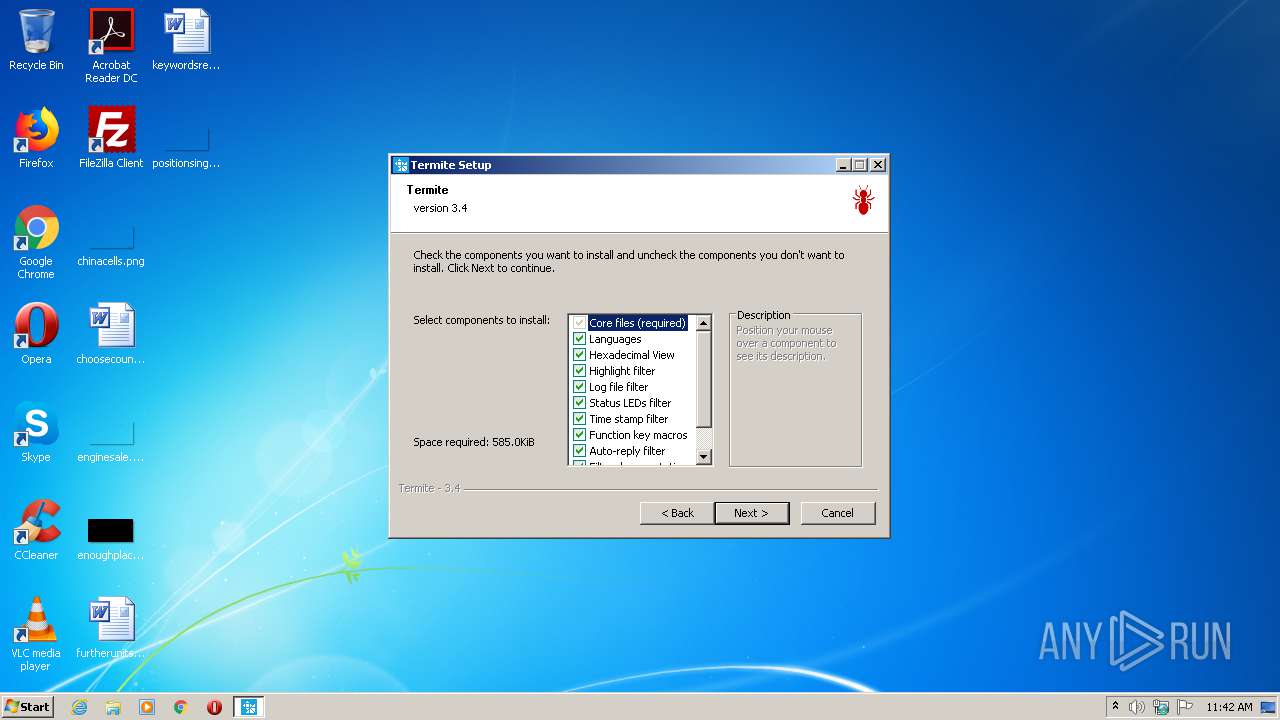
Loads dropped or rewritten executable
- Termite.exe (PID: 2568)
- termite-3.4.exe (PID: 2620)
Application was dropped or rewritten from another process
- Termite.exe (PID: 2568)
SUSPICIOUS
Executable content was dropped or overwritten
- termite-3.4.exe (PID: 2620)
Creates files in the user directory
- termite-3.4.exe (PID: 2620)
Creates a software uninstall entry
- termite-3.4.exe (PID: 2620)
Creates files in the program directory
- termite-3.4.exe (PID: 2620)
- Termite.exe (PID: 2568)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x32bf |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:45 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005E59 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42419 |
.rdata | 0x00007000 | 0x00001246 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0004 |
.data | 0x00009000 | 0x0001A818 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21193 |
.ndata | 0x00024000 | 0x00016000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x000045E0 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.68115 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.78498 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 3.03712 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 1.61802 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 2.17226 | 744 | UNKNOWN | English - United States | RT_ICON |
6 | 2.24703 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.79755 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70411 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
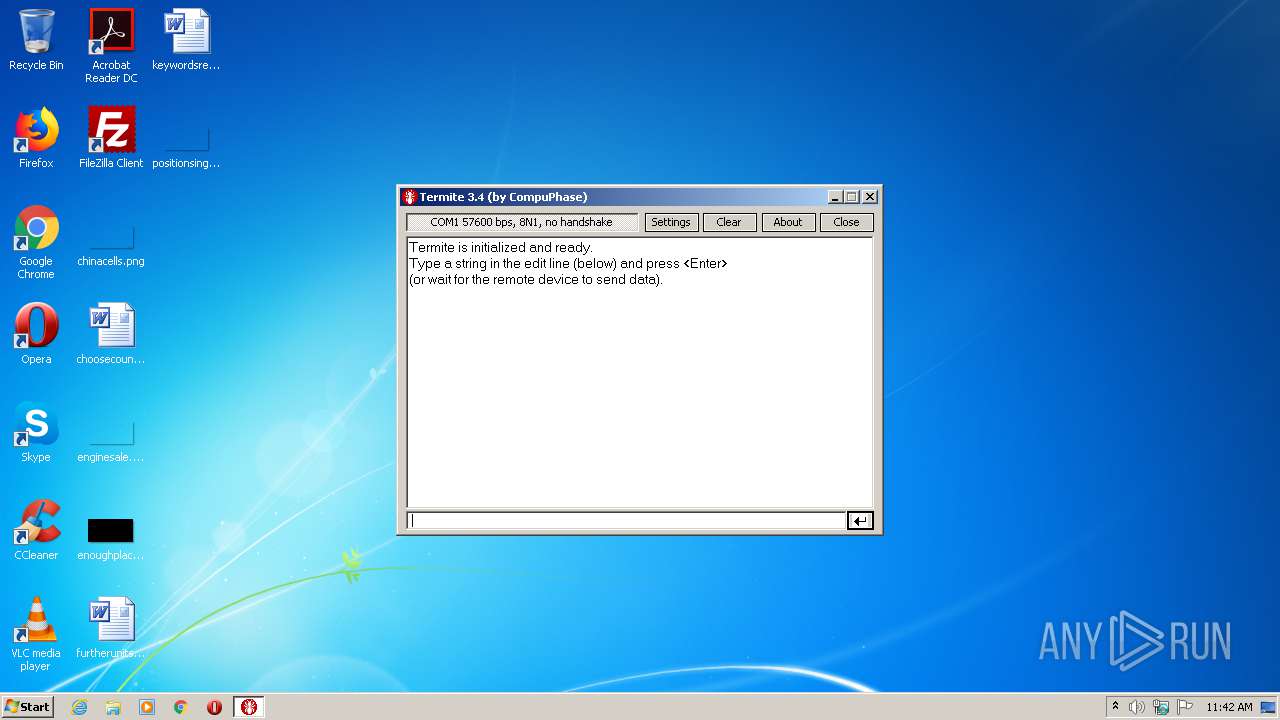
| 2288 | "C:\Users\admin\AppData\Local\Temp\termite-3.4.exe" | C:\Users\admin\AppData\Local\Temp\termite-3.4.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
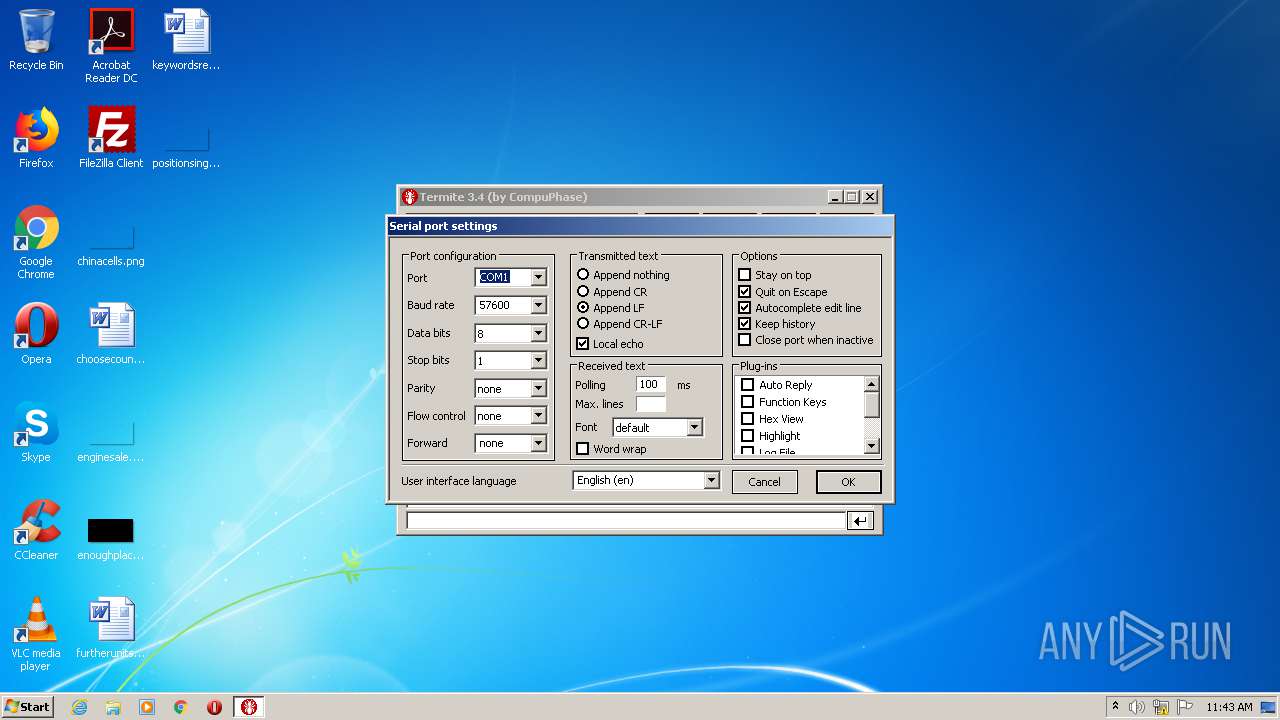
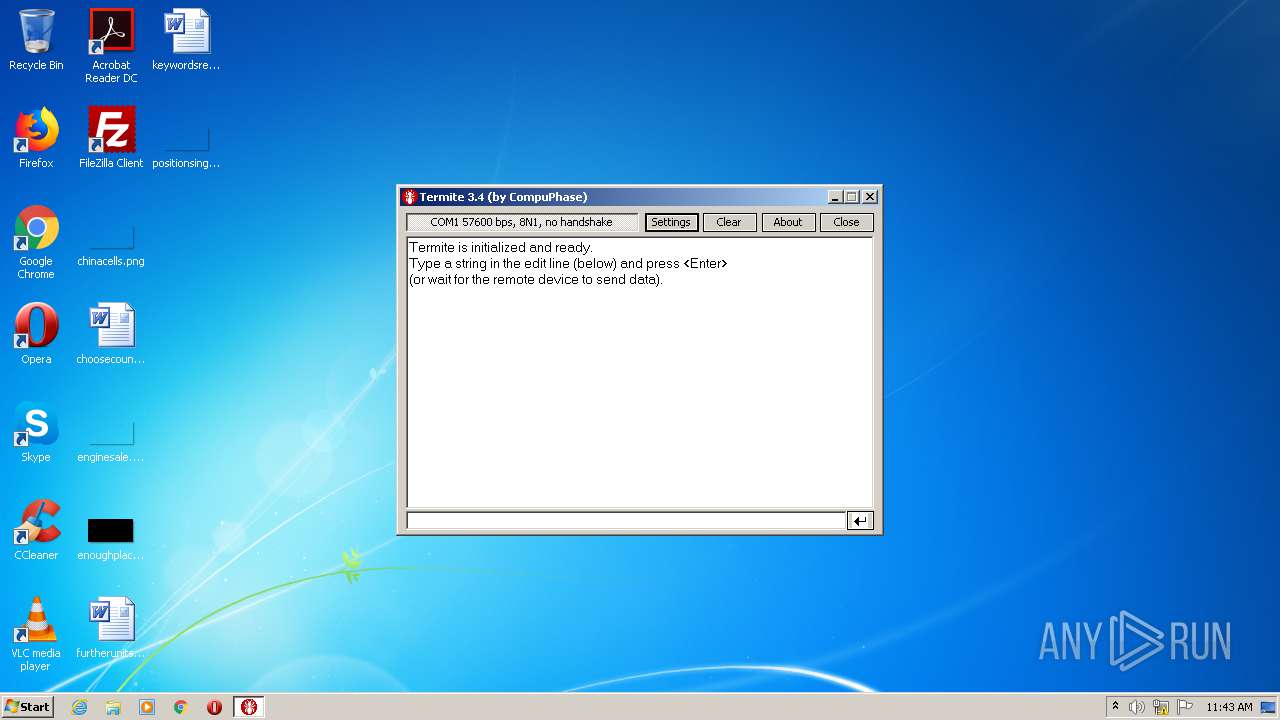
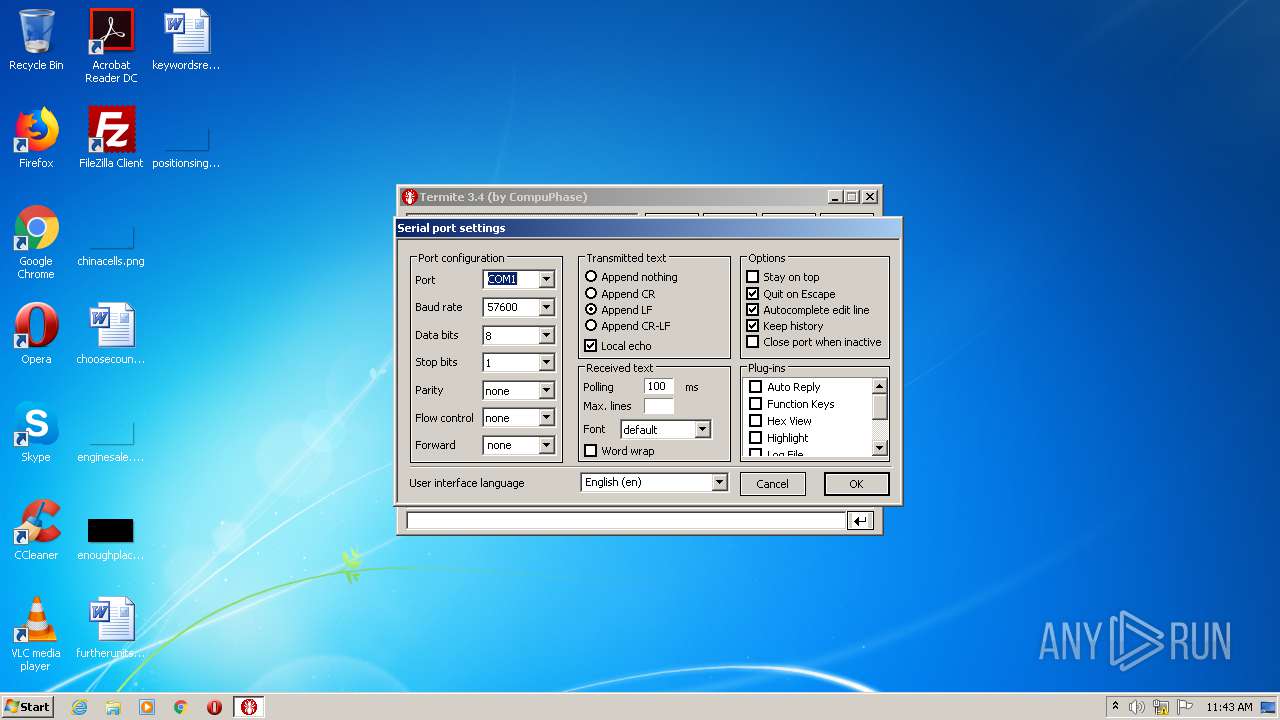
| 2568 | "C:\Program Files\Termite\Termite.exe" | C:\Program Files\Termite\Termite.exe | — | termite-3.4.exe | |||||||||||
User: admin Company: CompuPhase Integrity Level: HIGH Description: Termite RS232 terminal Exit code: 0 Version: 3.4.5809 Modules
| |||||||||||||||
| 2620 | "C:\Users\admin\AppData\Local\Temp\termite-3.4.exe" | C:\Users\admin\AppData\Local\Temp\termite-3.4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
349
Read events
338
Write events
11
Delete events
0
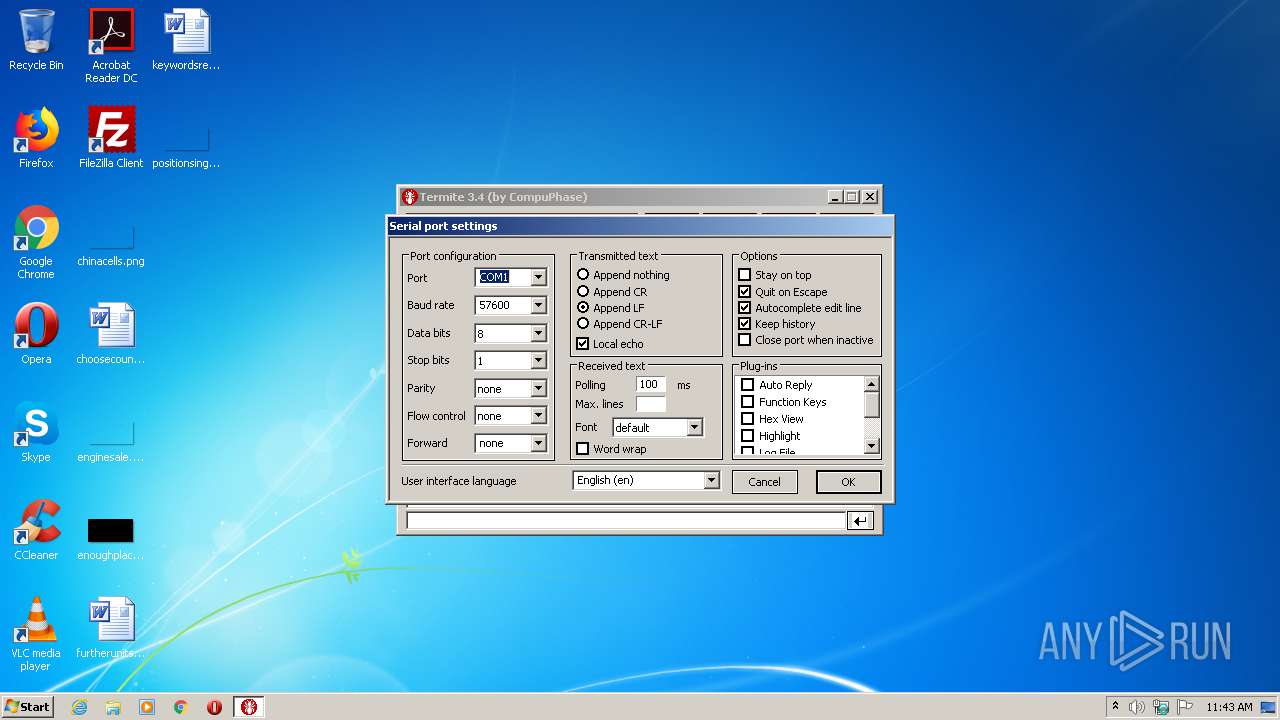
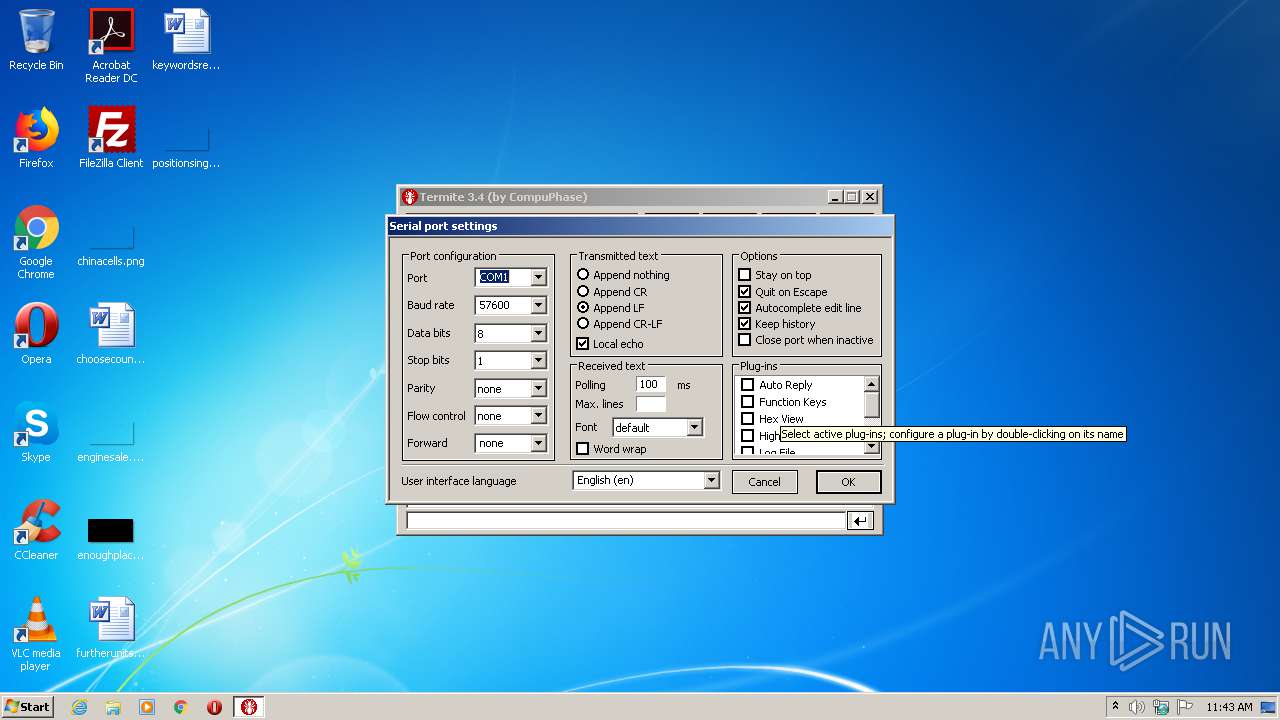
Modification events
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Termite | |||
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | DisplayName |
Value: Termite | |||
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Program Files\Termite\termite.exe" | |||
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | Version |
Value: 3.4 | |||
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | Publisher |
Value: CompuPhase | |||
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Termite\uninstall.exe" | |||
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Termite\uninstall.exe" /S | |||
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | HelpLink |
Value: APP_URL | |||
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | URLUpdateInfo |
Value: APP_URL | |||
| (PID) Process: | (2620) termite-3.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Termite |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
11
Suspicious files
1
Text files
41
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | termite-3.4.exe | C:\Users\admin\AppData\Local\Temp\nsu4D05.tmp | — | |
MD5:— | SHA256:— | |||
| 2620 | termite-3.4.exe | C:\Users\admin\AppData\Local\Temp\nsu4D06.tmp\modern-wizard.bmp | image | |
MD5:52FF52EEE3B944B862C11C268A02C196 | SHA256:2079F7A3EBA60E0D9EE827A7208AA052A71B384873B641DE5E299AEB8E733109 | |||
| 2620 | termite-3.4.exe | C:\Users\admin\AppData\Local\Temp\nsu4D06.tmp\nsDialogs.dll | executable | |
MD5:B3070CF20DB659FDFB3CB2ED38130E8D | SHA256:F2C1409FAF2952C1C91F4B5495158EF5C7D1A1DB6EEA4A18F163574BD52FCAD0 | |||
| 2620 | termite-3.4.exe | C:\Program Files\Termite\Termite.exe | executable | |
MD5:FFE7170AFE24B608D169FB430CD449D8 | SHA256:45B307E129AC3A8E6CB75117122A2D0232E0CCB4FB5C1410874CD41140EF165D | |||
| 2620 | termite-3.4.exe | C:\Users\admin\AppData\Local\Temp\nsu4D06.tmp\System.dll | executable | |
MD5:3F176D1EE13B0D7D6BD92E1C7A0B9BAE | SHA256:FA4AB1D6F79FD677433A31ADA7806373A789D34328DA46CCB0449BBF347BD73E | |||
| 2620 | termite-3.4.exe | C:\Program Files\Termite\Hex_View.flt | executable | |
MD5:48631428B90111ABA0811B62171A9A49 | SHA256:7E320627BAF754F07E5D216D04D88090D69292E06221707AC7E45CC3DE0BBB40 | |||
| 2620 | termite-3.4.exe | C:\Program Files\Termite\uninstall.exe | executable | |
MD5:A27B1E5FCF70A4BB1D4F6BBE72C8107B | SHA256:A0CEAB71BD4B5D0F79A13D331CE3C3C08197C55BA4696C19D1555D42FABB5EFB | |||
| 2620 | termite-3.4.exe | C:\Program Files\Termite\Status_LEDs.flt | executable | |
MD5:156132D736A27A5ADCB08508E2B57288 | SHA256:C028761361DCD45E316919735AB6E5317E12F199F861DFE399E86FB97F00EE03 | |||
| 2620 | termite-3.4.exe | C:\Program Files\Termite\Highlight.flt | executable | |
MD5:38774D86B58B2B8854DCD467F3782386 | SHA256:5BD21D115E152E881AA221BE4D7F94A1EEC6C0B308DAC446963252DD9A608B86 | |||
| 2620 | termite-3.4.exe | C:\Program Files\Termite\termite.cat | text | |
MD5:F6690B31C683F9650550A13596FEC223 | SHA256:87AD62803FE33B529BA2884203A299A880C9B945FF93D08FDD763B8D70474A08 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report