| File name: | recofn.exe |
| Full analysis: | https://app.any.run/tasks/b172a091-d3d2-43fc-b4a8-e5a7e77da9c0 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 09:18:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | C6D83AE88C6B6528854B679938B4BABC |
| SHA1: | 1F21CC6D11BD9DF1F06413DA44BB265FBB1F0240 |
| SHA256: | CA34AA0DB41B2E1518866480B454226000EFAF57E389F3B1D6DEAA8E25CBA712 |
| SSDEEP: | 24576:NU8w2UNiXTpnHFuNkhvNNbLsZXjLr/g88w3GaIpzfhjh8MGmHoJDHJm5VjYKGDLj:5AiXTXv/8XjLr/g88w3GaIpzfhjh8MGv |
MALICIOUS
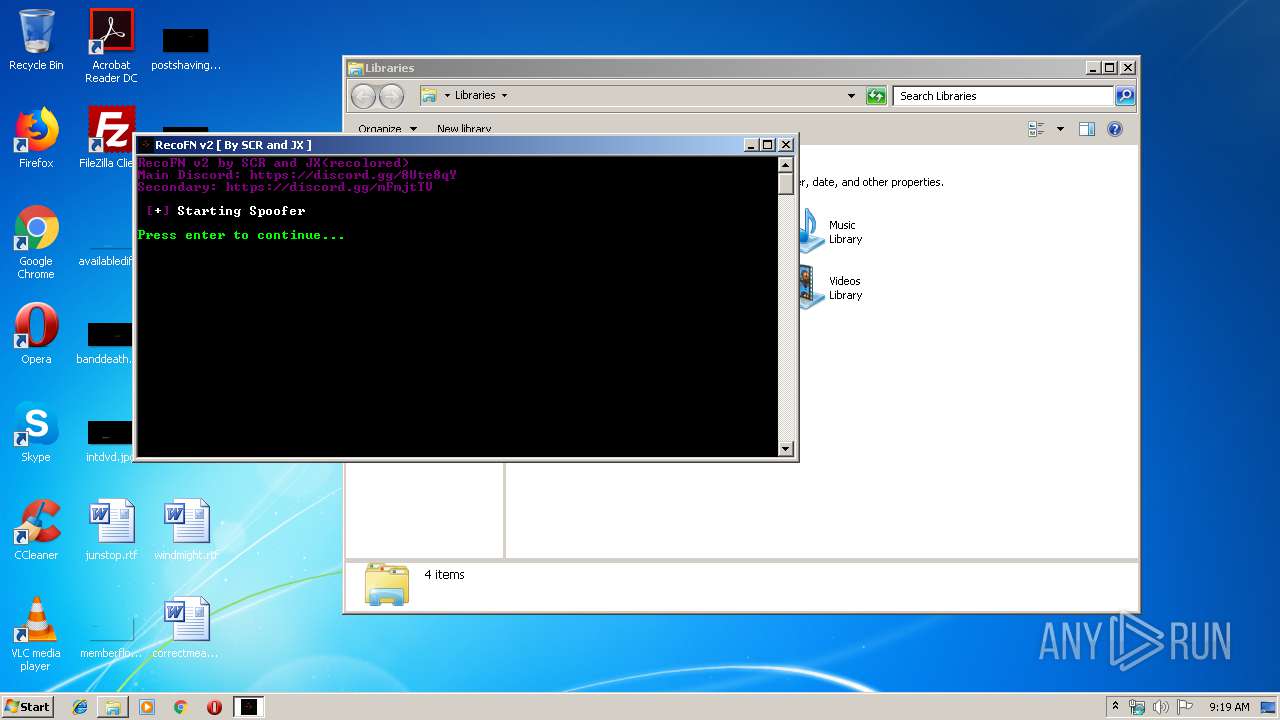
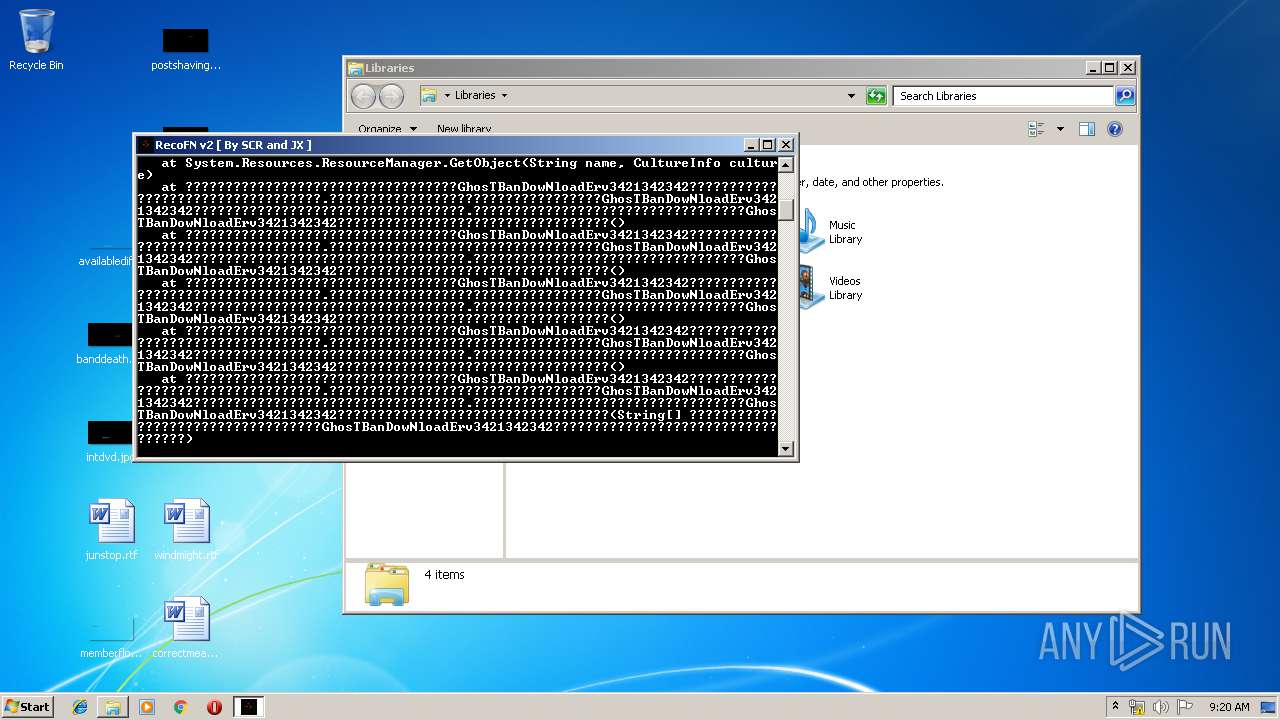
Runs app for hidden code execution
- recofn.exe (PID: 3820)
Changes settings of System certificates
- recofn.exe (PID: 3820)
SUSPICIOUS
Reads Environment values
- recofn.exe (PID: 3820)
Adds / modifies Windows certificates
- recofn.exe (PID: 3820)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3932)
- cmd.exe (PID: 1848)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1848)
- cmd.exe (PID: 3848)
Creates files in the Windows directory
- recofn.exe (PID: 3820)
Starts CMD.EXE for commands execution
- recofn.exe (PID: 3820)
- cmd.exe (PID: 3848)
Application launched itself
- cmd.exe (PID: 3848)
Writes to a desktop.ini file (may be used to cloak folders)
- WMIC.exe (PID: 2720)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3840)
- cmd.exe (PID: 3112)
- cmd.exe (PID: 4092)
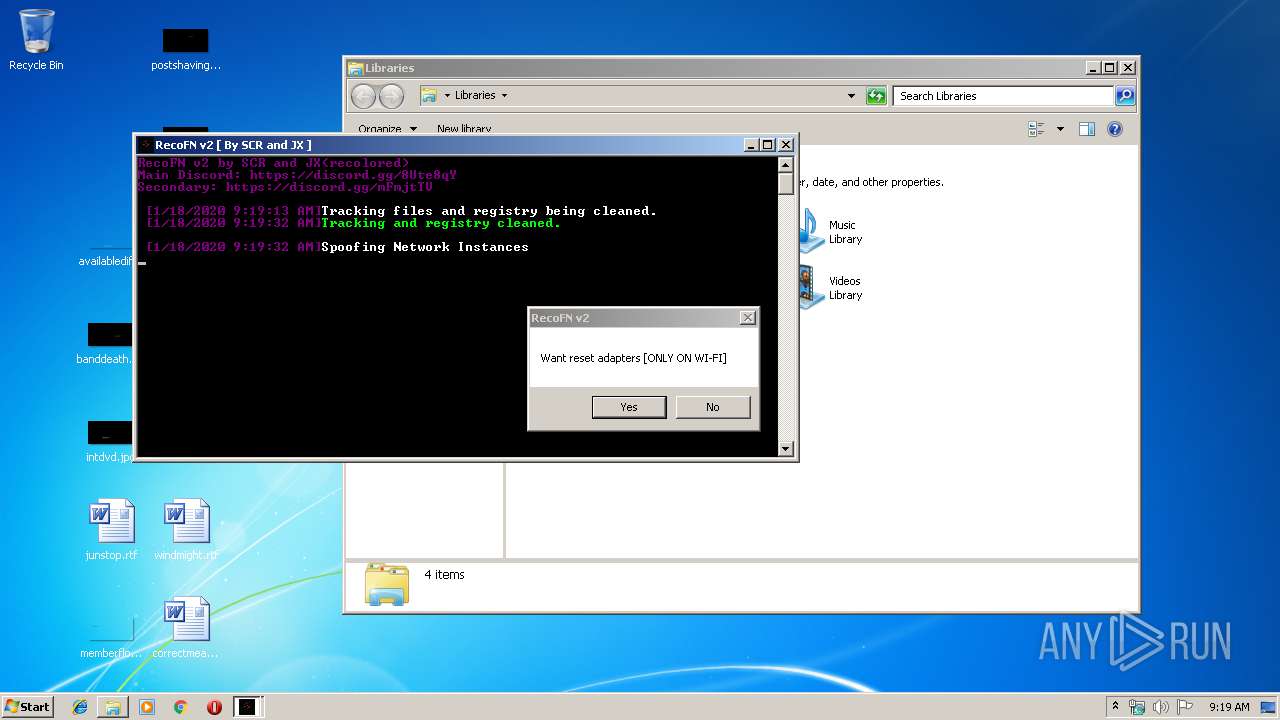
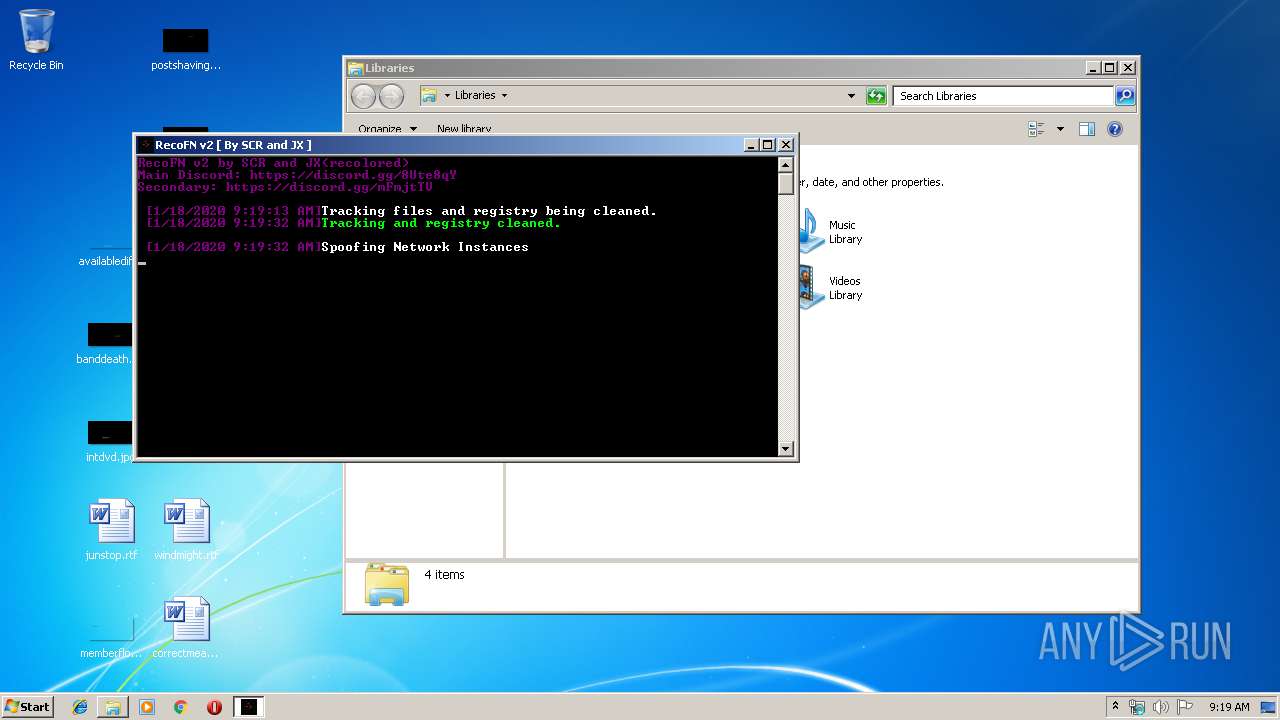
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3848)
Executed via COM
- rundll32.exe (PID: 3196)
Removes files from Windows directory
- recofn.exe (PID: 3820)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (62) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:13 03:19:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 1201152 |
| InitializedDataSize: | 274432 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12722e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | thx to Raiin#1337 for halp |
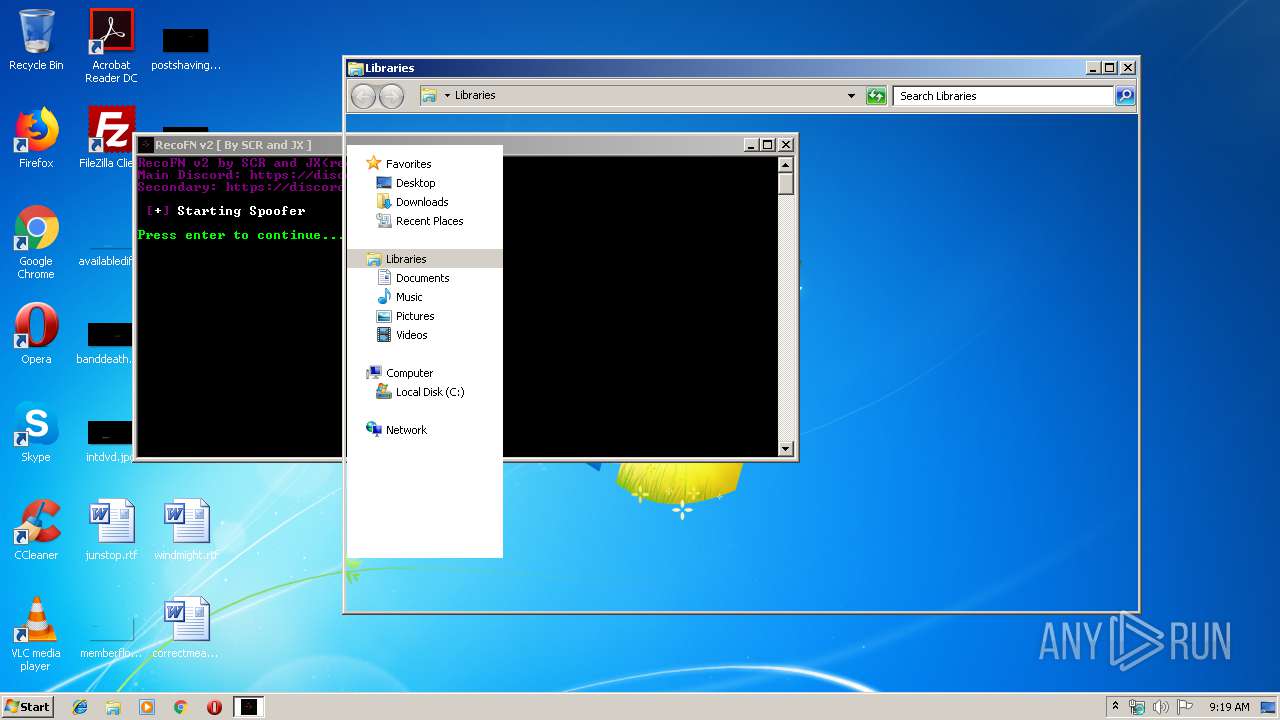
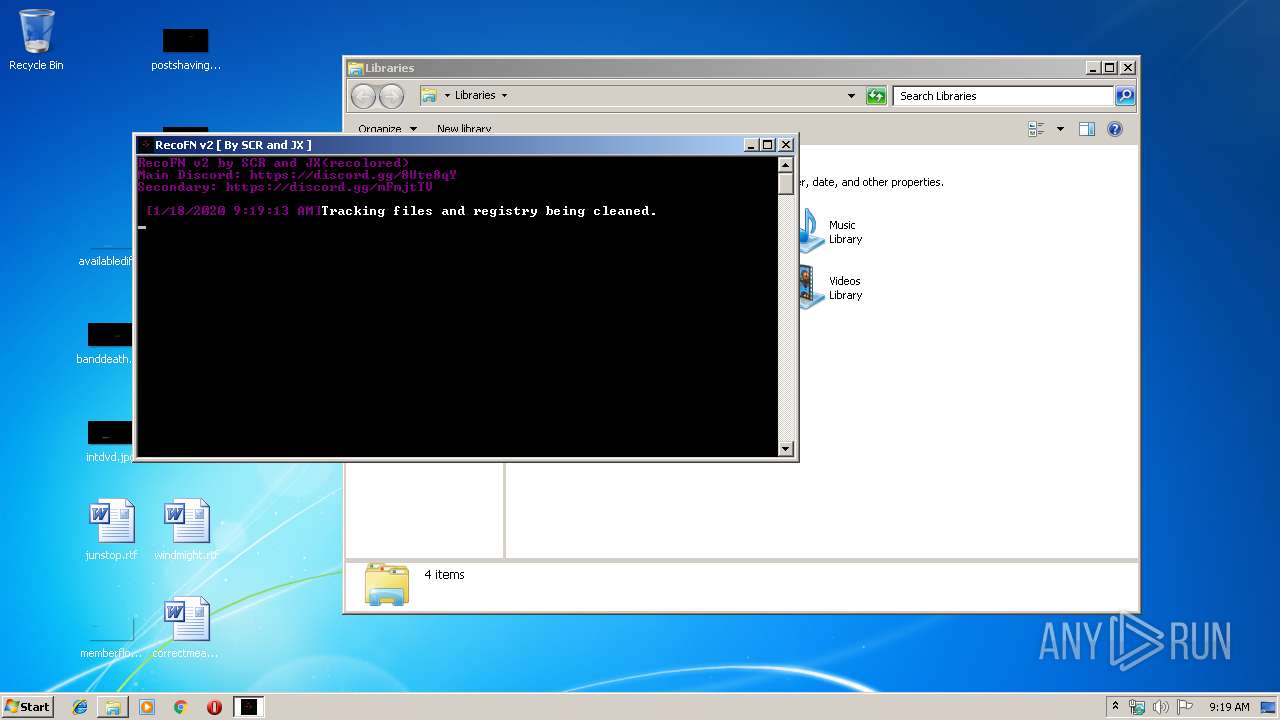
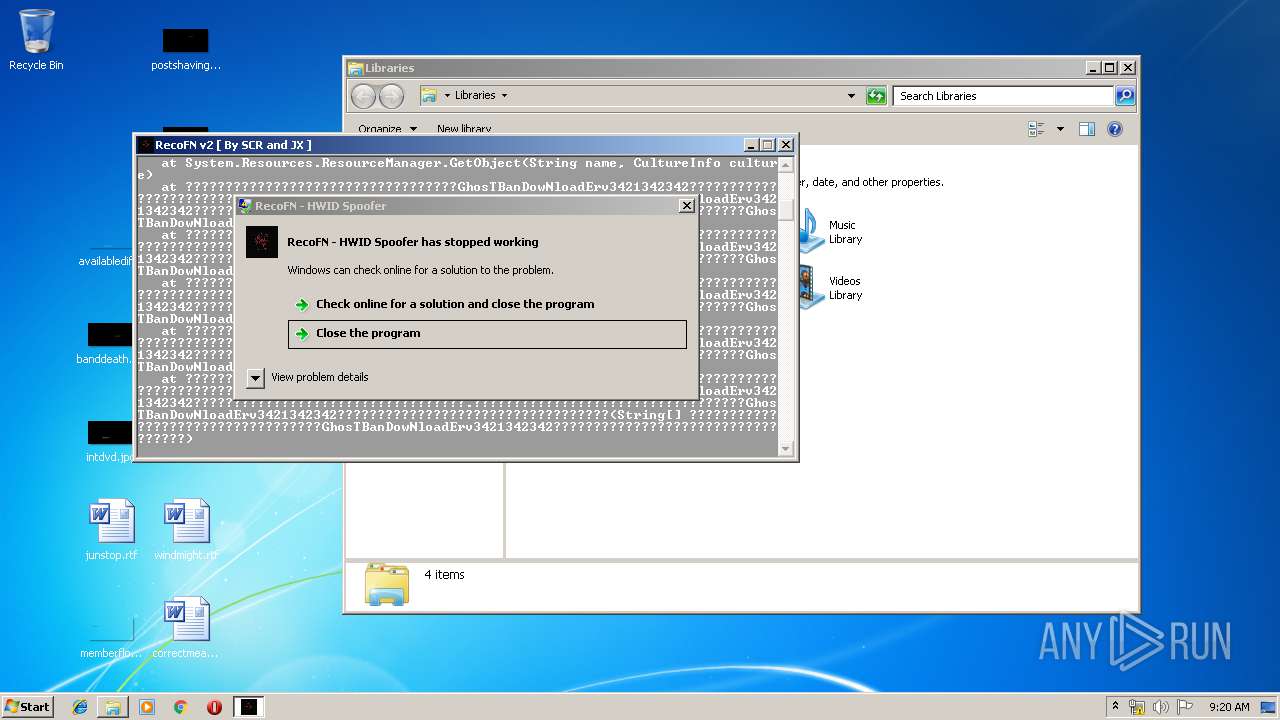
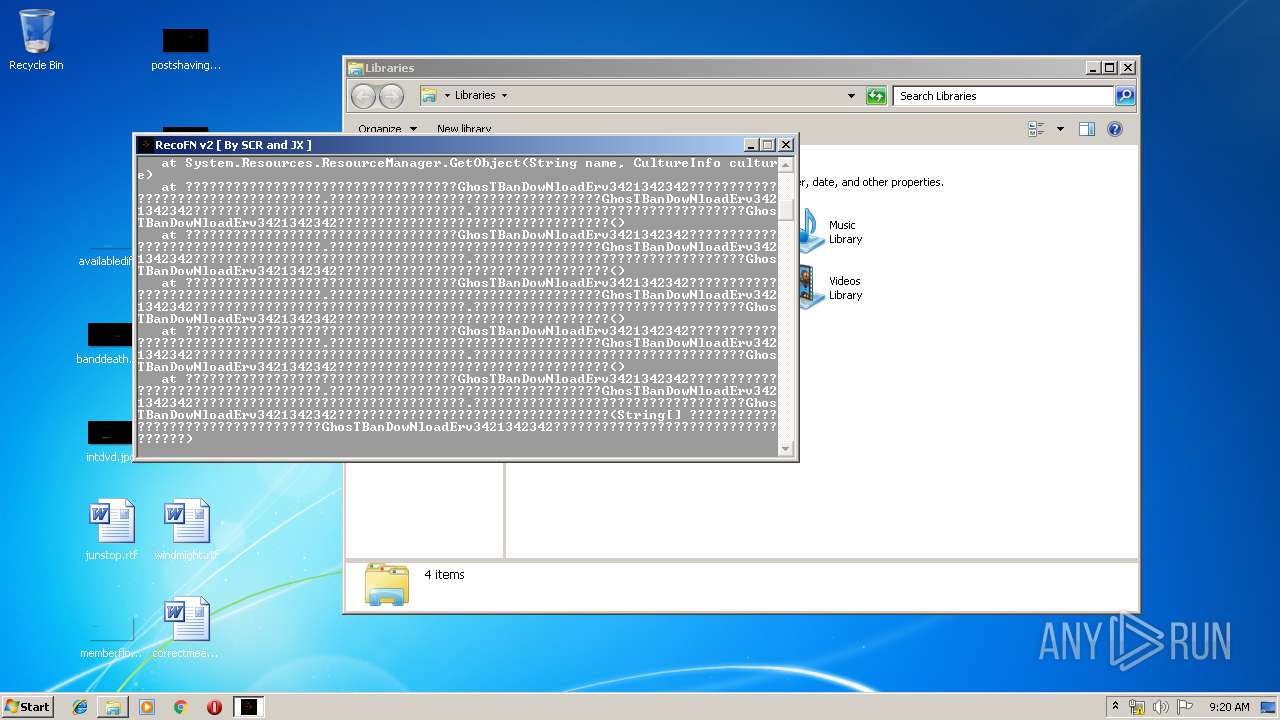
| FileDescription: | RecoFN - HWID Spoofer |
| FileVersion: | 1.0.0.0 |
| InternalName: | RecoFN v2.exe |
| LegalCopyright: | Copyright © TS-23056 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | RecoFN v2.exe |
| ProductName: | RecoFN |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 13-Jan-2020 02:19:32 |
| Comments: | - |
| CompanyName: | thx to Raiin#1337 for halp |
| FileDescription: | RecoFN - HWID Spoofer |
| FileVersion: | 1.0.0.0 |
| InternalName: | RecoFN v2.exe |
| LegalCopyright: | Copyright © TS-23056 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | RecoFN v2.exe |
| ProductName: | RecoFN |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Jan-2020 02:19:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00125234 | 0x00125400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.13208 |
.rsrc | 0x00128000 | 0x00042D40 | 0x00042E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.34076 |
.reloc | 0x0016C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00772 | 3168 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 2.01924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
109
Monitored processes
64
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | taskkill /f /im CEFProcess.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 496 | reg delete "HKEY_LOCAL_MACHINE\Software\Epic Games" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 516 | taskkill /f /im FortniteClient-Win64-Shipping_BE.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | "C:\Users\admin\AppData\Local\Temp\recofn.exe" | C:\Users\admin\AppData\Local\Temp\recofn.exe | — | explorer.exe | |||||||||||
User: admin Company: thx to Raiin#1337 for halp Integrity Level: MEDIUM Description: RecoFN - HWID Spoofer Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 600 | taskkill /f /im BEServices.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | taskkill /f /im FortniteClient-Win64-Shipping_EAC.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | REG QUERY HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Class\{4D36E972-E325-11CE-BFC1-08002bE10318}\07 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | REG QUERY HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Class\{4D36E972-E325-11CE-BFC1-08002bE10318}\0007 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | taskkill /f /im FortniteLauncher.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1152 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | recofn.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
555
Read events
362
Write events
193
Delete events
0
Modification events
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BaseBoardProduct |
Value: Gigabyte X299-WU8 | |||
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BaseBoardVersion |
Value: 1.6 | |||
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BaseBoardManufacturer |
Value: EVGA | |||
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | SystemVersion |
Value: 1.6 | |||
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | SystemManufacturer |
Value: EVGA | |||
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BIOSReleaseDate |
Value: 01/05/2016 | |||
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | SystemProductName |
Value: PL-7A39 | |||
| (PID) Process: | (3820) recofn.exe | Key: | HKEY_LOCAL_MACHINE\HARDWARE\DESCRIPTION\System\BIOS |
| Operation: | write | Name: | BIOSVersion |
Value: A.04 | |||
Executable files
0
Suspicious files
0
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3820 | recofn.exe | C:\Windows\Media\hm65c.bat | text | |
MD5:— | SHA256:— | |||
| 2720 | WMIC.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 3820 | recofn.exe | C:\Windows\Cursors\special.bat | text | |
MD5:F24F62EEB789199B9B2E467DF3B1876B | SHA256:E596899F114B5162402325DFB31FDAA792FABED718628336CC7A35A24F38EAA9 | |||
| 2720 | WMIC.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\desktop.ini | ini | |
MD5:BA96961F5E22882527919E19DAEA510F | SHA256:DACE5AD59099429D8AED4EE279F1263EFB65D64456931398465A396CF0E79BD7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | recofn.exe | GET | 204 | 172.217.18.110:80 | http://clients3.google.com/generate_204 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3820 | recofn.exe | 172.217.18.110:80 | clients3.google.com | Google Inc. | US | whitelisted |
3820 | recofn.exe | 104.20.68.143:443 | pastebin.com | Cloudflare Inc | US | malicious |
3820 | recofn.exe | 74.115.50.111:443 | 127737596-617361524549731340.preview.editmysite.com | Weebly, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
127737596-617361524549731340.preview.editmysite.com |
| unknown |
clients3.google.com |
| whitelisted |