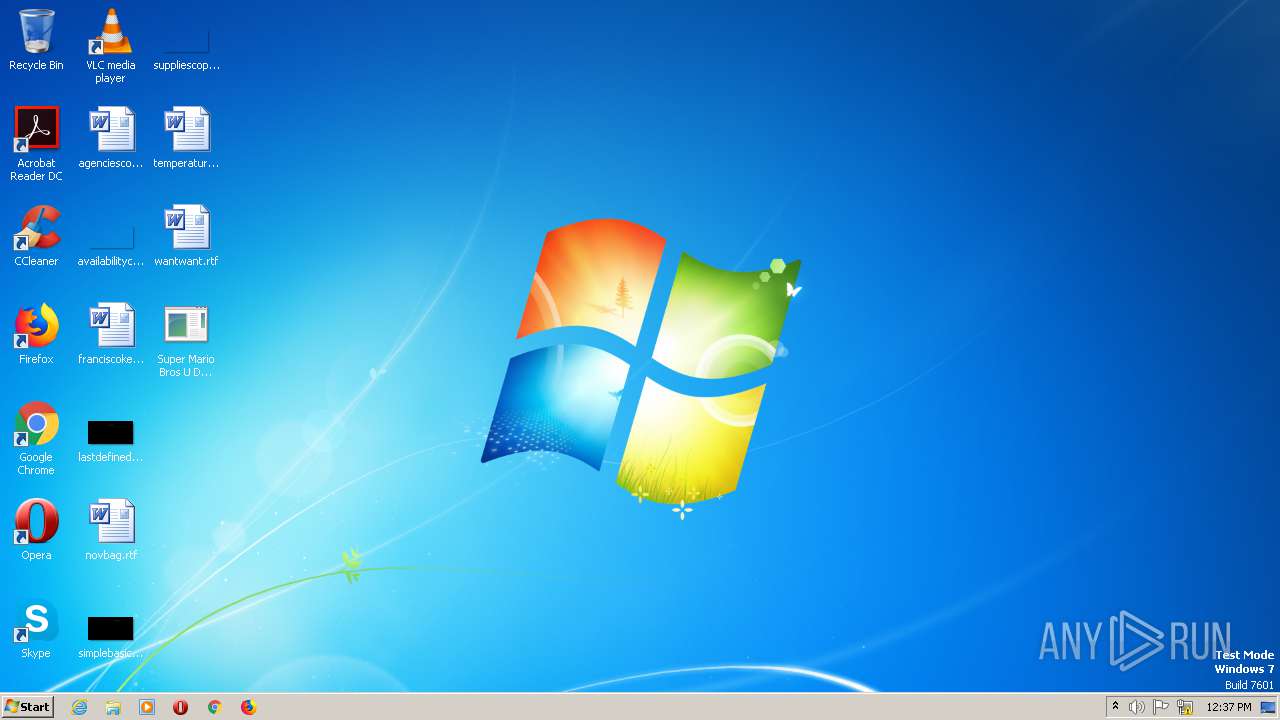
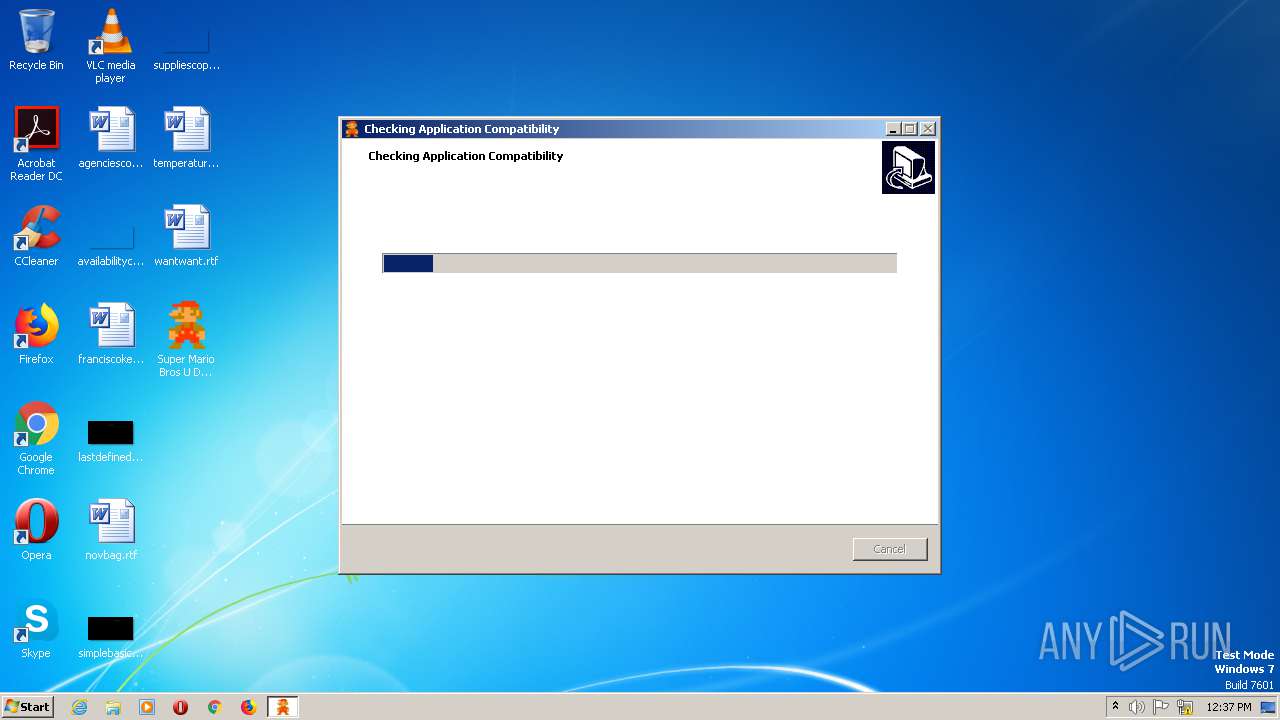
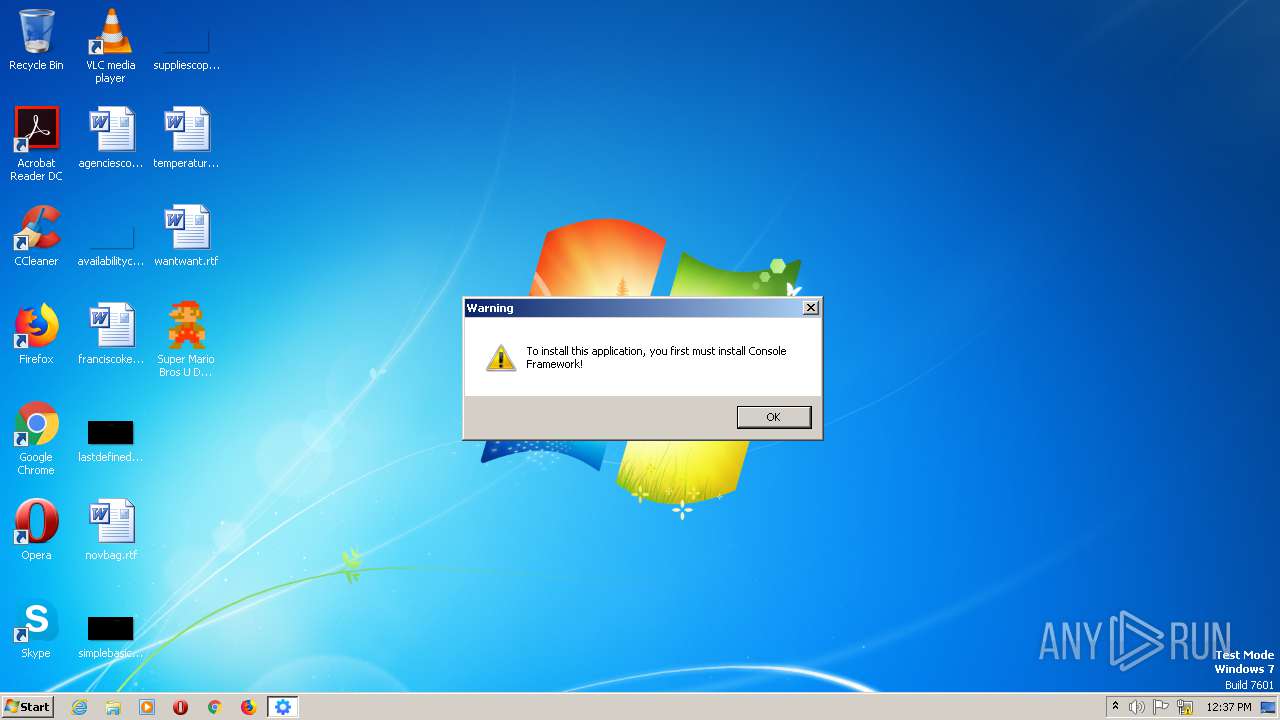
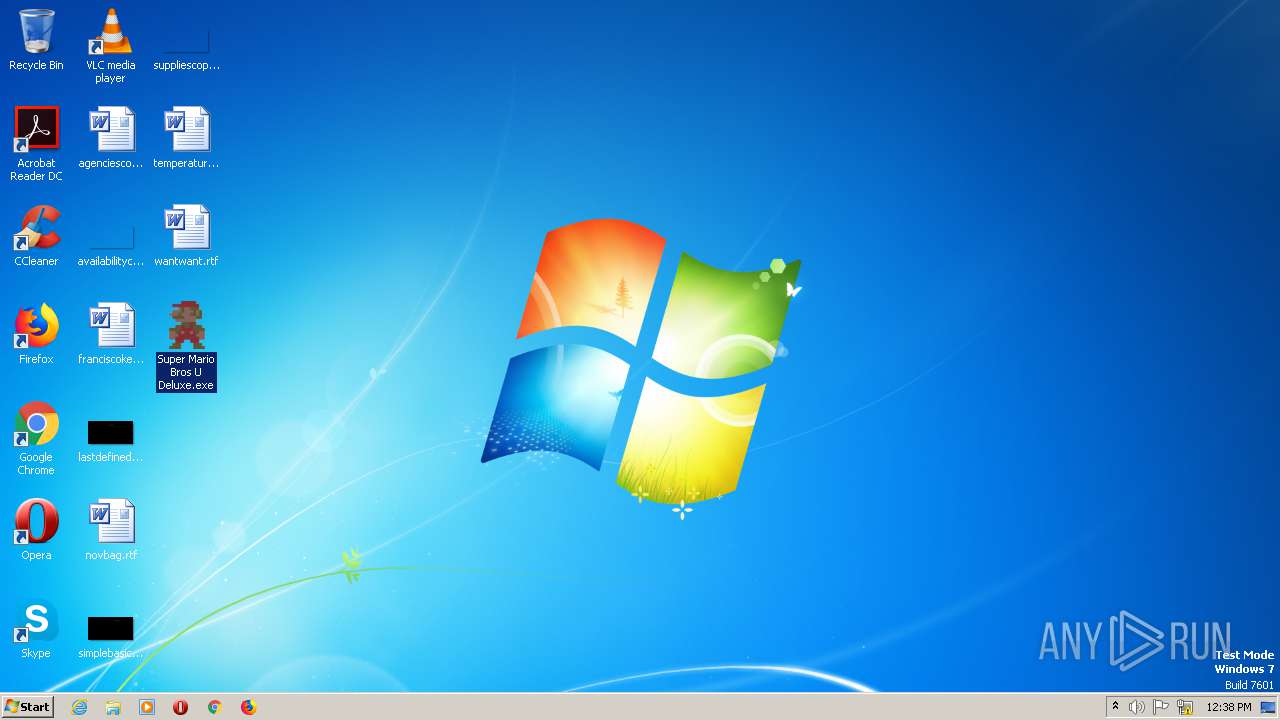
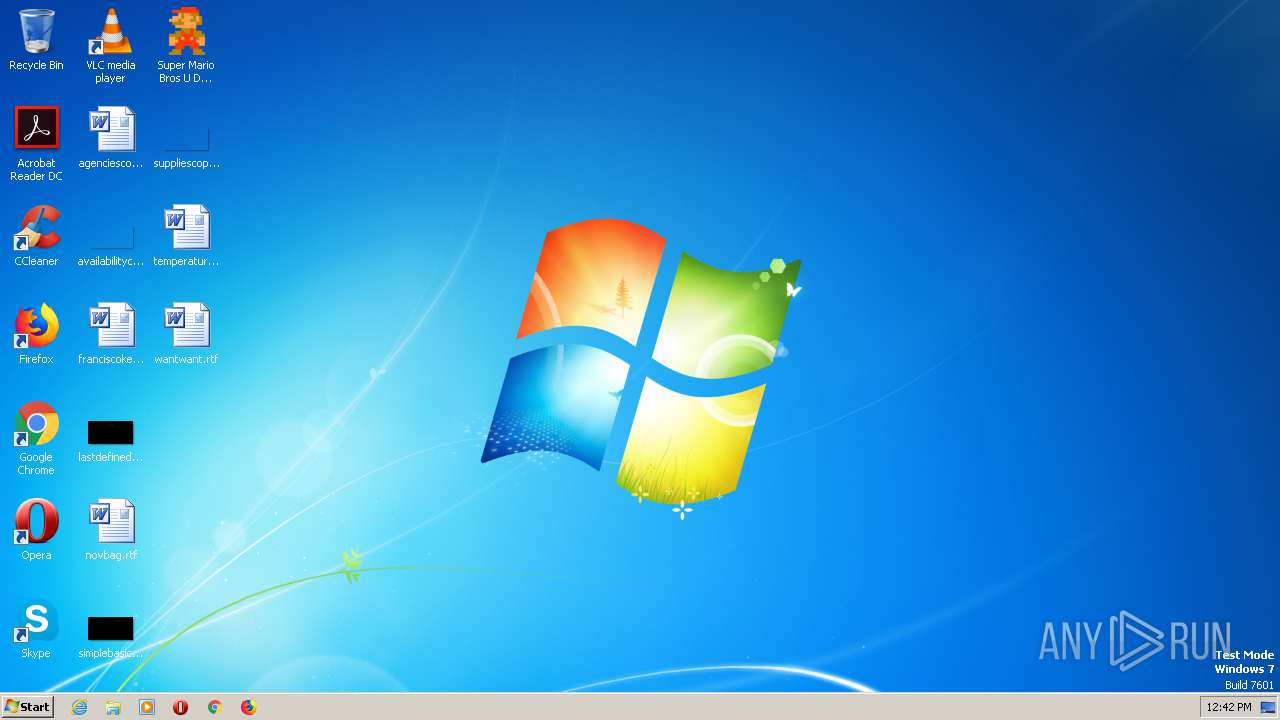
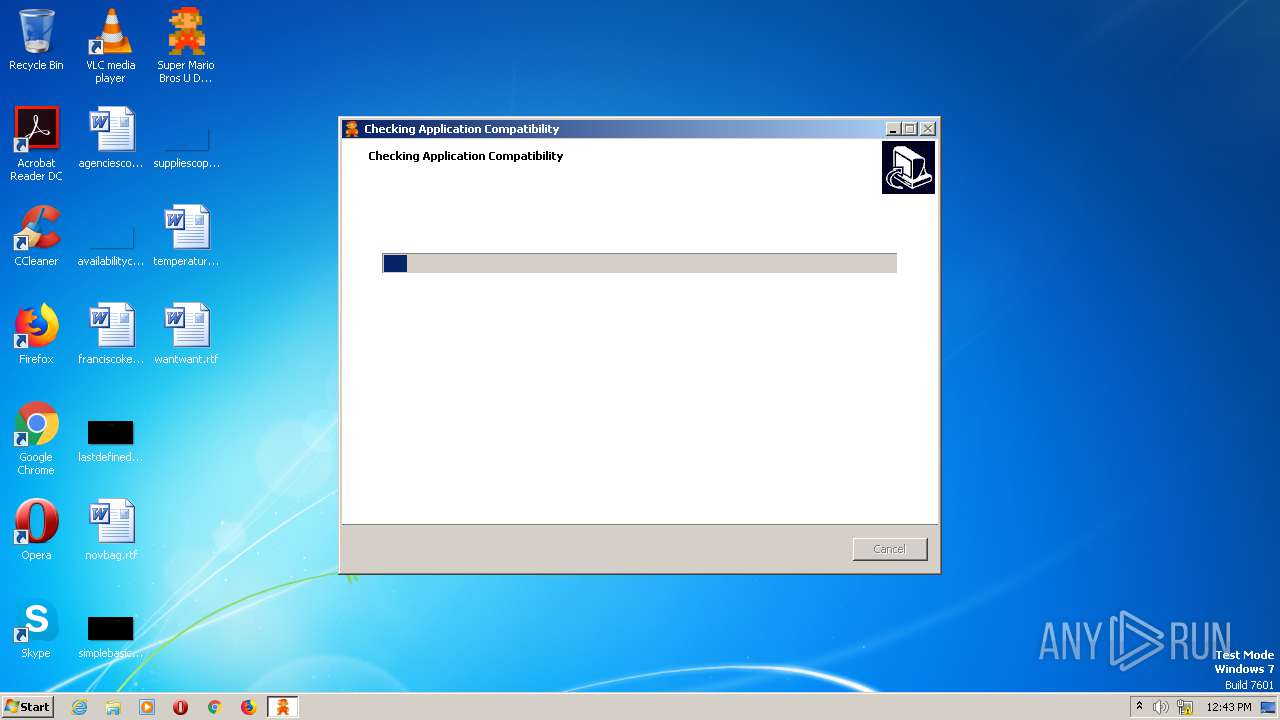
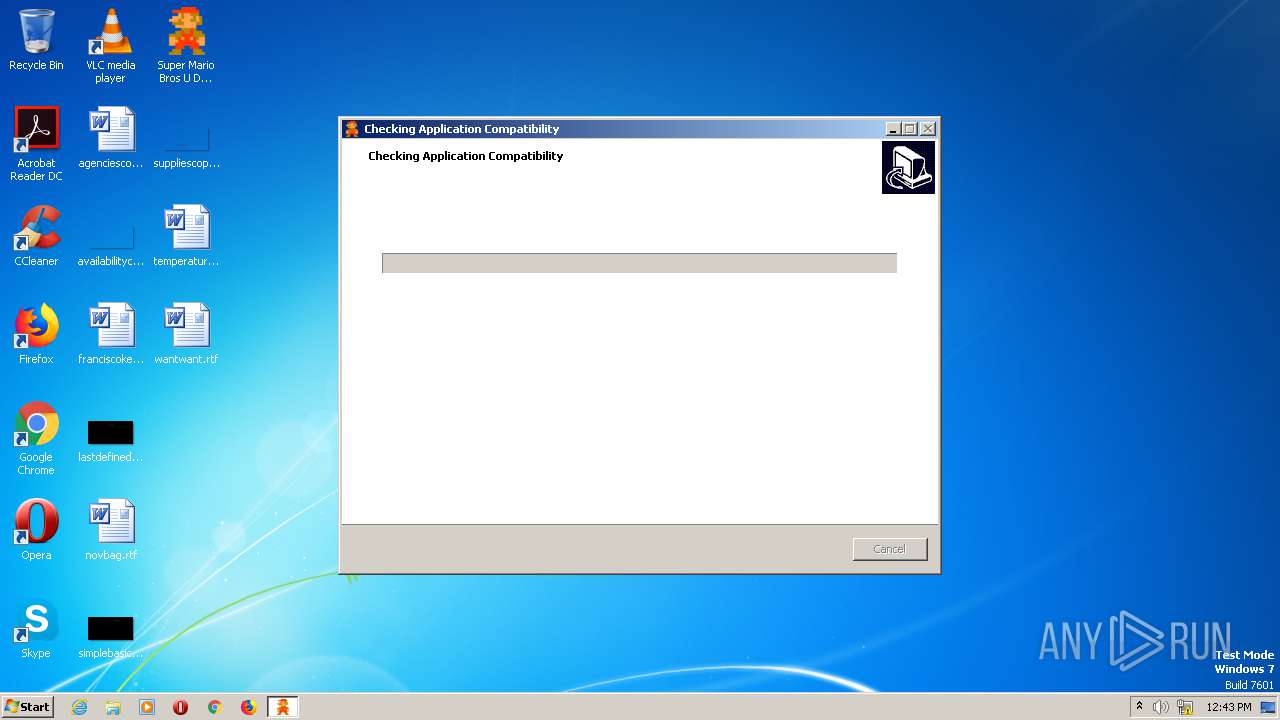
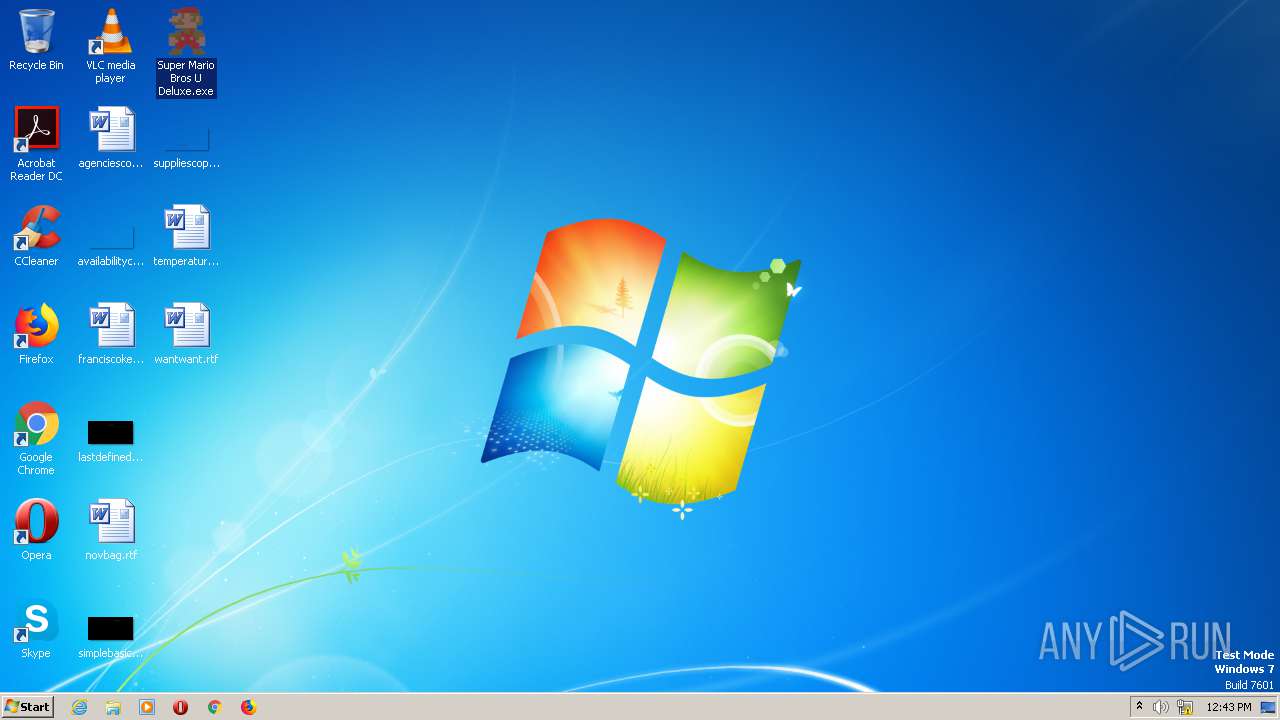
| File name: | Super Mario Bros U Deluxe.exe |
| Full analysis: | https://app.any.run/tasks/2c9ad7cf-bb68-42d4-a22d-c6460b2e7d67 |
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2021, 12:37:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 620D17A4BD47EC2C5DB4C89C211B31CF |
| SHA1: | 3E8CA2F821F2269FE15552A5A9930E6AF1C53B0C |
| SHA256: | CA379A1F9F0F705A9ACDB45C6F82CFE90F772619A0B24237C7928BF88A272865 |
| SSDEEP: | 786432:dexAInNYDaUA2Z/pKvT4ccxPw3VXZqE4GxoF3eDDh1U0f:d4AInbVvTgGXZq5T3ecE |
MALICIOUS
Drops executable file immediately after starts
- Super Mario Bros U Deluxe.tmp (PID: 2484)
- Super Mario Bros U Deluxe.exe (PID: 284)
- Super Mario Bros U Deluxe.exe (PID: 2452)
- Super Mario Bros U Deluxe.tmp (PID: 2568)
- Super Mario Bros U Deluxe.exe (PID: 944)
- Super Mario Bros U Deluxe.exe (PID: 2404)
- Super Mario Bros U Deluxe.tmp (PID: 372)
- GoogleUpdateSetup.exe (PID: 3356)
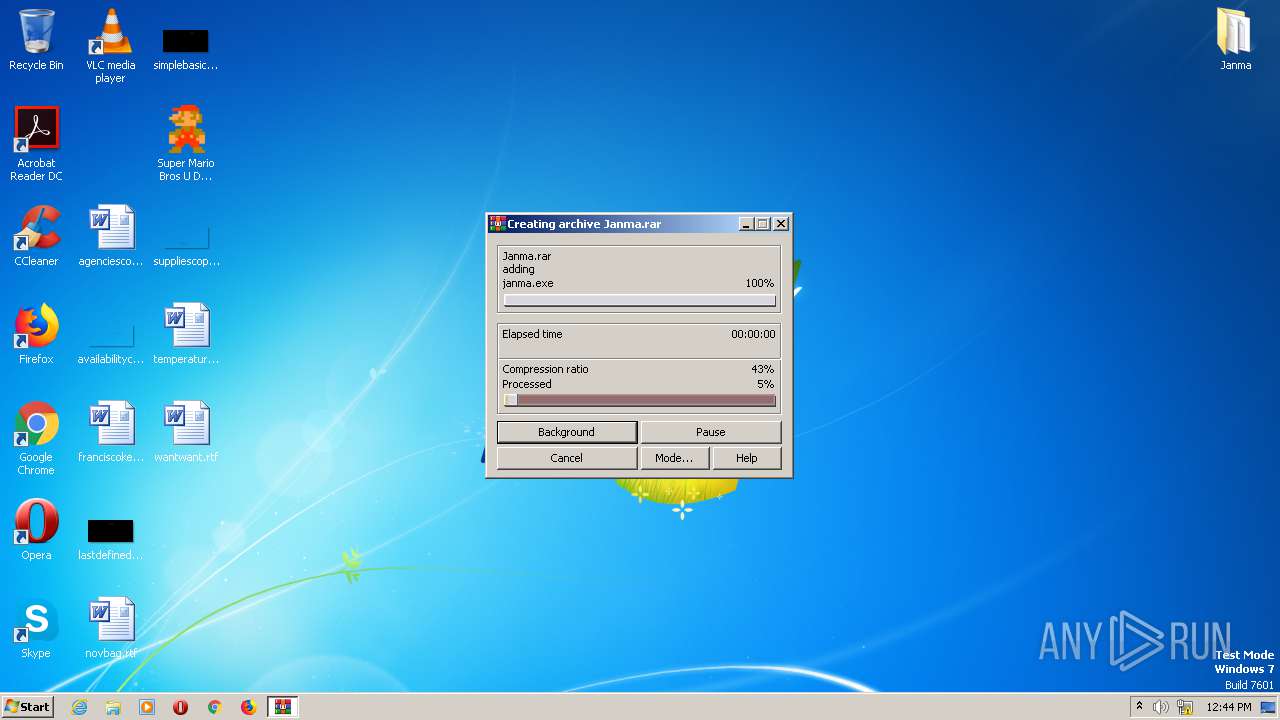
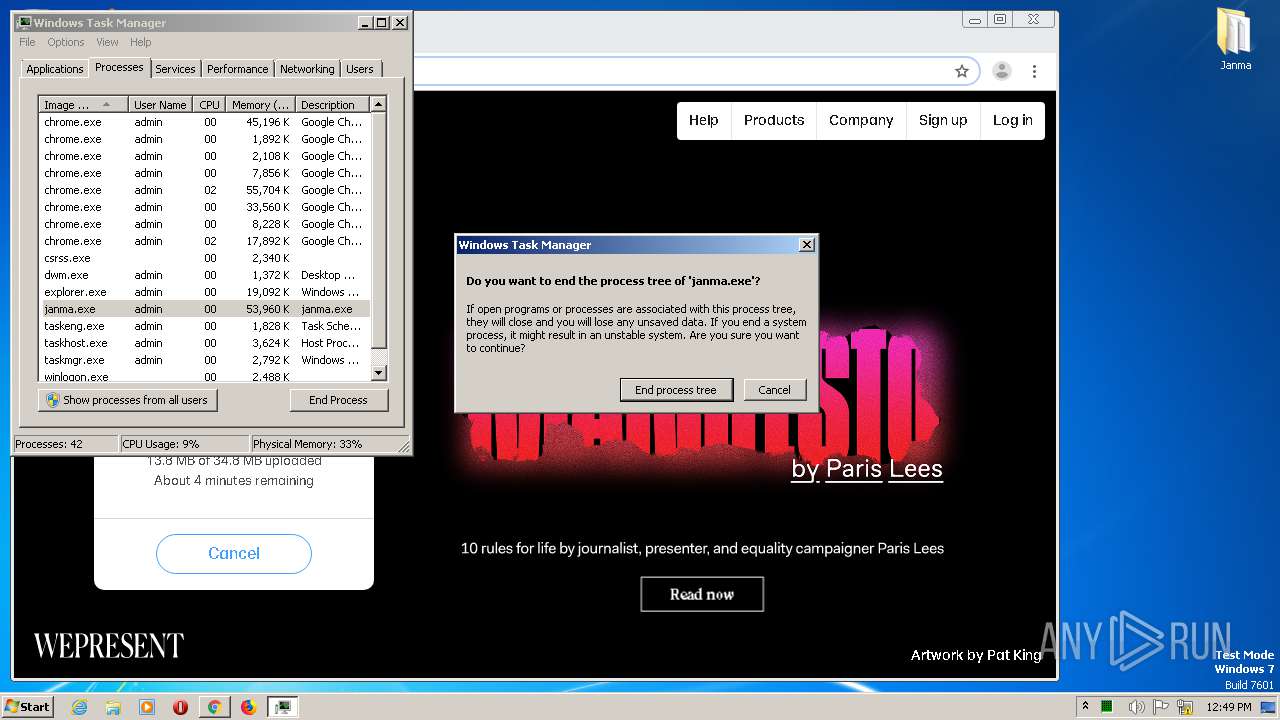
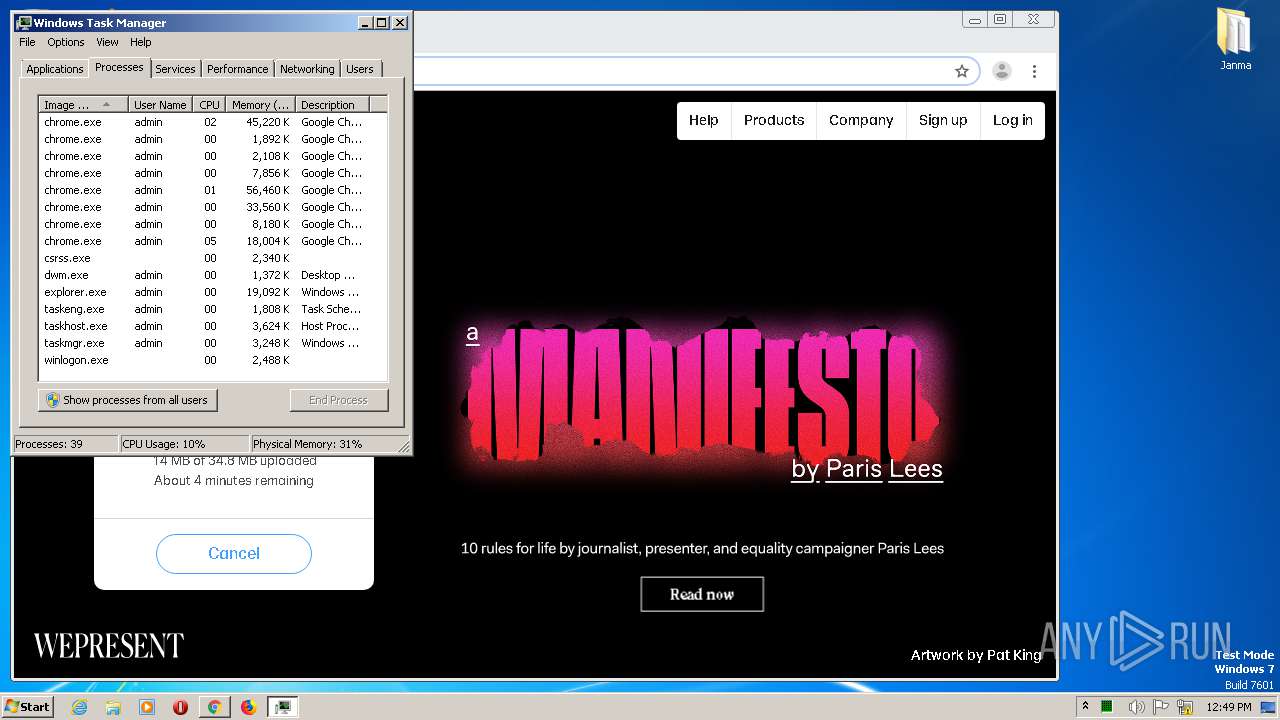
Loads dropped or rewritten executable
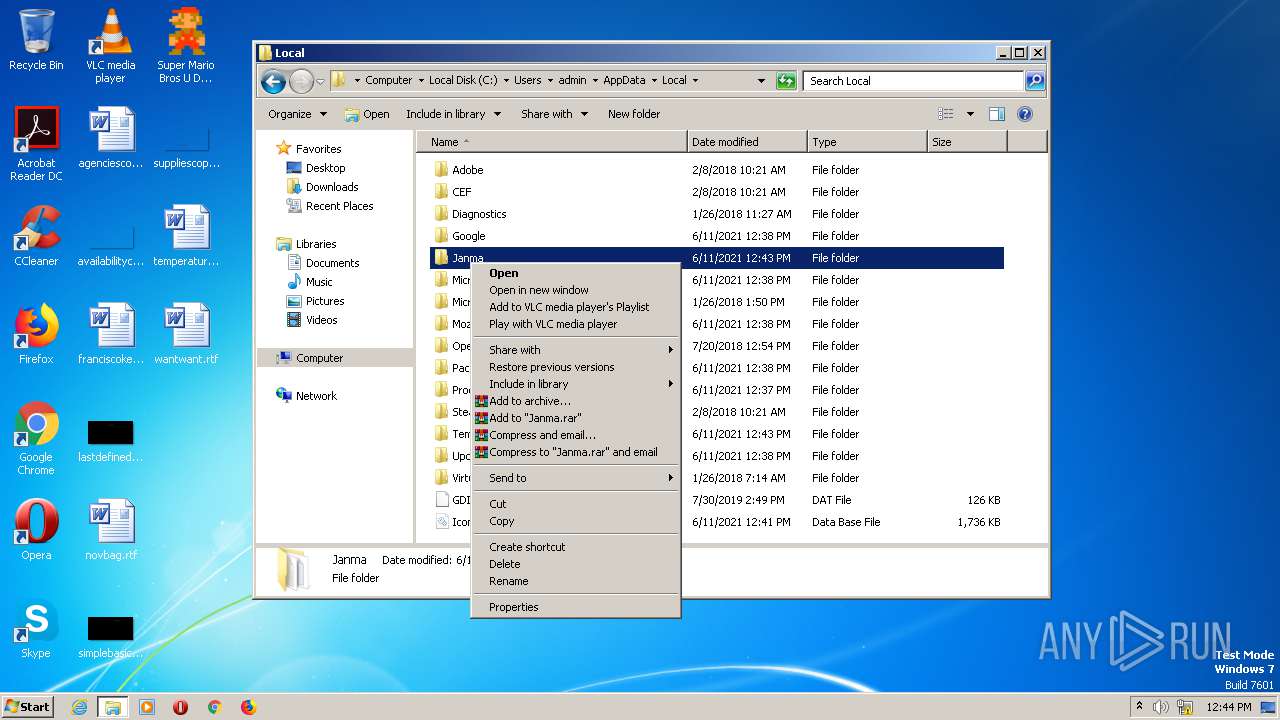
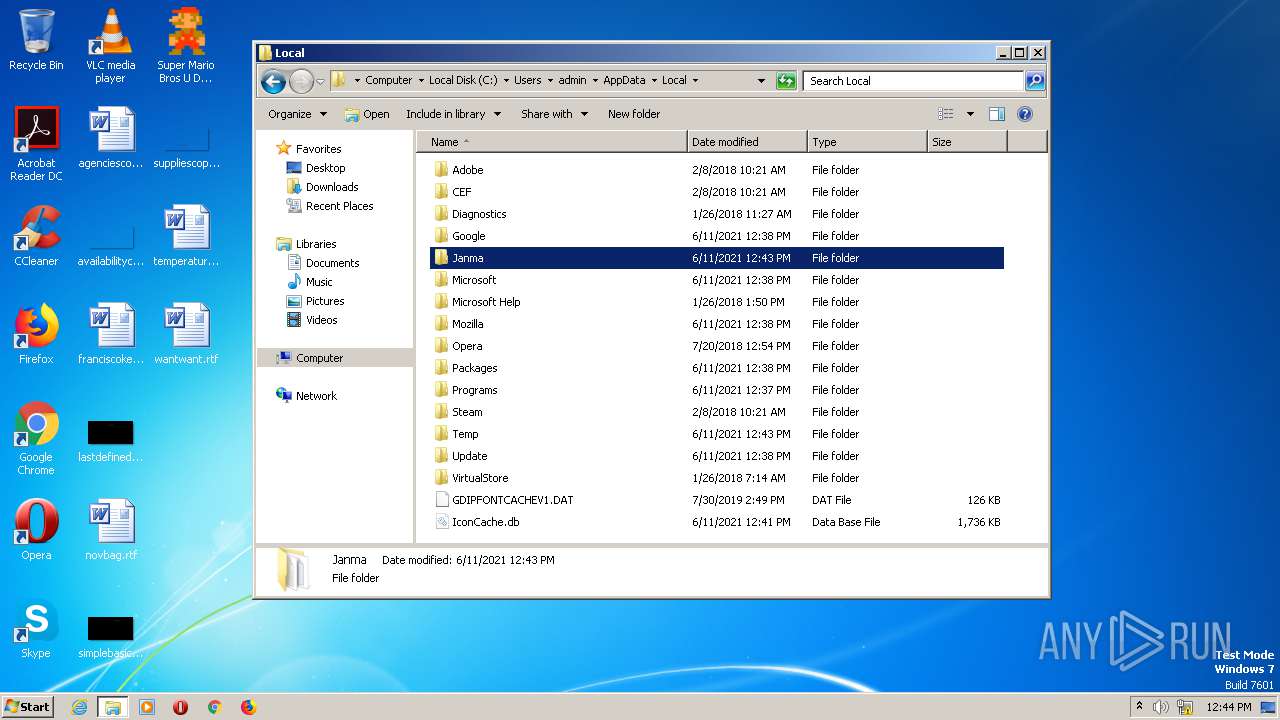
- janma.exe (PID: 2116)
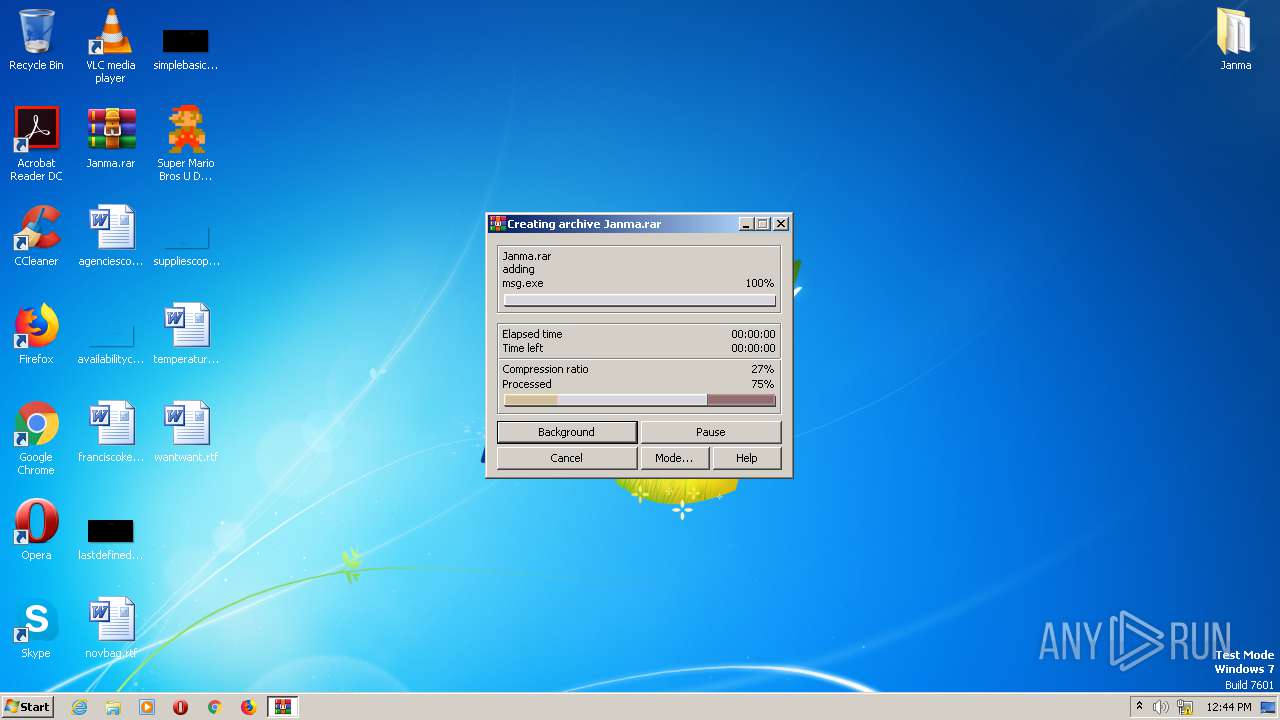
- msg.exe (PID: 2084)
- janma.exe (PID: 2796)
- janma.exe (PID: 2348)
- janma.exe (PID: 2616)
- janma.exe (PID: 2808)
- janma.exe (PID: 3028)
- janma.exe (PID: 2852)
- janma.exe (PID: 2128)
- janma.exe (PID: 3060)
- msg.exe (PID: 124)
- SearchProtocolHost.exe (PID: 2932)
- janma.exe (PID: 2824)
- janma.exe (PID: 2352)
- janma.exe (PID: 2264)
- janma.exe (PID: 2876)
- GoogleUpdate.exe (PID: 760)
- GoogleUpdate.exe (PID: 1136)
- GoogleUpdate.exe (PID: 2528)
Application was dropped or rewritten from another process
- msg.exe (PID: 2084)
- msg.exe (PID: 124)
- ChromeRecovery.exe (PID: 2780)
- GoogleUpdateSetup.exe (PID: 3356)
- GoogleUpdate.exe (PID: 760)
- GoogleUpdateComRegisterShell64.exe (PID: 3312)
- GoogleUpdateComRegisterShell64.exe (PID: 2460)
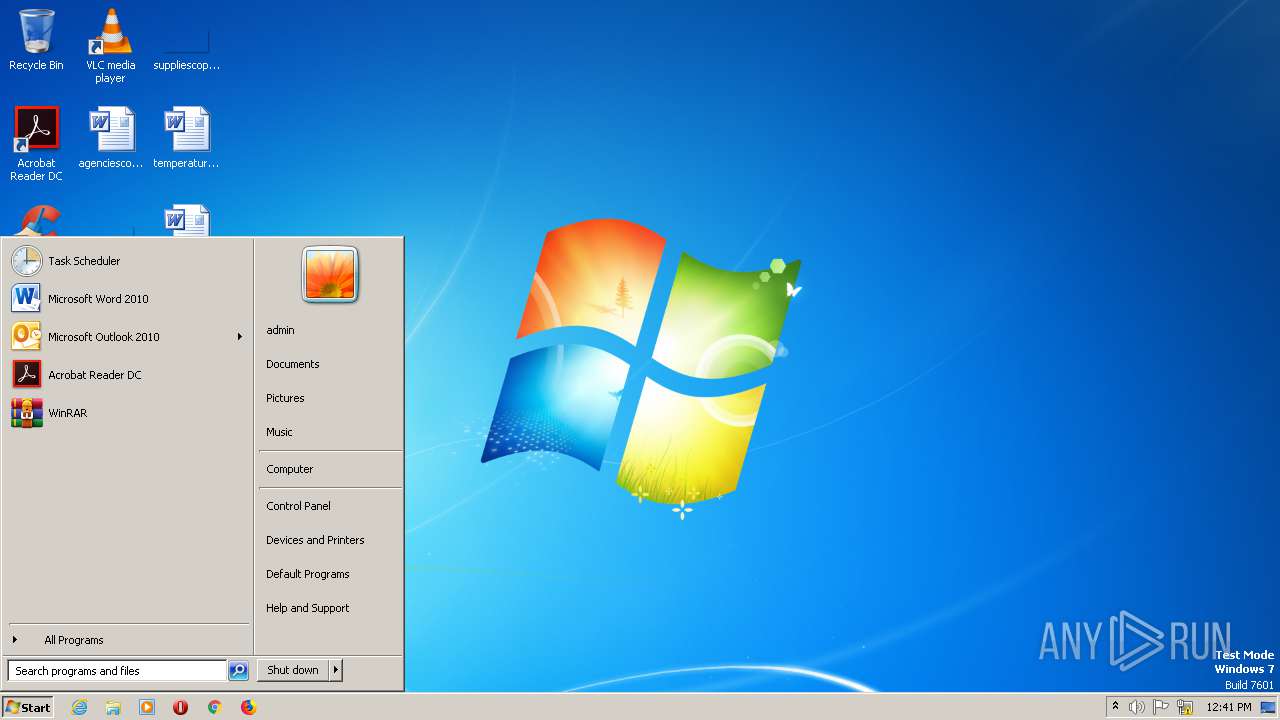
Loads the Task Scheduler COM API
- janma.exe (PID: 2116)
- janma.exe (PID: 2796)
- janma.exe (PID: 2808)
- janma.exe (PID: 2852)
- janma.exe (PID: 2128)
- janma.exe (PID: 2616)
- janma.exe (PID: 3028)
- janma.exe (PID: 3060)
- janma.exe (PID: 2824)
- janma.exe (PID: 2352)
- janma.exe (PID: 2264)
- janma.exe (PID: 2876)
- GoogleUpdate.exe (PID: 760)
SUSPICIOUS
Executable content was dropped or overwritten
- Super Mario Bros U Deluxe.exe (PID: 2436)
- Super Mario Bros U Deluxe.tmp (PID: 2932)
- Super Mario Bros U Deluxe.exe (PID: 284)
- Super Mario Bros U Deluxe.tmp (PID: 2484)
- janma.exe (PID: 2116)
- Super Mario Bros U Deluxe.exe (PID: 2712)
- Super Mario Bros U Deluxe.exe (PID: 2452)
- Super Mario Bros U Deluxe.tmp (PID: 2568)
- Super Mario Bros U Deluxe.exe (PID: 2404)
- janma.exe (PID: 3060)
- Super Mario Bros U Deluxe.tmp (PID: 372)
- Super Mario Bros U Deluxe.exe (PID: 944)
- GoogleUpdateSetup.exe (PID: 3356)
Drops a file with too old compile date
- Super Mario Bros U Deluxe.tmp (PID: 2484)
- janma.exe (PID: 2116)
- Super Mario Bros U Deluxe.tmp (PID: 2568)
Drops a file with a compile date too recent
- Super Mario Bros U Deluxe.tmp (PID: 2484)
- janma.exe (PID: 2116)
- Super Mario Bros U Deluxe.tmp (PID: 2568)
- firefox.exe (PID: 2052)
Drops a file that was compiled in debug mode
- Super Mario Bros U Deluxe.tmp (PID: 2484)
- janma.exe (PID: 2116)
- Super Mario Bros U Deluxe.tmp (PID: 2568)
- GoogleUpdateSetup.exe (PID: 3356)
Loads Python modules
- msg.exe (PID: 2084)
- janma.exe (PID: 2116)
- janma.exe (PID: 2348)
- janma.exe (PID: 2796)
- janma.exe (PID: 2852)
- janma.exe (PID: 2808)
- janma.exe (PID: 3028)
- janma.exe (PID: 2616)
- janma.exe (PID: 2128)
- janma.exe (PID: 3060)
- msg.exe (PID: 124)
- janma.exe (PID: 2824)
- janma.exe (PID: 2264)
- janma.exe (PID: 2352)
- janma.exe (PID: 2876)
Executed via Task Scheduler
- janma.exe (PID: 2348)
- janma.exe (PID: 3028)
- janma.exe (PID: 2808)
- janma.exe (PID: 2796)
- janma.exe (PID: 2616)
- janma.exe (PID: 2852)
- janma.exe (PID: 2128)
- janma.exe (PID: 2824)
- janma.exe (PID: 2352)
- janma.exe (PID: 2264)
- janma.exe (PID: 2876)
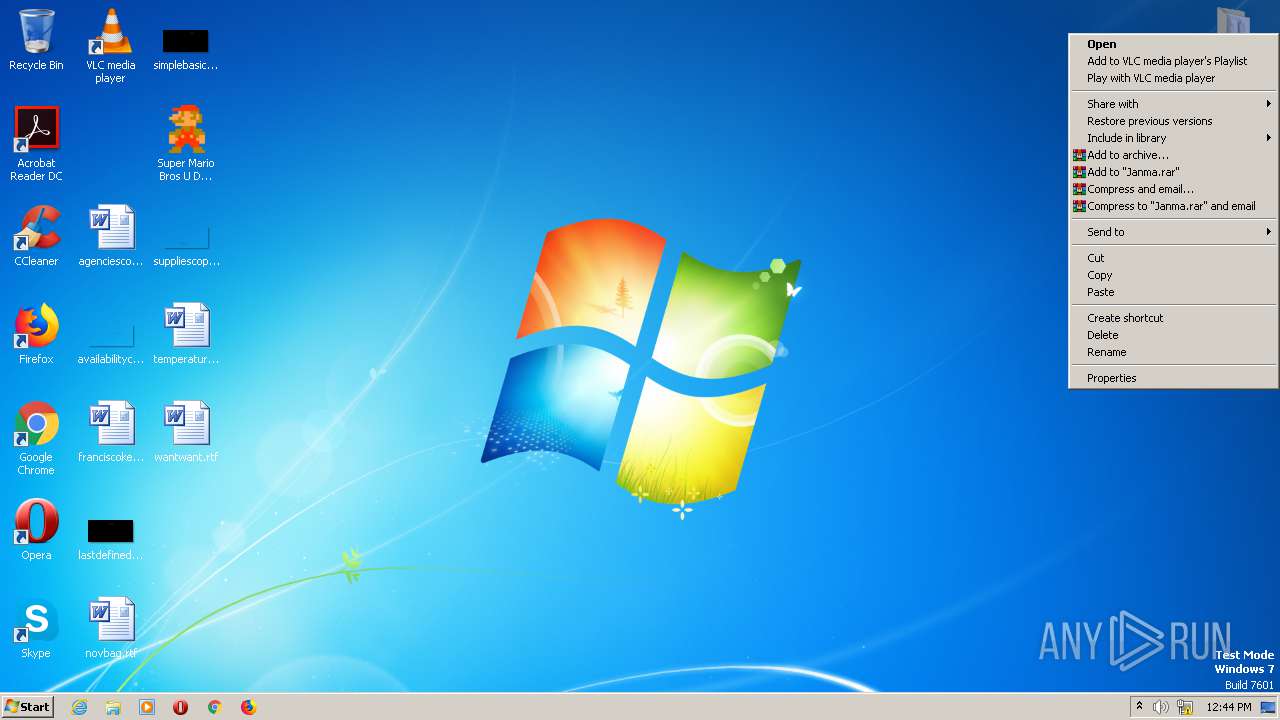
Modifies files in Chrome extension folder
- chrome.exe (PID: 1904)
Creates a directory in Program Files
- GoogleUpdateSetup.exe (PID: 3356)
- GoogleUpdate.exe (PID: 760)
Creates files in the program directory
- GoogleUpdateSetup.exe (PID: 3356)
- GoogleUpdate.exe (PID: 760)
Disables SEHOP
- GoogleUpdate.exe (PID: 760)
Creates/Modifies COM task schedule object
- GoogleUpdate.exe (PID: 2528)
- GoogleUpdateComRegisterShell64.exe (PID: 2460)
- GoogleUpdateComRegisterShell64.exe (PID: 3312)
INFO
Application was dropped or rewritten from another process
- Super Mario Bros U Deluxe.tmp (PID: 2932)
- Super Mario Bros U Deluxe.tmp (PID: 2484)
- Super Mario Bros U Deluxe.tmp (PID: 2612)
- Super Mario Bros U Deluxe.tmp (PID: 2568)
- Super Mario Bros U Deluxe.tmp (PID: 888)
- Super Mario Bros U Deluxe.tmp (PID: 372)
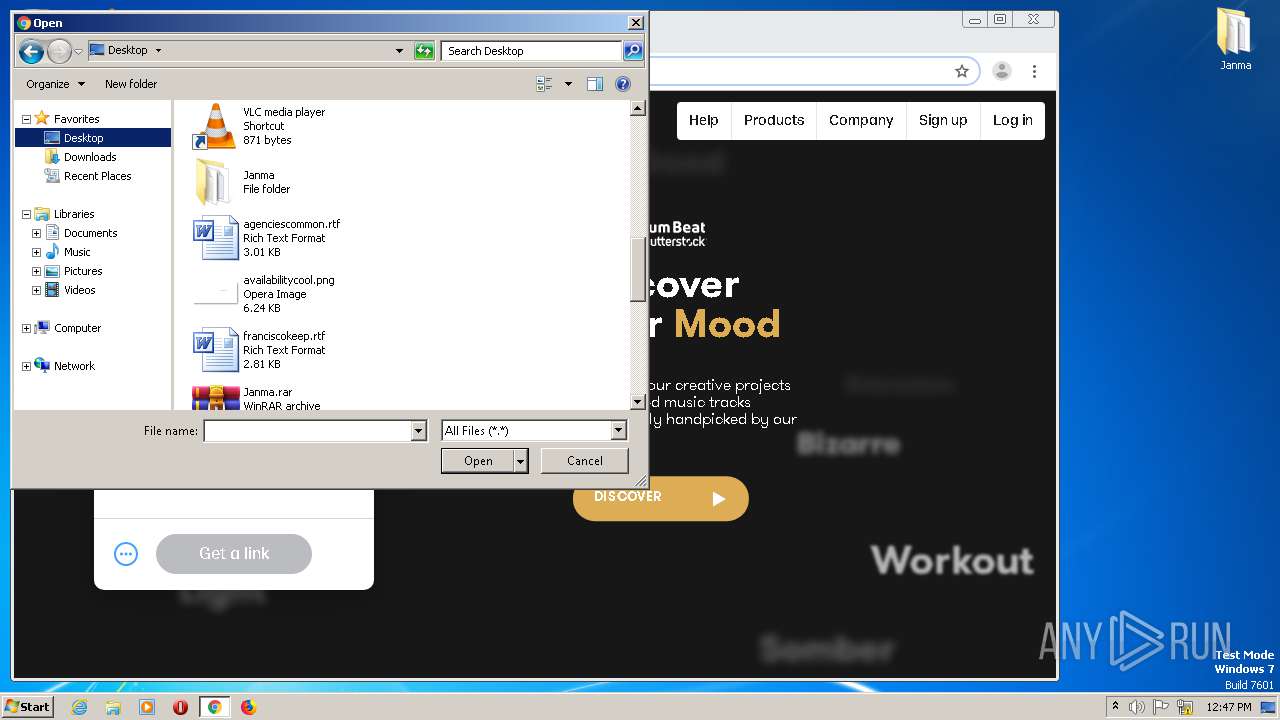
Dropped object may contain Bitcoin addresses
- Super Mario Bros U Deluxe.tmp (PID: 2484)
- janma.exe (PID: 2116)
- Super Mario Bros U Deluxe.tmp (PID: 2568)
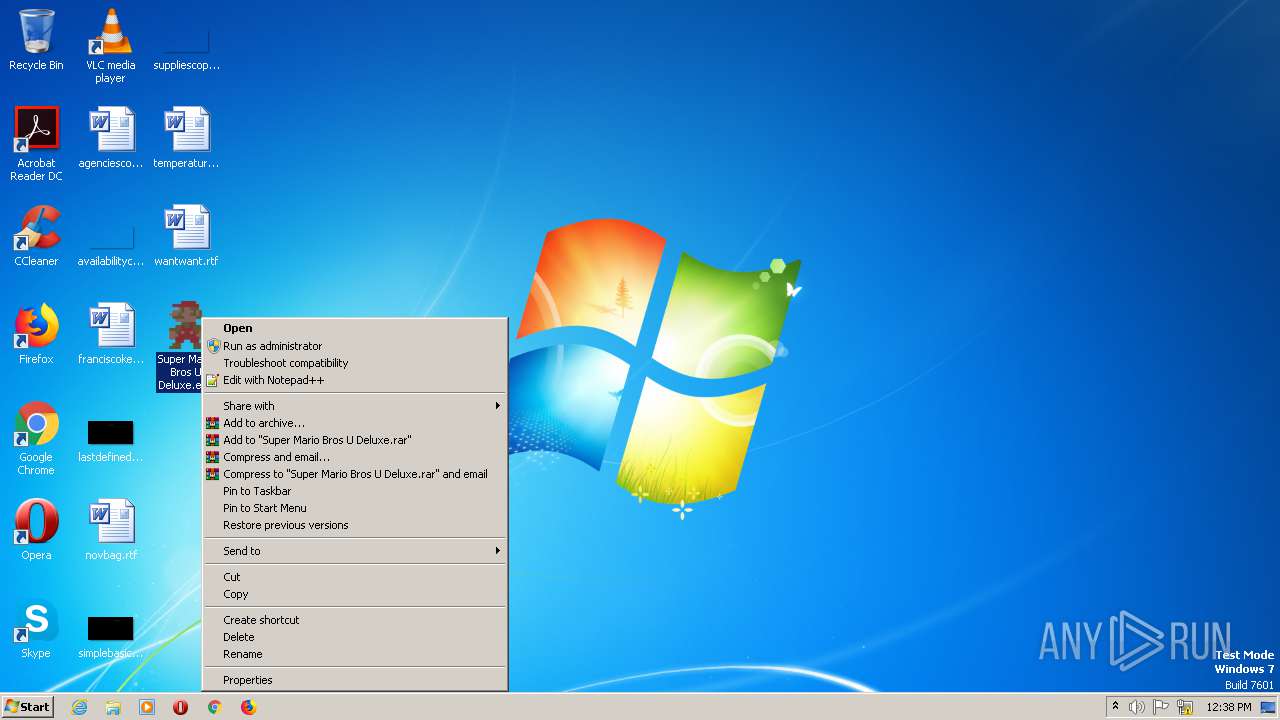
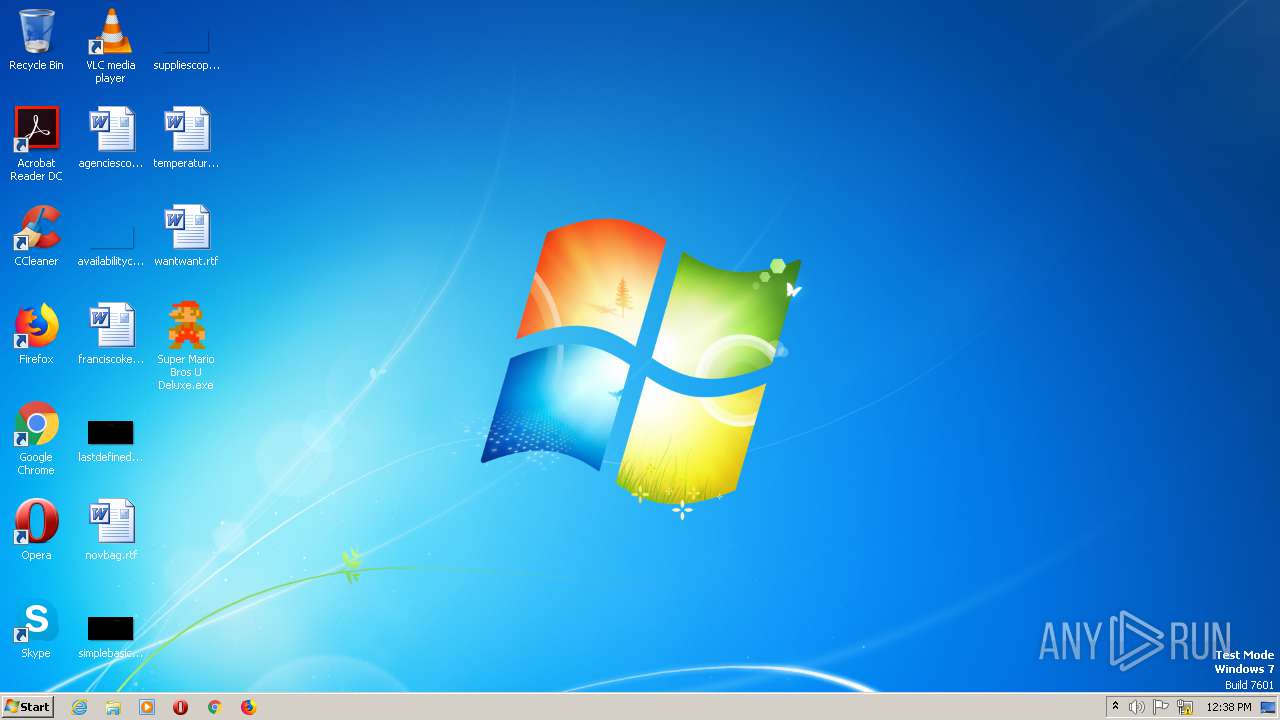
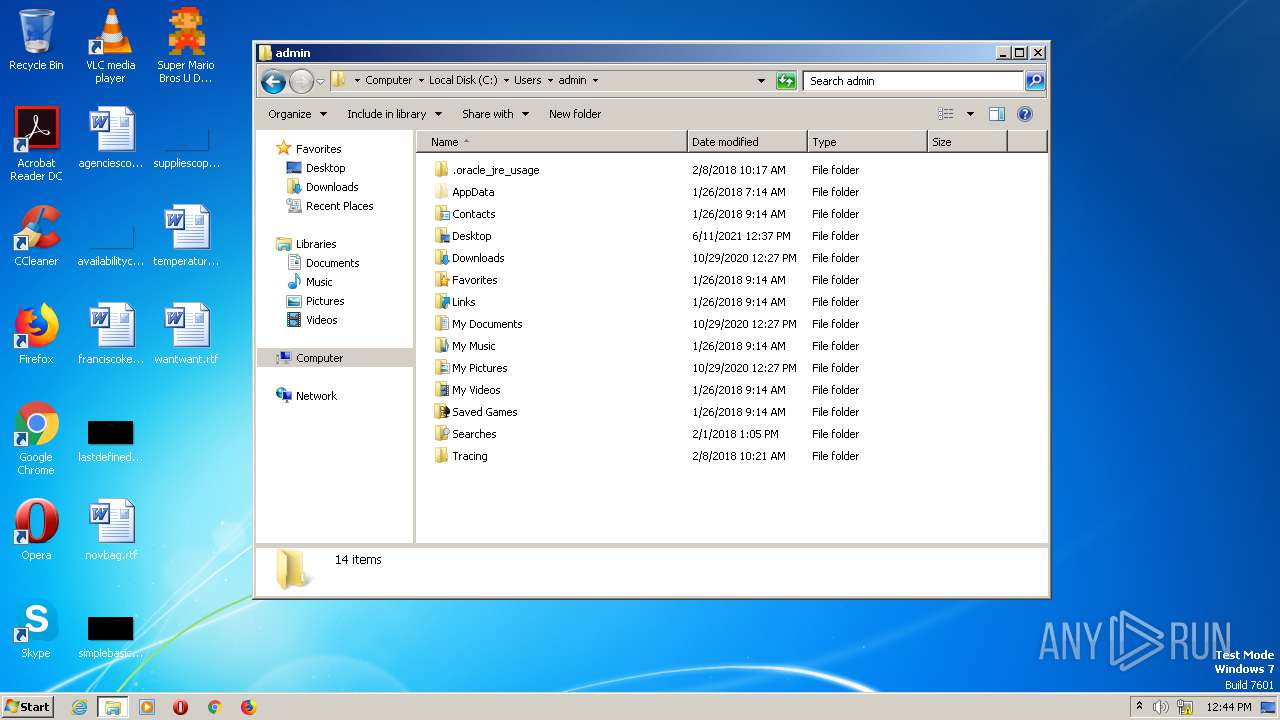
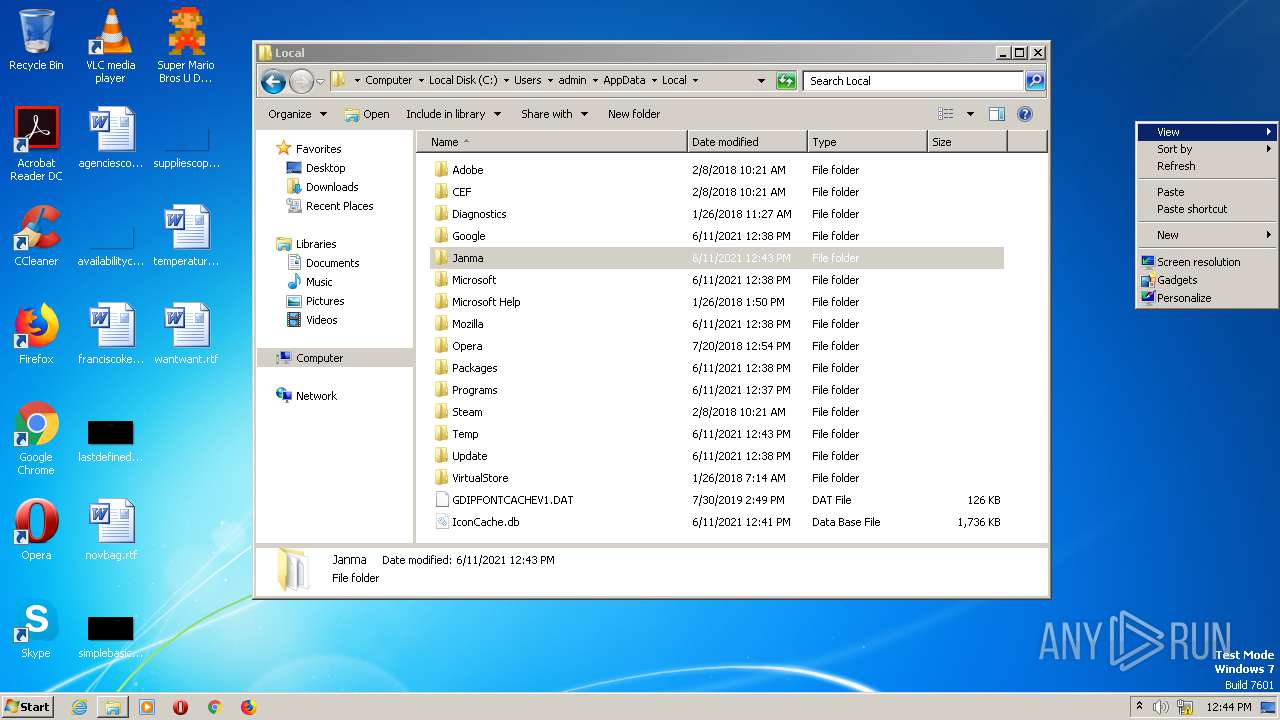
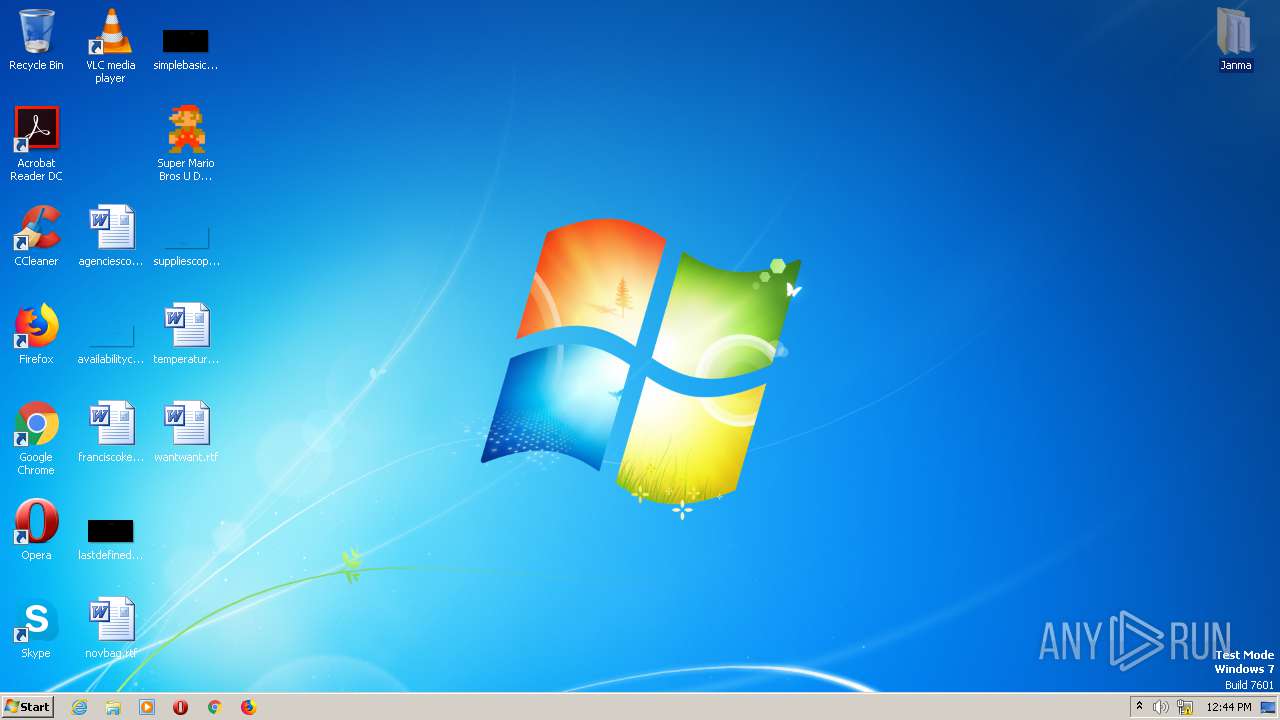
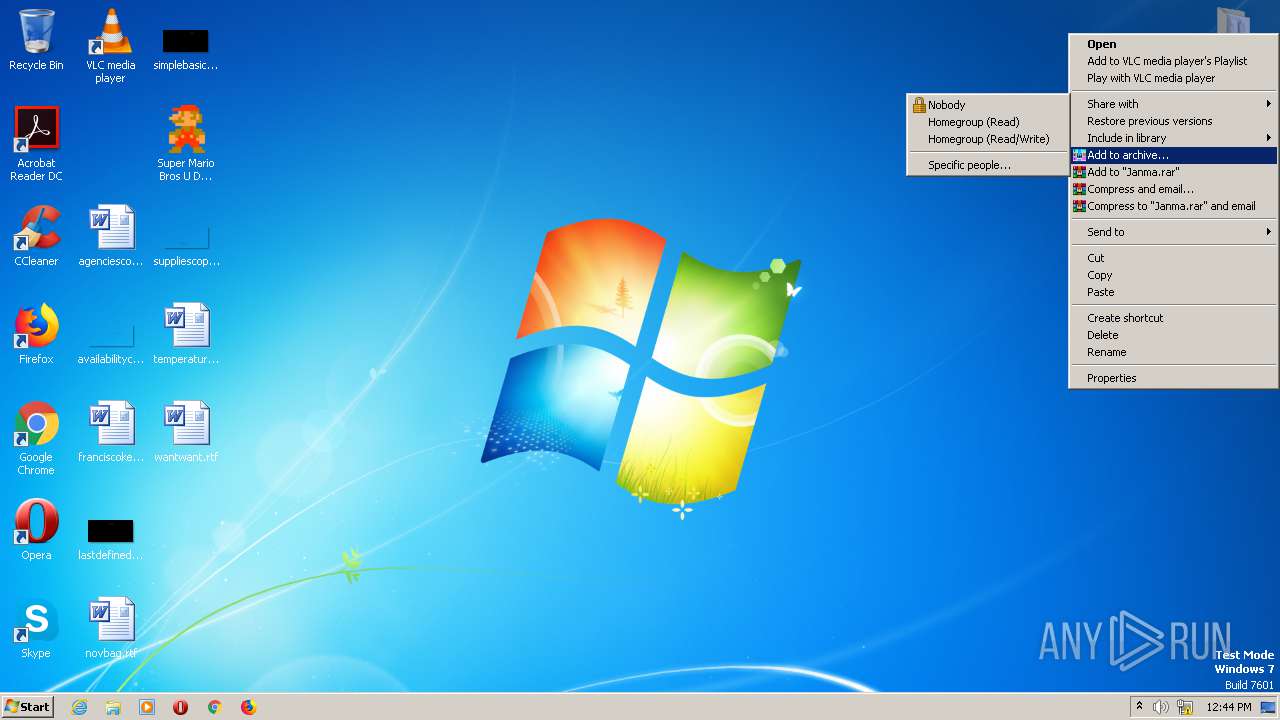
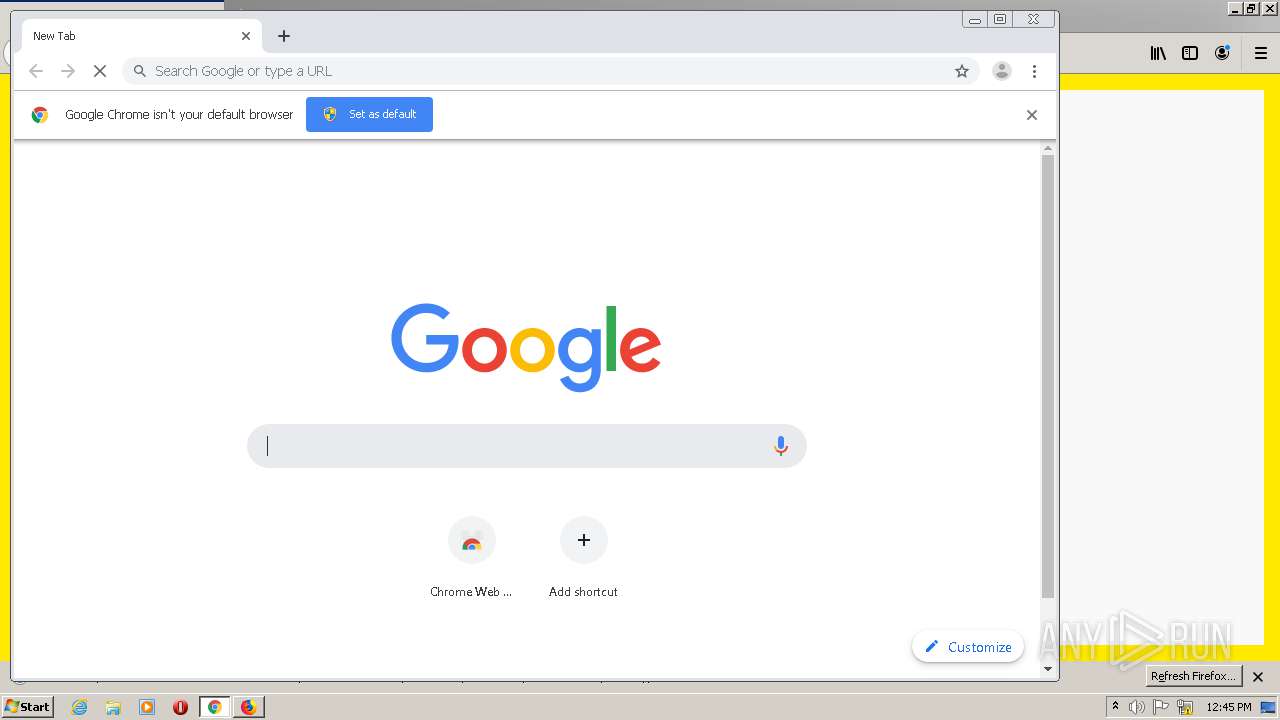
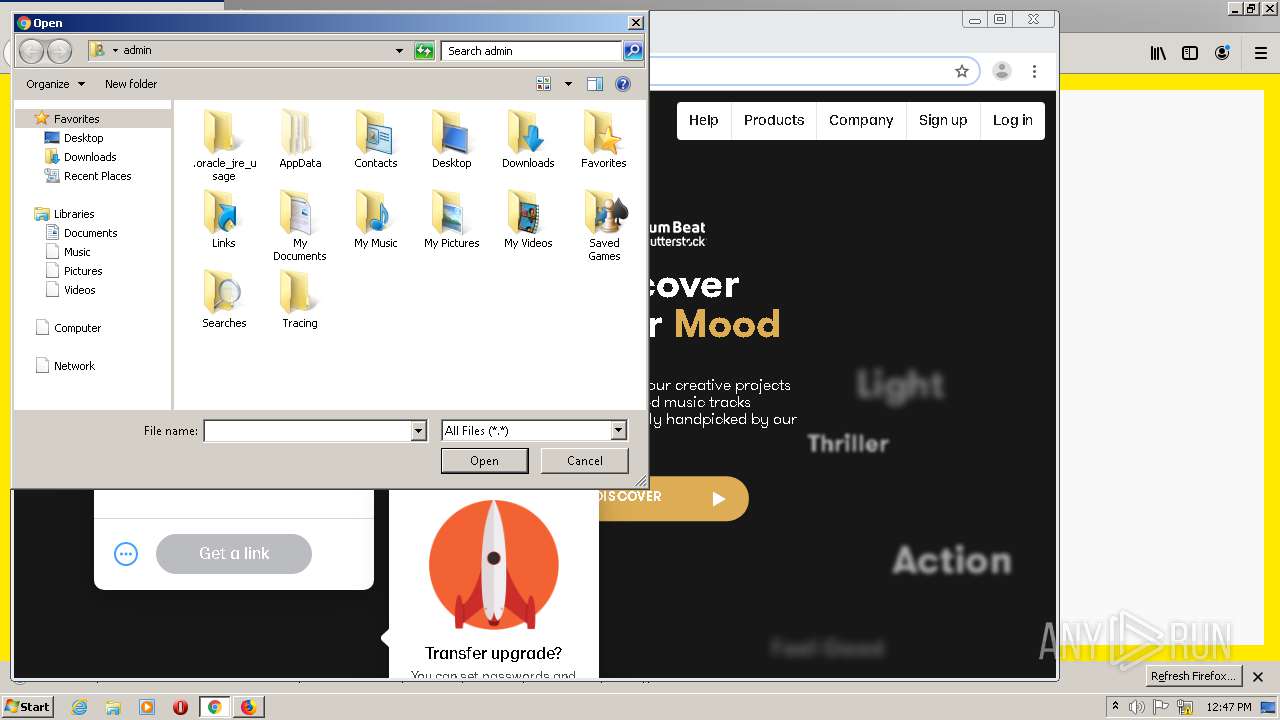
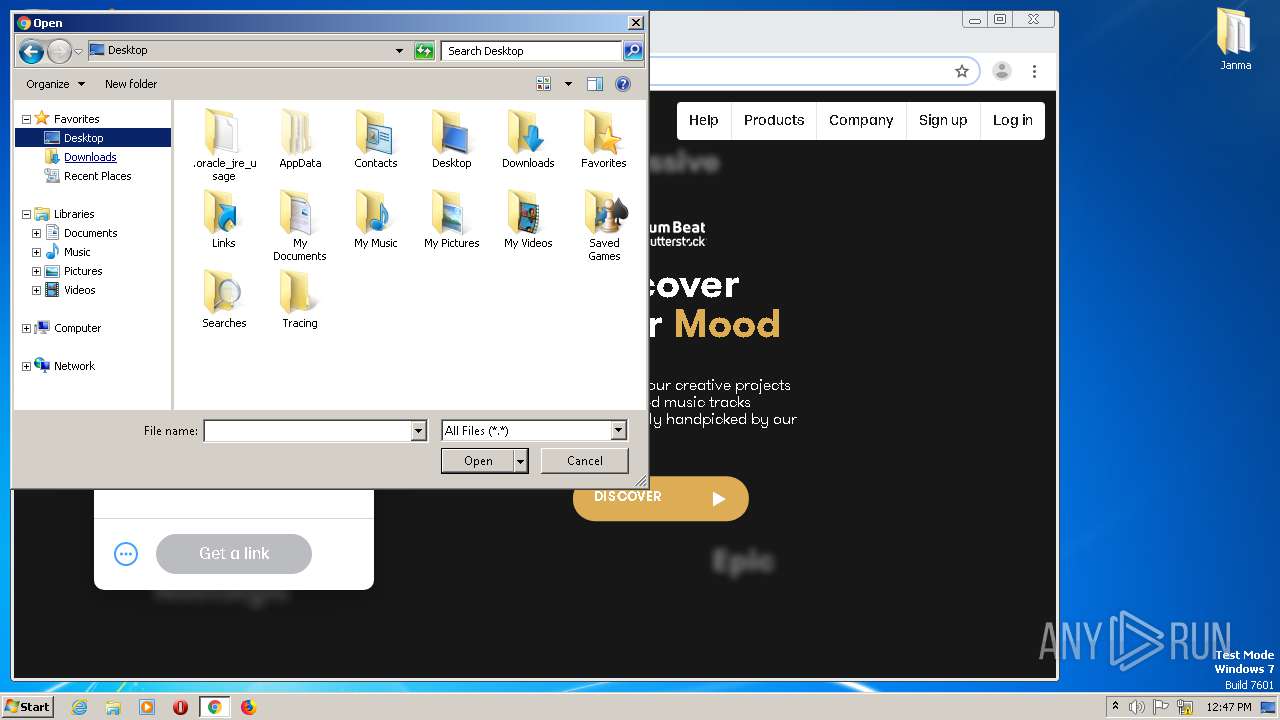
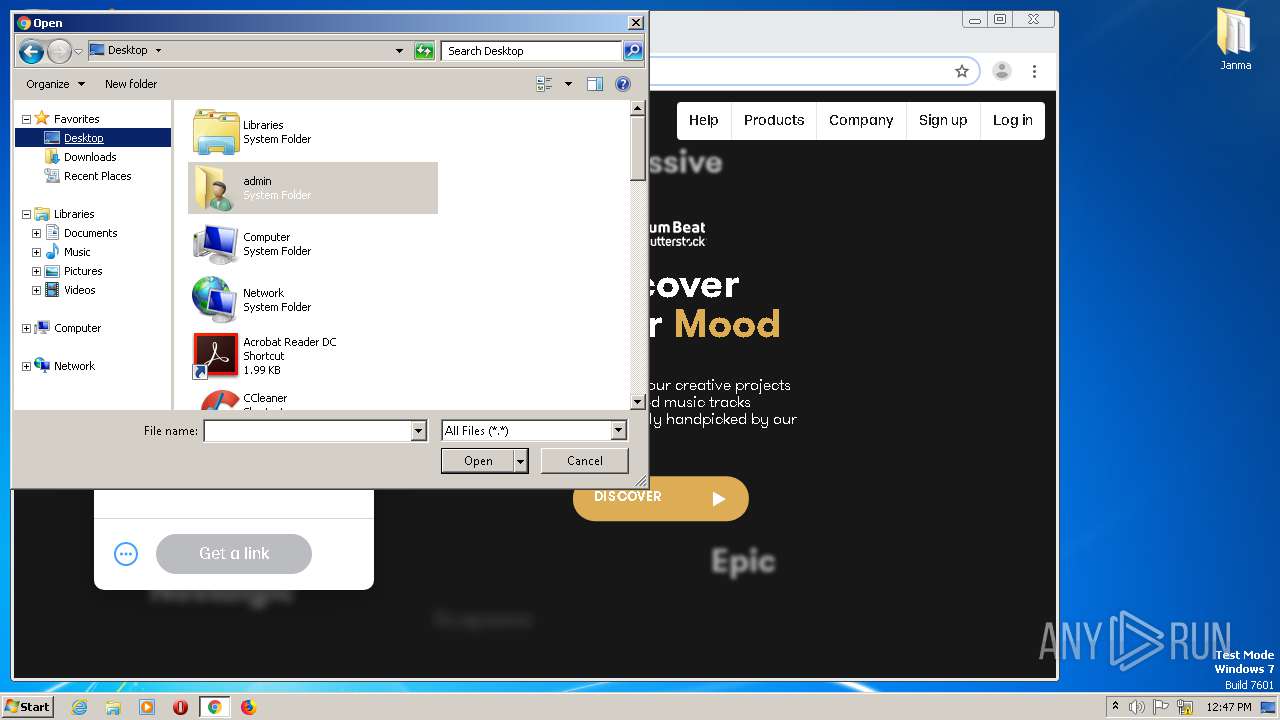
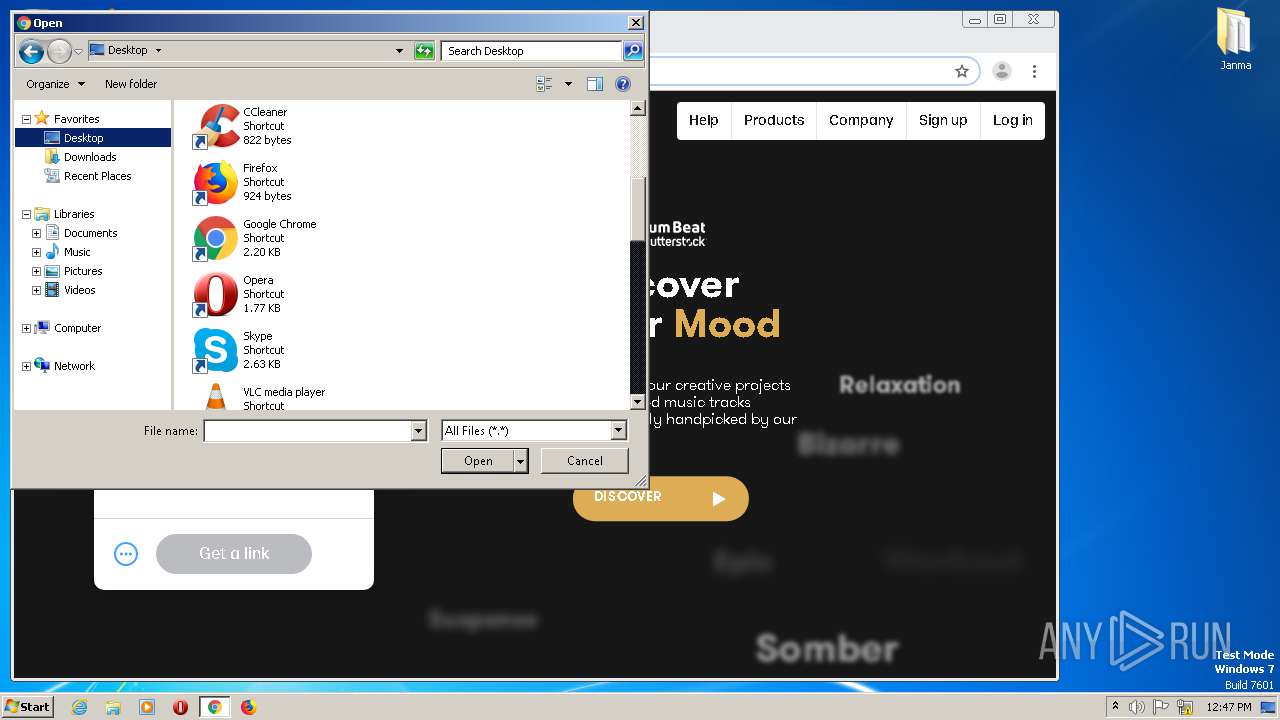
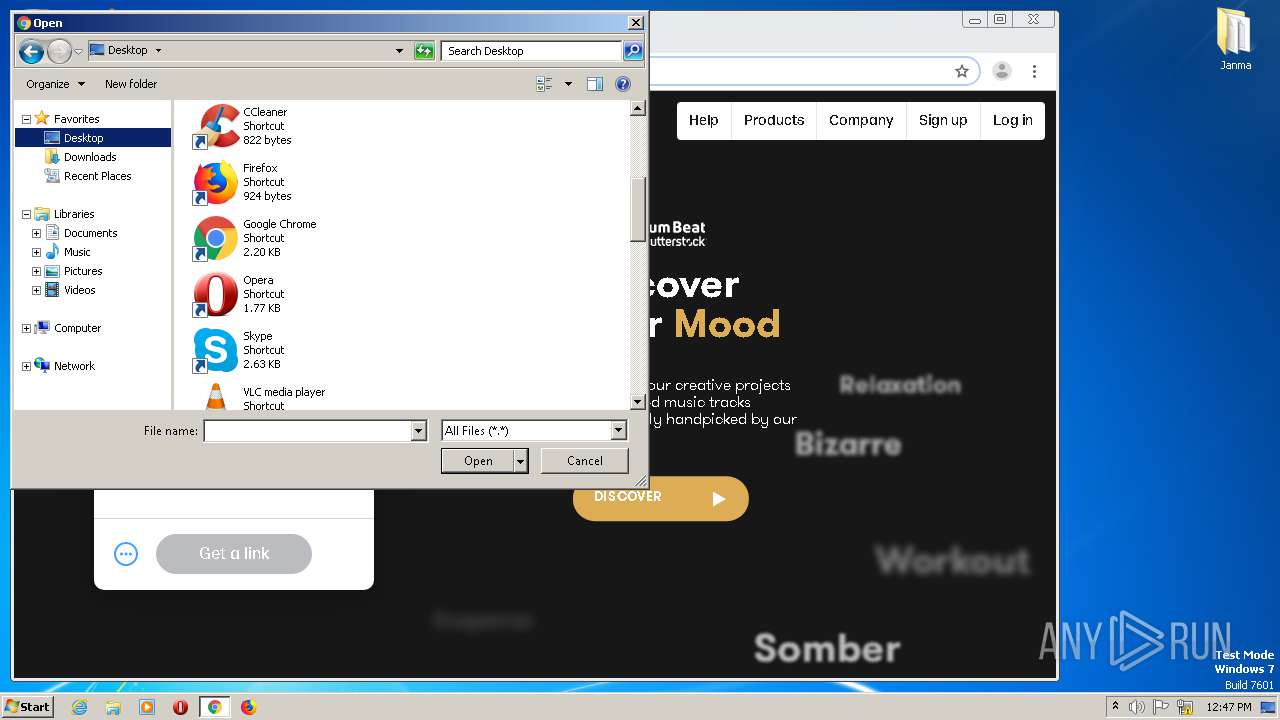
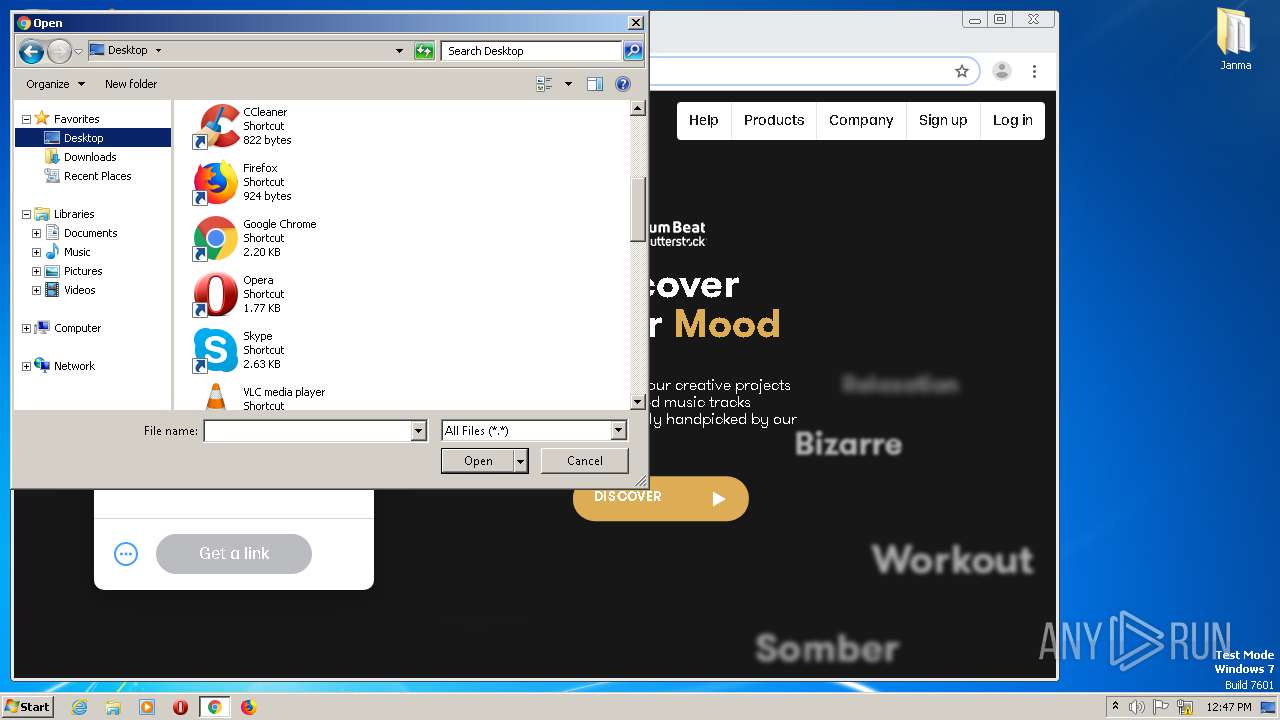
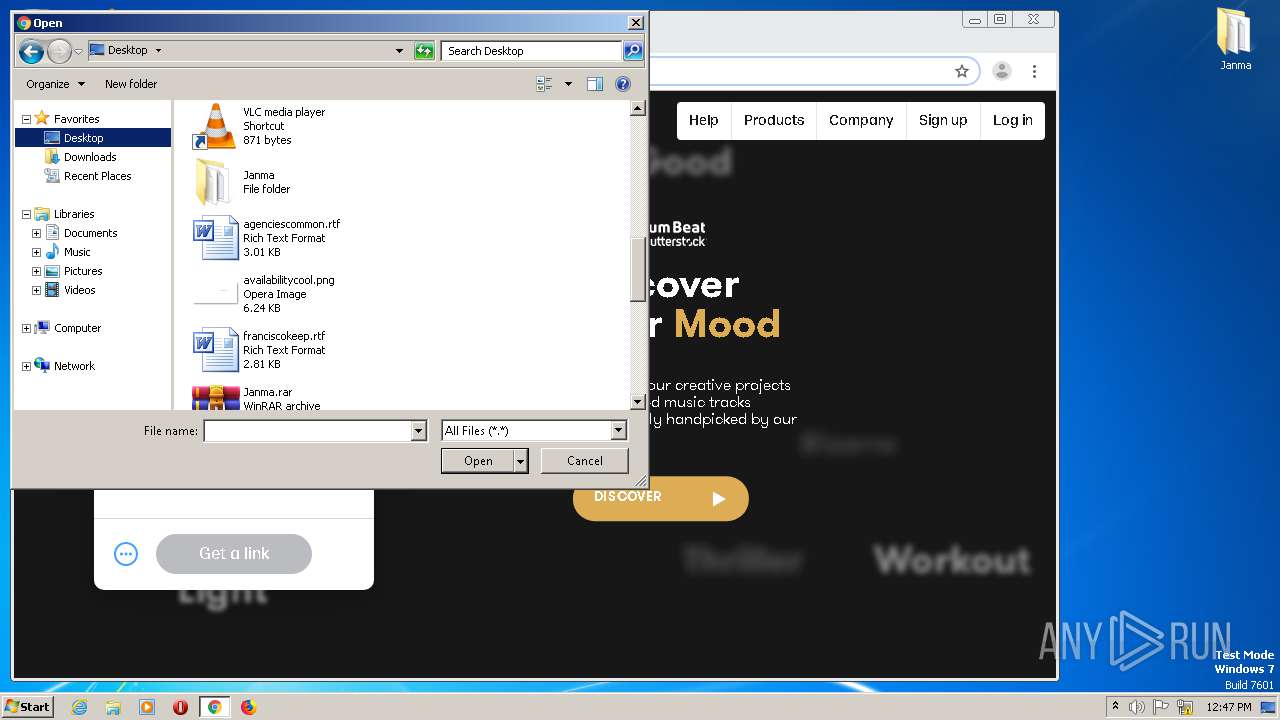
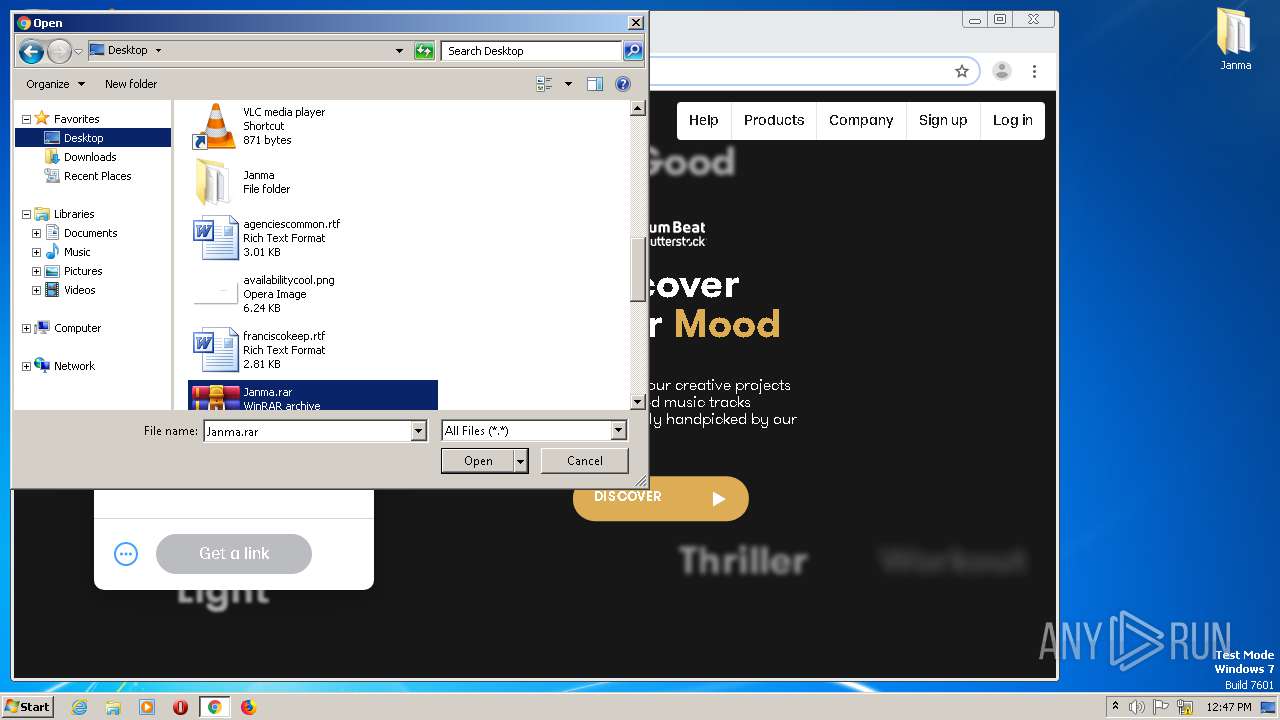
Manual execution by user
- Super Mario Bros U Deluxe.exe (PID: 2712)
- Super Mario Bros U Deluxe.exe (PID: 944)
- firefox.exe (PID: 2052)
- explorer.exe (PID: 2056)
- WinRAR.exe (PID: 1804)
- chrome.exe (PID: 1904)
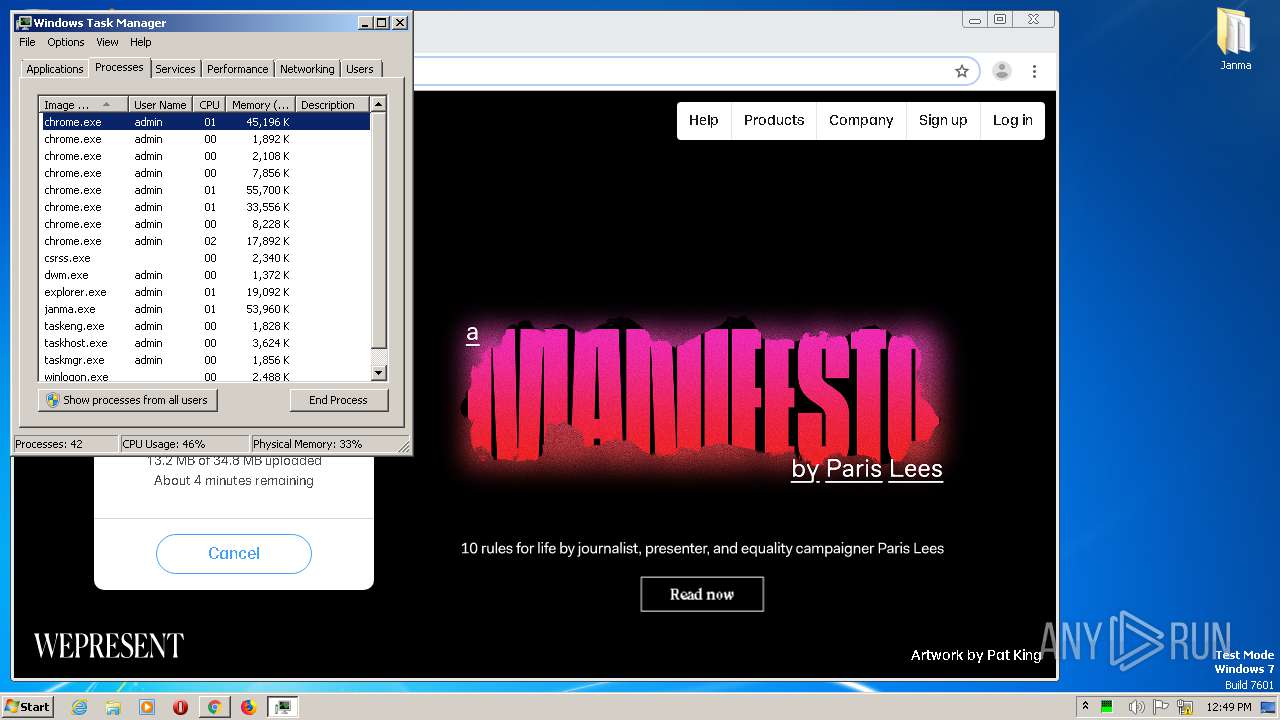
- taskmgr.exe (PID: 2056)
Creates files in the program directory
- firefox.exe (PID: 2052)
Creates files in the user directory
- firefox.exe (PID: 2052)
Application launched itself
- firefox.exe (PID: 2052)
- chrome.exe (PID: 1904)
Reads CPU info
- firefox.exe (PID: 2052)
Reads the hosts file
- chrome.exe (PID: 3604)
- chrome.exe (PID: 1904)
Reads settings of System Certificates
- chrome.exe (PID: 3604)
- pingsender.exe (PID: 2464)
- pingsender.exe (PID: 2576)
- pingsender.exe (PID: 320)
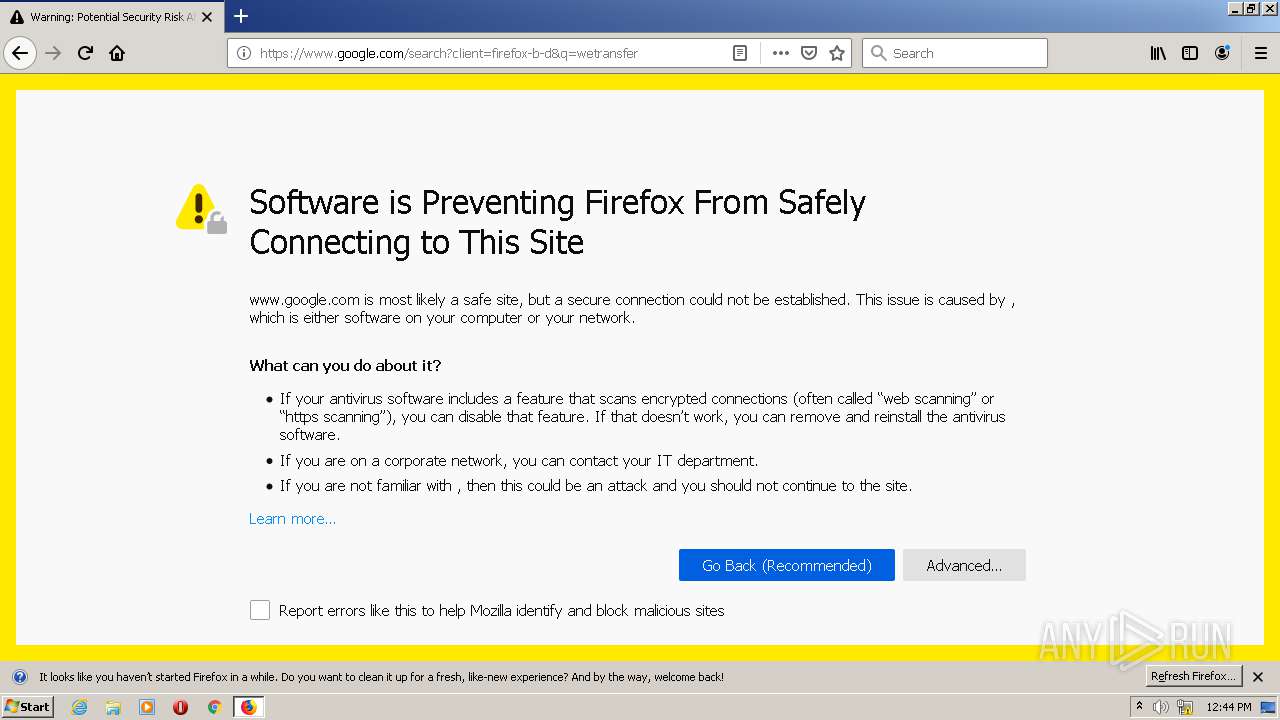
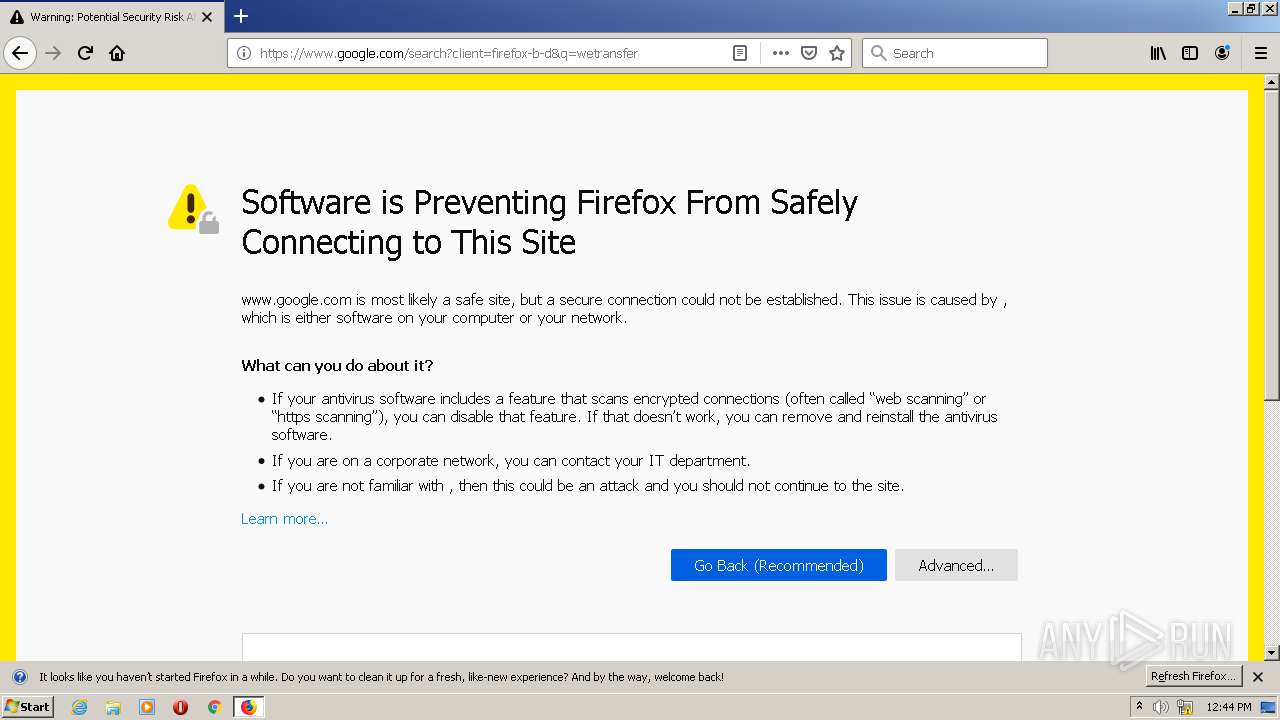
Changes settings of System certificates
- chrome.exe (PID: 3604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| ProductVersion: | 5.0.6 |
|---|---|
| ProductName: | Janma |
| OriginalFileName: | |
| LegalCopyright: | |
| FileVersion: | |
| FileDescription: | Janma Setup |
| CompanyName: | LGN Software |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | 6 |
| OSVersion: | 6 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 118784 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2020:05:21 07:56:23+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-May-2020 05:56:23 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | LGN Software |
| FileDescription: | Janma Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | Janma |
| ProductVersion: | 5.0.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 21-May-2020 05:56:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B3604 | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35433 |
.itext | 0x000B5000 | 0x00001684 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.9709 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.04216 |
.bss | 0x000BB000 | 0x00006DA0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x000180C0 | 0x00018200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.08525 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.18154 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.94492 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.21225 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.24039 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054058 |
Total processes
182
Monitored processes
87
Malicious processes
20
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Janma\msg.exe" | C:\Users\admin\AppData\Local\Janma\msg.exe | — | Super Mario Bros U Deluxe.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 284 | "C:\Users\admin\Desktop\Super Mario Bros U Deluxe.exe" /SILENT | C:\Users\admin\Desktop\Super Mario Bros U Deluxe.exe | Super Mario Bros U Deluxe.tmp | ||||||||||||
User: admin Company: LGN Software Integrity Level: MEDIUM Description: Janma Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 320 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/0672b7f4-25e4-45bd-9f1a-df2a590358c8/main/Firefox/67.0.4/release/20190619235627?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nltxvmn2.default\saved-telemetry-pings\0672b7f4-25e4-45bd-9f1a-df2a590358c8 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 372 | "C:\Users\admin\AppData\Local\Temp\is-7VGME.tmp\Super Mario Bros U Deluxe.tmp" /SL5="$30196,30754933,861184,C:\Users\admin\Desktop\Super Mario Bros U Deluxe.exe" /SILENT | C:\Users\admin\AppData\Local\Temp\is-7VGME.tmp\Super Mario Bros U Deluxe.tmp | Super Mario Bros U Deluxe.exe | ||||||||||||
User: admin Company: LGN Software Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 5 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2052.3.642934680\1178501938" -childID 1 -isForBrowser -prefsHandle 1800 -prefMapHandle 1784 -prefsLen 1 -prefMapSize 188894 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2052 "\\.\pipe\gecko-crash-server-pipe.2052" 1808 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 760 | "C:\Program Files (x86)\Google\Temp\GUM739D.tmp\GoogleUpdate.exe" /install "runtime=true&needsadmin=true" /installsource chromerecovery /silent | C:\Program Files (x86)\Google\Temp\GUM739D.tmp\GoogleUpdate.exe | — | GoogleUpdateSetup.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Installer Exit code: 0 Version: 1.3.36.81 Modules
| |||||||||||||||
| 888 | "C:\Users\admin\AppData\Local\Temp\is-5V85U.tmp\Super Mario Bros U Deluxe.tmp" /SL5="$20196,30754933,861184,C:\Users\admin\Desktop\Super Mario Bros U Deluxe.exe" | C:\Users\admin\AppData\Local\Temp\is-5V85U.tmp\Super Mario Bros U Deluxe.tmp | — | Super Mario Bros U Deluxe.exe | |||||||||||
User: admin Company: LGN Software Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 944 | "C:\Users\admin\Desktop\Super Mario Bros U Deluxe.exe" | C:\Users\admin\Desktop\Super Mario Bros U Deluxe.exe | Explorer.EXE | ||||||||||||
User: admin Company: LGN Software Integrity Level: MEDIUM Description: Janma Setup Exit code: 1 Version: Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11961077408328624371,15164670362701732314,131072 --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15510771575820925300 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4104 /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11961077408328624371,15164670362701732314,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15099001419083184609 --mojo-platform-channel-handle=3856 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
8 275
Read events
7 573
Write events
636
Delete events
66
Modification events
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 740B0000EEF30392BE5ED701 | |||
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: BF50DC6A1EBDE8C44074CC90F2AA39415F24BB234D792AF41DF6D315F588863E | |||
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: BF50DC6A1EBDE8C44074CC90F2AA39415F24BB234D792AF41DF6D315F588863E | |||
| (PID) Process: | (2932) Super Mario Bros U Deluxe.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 740B0000EEF30392BE5ED701 | |||
Executable files
912
Suspicious files
117
Text files
6 897
Unknown types
79
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
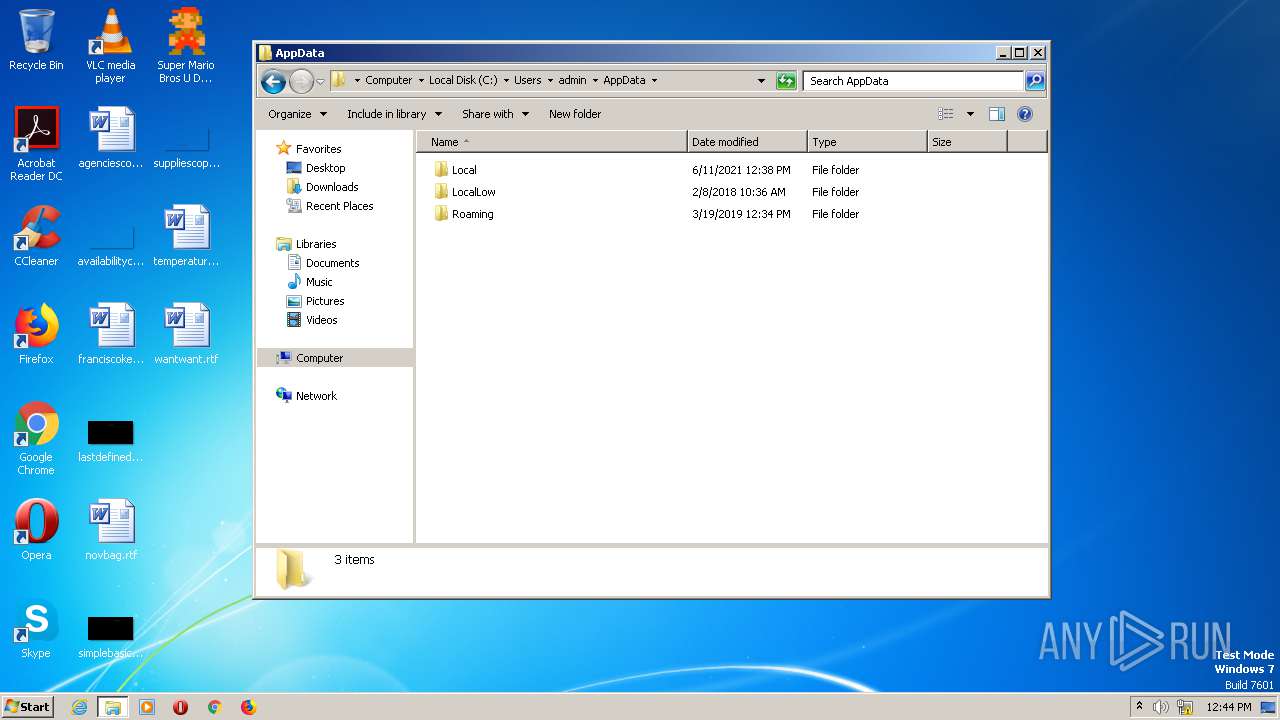
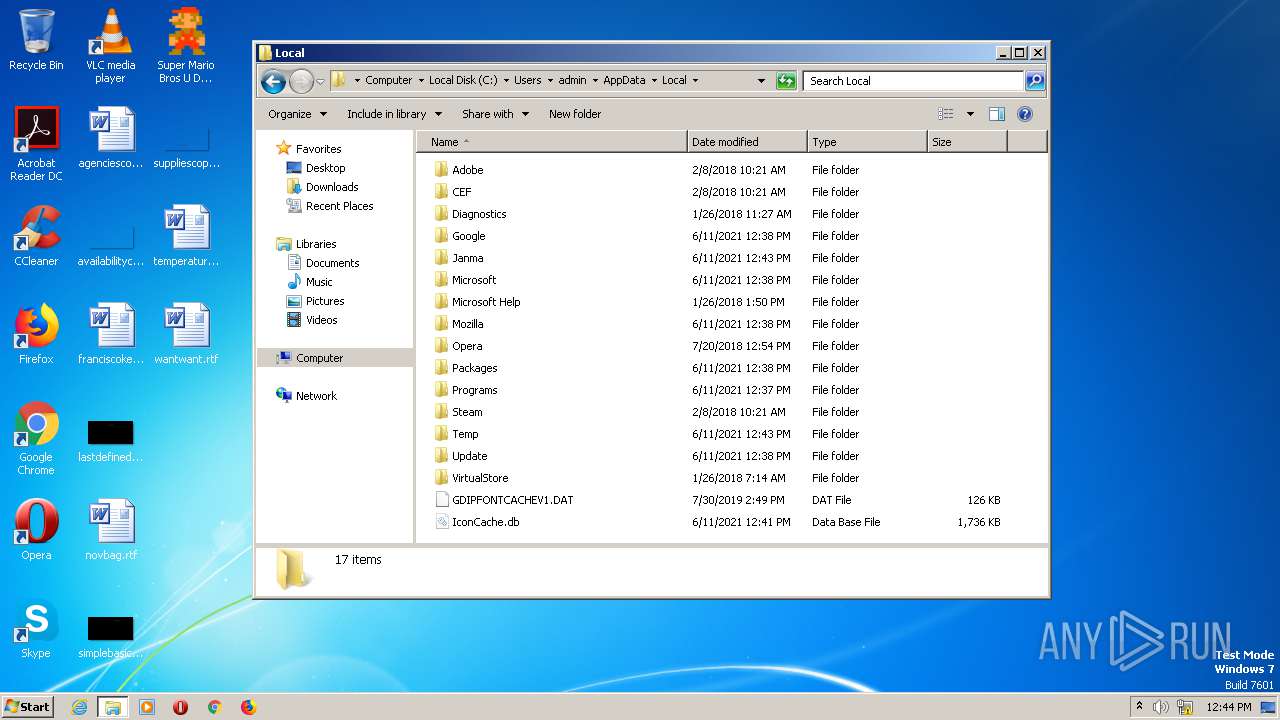
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\is-DDOL5.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\is-36FPN.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\janma.exe | — | |
MD5:— | SHA256:— | |||
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\is-LOPOP.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\is-HM2TB.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\is-D2D2E.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\is-JNM35.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\is-R7QB0.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\is-V1B7C.tmp | — | |
MD5:— | SHA256:— | |||
| 2484 | Super Mario Bros U Deluxe.tmp | C:\Users\admin\AppData\Local\Janma\is-EAHVG.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
299
TCP/UDP connections
234
DNS requests
150
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
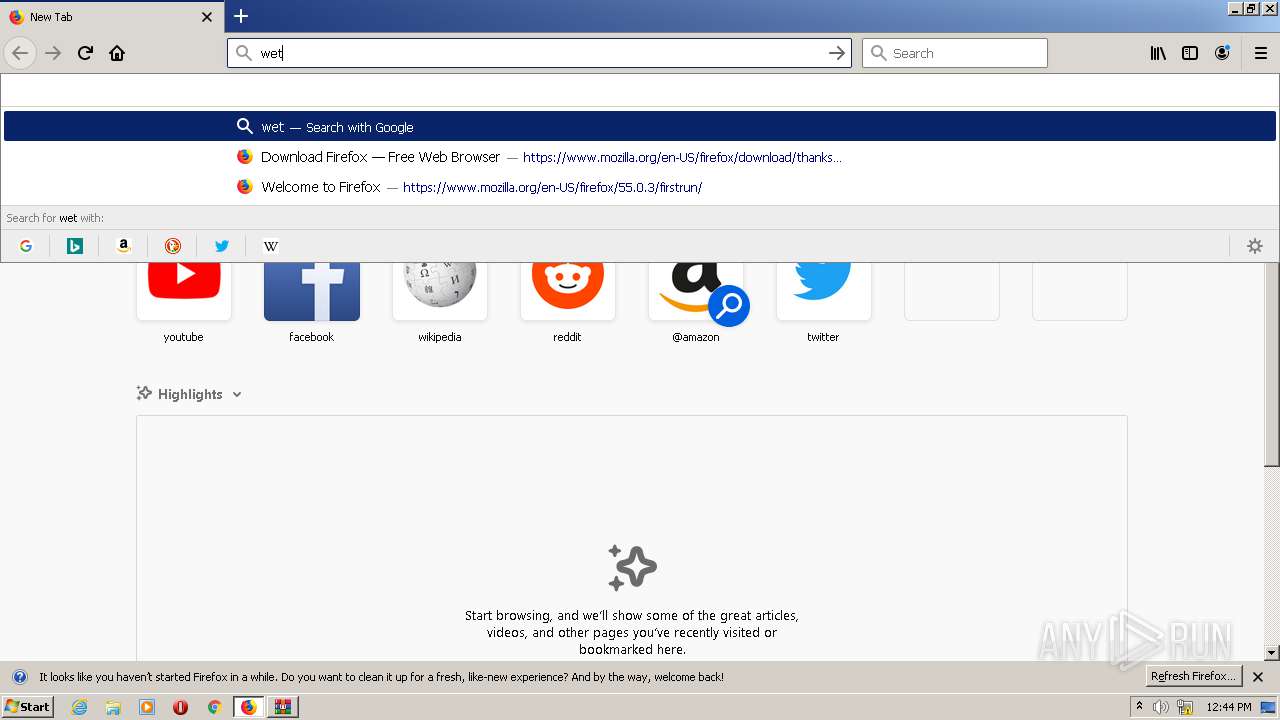
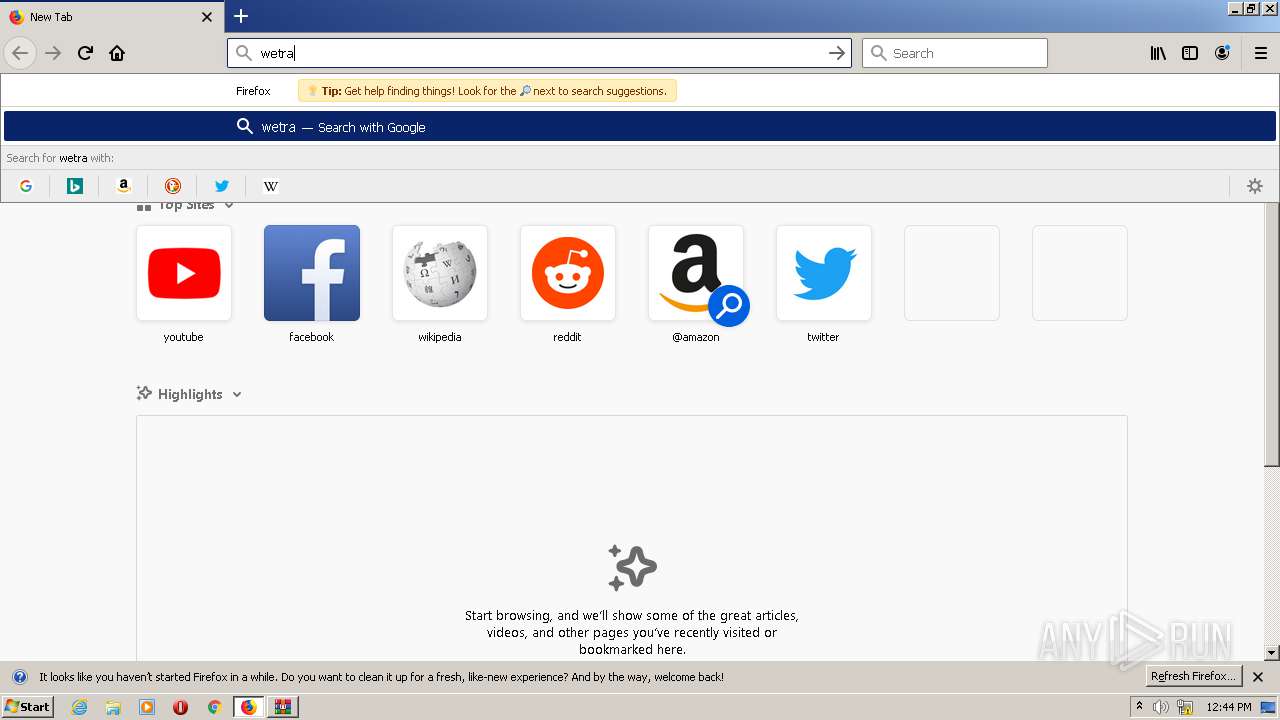
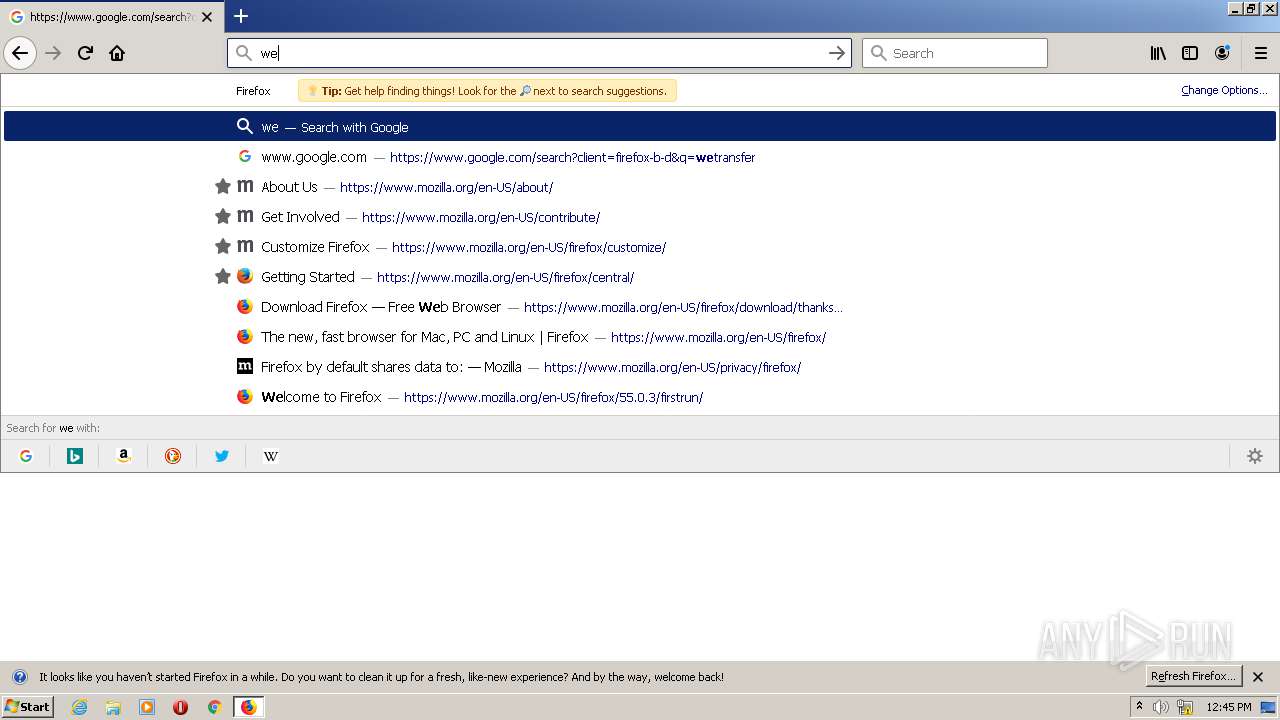
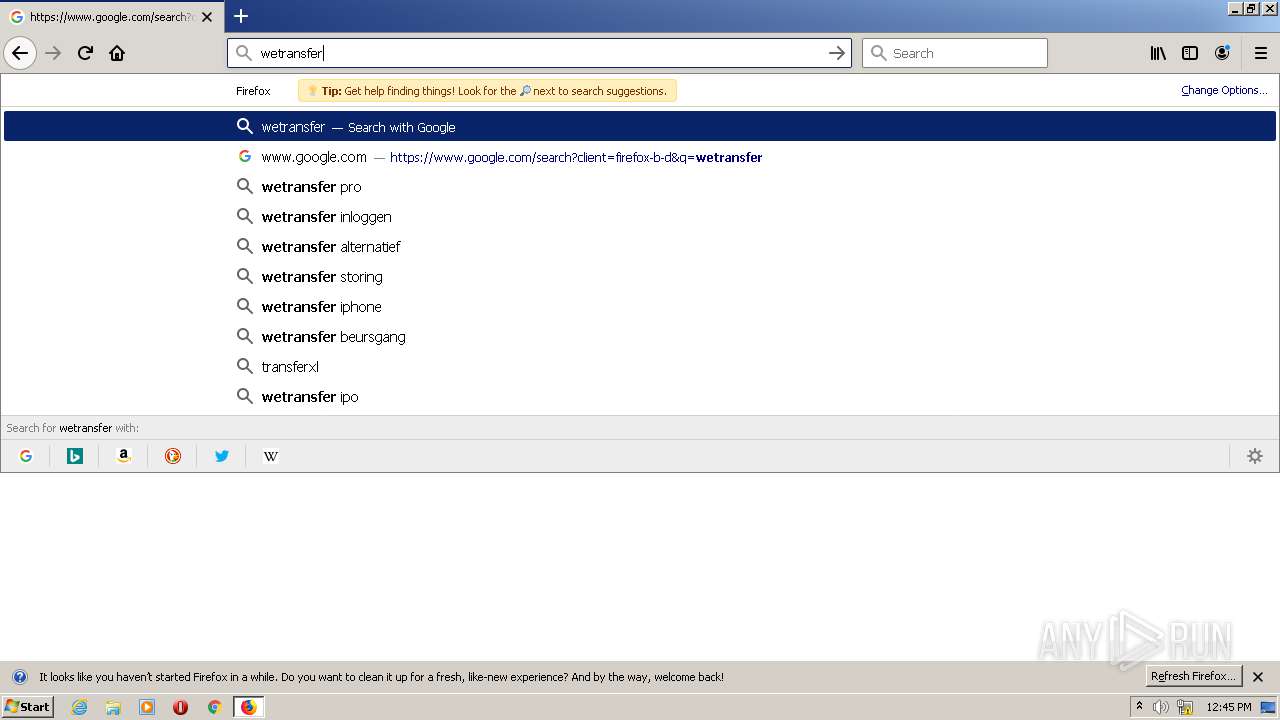
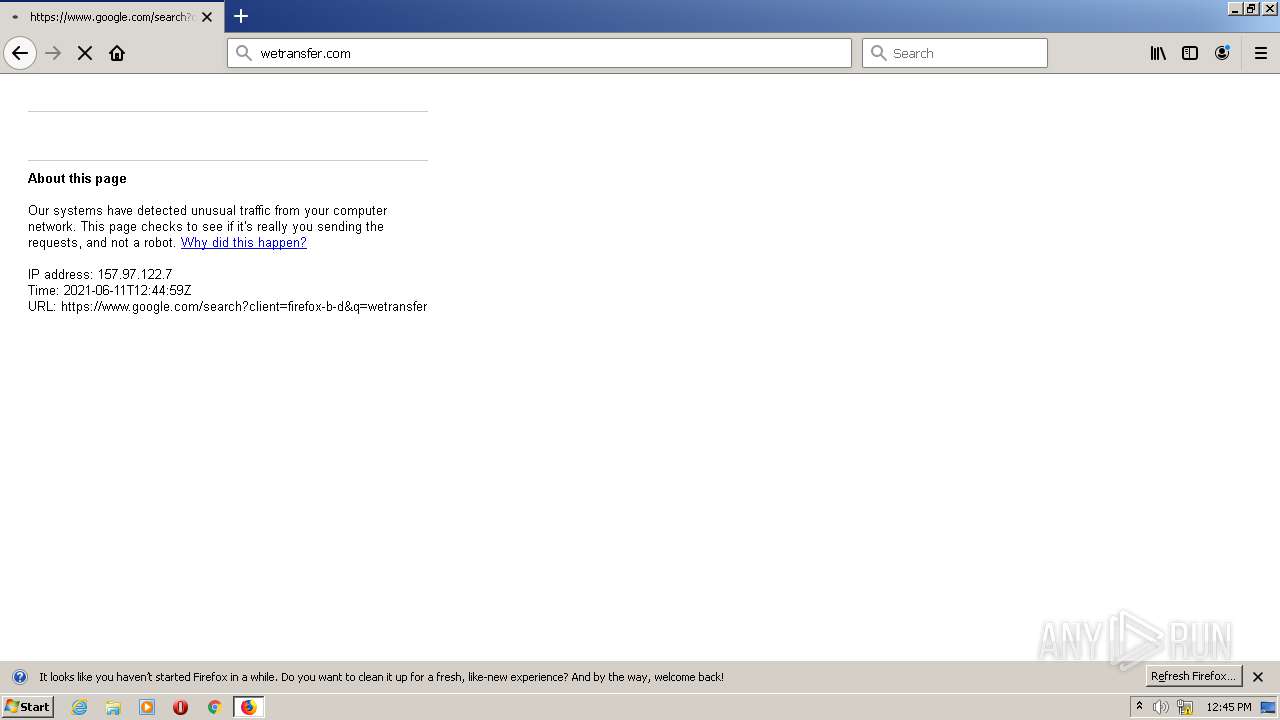
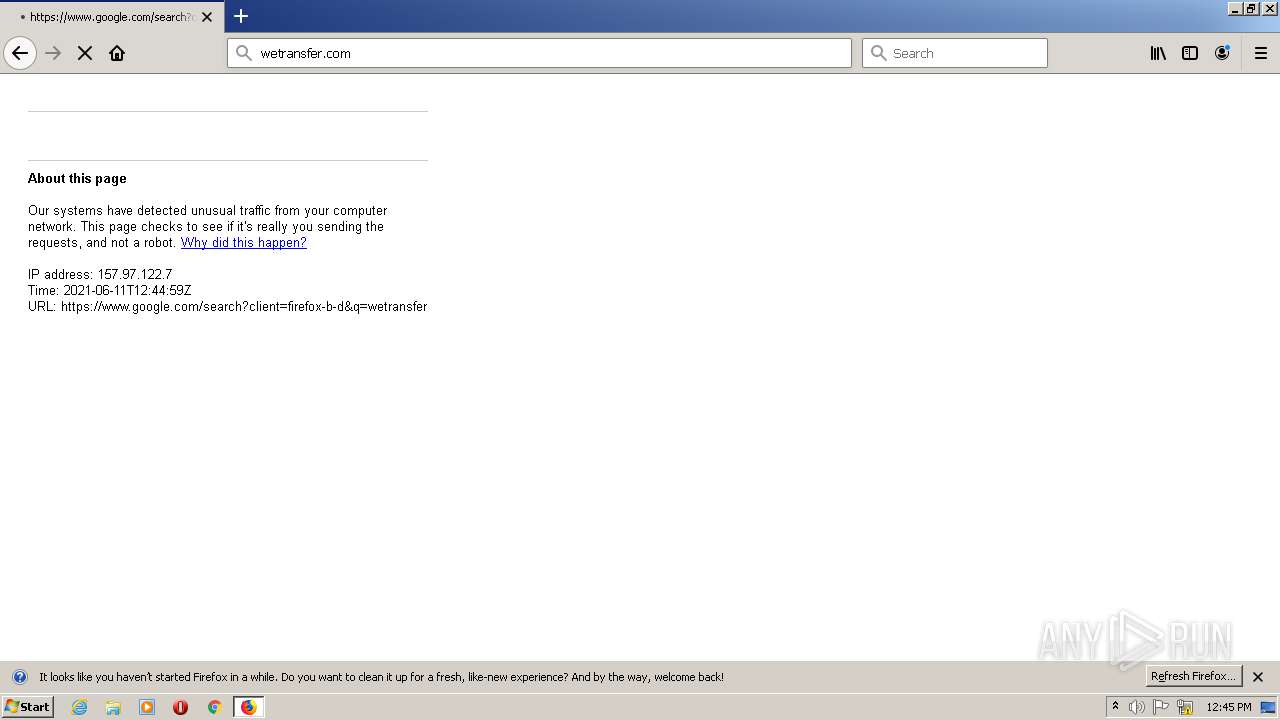
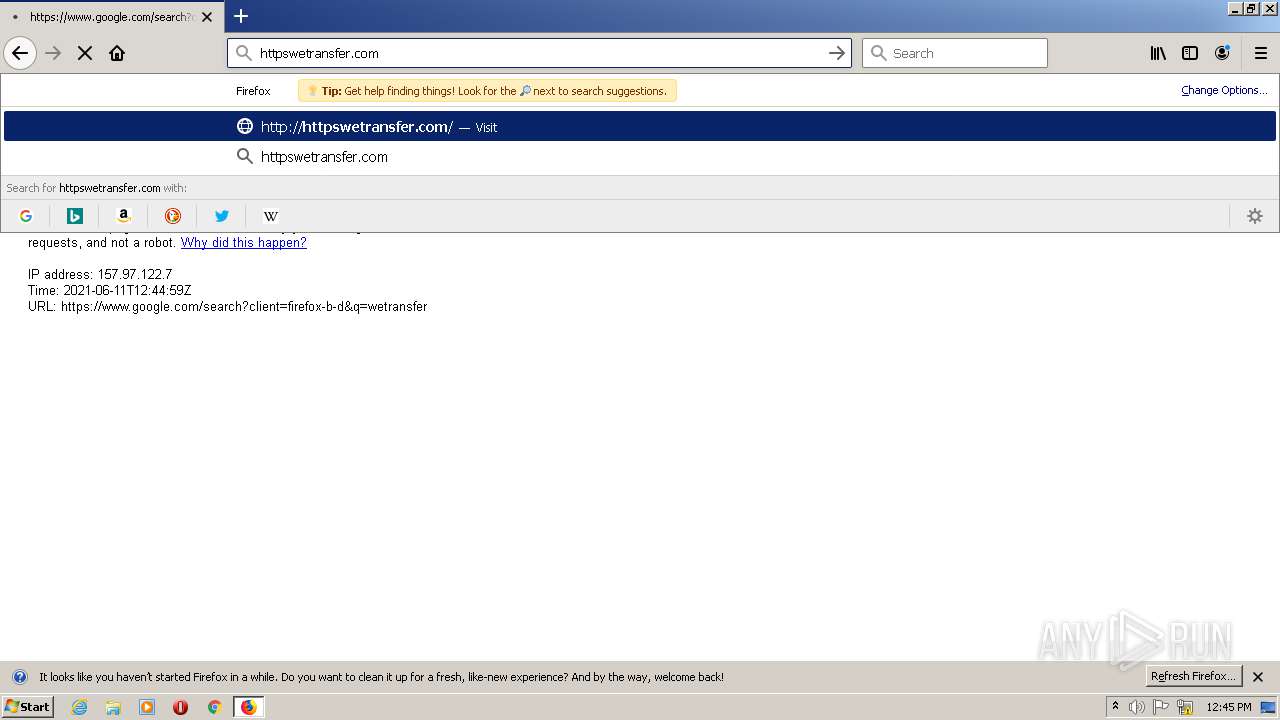
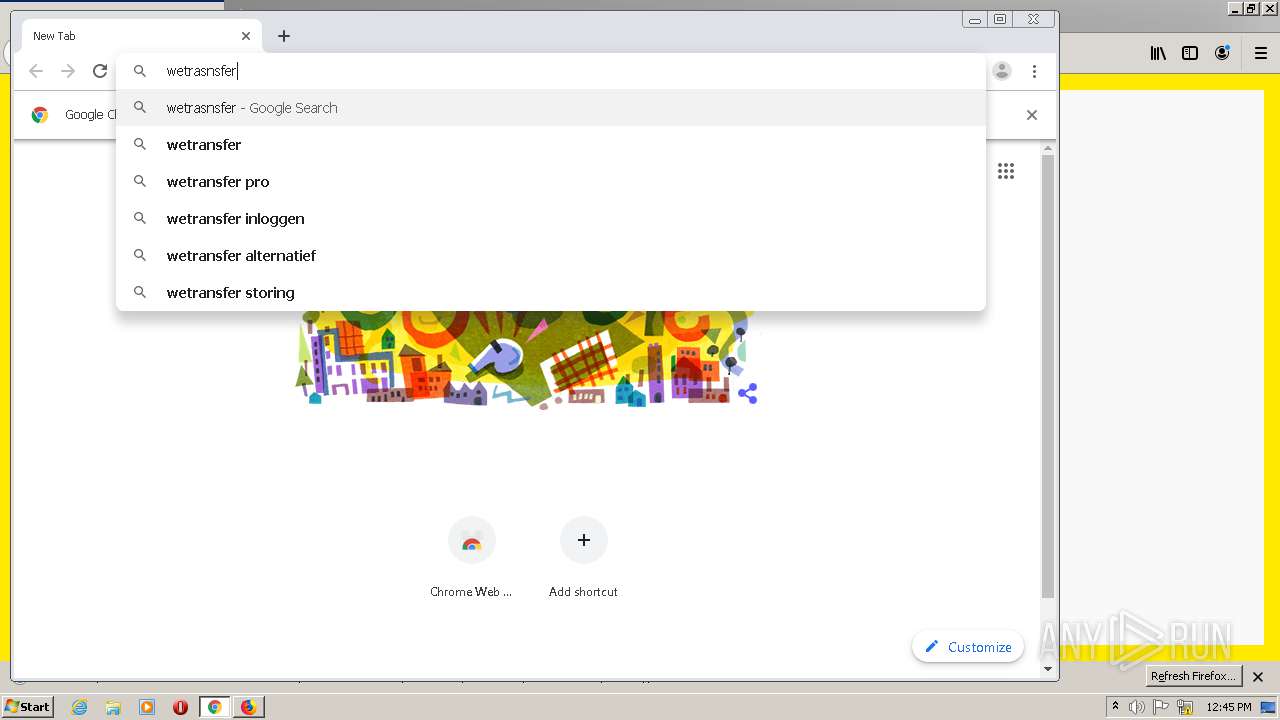
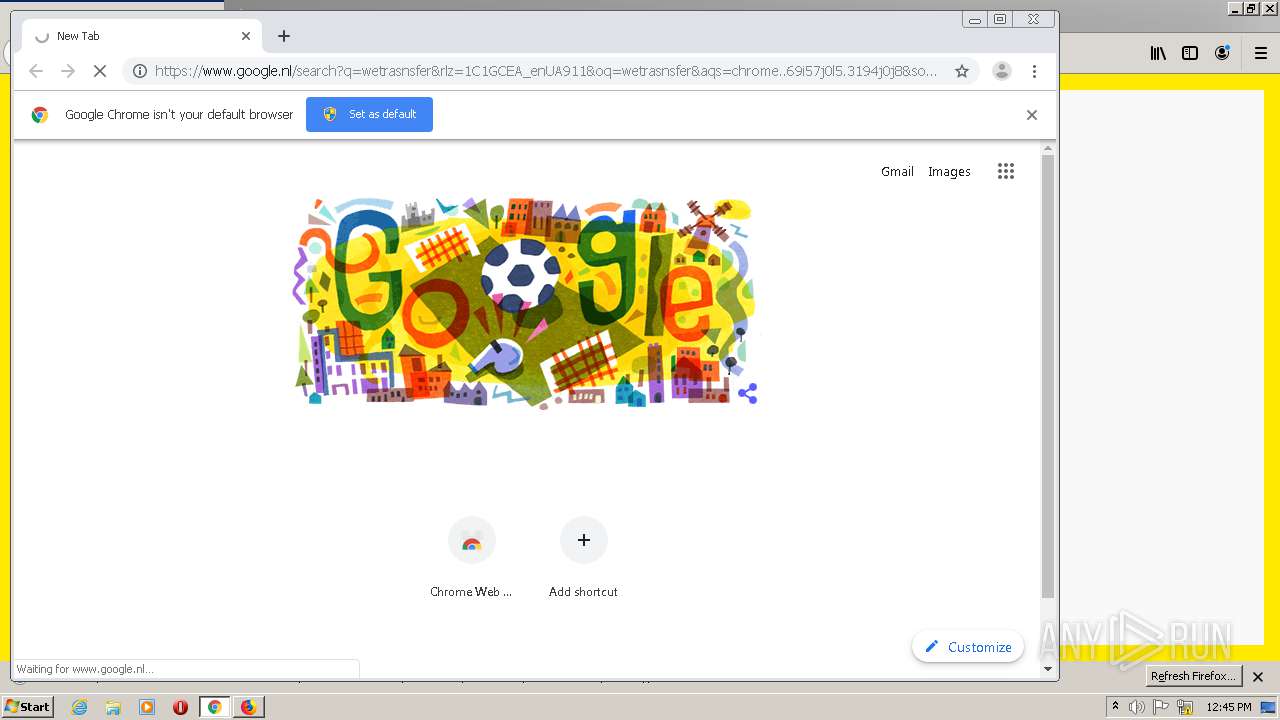
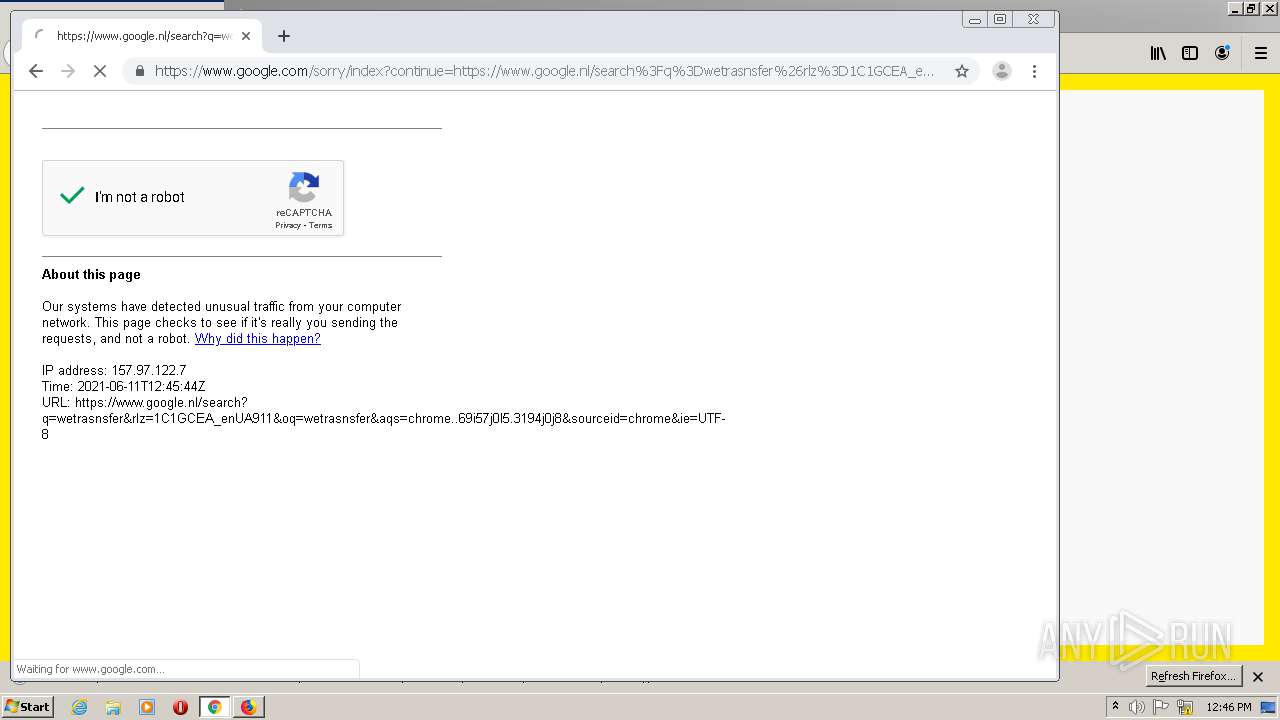
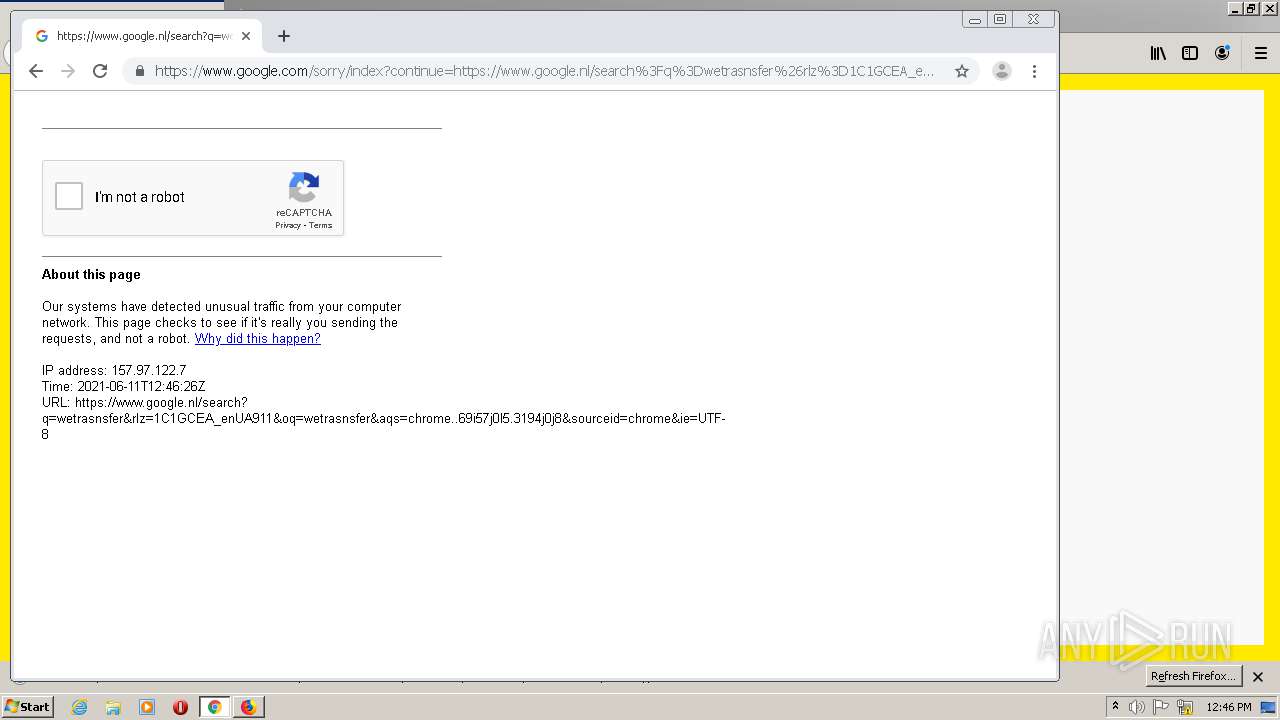
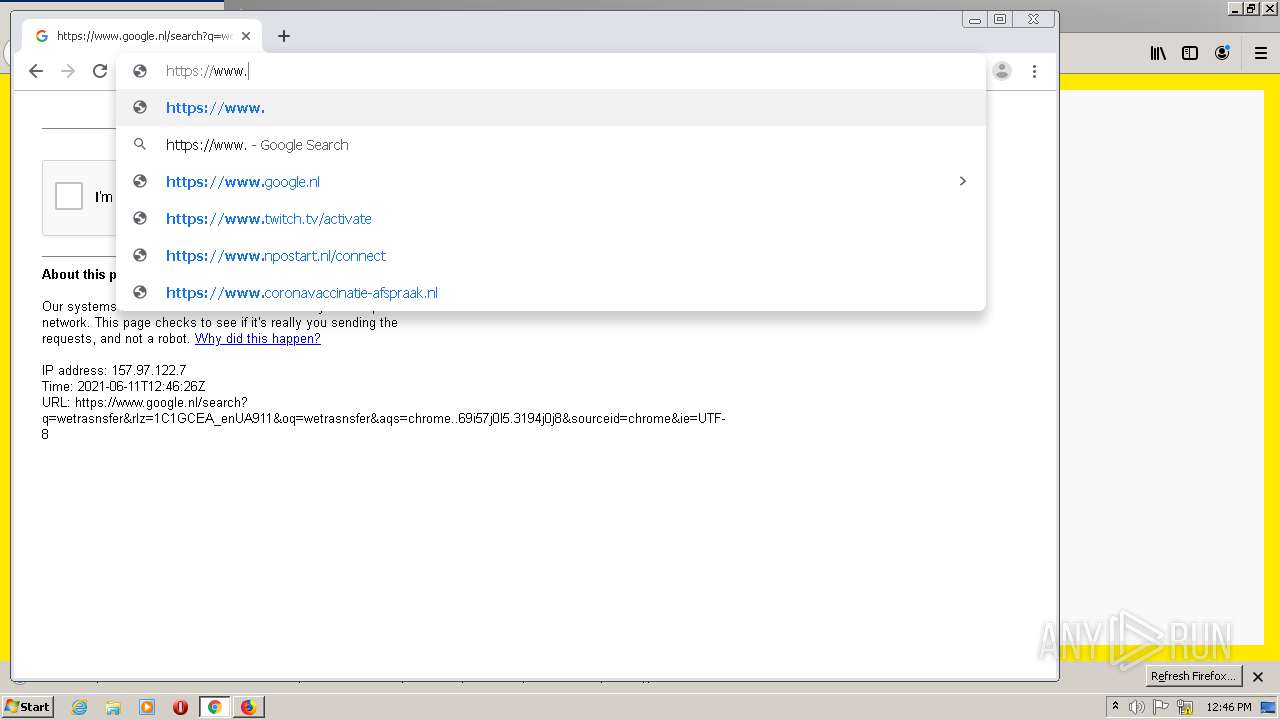
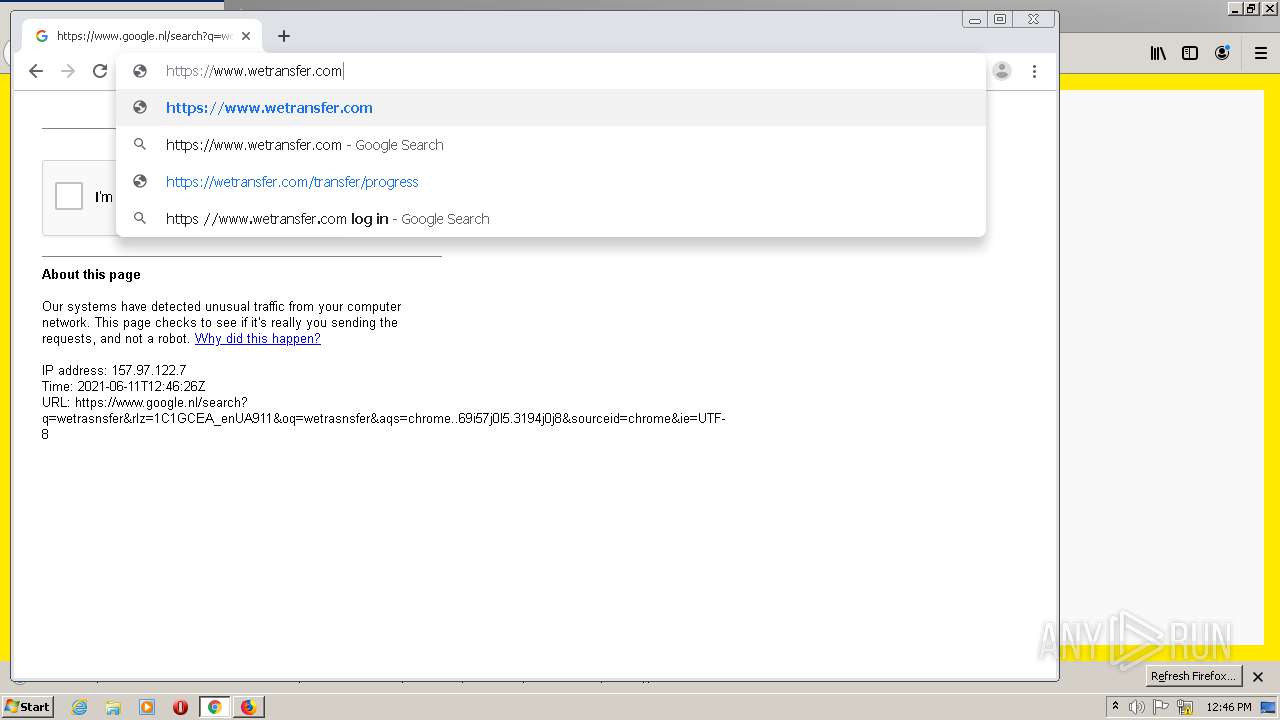
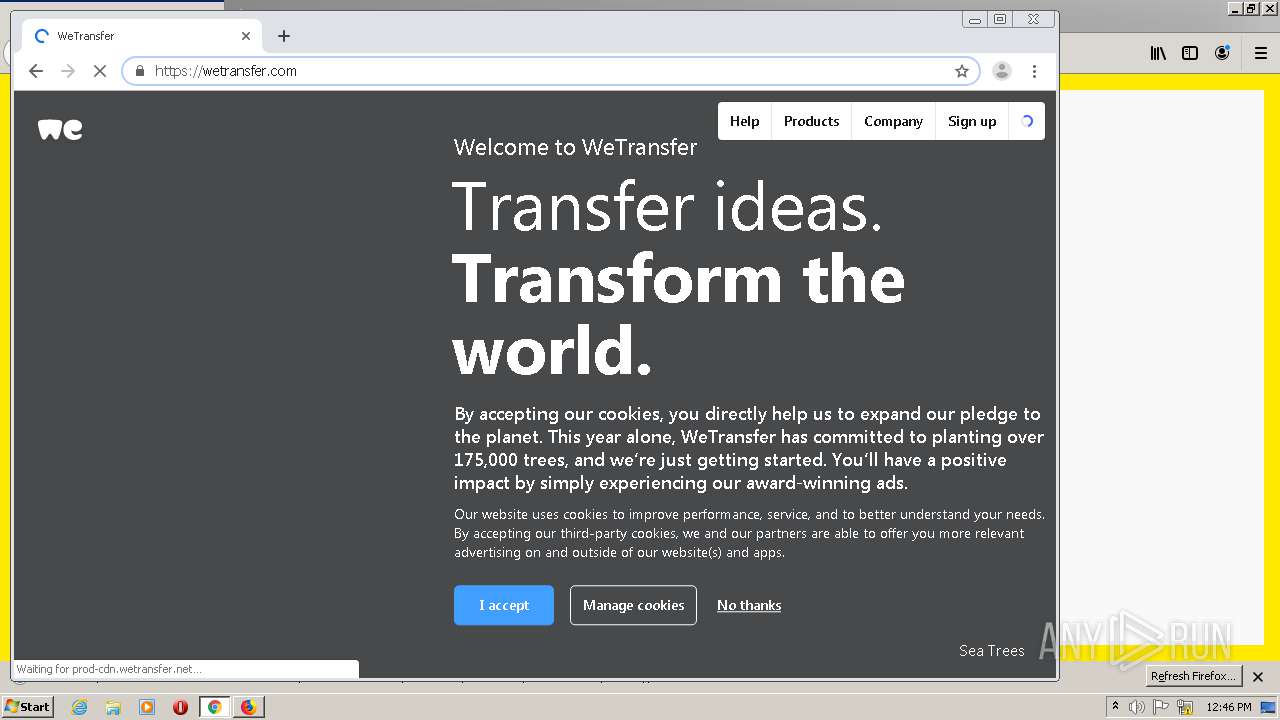
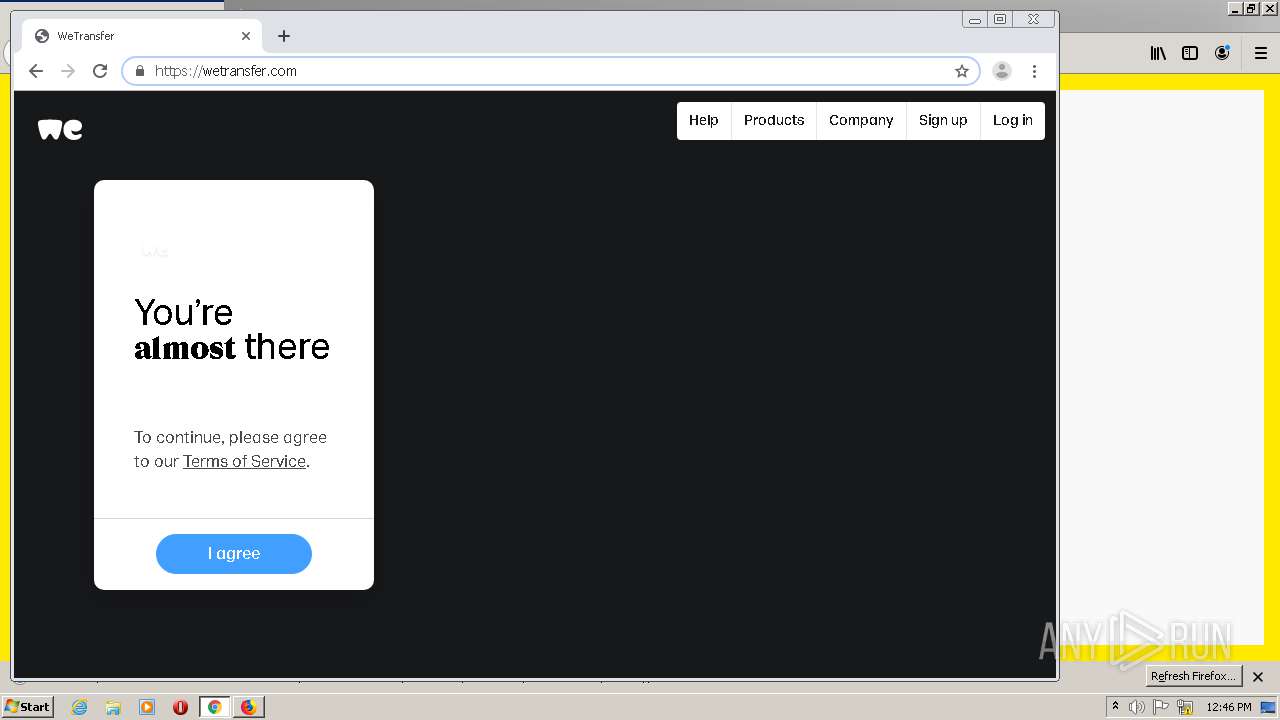
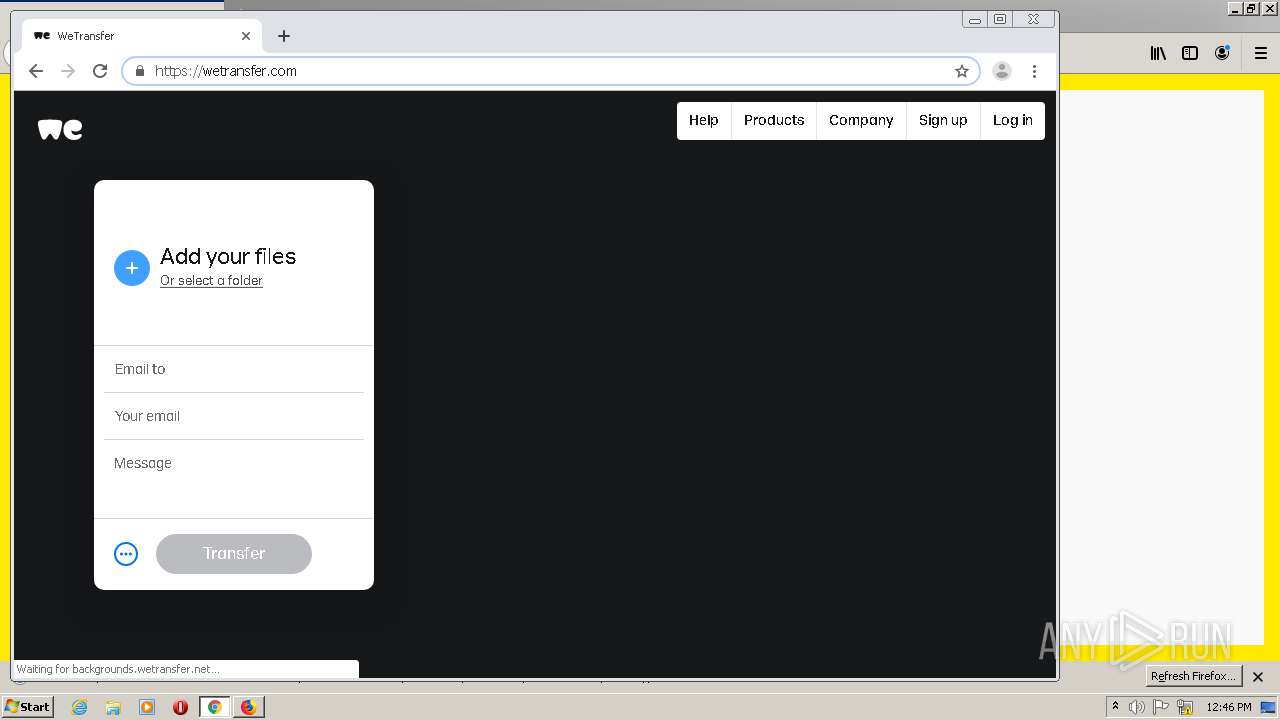
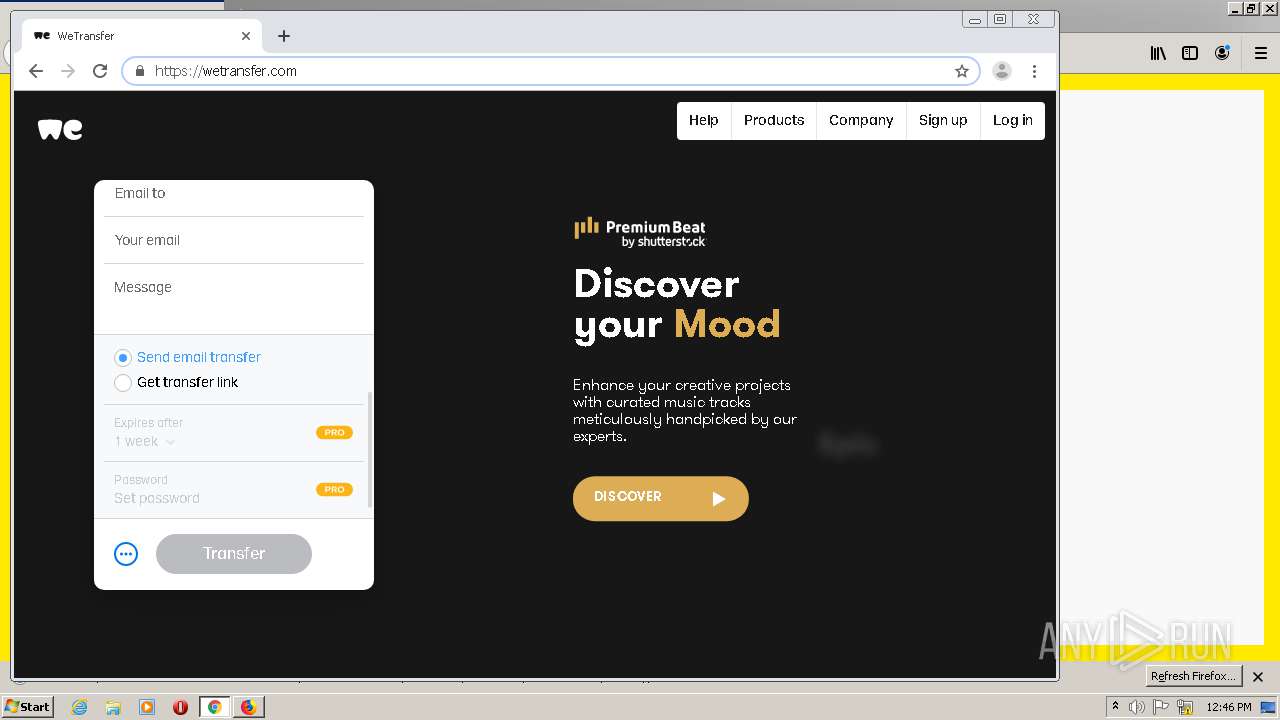
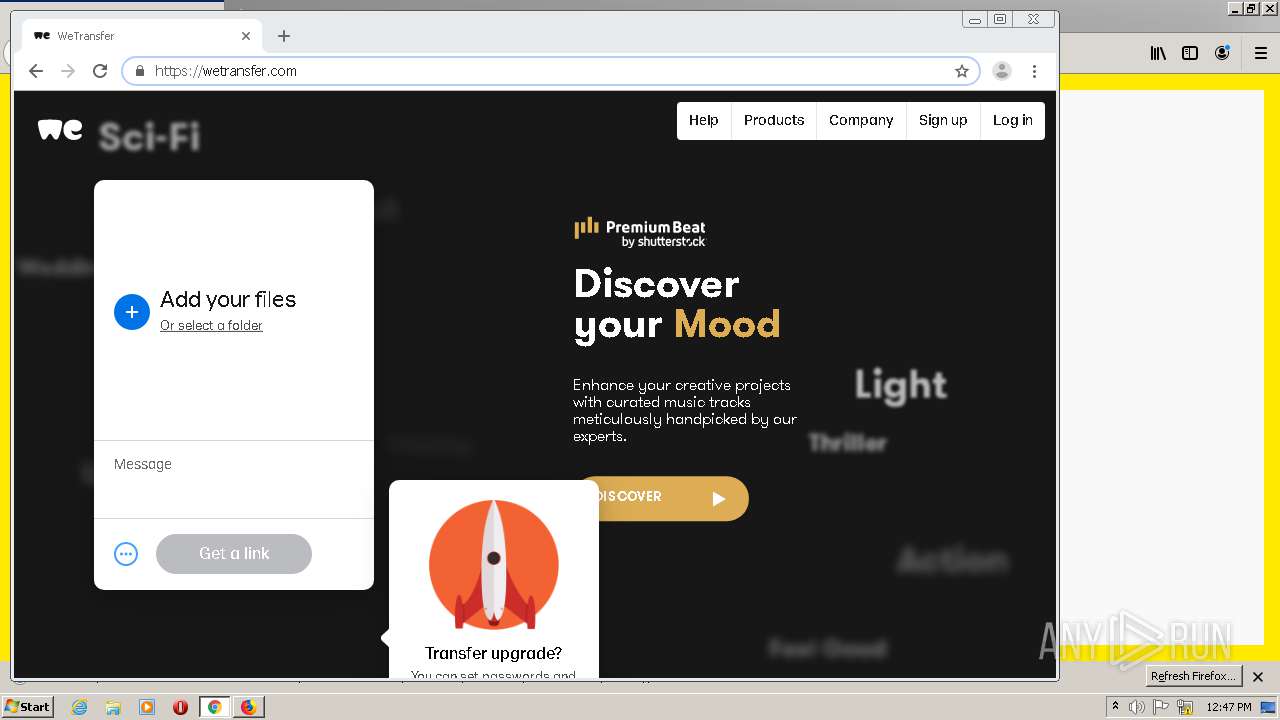
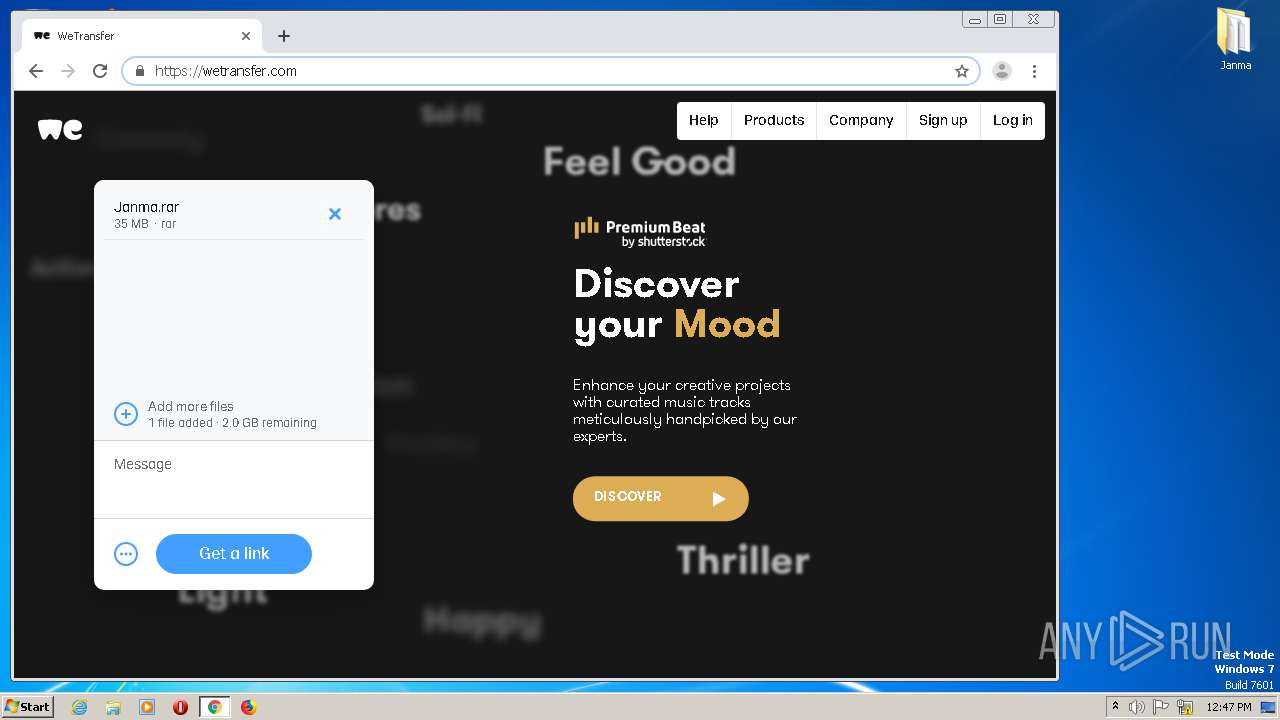
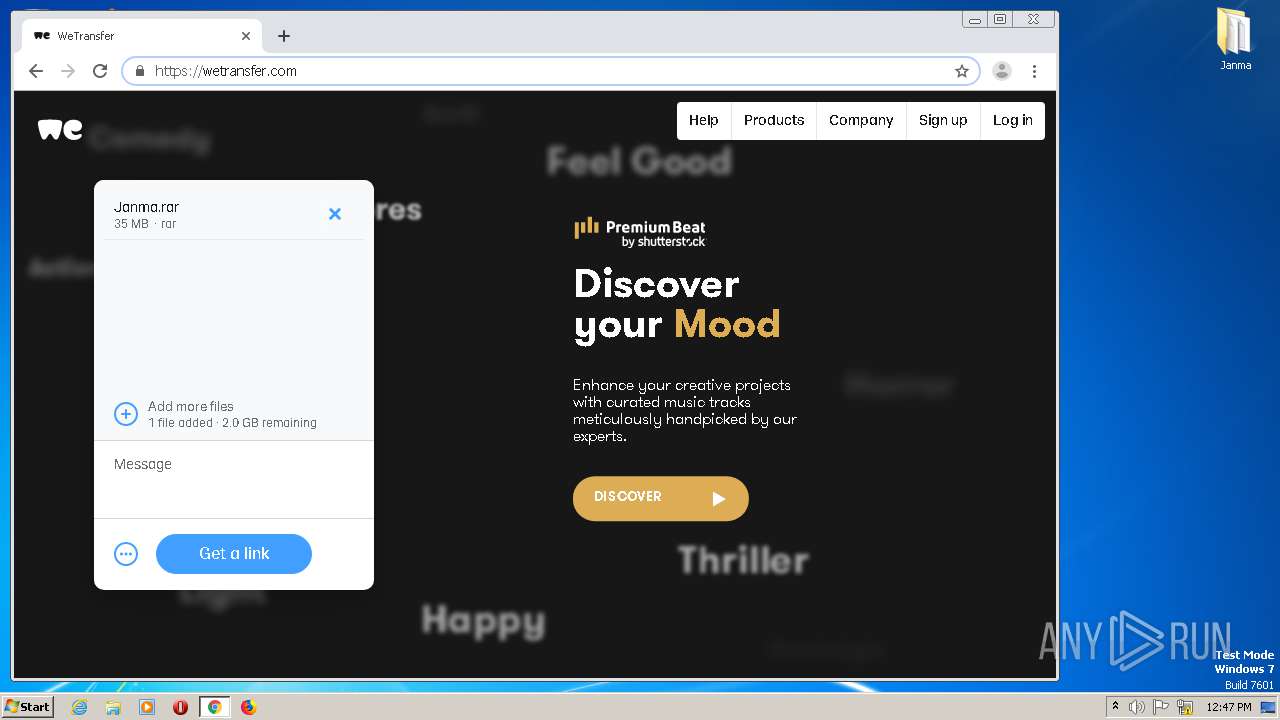
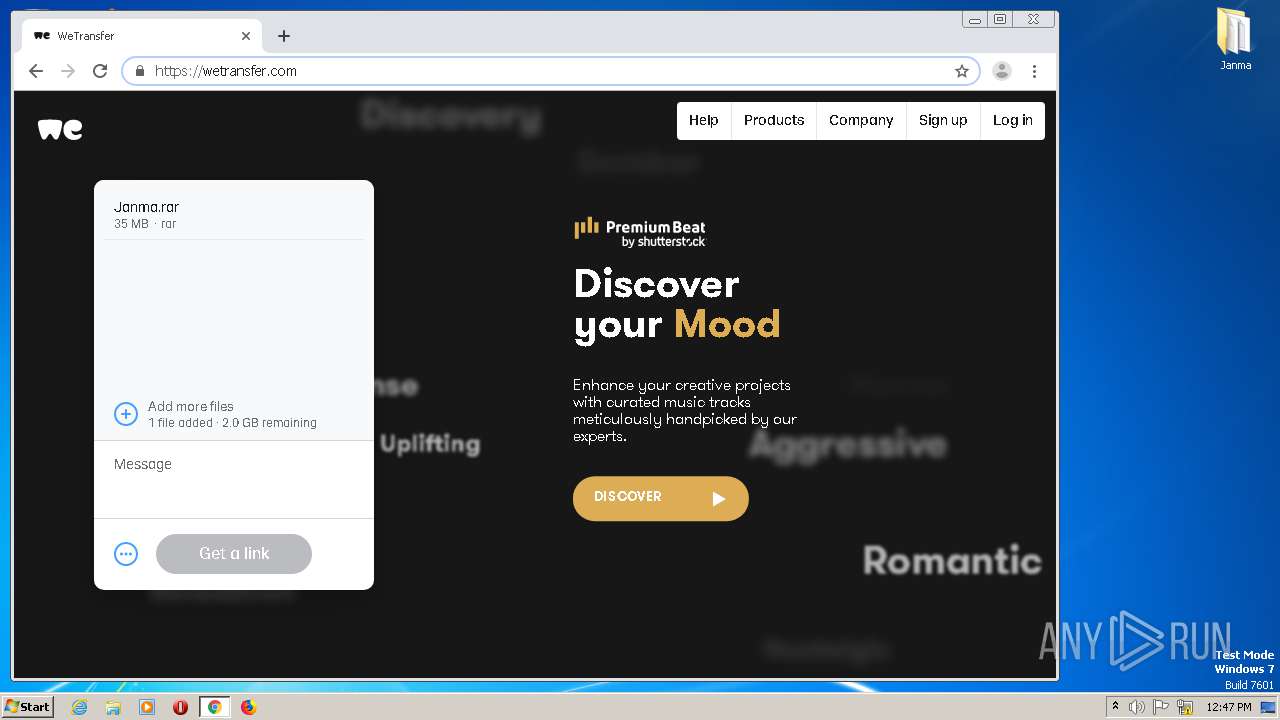
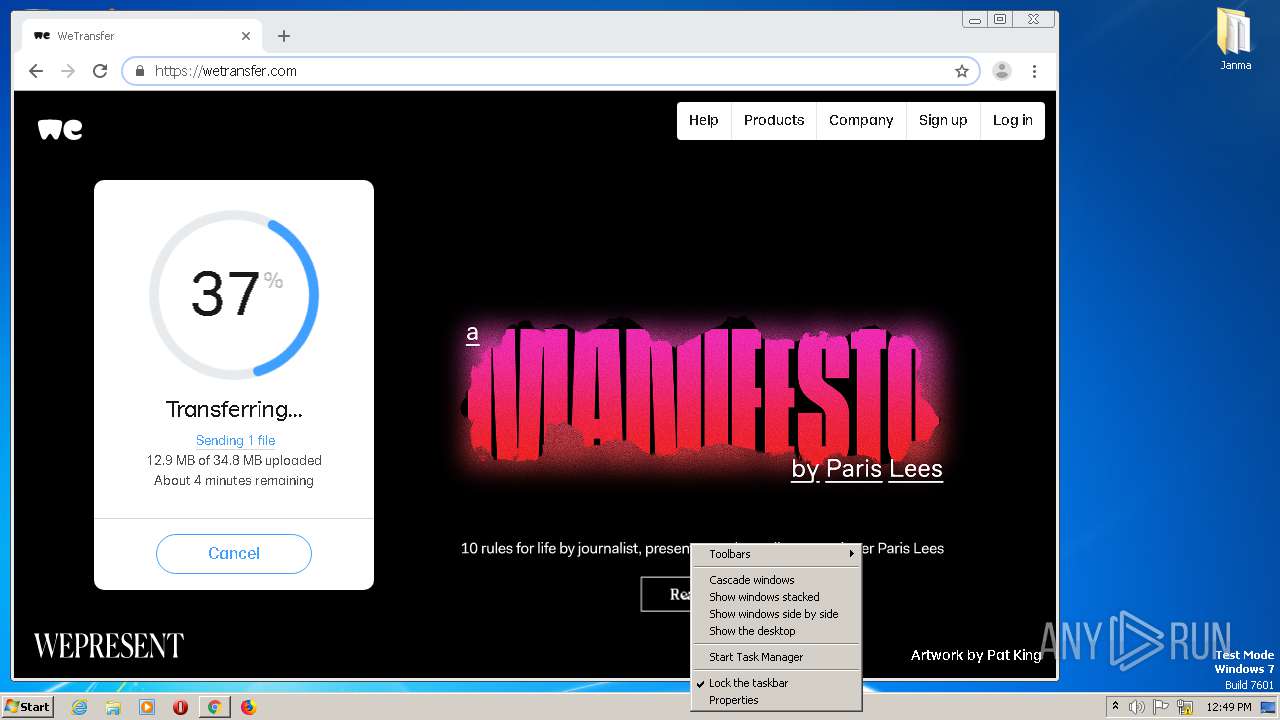
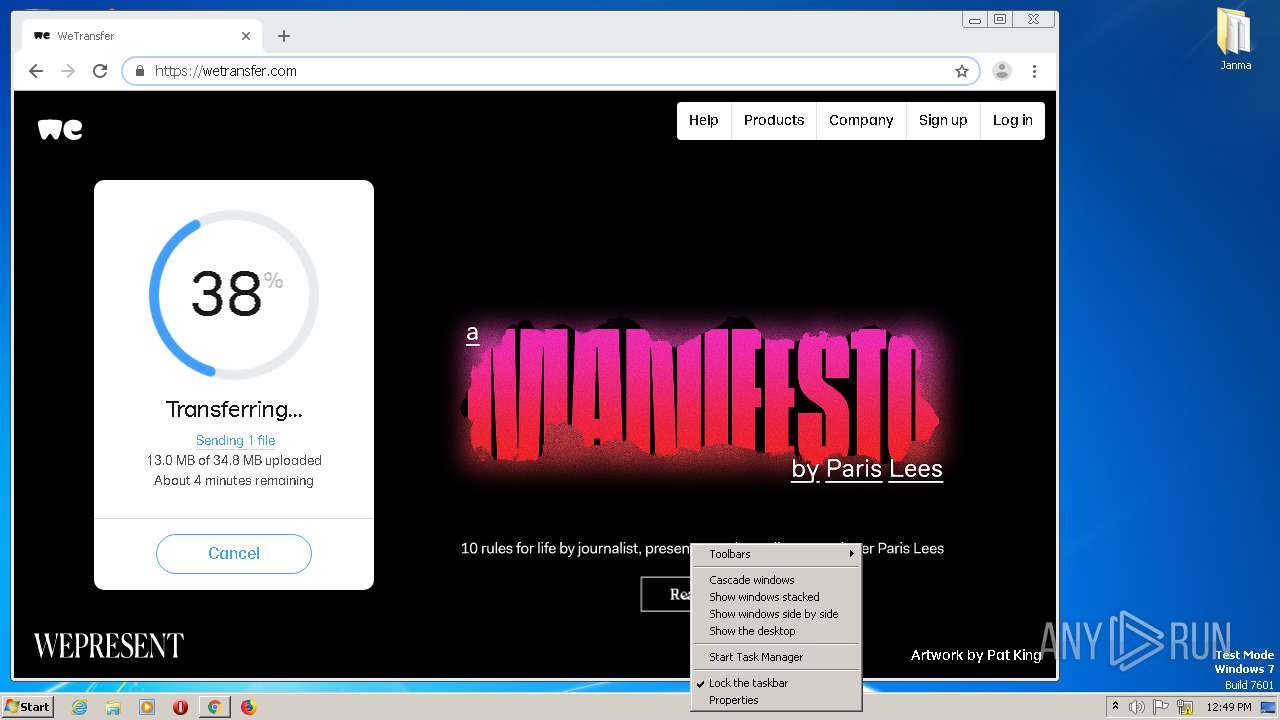
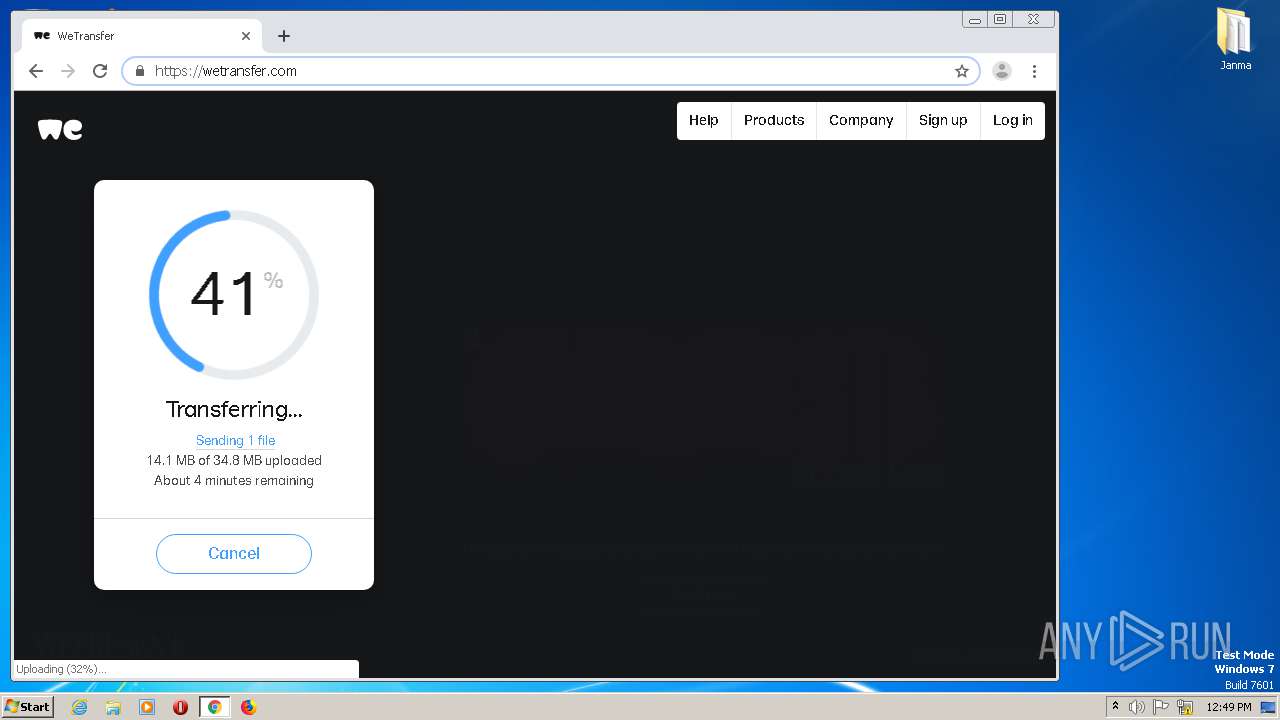
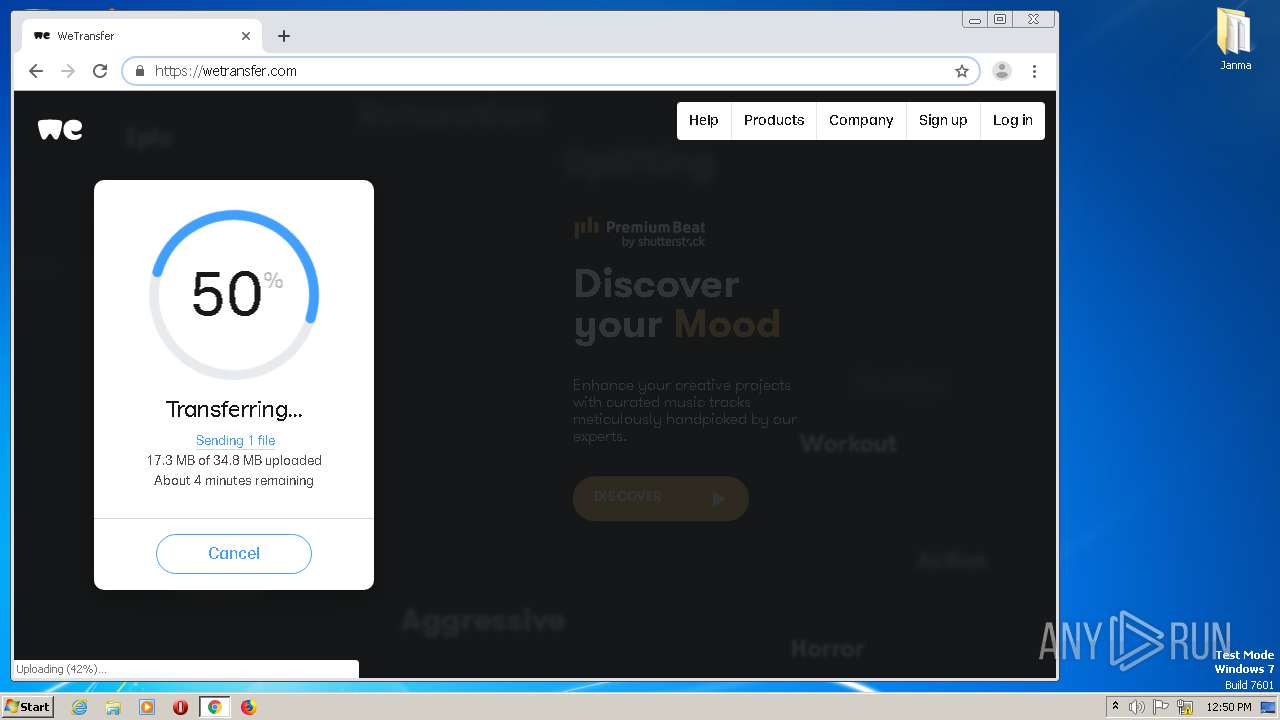
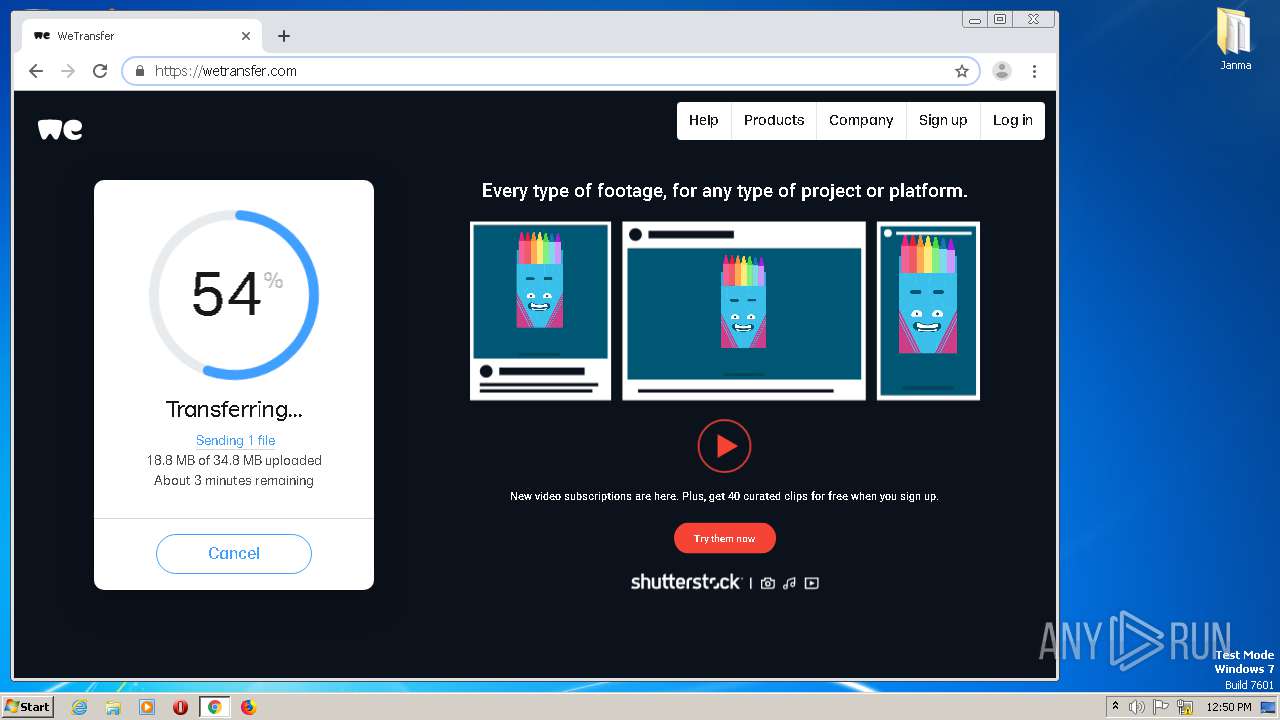
2052 | firefox.exe | GET | 301 | 54.216.161.59:80 | http://wetransfer.com/ | IE | — | — | shared |
2052 | firefox.exe | GET | 200 | 142.250.185.68:443 | https://www.google.com/complete/search?client=firefox&q=wet | US | text | 318 b | malicious |
2052 | firefox.exe | GET | 200 | 142.250.185.68:443 | https://www.google.com/complete/search?client=firefox&q=https%3Ewetransfer.com | US | text | 560 b | malicious |
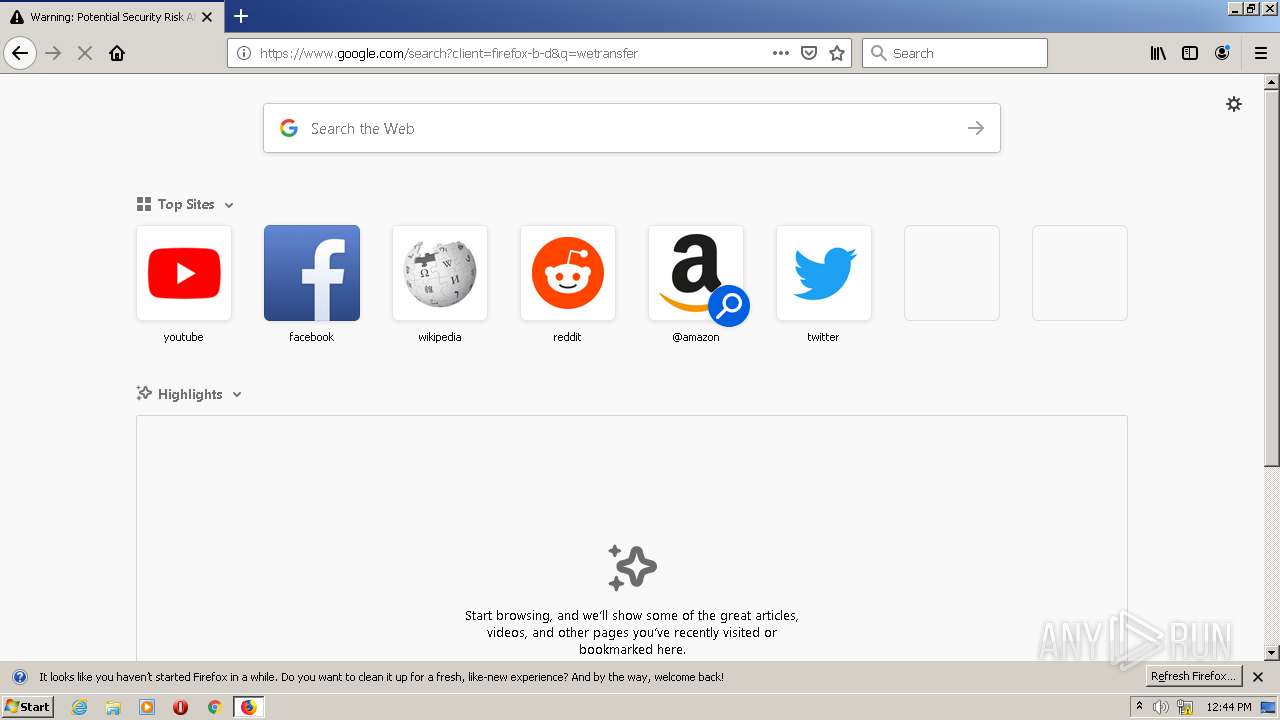
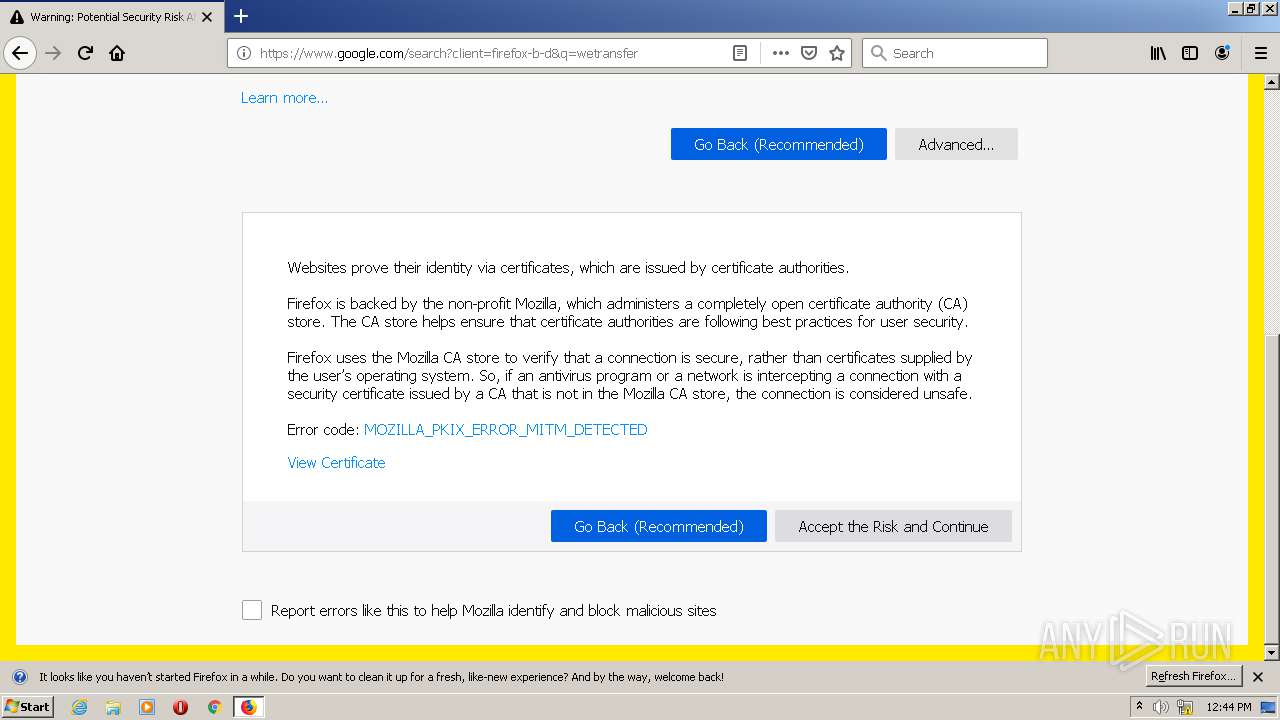
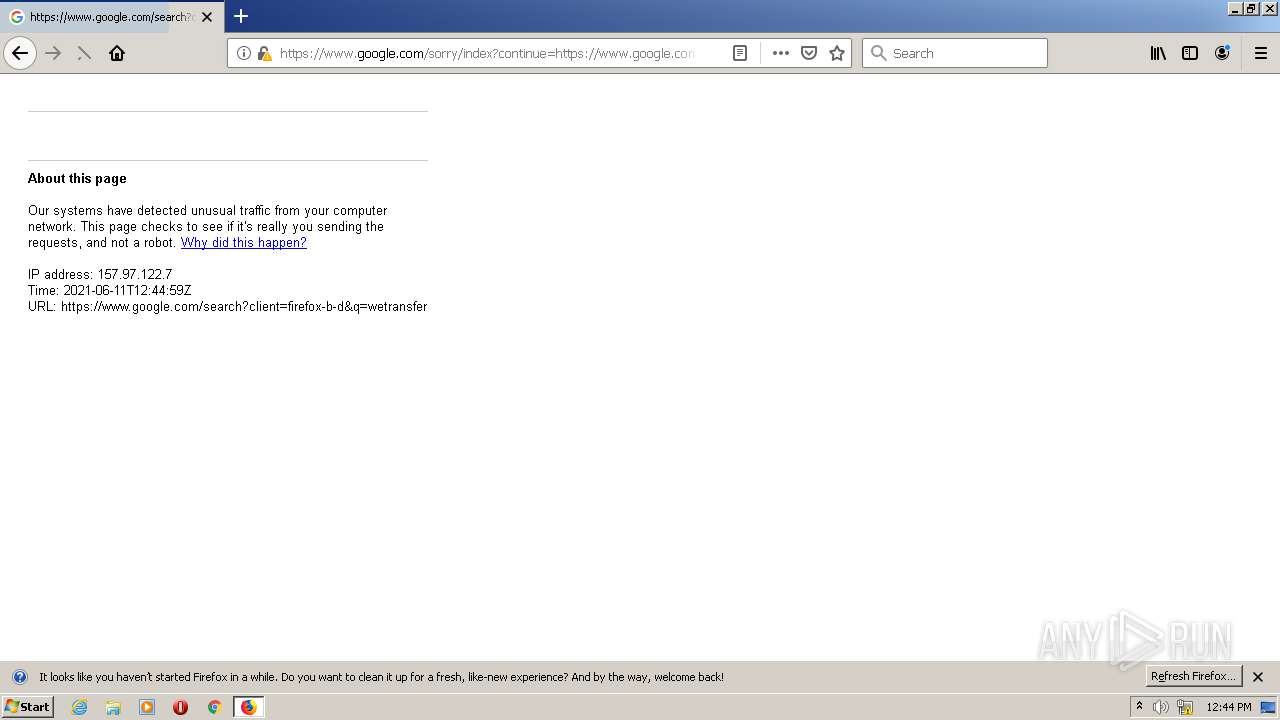
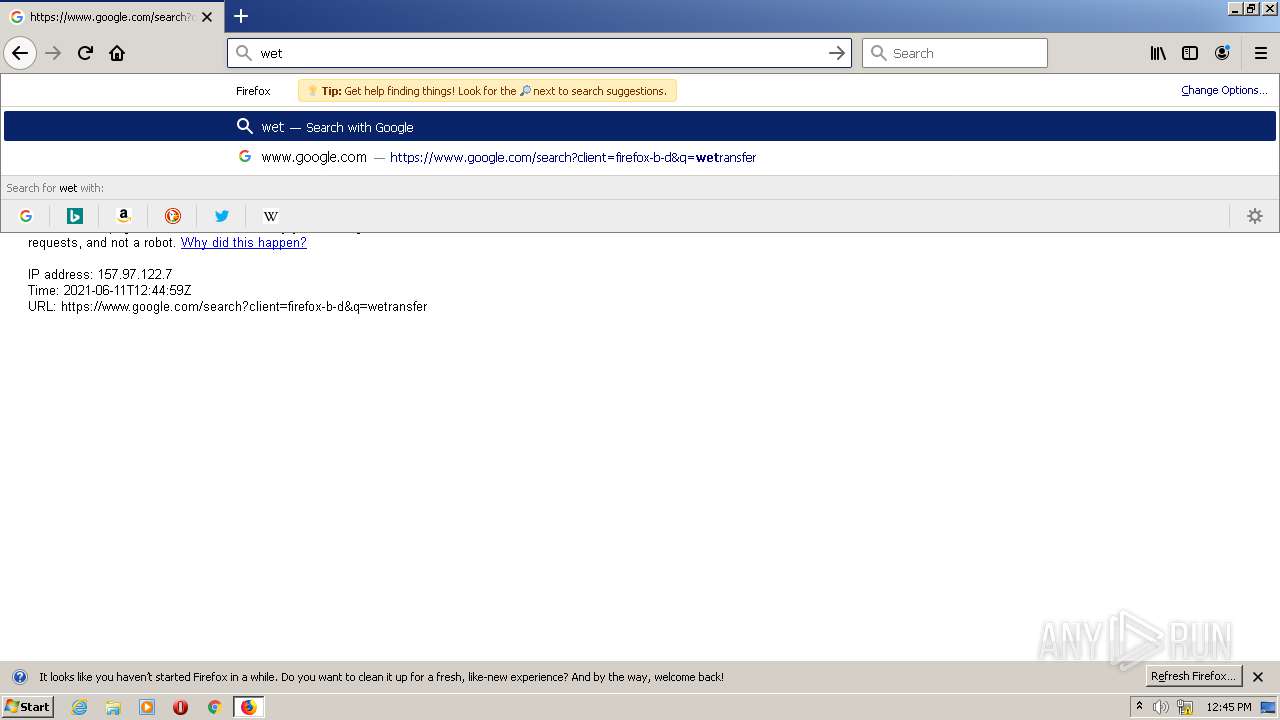
2052 | firefox.exe | GET | 302 | 142.250.185.68:443 | https://www.google.com/search?client=firefox-b-d&q=wetransfer | US | html | 361 b | malicious |
2052 | firefox.exe | GET | 200 | 142.250.185.68:443 | https://www.google.com/complete/search?client=firefox&q=wetransfer | US | text | 285 b | malicious |
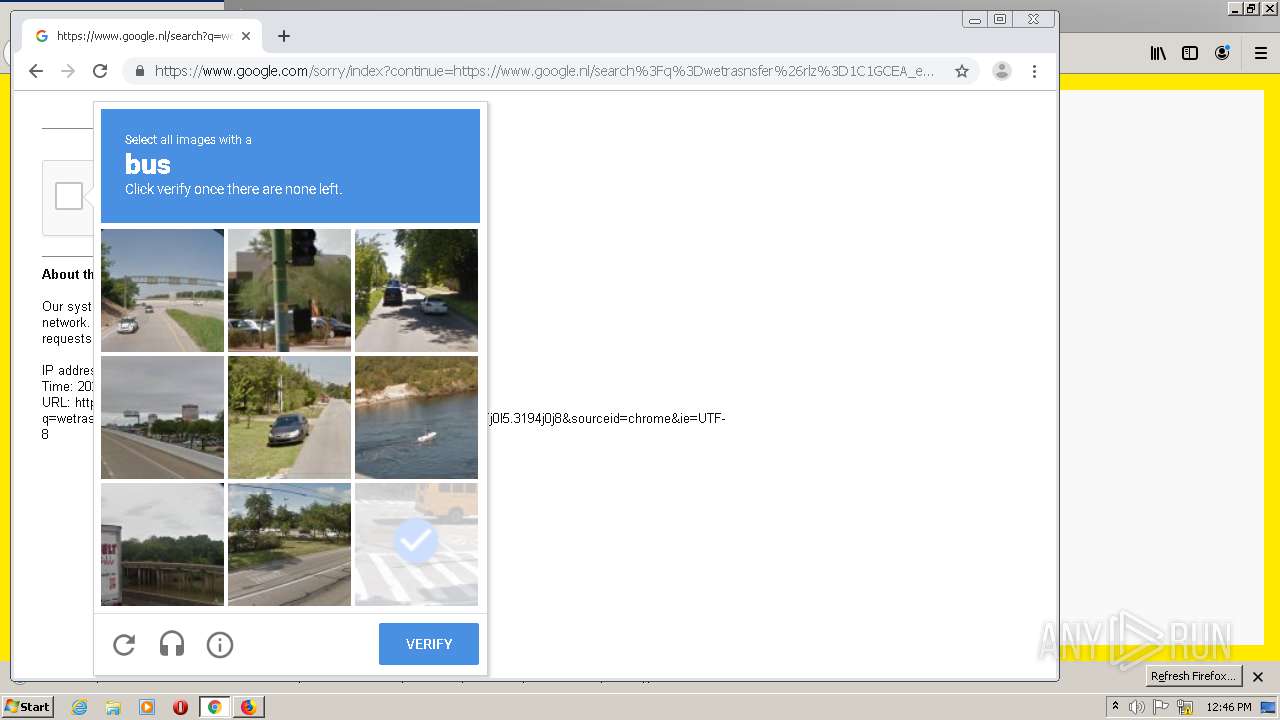
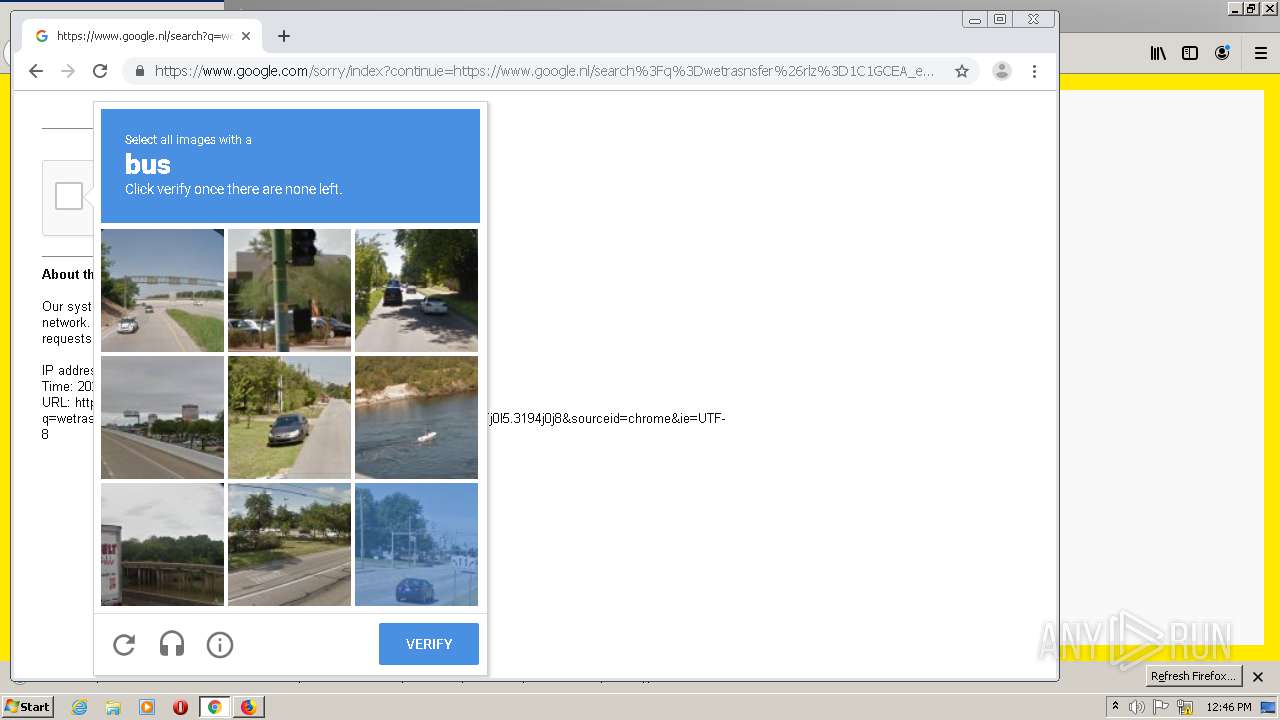
2052 | firefox.exe | GET | 200 | 142.250.185.68:443 | https://www.google.com/recaptcha/api.js | US | text | 850 b | malicious |
2052 | firefox.exe | GET | 200 | 142.250.185.227:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=75 | US | compressed | 84.2 Kb | whitelisted |
2052 | firefox.exe | GET | 200 | 142.250.185.68:443 | https://www.google.com/complete/search?client=firefox&q=wetr | US | text | 245 b | malicious |
2052 | firefox.exe | GET | 200 | 142.250.186.67:443 | https://www.google.com.ua/async/ddljson?async=ntp:1 | US | text | 119 Kb | whitelisted |
2052 | firefox.exe | GET | 200 | 142.250.186.67:443 | https://www.google.com.ua/async/newtab_ogb?hl=en-US&async=fixed:0 | US | text | 154 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2116 | janma.exe | 104.21.16.147:443 | sc.vrss.win | Cloudflare Inc | US | suspicious |
2116 | janma.exe | 172.67.139.153:443 | web.downloadgame247.com | — | US | suspicious |
2116 | janma.exe | 104.21.5.22:443 | api.mariodeluxe.com | Cloudflare Inc | US | suspicious |
2796 | janma.exe | 104.21.16.147:443 | sc.vrss.win | Cloudflare Inc | US | suspicious |
2116 | janma.exe | 172.67.173.77:443 | rss.mario-deluxe.net | — | US | unknown |
2796 | janma.exe | 172.67.139.153:443 | web.downloadgame247.com | — | US | suspicious |
2796 | janma.exe | 104.21.5.22:443 | api.mariodeluxe.com | Cloudflare Inc | US | suspicious |
2796 | janma.exe | 172.67.173.77:443 | rss.mario-deluxe.net | — | US | unknown |
— | — | 104.21.16.147:443 | sc.vrss.win | Cloudflare Inc | US | suspicious |
— | — | 104.21.5.22:443 | api.mariodeluxe.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sc.vrss.win |
| suspicious |
s.myplaylist.win |
| unknown |
web.downloadgame247.com |
| suspicious |
app.download-mario.com |
| unknown |
api.mariodeluxe.com |
| suspicious |
rss.mario-deluxe.net |
| unknown |
teredo.ipv6.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
580 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
580 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |